 Open Access
Open Access
ARTICLE
An Agent-Based Network Power Management Scheme in WSN for Enhanced Edge Communication in Beyond 5G Networks
1 School of Computer Science and Engineering, Yeungnam University, Gyeongsan-si, Republic of Korea
2 Department of Electrical Engineering, Yeungnam University, Gyeongsan-si, Republic of Korea
3 Department of Computer Engineering, Gachon University, Seongnam-si, Republic of Korea
* Corresponding Authors: Khizar Abbas. Email: ; Kwonhue Choi. Email:
# These authors contributed equally to this work
Computers, Materials & Continua 2026, 87(3), 42 https://doi.org/10.32604/cmc.2026.077012
Received 30 November 2025; Accepted 20 January 2026; Issue published 09 April 2026
Abstract
In a distributed edge computing environment, Internet of Things (IoT) and Vehicular-IoT (V-IoT) devices communicate through Wireless Sensor Networks (WSNs) by collecting and transmitting data from different environments. Although energy efficiency is always a critical challenge in WSN due to limited battery power, along with the demand for fast communication over edge devices in 5G and beyond 5G scenarios. Therefore, to overcome the challenges, an advanced hierarchical agent-based power management scheme is proposed for WSNs that optimizes energy distribution while maintaining reliable communication. The proposed model employs Master Agents (MAs), Coordination Agents (CoAs), and Task Agents (TAs) to manage power allocation by following a specific order of selection of nodes. The system dynamically adjusts power distribution based on node requirements, trust values, and communication demands over an optimally covered area of nodes, distributed with a 2D Poisson Point Process. Simulation results demonstrate improved energy efficiency, extended network lifetime, and enhanced communication reliability in edge computing scenarios.Keywords
The rapid proliferation of IoT and industrial IoT devices demands sustainable networks with enhanced computation and communication capabilities [1]. Wireless Sensor Networks (WSNs) play a pivotal role, particularly when integrated with Mobile Edge Computing (MEC) for low-latency, high-bandwidth processing [2–4]. From smart homes to wearable health monitors [5,6], these resource-constrained devices continuously sense environmental parameters (temperature, humidity, sound, light [7]) and transmit data to edge servers or clouds.
1.1 Challenges in Edge-Enabled WSNs
IoT applications—smart cities, healthcare monitoring, industrial automation [8–10]—impose stringent requirements on WSNs: intensive computation, continuous sensing, and multi-task operations under 6G constraints (limited memory, bandwidth [11,12]). MEC mitigates cloud latency by enabling edge processing [13], yet battery-constrained sensor nodes face critical power management challenges.
Key limitations of traditional approaches include:
• Static power allocation ignoring dynamic topologies and node heterogeneity.
• Clustering overhead (e.g., LEACH CH election every round).
• Lack of trust-awareness for unreliable edge environments.
• Scalability issues for dense, Poisson-distributed deployments.
We propose a hierarchical multi-agent power management framework addressing these gaps:
a. Trust-driven redistribution: Adaptive power allocation via MA
b. Non-clustered deployment: 2D Poisson Point Process with hybrid CoA selection.
