 Open Access
Open Access
ARTICLE
Deterministic PCA-Synchronized 3-D Mesh Watermarking with Fullerene-Guided Carrier Selection
School of Cyber Science and Engineering, Sichuan University, Chengdu, China
* Corresponding Author: Hongxia Wang. Email:
Computers, Materials & Continua 2026, 87(2), 89 https://doi.org/10.32604/cmc.2026.075967
Received 11 November 2025; Accepted 28 January 2026; Issue published 12 March 2026
Abstract
Mesh models are among the primary representations for storing 3-D objects, encapsulating detailed geometric information. 3-D mesh watermarking, in particular, plays a central role in the protection of 3-D content. However, frequency-domain methods rely on complex parameterization and spectral decomposition, which are sensitive to mesh topology and resolution and often introduce perceptible artifacts. Spatial-domain techniques, on the other hand, typically embed watermarks in global or randomly selected regions, leading to visible distortions and reduced robustness. To address the above limitations and protect model copyright without compromising the original aesthetic quality, we propose a deterministice PCA-synchronized 3D mesh watermarking method with fullerene-guided carrier selection. First, a deterministic principal component analysis (PCA)–based mesh synchronization algorithm is employed to align the models to a canonical pose. Next, a fullerene-inspired carrier selection strategy is employed to determine the watermark carriers, leveraging the structural characteristics of fullerene molecules to achieve a more rational and effective carrier selection. Finally, to balance the embedding strength and enhance visual quality, the watermark information is embedded using an APQIM (Adaptive Parity-Check Quantization Index Modulation) scheme. The experimental results show that our method can achieve high visual quality with scalable capacity and strong robustness compared with existing methods. The watermarking scheme can resist various attacks, including simplification, smoothing, Gaussian noise, translation, and rotation.Keywords
With the rapid advancement of computer graphics and hardware technologies, three-dimensional (3-D) models have become indispensable in film production, industrial design, VR and AR, online gaming, and digital cultural industries [1]. The increasing realism of these models stems from the maturity of modeling software and steady improvements in rendering hardware. However, this accessibility also exposes 3-D assets to copyright infringement [2]. High-resolution character models in games can be illicitly extracted and redistributed, industrial prototypes may be misappropriated without authorization, and piracy frequently occurs on 3-D printing and digital asset trading platforms. Digital watermarking has long been studied and deployed for copyright protection in conventional media such as images and text documents [3,4]. To address these threats, 3-D digital watermarking has emerged as a promising solution for intellectual property protection [5].
Among the various representations of 3-D data, mesh models are particularly dominant due to their compact structure, efficient storage, fast rendering, and flexibility in editing and deformation [6]. Beyond their efficiency, meshes also carry expressive geometric and structural information, which underpins critical applications in VR and AR, digital twins, medical imaging, cultural heritage preservation, and industrial manufacturing. These unique characteristics make mesh watermarking a central research direction in 3-D copyright protection [7].
Despite their importance, mesh watermarking presents challenges distinct from watermarking traditional media such as images or audio:
• Geometric complexity: Meshes contain large numbers of vertices, edges, and faces with intricate local structures. Even minor perturbations may cause perceptible distortions.
• Diverse operations: In practice, meshes are often subject to simplification, resampling, smoothing, compression, and reconstruction, each of which may disrupt watermark integrity.
• Flexible representations: A single object can be represented by meshes with varying resolutions and topologies, complicating robustness across representations.
• Complex perceptual sensitivity: Human vision is highly sensitive to geometric distortions, making imperceptible watermarking considerably harder than in images.
Thus, the core challenge is to design watermarking algorithms that are both imperceptible and robust, while preserving the visual fidelity of the original model.
Existing approaches can be broadly categorized into frequency- and spatial-domain methods [8]. Frequency-domain techniques parameterize or decompose meshes (e.g., via spherical parameterization, Laplacian spectra, spherical harmonics, or wavelet transforms) before embedding watermarks in transform coefficients. While these methods can achieve favorable robustness—imperceptibility trade-offs against global deformations, they suffer from high preprocessing cost, sensitivity to mesh topology and resolution, and vulnerability to resampling or nonlinear reconstruction [9,10]. In contrast, spatial-domain techniques embed watermarks directly in vertex coordinates, differential coordinates, or normal vectors. These methods are computationally efficient, impose minimal embedding and extraction overhead, and integrate seamlessly into modeling and rendering pipelines [11]. In practice, the simplicity, scalability, and direct control over visual quality make spatial-domain methods more attractive for real-world applications despite their robustness challenges [12]. However, spatial methods embed directly in vertex coordinates without geometric guidance, often causing noticeable distortions in salient regions and offering limited robustness to geometric attacks.
Motivated by these considerations, we adopt a spatial-domain approach and introduce an improved mesh watermarking framework. Our method integrates localized embedding with a perception-driven distortion minimization mechanism, enabling enhanced robustness and imperceptibility without sacrificing visual quality. Specifically, we design a deterministic principal component analysis (PCA) algorithm for mesh synchronization, ensuring alignment to a canonical pose. We then embed watermark bits into mesh patches identified by a novel spatial partitioning strategy inspired by fullerene molecular structures, thereby ensuring a more uniform and geometry-aware distribution of watermark carriers across the model. Finally, we propose an adaptive parity-check quantization index modulation (PQIM) scheme that dynamically adjusts embedding strength to local geometric properties, thereby balancing imperceptibility and robustness.
Our contributions are summarized as follows:
• We propose a deterministic PCA-synchronized 3-D mesh watermarking with fullerene-guided carrier selection method. Extensive experiments on diverse 3D models validate the effectiveness and superiority of the proposed method in terms of both imperceptibility and robustness.
• A deterministic PCA-based synchronization algorithm that consistently aligns meshes to a canonical pose.
• Our method employs a fullerene-inspired spatial partitioning strategy to enable structured and effective selection of watermark carriers.
• An APQIM scheme that dynamically adjusts embedding strength according to local geometry, ensuring imperceptibility while maintaining robustness.
2.1 Watermarking in Spectral Domain
Watermarking in the spectral domain embeds data in transformed frequency representations, achieving better robustness—imperceptibility trade-offs but often at the cost of higher complexity or visual artifacts. Murotani et al. [8] embedded watermarks by modulating spectra-domain coefficients derived from the eigenvectors of the Laplacian matrix. This method provides robustness against rotation, scaling, and translation, but it is computationally intensive and sensitive to local editing. Cayre and Macq [9] utilized the Laplacian spectrum of the mesh and embedded watermarks by modifying low- or mid-spectra components. Their method, based on spectral characteristics, offers strong robustness against geometric attacks. Liu et al. [10] proposed a blind spectral-domain watermarking method for parameterised surfaces, which involved modifying the coefficients of the dirichlet manifold harmonic transform (DMHT). Although their method is robust, it requires mesh parameterisation and is computationally expensive. Compared with spatial-domain approaches, spectra-domain methods achieve a more favorable balance between robustness and imperceptibility. However, due to their inherent characteristics, they often leave structured artifacts on the model surface, which we consider unacceptable from the perspective of preserving the aesthetic integrity of 3-D meshes.
2.2 Watermarking in Spatial Domain
Watermarking in the spatial domain embeds information directly into geometric features (e.g., vertices or normals), offering simplicity and efficiency but with limited robustness to geometric attacks. Since 3-D mesh watermarking techniques were introduced in [13], there have been several attempts to improve the performance in terms of imperceptibility and robustness. Cho et al. [14] presented a blind watermarking method based on the statistical distribution of vertex norms. By partitioning the norms into statistical intervals and adjusting their distribution, they achieved blind extraction and improved robustness. However, the method still exhibits limited capacity and significant visual distortion. Building upon Cho et al. [14], Delmotte et al. [15] proposed a blind watermarking method for 3-D printed objects that embeds data in shape histograms instead of vertex coordinates, improving robustness to resampling and print—scan processes while preserving geometric fidelity. Nevertheless, the method still suffers from low embedding capacity and limited imperceptibility. Yang et al. [16] introduced a watermarking approach based on algebraic topology and differential geometry, achieving zero visual distortion, strong resistance to arbitrary topological attacks. Nevertheless, methods of this type are entirely vulnerable to attacks involving vertex modifications, such as face reordering, which significantly limits its practical applicability. Deep learning-based approaches [17,18] may appear to represent a new direction, but they are essentially extensions of spatial-domain methods, leveraging neural networks to automatically learn how to embed information without compromising the visual appearance of the model. While these methods have achieved certain improvements in robustness, they require large amounts of training data and exhibit limited generalization, making them difficult to deploy in real-world scenarios. Among these methods, even though some achieve satisfactory imperceptibility and robustness, their practical application is hindered by an insufficient embedding capacity.
We designed three parts to accomplish watermark embedding. The first part is a deterministic PCA-based mesh synchronization algorithm, which provides a deterministic synchronization mechanism for watermark embedding. The second part is a face-selection algorithm based on fullerene molecular models and PCA mapping, enabling a more rational choice of mesh faces as watermark carriers. The third part is a triangular-face perturbation algorithm based on parity-check quantization index modulation, which minimizes modifications to the mesh faces while maintaining robustness.
