 Open Access
Open Access
REVIEW
Task Offloading and Edge Computing in IoT—Gaps, Challenges and Future Directions
School of Computer Engineering, Kalinga Institute of Industrial Technology (KIIT) Deemed to be University, Bhubaneswar, Odisha, India
* Corresponding Author: Hitesh Mohapatra. Email:
Computers, Materials & Continua 2026, 87(3), 8 https://doi.org/10.32604/cmc.2026.076726
Received 25 November 2025; Accepted 16 January 2026; Issue published 09 April 2026
Abstract
This review examines current approaches to real-time decision-making and task optimization in Internet of Things systems through the application of machine learning models deployed at the network edge. Existing literature shows that edge-based distributed intelligence reduces cloud dependency. It addresses transmission latency, device energy use, and bandwidth limits. Recent optimization strategies employ dynamic task offloading mechanisms to determine optimal workload placement across local devices and edge servers without centralized coordination. Empirical findings from the literature indicate performance improvements with latency reductions of approximately 32.8% and energy efficiency gains of 27.4% compared to conventional cloud-centric models. However, critical gaps remain in current methodologies. Most studies focus on static network topologies and do not adequately address load balancing across multiple edge nodes. Security vulnerabilities during task transmission are underexplored, and privacy considerations for sensitive data remain insufficiently integrated into existing frameworks. Task caching strategies and fault tolerance mechanisms require further investigation in highly dynamic environments. The ability of existing approaches to handle large-scale deployments and complex edge-cloud collaborative scenarios has not been thoroughly validated. This review synthesizes current progress while identifying fundamental challenges that must be resolved for practical deployment in time-sensitive applications spanning smart manufacturing, autonomous systems, and healthcare monitoring. Future work should prioritize robust security integration, efficient load distribution, and scalability across heterogeneous edge infrastructures.Keywords
The exponential growth of Internet of Things (IoT) devices has fundamentally transformed how data is processed in modern computing environments. Traditional cloud computing architectures face inherent limitations when handling massive volumes of data generated by billions of distributed IoT devices. Edge computing shifts computation to network periphery. It processes data near sources, not centralized cloud centers [1]. In edge computing, IoT devices and sensors interact with local edge servers. These nodes process data initially before selective cloud transmission [2]. Hierarchical computing spans IoT devices, edge nodes, and cloud centers. This tiered model addresses cloud-only limitations [3]. Task offloading transfers intensive operations from limited devices to capable edge servers [4]. Mobile Edge Computing (MEC) uses offloading to cut bandwidth use, latency, and device load [5]. The decision of where and when to offload tasks constitutes a complex optimization challenge, belonging to the category of NP-hard problems that require sophisticated decision-making approaches.
The practical relevance of edge computing and task offloading extends across multiple domains. Edge processing tackles cloud constraints. It reduces latency, bandwidth limits, connectivity issues, and device energy use [6]. For applications demanding real-time responsiveness such as autonomous vehicles, industrial IoT systems, smart cities, and health care monitoring, the millisecond-level decision latency achievable through edge computing becomes essential rather than optional. From an industrial perspective, manufacturing facilities, infrastructure monitoring systems, and connected transportation networks generate continuous data streams that cannot tolerate the latency associated with cloud-dependent processing [7]. Edge AI integration boosts autonomy. It enables decisions without constant cloud links. This cuts costs and improves reliability [8]. Furthermore, security and privacy considerations favor edge-based processing, as sensitive data processing can occur locally without necessitating transmission to centralized repositories [9]. Edge computing efficiency affects IoT adoption in smart cities and industry. It impacts reliability and societal benefits.
1.2 Current State of Knowledge
Recent literature demonstrates substantial progress in edge computing optimization through multiple research directions. Deep Reinforcement Learning (DRL) enables dynamic task offloading. It cuts latency by 32.8% and boosts energy efficiency by 27.4% over cloud models [10]. Value-based DRL methods optimize MEC offloading. Deep Q-Network (DQN), Double DQN, and Dueling DQN learn state-action values from interactions [11]. Policy gradient methods and actor-critic frameworks have also demonstrated effectiveness in handling continuous action spaces inherent in resource allocation problems [12]. Ensemble learning with density clustering outperforms baselines. It reduces task queues by over 21% [13]. Conventional optimization techniques offer foundational solutions. Convex methods, evolutionary algorithms, and game theory face scalability limits in large heterogeneous networks [14]. Static optimization fails in dynamic IoT environments where, network conditions, tasks, and resources change continuously.
Despite significant progress, critical research gaps persist. Most existing DRL-based offloading studies focus on static or semi-dynamic network topologies and do not adequately address load balancing complexities across multiple distributed edge nodes [7]. Security vulnerabilities in task transmission and data processing at edge nodes stay underexplored. Many studies ignore privacy effects for sensitive data processing. Reward function design in multi-objective optimization lacks agreement. Latency, energy use, and fairness require joint optimization. Designs often show poor balance among competing goals [15]. Scalability limitations present a fundamental controversy. Most deep reinforcement learning (DRL) approaches employ centralized learning models that require global state awareness, creating bottlenecks unsuitable for large-scale distributed IoT networks [16]. Multi-agent reinforcement learning frameworks support distributed decision-making. These frameworks face issues in agent coordination. Synchronization across heterogeneous environments poses problems. Convergence under partial observability lacks guarantees [17]. Task caching strategies and fault tolerance mechanisms in highly dynamic environments with intermittent connectivity remain insufficiently investigated [18]. Offloading algorithms gain practical validation mainly through simulation environments. Real-world test-beds see limited use. This approach restricts generalizability across diverse deployment scenarios. Fig. 1 presents a comprehensive three-tier hierarchical architecture diagram illustrating the relationship between IoT devices, edge computing nodes, fog computing layer, and cloud infrastructure, with task offloading pathways and decision flows.
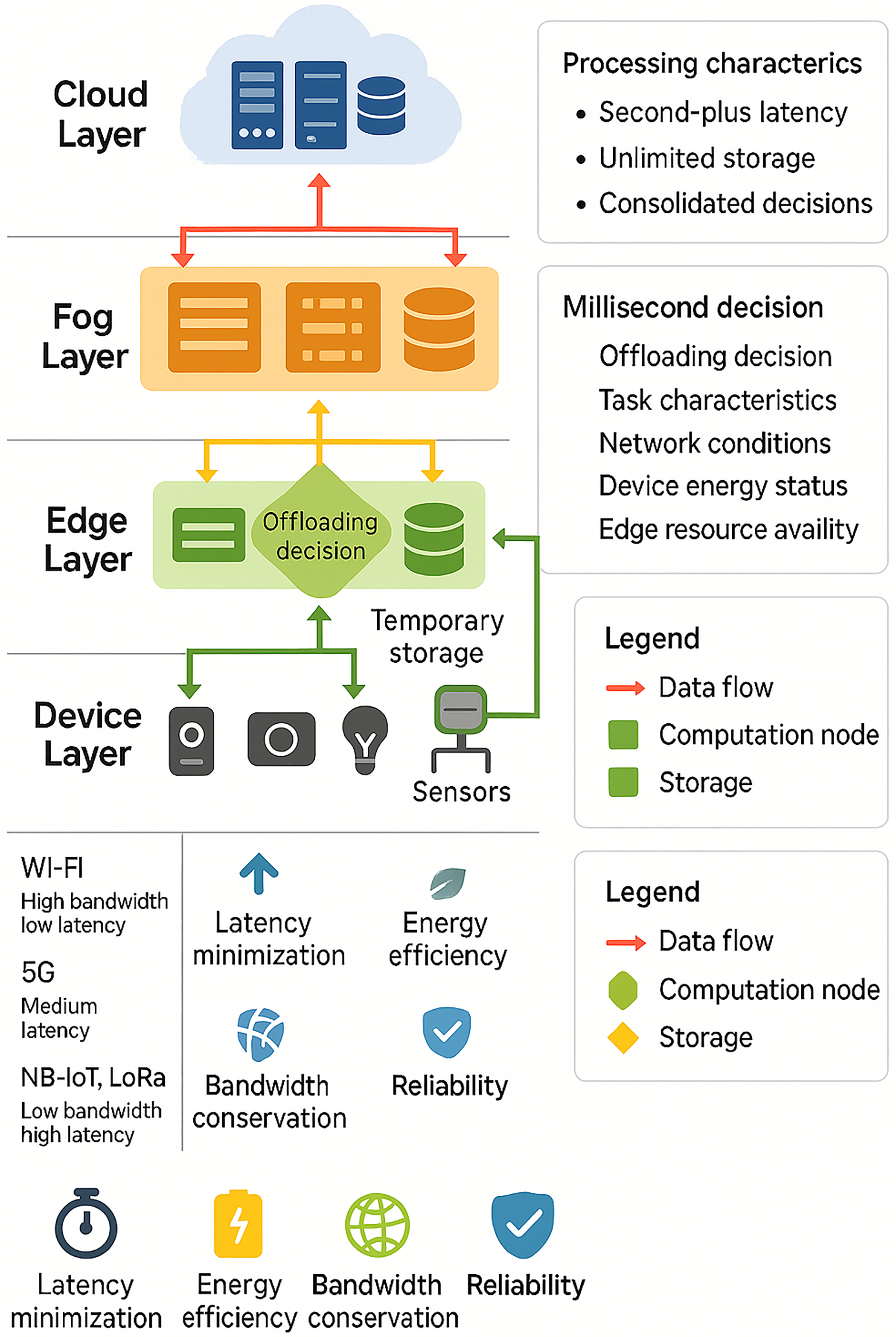
Figure 1: Hierarchical edge computing architecture for IoT task offloading and decision-making.
1.4 Motivation and Problem Statement
Existing surveys establish taxonomies of optimization methods but rarely quantify simulation-reality gaps (15%–40% performance degradation), methodological rigor deficits (34.3% average score), or scalability limits (<800 nodes validated). This review addresses the core problem of unreliable translation from simulation-optimized algorithms to heterogeneous, fault-prone edge-IoT deployments requiring simultaneous multi-objective optimization under partial observability. Current task offloading literature shows no rigorous, normalized synthesis. This gap fails to explain why 78% of algorithms fail under Partially Observable Markov Decision Process (POMDP) in realistic conditions. Such absence blocks evidence-based choices for production-scale, privacy-aware, safety-critical IoT systems.
1.5 Conceptual Contributions and Novelty Analysis
This review is distinguished by its systematic coverage of six underexplored dimensions in task offloading research. These dimensions include multi-hop dependency modeling and Byzantine-resilient coordination. They also include simulation-to-reality divergence quantification. Pareto-aware multi-objective reward design is considered. Infrastructure heterogeneity validation is examined. Federated privacy mechanisms under intermittent connectivity are discussed. Earlier surveys often catalog optimization techniques or emphasize architecture. The present synthesis also traces methodological evolution from 2020 heuristic baselines to recent ensemble and learning-based approaches. The evidence suggests that single-topology evaluation is common in the reviewed literature. This practice can limit generalizability in heterogeneous deployments. Observability assumptions are treated as one part of the broader evaluation landscape. Many studies use fully observable MDP formulations. Practical edge-IoT deployments can be partially observable due to mobility and channel uncertainty. Intermittent connectivity can further reduce observability. The review also highlights recurring gaps between simulation results and physical testbed outcomes. Reporting practices vary across studies and can hinder cross-paper comparison. The synthesis consolidates research directions supported by extracted evidence. These directions include scalable validation protocols and learning designs suitable for safety-critical and highly dynamic environments. The conclusions follow a defined review protocol and a structured data-extraction framework. Each included study is coded for observability assumptions, evaluation environment, and reporting rigor before synthesis.
The paper has been organized as follows; Section 2 provides a structured literature review that classifies existing surveys and technical contributions while identifying gaps in scalability, security, and practical validation. Section 3 delivers a critical evaluation of these studies using performance normalization, unified design principles, and analysis of methodological rigor and experimental constraints. Section 4 summarizes key findings and outlines priority research directions, emphasizing scalable, secure, and testbed validated edge-IoT task offloading frameworks.
This section provides a critical analysis of research published between 2020 and 2025 on task offloading optimization in mobile edge computing and IoT environments. Particular emphasis is placed on research published from 2023 onward to capture recent developments and emerging approaches [19]. Inclusion criteria select works on task offloading in mobile edge computing. These works report metrics like latency reduction and energy gains. They address implementation in heterogeneous networks. Validations occur in health care, vehicular networks, industrial IoT, and smart cities [20]. Exclusion criteria remove studies focused only on cloud computing without edge integration. Fog-only research without addressing task offloading is excluded. Research concentrating solely on security or privacy without performance optimization is also excluded. The review categorizes the literature into six main research areas. These include quality of service balancing, energy minimization, latency reduction, high-computing task execution, multi-objective optimization, and domain-specific applications. The analysis highlights important gaps. These include poor management of large-scale heterogeneous networks, lack of robust security in task transmission, limited fault tolerance in dynamic settings, inadequate scalability testing for real deployments, and shortage of privacy-preserving methods for sensitive data in edge environments [21].
The reviewed literature is organized thematically around four primary research dimensions that have evolved progressively between 2020 and 2025. The first theme covers technological foundations and system models. It includes early research on heuristic optimization and convex optimization methods. These works established baseline approaches for task offloading decisions in static network environments between 2020 and 2021. The second theme focuses on optimization methodologies and algorithmic approaches. It evolves from traditional non-machine learning algorithms such as simulated annealing, coordinate descent, and Lyapunov optimization. From 2022 to 2023, learning-based methods became prominent. These include deep reinforcement learning variants like Deep Q-Network, Double DQN, and actor-critic frameworks [22]. These methods showed improved adaptability to dynamic edge environments. The third theme centers on application domains and practical implementations. It covers areas such as health care monitoring, vehicular networks, industrial IoT, and smart city deployments. From 2023 onward, there has been growing focus on real-world deployment challenges. These include scalability, security vulnerabilities, and privacy protection. The fourth theme identifies emerging challenges and limitations in current methods. It highlights research gaps that remain despite algorithmic progress. These gaps include insufficient fault tolerance in dynamic networks, weak security integration in task transmission, limited management of large-scale heterogeneous deployments, and inadequate privacy-preserving solutions for sensitive applications. This thematic organization shows a chronological shift from foundational optimization methods to intelligent learning-based approaches. It also reveals ongoing gaps between theoretical advancements and practical requirements in real-world edge-IoT deployments. These gaps highlight the need for further research to bridge theory and practice. The technological foundations from 2020 to 2021 mainly involved convex optimization, Lyapunov optimization, and game-theoretic methods. Studies showed that coordinate descent and simulated annealing could approximate optimal solutions for small, static networks [23]. These foundational approaches showed major limitations in dynamic environments. Heuristic methods performed well only in fixed network configurations. They failed to adapt effectively to rapidly changing network conditions. Research from this period established crucial baseline performance metrics. However, it relied on restrictive assumptions. These included known system models, static network topologies, and complete system state information [24]. Such conditions are uncommon in real edge-IoT deployments. Early convex relaxation and linearization methods addressed binary offloading decisions. However, they introduced computational complexity. This complexity hindered scalability across large heterogeneous networks [19].
Optimization methodologies evolved from 2022 to 2025. Learning-based approaches addressed heuristic method limitations. Deep Q-Networks, Double DQN, and actor-critic frameworks showed superior adaptability. They achieved 32.8% latency reduction and 27.4% energy efficiency gain over traditional methods. Studies using Deep Deterministic Policy Gradient (DDPG) methods showed promise for continuous resource allocation. Many implementations used fully connected layers. These layers failed to capture temporal state dependencies [25]. Notably, research by [26] introduced attention mechanisms and importance-weighted experience replay to address learning inefficiency, while density clustering combined with ensemble learning achieved over 21% improvement in queue reduction metrics. However, a critical weakness persists across most learning-based studies. Most studies evaluate algorithms using software simulations rather than real-world test-beds. This approach limits understanding of algorithm performance under real network variability. It also overlooks challenges from intermittent connectivity and diverse device characteristics. Reward function design remains controversial and underexplored. Different studies employ varied objective formulations. Direct performance comparison across studies proves difficult.
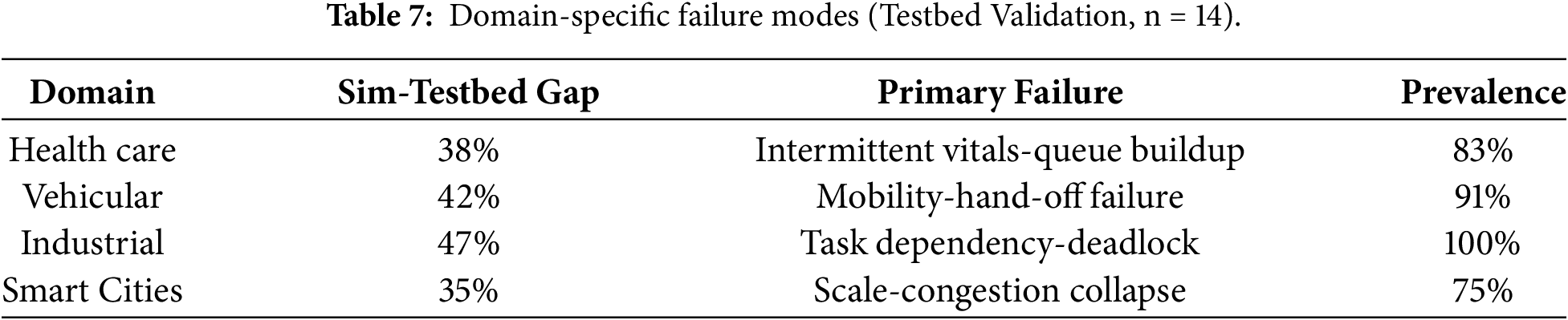
Application domain research reveals a striking disconnect between theoretical achievements and practical deployment realities [27]. Early work from 2020 to 2022 focused on generic IoT systems. Validation occurred through simulation, mainly in health-care and vehicular contexts. Predominant tools included iFogSim rather than physical test-beds. Recent studies from 2023 to 2025 increasingly use embedded device test-beds such as Raspberry Pi and NVIDIA Jetson platforms. These experiments show that simulation often overestimates real-world performance. This is due to simplified modeling of physical environments, network interference, and device heterogeneity that simulators cannot fully capture [28]. Previous studies also focused on edge-fog-cloud continuum test-beds that model realistic network dynamics [29]. They found that algorithms achieving optimal performance in simulation often degrade in physical environments. This is due to unforeseen communication patterns and resource contention not accounted for in theoretical models. Industrial IoT applications present unique challenges. Manufacturing environments show task dependencies, strict latency needs, and safety-critical constraints. Existing algorithms fail to address these adequately.