c. Theoretical guarantees: Trust convergence (Theorem 1–2), energy conservation (Theorem 3),
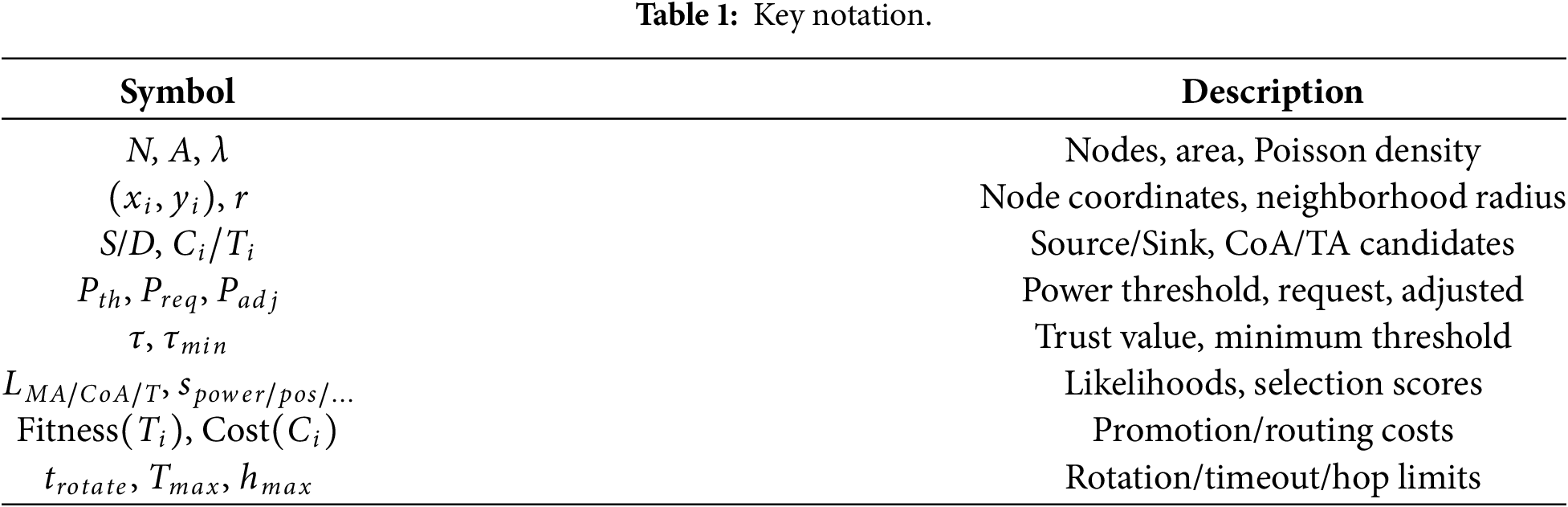
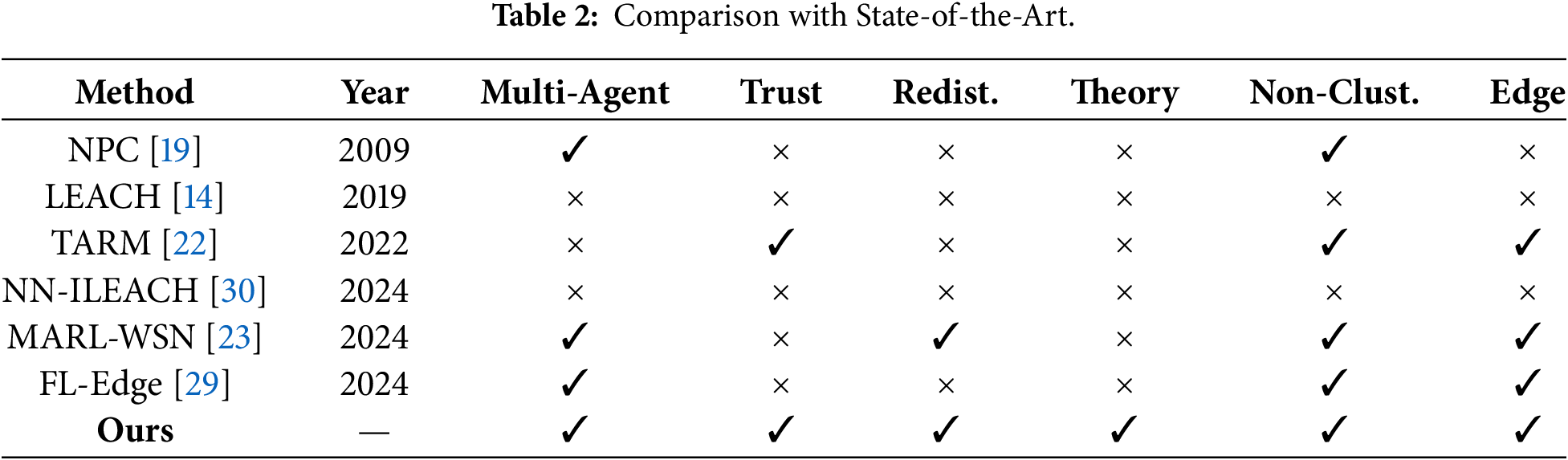
Table 1 summarizes notation. The paper is organized as follows: Section 2 positions our novelty compared to existing works, Section 3 describes the proposed model and system assumptions. Section 4 describes proposed algorithms and related analysis. Section 5 is to demonstrate the simulation results and finally the paper is concluded with discussion of results, supporting our proposed method in Section 6, discussing the results of our proposed method.