3.1.1 Deterministic PCA-Based Mesh Synchronization Algorithm
Our proposed watermarking method requires modifying specific triangular faces. Hence, accurately identifying the watermark-bearing carriers during extraction is of paramount importance. We propose a deterministic PCA-based mesh synchronization algorithm to address the synchronization problem in watermark embedding and extraction, as shown in Fig. 1. The core idea is to automatically construct a deterministic coordinate system aligned with the intrinsic directions of the mesh through deterministic PCA of the model’s geometric structure, providing a unified reference frame for both embedding and extraction. This design fundamentally avoids the synchronization failures caused by coordinate system shifts or randomness in traditional methods [19], ensuring that the watermark can be accurately recovered even under complex geometric transformations.
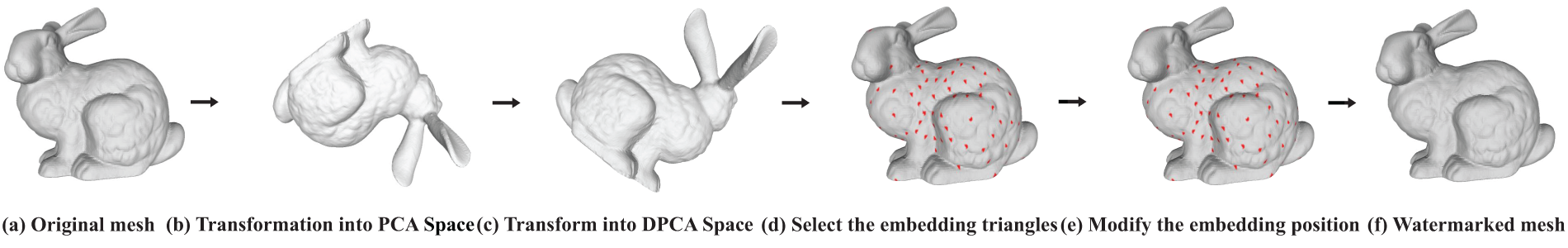
Figure 1: Overview of our methods. (a) The mesh before watermarking. (b) Transform the mesh into the PCA space. (c) Transform the mesh into the DPCA space. (d) Selecting embedding triangles in the mesh using the fullerene-based method. (e) Modify the corresponding surface on the mesh according to the APQIM method. (f) Obtained the watermarked mesh.
The deterministic PCA-based mesh synchronization algorithm first centralizes all vertices of the model using (1). In this process, the centroid is estimated based on volumetric moments, as described in (2) and (3). As the centroid is derived from volumetric moments, which require a watertight representation, the proposed algorithm naturally targets closed 3D models, a common assumption in 3D mesh models watermarking scenarios.
where
By performing eigen-decomposition on S, a
Then, according to Eq. (5), we transform the points on the model into the PCA coordinate system.
However, since the resulting eigenvectors do not have a fixed direction (they represent lines rather than oriented vectors [20]), applying PCA to realign a model after a rotation attack may fail to restore the model to its original PCA-aligned position. To enforce a deterministic and consistent coordinate system, the eigenvectors obtained from PCA are first sorted in descending order according to their corresponding eigenvalues, so that the principal directions associated with the largest, intermediate, and smallest variances are consistently assigned to the
Specifically, we first sort the three principal axes of the computed eigenvector matrix
where M is the original coordinate axes matrix and T is the corresponding rotation matrix for adjusting the coordinate axes directions. T is determined based on three principal axes passing through the centroid of the model. For each axis, the distance from the centroid to the intersection point with the model surface is calculated. The direction corresponding to the longest segment is taken as the positive direction. Then, it is determined whether this direction aligns with the original eigenvector direction: if aligned, assign +1; otherwise, assign −1. This procedure yields eight possible combinations of these assignments, as shown in (7).
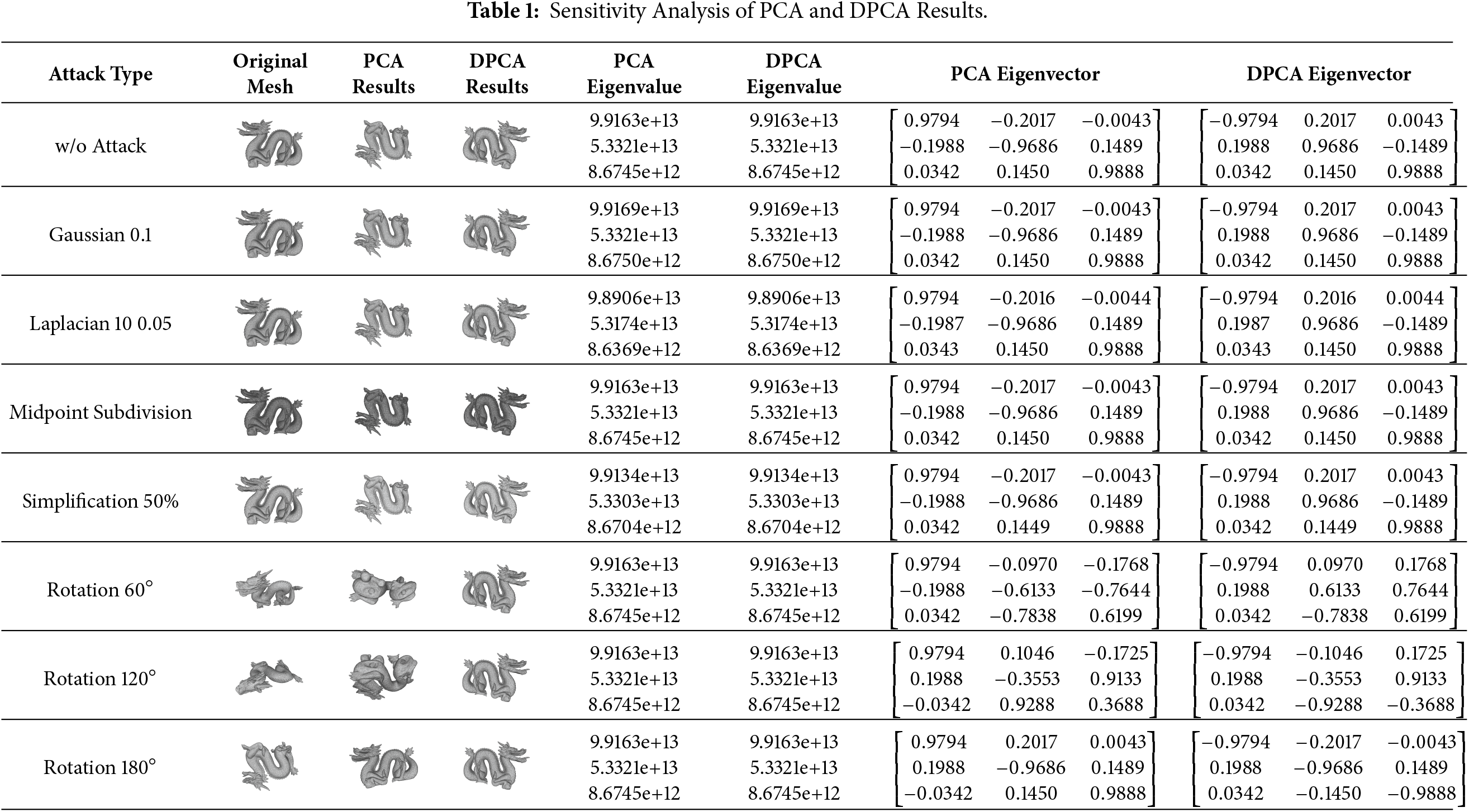
By employing (6) and (7), we obtain a deterministic PCA matrix that ensures uniqueness of the result and thereby guarantees synchronization of the watermark. To demonstrate that the eigenvalues and eigenvectors of PCA remain stable under small perturbations, we conducted a sensitivity analysis experiment, and the results are reported in Table 1. We performed PCA and DPCA on the original model as well as on models subjected to various perturbations, and transformed them into the corresponding new coordinate frames. It can be observed that the eigenvalues obtained by both PCA and DPCA remain highly stable under different perturbations. However, the eigenvectors produced by conventional PCA may be rotated to different orientations under rotation attacks, whereas the eigenvectors obtained by DPCA consistently maintain a unified orientation due to our proposed improvements.
3.1.2 Region Selection Algorithm Based on Fullerene Molecular Model
To minimize modifications to 3-D mesh models and preserve their original state and aesthetic quality, we designed a face selection method based on fullerene molecular models and deterministic PCA mapping as shown in Fig. 2. Unlike existing approaches that commonly rely on random selection or local heuristics, this method leverages the high symmetry and uniform distribution characteristics of fullerene molecular structures [21] to construct a stable partitioning framework in three-dimensional space. This ensures that the selection of mesh faces for watermark embedding is both unique and globally balanced. In Fig. 3, we illustrate three carrier selection strategies: uniform spherical partitioning, Fibonacci spirals, and the fullerene-based approach. Compared with uniform spherical and Fibonacci-based carrier selection strategies, the fullerene-guided approach provides a more structured and geometrically balanced partition of the embedding space. Uniform spherical sampling ensures angular uniformity but suffers from severe carrier clustering near the model center, while Fibonacci spirals, although improving spherical coverage, exhibit asymmetry that can adversely affect subsequent PCA computations. In contrast, the fullerene molecular model offers a discrete, highly symmetric, and near-equal-area directional set, which effectively distributes embedding carriers across the entire surface. This structured partition significantly reduces repeated face selection and carrier collisions, thereby improving both robustness and imperceptibility, especially under high embedding capacities. Therefore, we have chosen the carrier selection scheme based on the fullerene molecule model. By integrating deterministic PCA mapping, the faces in the PCA-aligned model are associated with their counterparts in the original mesh, allowing modifications to be applied solely to the selected watermark carrier faces while leaving non-watermarked regions untouched. This strategy further enhances the imperceptibility of the watermark.
