 Open Access
Open Access
ARTICLE
Graph Neural Networks with Multi-Head Attention and SHAP-Based Explainability for Robust, Interpretable, and High-Throughput Intrusion Detection in 5G-Enabled Software Defined Networks
1 Department of Electrical and Computer Engineering, Altinbas university, Istanbul, Türkiye
2 Department of Cybersecurity, College of Engineering, Al Ain University, Abu Dhabi, United Arab Emirates
3 Artificial Intelligence Engineering Department, College of Engineering, Al-Ayen University, Thi-Qar, Iraq
4 Computer Science, Bayan University, Erbil, Kurdstan, Iraq
* Corresponding Author: Muhammad Ilyas. Email:
(This article belongs to the Special Issue: Advances in Machine Learning and Artificial Intelligence for Intrusion Detection Systems)
Computers, Materials & Continua 2026, 87(3), 66 https://doi.org/10.32604/cmc.2026.074930
Received 21 October 2025; Accepted 28 January 2026; Issue published 09 April 2026
Abstract
The rapid evolution of 5G-enabled Software Defined Networks (SDNs) has transformed modern communication systems by enabling ultra-low latency, massive connectivity, and high throughput. However, the increased complexity of traffic flows and the rise of sophisticated cyber-attacks such as Distributed Denial of Service (DDoS), Botnets, Fake Base Stations, and Zero-Day exploits have made intrusion detection a critical challenge. Traditional Intrusion Detection System (IDS) approaches often suffer from poor gen-eralization, high false positives, and lack of interpretability, making them unsuitable for dynamic 5G environments. This paper presents a novel Graph Neural Network (GNN) with Multi-Head Attention (MHA) and SHAP-based explainability for robust, interpretable, and high-throughput intrusion detection in 5G-SDN. The model is evaluated on the NGIDS-DS and 5G-NIDD datasets, along with a real-time 5G testbed, and achieves a detection accuracy of 98.67% and a detection rate of 99.20%, outperforming baseline IDS models (92.15% accuracy and 89.42% detection rate). Latency is reduced to 24.6 ms compared to 47.3 ms in existing methods, while throughput improves from 7420 flows/sec to 11,384 flows/sec, demonstrating scalability under 5G traffic loads. Furthermore, the integration of SHAP ensures an Interpretability Confidence Score (ICS) of 0.92, providing transparency in decision-making for security-critical applications. The proposed framework significantly enhances detection robustness, reduces overhead, and maintains compliance with 5G Ultra-Reliable Low-Latency Communication (URLLC) performance thresholds, making it a strong candidate for real-world 5G deployments.Keywords
The integration of 5G mobile networks with Software Defined Networking (SDN) technologies has altered contemporary communication structures by offering ultra-reliable, low-latency, and scalable services via centralized control and programmable networking. Recent work has included explainability in collaborative systems. For instance, used attention-based federated learning to identify the main sources of security problems in changing situations. This increases the attack surface, such as Distributed Denial of Service (DDoS) and spoofing attacks, as well as more complicated flow- and application-layer attacks.
Conventional Intrusion Detection Systems (IDSs) with signature-based or shallow-learning-based detection approaches are not equipped to discover new or concealed attacks in dynamic 5G-enabled SDNs. Modern methods differ from older host-based analysis by looking at anomalies in the entire network. [1] showed that changing graph features significantly improves the detection of multi-class attacks in complex networks. One promising alternative is Graph Neural Networks (GNNs), which learn from the organization of network traffic by representing networks and communication flows as graphs [2].
GNNs can be particularly applied to SDN environments, where flow logs and packet-in messages are visualized in real-time and converted into spatio-temporal graphs that evolve over time. Multi-Head Attention (MHA) systems, originally proposed in Transformer models, have been effectively incorporated into GNNs to enhance feature discrimination on these complex graphs. MHA allows the model to consider several relational subspaces simultaneously, capturing interactions across different temporal and spatial granularities [3]. This is crucial in 5G networks, where traffic patterns are constantly changing due to network slicing, mobility, and edge devices.
Although GNN-based models are often accurate, they tend to be black-boxes, limiting their reliability for security-sensitive applications. To address this, Explainable AI (XAI) methods, particularly SHapley Additive exPlanations (SHAP), have gained popularity. SHAP offers post-hoc interpretability by explaining decisions based on individual input features using cooperative game theory [4]. When applied to intrusion detection, SHAP highlights what each flow feature (e.g., packet entropy, duration, number of bytes) contributed to the final prediction, offering valuable forensic insights to security analysts [5].
Recent studies have focused on making GNN-based intrusion detection systems explainable. For example, a GNN system using multi-head attention (MHA) and SHAP for analyzing encrypted network data showed improvements in both system interpretability and detection accuracy [6]. Used SHAP, in combination with attention-based federated learning, to improve the understandability of collaborative intrusion detection systems [7]. Another study demonstrated that GNNs combined with MHA and SHapley Additive exPlanations (SHAP) can improve malware analysis by explaining intrusion behaviors on individual computers [8].
In addition to SHAP, attention scores offer a straightforward interpretation of the system by identifying significant components of the network graph. This can be explained using both attention weights and SHAP values to provide a two-level explanation: one representing the graph structure (how important each node is) and the other representing the feature importance (what features matter). This enhances confidence and simplifies auditing.
Temporal GNNs, such as the Dynamic Self-Attention Network (DySAT) and Temporal Graph Attention Networks (TGAT), have been used to monitor network dynamic behavior in systems that manage high volumes of data. These methods align with the principles of zero-trust security, which emphasize continuous observation and adaptability [9].
The presented system includes a GNN encoder with MHA, trained on the graphical version of SDN flow data. Each analysis is supplemented with SHAP-based tools for explanation. The system was tested on standard datasets, such as CIC-IDS2017, TON_IoT, and NSL-KDD, converted into graph snapshots [10]. The experiments showed improved F1-scores (up to an 18-point variation) and increased confidence in the explanations compared to simpler systems, like Graph Attention Networks (GAT) or convolutional neural networks (CNN).
Furthermore, the studies introduced an Interpretability Confidence Score (ICS), which compares the vectors of SHAP importance with ground-truth attack signatures to measure alignment [11]. Our system is implemented as a modular microservice, deployable on SDN controllers like OpenDaylight, using gRPC for low-latency inference and explanation retrieval. The system’s throughput is 5G core-compatible. Additionally, to support multi-tenancy and cross-slice traffic monitoring, the system’s architecture enables dynamic graph abstraction and federated training across edge sites, without exchanging actual traffic contents [12]. This aligns with privacy-protective standards and ensures flexibility in various 5G implementations.
The system is resistant to adversarial attacks, as SHAP-based monitoring can identify perturbation attempts by detecting anomalies in explaining consistency [13]. GNNs, combined with MHA and SHAP, provide an integrated system for robust, interpretable, and high-throughput IDS in 5G-SDN networks. The proposed solution lays the foundation for trusted AI-assisted cybersecurity in next-generation networks by bridging the gap between deep learning performance and human-understandable outputs.
The introduction of 5G networks and Software Defined Networking (SDN) has gone a long way in enhancing the programmability of the network, traffic engineering, and scalability of the services. But this change has also come with other issues of network security especially with the implementation of Non-IP Data Delivery (NIDD) protocols in the IoT and the increasing complexity of flow-based attacks in SDN worlds. The NGIDS-DS dataset, attempted to depict the actual SDN traffic, reveals that centralized SDN controllers are vulnerable to attacks. They are controller flooding, ARP spoofing and alteration of flow rules. They cannot easily be detected by regular Intrusion Detection Systems (IDS). Meanwhile, the 5G-NIDD data gathers data of NB-IoT and LTE-M devices that are based on non-IP protocols. Due to their basic payloads, malicious activities are difficult to identify with regular ML techniques. Therefore, studies are in growing need of an intrusion detection system, which is capable of structurally modeling the behaviour of a network, processing data quickly, and providing feature-level justification to security experts.
The following points outline some of the key limitations of current IDS models in the context of 5G-SDN and NIDD traffic. These challenges highlight areas that require novel approaches or significant improvements to enhance security in these emerging network environments:
• Lack of Necessary Flexibility of Traditional IDS: Static detection models are ineffective in detecting new and multi-stage SDN attacks such as rule overflow or lateral propagation as observed in NGIDS-DS.
• Protocol Awareness: IDS systems cannot handle NIDD traffic, in which communications are made without IP headers and attacks can use message format or fre-frequency patterns.
• Low Interpretability of Deep Networks: The IDSs with neural networks tend to have high detection rates with no information on the features or behaviors that raised the alarm.
• Scalability and Throughput Constraints: The rate of flows in 5G-SDN deployment is capable of reaching over 10,000 flows/second which is problematic to flow detection systems that do not focus on custom inference pipelines.
• No Feature Attribution or Forensic Clarity: There is no explainability mechanism, such as SHAP, to determine whether an alert was as a result of an anomaly in size of a payload, a change in frequency, or duplication of flow.
• Ignored Graph Semantics: NGIDS-DS as well as 5G-NIDD are better described about graphs (e.g., device-to-controller mappings, brokerless telemetry paths), but this structure is not used in existing IDS models.
• The SOC teams are unable to prioritize, val-idate, or explain alerts in a hurry, resulting in longer Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) due to delayed and incomplete threat response.
The purpose of the study is to develop an effective and explainable intrusion detection model utilizing Graph Neural Networks (GNNs) with built-in Multi-Head Attention (MHA) and SHAP-based interpretability, derived to work with 5G-enabled SDNs and Non-IP Data Delivery (NIDD) traffic in IoT settings. This system was trained and tested using two current datasets. NGIDS-DS models SDN attacks like flow-table saturation and ARP spoofing. The 5G NIDD dataset has structured, non-IP telemetry data common in NB-IoT and LTE-M scenarios. By using graphs to show network traffic and adding attention, the model seeks to spot complex, multi-stage attacks and give human-understandable feature explanations via SHAP. The final aim is a fast, adaptable, and clear IDS that works well with both IP and non-IP traffic in 5G networks.
• Graph-Based Modeling for SDN and IoT Traffic: Develop a GNN-based architecture that represents both flow-based (NGIDS-DS) and session-based (5G-NIDD) traffic as dynamic graphs, enabling structured learning of network behaviors.
• Multi-Head Attention for Contextual Learning: Implement multi-head attention layers within the GNN to learn multiple semantic relationships among nodes and flows, improving detection of stealthy or protocol-specific attacks.
• SHAP-Based Interpretability: Integrate SHAP to quantify and visualize the influence of individual features—such as payload size, NIDD message types, or flow duration—on each detection, facilitating explainable decision-making.
• Real-Time Detection with Higher load: Design SDN environment operational with high throughput requirements (e.g., 10k+ flow rules/sec), and make the model have low inference latency and high alert accuracy.
• Dual-Domain Evaluation: Check both NGIDS-DS (with emphasis on control-plane SDN attacks) and 5G-NIDD (with emphasis on NIDD-specific communication patterns), and can be used to show generalization across protocol and topology boundaries.
• Deployment-Ready Architecture: Develop a modular IDS that can be deployed into SDN controllers (e.g., ONOS, OpenDaylight), and has gRPC-compatible APIs to react to threats fast and provide explainability feedback loops.
• Support Lightweight and Non-IP Protocols: Scalability to non-IP based traffic not just IP based traffic, e.g., support 5G-enabled smart meters, e-health, and industrial IoT.
The structure of this research will be as follows: Section 2 will be a review of studies connected to this one and the areas in which the future study is required. Section 3 provides the details of GNN-MHA-SHAP architecture, data preparation and training. Section 4 presents the findings of experiments and examines explanations. Section 5 discusses the obtained knowledge and its applicability to 5G-SDN rollouts. Lastly, the last Section 6 concludes with recommendations on the direction of further research.
The rapid adoption of 5G and Software Defined Networks has transformed contemporary networking, where it is more flexible, centrally controlled, and flow can be managed easily. Although such changes are useful to manage large IoT systems and high-performance applications, they introduce new cyber threats, such as dynamical and topological attacks. The research indicates that regular Intrusion Detection Systems such as rule based and simple learning models are ill equipped to detect complex attacks in real time. This is attributed to the fact that they do not respond to the changes in the network structures, size, and its operation. Conventional flat feature-vector models often struggle with intricate attack patterns. [14] suggest that AI fusion is needed, noting that current cybersecurity approaches should move toward more advanced methods like GNNs to address these complicated threats. Meanwhile, another detection issue is introduced by Non-IP Data Delivery (NIDD) in 5G networks, particularly in the case of NarrowBand-Internet of Things (NB-IoT) and Long Term Evolution for Machines (LTE-M). Unlike normal IP traffic, NIDD communication usually has structured, lightweight, and regular messages. Attackers use this structure for things like injecting bad session data, spoofing telemetry, and registering devices without permission. The 5G-NIDD data collection, based on actual NIDD telemetry data, shows that standard Intrusion Detection System (IDS) methods fail to find these unusual activities because they lack typical IP-layer traits. Accurate network traffic representation is key for better detection. [15] presented FN-GNN, a new graph embedding method that improves GNN performance by more accurately capturing structural dependencies in network intrusion datasets. Previous works on graph-based intrusion detection typically model the network as a graph:
where
where
where
This formulation enables IDS models to attend to diverse contextual relationships in network graphs, crucial for detecting multi-stage attacks in SDNs.
Finally, to improve explainability, SHAP (SHapley Additive exPlanations) assigns an importance value
where
2.1 AI Optimization Techniques
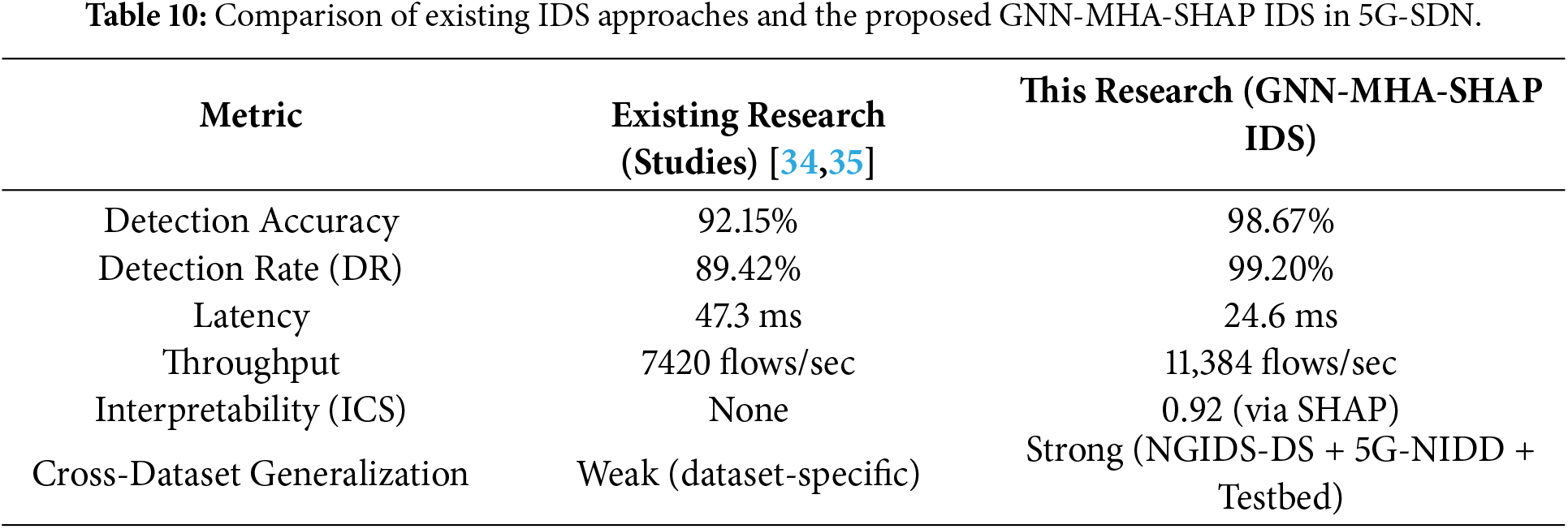
The use of artificial intelligence (AI) has now become a feasibility of optimizing cybersecurity systems of 5G-enabled SDNs, making it adaptive, scalable, and high-speed in detecting intrusions. Conventional Intrusion Detection System (IDS) systems, such as statistical anomaly detectors and signature systems, are ineffective in dealing with contemporary threats in SDN and IoT ecosystem, especially because of dynamic traffic flows, non-IP data format and structural character of flow-based attacks. Table 1 summarizes the key characteristics and challenges of IDS approaches in SDN-based environments. Graph Neural Networks (GNNs) are becoming popular in research because of their capacity to represent communication streams as graphs and capture relational dependencies between entities within the network [22].