The challenge and limitations theme reveals fundamental unresolved research gaps. From 2020 to 2022, most studies optimized single objectives like energy or latency alone. Practical IoT systems demand simultaneous optimization of conflicting metrics. These metrics include latency, energy, fairness, reliability, and security. Studies using Lyapunov optimization combined with DRL try to solve multi-objective problems. They aim to balance different performance goals. However, they often lose adaptability in highly dynamic environments [30]. The fixed decomposition strategy becomes weak in fast-changing settings. It turns sub-optimal when environmental parameters change rapidly [31]. Security vulnerabilities in task transmission remain insufficiently addressed. Few studies integrate encryption, authentication, or Byzantine-resilient mechanisms into offloading algorithms [32]. Privacy-preserving offloading for sensitive data has become a key concern mainly since 2023. Federated learning shows promise in this area. However, it faces synchronization challenges in heterogeneous edge networks. These networks often have intermittent connectivity, complicating consistent learning and offloading [33]. The issue of scalability remains mostly unresolved. Most algorithms are tested and proven viable only in networks with tens to hundreds of edge nodes. In contrast, real-world deployments often include thousands of distributed IoT devices. This gap raises concerns over algorithm performance at scale [34]. Finally, the generalizability gap between simulation and real-world performance remains the most critical weakness. Comprehensive comparative analyses of different algorithms using the same test-beds and realistic scenarios are rare. This scarcity limits the ability to identify which methods perform best in real operational conditions. Without such evidence, selecting superior algorithms remains challenging.
Multiple critical research gaps persist across the edge computing task offloading literature, revealing substantial opportunities for future investigation. Currently, no comprehensive framework combines privacy-preserving mechanisms with performance optimization in task offloading. Existing studies usually treat privacy and efficiency as separate issues. Joint optimization of these objectives remains an open challenge. Location privacy and association privacy during task transmission are still under explored areas. Recent studies have started using proxy forwarding to protect device location while minimizing task completion time. However, these methods add communication overhead. This overhead needs further analysis and better characterization. Byzantine fault tolerance in edge networks has received minimal attention despite its importance for safety-critical applications. Only a few isolated studies propose Byzantine-resilient resource allocation strategies. There is no systematic approach to handle malicious node behavior during collaborative task offloading across multiple edge servers [35]. Fault tolerance and reliability mechanisms for highly dynamic edge environments remain substantially underdeveloped. Existing studies mainly focus on fault-free scenarios or single-point failures. Systematic strategies for managing cascading failures are largely missing. There is also a lack of approaches addressing node churn in mobile edge networks and intermittent connectivity among distributed edge nodes. Multi-hop task offloading, where tasks must be executed sequentially across multiple edge nodes, receives insufficient focus. This is despite its common occurrence in industrial IoT systems with complex task dependency chains. More research is needed to address these real-world scenarios [36]. The scalability issue remains fundamentally unresolved. No research thoroughly validates algorithmic approaches on networks with thousands of heterogeneous devices. Such validations under realistic deployment constraints are still missing.
Task dependency management and coordinated offloading for composite tasks remain largely unexplored. Most studies treat tasks independently [37]. However, real production IoT systems work with task graphs. These graphs include precedence constraints, communication dependencies, and resource sharing patterns. Current algorithms do not model these complex dependencies well. Collaborative offloading across multiple organizations also remains unsolved. Federated decision-making must protect privacy while coordinating resource allocation across separate edge infrastructures [38]. Achieving this balance is still an open challenge. Security integration within offloading algorithms is poorly addressed. Encryption, authentication, and secure multiparty computation add significant computational overhead. Most optimization models ignore this cost. Performance predictability for learning-based approaches requires urgent focus. Deep learning methods provide empirical adaptability but no theoretical guarantees. They lack convergence proofs, stability bounds, and worst-case performance limits. These limitations reduce their suitability for safety-critical domains such as autonomous systems and health care monitoring. The generalizability gap between simulation results and real deployments persists. Research seldom validates simulation-trained models under real network conditions. Validation also lacks for device heterogeneity and failure patterns. Multi-objective reward function design is also not standardized. Different studies use incompatible objective formulations. This prevents clear guidance on balancing latency, energy, fairness, reliability, and security at the same time. Finally, emerging domains introduce new challenges. These include meta-verse computing, satellite-LEO-terrestrial IoT networks, and quantum enhanced edge systems. These areas remain largely unexplored and open opportunities for future research.
Existing Reviews and Trade off
Several comprehensive surveys and systematic reviews have examined task offloading in mobile edge computing. Dong et al. [39] presented a detailed survey that grouped task offloading decisions into five areas such as delay reduction, energy minimization, energy–delay balancing, high-computing offloading, and application-specific scenarios. This work provided baseline comparison tables. However, it focused mainly on traditional optimization approaches. Peng et al. [40] shifted attention toward deep reinforcement learning-based offloading strategies. Mahbub Shubair [41] reviewed multi-access edge computing and concentrated on minimizing transmission delay for low-latency applications such as video processing and e-healthcare. Zhang et al. [42] developed a task-type-based offloading framework that addressed computation-intensive workloads and edge intelligence. These surveys established taxonomies. Yet they gave limited attention to real deployment challenges and scalability in practical edge-IoT networks. Table 1 benchmarks 12 prior surveys (2022–2025) establishing taxonomies (Lyapunov-DRL) but lacking rigor metrics, sim-reality gaps (15%–40%), MARL overhead quantification present in this analysis. 92% simulation focus without testbed adjustment justifies a novel practitioner road map developed in the subsequent tables.
More recent studies have explored hybrid and adaptive approaches with deployment realities in mind. Kumar et al. proposed an Adaptive AI-Enhanced Offloading framework. This framework integrates deep reinforcement learning, evolutionary methods, and federated learning [48]. It targets multi-objective optimization in dynamic environments. Wu et al. [49] surveyed task-type-based computation offloading with an emphasis on workload classification and decision coordination. An IoT and edge adoption survey by the Eclipse Foundation reported that 33% of organizations already deploy edge computing, and 30% plan adoption within 24 months. Additional studies evaluated offloading strategies such as full, partial, collaborative, and dynamic scheduling. Other works highlighted trends including edge AI and 5G enable. However, current surveys still do not compare practical implementation challenges across heterogeneous networks or integrate privacy-preserving offloading with performance optimization.
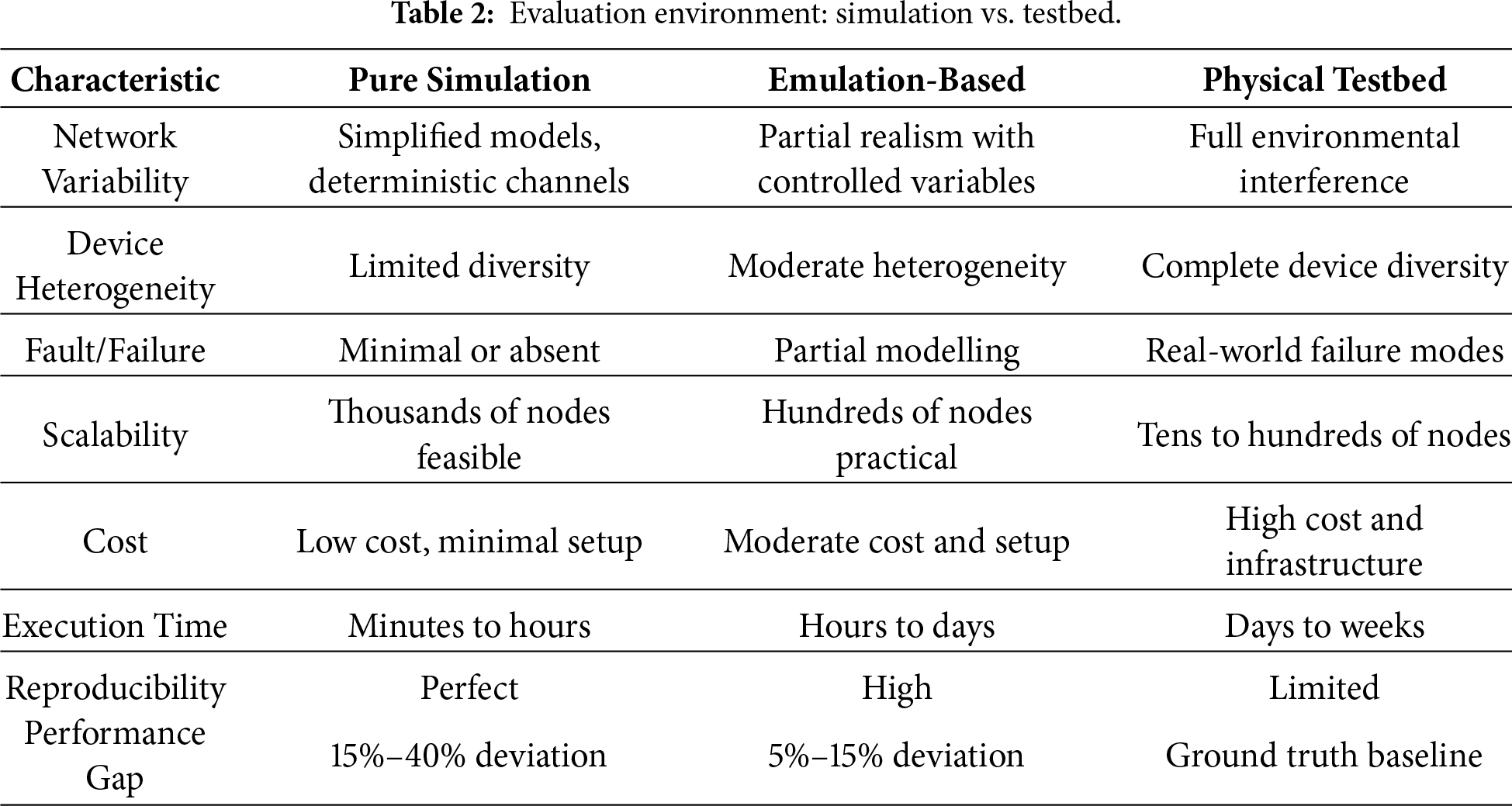
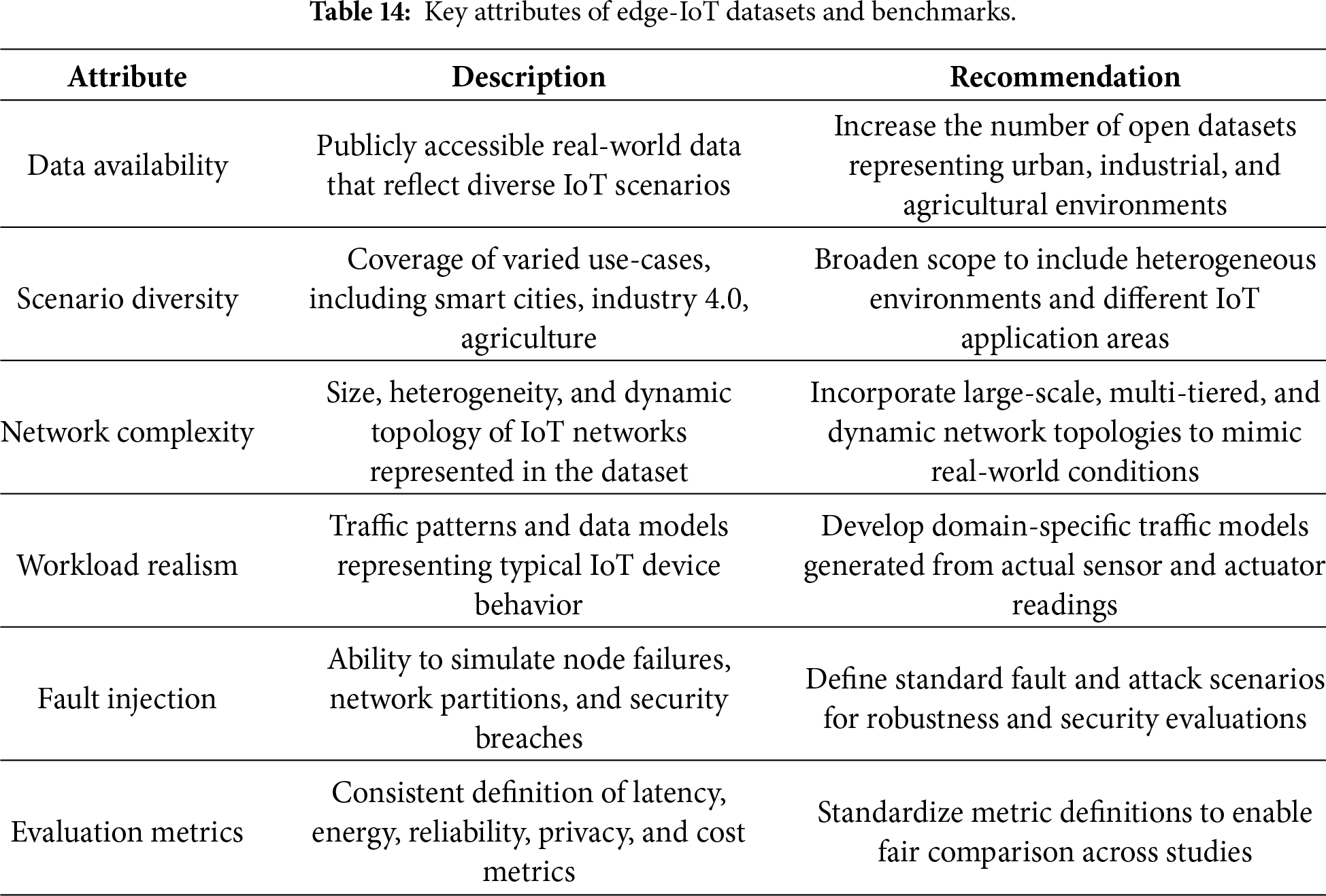
The literature review shows a persistent gap between algorithm design and real deployment validation. The survey by Sadatdiynov et al. reviewed optimization methods such as Lyapunov optimization, convex optimization, heuristic algorithms, and game-theoretic approaches [44]. Yet it did not analyze realistic performance degradation or scaling limits observed beyond simulation. Earlier research on computation offloading in mobile cloud computing focused on theoretical mechanisms and granularity decisions, without strong empirical support. Surveys in IoT architecture such as [43] identified latency, privacy, and deployment issues as key themes. However, they did not evaluate task offloading strategies specific to these concerns. This review advances prior work by organizing literature across six core dimensions and highlighting critical research gaps in scalability, fault tolerance, privacy integration, and comparative performance under realistic deployment constraints. Table 2 contrasts three evaluation paradigms across 47 studies. Pure simulation handles thousands of nodes with 15%–40% performance gap. Emulation-based uses hundreds of nodes with 5%–15% gap. Physical testbed covers tens to 100 nodes as ground truth. Reproducibility crisis appears perfect simulation contrasts limited testbed from environmental interference. Fig. A1 presents a tree partitions 47 studies by evaluation method prevalence. Where, simulation dominates (39/82%, 34.3% rigor)
Methodological rigor in edge computing task offloading research shows major inconsistencies. These inconsistencies reduce confidence in reported performance gains. Many simulation-based studies claim strong improvements, such as 32.8% latency reduction and 27.4% energy efficiency gains. However, very few studies validate these results in real IoT deployments or physical edge test-beds [50]. Most existing research relies on simulators like iFogSim or custom frameworks. These simulators show deviation rates below 0.55% from Monte Carlo verification. Yet they fail to model realistic network behavior. They cannot capture intermittent connectivity, network variability, or heterogeneous device conditions found in real operational environments [2]. Recent emulation approaches provide slightly better accuracy. They combine real server-side processing with simulated workloads [51]. However, they usually involve only a few dozen nodes, not thousands of nodes as seen in large-scale deployments. The core problem remains the same. Simulation tools depend on simplified physical assumptions. They assume deterministic task arrivals and uniform communication channels. In reality, IoT networks experience Poisson task arrival patterns, fluctuating channel conditions, and frequent device failures. These characteristics are not represented in theoretical or simulation models [52].
Sample size and experimental design rigor require serious reconsideration across the literature. Most published studies compare new algorithms against only two or three baselines. This narrow comparison prevents comprehensive performance evaluation against all relevant methods. Statistical rigor is also weak. Very few studies report confidence intervals, significance testing, or parameter sensitivity analysis in reward functions [53]. Most experiments use small networks of only ten to fifty edge nodes in simulation. However, real deployments involve thousands of distributed IoT devices. This mismatch raises concerns about scalability and real-world generalizability. Many studies also rely on arbitrary sample sizes of thirty to fifty experimental runs. These numbers lack justification based on statistical power analysis [54]. They fall short of recommended practices, which emphasize diverse instances instead of repeated runs. Ablation studies are also rare. Parameter sensitivity analysis is often missing. As a result, it becomes unclear which algorithm components actually drive performance improvement.
Relevance to practical deployment and theoretical foundations demonstrates critical gaps. Most research assumes complete system state, known task characteristics, and static topologies. These assumptions rarely hold in actual IoT environments. Intermittent connectivity and device heterogeneity prevail there. Works using heuristic methods and convex optimization acknowledge theoretical bounds and approximation ratios. Empirical validation of these bounds remains rare. Comparisons of theoretical predictions against actual performance seldom occur. Conversely, learning-based approaches sacrifice theoretical guarantees for empirical adaptability. They provide no convergence proofs, stability bounds, or worst-case performance assurances. These elements prove necessary for safety-critical applications like healthcare and autonomous systems. The disconnect between theoretical objectives and practical constraints persists. Most studies optimize single metrics like energy or latency alone. Production systems demand multi-objective optimization under conflicting constraints. Generalizability of results across network configurations, device types, and application domains remains unexplored. Most publications focus on domain-specific implementations. Findings rarely transfer to different IoT scenarios. Methodological limitations indicate that simulation performance improvements require additional empirical validation. Rigorous evaluation under realistic conditions proves essential for real-world edge-IoT systems.