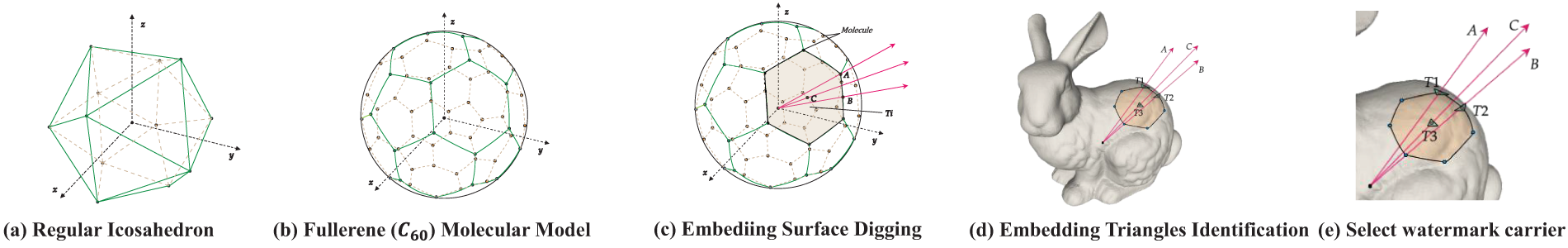
Figure 2: Overview of the watermark carrier selection algorithm based on the fullerene molecular model. Firstly, we calculate the fullerene molecular model through (a) and (b). Then, we determine the direction for embedding the watermark based on the points (e.g., A), edge centers of the fullerene molecular model (e.g., B) and face centers (e.g., C). Finally, after aligning the centroid of the mesh model with that of the fullerene molecular model, the watermark carrier is determined based on the intersection between the predefined embedding direction and the surface of the model (e.g., T1, T2, T3).
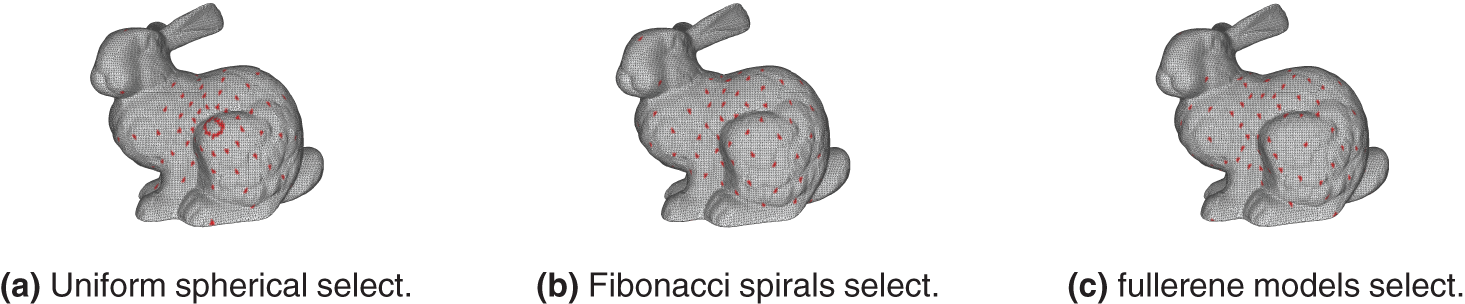
Figure 3: Three carrier selection strategies.
We first construct the mesh model of the fullerene molecule, which is carried out as follows: Using the golden ratio
where
Specifically, based on the deterministic PCA-based mesh synchronization algorithm, we construct a fullerene molecular model on the unit sphere and extract direction vectors formed by its vertices, edge midpoints, and face centers relative to the molecular centroid as watermark embedding directions. These direction vectors naturally provide a uniform coverage of three-dimensional space due to the inherent symmetry of the fullerene structure. Next, the fullerene model is spatially aligned with the deterministic PCA-aligned mesh. Since the deterministic PCA-based synchronization already centralizes the mesh and the fullerene model is also constructed with the origin as its reference, both centroids coincide at (0, 0, 0), allowing direct placement in the same coordinate system. This ensures a consistent reference frame for establishing correspondences between the two models. Based on the selected watermark embedding directions, we identify the mesh faces in the deterministic PCA-aligned model that intersect these directions. Using the deterministic PCA mapping, we then locate the corresponding triangular faces on the original model, which serve as the final watermark carrier faces. We do not directly modify the faces on the PCA-aligned model because the inverse transformation of the PCA alignment cannot perfectly restore the mesh to its original positions due to inherent loss. Therefore, the deterministic PCA-aligned mesh is only used for watermark synchronization, while all modifications are applied to the corresponding faces on the original model. This ensures that non-watermarked regions remain completely unaffected.
3.1.3 Adaptive Parity-Check QIM-Based Watermark Embedding
Compared with other quantization methods, APQIM offers high embedding robustness, controllable distortion, and low implementation complexity, making it particularly suitable for watermark embedding in 3-D mesh models. Therefore, in this work, we adopt APQIM as the core embedding method to minimize geometric perturbations while ensuring watermark robustness.
Concretely, The first step is to normalize
where
The optimal quantization step size
where
Finally, the actual modification
The detailed embedding process is illustrated in Fig. 4. In Fig. 4b, the modification direction is determined by the computed actual adjustment magnitude, allowing the modification to either protrude outward from or indent inward into the local surface of the model.
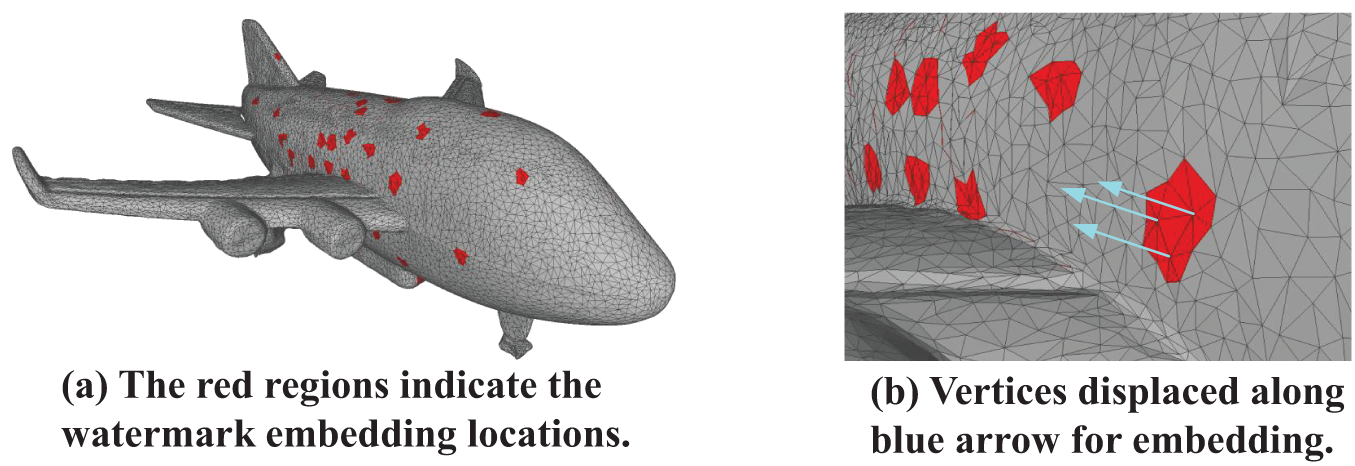
Figure 4: (a) Watermark embedded at the central triangle within the red region. (b) The embedding positions of the three vertices of the triangular face are displaced along the direction of the blue arrow.
The watermark extraction process is reverse to the embedding process, as shown in Fig. 5. First, the watermarked 3-D mesh model is transformed into spherical coordinates in the same way as during embedding. Then, the model is rotated to the embedding pose using the PCA algorithm. The space is divided according to the fullerene elements, and the intersecting faces of the model in each embedding direction are identified. Finally, the distances between these intersecting faces and the model center are computed, and after processing with the APQIM method, the parity of the integer parts of these distances is determined. Based on (15), the embedded watermark bitstream is then extracted. Based on (15), the embedded watermark bitstream is extracted.
where
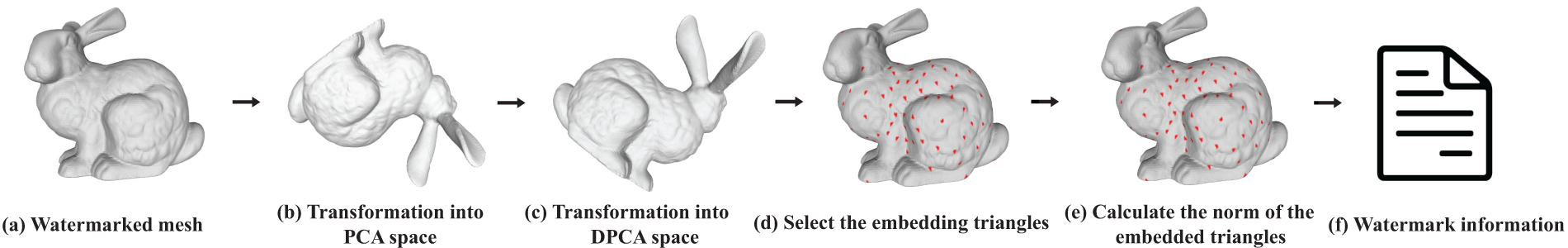
Figure 5: Overview of the watermark extraction algorithm. (a) The mesh from which we want to extract the watermark. (b) Transform the mesh into the PCA space. (c) Transform the mesh into the DPCA space. (d) Select watermark-containing triangular facets in the mesh using the fullerene-based method. (e) Calculate the embedded watermark information based on (d) using the APQIM method. (f) Obtained watermark information.