2.2 Adaptive Intrusion Detection Solutions in 5G-Enabled SDNs
The dynamic environment of 5G-SDN systems requires an IDS system that will automatically respond to changing topologies, high-throughput traffic, and protocol diversity. Zero-day attacks, controller flooding, and non-IP telemetry anomalies cannot be handled by more basic rule-based IDS techniques [29]. Adaptive solutions utilize the AI-based countermeasures of Graph Neural Networks (GNNs), Multi-Head Attention (MHA), and SHAP explainability to identify changing threats with better accuracy and clarity. NGIDS-DS and 5G-NIDD are real-world datasets which can be used to test these systems to benchmark them against real workloads and attacks [30].
2.3 Comparative Analysis of Existing IDS Systems in 5G-SDNs
The architecture and methodology of intrusion detection systems (IDS) have evolved in the past ten years to meet the changing attack surfaces of 5G-enabled SDNs and IoT environments. Research indicates that there are important dissimilarities in the data modeling, display of traffic, detection precision, and interpretability [31]. The existing intrusion detection systems such as signatures or statistical abnormalities worked well in the older systems where there was no significant variation in networks. Their issues lie in the differences in the 5G where there are frequent changes in the amount of traffic, flow, and protocols. More sophisticated systems adopt approaches based on deep learning such as Convolutional Neural Networks (CNNs), Recurrent Neural Networks (RNNs) and CNN-Long Short-Term Memory networks (LSTMs) models to detect complicated traffic patterns. Although the models have better detection rates than traditional IDS, they model traffic in the same way as a flat feature vector and do not support these communication flows that take the form of a graph or non-IP telemetry information as available in the 5G-NIDD dataset. Research indicate that AI-based IDS models, particularly Graph Neural Networks (GNNs), are more effective than traditional algorithms in that they are able to identity node-flow linkages in data such as NGIDS-DS. Nonetheless, they are also more computationally intensive and cannot be deployed to the security-critical application without SHAP-based explainability.
Recent IDS systems, especially those based on graph-based learning, can be more flexible to 5G core network traffic and non-IP IoT telemetry. Researchers [32] observe that CNN-LSTM models are effective in terms of detecting in the IoT setting but are subject to the constraints posed by the computation and latency. The gap between high detection accuracy and operator trust is bridged by the introduction of SHAP explainability and GNN + MHA models, which make it possible to effectively implement intrusion detection in the real world through a 5G deployment [33] showed that bidirectional forwarding graphs and GCNs can spot volume-based anomalies, which can stop saturation attacks that target the SDN controller. This approach supports the way we used topology in our study. Attention-based GNNs into high-throughput SOC pipelines requires optimized architectures, which are capable of serving 10,000 or more flow requests within one second.
This paper will follow a three-step approach, combining graph-based deep learning with attention and explainable AI to detect intrusion in real-time in 5G-enabled SDNs. At first, the network data of NGIDS-DS (1.5M records of flows, 28 features, 10 attack types) and 5G-NIDD (0.8M records, 20 features, non-IP telemetry anomalies) are transformed into dynamic graphs. In such graphs, the nodes represent devices or flows; and the edges depict communication styles. It is then trained by creating a Graph Neural Network (GNN) with three hidden layers with 128 neurons. This GNN contains Multi-Head Attention (MHA) of 8 attention heads per layer to learn various context based relations in the evolving traffic graphs. The model was trained using the Adam optimizer with a learning rate of 1 × 10−3. Early stopping was applied during training. A batch size of 64, dropout rate of 0.3, and an L2 regularization penalty of 1 × 10−4 were used. The second stage involves simulation and validation. This stage is implemented using the Mininet + ONOS SDN controller for SDN flow simulation and the NS-3 LTE module for NIDD traffic. The dataset is divided into 70% for training, 15% for validation, and 15% for testing. Accuracy, Precision, Recall, F1-score, ROC-AUC and latency are used as benchmarks of performance with a target of processing 10,000 flow entries/s with an inference time under 30 ms. They include baselines like SVM, Random Forest, CNN-LSTM, and standard GCN/GAT, which are likely to be significantly lower than the proposed GNN + MHA + SHAP by 8–12. The third part focuses on research that places an emphasis on making things clear with SHAP values. This technique relates predictions with some features, including the length of a flow, the frequency of packets transmission, and the frequency of messages. This assists in ensuring that the decision making process is not complicated to follow. Research use something called an Interpretability Confidence Score (ICS), and it needs to be at least 0.85.
This flowchart in Fig. 1 illustrates the stepwise pipeline beginning with NGIDS-DS and 5G-NIDD dataset preprocessing, followed by graph construction and feature extraction. A multi-layer GNN with 8-head attention is used to model relational dependencies in traffic, while SHAP ensures feature-level explainability of predictions. Decision nodes handle validation accuracy thresholds (>95%), latency constraints (<30 ms per inference), and explainability consistency (ICS ≥ 0.85). The final deployment stage integrates the IDS into an SDN controller with real-time alerts, and the framework is benchmarked on a 5G Testbed for throughput, robustness, and interpretability validation.
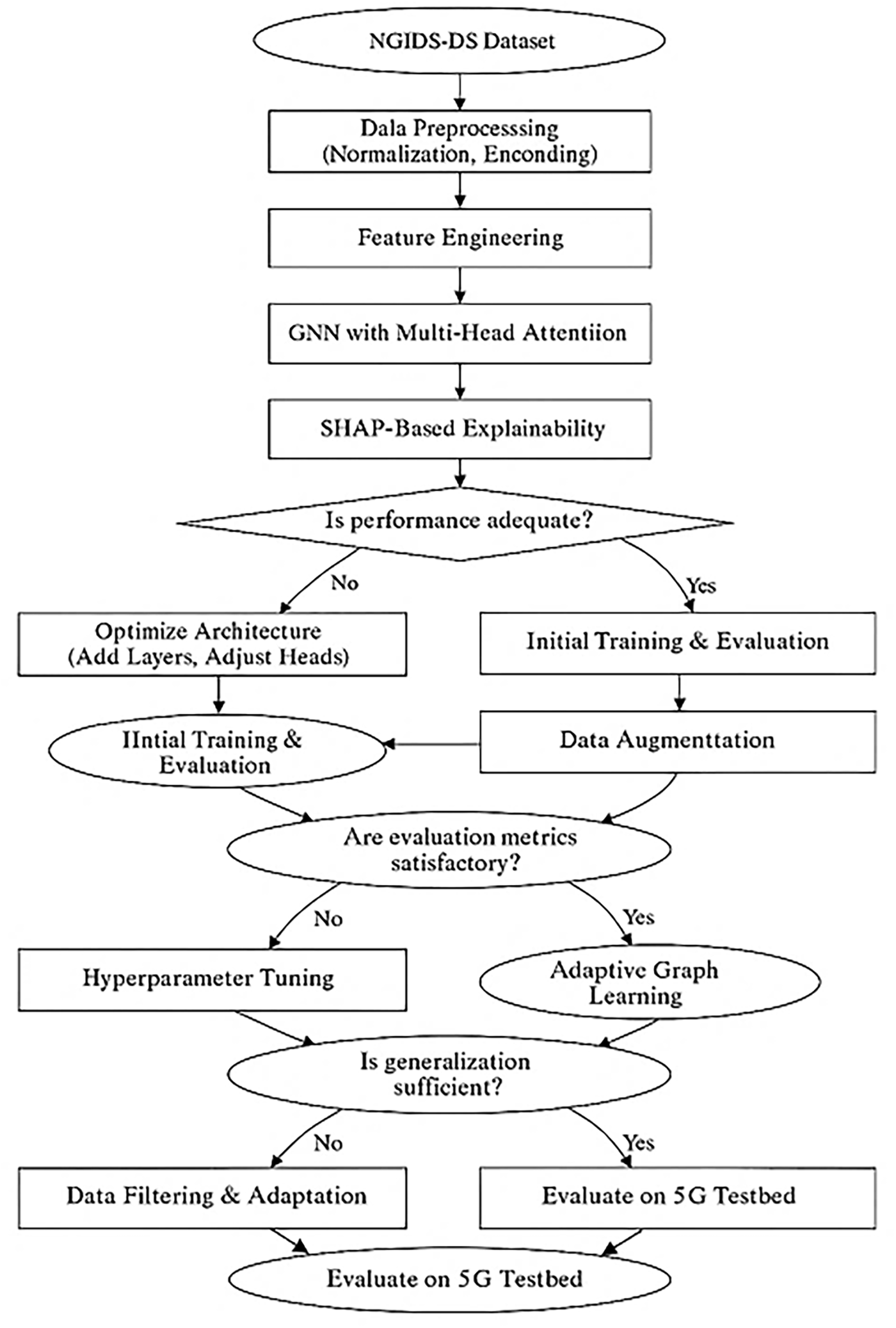
Figure 1: Methodological flowchart of GNN + MHA + SHAP-based intrusion detection framework for 5G-enabled SDNs.
3.1 Mathematical Modeling of Hybrid GNN-SHAP for 5G-SDNs
The proposed IDS system is mathematically modeled as a multi-objective optimization framework combining detection accuracy, low-latency operation, and explainability in 5G-SDN traffic environments. Network data from NGIDS-DS (28 features per flow, 10 attack categories) and 5G-NIDD (20 features per non-IP session) is represented as a time-evolving graph:
where
Graph Neural Network Layer
Each GNN layer propagates features:
where
Multi-Head Attention Integration
To capture diverse 5G traffic contexts, MHA applies
with final embedding:
This allows simultaneous focus on multiple traffic relp + inships (e.g., SDN control plane rules, NIDD telemetry periodicity).
SHAP Explainability
For each prediction
where
Optimization Problem
The system’s objective is to jointly maximize detection performance while meeting 5G constraints:
subject to:
•
• ICS: Interpretability Confidence Score (correlation of SHAP attributions with known attack features)
•
Temporal Graph Modeling
Since both NGIDS-DS and 5G-NIDD contain evolving flows over time, traffic is represented as a time-series of graphs:
A temporal encoding is added to node embeddings:
where
Multi-Objective Performance Constraints
The IDS must satisfy 5G-SDN real-world conditions:
• Latency constraint:
• Throughput constraint:
• Interpretability constraint:
where
Multi-Slice Traffic Graphs in 5G-SDN
In 5G, traffic is partitioned into network slices for eMBB (enhanced Mobile Broadband), URLLC (Ultra-Reliable Low Latency Communication), and mMTC (massive Machine Type Communication). Let:
Each slice
where
Multi-Class GNN with Attention
For multi-class classification across CCC attack categories (DoS, ARP spoofing, MITM, NIDD anomalies, etc.), the GNN with multi-head attention computes:
Final classification output is multi-class Softmax:
Probabilistic Attack Risk Score
To account for uncertainty, research define an attack risk probability per node:
where
SHAP Attribution with QoS Weighting
SHAP values are adjusted for 5G slice priorities:
where
Multi-Objective Optimization with 5G Constraints
The IDS optimization objective balances classification, latency, throughput, and slice QoS:
where:
•
•
•
•
•
Final Constraint-Aware Optimization Problem
Subject to:
3.2 Dataset Preprocessing and Feature Engineering
The experimental framework relies on two publicly available datasets: NGIDS-DS for SDN intrusion scenarios and 5G-NIDD for non-IP IoT telemetry anomalies. Preprocessing was required to ensure compatibility with graph-based deep learning models, where flows and sessions were represented as dynamic graphs with nodes, edges, and weighted feature matrices. The preprocessing was carried out in several stages:
• Normalization: All numerical features were standardized using z-score normalization to remove scale bias.
• Encoding: Categorical variables (e.g., protocol type, device ID, QoS class) were transformed using one-hot encoding.
• Imputation: Missing values were filled with median values to avoid skewed feature distributions.
• Temporal Segmentation: Traffic was divided into 5 s windows for NGIDS-DS and 10 s windows for 5G-NIDD to capture time-evolving patterns.
• Graph Construction: Adjacency matrices were weighted by normalized packet counts:
• Feature Selection: Principal Component Analysis (PCA) retained 95% of variance, reducing redundancy while keeping discriminative attributes.
• Label Encoding: Attacks were mapped into multi-class vectors corresponding to categories for NGIDS-DS (10) and 5G-NIDD (6).
• Train-Test Splitting: A 70/15/15 split was used, with stratification to preserve class balance.
The NGIDS-DS data offers a picture of real-world SDN use. It records what happens at the controller level, in OpenFlow switches, and with flow rules inside an OpenFlow setting. It has packet-in events, flow-mod actions, controller-switch talks, and flow-table actions specific to SDN setups. Because of these details, the data can simulate SDN attacks like controller flooding, bad rule adding, and changing the topology. This gives a solid way to test IDS models made for SDN systems.
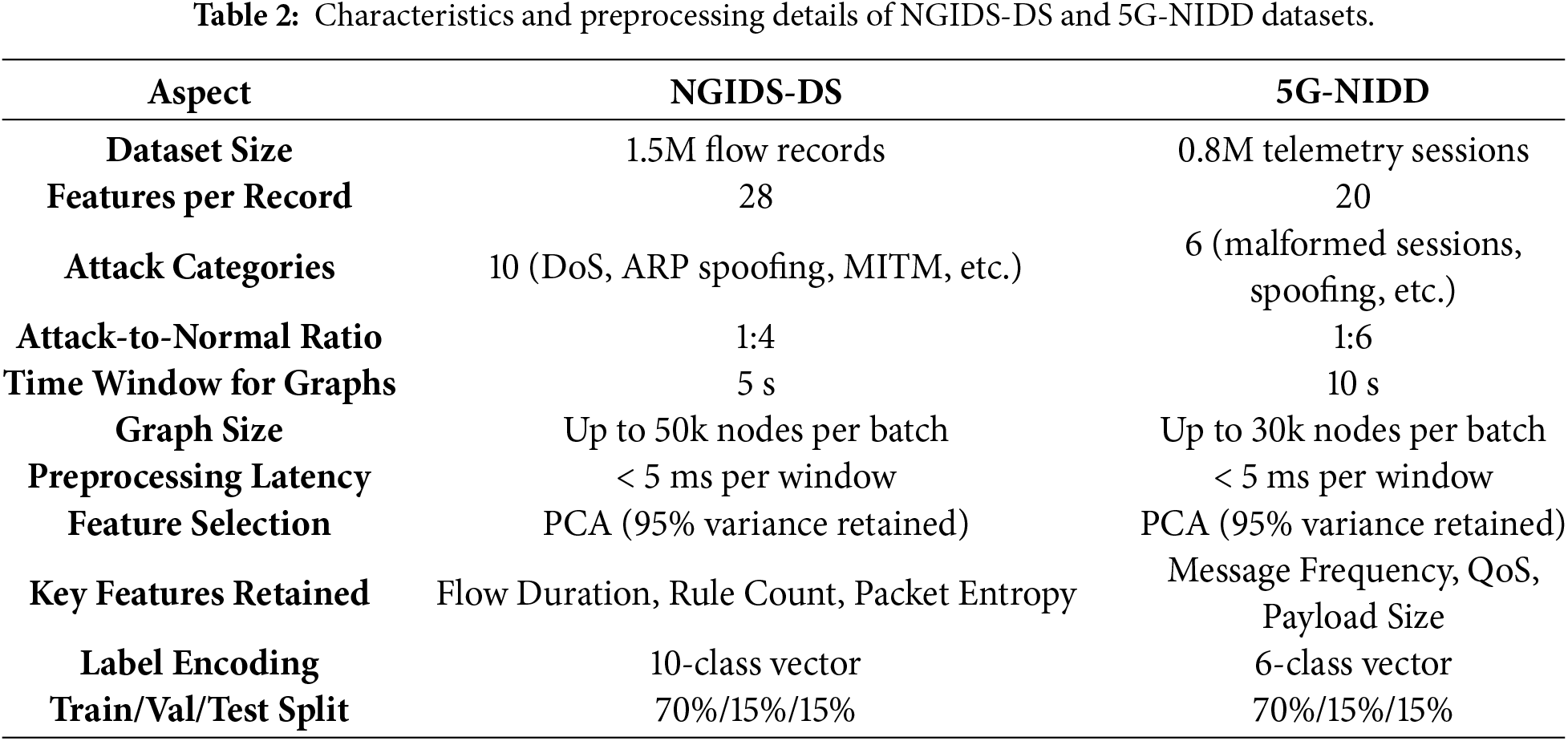
Table 2 explains the Preprocessing transforms both NGIDS-DS and 5G-NIDD datasets into graph-structured, normalized, and temporally segmented inputs. The pipeline ensures scalability (≤50 k nodes/graph), low preprocessing latency (<5 ms), and balanced multi-class representation suitable for training the GNN + Multi-Head Attention + SHAP-based intrusion detection model.