2.1 Agent-Based and Clustering Protocols
Traditional clustering (LEACH [14], HEED, EECS [15]) elects cluster heads probabilistically but suffers CH election overhead and fails in non-uniform deployments. Enhanced variants like firework-optimized LEACH [16,17] and gradient routing [18] improve load balancing but retain clustering rigidity.
Multi-agent systems offer distributed alternatives. NPC [19,20] uses threshold-based power reduction across agents but lacks hierarchy and trust. Three-layer clustering [21] combines centralized/distributed selection but requires base station coordination.
2.2 Trust and Routing Mechanisms
Trust-aware routing (TARM [22]) computes direct/indirect trust via edge nodes but uses static allocation. Recent MARL approaches [23,24] enable decentralized control through Q-learning, achieving power efficiency but requiring extensive training without trust-power coupling.
2.3 Edge Computing and Machine Learning
MEC frameworks address offloading [25–27] and ESN design [26], optimizing latency/cost. DDPG-based allocation [16] handles continuous actions but lacks WSN-specific trust. Federated learning [28,29] distributes training but assumes stable topologies, unsuitable for dynamic WSNs.
NN-ILEACH [30] uses neural networks for CH selection (11,361 rounds lifetime) but centralizes training and ignores trust.
2.4 Novelty Relative to Existing Frameworks
Table 2 compares our approach across seven criteria. Unlike clustering methods (overhead), single-agent trust (static), or MARL (training-heavy), we provide:
1. Hierarchical non-clustered agents: MA
2. Trust-power coupling: Dynamic redistribution with convergence guarantees.
3. Poisson scalability: Handles dense, irregular deployments.
4. Edge-ready:
It is evident that there are many works that exist where different approaches and methods were taken into consideration to attain energy-efficient sensor networks, and also some of the literature tried to enhance energy efficiency in edge environments. But in most cases, it lacks a technique that can be considered a systematic approach for energy-efficient smooth communication over the edge in the IoT-based WSN paradigm for V-IoT in beyond 5G network.
3 System Model and Assumptions
A resource-efficient system relies on multiple factors, and towards energy-efficient communication through a resource-constrained IoT network, the first step is establishing a network architecture with proper deployment of nodes, considering system requirements and infrastructure. The network architecture comprises multiple nodes, and in the IoT and IIoT scenario, it is possible to have multiple tasks over a network simultaneously, and it is evident that those can be different applications. Therefore, there are two possibilities to consider: a) application-specific operation by selecting heterogeneous nodes (where source and sink nodes are predefined) and b) selecting multiple paths for operation, where similar types of applications can occur at the same time within a homogeneous network. Therefore, in our work, we have considered the second option. In the next part of this subsection, detail description of the hierarchical agent-based WSN architecture is presented in Fig. 1.