OmniObject3-D: OmniObject3-D is a 3-D mesh model dataset comprising high-quality, real-scanned objects. It contains 6000 models spanning 190 everyday categories. The scans are highly realistic and were captured using professional equipment [22]. For our experiments, we randomly selected 300 models and simplified their face counts to between 68,000 and 72,000. Classical Models: Some classic 3-D models, including Bunny, Buddha, Cow, Horse, Dragon, etc. [23,24]. These models were created by Stanford University and the Georgia Institute of Technology, etc.
We adopt six state-of-the-art 3D mesh watermarking algorithms as our baselines for performance comparison. Among them, JIANG2017 [25], PENG2022 [26], TSAI2020 [27], and HOU2023 [28] are spatial-domain methods, SPECTRAL [29] represents a frequency-domain approach, and WANG2022 [30] is a deep learning-based method. Together, these baselines provide a comprehensive benchmark for evaluating the robustness and imperceptibility of our proposed scheme.
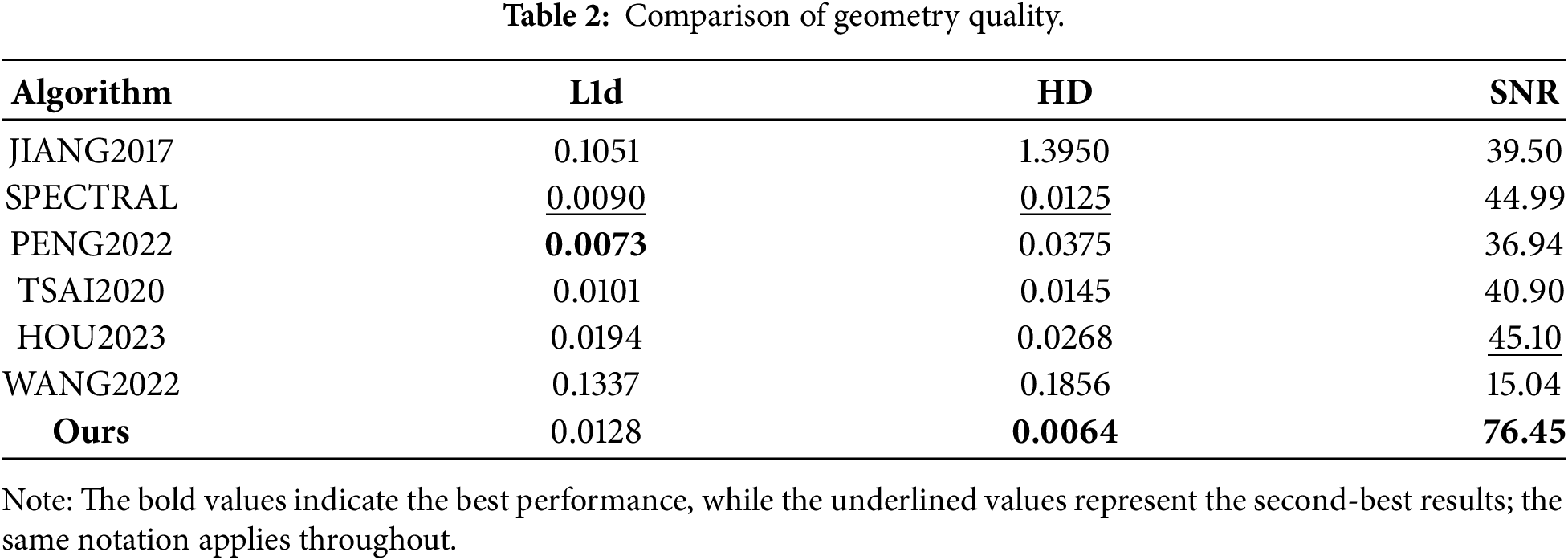
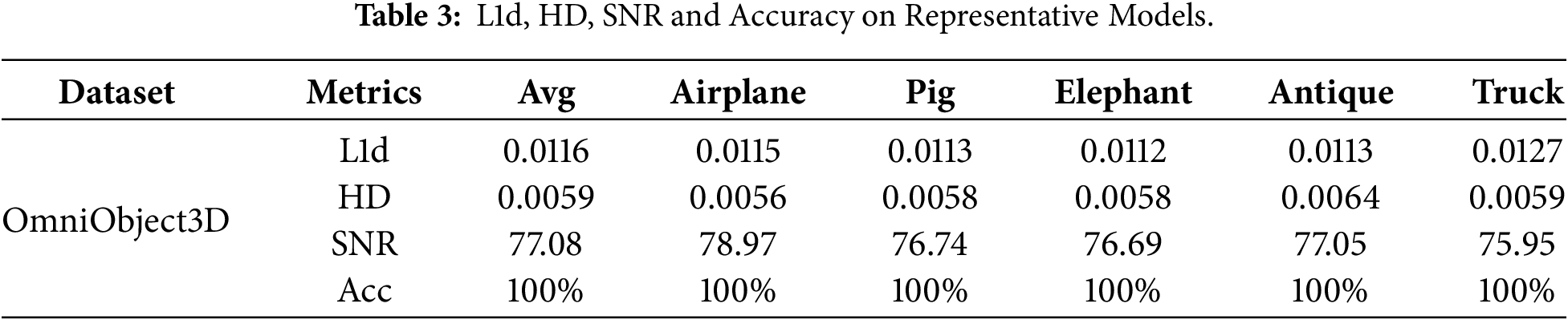
Imperceptibility: To demonstrate the superiority of the proposed method in terms of imperceptibility, we computed several widely used distortion metrics, including the L1 norm of vertex difference (L1d), Signal-to-Noise Ratio (SNR) and Hausdorff distance (HD), to quantify the degree of geometric deviation. Among these metrics, smaller values of L1d and HD are desirable, whereas a larger SNR value is preferable. Robustness: The accuracy of detection results is an important metric for evaluating the robustness of watermarking. We use average bit accuracy to evaluate the extracted message accuracy.
In this study, the workstation is Windows 11, RAM 128 GB, 13th Gen Intel(R) Core(TM) i9-13900K. All implementations were developed using Python 3.10.11. For a fair comparison, We set unified experimental standards. We choose Gaussian noise (
We conduct a comparative analysis against existing watermarking methods in terms of geometric quality, as reported in Table 2. The geometric distortion of the model is minimal, ensuring high visual quality. Experimental results show that the errors on all tested models remain at an extremely low level, well below the threshold of human visual perception, confirming that the proposed algorithm can preserve both geometric and visual characteristics. Furthermore, compared with existing methods, our approach consistently achieves better performance in HD and SNR, demonstrating that the integration of fullerene-based directional selection and adaptive quantization step size effectively reduces model perturbations and achieves strong imperceptibility without compromising robustness. The non-optimal L1d value arises because our method modifies only the selected specific facets rather than the entire mesh, as we aim to preserve more of the model’s original geometric details.
We present a comparison of several models before and after watermark embedding, with some typical models shown in Fig. 6, and their imperceptibility metrics are listed in detail in Table 3. We also visualized them. As we can see, (k)–(o) of Fig. 6 depict the vertex-wise geometric residuals, represented as a signed Euclidean distance field. The colormap encodes the magnitude and direction of deformation: red for positive values (protrusion), blue for negative values (indentation), and green for regions within a minimal tolerance threshold.