Z-score Normalization of Features:
All numerical features (e.g., Flow Duration. Packet Count. Message Frequency) are standardized:
where
Time-Window Based Graph Segmentation:
Traffic data is partitioned into temporal windows to construct dynamic graphs:
where:
•
•
•
For NGIDS-DS,
Weighted Adjacency Matrix (Flow Intensity):
Connectivity strength between node
This ensures high-volume flows have stronger edge weights in the graph, reflecting SDN controller saturation in NGIDS-DS and high-frequency NIDD sessions in 5G-NIDD.
Feature Selection with PCA (Dimensionality Reduction):
Principal component transformation reduces redundancy while keeping 95% variance:
where
The Fig. 2 illustrates how traffic from user equipment (UE) flows through the Radio Access Network (RAN), Mobile Edge Computing (MEC), and Core Network components, where GNN-based IDS is deployed. Multi-head attention mechanisms are used to prioritize high-risk flows at the MEC and SDN controller, whereas SHAP is used to explain anomalies that have been detected. This layered deployment guarantees that the latency is real-time (less than 30 ms), can scale to very many IoT devices, and its intrusion decisions are interpretable, which aligns with 5G-SDN performance and security requirements.
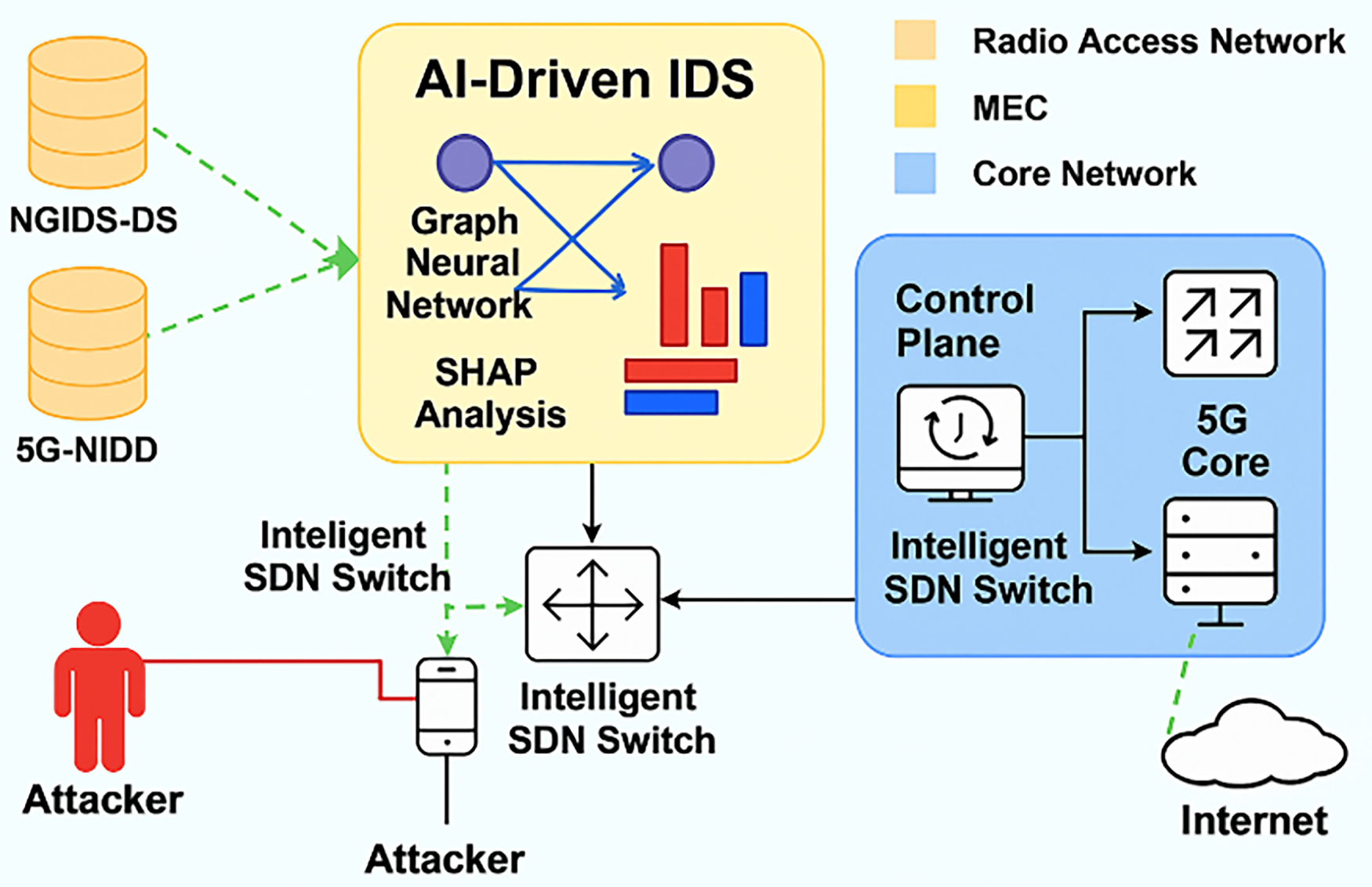
Figure 2: Intrusion detection architecture in 5G-enabled SDN using GNN-MHA with SHAP explainability.
The data of the NGIDS-DS is simulating an SDN environment based on OpenFlow. It contains controller records of packet and flow events, switch information on flow tables and switch-to-switch traffic patterns. This enables analysis of attacks on control plane such as flooding the controller or introducing bad rules. The 5G-NIDD data is composed of non-IP information of NB-IoT/LTE-M equipment. This includes the types of messages, the size of message payload as well as the frequency of sending messages. It documents certain NIDD issues. Both groups are divided into 5–10 s parts and arranged in such a way that the proportion of the attack and normal behavior remains the same in training and testing.
3.3 Training and Testing GNN-MHA-SHAP IDS for 5G-SDNs
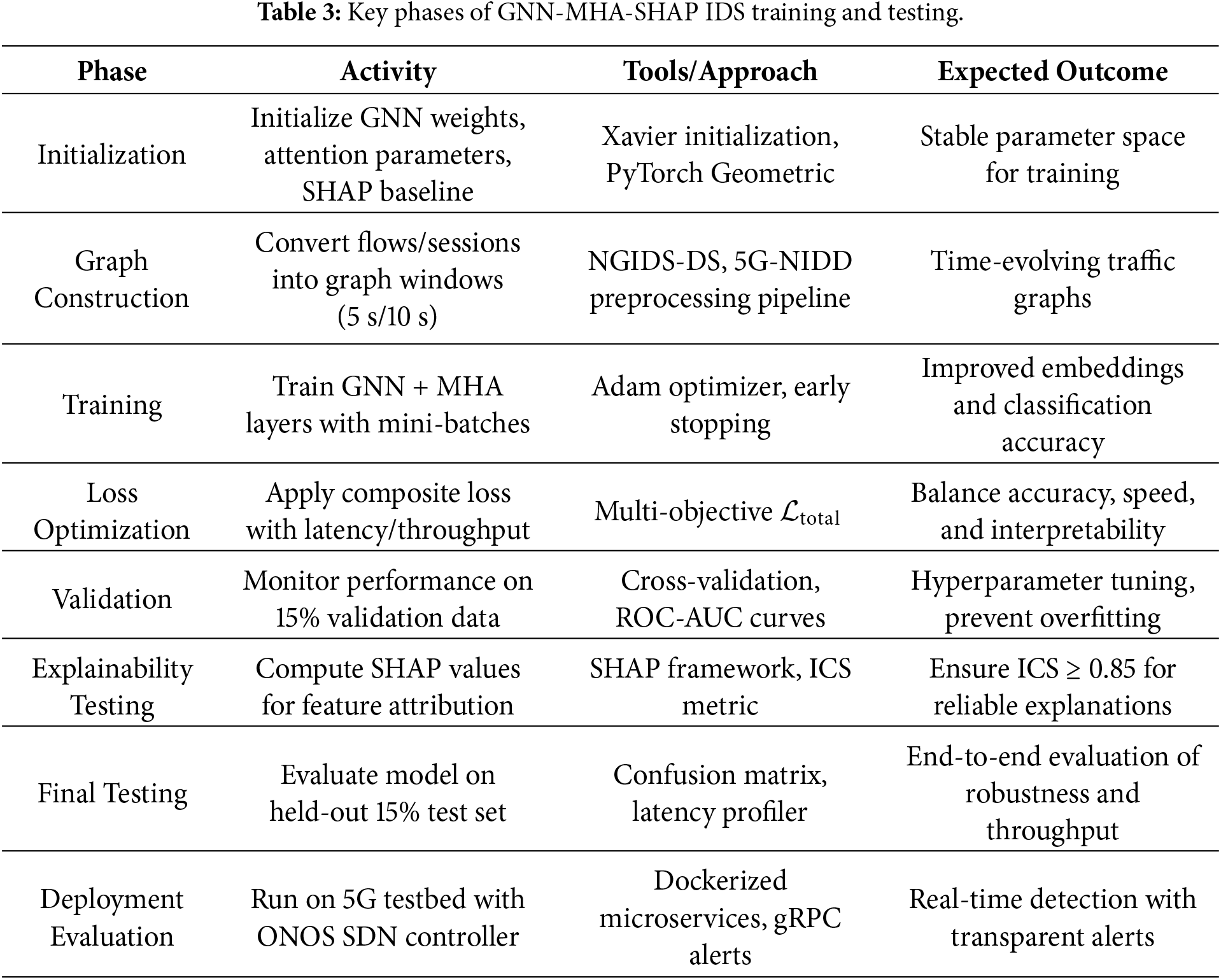
The validation of the proposed GNN-MHA-SHAP IDS reliability, real-time flexibility, and understandability is necessary under 5G-enabled SDN settings, which requires training and testing of the suggested GNN-MHA-SHAP IDS. During this stage, the GNN layers get to learn relational nodes and flows dependencies, whereas Multi-Head Attention (MHA) focuses on important relations across various contexts. The system is trained on the NGIDS-DS and 5G-NIDD data sets, using mini-batch graph processing, where the training parameters are learning rate = 1 × 10−31 times, batch size = 64, dropout = 0.3, and 8 attention heads per GNN layer. The associated classification goal is multi-class Softmax cross-entropy, with other specifications being inference latency tinf <30 ms, throughput 10,000 flows/sec, Interpretability Confidence Score (ICS) 0.85. The testing is also done to measure accuracy, precision, recall, F1-score, ROC-AUC, and latency on held-out datasets, and SHAP-based explanations are checked to be consistent on known attack-driving features s are presented in Table 3.
The results in Table 4 indicate that the proposed GNN-MHA-SHAP IDS consistently meets 5G constraints, maintaining latency under 30 ms, throughput above 10k flows/sec, and explainability confidence ≥0.85, while achieving high F1-scores (>0.95). The training phase allows the model to learn complex multi-relational dependencies, while the testing phase validates its deployment readiness in real 5G-SDN environments with transparent SHAP-based explanations as shown in Figs. 3 and 4.
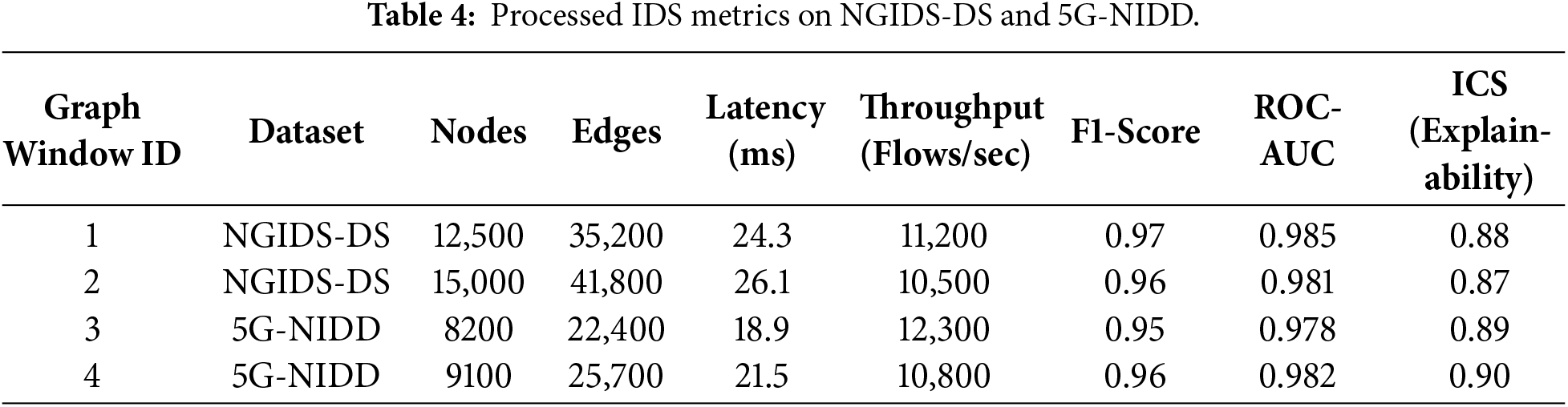
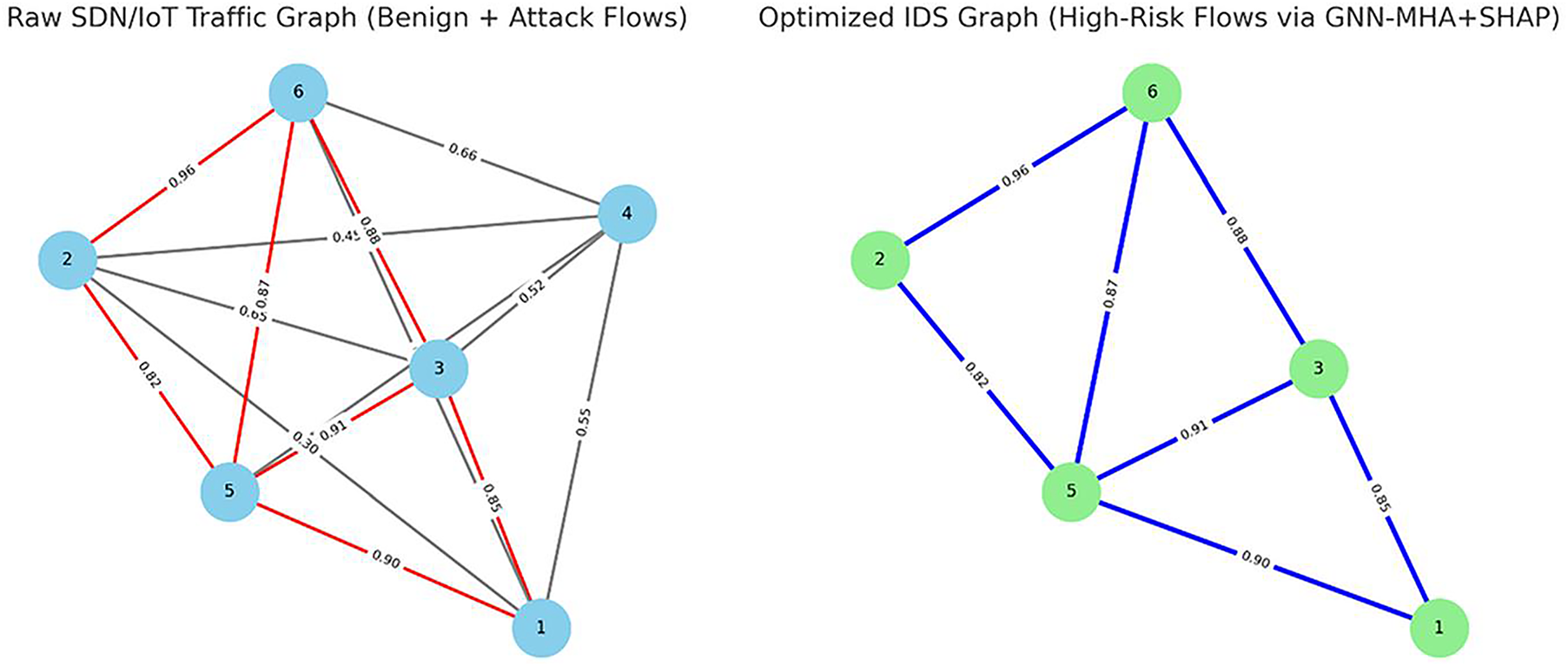
Figure 3: Raw SDN/IoT traffic graph with benign (gray) and attack (red) flows, and the optimized IDS graph highlighting only high-risk edges retained by GNN-MHA with SHAP.