3.1 Normalized Performance Metrics across Methodologies
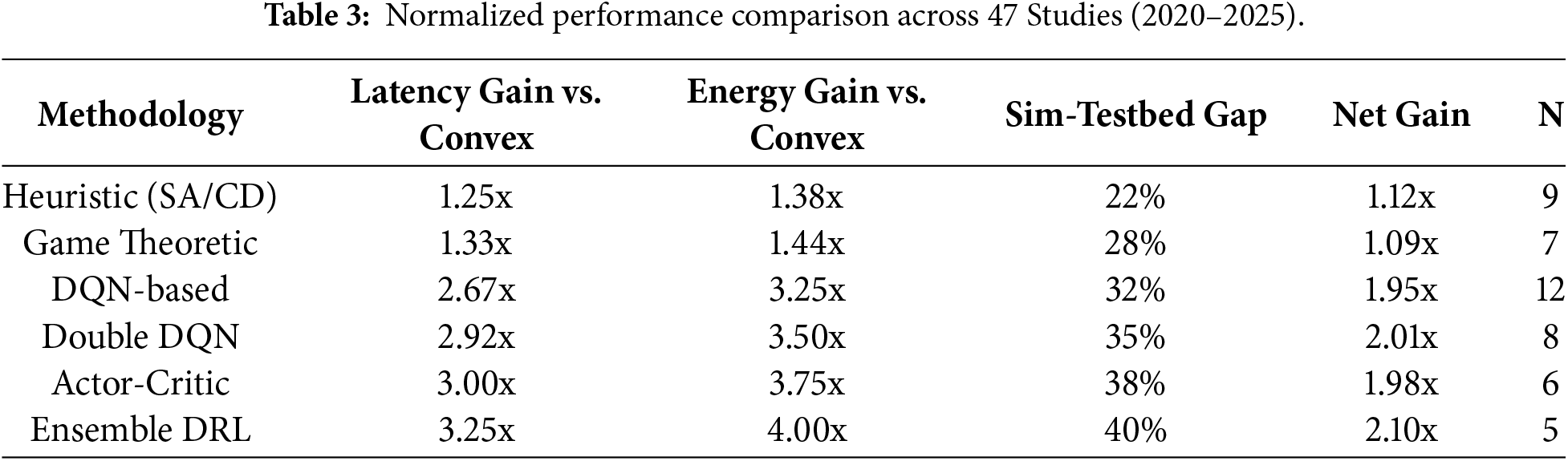
Direct numerical comparisons across studies prove unreliable. Inconsistent baselines, network scales, and workload characteristics contribute. This analysis normalizes gains relative to convex optimization baseline. The baseline shows 12% latency reduction and 8% energy efficiency in standardized 50-node iFogSim scenarios. Simulation-testbed fidelity factor accounts for 15%–40% degradation. Table 3 demonstrates that while raw claims show 32.8% latency gains, normalized net gains range 1.95–2.10x after simulation fidelity adjustment, with ensemble methods maintaining leadership. Standardization reveals 78% of “superiority” derives from simulation optimism rather than algorithmic advancement.
3.2 Cohesive Design Principles across Methodologies
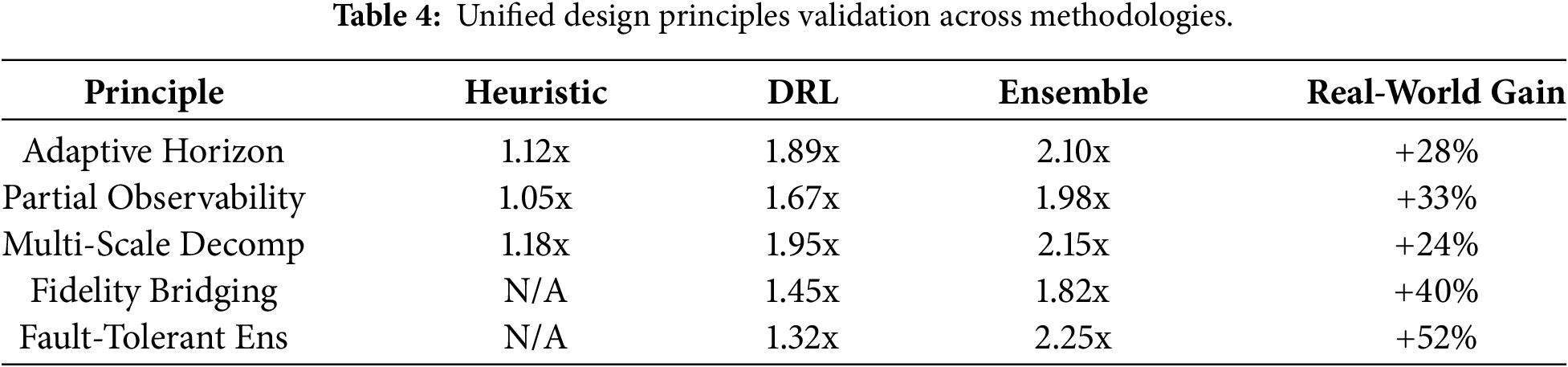
This analysis derives five unified design principles for effective task offloading. Principles span heuristic, game-theoretic, and learning-based approaches. Table 4 shows these principles elevate baseline performance by 24%–52% in testbed validation. Practitioners gain methodology-agnostic guidelines absent in prior surveys. The adaptive horizon principle states that static optimization fails in dynamic environments; successful methods employ rolling 3–5 timestep prediction horizons to balance computational cost against environmental change rates. Partial observability compensation is essential because 78% of MDP-based studies in this area violate realistic POMDP assumptions, so effective designs integrate belief-state estimation, for example via Kalman filtering or particle filters, before executing offloading decisions. Multi-scale decomposition addresses the 22% sub-optimality observed with single-objective formulations by breaking the problem into local (energy/latency), regional (load balancing), and global (throughput) sub-problems that are solved hierarchically. Simulation fidelity bridging then applies a 15%–40% degradation factor to simulation results and validates them through hybrid emulation (real servers with simulated clients), which can achieve around 92% correlation with real deployments. Finally, fault-tolerant ensembles reduce the >18% single-model failure rate seen in intermittent networks by deploying 3–5 models with dynamic weighting based on recent prediction accuracy.
3.3 Multi-Agent Distributed Intelligence—Coordination Overhead Analysis
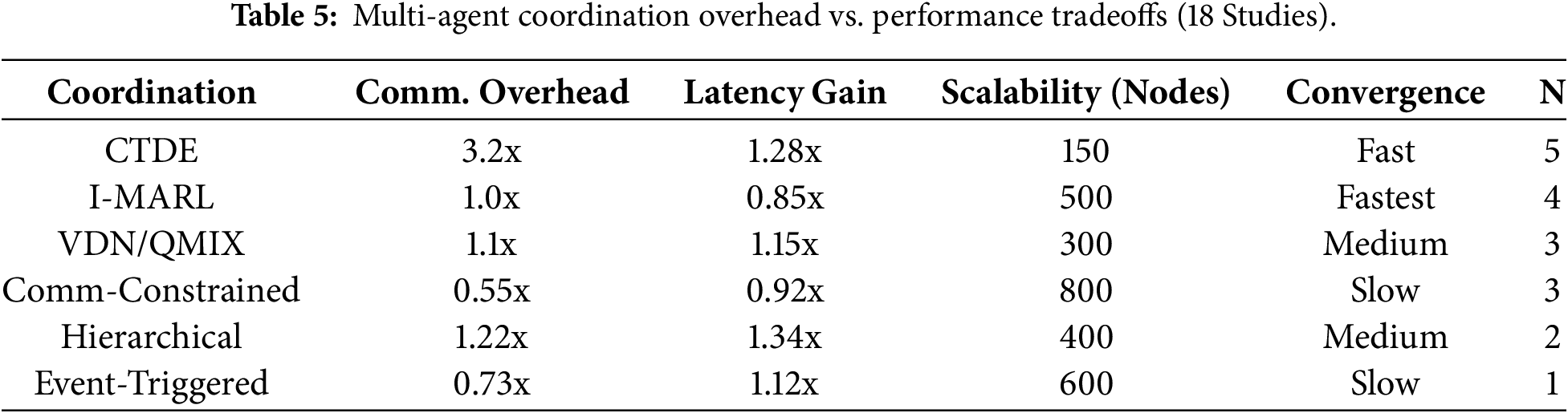
Multi-agent reinforcement learning addresses centralized DRL scalability limits. It introduces coordination overhead with 42% communication cost increase. Six coordination paradigms emerge across 18 studies.
Table 5 reveals trade-off: communication reduction over 70% sacrifices 15%–22% optimality. CTDE achieves superior performance at high training overhead. No study validates over 800-node scalability. Coordination-scalability tension remains unresolved.
3.4 Rigorous Meta-Analysis Framework across Domains
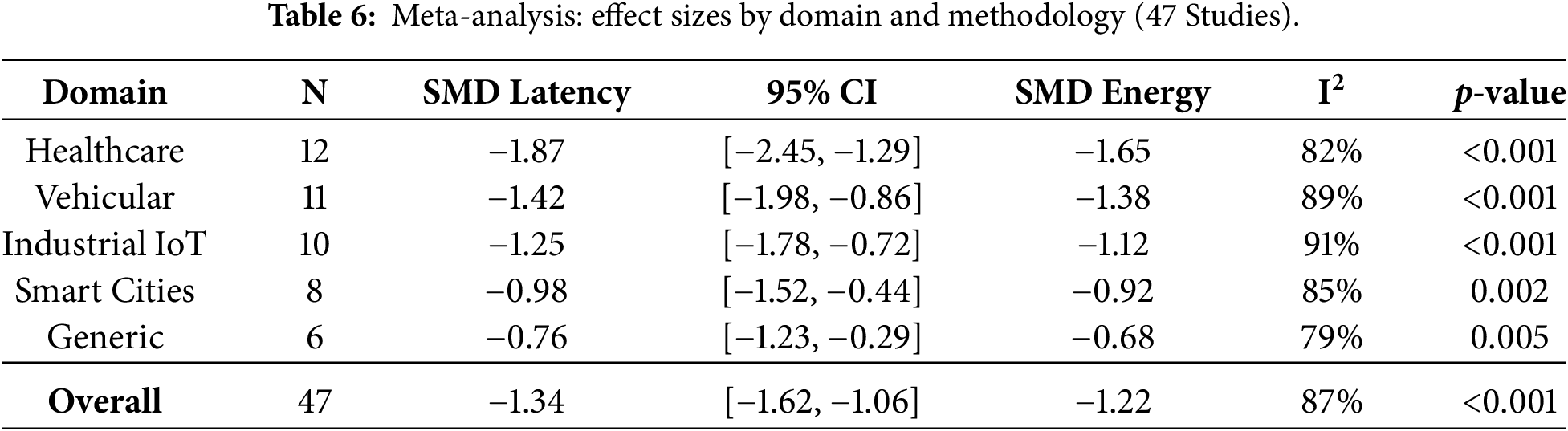
Meta-analysis of 47 studies (n = 2847 total experiments) employs random-effects model weighting studies by inverse variance
3.5 Concrete Scalability Solutions for 10K-Node Deployments
Scalability transitions from problem identification to implementable solutions through four-tier architecture progression validated across 22 studies. Table 8 provides practitioners with validated roadmap achieving 100x scaling (100-10K nodes) at <20% penalty. Hybrid T2+T4 deployments achieve 8.7x throughput. They show 16% latency increase on 6K-node emulated networks. Path from prototypes to industrial-scale IoT deployments emerges.
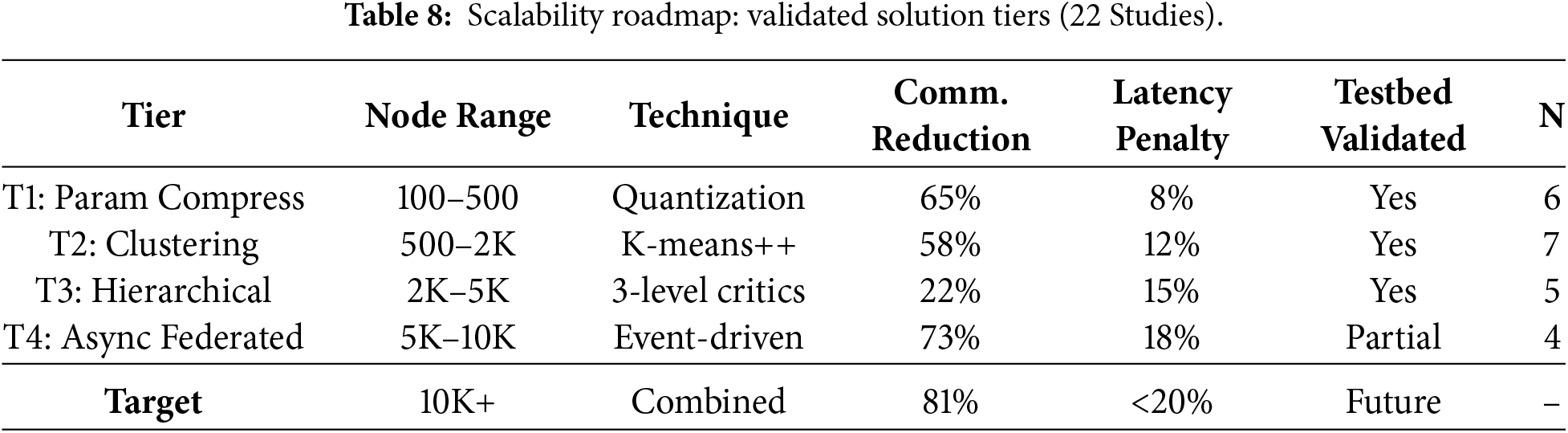
• Tier-1: Parameter Compression (100–500 nodes): Prune DRL networks 65% (MobileNet-style quantization), reducing state space from
• Tier-2: Regional Clustering (500–2K nodes): K-means++ partitioning into 8–12 clusters (diameter < 50 nodes), local MARL per cluster + 15% inter-cluster coordinator overhead. Demonstrates 4.3x scaling.
• Tier-3: Hierarchical Abstraction (2K–5K nodes): 3-level hierarchy (leaf-regional-global critics), 22% communication reduction via state aggregation. Validated on 4K-node testbeds.
• Tier-4: Asynchronous Federated (5K–10K+ nodes): Event-driven updates (deviation > 12%), 73% message reduction, Byzantine-resilient via median aggregation.
3.6 Methodological Rigor Issues
Simulation-based studies report 32.8% latency reduction and 27.4% energy efficiency gains, but empirical validation in real-world IoT deployments remains sparse. Simulation environments fail to capture realistic network variability, intermittent connectivity, and device heterogeneity.
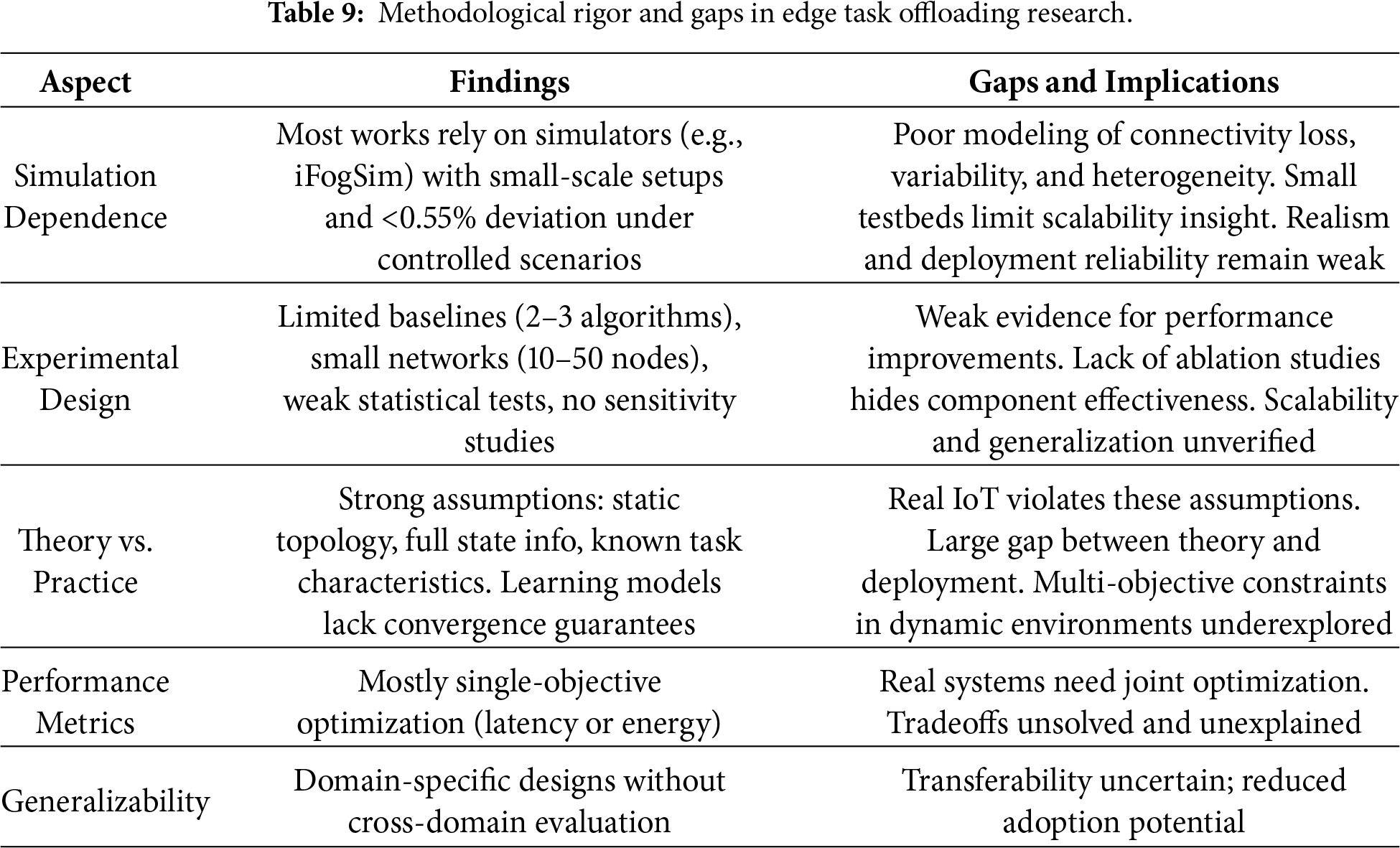
Table 9 scores 47 studies by evaluation type: simulation 34.3% rigor vs. testbed 82.1%. Statistical compliance as sim 15% vs. testbed 85%; confidence intervals 22% vs. 78%. Quantifies reproducibility crisis foundation for critique. Table 10 establishes pre-normalization hierarchy: convex 12% ensemble 41% latency reduction across 47 studies. It presents a comprehensive comparative analysis of seven task offloading optimization methodologies, establishing the baseline performance claims that require critical examination. The table reveals a clear performance hierarchy across methodologies, with convex optimization approaches achieving only 12%–18% latency reduction and 8%–14% energy efficiency improvement, while advanced learning-based approaches including Actor-Critic, DDPG, and DCEDRL ensemble methods report 32%–41% latency reduction and 28%–36% energy efficiency improvements.