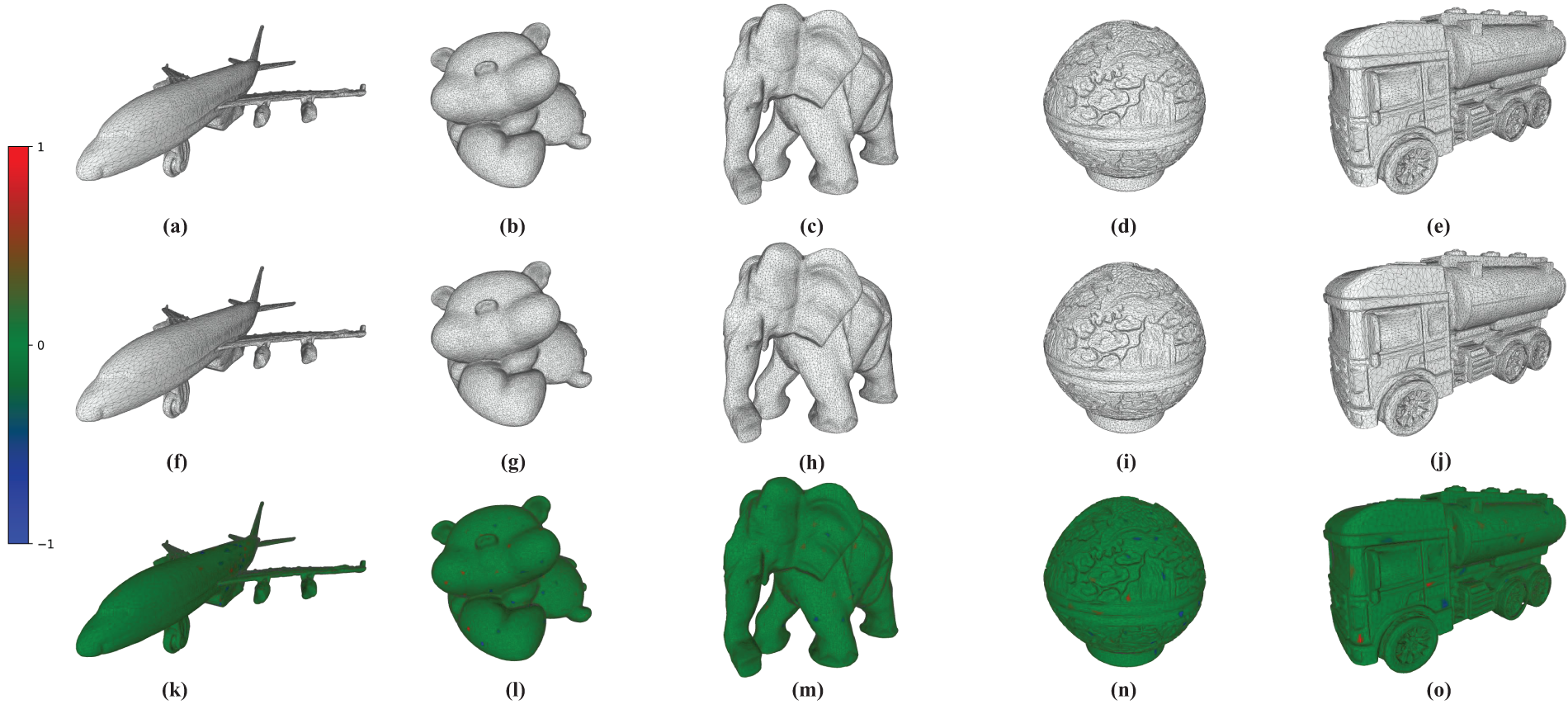
Figure 6: The experimental models in Table 3. (a)–(e) are original mesh models and (f)–(j) are mesh models with embedded watermarks. (k)–(o) show the geometric residuals (original vs. watermarked), color-coded by the signed deviation (red: positive, blue: negative, green: unchanged).
To demonstrate the superiority of the proposed method, we conducted comparative experiments with several existing approaches, evaluating robustness under different watermark capacities and common attacks, including gaussian noise, translation and rotation. During the experiments, the watermarked models were subjected to attacks of varying intensity, and the deterministic PCA-based mesh synchronization algorithm was employed during extraction to restore the model’s orientation, ensuring consistent watermark decoding. It can be observed that our method demonstrates strong robustness against Gaussian noise attacks, achieving over 96% bit accuracy even when the noise intensity reaches
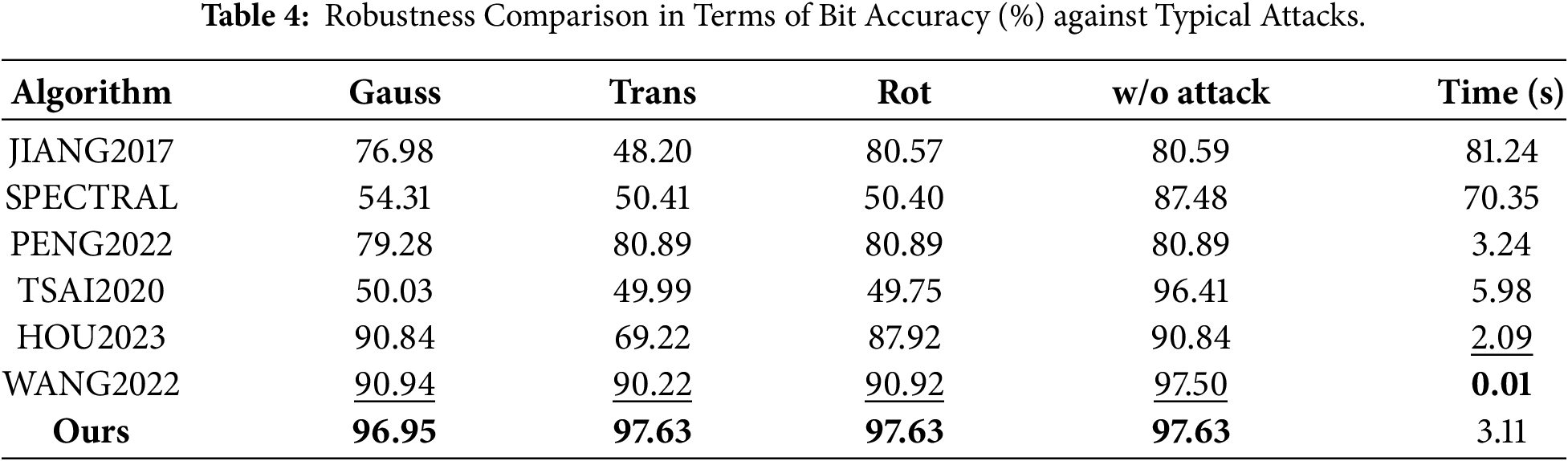
As shown in Table 5, we evaluate the bit accuracy across various embedding capacities to illustrate how extraction performance varies with payload size. It can be observed that the proposed method achieves peak robustness at an embedding capacity of 22 bits. Notably, although the watermark maintains relatively high bit accuracy as the capacity increases, a slight performance degradation is observed when reaching 182 bits. This degradation arises from the use of six embedding directions that coincide with the principal axes. Specifically, these six directions correspond to the positive and negative directions of the three principal axes (
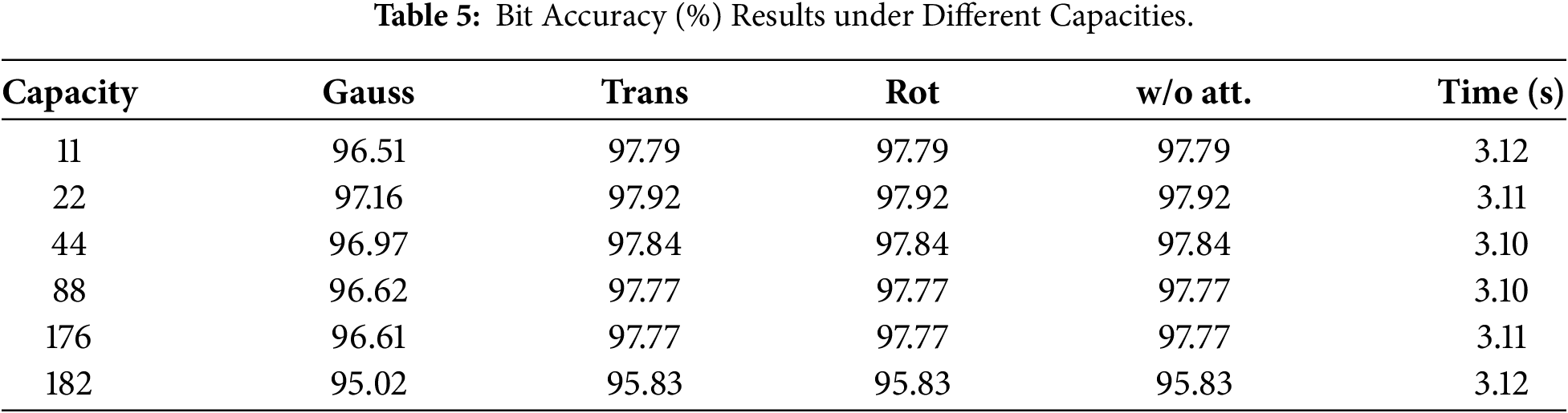
The various embedding capacity is adjusted by varying the number of embedding carriers assigned to each watermark bit. For low embedding capacities, multiple carriers are grouped to encode a single bit (e.g., at an embedding capacity of 8 bits, 22 carriers are jointly used to represent one bit). As the embedding capacity increases, the number of carriers allocated per bit decreases. At the maximum capacity of 176 bits, each embedding carrier independently carries one bit. This design enables capacity variation without altering the underlying carrier selection mechanism.
To further validate the robustness of the proposed method under various complex attack scenarios, as well as to examine the impact of different embedding capacities across these scenarios, we conducted the experiments shown in Fig. 7. As shown in Fig. 7a, our method exhibits strong robustness against Gaussian noise attacks across different embedding capacities. As shown in Fig. 7b–d, our method demonstrates complete resistance to translation, rotation and face reorder attacks. This is attributed to our deterministic PCA-based alignment, which consistently normalizes models to a canonical position, thereby neutralizing the impact of translation and rotation. Moreover, since our method is inherently independent of face ordering, face reordering attacks exert no influence on its performance.