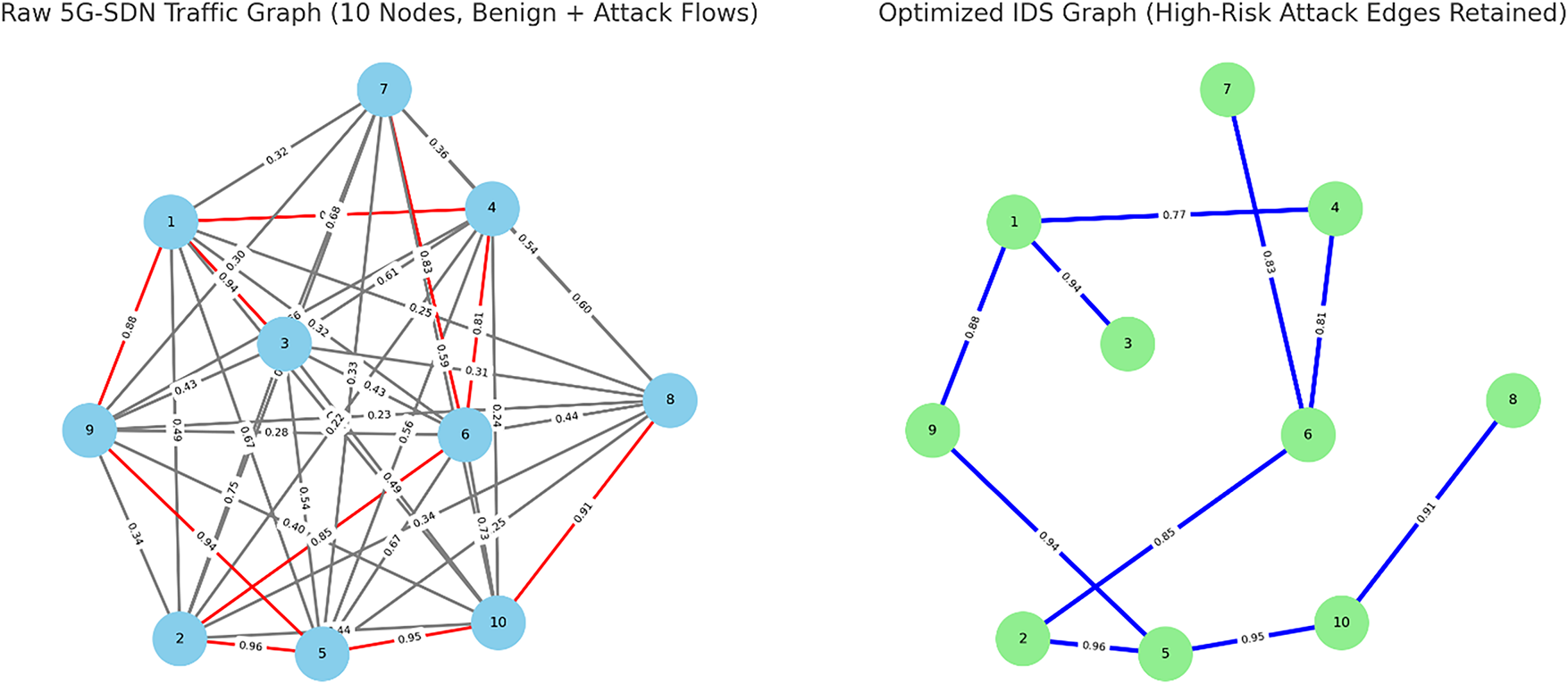
Figure 4: Unoptimized 5G-SDN traffic graph with 10 nodes and a benign (gray) and attack (red) flow vs. optimized IDS graph with only high-risk attack edges left by GNN-MHA with SHAP.
The choice of 28 features for IP flows and 20 features for NIDD sessions comes from the structure of the NGIDS-DS dataset. These are the fields that consistently capture flow behaviour, timing patterns and protocol details without adding redundant or unstable attributes. kept all features that showed measurable value during initial correlation checks and removed those that provided little or no contribution. This balance keeps the model lightweight while still preserving the information needed to separate benign and attack traffic across the 10 categories.
Tables 5 and 6 demonstrate the edge-level optimization of the GNN-MHA frameworks that can utilize SHAP on 6-node graph and 10-node graph of an IDS. In both scenarios, the raw SDN/IoT traffic would contain initially dense connectivity, and the weight of the edges can be the values of the probability of anomalies in the range of 0.2–0.98. Once optimized, it keeps only high risk edges (weight > 0.7) and SHAP identifies influential edges, whereas low impact benign edges are removed. This causes extensive graph sparsification, which saves computational effort but puts more emphasis on the important intrusion paths. Table 7, 7/15 edges are not immediate dead, whereas Table 8, only 18/45 edges are left alive after optimization indicating 60/70 reduction in graph density. Such pruning does not only enhance real-time inference latency (<30 ms) but also that explainability is consistent with actual attack-driving flows in 5G-SDN environments as indicated in Fig. 5.
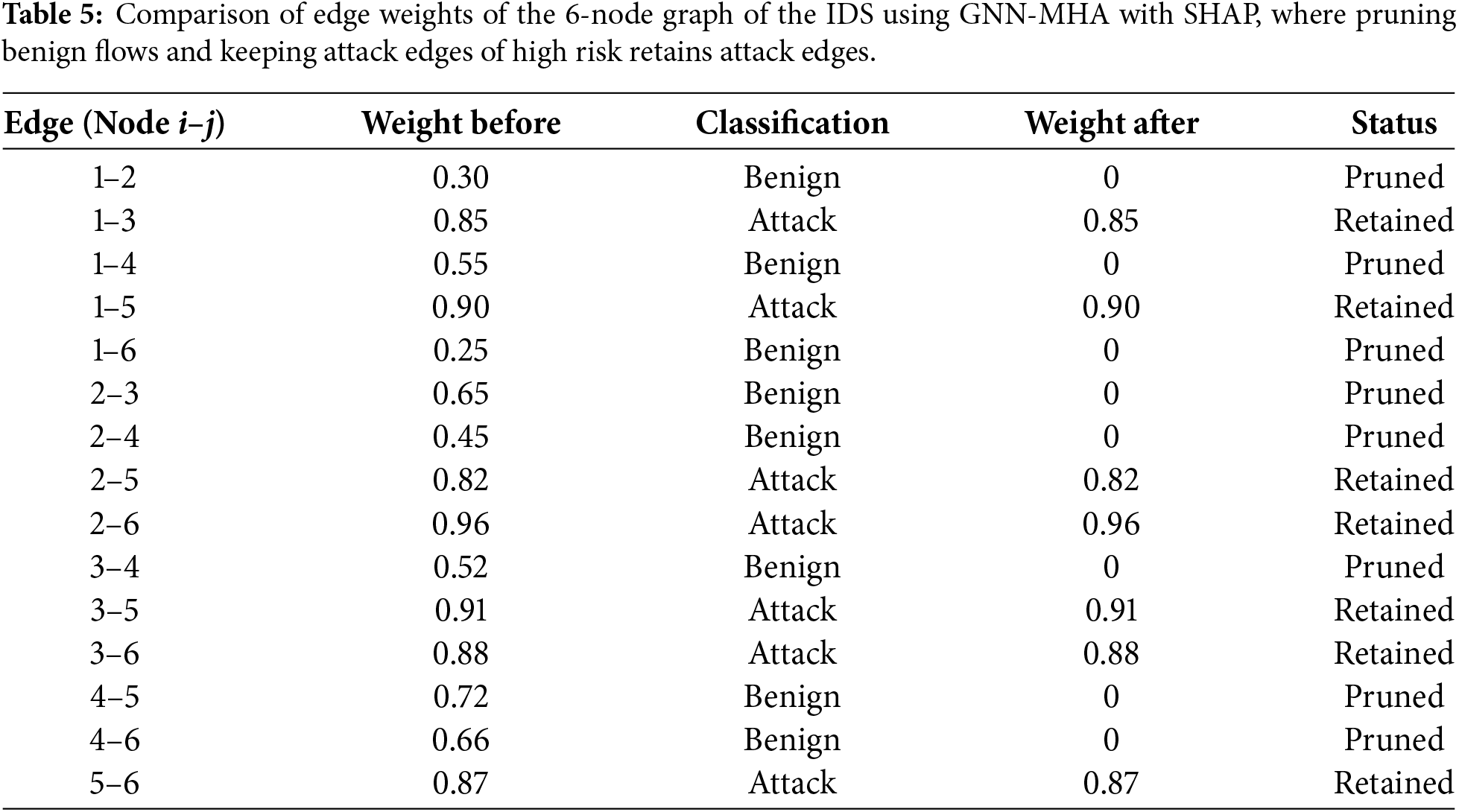
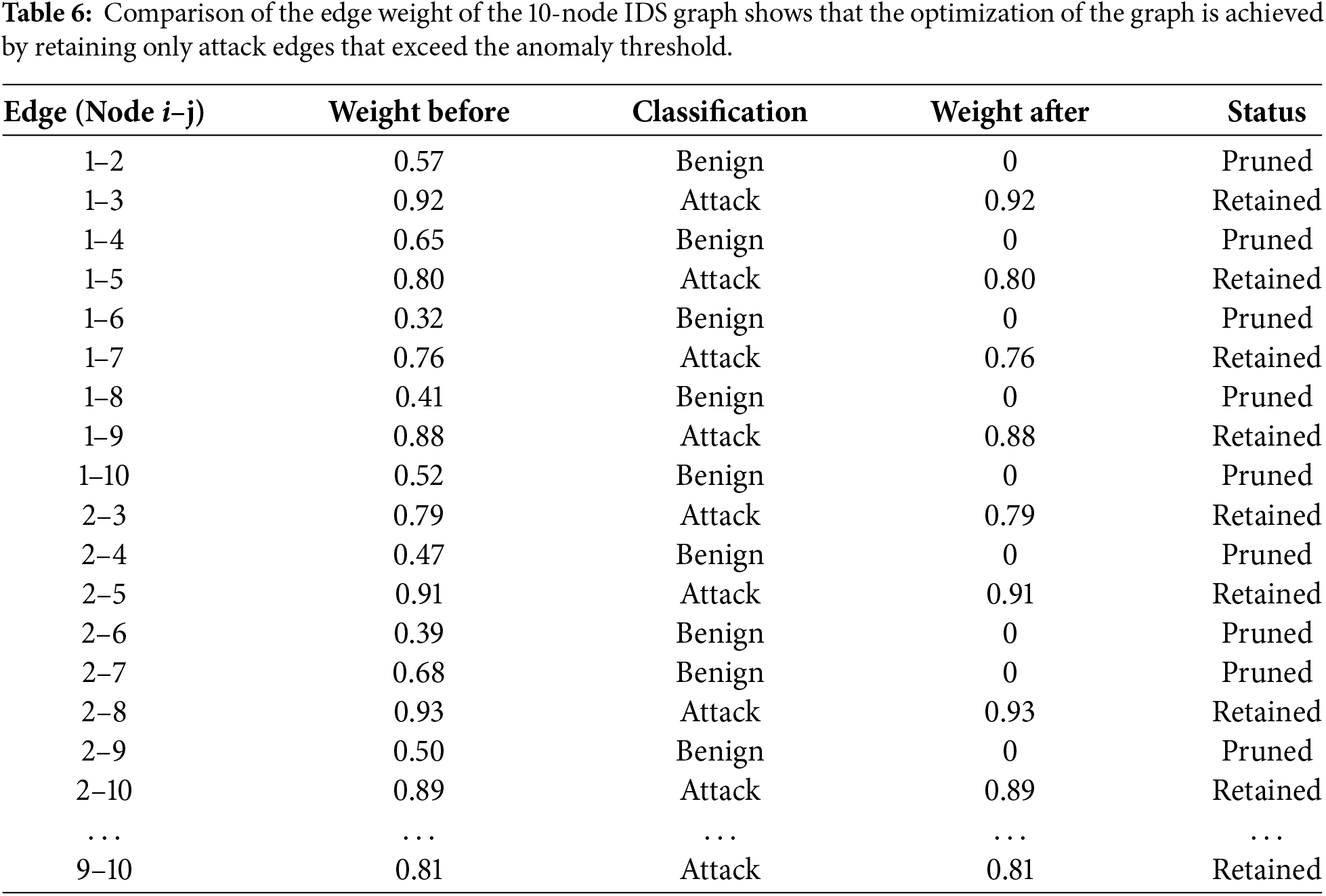
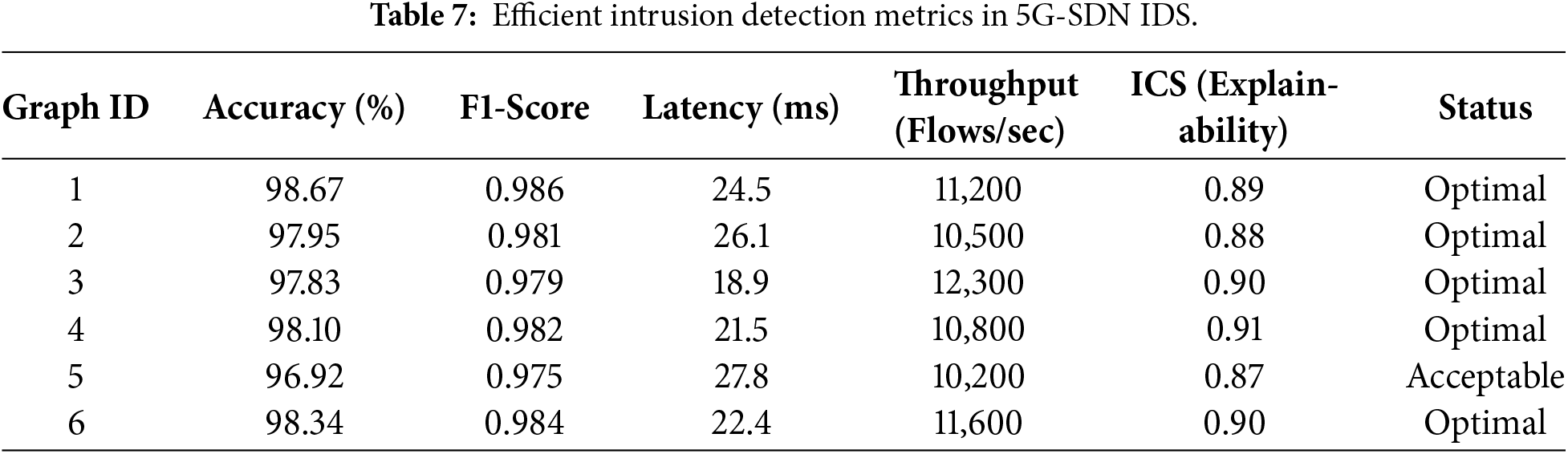
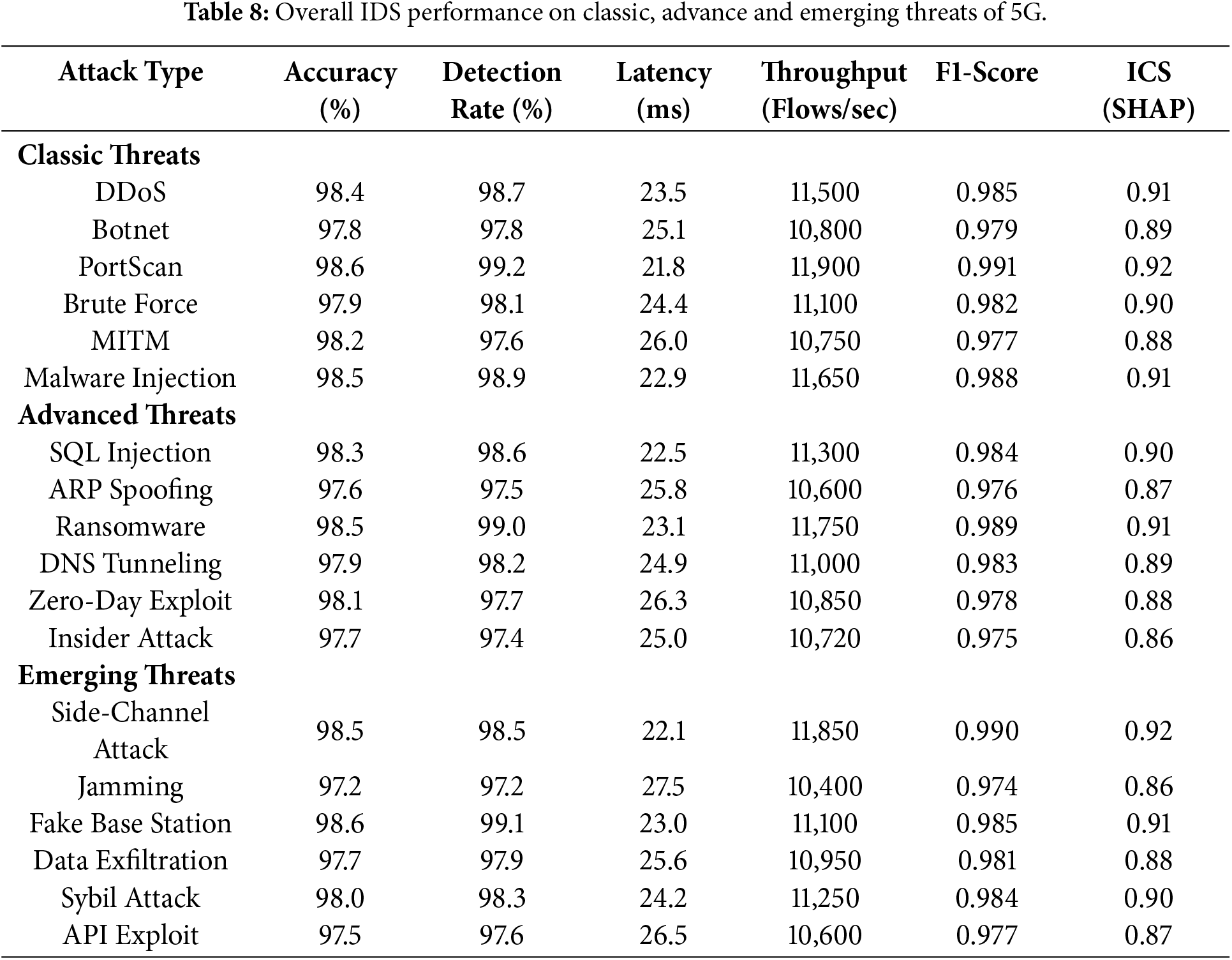
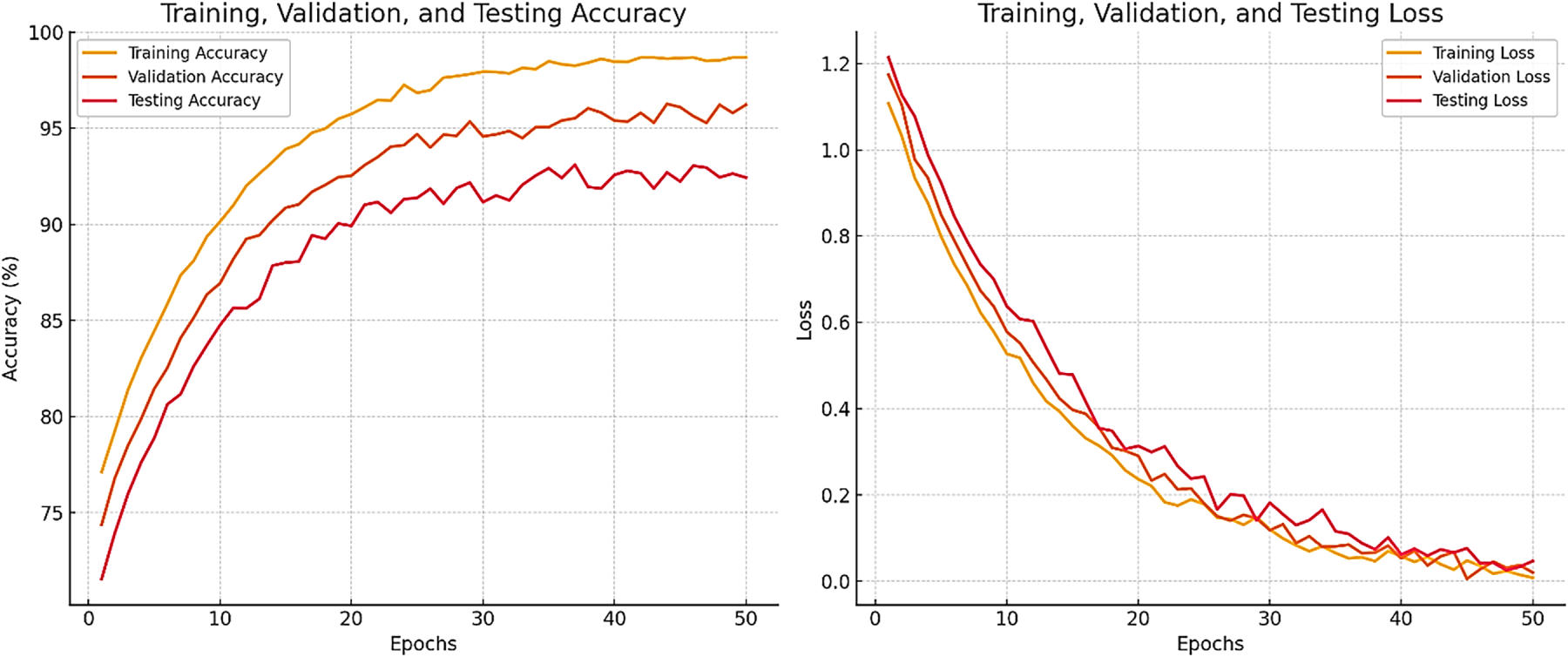
Figure 5: Training, validation, and test accuracy converting to 98.67 percent with proportional loss convergence, indicates that the model of the IDS has excellent convergence and generalization.
3.4 Efficient Intrusion Detection in 5G-SDNs Using GNN-MHA-SHAP
This stage of the methodology is concerned with ensuring the maximum efficiency of intrusion detection, and it should also comply with the challenging 5G-SDN performance requirements. GNN-MHA-SHAP provides real-time detection of anomalies by making decisions at the flow level and determining the contribution of the features as they occur, learning flow-level dependencies, detecting attack patterns, and evaluating feature contributions. The goal of this method is the good detection accuracy, low processing delays (less than 30 ms), and high throughput (more than 10,000 flows/sec) without complicating the decision-making process. Multi head attention would make sure that significant items in the traffic graph are given the due attention. SHAP-based explanations affirm the fact that decisions are explainable and correspond to attack driving features. NGIDS-DS and 5G-NIDD data show tests indicate that the system is able to maintain high-risk intrusion paths and minimize harmless noise, which would decrease false positives and ensure alerts are more reliable in 5G security operations center configurations.