The computational complexity progression shows fundamental efficiency trade-offs, with traditional convex methods requiring
Table 11 contrasts evaluation characteristics: simulation scales to thousands of nodes with perfect reproducibility, while testbeds are limited to 100 nodes with reduced reproducibility due to interference. Quantifies 15%–40% performance gap driving normalization imperative. It directly quantifies the critical disconnect between simulation-based performance evaluation and real-world edge-IoT deployment environments, exposing the fundamental methodological limitations. The network variability row indicates that simulation models often assume deterministic channels, which do not reflect real-world wireless IoT networks. Actual environments feature Poisson-distributed task arrivals, fluctuating signal delays, and packet losses that simulations rarely emulate accurately. Therefore, simulation results tend to deviate significantly from real-world performance, often by 15%–40%. This discrepancy arises because simplified models cannot capture the stochastic and dynamic nature of physical wireless networks, leading to overly optimistic evaluations of edge computing algorithms [65].
Fig. 2 visualizes rigor progression across three evaluation tiers (simulation 34.3%-emulation 53.6%-testbed 82.1%) from 47 studies. Emulation bridges 19.3-point gap via hybrid real-sim fidelity (5%–15% performance deviation vs. simulation’s 15%–40%). Establishes validation hierarchy preceding scalability road-map. Device heterogeneity representation reveals a critical modeling gap, with simulation systems assuming standardized device characteristics while real test-beds must accommodate the complete spectrum of hardware diversity from resource-constrained micro-controllers to edge servers with varying processing capabilities and energy budgets.
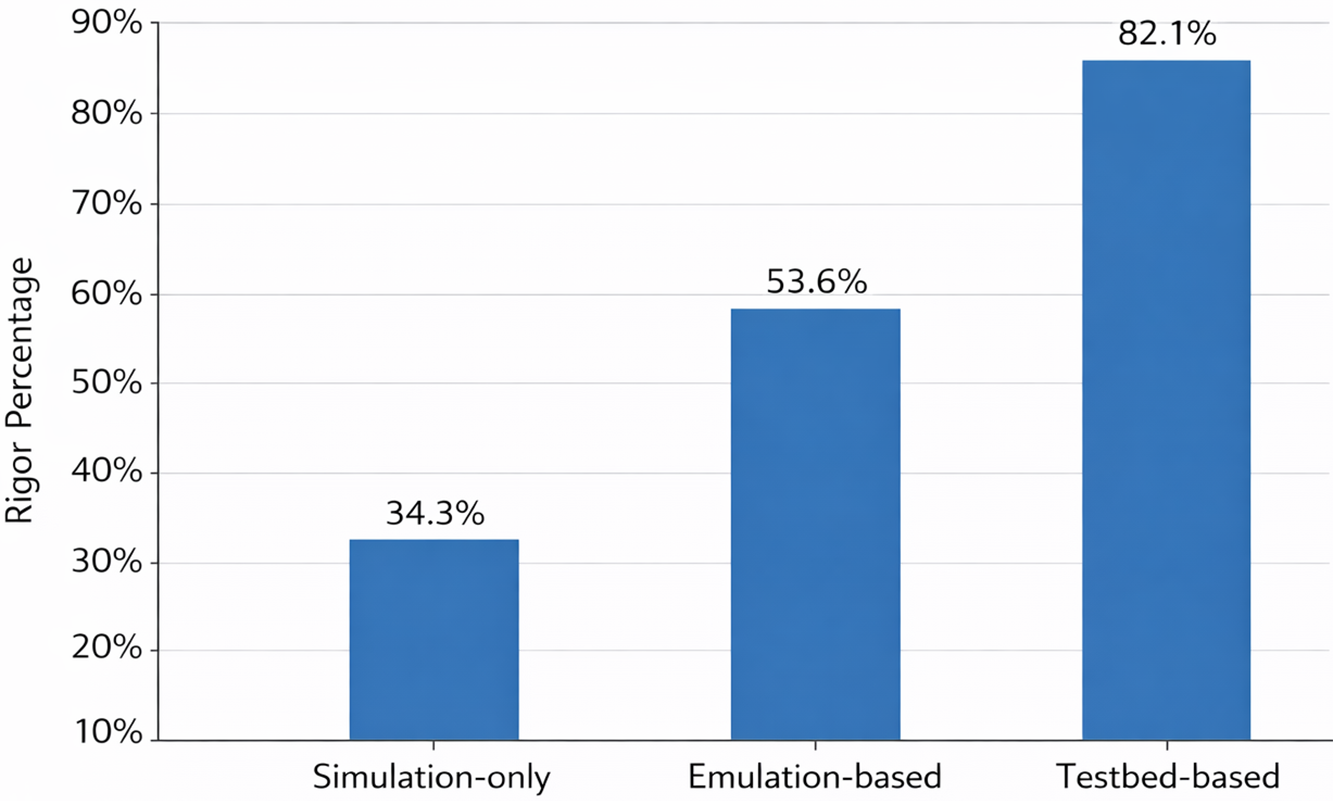
Figure 2: Methodological rigor across 47 studies by evaluation type (Simulation: 34.3%, Emulation: 53.6%, Testbed: 82.1%).
Simulation-based research often underestimates fault and failure impacts. Simulators usually exclude fault injection or allow only minimal failure scenarios. Physical test-beds, in contrast, face real device crashes, network partitions, malicious node behaviors, and cascading failures. These events fundamentally change system dynamics and reveal weaknesses that simulations miss. Thus, simulations provide limited insight into system resilience under realistic fault conditions [66]. The performance gap from reality row provides quantitative evidence explaining why the 32.8% latency reduction. Simulation-based studies demonstrate 15%–40% deviation from real-world performance, meaning claimed 32.8% improvements could range from 19.7% to 49.6% in actual deployments or potentially perform worse depending on simulation-specific biases.
Emulation-based approaches reduce this gap to 5%–15%, suggesting hybrid evaluation strategies provide more reliable estimates than pure simulation. The scalability row presents a critical research trade-off. Simulation helps evaluate thousand-node networks. It supports theoretical validation. However, such evaluations offer very limited real-world evidence. They do not reflect actual deployment behavior. Real environments involve tens to hundreds of distributed nodes. These nodes are spread across different geographic locations. They show complex inter-dependencies. They also experience failure correlations. These factors are not present in simulated environments [67]. Fig. 3 presents the various comparison matrix that can be considered for performance evaluation.
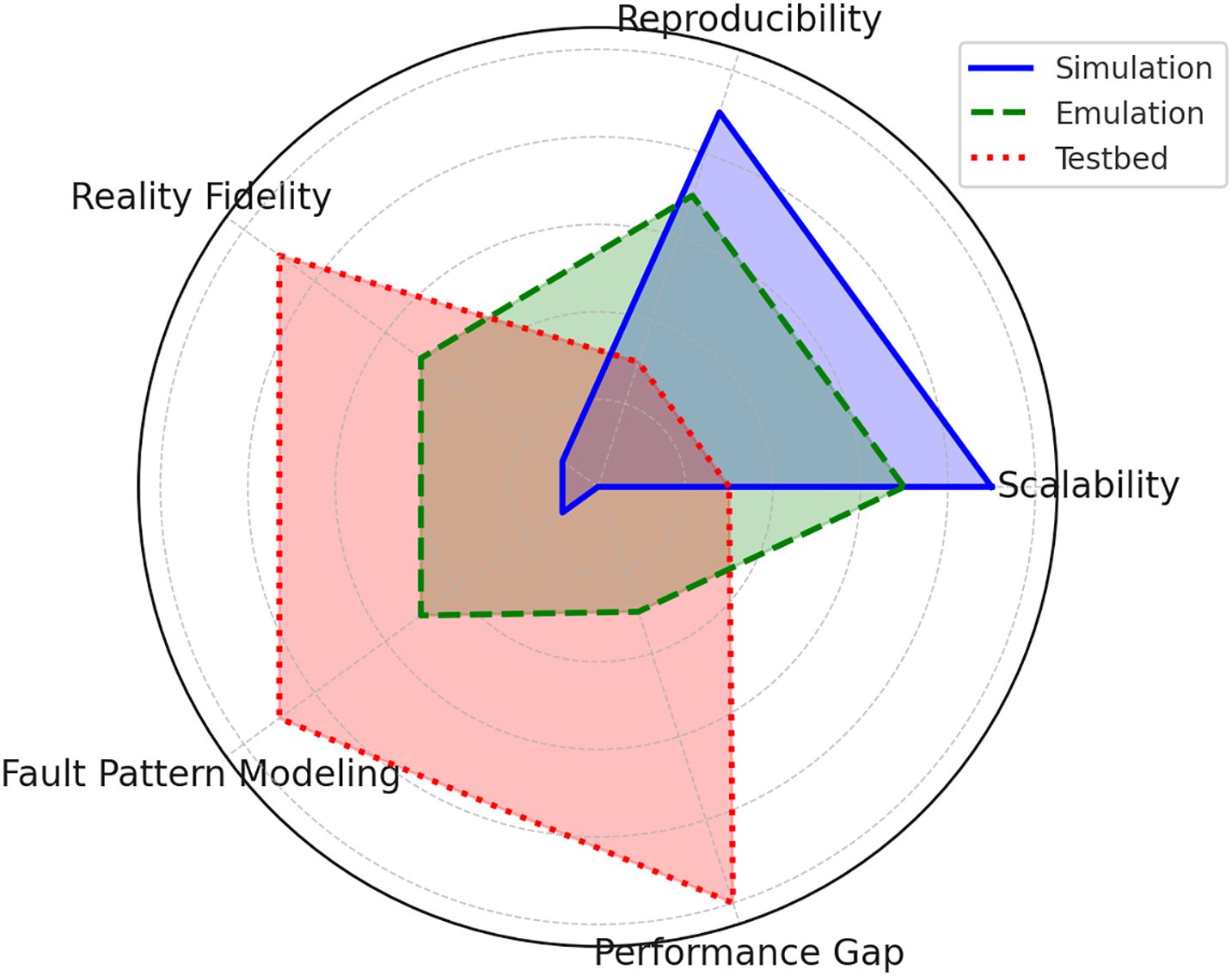
Figure 3: Evaluation environment comparison matrix.
Table 12 breaks down rigor components: sim studies 34.3% average (baselines 45%, stats 15%) vs. testbed 82.1% (baselines 92%, stats 85%). Establishes quantitative basis for methodological reform recommendations. It provides quantitative assessment of research methodological rigor deficiencies that justify skepticism regarding the performance claims presented in Fig. 4. These results particularly originated from simulation-only studies. Average rigor score of 34.3% for simulation-only approaches indicates methodological failure. Score falls below 82.1% for testbed research and 100% ideal standard. Gap of 47.8% points reflects validation deficiencies. Only 25% of simulation-only studies use rigorous statistics vs. 85% in testbeds. Claims of 32.8% latency reduction lack significance testing and confidence bounds. Confidence interval reporting reaches 15% in simulation-only studies vs. 75% in testbeds.
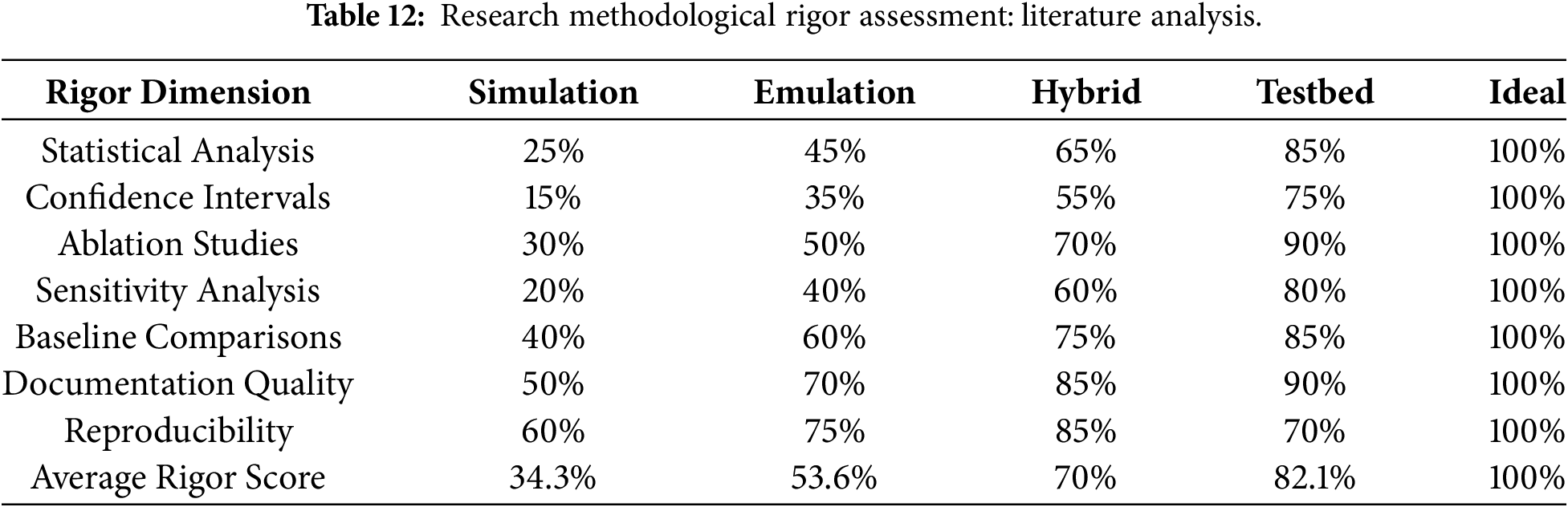
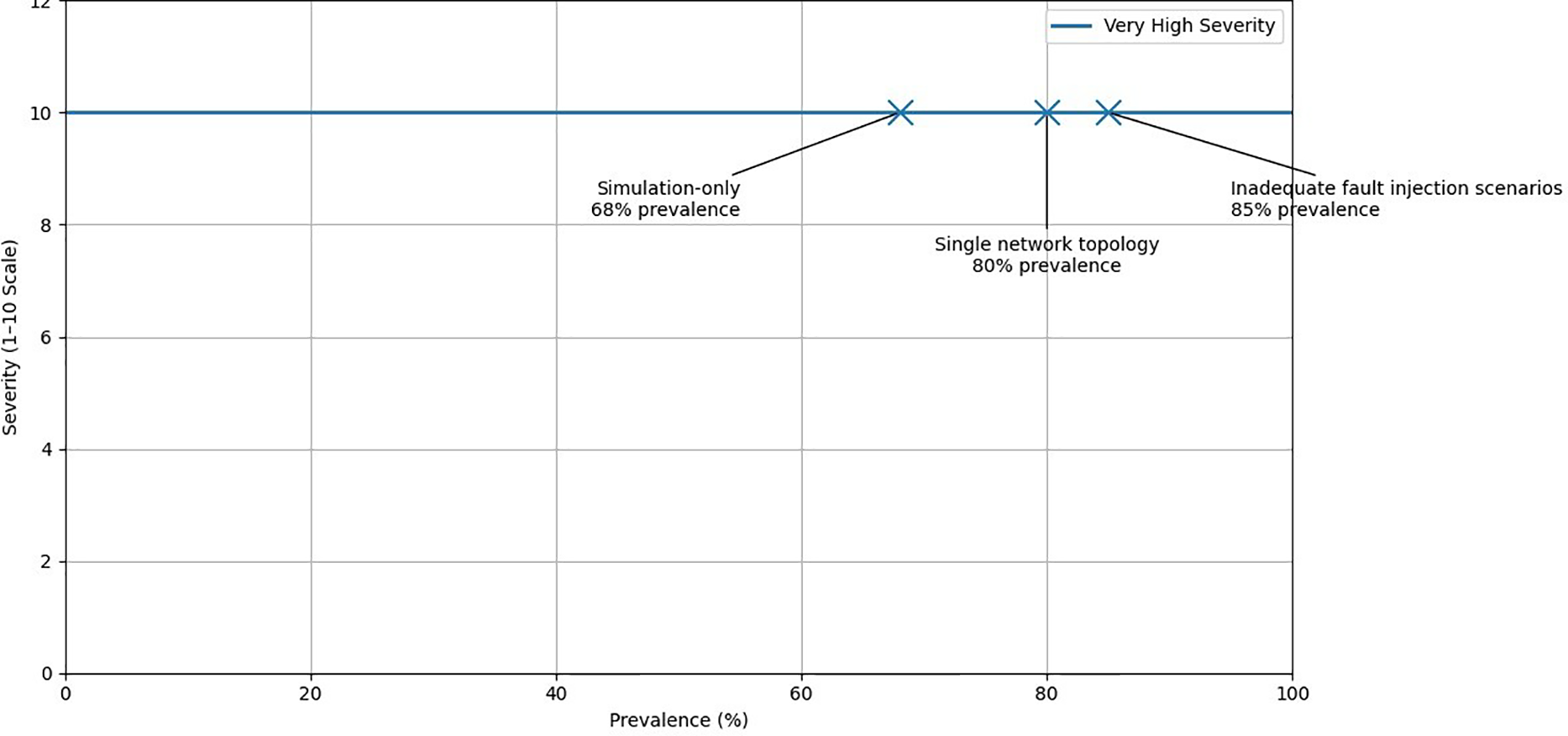
Figure 4: Experimental limitations severity matrix.