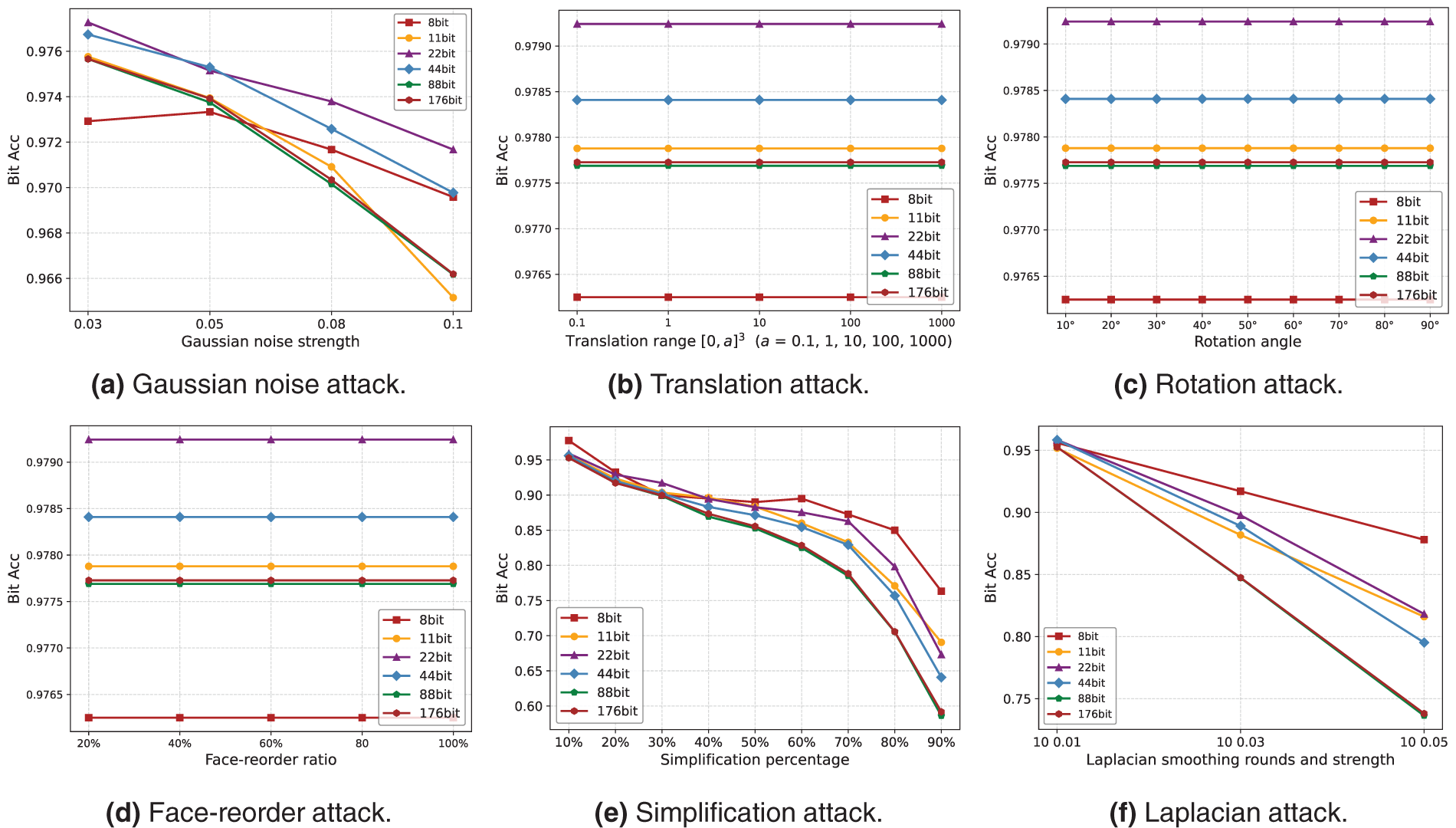
Figure 7: Robustness performance under various attacks and embedding capacities.
Meanwhile, Fig. 7e shows the bit accuracy after meshes with different embedding capacities undergo simplification attacks. It can be observed that our method exhibits strong robustness against simplification attacks. With a 50% reduction in the number of mesh faces, the proposed watermarking scheme consistently achieves a decoding accuracy above 85% across all tested capacities. Even when 80% of the mesh faces are removed, the bit accuracy remains close to 85% under 8-bit embedding capacities. It is worth noting that when the model is simplified by 50%, most of its details are lost, which compromises its visual aesthetics and makes model protection meaningless. We also performed 10 iterations of Laplacian smoothing with intensities of 0.01, 0.03, and 0.05 as illustrated in Fig. 7f. Under Laplacian smoothing attacks, the watermark bit accuracy shows a noticeable decline with increasing embedding capacity. However, the method still achieves an overall accuracy exceeding 73%, demonstrating reasonable robustness.
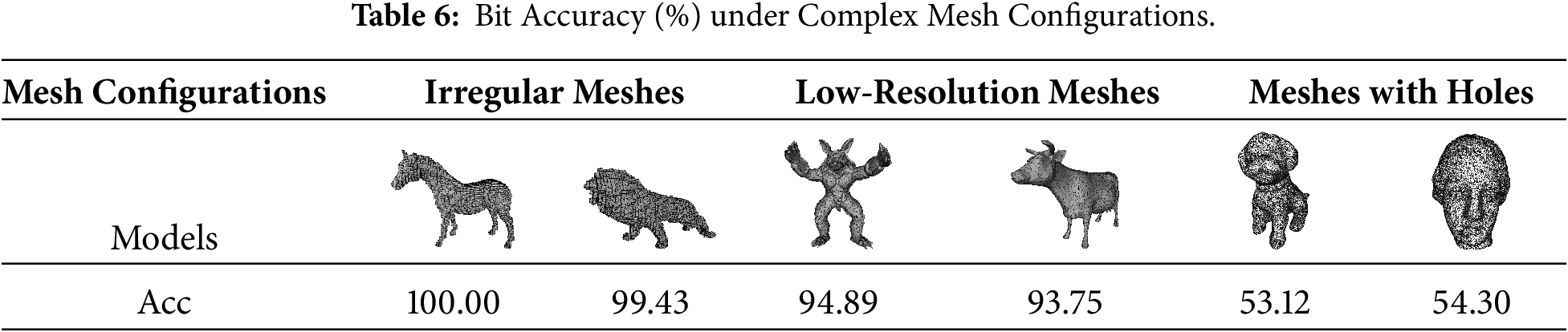
4.4 Stress-Test Evaluation on Challenging Mesh Configurations
To evaluate the robustness of the proposed watermarking pipeline under non-ideal conditions, we further conduct a stress-test evaluation on challenging mesh configurations, including irregular meshes, low-resolution meshes and meshes with holes structures. These models are drawn from our test dataset, but we have processed them to meet the conditions of irregular meshes, low-poly geometries, and meshes with holes. This ensures that our stress-test experiments accurately evaluate the robustness of the proposed method under challenging, non-ideal mesh configurations. The embedding capacity is set to 176 bits. As shown in Table 6, the results demonstrate that our method maintains high robustness for irregular meshes and low-poly geometries, achieving bit accuracy of approximately 99% and 95%, respectively. However, for meshes containing holes, the extraction process is significantly affected, resulting in a much lower bit accuracy of around 53%. These findings indicate that while the proposed scheme is generally robust to geometric irregularities and reduced mesh resolution, additional strategies may be required to handle topological defects such as holes.