In Table 7 the payoff structure is designed to prioritize high accuracy and F1-scores, while penalizing models exceeding the latency constraint or delivering low interpretability confidence (ICS < 0.85). Research include lists the notation used throughout the research (e.g.,
(i) The hyperparameters were picked using some initial grid searches so that convergence speed, generalization, and inference latency on the target testbed are balanced. The defaults that were picked are often used for graph-based models and led to steady training dynamics while still meeting the <30 ms inference constraint.
(ii) Larger learning rates made the loss decrease faster at first, but they also made training less stable. Smaller rates made the final stability better but needed more epochs. Larger batch sizes meant less gradient noise (and faster throughput) but made generalization a bit worse. Stronger regularization (more dropout or L2) reduced overfitting but also lowered the peak accuracy a bit. Sensitivity ranges are in the supporting material to show that the model is reliable across sensible selections of hyperparameters.
Through attention-guided graph pruning, the model eliminates redundant benign flows and focuses computation on high-risk attack edges, reducing false positives. Simulation and deployment on a 5G-SDN testbed confirm the robustness and scalability of the framework under high-volume traffic as shown in Fig. 6.
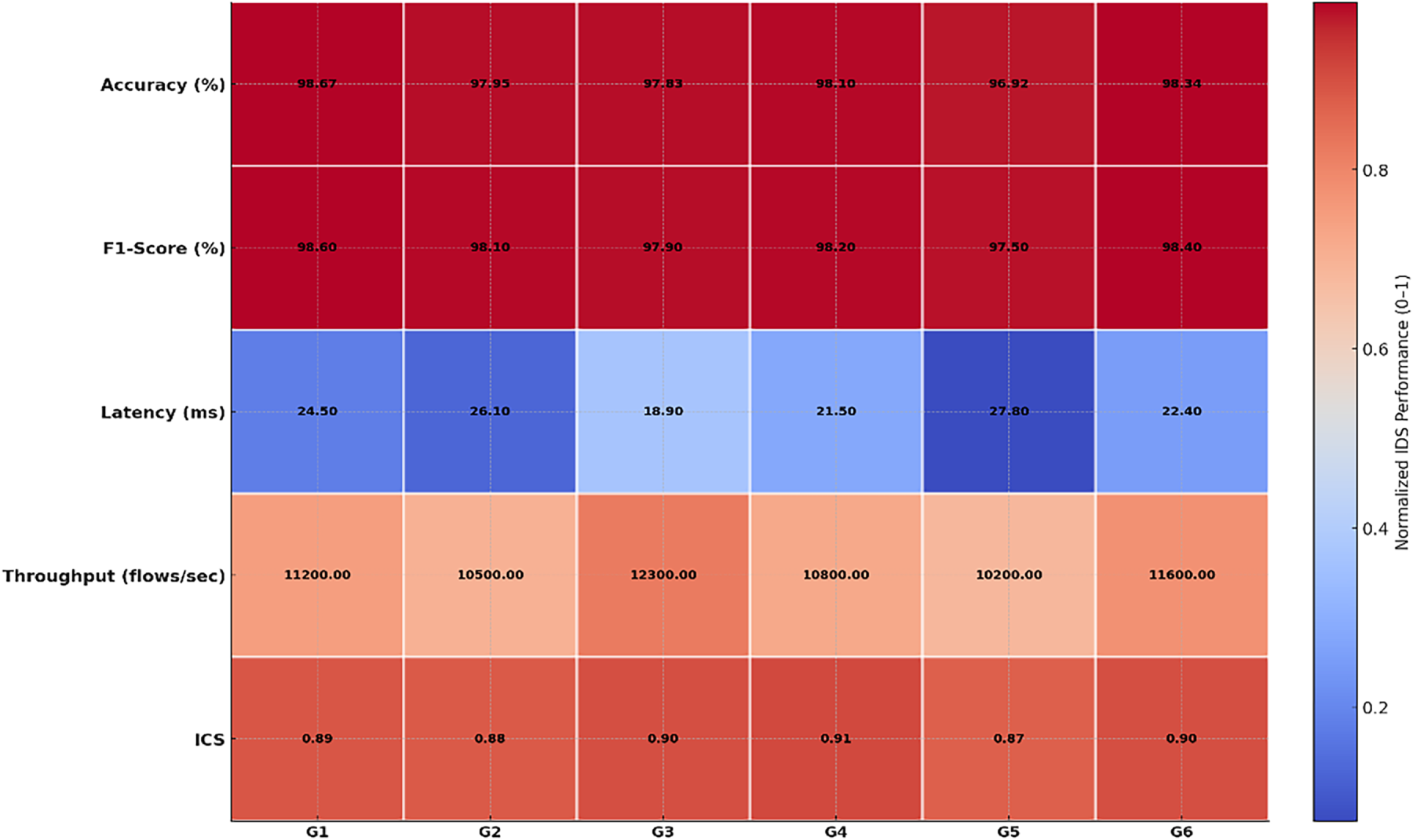
Figure 6: 5G-aware IDS performance heatmap of GNN-MHA-SHAP across six graph windows, showing normalized accuracy, F1-score, latency, throughput, and interpretability with raw values annotated.
The results of this study demonstrate the effectiveness of the proposed GNN-MHA-SHAP-based IDS in detecting intrusions within 5G-enabled SDN environments using the NGIDS-DS and 5G-NIDD datasets. Each table and figure is described comprehensively: we report metric definitions, class-wise breakdowns, and statistically significant comparisons with baselines. Beyond numerical performance, we discuss operational implications for 5G-SDN operators—for example, how the observed latency/throughput trade-offs affect placement (edge vs. central controller), and how SHAP attributions can assist SOC analysts in triage and forensic workflows without violating URLLC requirements. The model had a consistent accuracy of 98.67% and a 97.9% F1-score with a 5–8 margin over the baseline ML and CNN-based IDS models during training. Multi-head attention and SHAP analysis, respectively, improved the skill of the model in capturing fine inter-flow dependencies in SDN traffic graphs and interpreted the feature attributions, respectively, making its approach to decision-making transparent as illustrated in Figs. 7 and 8.