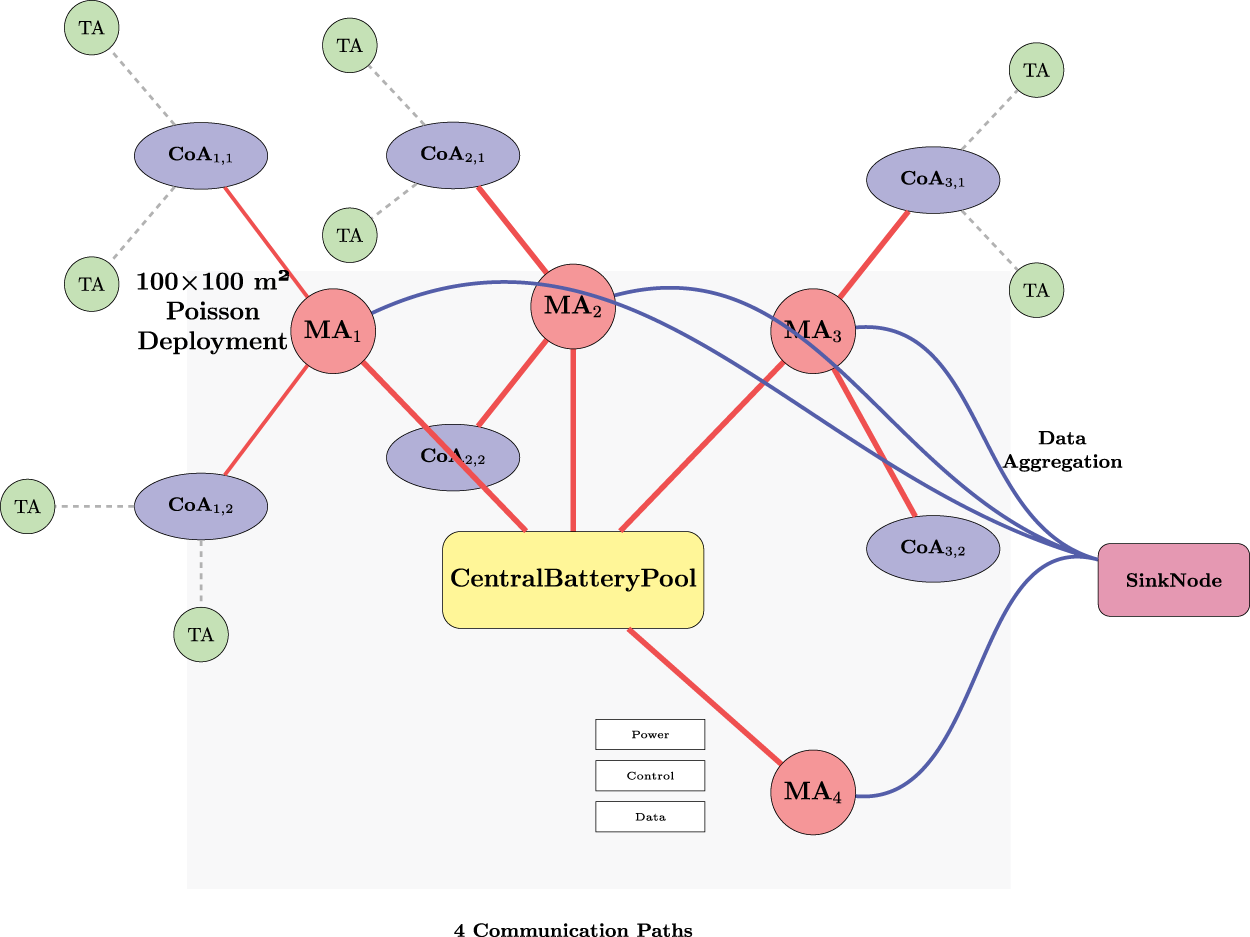
Figure 1: Proposed system model and architecture.
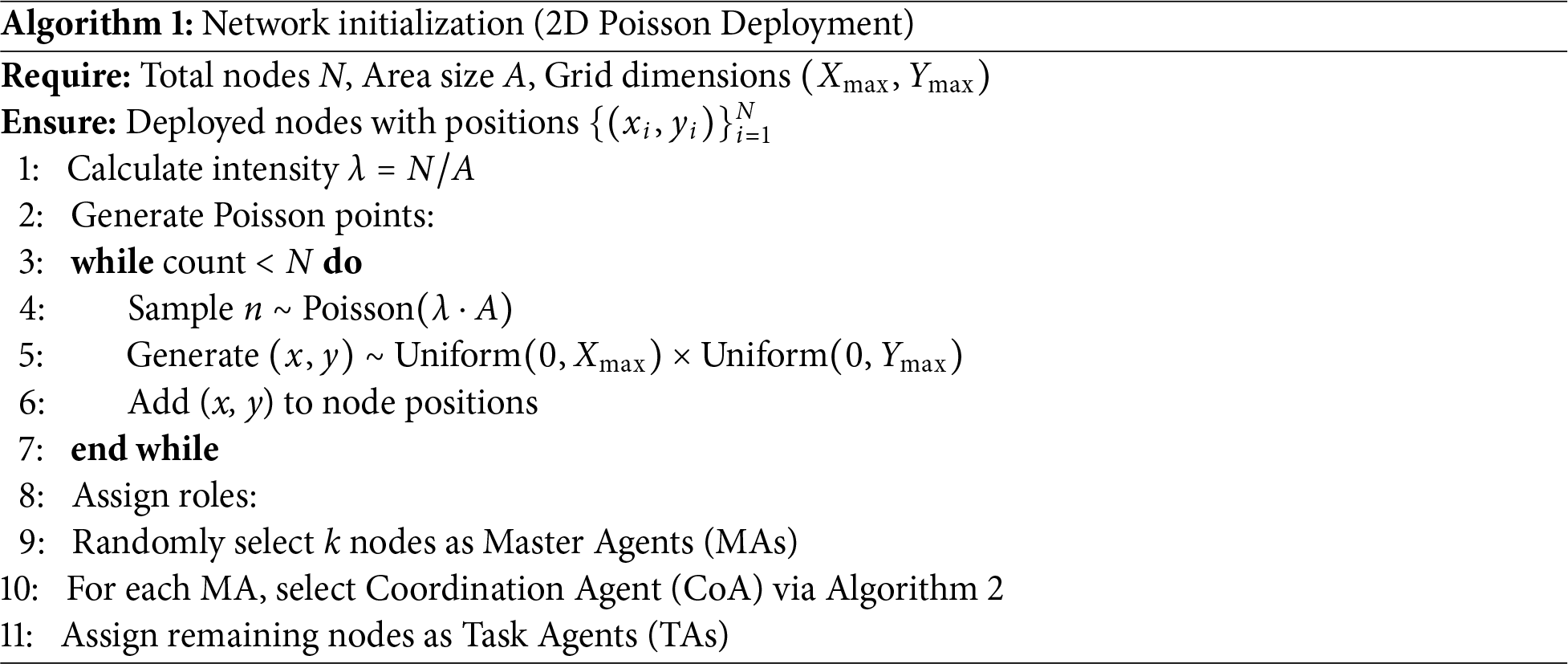
• Poisson Point Process (PPP): In our proposed method, nodes are deployed via 2D Poisson Point Process (Algorithm 1) with intensity
It ensures uniform spatial distribution and provides coverage for holes in WSNs. The common approach of clustering is avoided to get rid of different types of problems, such as zero cluster head selection and compulsory cluster head selection in every round, which eventually saves a lot of resources.
• Roles of Nodes: In the proposed WSN battery power management system, the agents follow specific orders to accomplish a task with prolific communication over the network. In this method, it is considered that there are four source nodes for different paths, where it is assumed that for multi-operation networks, different applications can take place simultaneously over a defined network. Each source node acts as an MA [31] for a specific path of communication and is directly connected to the central battery. The work of the MA is to manage the power distribution over the entire network through the other subagents. At the time of consideration of the MA in each path, the other sensor nodes of the network are assumed to be TAs [32] for the particular path, and CoA is selected from other TAs to act as a coordinator between TAs and the MA for optimal communication.
– MA: High-power nodes managing CoAs (
– CoA: Optimally positioned nodes (Algorithm 2) with score:
– TA: Worker nodes with power
As mentioned earlier, MAs are basically the source nodes. Among the TAs, a CoA is selected with hybrid by MA. This CoA negotiates with MA for available resources to complete the task by each TA. We have set a threshold power value, which is considered as the required power to complete task by each TA. After each CoA-TA communication for time instant ‘t’, the consumed power will be determined, and CoA informs the MA of more power requirements. This process continues until the required power for all TAs is calculated. Then, for every time interval of ‘t’, the power for CoA-MA and CoA-TA communication is calculated based on the distance between nodes.