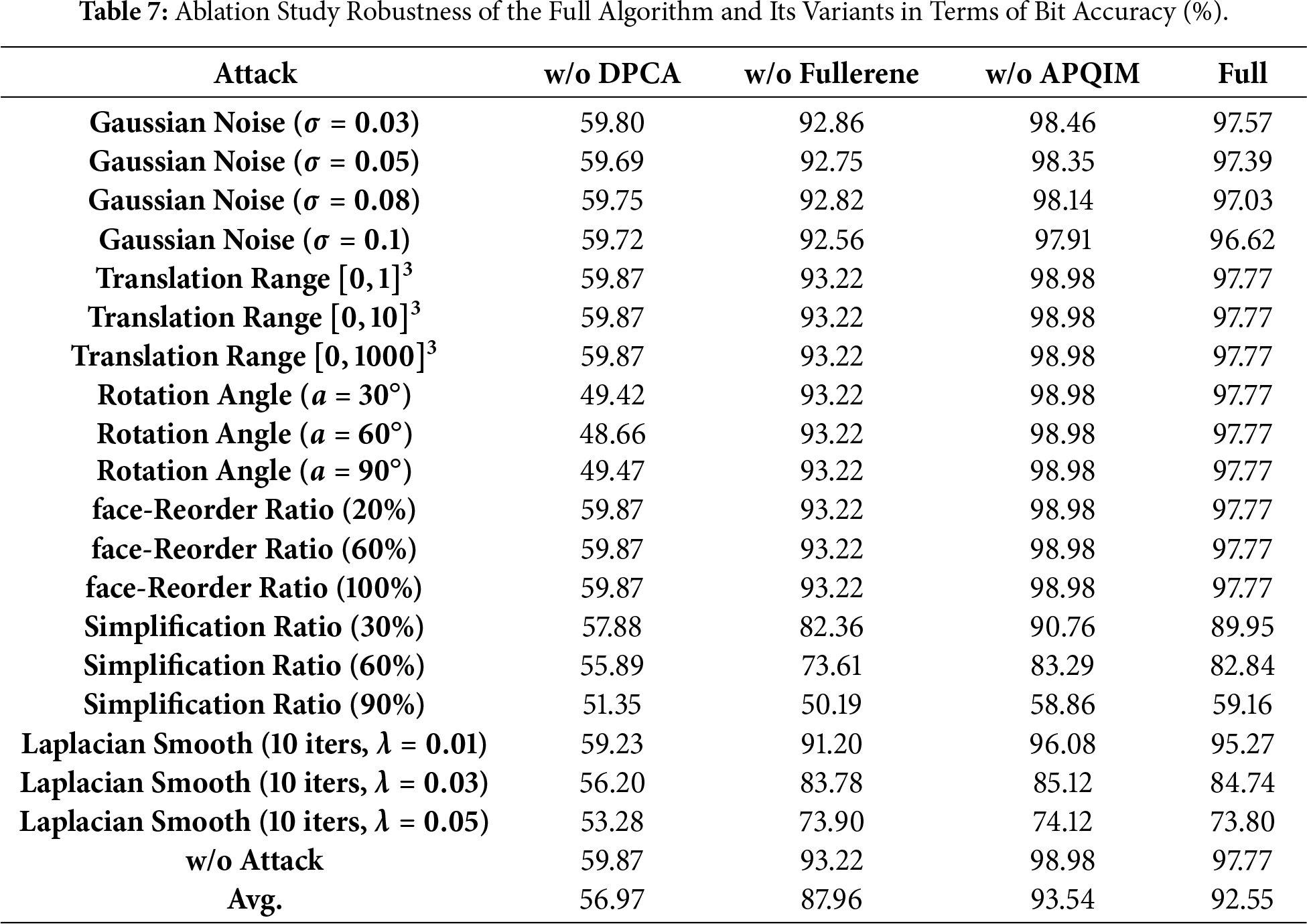
For the ablation study, each of the three modules (Deterministic PCA-based mesh synchronization algorithm, Region selection algorithm based on fullerene molecular model, and Adaptive Parity-Check QIM-based watermark embedding) was respectively replaced by the following conventional implementations: (1) traditional PCA synchronization; (2) spatial-equal partition spherical-coordinate based carrier selection; and (3) fixed-value Parity-Check QIM embedding. We first evaluate the robustness of the complete configuration and the three ablated variants under different embedding capacities, as shown in Fig. 8a. As we can see, when the deterministic PCA method is used instead of the conventional PCA, the watermark bit accuracy increases from approximately 60%–72% to around 97%. Additionally, increasing the embedding capacity raises the likelihood of carrier collisions, further reducing robustness. As discussed in Section 4.3, modifying vertices on facets located near the principal axes can adversely affect the PCA results, leading to a degradation in watermark extraction accuracy. To mitigate this issue, the six fullerene directions that coincide with the principal axes are excluded from the embedding directions. Meanwhile, we aim to evaluate the performance of our method under larger embedding capacities to demonstrate its superiority in high-capacity scenarios. Consequently, a more robust embedding capacity of 176-bits is adopted in our experiments. The robustness under no attack at this 176-bit embedding capacity is presented in Fig. 8b. We evaluated the experimental results under six representative attacks, including Gaussian noise, translation, rotation, face reordering, simplification, and Laplacian smoothing as shown in Table 7. As observed, incorporating the deterministic PCA algorithm significantly enhances watermark robustness and achieves complete resistance to translation and rotation attacks. The fullerene molecular model–based region selection method further improves bit accuracy, as conventional selection strategies tend to cause excessive facet collisions, where the same or adjacent faces are modified multiple times, leading to the failure of certain embedded watermark bits. However, repeatedly modifying the same embedding carrier may cause the previously altered face to be adjusted in the opposite direction, which explains the reduction in the overall geometric modification magnitude. When APQIM is not used, the watermark bit accuracy improves; however, this comes at the cost of reduced visual quality. The adaptive PQIM can flexibly adjust the embedding strength according to each model’s specific characteristics, whereas the fixed-value approach frequently suffers from over- or under-embedding. These results fully demonstrate the effectiveness of the three modules.
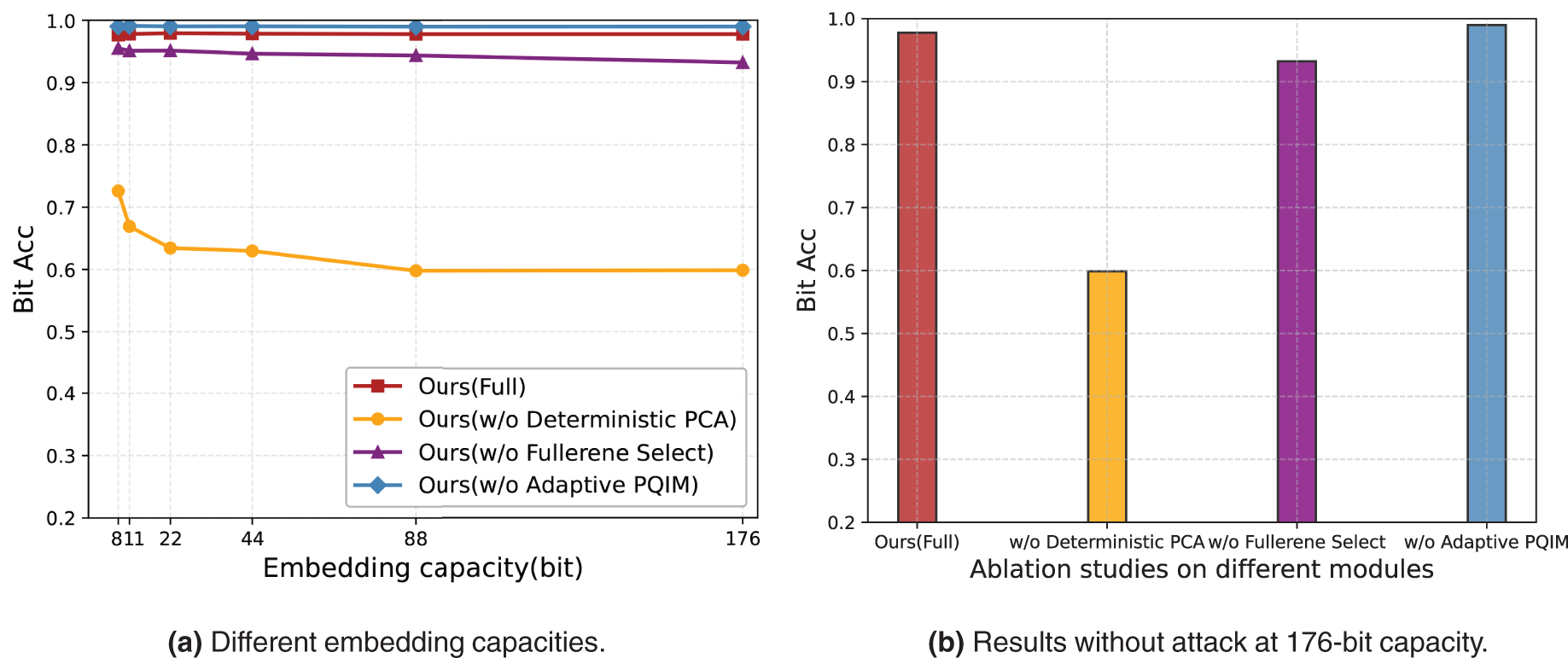
Figure 8: Full and reduced variants under different embedding capacities.
This paper proposes a novel and robust 3D mesh watermarking scheme for copyright protection in realistic 3D content-sharing environments, where typical geometric and signal-processing operations (e.g., gaussian noise, translation, rotation, face reordering, simplification, and Laplacian smoothing) are regarded as the primary adversarial factors. During the watermark embedding stage, a deterministic PCA-based mesh synchronization algorithm is introduced to ensure alignment invariance, followed by a region selection strategy inspired by the fullerene molecular model that modifies only a small subset of mesh patches to preserve watermark imperceptibility and maintain aesthetic quality. An adaptive parity-check quantization index modulation scheme is then employed to further enhance visual quality while maintaining high robustness. In the extraction phase, our method operates blindly, requiring no access to the original model.
Extensive experiments under controlled attack intensities empirically establish the tolerance range of the watermark against these adversarial operations. Specifically, the deterministic PCA-based synchronization ensures invariance to affine transformations, while the fullerene-based region selection and adaptive PQIM embedding provide resilience against local geometric and signal-level distortions. As a result, our method achieves superior imperceptibility for the same watermark capacity, with an average Lld of 0.0128, HD of 0.0064, and SNR up to 76.45, while demonstrating excellent robustness against a wide range of attacks, particularly simplification. These components together constitute a practical robustness guarantee for copyright verification in 3D watermarking applications, striking an effective balance between robustness and geometric fidelity.
While our proposed 3-D mesh watermarking scheme demonstrates strong robustness across a wide range of attacks, including geometric transformations, noise, simplification, and low-poly meshes, certain limitations remain. Specifically, models containing topological defects such as holes may compromise the PCA-based synchronization and carrier selection, leading to degraded watermark extraction accuracy. Similarly, since the current scheme relies on the global centroid, it may be sensitive to partial mesh cropping that alters the centroid location. Although a strict mathematical robustness bound is not derived in this work, the proposed framework provides empirical evidence of its stability under representative adversarial conditions. In future work, we plan to formalize the robustness analysis by modeling watermark embedding and extraction as a probabilistic communication process under bounded geometric perturbations, which will enable the derivation of theoretical robustness limits against both known and adaptive adversaries. Furthermore, to address current limitations arising from the use of a global centroid and the fullerene direction set in carrier selection, we will explore adaptive sampling strategies independent of global centroids or guided by local geometric features, ensuring reliable watermark embedding across more diverse topological structures.
Acknowledgement: We would like to express our gratitude to all those who have helped us during the writing of this paper.