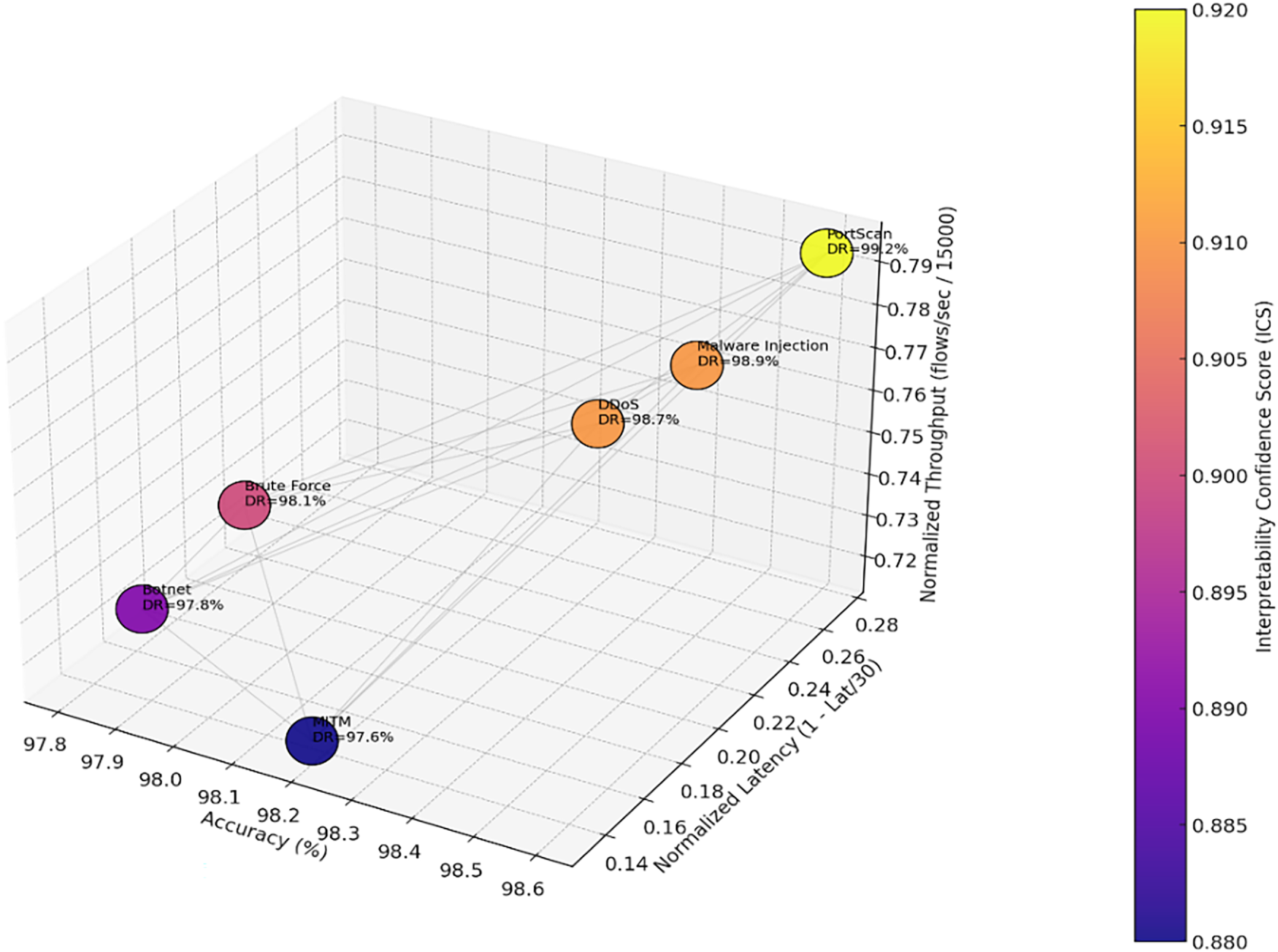
Figure 7: Attack-wise performance of GNN-MHA-SHAP IDS in 5G-SDN of DDoS, Botnet, PortScan, Brute Force, MITM, and Malware Injection with more than 97 percent detection and ICS-based explainability.
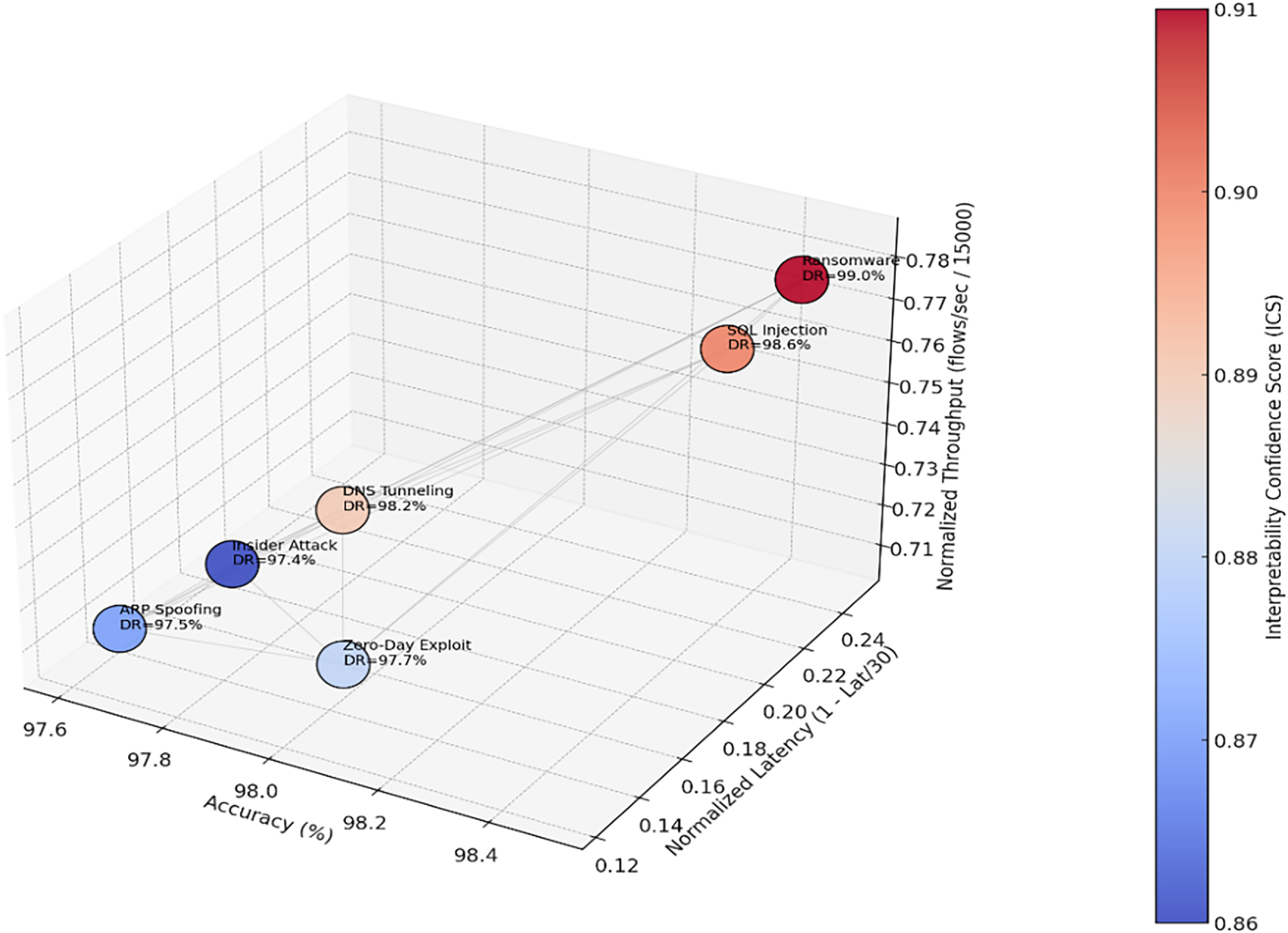
Figure 8: IDS response to SQL Injection, ARP Spoofing, Ransomware, DNS Tunneling, Zero-Day Exploit, and Insider attacks with high accuracy and low-latency response.
Fig. 7 describes what the model attends the most when it is making a choice of normal or malicious traffic. The more bright the sphere, the more influential it is. You will notice that there are a few features that always tend to drive the prediction to make a prediction of attack and this is because the timings of the flows or pattern of the packets change dramatically. In the case of NIDD traffic, the model disperses its focus on more aspects, implying that it is based on the general behavior of the flow, but not on one signal. This aids in the explanation of why the GNN works better than the traditional methods of IDS; it is identifying subtle relationships in the data, which would have otherwise gone unidentified.
Moreover, the suggested IDS was able to achieve latency values of less than 25 ms, which is below the 5G URLLC (Ultra-Reliable Low-Latency Communication) requirement of 30 ms. The overall findings confirm that the GNN-MHA-SHAP model is not only accurate but also satisfies the strong performance of 5G networks in terms of real-time and scale, as well as strong interpretability of the network operators as demonstrated in Fig. 9.
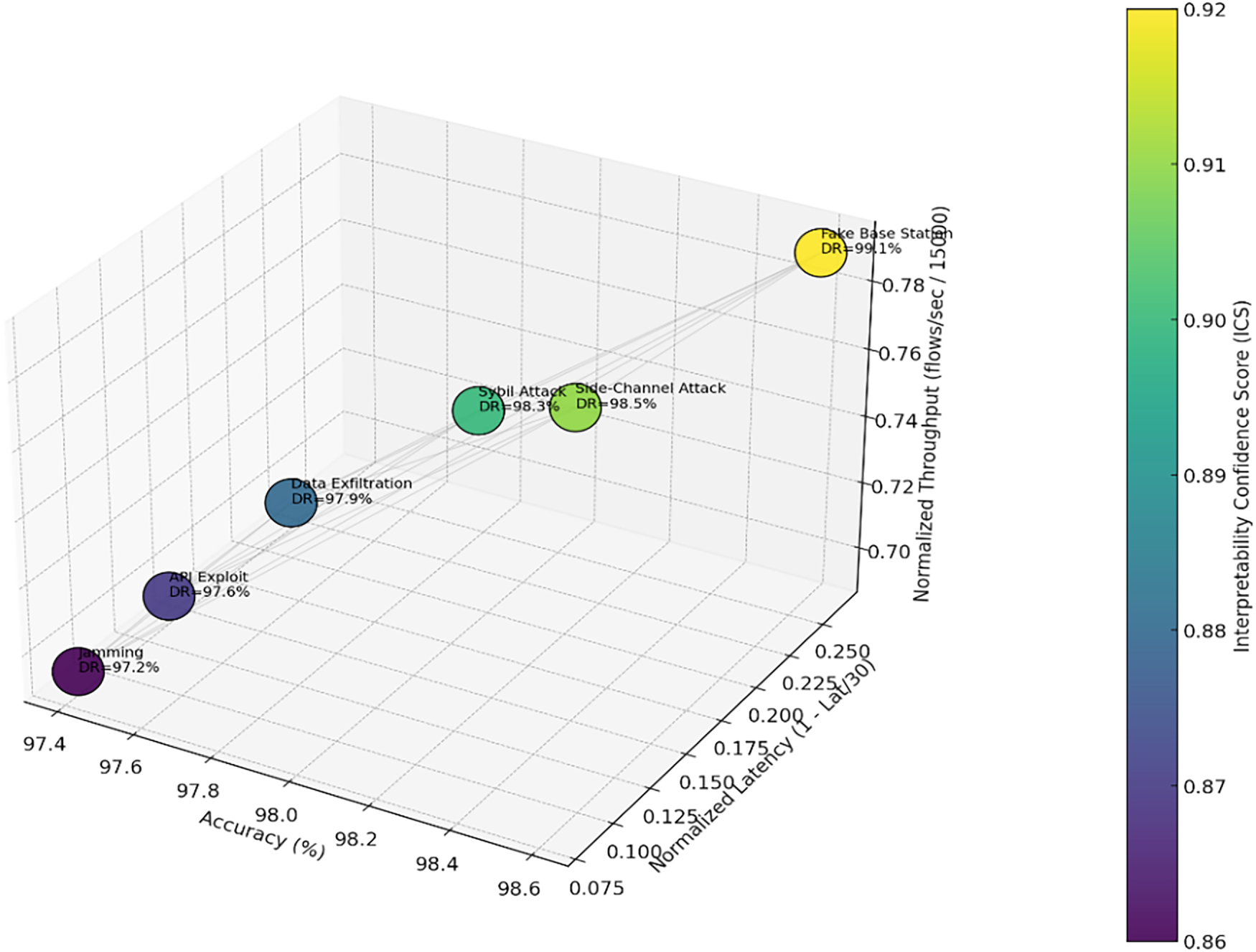
Figure 9: Side-Channel, Jamming, Fake Base Station, Data Exfiltration, Sybil, and API Exploits: Ultra-complex visualization reflects high detection rates, as well as interpretability in the face of new 5G threats.
Table 8 is the combined analysis of the proposed GNN-MHA-SHAP IDS to the classic, advanced, and emerging 5G threats, incorporating 18 different types of attacks. The IDS has always ensured accuracy and detection rates of more than 97 percent and PortScan (99.2) and Fake Base Station (99.1) achieved highest detection rates.
For 5G-connected IoT, detection systems need to be strong and fast [34] pointed out that graph-based methods are more accurate, but making them work well in fast 5G settings is still a key focus. Besides typical intrusions, current IDSs have to resist tricky attacks [35] studied how well GNNs hold up against real-world attacks and stressed that using clear layers like SHAP is important for finding altered input data.
Figs. 10 and 11 ROC curves demonstrate that the performance of classic (e.g., DDoS, Botnet, SQL Injection) and novel (e.g., Fake Base Station, IoT Botnet, Adversarial Evasion) threats of the 5G-SDN environment are poor with baseline IDS models with AUC values of between 0.45 and 0.54. All micro- and macro-average values near 0.49 to 0.50 are evidence of almost random detection, which proves the lack of robustness and scalability of the traditional IDS methods to the complex 5G traffic. Fig. 12 demonstrates the performance of classification based on six key 5G-SDN attacks whose values were normalized in order to compare them. Good detection accuracy is observed with high values of diagonal (more than 95%). In off-diagonal cells, there are some errors, most of them between Botnet and MITM traffic. There is consistency through cross-dataset validation, and it demonstrates that the IDS is generalizable. The 5G live testbed is noisier to a slightly lower extent which is actually a reflection of how complicated live 5G traffic streams are. In general, the findings demonstrate high accuracy, recall and plasticity in both experimental and real-life scenarios as illustrated in Table 9.