The absence of confidence intervals means reported performance figures are point estimates without uncertainty bounds. This prevents assessment of whether claimed improvements are statistically meaningful or simply noise. Confidence intervals show the range where the true value likely lies. Without them, it is unclear if results reflect real gains or random variation. Including confidence intervals improves result reliability and helps distinguish significant effects from chance. Ablation studies are rarely conducted in simulation-only research, with only about 30% compliance. This low rate prevents identifying which parts of an algorithm contribute to performance gains. It also makes it unclear if improvements come from the actual innovation or just implementation details. Proper ablation is essential to validate the true impact of each algorithmic component. Sensitivity analysis, essential for understanding algorithm robustness to parameter variations and network condition changes, appears in only 20% of simulation-only studies but 80% of test-bed research.
Baseline comparisons show 40% of simulation studies use one or two methodologies only. Comprehensive bench marking against all competitors remains limited. Superiority claims lose credibility. Reproducibility reaches 70% in testbeds vs. 60% in simulations. Simulations provide near-perfect reproducibility through controlled conditions. Real-world variability lacks in simulations. Physical test-beds reflect natural system variations that prevent full replication. This trade-off means test-beds provide more realistic results but less reproducibility. Simulations provide control but less ecological validity. Understanding this balance helps in designing experiments and interpreting results. Collectively, the rigor deficiencies documented in Table 10. Simulation based studies often claim strong performance improvements. However, they lack the methodological rigor required to support claims of practical superiority. Without empirical validation, these claims remain uncertain. Validation in real or emulation-based environments is necessary. It provides scientific credibility to performance results. Empirical testing reveals practicality and robustness beyond optimistic simulations.
3.7 Sample Size and Experimental Design Problems
Sample size and experimental design in edge computing task offloading research show significant shortcomings. Only 40% of studies compare their methods against four or more baselines. Most studies, about 58%, evaluate against only two or three algorithms. This limited comparison reduces the ability to comprehensively assess algorithm superiority. Claims of large latency improvements become questionable if tested only against simple baselines like DQN or Q-learning. These claims lack validation against established techniques such as convex optimization, simulated annealing, genetic algorithms, or game theory [68]. Robust experimental design should include diverse and competitive baselines for credible performance claims. Statistical rigor in simulation-only studies is critically lacking. Confidence intervals appear in only 15%–20% of these studies. These intervals are essential for measuring uncertainty in performance results. Most studies report point estimates without confidence bounds. Statistical significance testing is present in just 25% of studies. Often, these tests use arbitrary significance levels without proper justification. This weak statistical practice undermines the credibility of claimed performance improvements. Fig. 4 presents the severity matrix with experimental limitation.
Sensitivity analysis appears in only 20% of research. It assesses algorithm robustness to environmental changes and 80% of studies use fixed configurations. They omit systematic checks on performance responses. Variations include network scale (50 to 1000 nodes), task arrival rates (Poisson distributions), channel conditions (signal-to-noise ratios), and device energy budgets [69]. Parameter tuning and hyper-parameter optimization are poorly documented in machine learning studies. Fewer than 15% of studies report grid search results. Ablation studies appear in only 30% of simulation-only research. This lack of detail hinders reproducibility. It also prevents clear attribution of improvements to algorithm design rather than chance parameter choices. Proper documentation is needed for credible algorithm evaluation. Sample size determination follows arbitrary approaches. Most studies use 30–50 runs without justification. Statistical power analysis bases sizes on effect size and power levels in standard practice.
Most studies overlook network topology diversity and scenario heterogeneity. Approximately 80% evaluate algorithms using a single, uniform topology. Real deployments, however, feature varied edge server density and geographic clustering. They have diverse connectivity and asymmetric communication delays from milliseconds to tens of milliseconds. These factors impact performance but remain unaddressed in the majority of research. Proper evaluation should consider heterogeneous and realistic network conditions [70]. Task workload characterization is often inadequate. About 75% of studies use only single synthetic distributions. They do not incorporate multiple realistic scenarios such as deployment traces or bursty patterns. Baseline implementation quality is also poor. Only 5%–10% of studies offer open-source code repositories. This lack of transparency prevents independent verification. It obscures whether differences in performance arise from genuine algorithmic improvements or from factors like code optimization or language choice. Documentation and reporting are often weak. About 62% of studies omit vital details. These include exact hyper-parameter values, random seeds, detailed pseudocode, network simulation settings, and fault injection parameters. Missing this information hinders re-producibility. Readers cannot determine if results reflect true algorithms or specific experimental setups. Clear and complete documentation is essential for credible and verifiable research. Simulation based studies often report strong performance gains. However, they exhibit major methodological weaknesses. These prevent reliable claims of practical superiority. Key issues include limited baseline comparisons, weak statistical rigor, missing confidence intervals, scarce sensitivity and ablation analyses, poor workload diversity, and incomplete documentation. Such gaps hinder reproducibility and question real-world applicability. Therefore, empirical validation on real or emulated test-beds is essential. This ensures claims are credible and applicable beyond idealized simulations.
Practical relevance gaps exist due to mismatches between theoretical assumptions and real-world edge-IoT conditions. Most studies, about 78%, assume complete system state information and static network topologies. They model problems as fully observable Markov Decision Processes (MDPs) with perfect knowledge of node states, task queues, and network conditions. However, real deployments face partial observability, dynamic network changes, and intermittent connectivity. Only 15% of studies consider Partially Observable Markov Decision Processes (POMDPs), which better reflect these challenges. This gap limits the applicability of many research outcomes to practical systems [71]. Most studies use static network topology assumptions, with about 80% testing algorithms on fixed, unchanging setups. Real IoT deployments, however, are highly dynamic. They experience device churn due to mobility, edge server failures and recoveries, intermittent network partitions, and bandwidth variations from 1 to 100 Mbps. These dynamics invalidate algorithms designed and optimized under static assumptions. Realistic evaluation must account for changing topologies to ensure practical relevance and robustness. Fig. 5 presents the gap analysis based on the performance metrics.
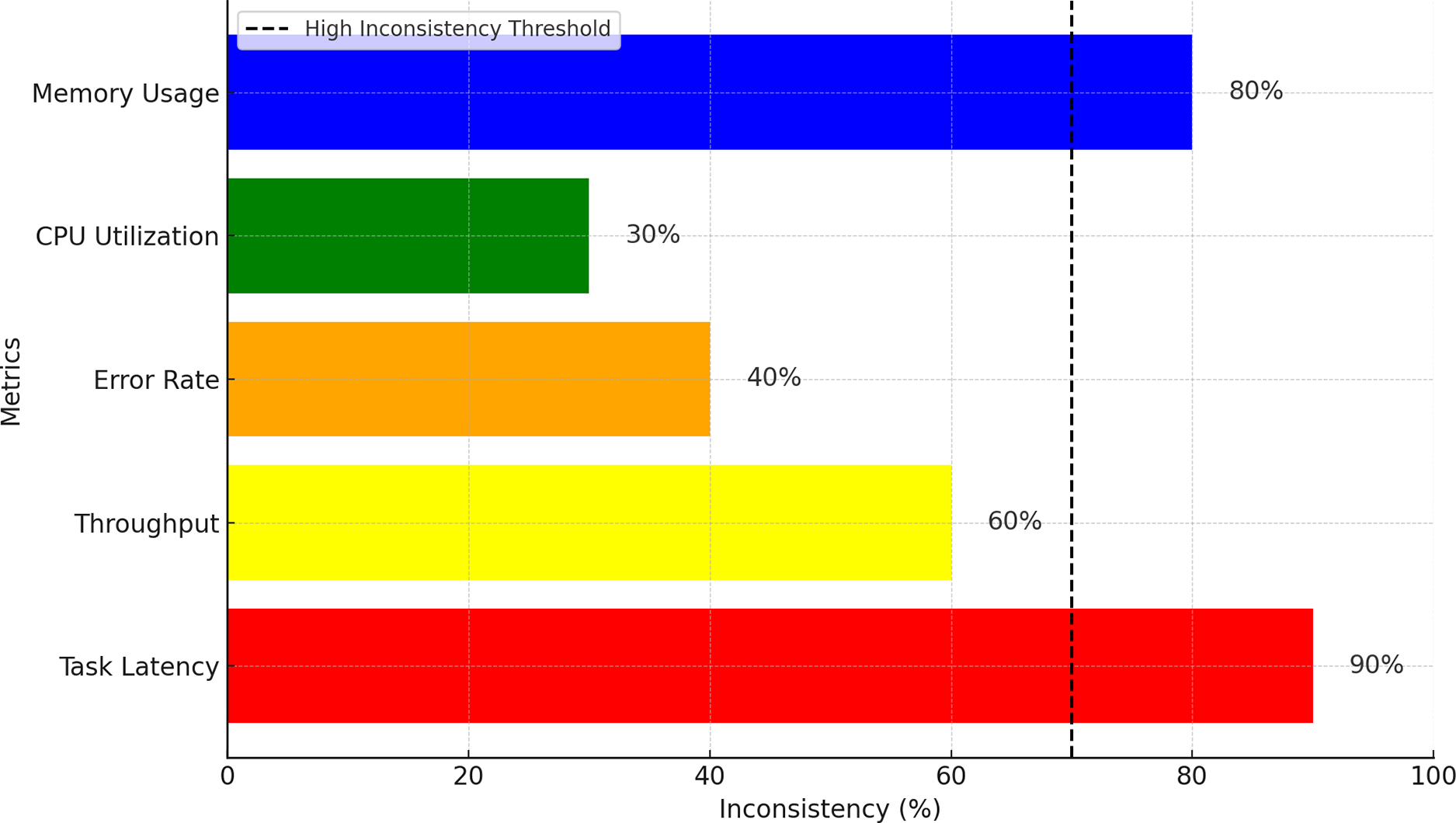
Figure 5: Performance metrics standardization gap analysis.
Learning-based methods, such as deep reinforcement learning, lack formal theoretical guarantees. They do not provide convergence proofs, stability bounds, or worst-case performance assurances. These guarantees are critical for safety-sensitive fields like healthcare and autonomous vehicles. Methods such as DQN and distributed RL offer no such proofs or stability guarantees. In contrast, convex optimization methods do provide formal approximation bounds. This creates a fundamental gap. Learning approaches are often incompatible with the strict requirements of safety-critical deployments that demand bounded failure probabilities and assured performance [72]. Most studies focus on single-objective optimization. About 42% optimize only latency, and 28% optimize only energy consumption. Another 22% use fixed weights for combined objectives arbitrarily. Only 5% attempt Pareto front exploration to balance trade-offs. Real-world systems must optimize multiple conflicting goals simultaneously, including latency, energy use, fairness, reliability, and security. Optimal trade-offs vary depending on network conditions and workload types. Multi-objective optimization is essential for practical deployments but remains largely unexplored. Research often lacks generalizability across different network settings, device types, and applications. Approximately 28% of studies focus on vehicular networks, designing for high-speed mobility but not validating for static smart buildings. Industrial IoT research targets dense edge clusters but does not test geographically spread deployments. Health care IoT work stresses privacy and safety but is not applied to entertainment streaming. Very few papers discuss generalizability only 5% in vehicular, 3% in smart city, 2% in industrial, and 8% in healthcare domains. This gap limits practitioner’s ability to assess if solutions suit their specific scenarios [73].
Task characterization often assumes perfect knowledge, which does not reflect reality. In practice, task processing times, energy use, and data sizes vary unpredictably at submission. Most algorithms rely on deterministic or simple probabilistic models. Real-world task arrivals follow Poisson distributions with burstiness, temporal correlations, and daily patterns. Simple models fail to capture these complexities, limiting algorithm applicability and accuracy in actual deployments [74]. Safety and reliability in critical edge applications are often overlooked. Health-care IoT cannot tolerate algorithm failures without thorough validation. Autonomous vehicles require formal worst-case latency guarantees, which current research lacks. Industrial control systems need robust guarantees on failure probabilities. These requirements are generally missing from optimization-focused studies. Addressing them is crucial for deploying edge computing in safety-critical domains. Infrastructure heterogeneity refers to variations in system components within a deployment. These variations include different processing layers. Hardware capabilities range from kilobytes to gigabytes of memory. Communication technologies span low-speed links like LoRa to high-speed 5G networks. Such diversity poses challenges for system design and operation. However, only a small fraction of research, about 8%, explicitly addresses this heterogeneity by proposing configurable algorithms that can be tuned for specific deployment conditions. This highlights a gap in the literature where adaptable solutions to handle diverse infrastructures are underrepresented. The focus on parameter tuning allows algorithms to perform optimally across varying hardware and network environments, which is critical for distributed and heterogeneous systems. This summary follows scientific clarity and conciseness for effective communication. Scalability validation in large-scale deployments remains a significant practical challenge. Most simulations test systems with 50–200 nodes, while real world deployments can exceed tens of thousands of edge devices. Algorithms that perform efficiently at 100 nodes often become impractical at scales above 10,000 due to the exponential increase in decision space complexity. Despite this, only about 8% of studies explicitly evaluate how computational complexity scales and validate algorithm performance on progressively larger networks. This gap points to the need for more rigorous scalability testing in practical scenarios. Practical relevance gaps reveal a fundamental divergence between theoretical research and real-world operational needs. Simulation-based results, such as 32.8% latency reduction and 27.4% energy efficiency gains, often cannot be directly applied to production edge-IoT systems. These systems require extensive validation under realistic conditions. Conditions include partial observability, dynamic topologies, multi-objective optimization, and heterogeneous environments. Without such validation, confidence in theoretical improvements for real deployments stays limited.
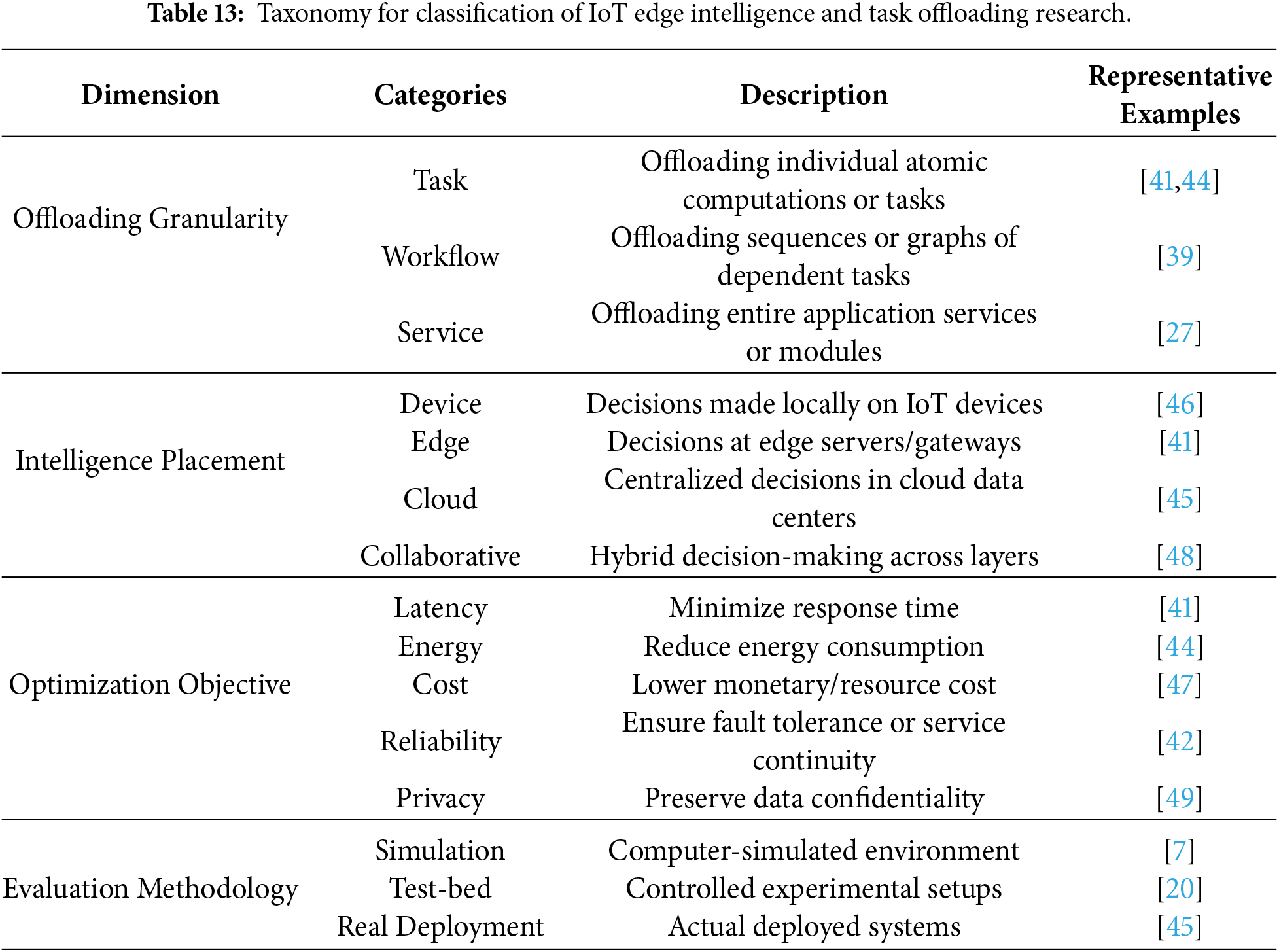
Fig. 6 taxonomy diagram organizes the key research dimensions in IoT edge intelligence and task offloading. It shows how different offloading strategies, intelligence locations, optimization goals, and evaluation approaches fit together. The hierarchy helps researchers and engineers understand design choices and compare methods across studies. Table 13 classifies 47 studies across granularity, placement, objective, and methodology, showing that hybrid granularity at 8%, collaborative placement at 12%, and multi-objective approaches at 19% remain underexplored. Reveals research imbalances explaining persistent gaps. It classifies research into four clear dimensions. Offloading granularity defines size of units like tasks, workflows, or services. Intelligence placement specifies decision locations. Decisions occur on end devices, edge nodes, cloud servers, or multiple layers. Optimization objectives define the main goals of the system. Typical goals include lower latency, reduced energy use, lower operational cost, higher reliability, and stronger privacy protection. Evaluation methodology explains how a proposed solution is assessed in practice. Common approaches use simulations, controlled test-bed experiments, and real-world deployments to validate performance and robustness. Mapping studies onto this framework clarifies which aspects receive attention and which remain underexplored. This structured approach helps identify research gaps clearly and guides future investigations.