Funding Statement: This work was supported by the National Natural Science Foundation of China (NSFC) under Grant 62272331 and the Key Laboratory of Data Protection and Intelligent Management, Ministry of Education, Sichuan University and the Fundamental Research Funds for the Central Universities under Grant SCU2023D008.
Author Contributions: Study conception and design: Run Jiao, Hongxia Wang; Data collection: Qingyuan Hou, Ziyu Jiang; Analysis and interpretation of results: Run Jiao, Qingyuan Hou, Ziyu Jiang, Hongxia Wang; Draft manuscript preparation: Run Jiao, Hongxia Wang. All authors reviewed and approved the final version of the manuscript.
Availability of Data and Materials: The OmniObject3D dataset presented in this study are available in https://opendatalab.org.cn/OpenXDLab/OmniObject3D-New (accessed on 14 November 2025). The classical models dataset presented in this study are available in https://graphics.stanford.edu/data/3Dscanrep/ (accessed on 14 November 2025) and https://sites.cc.gatech.edu/projects/large_models/ (accessed on 14 November 2025).
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest.
References
1. Daneshmand M, Helmi A, Avots E, Noroozi F, Alisinanoglu F, Arslan HS, et al. 3D scanning: a comprehensive survey. arXiv:1801.08863. 2018. [Google Scholar]
2. Garg H. A comprehensive study of watermarking schemes for 3D polygon mesh objects. Int J Inf Comput Secur. 2022;19(1–2):48–72. doi:10.1504/ijics.2022.126753. [Google Scholar] [CrossRef]
3. Jiang Z, Wang H, Shi Z, Jiao R. Reversible source-aware natural language watermarking via customized lexical substitution. Inf Process Manag. 2025;62(2):103977. doi:10.1016/j.ipm.2024.103977. [Google Scholar] [CrossRef]
4. Wang K, Wu S, Yin X, Lu W, Luo X, Yang R. Robust image watermarking with synchronization using template enhanced-extracted network. IEEE Trans Circuits Syst Video Technol. 2025;35(2):1602–14. doi:10.1109/tcsvt.2024.3474029. [Google Scholar] [CrossRef]
5. Abulkasim H, Jamjoom M, Abbas S. Securing copyright using 3D objects blind watermarking scheme. Comput Mater Contin. 2022;72(3):5969–83. doi:10.32604/cmc.2022.027999. [Google Scholar] [CrossRef]
6. Narendra M, Valarmathi M, Anbarasi LJ. Watermarking techniques for three-dimensional (3D) mesh models: a survey. Multimed Syst. 2022;28(2):623–41. doi:10.1007/s00530-021-00860-z. [Google Scholar] [CrossRef]
7. Elhamzi W, Jallouli M, Bouteraa Y. High efficiency crypto-watermarking system based on clifford-multiwavelet for 3D meshes security. Comput Mater Contin. 2022;73(2):4329–47. doi:10.32604/cmc.2022.030954. [Google Scholar] [CrossRef]
8. Murotani K, Sugihara K. Watermarking 3D polygonal meshes using the singular spectrum analysis. In: Mathematics of Surfaces: 10th IMA International Conference; 2003 Sep 15–17; Leeds, UK. Berlin/Heidelberg, Germany: Springer; 2003. p. 85–98. [Google Scholar]
9. Cayre F, Macq B. Data hiding on 3-D triangle meshes. IEEE Trans Signal Process. 2003;51(4):939–49. doi:10.1109/tsp.2003.809380. [Google Scholar] [CrossRef]
10. Liu Y, Prabhakaran B, Guo X. Spectral watermarking for parameterized surfaces. IEEE Trans Inf Forensics Secur. 2012;7(5):1459–71. doi:10.1109/tifs.2012.2204251. [Google Scholar] [CrossRef]
11. Girdhar A, Kumar V. Comprehensive survey of 3D image steganography techniques. IET Image Process. 2018;12(1):1–10. doi:10.1049/iet-ipr.2017.0162. [Google Scholar] [CrossRef]
12. Gul E, Tam GK. Survey: 3D watermarking techniques. J Vis Commun Image Represent. 2025;112(22):104572. doi:10.1016/j.jvcir.2025.104572. [Google Scholar] [CrossRef]
13. Benedens O. Geometry-based watermarking of 3D models. IEEE Comput Graphics Appl. 1999;19(1):46–55. doi:10.1109/38.736468. [Google Scholar] [CrossRef]
14. Cho JW, Prost R, Jung HY. An oblivious watermarking for 3-D polygonal meshes using distribution of vertex norms. IEEE Trans Signal Process. 2007;55(1):142–55. doi:10.1109/tsp.2006.882111. [Google Scholar] [CrossRef]
15. Delmotte A, Tanaka K, Kubo H, Funatomi T, Mukaigawa Y. Blind watermarking for 3-D printed objects using surface norm distribution. In: Proceedings of the 2018 Joint 7th International Conference on Informatics, Electronics & Vision (ICIEV) and 2018 2nd International Conference on Imaging, Vision & Pattern Recognition (icIVPR); 2018 Jun 25–29; Kitakyushu, Japan. p. 282–8. [Google Scholar]
16. Yang X, Li B, Wang Y, Tu C, Ma X, Wang X. Math3Dmark: a novel and almost perfect 3D mesh watermarking scheme based on mathematics. In: Proceedings of the 2025 IEEE International Conference on Electronics, Energy Systems and Power Engineering (EESPE); 2025 Mar 17–19; Shenyang, China. p. 1078–81. [Google Scholar]
17. Zhu X, Ye G, Luo X, Wei X. Rethinking mesh watermark: towards highly robust and adaptable deep 3D mesh watermarking. Proc AAAI Conf Artif Intell. 2024;38(7):7784–92. doi:10.1609/aaai.v38i7.28613. [Google Scholar] [CrossRef]
18. Zhu X, Ye G, Dong C, Luo X, Zhang S, Wei X. Mesh watermark removal attack and mitigation: a novel perspective of function space. Proc AAAI Conf Artif Intell. 2025;39(10):11004–12. doi:10.1609/aaai.v39i10.33196. [Google Scholar] [CrossRef]
19. Abdi H, Williams LJ. Principal component analysis. Wiley Interdiscip Rev Computat Statistics. 2010;2(4):433–59. doi:10.1002/wics.101. [Google Scholar] [CrossRef]
20. Liu H, Yan J, Zhang D. What is wrong with mesh PCA in coordinate direction normalization. Pattern Recognit. 2006;39(11):2244–7. doi:10.1016/j.patcog.2006.05.019. [Google Scholar] [CrossRef]
21. Dunlap BI, Zope RR. Efficient quantum-chemical geometry optimization and the structure of large icosahedral fullerenes. Chem Phys Lett. 2006;422(4–6):451–4. doi:10.1016/j.cplett.2006.02.100. [Google Scholar] [CrossRef]
22. Wu T, Zhang J, Fu X, Wang Y, Ren J, Pan L, et al. OmniObject3D: large-vocabulary 3D object dataset for realistic perception, reconstruction and generation. In: Proceedings of the 2023 IEEE/CVF Conference on Computer Vision and Pattern Recognition (CVPR); 2023 Jun 17–24; Vancouver, BC, Canada. [Google Scholar]
23. Stanford University. The stanford 3D scanning repository. [cited 2025 Nov 14]. Available from: https://graphics.stanford.edu/data/3Dscanrep/. [Google Scholar]
24. Georgia Institute of Technology. The large geometric models archive. [cited 2025 Nov 14]. Available from: https://sites.cc.gatech.edu/projects/large_models/. [Google Scholar]
25. Jiang R, Zhou H, Zhang W, Yu N. Reversible data hiding in encrypted three-dimensional mesh models. IEEE Trans Multimed. 2017;20(1):55–67. doi:10.1109/tmm.2017.2723244. [Google Scholar] [CrossRef]
26. Peng F, Liao T, Long M. A semi-fragile reversible watermarking for authenticating 3D models in dual domains based on variable direction double modulation. IEEE Trans Circuits Syst Video Technol. 2022;32(12):8394–408. doi:10.1109/tcsvt.2022.3192542. [Google Scholar] [CrossRef]
27. Tsai YY. Separable reversible data hiding for encrypted three-dimensional models based on spatial subdivision and space encoding. IEEE Trans Multimed. 2020;23:2286–96. doi:10.1109/tmm.2020.3009492. [Google Scholar] [CrossRef]
28. Hou G, Ou B, Long M, Peng F. Separable reversible data hiding for encrypted 3D mesh models based on octree subdivision and multi-MSB prediction. IEEE Trans Multimed. 2023;26(6):2395–407. doi:10.1109/tmm.2023.3295578. [Google Scholar] [CrossRef]
29. Al-Khafaji H, Abhayaratne C. Graph spectral domain blind watermarking. In: ICASSP 2019–2019 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP); 2019 May 12–17; Brighton, UK. p. 2492–6. [Google Scholar]
30. Wang F, Zhou H, Fang H, Zhang W, Yu N. Deep 3D mesh watermarking with self-adaptive robustness. Cybersecurity. 2022;5(1):24. doi:10.1186/s42400-022-00125-w. [Google Scholar] [CrossRef]
31. Critchley F. Influence in principal components analysis. Biometrika. 1985;72(3):627–36. doi:10.2307/2336735. [Google Scholar] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF Downloads
Downloads
 Citation Tools
Citation Tools