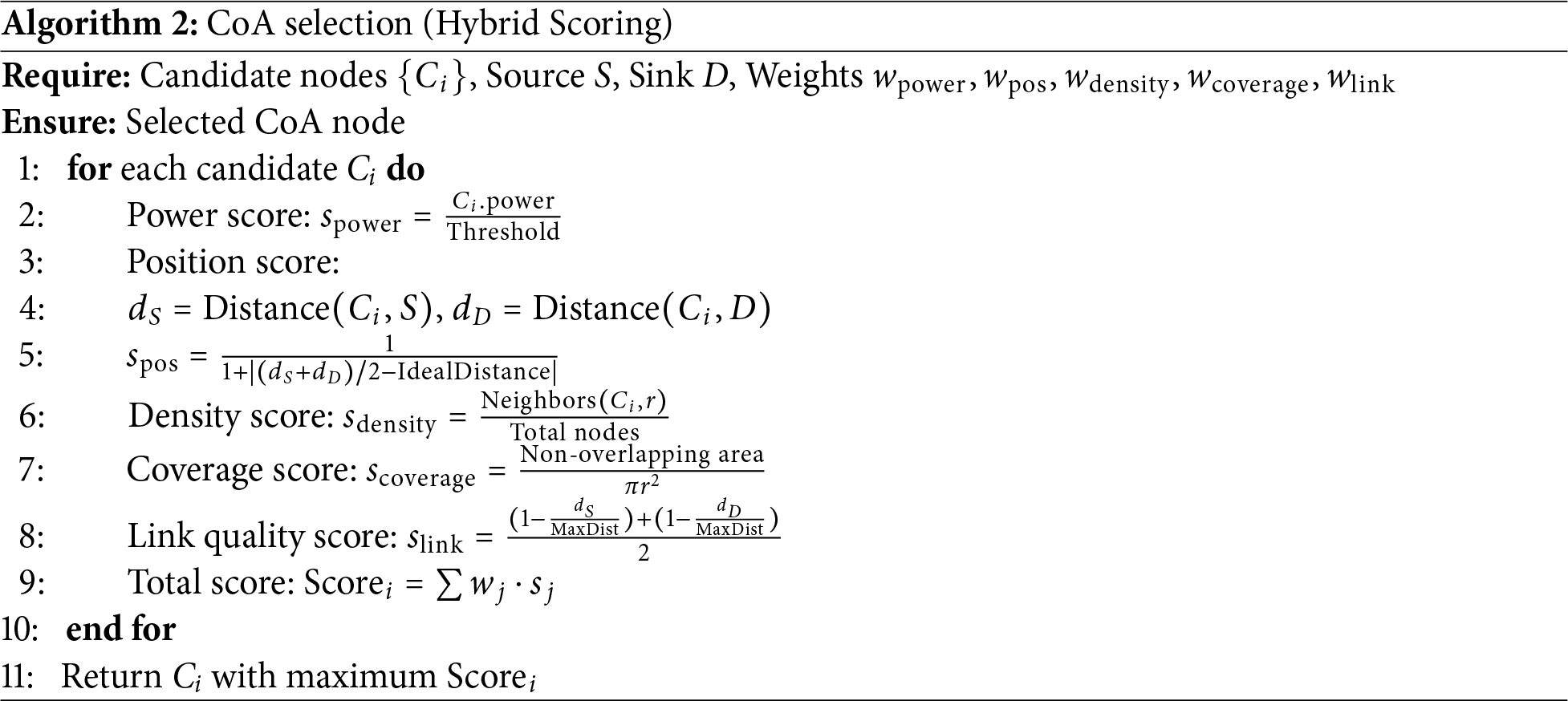
The CoA (Algorithm 2) is chosen using a weighted scoring mechanism that identifies the node best suited to coordinate the traffic on a given path. Each candidate node is evaluated against five criteria: energy efficiency, position in the topology, local node density, coverage, and link quality. The individual scores are combined into a single weighted score that reflects how suitable the node is to act as a CoA.
First, a power score captures how much usable energy the node still has, normalized with respect to the threshold power level. A positional score then measures how well the node is placed between the source and sink, with nodes located roughly midway between them being preferred. A density score evaluates how many neighbors lie within a given radius, so that a CoA has enough nearby nodes to coordinate without becoming overloaded.
The coverage score reflects how much non-overlapping area the node can cover within its communication range, encouraging selections that improve overall sensing and connectivity. Finally, a link-quality score is obtained from the normalized distances to the source and destination; shorter, more reliable links receive higher values. The five scores are weighted according to design priorities (
The scoring model normalizes each component to the interval [0, 1], so all metrics are directly comparable even though they capture different aspects of a node’s behavior. The CoA is then chosen as the node with the highest overall score, ensuring that the selected coordinator is, at that moment, the most suitable option for the network. In this way, the method balances energy efficiency, coverage, and link quality while keeping the computation lightweight enough to be practical for dynamic wireless sensor networks such as V-IoT where the nodes are homogeneous (Appendix A.2).