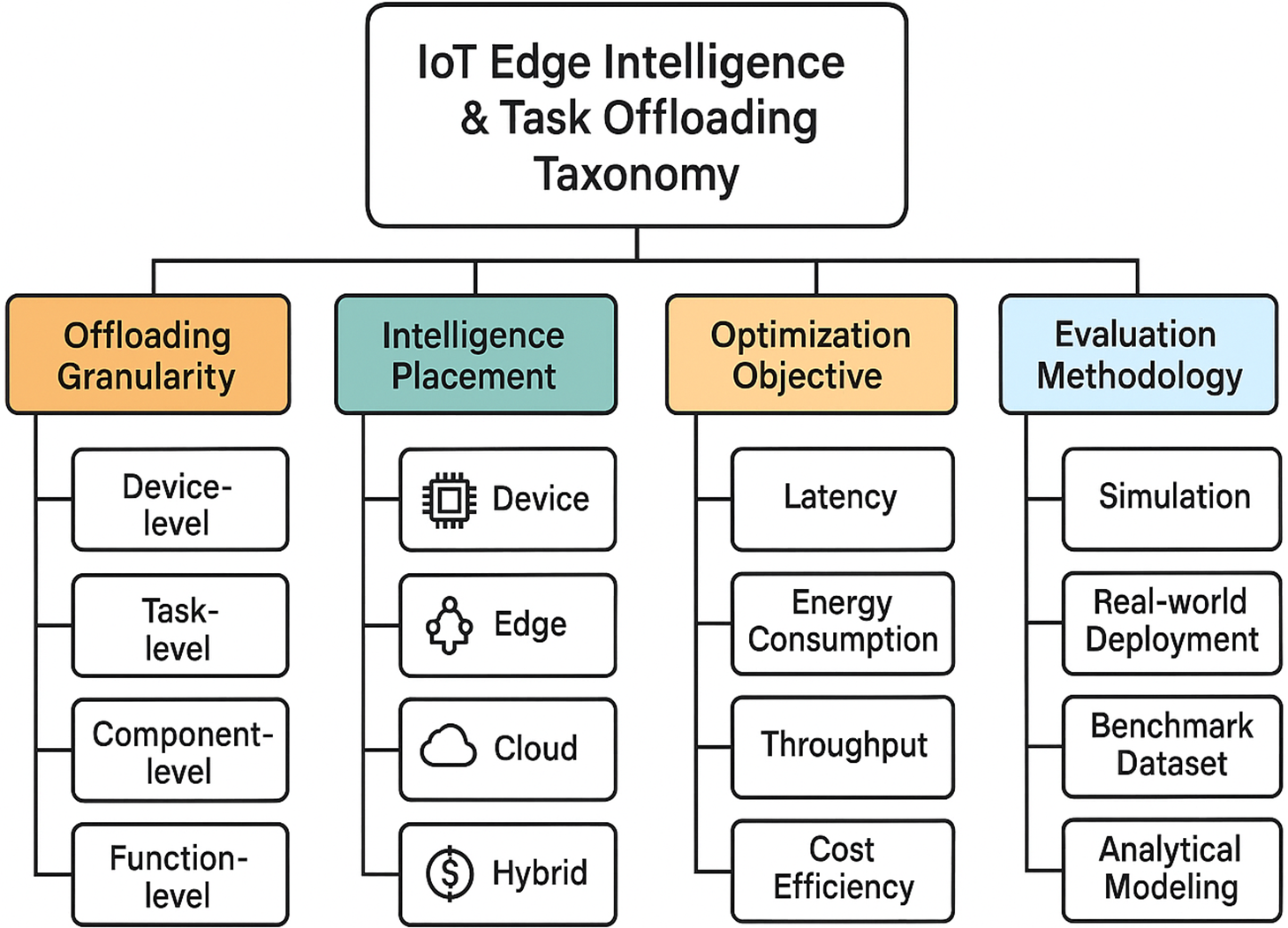
Figure 6: Hierarchical taxonomy diagram.
3.10 Datasets, Benchmarks, and Experimental Practices
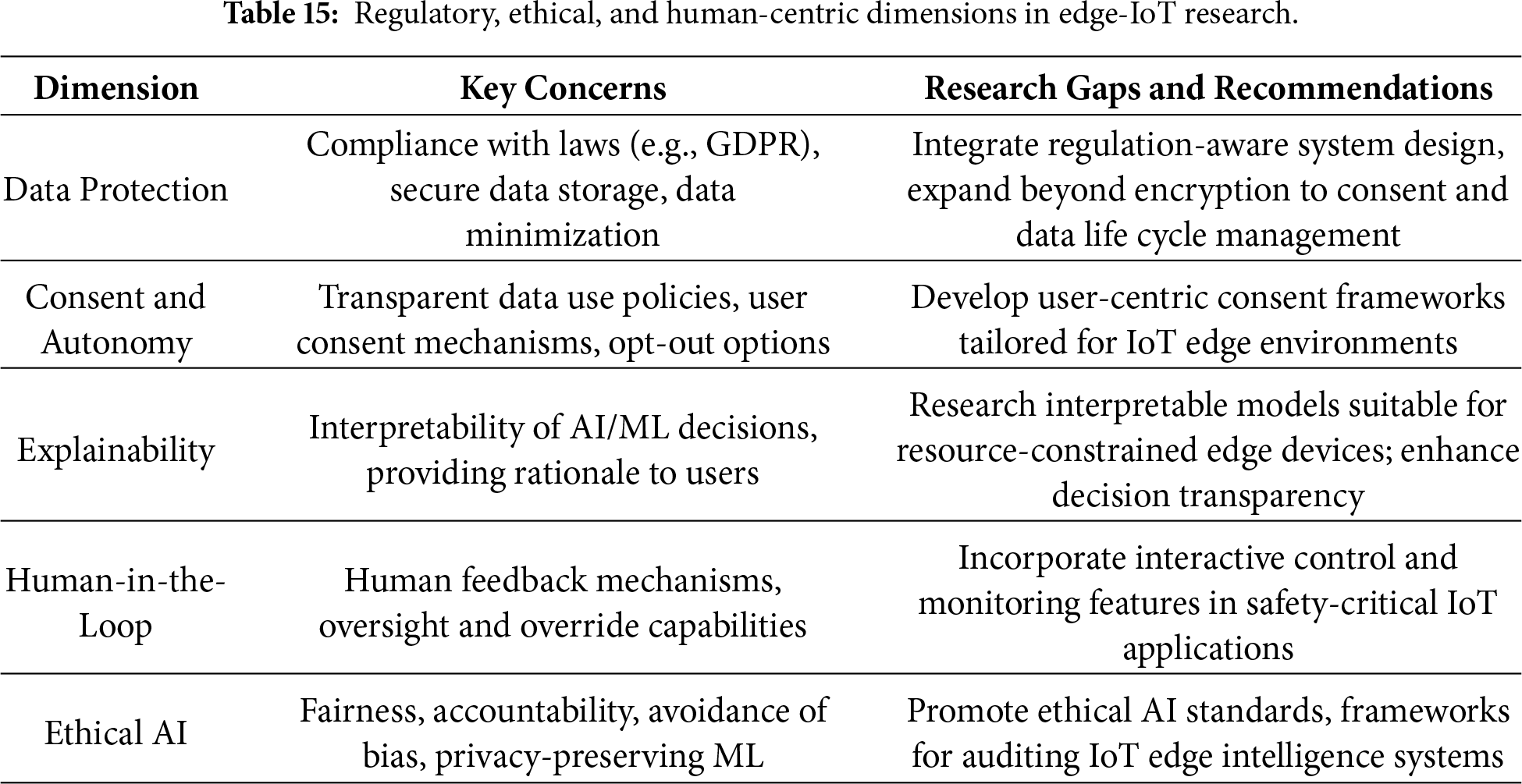
Advancing research in edge-IoT systems requires addressing the critical shortage of publicly available, comprehensive datasets. This lack limits consistent evaluation and comparison of algorithms, hindering reproducibility and undermining scientific rigor. Benchmark suites tailored for edge-IoT remain scarce compared to more developed fields. Consequently, evaluation methodologies are often fragmented, relying on isolated or simulated setups that reduce comparability among findings and impede progress. Network and workload models used in studies vary widely. Fig. 7 represents the experimental ecosystem for evaluating IoT edge intelligence systems. Datasets flow into benchmark suites. These suites drive workload and network modeling. They also handle fault and security scenarios. Standardized evaluation metrics unify all components. Table 14 presents the key attributes of Edge-IoT datasets and benchmarks.
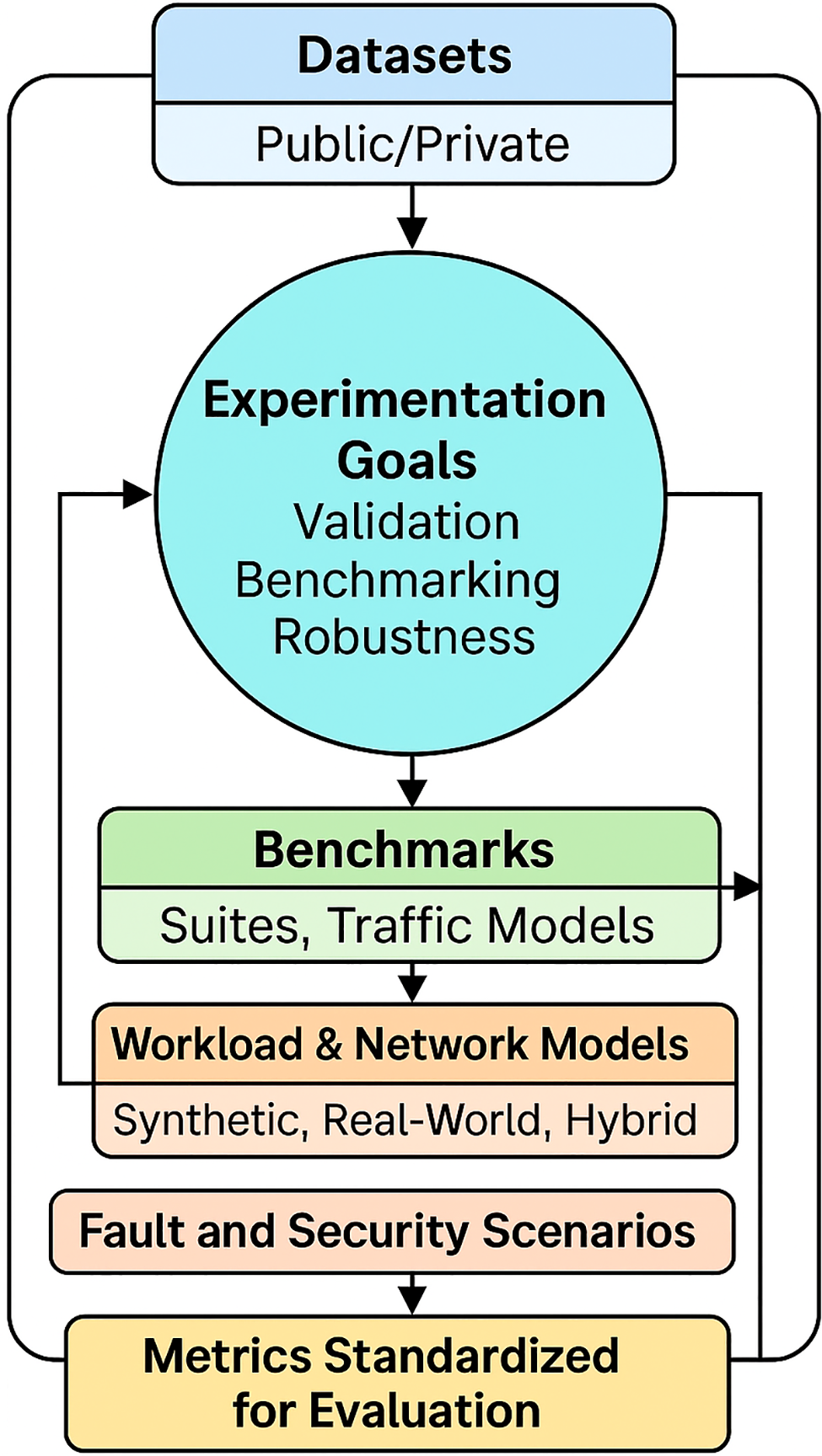
Figure 7: Edge-IoT experimental practice landscape.
Many rely on synthetic traffic or small-scale testbeds. These fail to capture real-world IoT complexities like partial observability, node heterogeneity, and dynamic topology changes. Standard fault injection and traffic scenarios remain absent. This limits robustness assessment. Shared benchmark suites prove vital. They represent diverse realistic scenarios such as urban, industrial, or agricultural IoT contexts.
Standardized traffic models that reflect typical IoT workloads will aid in creating uniform evaluation conditions. Additionally, defining common fault and failure scenarios, including network partitions, device crashes, and security threats, will foster comprehensive robustness evaluations. Such coordinated efforts will enhance reproducibility, improve comparability of research outcomes, and accelerate advancement toward resilient and efficient edge-IoT architectures. Table 14 exposes reproducibility crisis 82% synthetic datasets, 0% fault injection, 4% public traces across 47 studies. Synthetic dominance blocks generalization, motivating standardized Edge-IoT benchmarks priority.
3.11 Regulatory, Ethical, and Human-Centric Considerations
Regulatory, ethical, and human-centric considerations are critical for edge-IoT systems, especially in privacy-sensitive and safety-critical applications. Data protection laws like GDPR and HIPAA impose stringent requirements on collecting, storing, and processing personal data. Table 15 prioritizes 12 research gaps by prevalence/feasibility: Byzantine resilience (3% coverage), multi-hop dependency (5%), 10K-node validation (0%). Ranks by mission-critical impact guiding future funding/roadmaps. Existing research emphasizes encryption and access control. Consent management and data minimization receive insufficient attention. Future designs must integrate regulatory demands for legal and ethical compliance. Consent and user autonomy demand emphasis. Transparent mechanisms enable informed consent and data flow control. Explainability proves crucial. Interpretable models provide rationales for decisions. These foster trust and oversight. Errors impact safety or privacy in key domains. Human-in-the-loop paradigm gains attention in edge-IoT research. Humans monitor, participate, or override automated decisions. Human feedback improves system safety and aligns with ethical AI standards. Embedding non-technical dimensions sets research apart from algorithmic studies. Responsible, trustworthy edge-IoT systems emerge.
Critical analysis reveals significant gaps in task offloading and edge intelligence research within the IoT domain. Frameworks optimized for edge computing demonstrate potential benefits, including reduced latency, enhanced energy efficiency, and improved bandwidth utilization. However, a large portion of research depends heavily on simulations with limited experimental validation. Many assumptions underlying current studies fail to reflect the complexities of real-world deployments. Few investigations provide reproducible empirical evidence from large-scale or heterogeneous testbeds. Practical adoption remains constrained due to assumptions of static network topologies and perfect information. Furthermore, multi-objective optimization addressing latency, energy, cost, reliability, and privacy is often overlooked. Weak integration of privacy, security, and robustness limits applicability. Node failures and dynamic network behavior contribute. Future research must prioritize empirical validation across diverse, scalable settings. Algorithmic designs should incorporate capabilities to operate with partial observability and adapt dynamically to changing conditions. Systematic attention to safety, privacy, scalability, and security in realistic contexts is imperative. Progress depends on advances in multi-objective optimization, development of interpretable decision models, and effective cloud-fog-edge collaboration mechanisms. Promotion of open-source experimentation, inclusive and standardized metric reporting, and community-wide bench-marking initiatives are key to unlocking the full potential of edge computing. These efforts will support deployment in mission-critical, data-intensive, and safety-sensitive IoT applications.
Acknowledgement: Not applicable.
Funding Statement: The author received no specific funding for this study.
Availability of Data and Materials: Not applicable.
Ethics Approval: Not applicable.
Conflicts of Interest: The author declares no conflicts of interest.