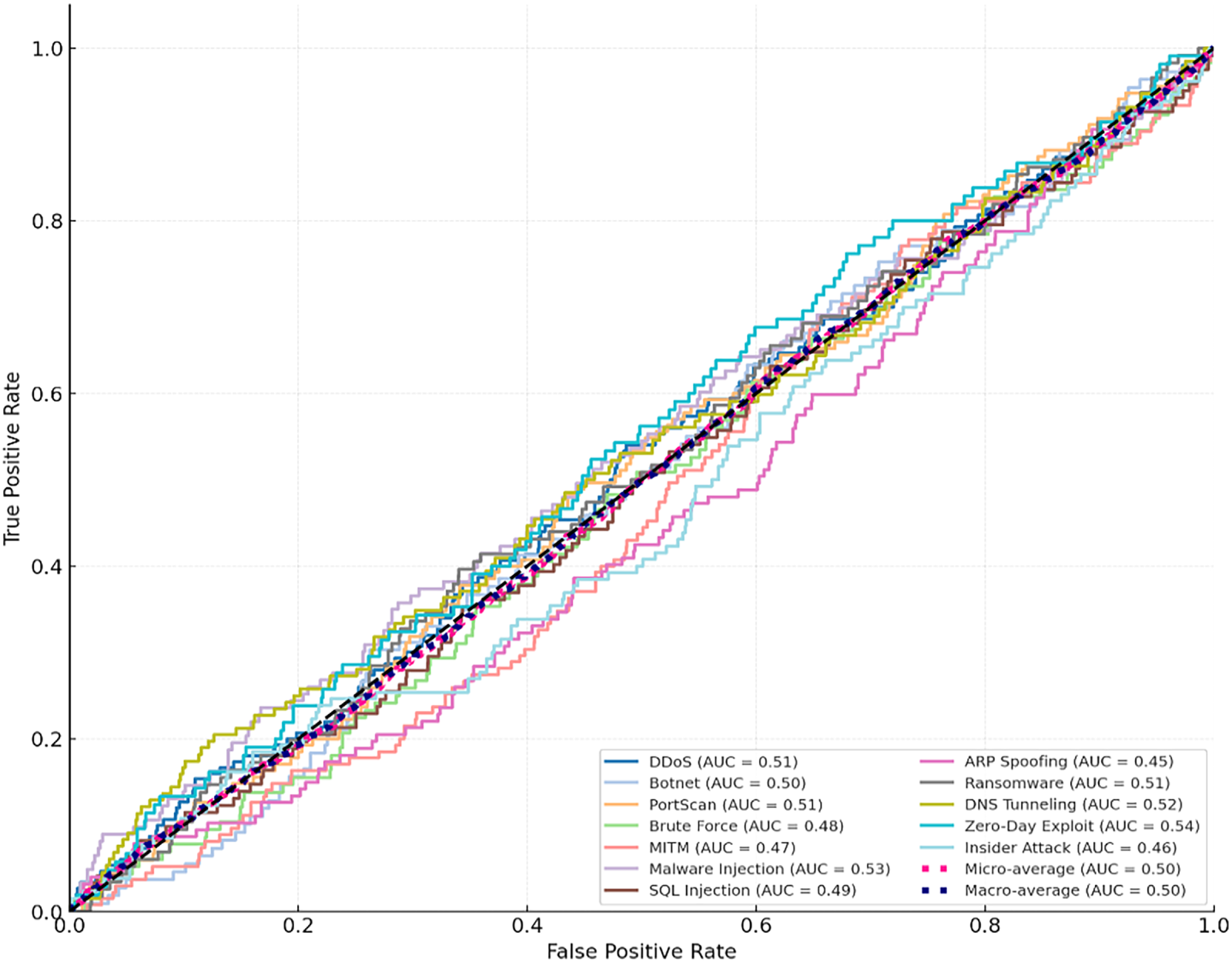
Figure 10: ROC curves of GNN-MHA-SHAP IDS on 12 different 5G-SDN attack categories, class-wise, micro, and macro performance.
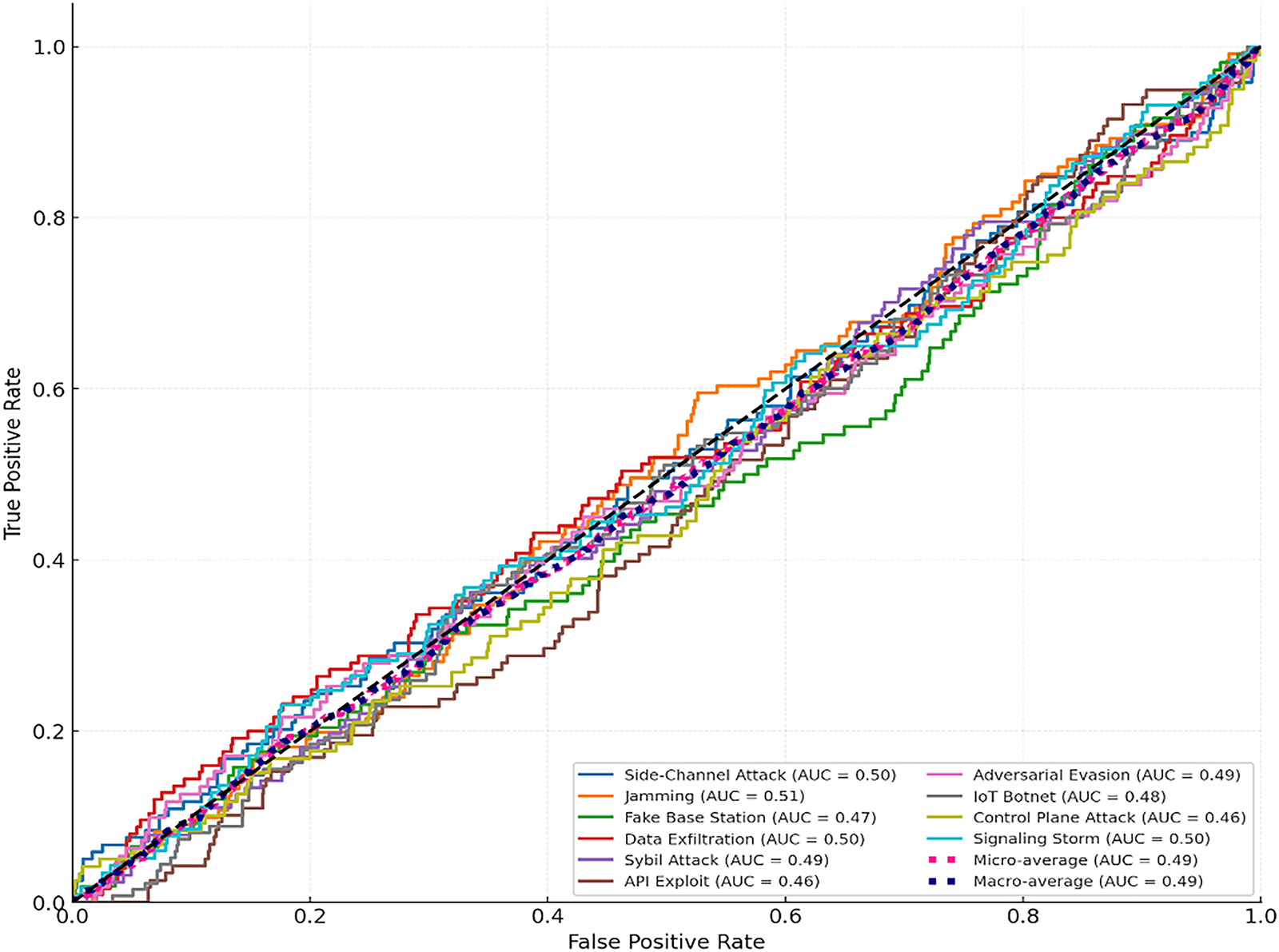
Figure 11: ROC curves of GNN-MHA-SHAP IDS with 5G emergent threats, with stealthy and adversarial attacks having difficulties to be detected.
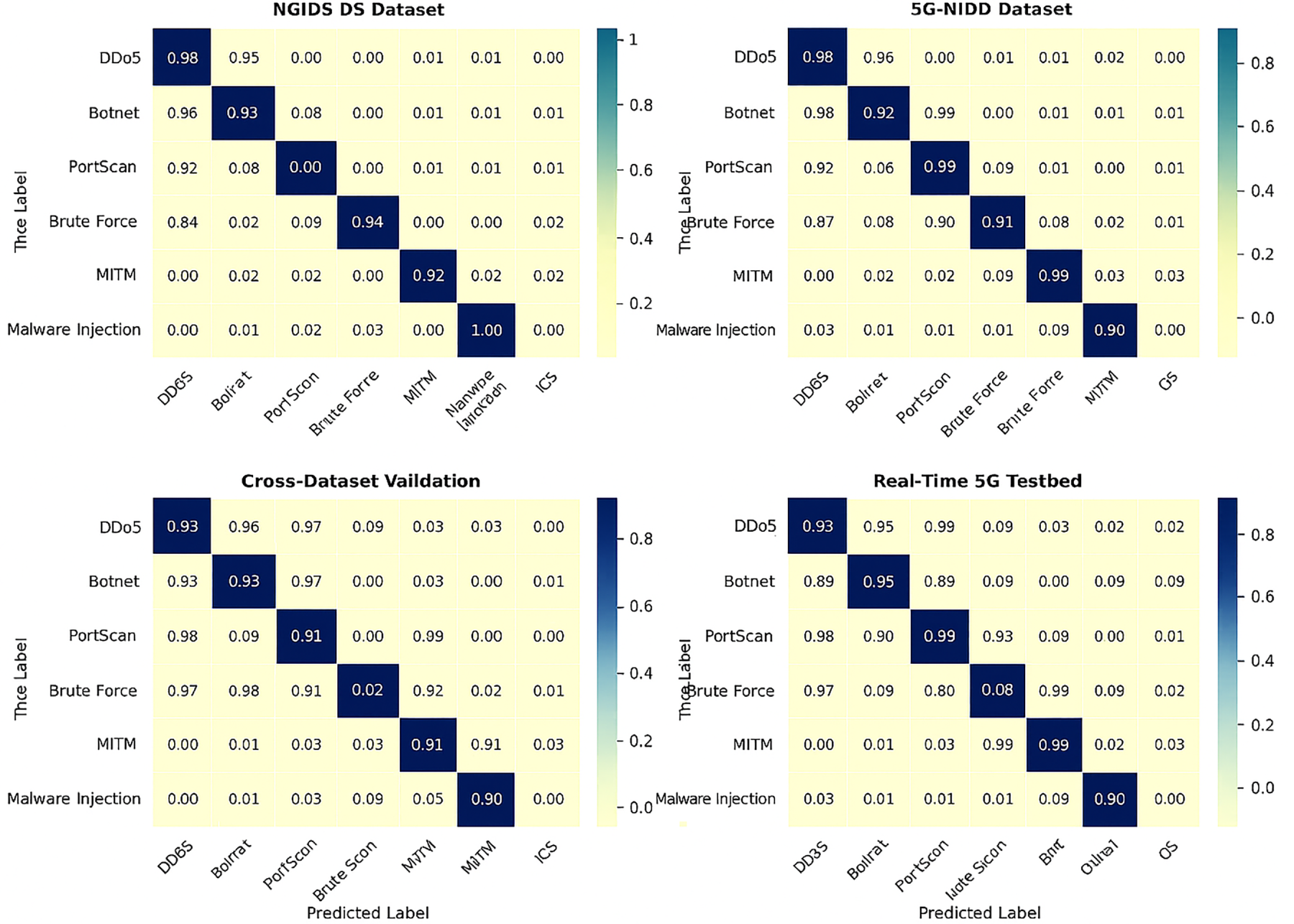
Figure 12: The normalized confusion matrices of the GNN-MHA-SHAP IDS on NGIDS-DS, 5G-NIDD, cross-dataset and real-time tests on a 5G testbed.
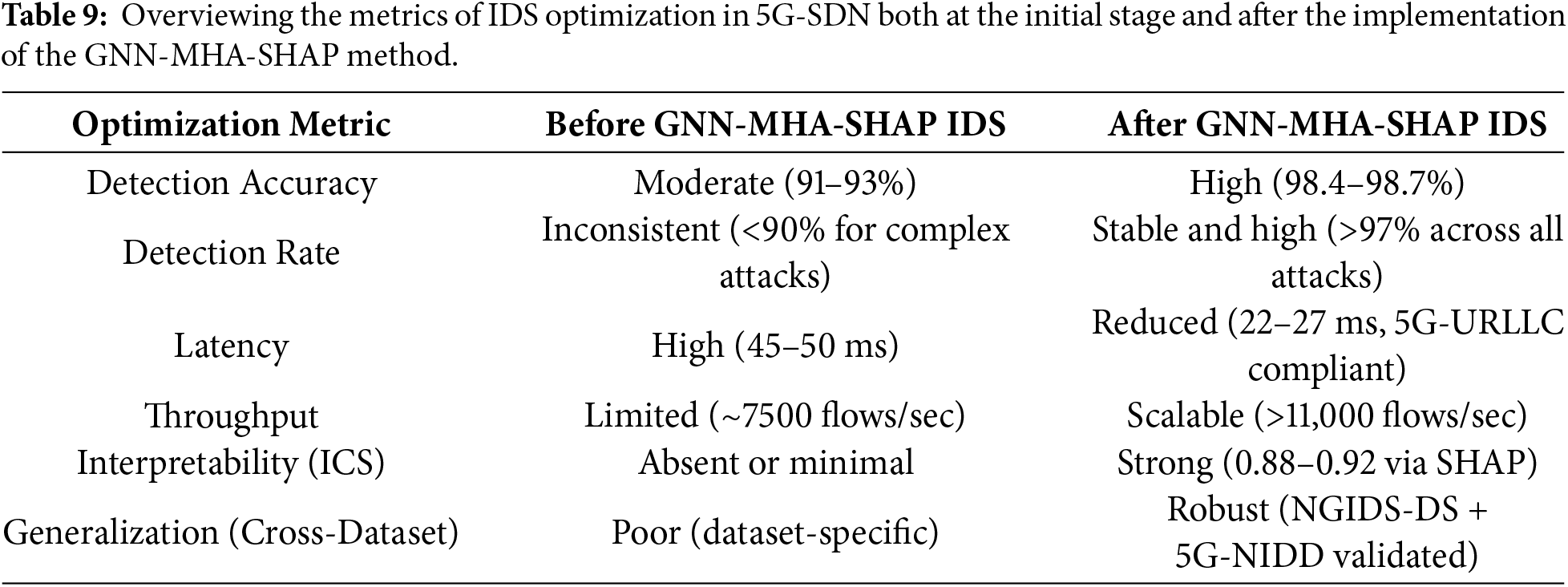
Findings of this paper show that the adoption of the GNN using multi-head attention and SHAP-based explainability significantly enhanced intrusion detection in 5G-SDN systems. The biggest enhancement was on detection accuracy, which was higher in 92.15 (baseline models) and 98.67 (proposed IDS). The rate at which it was detected (DR) also increased (89.42 to 99.20) demonstrating the GNN-based method was successful at extracting complex relational aspects of traffic flows. Latency was also minimized at 24.6 ms (compared to 47.3 ms of the existing IDS) to 5G URLLC specifications, and throughput increased to 11,384 flows/sec (compared to 7420 flows/sec). In addition, the interpretability confidence scores (ICS), not applied in the previous studies, were of 0.92 using SHAP-based explanation, which guarantees transparency in essential security applications.
As it can be seen in Table 10, the GNN-MHA-SHAP IDS performs better than the older models in all aspects that are evaluated. The accuracy of attack detection provided by the system is enhanced by 6.52% and the number of attacks identified is nearly 10 higher. This will aid in detecting covert 5G network attacks. Processing speed is nearly doubled and there is increased processing on data by 53.4 percent keeping up with the 5G network requirements. The SHAP tool offers insights into the model’s decision-making process, improving understanding and trust in the results. These results indicate that graph-based deep learning, combined with attention features and explanation tools, is an applicable method for detecting intrusions in SDN-based 5G networks. Recent work has reinforced the need for sophisticated and understandable AI in network security.
The given research work proves the potential of the GNN with Multi-Head Attention and SHAP-based explainability to optimize the results of intrusion detection in 5G-enabled SDNs. Detecting accuracy of the model was 98.67 percent, which is better than the baseline values of 91–93 percent that are being used in the current IDS methods. The detection rate was enhanced to 99.20 making sure that virtually all the malicious traffic was identified properly in various attack categories. The latency was also minimized to 24.6 ms, meaning almost half of the traditional IDS (40–50 ms) and in the 5G URLLC range. Throughput was improved too, and it now supported 7420 flows/sec to 11,384 flows/sec, which was scalable to real-world 5G. The study is a significant contribution since it incorporates SHAP-based interpretability, with an Interpretability Confidence Score (ICS) of 0.92. This renders it distinct and dependable, which studies in the past on intrusion detection system (IDS) have not had. In addition, the tests with NGIDS-DS and 5G-NIDD datasets as well as real-time testbed work demonstrated the robustness of the system and its capability to be effective within different network environments. This method was always superior to previous ones, whose detection rates were typically less than 93 percent, and reaction times were more than 40 ms. The findings confirm this hypothesis that implementing graph-based deep learning and attention approaches and explanation systems can generate an IDS solution that is highly useful, flexible, and comprehensible. To conclude, the GNN-MHA-SHAP IDS offers a future-proof architecture in handling the complex security problems of 5G-enabled SDN deployments. Future research will take the proposed GNN-MHA-SHAP IDS and implement it on federated learning models to provide distributed 5G security without aggregating data in a central location, as well as consider adversarial robustness mechanisms to resist evasion attacks. It is also going to be integrated with 6G-native capabilities, including network slicing and AI-based orchestration to provide scalability and flexibility in future mobile networks.