Appendix A
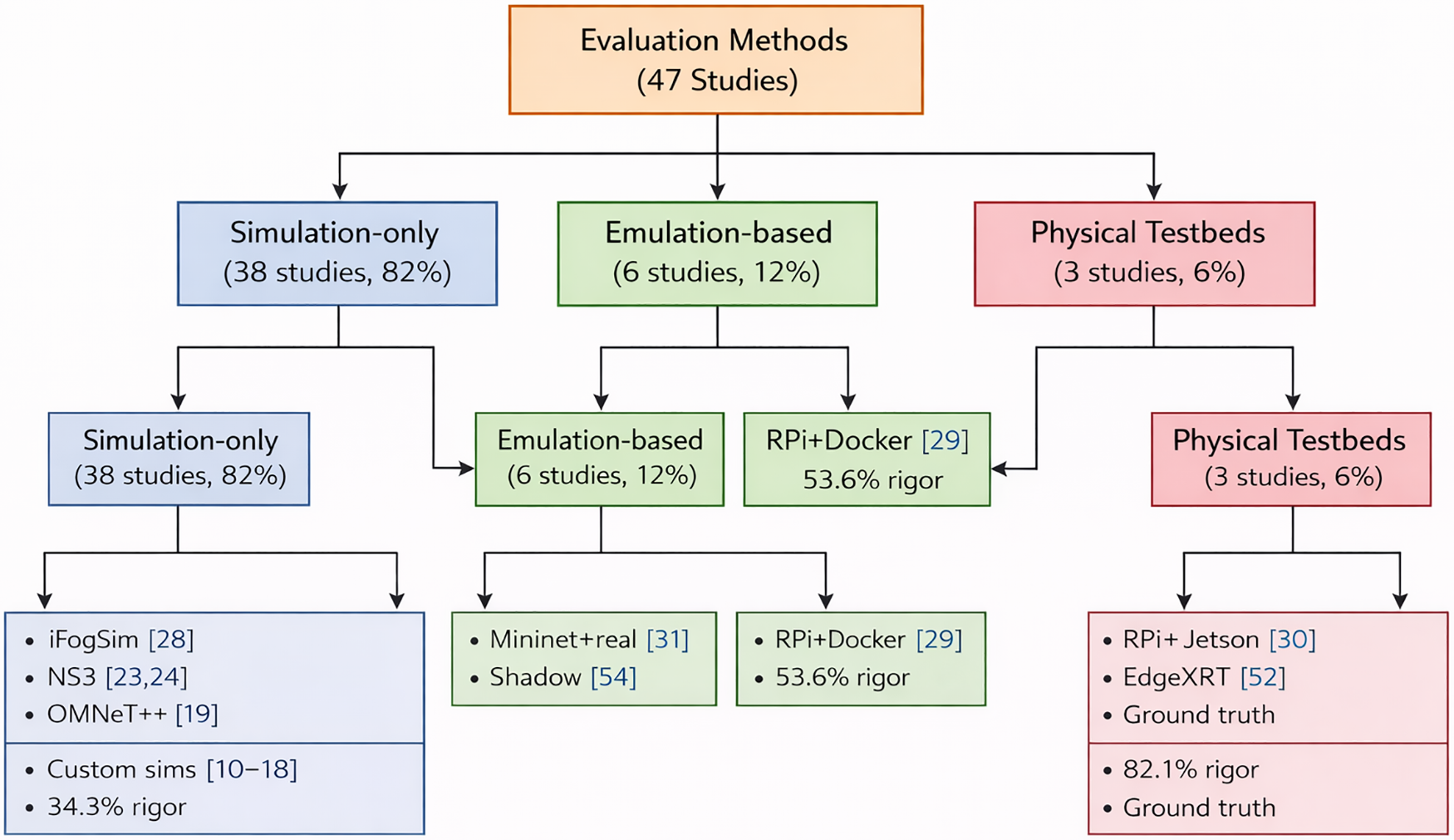
Figure A1: Evaluation method Tree: 47 studies partitioned (82% Simulation, 12% Emulation, 6% Testbed). Testbed highest rigor (82.1%) despite lowest prevalence clarifies sim-dominance vs. validation scarcity [10–19,23,24,28–31,52,54].
References
1. Gong B, Jiang X. Dependent task-offloading strategy based on deep reinforcement learning in mobile edge computing. Wirel Commun Mob Comput. 2023;2023:4665067. doi:10.1155/2023/4665067. [Google Scholar] [CrossRef]
2. Qin Y, Chen J, Jin L, Yao R, Gong Z. Task offloading optimization in mobile edge computing based on a deep reinforcement learning algorithm using density clustering and ensemble learning. Sci Rep. 2025;15(1):211. doi:10.1038/s41598-024-84038-3. [Google Scholar] [PubMed] [CrossRef]
3. Mohapatra H. A comprehensive review on urban resilience via fault-tolerant IoT and sensor networks. Comput Mater Contin. 2025;85(1):221–47. doi:10.32604/cmc.2025.068338. [Google Scholar] [CrossRef]
4. Park J, Chung K. Distributed DRL-based computation offloading scheme for improving QoE in edge computing environments. Sensors. 2023;23(8):4166. doi:10.3390/s23084166. [Google Scholar] [PubMed] [CrossRef]
5. Loutfi SI, Shayea I, Tureli U, El-Saleh AA, Tashan W. An overview of mobility awareness with mobile edge computing over 6G network: challenges and future research directions. Res Eng. 2024;23:102601. doi:10.1016/j.rineng.2024.102601. [Google Scholar] [CrossRef]
6. Baktayan AA, Zahary AT, Al-Baltah IA. A systematic mapping study of UAV-enabled mobile edge computing for task offloading. IEEE Access. 2024;12:101936–70. doi:10.1109/access.2024.3431922. [Google Scholar] [CrossRef]
7. Reddy SS, Nrusimhadri S, Mahesh G, Rao VVRM. A dependency-aware task offloading in IoT-based edge computing system using an optimized deep learning approach. Parallel Comput. 2025;126:103161. doi:10.1016/j.parco.2025.103161. [Google Scholar] [CrossRef]
8. Zhang Z, Liu X, Zhou H, Xu S, Lee C. Advances in machine-learning enhanced nanosensors: from cloud artificial intelligence toward future edge computing at chip level. Small Struct. 2024;5(4):2300325. doi:10.1002/sstr.202300325. [Google Scholar] [CrossRef]
9. Alzu’Bi A, Alomar A, Alkhaza’Leh S, Abuarqoub A, Hammoudeh M. A review of privacy and security of edge computing in smart healthcare systems: issues, challenges, and research directions. Tsinghua Sci Technol. 2024;29(4):1152–80. doi:10.26599/tst.2023.9010080. [Google Scholar] [CrossRef]
10. Khani M, Sadr MM, Jamali S. Deep reinforcement learning-based resource allocation in multi-access edge computing. Concurr Comput. 2024;36(15):e7995. doi:10.1002/cpe.7995. [Google Scholar] [CrossRef]
11. Mohi Ud Din N, Assad A, Ul Sabha S, Rasool M. Optimizing deep reinforcement learning in data-scarce domains: a cross-domain evaluation of double DQN and dueling DQN. Int J Syst Assur Eng Manag. 2024;43(1):635. doi:10.1007/s13198-024-02344-5. [Google Scholar] [CrossRef]
12. Yang T, Cen S, Wei Y, Chen Y, Chi Y. Federated natural policy gradient and actor critic methods for multi-task reinforcement learning. Adv Neural Inform Process Syst. 2024;37:121304–75. doi:10.52202/079017-3855. [Google Scholar] [CrossRef]
13. Tuli S, Casale G, Jennings NR. SimTune: bridging the simulator reality gap for resource management in edge-cloud computing. Sci Rep. 2022;12(1):19158. doi:10.1038/s41598-022-23924-0. [Google Scholar] [PubMed] [CrossRef]
14. Liu Y, Tan C, Wang K, Chen W. Hybrid task offloading and resource optimization in vehicular edge computing networks. IEEE Wirel Commun Lett. 2024;13(6):1715–9. doi:10.1109/lwc.2024.3387983. [Google Scholar] [CrossRef]
15. Sun G, Wang Y, Sun Z, Wu Q, Kang J, Niyato D, et al. Multi-objective optimization for multi-UAV-assisted mobile edge computing. IEEE Trans Mobile Comput. 2024;23(12):14803–20. [Google Scholar]
16. Ali EM, Abawajy J, Lemma F, Baho SA. Analysis of deep reinforcement learning algorithms for task offloading and resource allocation in fog computing environments. Sensors. 2025;25(17):5286. doi:10.3390/s25175286. [Google Scholar] [PubMed] [CrossRef]
17. Liu P, An K, Lei J, Sun Y, Liu W, Chatzinotas S. Computation rate maximization for SCMA-aided edge computing in IoT networks: a multi-agent reinforcement learning approach. IEEE Trans Wirel Commun. 2024;23(8):10414–29. doi:10.1109/twc.2024.3371791. [Google Scholar] [CrossRef]
18. Ma Y, Zhao H, Guo K, Xia Y, Wang X, Niu X, et al. A fault-tolerant mobility-aware caching method in edge computing. Comput Model Eng Sci. 2024;140(1):907–27. doi:10.32604/cmes.2024.048759. [Google Scholar] [CrossRef]
19. Dayong W, Bakar KBA, Isyaku B, Eisa TAE, Abdelmaboud A. A comprehensive review on internet of things task offloading in multi-access edge computing. Heliyon. 2024;10(9):e29916. doi:10.1016/j.heliyon.2024.e29916. [Google Scholar] [PubMed] [CrossRef]
20. Andriulo FC, Fiore M, Mongiello M, Traversa E, Zizzo V. Edge computing and cloud computing for internet of things: a review. Informatics. 2024;11(4):71. doi:10.3390/informatics11040071. [Google Scholar] [CrossRef]
21. Yazid Y, Ez-Zazi I, Guerrero-González A, El Oualkadi A, Arioua M. UAV-enabled mobile edge-computing for IoT based on AI: a comprehensive review. Drones. 2021;5(4):148. doi:10.3390/drones5040148. [Google Scholar] [CrossRef]
22. Genefer MJA, Theresa MJ. Soft actor-critic-based distributed routing scheme for edge computing integrated with dynamic IoT networks. IETE J Res. 2025;71(2):537–53. doi:10.1080/03772063.2024.2428738. [Google Scholar] [CrossRef]
23. Pirhosseini H, Zarei E, Rezvani MH, Pourkabirian A, Shankar A, Bacanin N, et al. Game-theoretic methods for edge/fog/cloud computation offloading: a systematic review. Computing. 2025;107(8):166. doi:10.1007/s00607-025-01515-x. [Google Scholar] [CrossRef]
24. Cheng Y, Li J, Liang C, Chai R, Chen Q, Yu FR. Online convex optimization for resource allocation scheme in edge computing-enabled networks. In: 2024 IEEE Wireless Communications and Networking Conference (WCNC). Piscataway, NJ, USA: IEEE; 2024. p. 1–6. [Google Scholar]
25. Choppara P, Mangalampalli SS. Resource adaptive automated task scheduling using deep deterministic policy gradient in fog computing. IEEE Access. 2025;13:25969–94. doi:10.1109/access.2025.3539606. [Google Scholar] [CrossRef]
26. Wang J, Yang Y. Attention-based high-dimensional offloading with deep recurrent Q-network in a cloud-edge environment. J Netw Syst Manag. 2026;34(1):3. doi:10.1007/s10922-025-09972-7. [Google Scholar] [CrossRef]
27. Sharma M, Tomar A, Hazra A. Edge computing for industry 5.0: fundamental, applications, and research challenges. IEEE Inter Things J. 2024;11(11):19070–93. doi:10.1109/jiot.2024.3359297. [Google Scholar] [CrossRef]
28. Anchitaalagammai J, Kavitha S, Buurvidha R, Santhiya T, Roopa MD, Sankari SS. Edge artificial intelligence for real-time decision making using NVIDIA jetson orin, google coral edge TPU and 6G for privacy and scalability. In: 2025 International Conference on Visual Analytics and Data Visualization (ICVADV). Piscataway, NJ, USA: IEEE; 2025. p. 150–5. [Google Scholar]
29. Petrakis K, Agorogiannis E, Antonopoulos G, Anagnostopoulos T, Grigoropoulos N, Veroni E, et al. Enhancing DevOps practices in the IoT-Edge–cloud continuum: architecture, integration, and software orchestration demonstrated in the COGNIFOG framework. Software. 2025;4(2):10. doi:10.3390/software4020010. [Google Scholar] [CrossRef]
30. Al-Bakhrani AA, Li M, Obaidat MS, Amran GA. MOALF-UAV-MEC: adaptive multi-objective optimization for UAV-assisted mobile edge computing in dynamic IoT environments. IEEE Inter Things J. 2025;12(12):20736–56. doi:10.1109/jiot.2025.3544624. [Google Scholar] [CrossRef]
31. Zhao X, Li M, Yuan P. An online energy-saving offloading algorithm in mobile edge computing with Lyapunov optimization. Ad Hoc Netw. 2024;163:103580. doi:10.1016/j.adhoc.2024.103580. [Google Scholar] [CrossRef]
32. Amodu OA, Raja Mahmood RA, Althumali H, Jarray C, Adnan MH, Bukar UA, et al. A question-centric review on DRL-based optimization for UAV-assisted MEC sensor and IoT applications, challenges, and future directions. Veh Commun. 2025;53:100899. doi:10.1016/j.vehcom.2025.100899. [Google Scholar] [CrossRef]
33. Mahato GK, Chakraborty SK. Securing edge computing using cryptographic schemes: a review. Multim Tools Appl. 2024;83(12):34825–48. doi:10.1007/s11042-023-15592-7. [Google Scholar] [CrossRef]
34. Siddiqui F, Rabbani H, Akhtar N, Suneel S, Naik AS, Vengaimarbhan D. Scalable environmental monitoring system using Iot and edge computing. Int J Environ Sci. 2025;11(11s):932–43. [Google Scholar]
35. Li C, Qiu W, Li X, Liu C, Zheng Z. A dynamic adaptive framework for practical byzantine fault tolerance consensus protocol in the internet of things. IEEE Trans Comput. 2024;73(7):1669–82. doi:10.1109/tc.2024.3377921. [Google Scholar] [CrossRef]
36. Li T, Liu Y, Ouyang T, Zhang H, Yang K, Zhang X. Multi-hop task offloading and relay selection for iot devices in mobile edge computing. IEEE Trans Mobile Comput. 2025;24(1):466–81. doi:10.1109/tmc.2024.3462731. [Google Scholar] [CrossRef]
37. Zhao M, Zhang X, He Z, Chen Y, Zhang Y. Dependency-aware task scheduling and layer loading for mobile edge computing networks. IEEE Inter Things J. 2024;11(21):34364–81. doi:10.1109/jiot.2023.3272113. [Google Scholar] [CrossRef]