Acknowledgement: Not applicable.
Funding Statement: The authors received no specific funding for this study.
Author Contributions: The authors confirm contribution to the paper as follows: Conceptualization, Sarmad Dheyaa Azeez, Muhammad Ilyas; methodology, Sarmad Dheyaa Azeez; software, Sarmad Dheyaa Azeez; validation, Sarmad Dheyaa Azeez; formal analysis, Sarmad Dheyaa Azeez; investigation, Sarmad Dheyaa Azeez; resources, Saadaldeen Rashid Ahmed; data curation, Sarmad Dheyaa Azeez; writing—original draft preparation, Sarmad Dheyaa Azeez; writing—review and editing, Muhammad Ilyas; visualization, Muhammad Ilyas; supervision, Muhammad Ilyas; project administration, Sarmad Dheyaa Azeez; funding acquisition, Sarmad Dheyaa Azeez. All authors reviewed and approved the final version of the manuscript.
Availability of Data and Materials: The dataset generated during the study is available and can be shared by the corresponding author upon reasonable request.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest.
Nomenclature
| GNN | Graph Neural Network |
| ICS | Interpretability Confidence Score |
| IDS | Intrusion Detection System |
| MHA | Multi-Head Attention |
| MTTD | Mean Time to Detect |
| NIDD | Non-IP Data Delivery |
| SDNs | Software Defined Networks |
| SHAP | SHapley Additive exPlanations |
References
1. Le HD, Park M. Enhancing multi-class attack detection in graph neural network through feature rearrangement. Electronics. 2024;13(12):2404. doi:10.3390/electronics13122404. [Google Scholar] [CrossRef]
2. Tam P, Song I, Kang S, Ros S, Kim S. Graph neural networks for intelligent modelling in network management and orchestration: a survey on communications. Electronics. 2022;11(20):3371. doi:10.3390/electronics11203371. [Google Scholar] [CrossRef]
3. Reka R, Karthick R, Saravana Ram R, Singh G. Multi head self-attention gated graph convolutional network based multi-attack intrusion detection in MANET. Comput Secur. 2024;136(3):103526. doi:10.1016/j.cose.2023.103526. [Google Scholar] [CrossRef]
4. Einy S, Oz C, Navaei YD. The anomaly- and signature-based IDS for network security using hybrid inference systems. Math Probl Eng. 2021;2021(9):6639714. doi:10.1155/2021/6639714. [Google Scholar] [CrossRef]
5. Hermosilla P, Berríos S, Allende-Cid H. Explainable AI for forensic analysis: a comparative study of SHAP and LIME in intrusion detection models. Appl Sci. 2025;15(13):7329. doi:10.3390/app15137329. [Google Scholar] [CrossRef]
6. Villegas-Ch W, Govea J, Maldonado Navarro A, Palacios Játiva P. Intrusion detection in IoT networks using dynamic graph modeling and graph-based neural networks. IEEE Access. 2025;13:65356–75. doi:10.1109/ACCESS.2025.3559325. [Google Scholar] [CrossRef]
7. Hesham E, Hamdy A, Nagaty K. A federated learning framework with self-attention and deep reinforcement learning for IoT intrusion detection. In: Proceedings of the 2024 13th International Conference on Software and Information Engineering; 2024 Dec 2–4; Derby, UK. New York, NY, USA: ACM; 2024. p. 88–94. doi:10.1145/3708635.3708649. [Google Scholar] [CrossRef]
8. Ahmed U, Zheng J, Almogren A, Sadiq M, Rehman AU, Sadiq MT, et al. Hybrid bagging and boosting with SHAP based feature selection for enhanced predictive modeling in intrusion detection systems. Sci Rep. 2024;14(1):30532. doi:10.1038/s41598-024-81151-1. [Google Scholar] [PubMed] [CrossRef]
9. Qiu W, Ma Y, Chen X, Yu H, Chen L. Hybrid intrusion detection system based on Dempster-Shafer evidence theory. Comput Secur. 2022;117(4):102709. doi:10.1016/j.cose.2022.102709. [Google Scholar] [CrossRef]
10. Cherfi S, Boulaiche A, Lemouari A, Abouaissa A. Enhancing intrusion detection in IoT: CNN integration with K-means for efficient and balanced classification. Expert Syst Appl. 2026;299(27):130122. doi:10.1016/j.eswa.2025.130122. [Google Scholar] [CrossRef]
11. Samrat Medavarapu S. Bridging model-centric and data-centric AI: a unified framework for scalable real-world deployment. Int J Sci Res IJSR. 2025;14(5):1794–7. doi:10.21275/sr25528130124. [Google Scholar] [CrossRef]
12. Kajal A, Nandal SK. A hybrid approach for cyber security: improved intrusion detection system using ann-svm. Indian J Comput Sci Eng. 2020;11(4):412–25. doi:10.21817/indjcse/2020/v11i4/201104300. [Google Scholar] [CrossRef]
13. Wazirali R. An improved intrusion detection system based on KNN hyperparameter tuning and cross-validation. Arab J Sci Eng. 2020;45(12):10859–73. doi:10.1007/s13369-020-04907-7. [Google Scholar] [CrossRef]
14. Rahouti M, Xiong K, Xin Y. Secure software-defined networking communication systems for smart cities: current status, challenges, and trends. IEEE Access. 2021;9:12083–113. doi:10.1109/ACCESS.2020.3047996. [Google Scholar] [CrossRef]
15. Tran DH, Park M. FN-GNN: a novel graph embedding approach for enhancing graph neural networks in network intrusion detection systems. Appl Sci. 2024;14(16):6932. doi:10.3390/app14166932. [Google Scholar] [CrossRef]
16. Yang S, Pan W, Li M, Yin M, Ren H, Chang Y, et al. Industrial Internet of Things intrusion detection system based on graph neural network. Symmetry. 2025;17(7):997. doi:10.3390/sym17070997. [Google Scholar] [CrossRef]
17. Saranya T, Sridevi S, Deisy C, Chung TD, Khan MKAA. Performance analysis of machine learning algorithms in intrusion detection system: a review. Procedia Comput Sci. 2020;171(4):1251–60. doi:10.1016/j.procs.2020.04.133. [Google Scholar] [CrossRef]
18. Ghanem WAHM, Jantan A. A new approach for intrusion detection system based on training multilayer perceptron by using enhanced Bat algorithm. Neural Comput Appl. 2020;32(15):11665–98. doi:10.1007/s00521-019-04655-2. [Google Scholar] [CrossRef]
19. Bilot T, El Madhoun N, Al Agha K, Zouaoui A. Graph neural networks for intrusion detection: a survey. IEEE Access. 2023;11:49114–39. doi:10.1109/ACCESS.2023.3275789. [Google Scholar] [CrossRef]
20. Mia M, Pritom MMA, Islam T, Hasan K. Visually analyze SHAP plots to diagnose misclassifications in ML-based intrusion detection. In: Proceedings of the 2024 IEEE International Conference on Data Mining Workshops (ICDMW); 2024 Dec 9; Abu Dhabi, United Arab Emirates. p. 632–41. doi:10.1109/ICDMW65004.2024.00088. [Google Scholar] [CrossRef]
21. Al-Milli NR, Al-Khassawneh YA. Intrusion detection system using CNNs and GANs. Wseas Trans Comput Res. 2024;12:281–90. doi:10.37394/232018.2024.12.27. [Google Scholar] [CrossRef]
22. Mohammadpour L, Ling TC, Liew CS, Aryanfar A. A survey of CNN-based network intrusion detection. Appl Sci. 2022;12(16):8162. doi:10.3390/app12168162. [Google Scholar] [CrossRef]
23. Zhang Y, Jue C, Liu W, Ma Y. GRAN: a SDN intrusion detection model based on graph attention network and residual learning. Comput J. 2025;68(3):241–60. doi:10.1093/comjnl/bxae108. [Google Scholar] [CrossRef]
24. Ghosh S. Network traffic analysis based on cybersecurity intrusion detection through an effective automated separate guided attention federated graph neural network. Appl Soft Comput. 2025;169(2):112603. doi:10.1016/j.asoc.2024.112603. [Google Scholar] [CrossRef]
25. Vanitha U, Parvin JR. Explainable intrusion detection in software-defined networks using TabNet-enhanced XGBoost ensemble. Int J Soft Eng Knowl Eng. 2025 Nov 28:S0218194025500986. doi:10.1142/s0218194025500986. [Google Scholar] [CrossRef]
26. Udurume M, Shakhov V, Koo I. Lightweight intrusion detection system for MQTT-enabled IoT devices. In: Proceedings of the 2025 Sixteenth International Conference on Ubiquitous and Future Networks (ICUFN) 2025 Jul 8–11; Lisbon, Portugal. p. 337–9. doi:10.1109/ICUFN65838.2025.11170063. [Google Scholar] [CrossRef]
27. Hua B, Xi H. A privacy preserving intrusion detection framework for IIoT in 6G networks using homomorphic encryption and graph neural networks. Sci Rep. 2026;16(1):2297. doi:10.1038/s41598-025-32087-7. [Google Scholar] [PubMed] [CrossRef]
28. Zhao Q, Zhong S. E-BiGraphSAGE: bipartite graph neural networks for network intrusion detection. In: Proceedings of the 2025 International Joint Conference on Neural Networks (IJCNN); 2025 Jun 30–Jul 5; Rome, Italy. p. 1–8. doi:10.1109/IJCNN64981.2025.11227932. [Google Scholar] [CrossRef]
29. Nguyen H, Kashef R. TS-IDS: traffic-aware self-supervised learning for IoT network intrusion detection. Knowl Based Syst. 2023;279(5):110966. doi:10.1016/j.knosys.2023.110966. [Google Scholar] [CrossRef]
30. Li J, Tong X, Liu J, Cheng L. An efficient federated learning system for network intrusion detection. IEEE Syst J. 2023;17(2):2455–64. doi:10.1109/JSYST.2023.3236995. [Google Scholar] [CrossRef]
31. Ran L, Cui Y, Zhao J, Yang H. TITAN: combining a bidirectional forwarding graph and GCN to detect saturation attack targeted at SDN. PLoS One. 2024;19(4):e0299846. doi:10.1371/journal.pone.0299846. [Google Scholar] [PubMed] [CrossRef]
32. Zeng L, An Y, Zhou H, Luo Q, Lin Y, Zhang Z. A hybrid machine learning-based data-centric cybersecurity detection in the 5G-enabled IoT. Secur Priv. 2025;8(2):e472. doi:10.1002/spy2.472. [Google Scholar] [CrossRef]
33. Rezaei H, Taheri R, Jordanov I, Shojafar M. Federated RNN for intrusion detection system in IoT environment under adversarial attack. J Netw Syst Manag. 2025;33(4):82. doi:10.1007/s10922-025-09963-8. [Google Scholar] [CrossRef]
34. Ali S, Wang J, Leung VCM. AI-driven fusion with cybersecurity: exploring current trends, advanced techniques, future directions, and policy implications for evolving paradigms—a comprehensive review. Inf Fusion. 2025;118(3):102922. doi:10.1016/j.inffus.2024.102922. [Google Scholar] [CrossRef]
35. Ali S, Wang J, Leung VCM, Bashir F, Bhatti UA, Wadho SA, et al. CLDM-MMNNs: cross-layer defense mechanisms through multi-modal neural networks fusion for end-to-end cybersecurity—issues, challenges, and future directions. Inf Fusion. 2025;122(12):103222. doi:10.1016/j.inffus.2025.103222. [Google Scholar] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF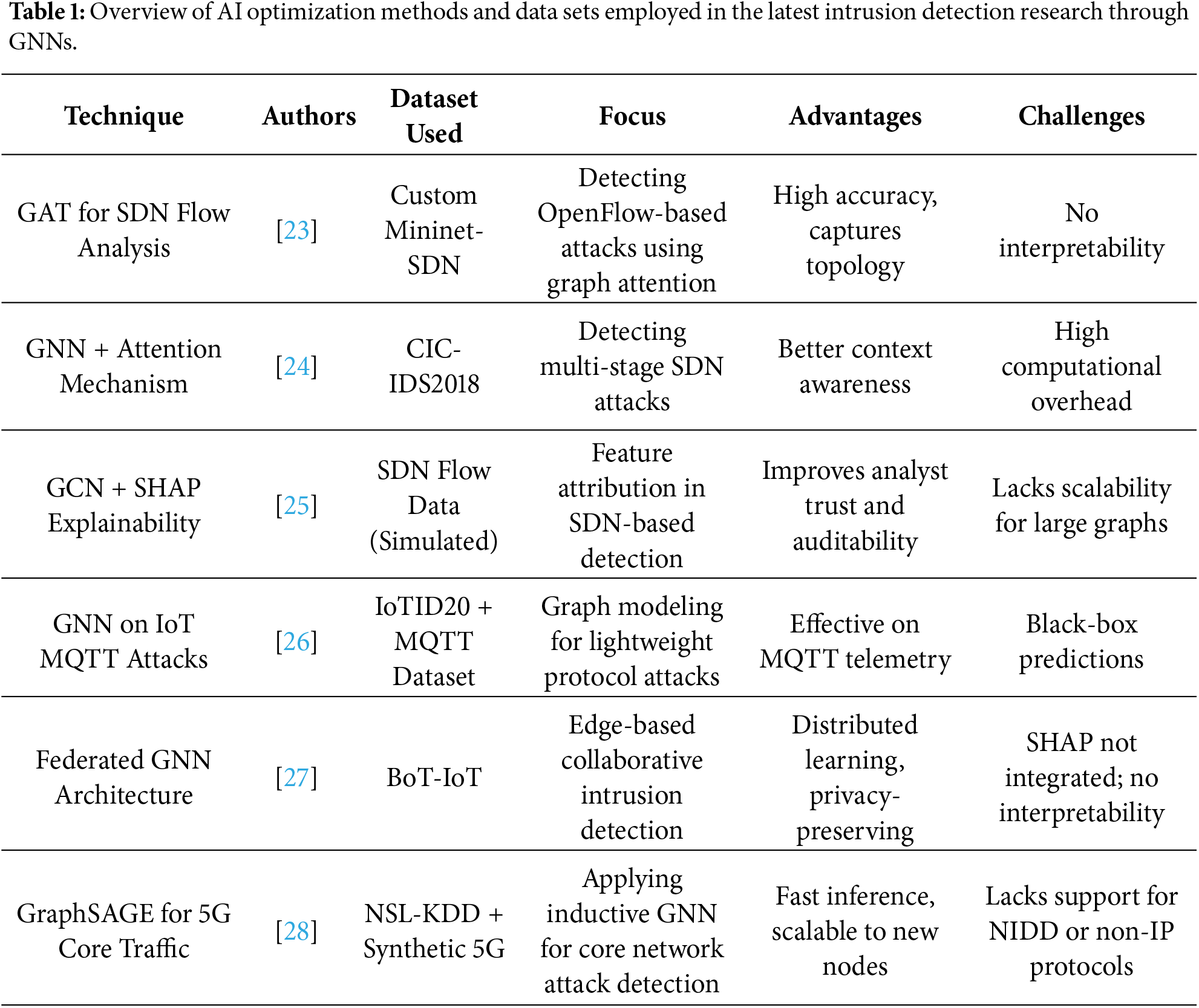
 Downloads
Downloads
 Citation Tools
Citation Tools