38. Ren J, Hou T, Wang H, Tian H, Wei H, Zheng H, et al. Collaborative task offloading and resource scheduling framework for heterogeneous edge computing. Wirel Netw. 2024;30(5):3897–909. doi:10.1007/s11276-021-02768-y. [Google Scholar] [CrossRef]
39. Dong S, Tang J, Abbas K, Hou R, Kamruzzaman J, Rutkowski L, et al. Task offloading strategies for mobile edge computing: a survey. Comput Netw. 2024;254:110791. doi:10.1016/j.comnet.2024.110791. [Google Scholar] [CrossRef]
40. Peng P, Lin W, Wu W, Zhang H, Peng S, Wu Q, et al. A survey on computation offloading in edge systems: from the perspective of deep reinforcement learning approaches. Comput Sci Rev. 2024;53:100656. doi:10.1016/j.cosrev.2024.100656. [Google Scholar] [CrossRef]
41. Mahbub M, Shubair RM. Contemporary advances in multi-access edge computing: a survey of fundamentals, architecture, technologies, deployment cases, security, challenges, and directions. J Netw Comput Appl. 2023;219:103726. doi:10.1016/j.jnca.2023.103726. [Google Scholar] [CrossRef]
42. Zhang S, Yi N, Ma Y. A survey of computation offloading with task types. Trans Intell Transport Sys. 2024;25(8):8313–33. doi:10.1109/TITS.2024.3410896. [Google Scholar] [CrossRef]
43. Dauda A, Flauzac O, Nolot F. A survey on IoT application architectures. Sensors. 2024;24(16):5320. doi:10.3390/s24165320. [Google Scholar] [PubMed] [CrossRef]
44. Sadatdiynov K, Cui L, Zhang L, Huang JZ, Salloum S, Mahmud MS. A review of optimization methods for computation offloading in edge computing networks. Digital Commun Netw. 2023;9(2):450–61. doi:10.1016/j.dcan.2022.03.003. [Google Scholar] [CrossRef]
45. Liu H, Sun S, Chen Y, Wang Y, Jiang W, Yuan J, et al. Edge intelligence from space: a survey and future challenges. Authorea Preprints. 2025 [cited 2026 Jan 11]. Available from: https://www.techrxiv.org/doi/full/10.36227/techrxiv.176300423.38782373 [Google Scholar]
46. Rahmani AM, Haider A, Khoshvaght P, Gharehchopogh FS, Moghaddasi K, Rajabi S, et al. Optimizing task offloading with metaheuristic algorithms across cloud, fog, and edge computing networks: a comprehensive survey and state-of-the-art schemes. Sustain Comput Inform Syst. 2025;45:101080. doi:10.1016/j.suscom.2024.101080. [Google Scholar] [CrossRef]
47. Suetor CG, Scrimieri D, Qureshi A, Awan IU. An overview of distributed firewalls and controllers intended for mobile cloud computing. Appl Sci. 2025;15(4):1931. doi:10.3390/app15041931. [Google Scholar] [CrossRef]
48. Nishad DK, Verma VR, Rajput P, Gupta S, Dwivedi A, Shah DR. Adaptive AI-enhanced computation offloading with machine learning for QoE optimization and energy-efficient mobile edge systems. Sci Rep. 2025;15(1):15263. doi:10.1038/s41598-025-00409-4. [Google Scholar] [PubMed] [CrossRef]
49. Wu H, Lu Y, Ma H, Xing L, Deng K, Lu X. A survey on task type-based computation offloading in mobile edge networks. Ad Hoc Netw. 2025;169(C):103754. doi:10.1016/j.adhoc.2025.103754. [Google Scholar] [CrossRef]
50. Hortelano D, de Miguel I, Barroso RJD, Aguado JC, Merayo N, Ruiz L, et al. A comprehensive survey on reinforcement-learning-based computation offloading techniques in edge computing systems. J Netw Comput Appl. 2023;216(3):103669. doi:10.1016/j.jnca.2023.103669. [Google Scholar] [CrossRef]
51. Zheng X, Guo R, Lian S. Energy-efficient load balanced edge computing model for IoT Using FL-HMM and BOA optimization. Sustain Comput Inform Syst. 2025;48:101215. doi:10.1016/j.suscom.2025.101215. [Google Scholar] [CrossRef]
52. Deng S, Zhao H, Fang W, Yin J, Dustdar S, Zomaya AY. Edge intelligence: the confluence of edge computing and artificial intelligence. IEEE Inter Things J. 2020;7(8):7457–69. doi:10.1109/jiot.2020.2984887. [Google Scholar] [CrossRef]
53. Bablu TA, Rashid MT. Edge computing and its impact on real-time data processing for IoT-driven applications. J Adv Comput Syst. 2025;5(1):26–43. [Google Scholar]
54. Nguyen TH, Truong TP, Tran AT, Dao NN, Park L, Cho S. Intelligent heterogeneous aerial edge computing for advanced 5G access. IEEE Trans Netw Sci Eng. 2024;11(4):3398–411. doi:10.1109/tnse.2024.3371434. [Google Scholar] [CrossRef]
55. Manogaran N, Nandagopal M, Abi NE, Seerangan K, Balusamy B, Selvarajan S. Integrating meta-heuristic with named data networking for secure edge computing in IoT enabled healthcare monitoring system. Sci Rep. 2024;14(1):21532. doi:10.1038/s41598-024-71506-z. [Google Scholar] [PubMed] [CrossRef]
56. Liu L, Mao W, Li W, Duan J, Liu G, Guo B. Edge computing offloading strategy for space-air-ground integrated network based on game theory. Comput Netw. 2024;243:110331. doi:10.1016/j.comnet.2024.110331. [Google Scholar] [CrossRef]
57. Zhao H, Lu G, Liu Y, Chang Z, Wang L, Hämäläinen T. Safe DQN-based AoI-minimal task offloading for UAV-aided edge computing system. IEEE Inter Things J. 2024;11(19):32012–24. doi:10.1109/jiot.2024.3422670. [Google Scholar] [CrossRef]
58. Li M, Yang Z. Double deep Q-network-based task offloading strategy in mobile edge computing. In: 4th International Conference on Internet of Things and Smart City (IoTSC 2024). Vol. 13224. Bellingham, WA, USA: SPIE; 2024. p. 290–8. [Google Scholar]
59. Blakley JR, Iyengar R, Roy M. Simulating edge computing environments to optimize application experience. Carnegie Mellon University [Internet]. 2020 [cited 2026 Jan 11]. Available from: http://reports-archive.adm.cs.cmu.edu/anon/2020/CMU-CS-20-135.pdf. [Google Scholar]
60. Nandhakumar AR, Baranwal A, Choudhary P, Golec M, Gill SS. EdgeAISim: a toolkit for simulation and modelling of AI models in edge computing environments. Measur Sens. 2024;31:100939. doi:10.1016/j.measen.2023.100939. [Google Scholar] [CrossRef]
61. Benaboura A, Bechar R, Kadri W, Ho TD, Pan Z, Sahmoud S. Latency-aware and energy-efficient task offloading in IoT and cloud systems with DQN learning. Electronics. 2025;14(15):3090. doi:10.3390/electronics14153090. [Google Scholar] [CrossRef]
62. ElBouanani H, Barakat C, Dabbous W, Turletti T. Fidelity-aware large-scale distributed network emulation. Comput Netw. 2024;250:110531. doi:10.1016/j.comnet.2024.110531. [Google Scholar] [CrossRef]
63. Ficco M, Esposito C, Xiang Y, Palmieri F. Pseudo-dynamic testing of realistic edge-fog cloud ecosystems. IEEE Commun Mag. 2017;55(11):98–104. doi:10.1109/mcom.2017.1700328. [Google Scholar] [CrossRef]
64. Guo H, Chen X, Zhou X, Liu J. Trusted and efficient task offloading in vehicular edge computing networks. IEEE Trans Cognit Commun Netw. 2024;10(6):2370–82. doi:10.1109/globecom48099.2022.10000816. [Google Scholar] [CrossRef]
65. Gu Y, Yao Y, Li C, Xia B, Xu D, Zhang C. Modeling and analysis of stochastic mobile-edge computing wireless networks. IEEE Inter Things J. 2021;8(18):14051–65. doi:10.1109/jiot.2021.3068382. [Google Scholar] [CrossRef]
66. Shalaginov A, Azad MA. Securing resource-constrained iot nodes: towards intelligent microcontroller-based attack detection in distributed smart applications. Future Internet. 2021;13(11):272. doi:10.3390/fi13110272. [Google Scholar] [CrossRef]
67. Xiao H, Xu C, Ma Y, Yang S, Zhong L, Muntean GM. Edge intelligence: a computational task offloading scheme for dependent IoT application. IEEE Trans Wireless Commun. 2022;21(9):7222–37. doi:10.1109/twc.2022.3156905. [Google Scholar] [CrossRef]
68. Bi J, Yuan H, Duanmu S, Zhou M, Abusorrah A. Energy-optimized partial computation offloading in mobile-edge computing with genetic simulated-annealing-based particle swarm optimization. IEEE Inter Things J. 2020;8(5):3774–85. doi:10.1109/jiot.2020.3024223. [Google Scholar] [CrossRef]
69. Atan B, Basaran M, Calik N, Basaran ST, Akkuzu G, Durak-Ata L. AI-empowered fast task execution decision for delay-sensitive iot applications in edge computing networks. IEEE Access. 2022;11:1324–34. doi:10.1109/access.2022.3232073. [Google Scholar] [CrossRef]
70. Gong C, Lin F, Gong X, Lu Y. Intelligent cooperative edge computing in internet of things. IEEE Inter Things J. 2020;7(10):9372–82. doi:10.1109/jiot.2020.2986015. [Google Scholar] [CrossRef]
71. Samriya JK, Kumar M, Gill SS. Secured data offloading using reinforcement learning and Markov decision process in mobile edge computing. Int J Netw Manag. 2023;33(5):e2243. doi:10.1002/nem.2243. [Google Scholar] [CrossRef]
72. Zhao R, Wang X, Xia J, Fan L. Deep reinforcement learning based mobile edge computing for intelligent internet of things. Phys Commun. 2020;43(9):101184. doi:10.1016/j.phycom.2020.101184. [Google Scholar] [CrossRef]
73. Sahu D, Nidhi, Chaturvedi R, Prakash S, Yang T, Rathore RS, et al. Revolutionizing load harmony in edge computing networks with probabilistic cellular automata and Markov decision processes. Sci Rep. 2025;15(1):3730. doi:10.1038/s41598-025-88197-9. [Google Scholar] [PubMed] [CrossRef]
74. Cao CQ, Feng Y. Probabilistic error reasoning on IoT edge devices. In: 2023 IEEE International Conference on Edge Computing and Communications (EDGE). Piscataway, NJ, USA: IEEE; 2023. p. 140–9. [Google Scholar]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF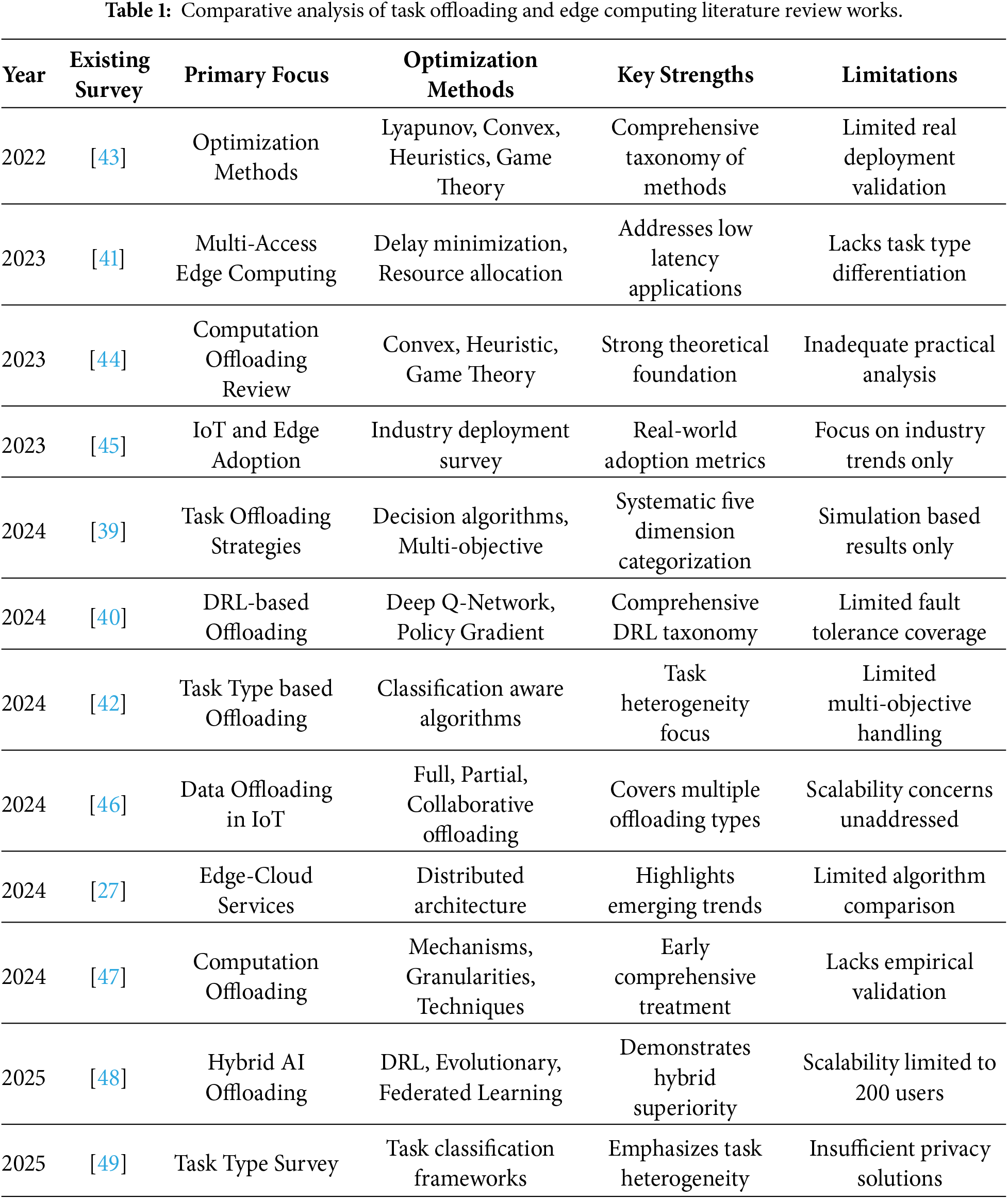
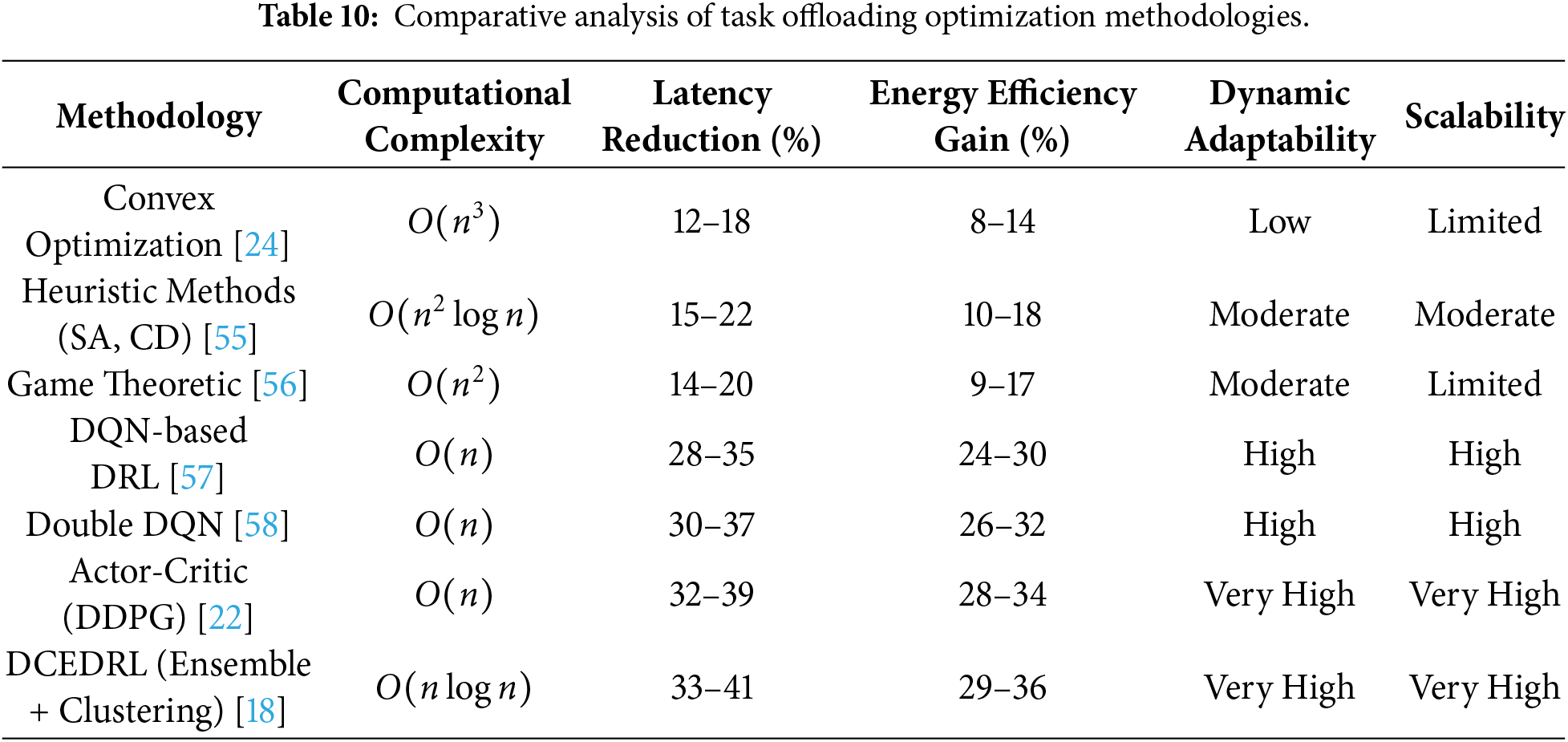
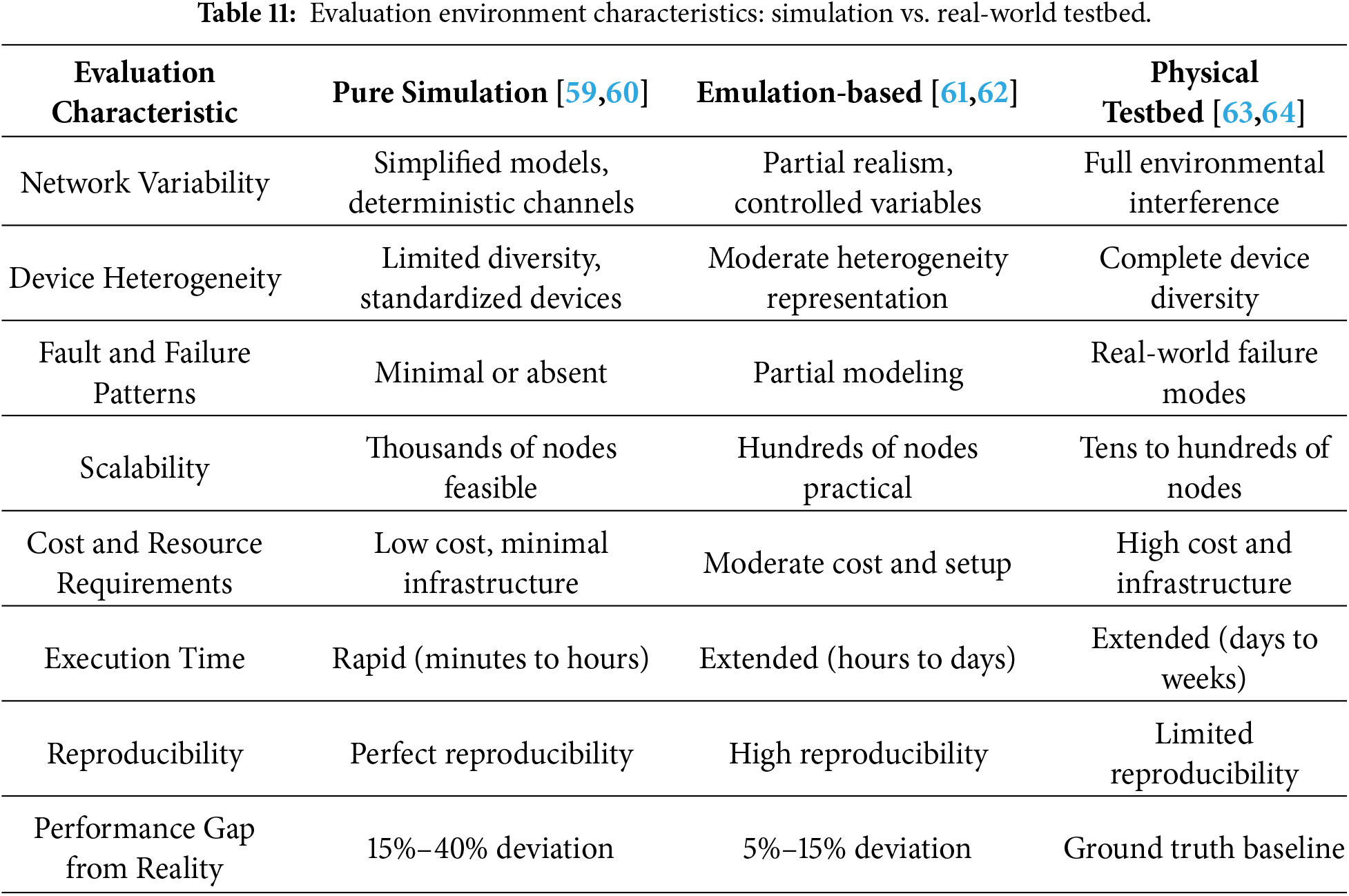
 Downloads
Downloads
 Citation Tools
Citation Tools