In the proposed scheme the power management depends mainly on trust-based node selection and power distribution. Fig. 2 summarizes the proposed agent-based power management cycle.
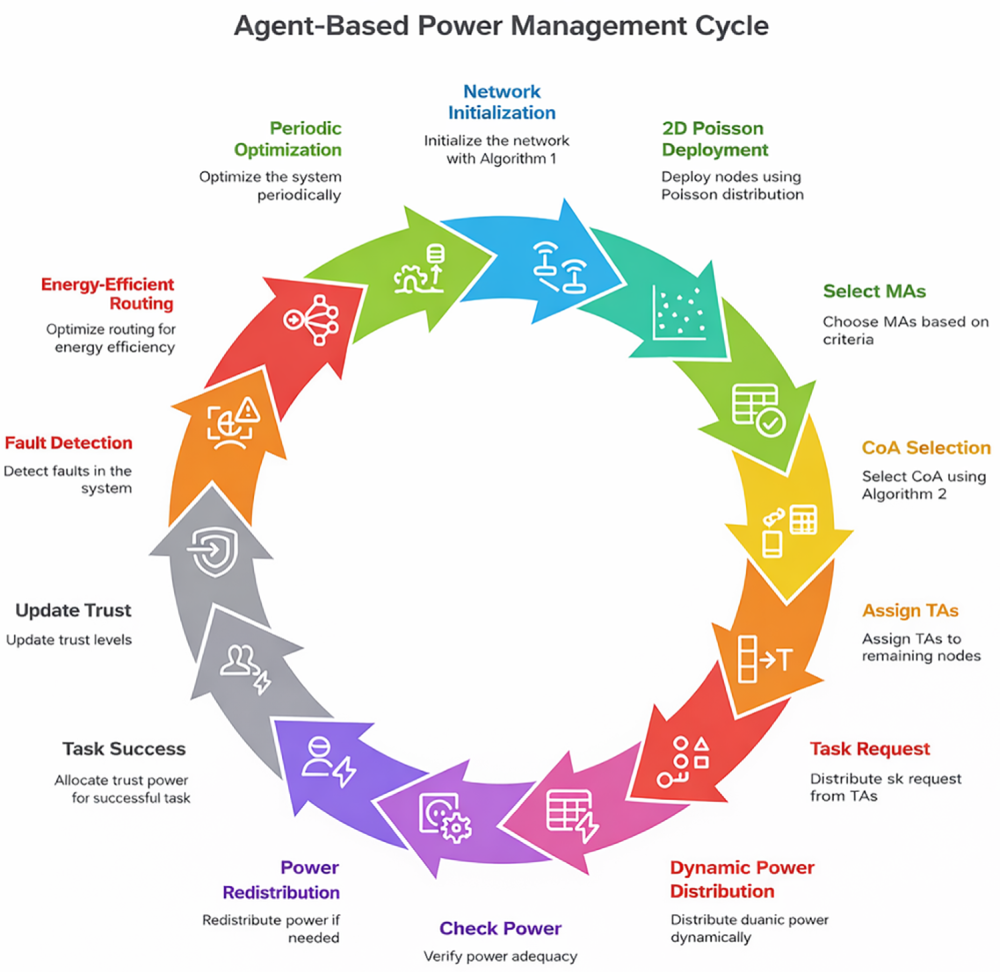
Figure 2: Comprehensive representation of proposed power management scheme.
3.2.1 Power and Trust Dynamics
The proposed agent-based power management scheme jointly models the evolution of node power and trust to capture both energy sustainability and communication reliability. Each node
Trust dynamics follow a weighted update rule that combines historical behavior, power efficiency, and link quality. For active nodes, the trust value is updated as
where
For inactive nodes, a decay factor is applied to penalize prolonged non-participation, i.e.,
Power allocation in the proposed scheme is performed hierarchically along the path
These likelihoods are used to adjust the initial request and account for potential deficits along the path. The adjusted power demand is expressed as
so that lower likelihoods (i.e., weaker nodes) increase the required energy budget for reliable delivery.
If the remaining global battery
This section presents the distributed algorithms that implement the power management model described in Section 3. The algorithms operate over the hierarchical path
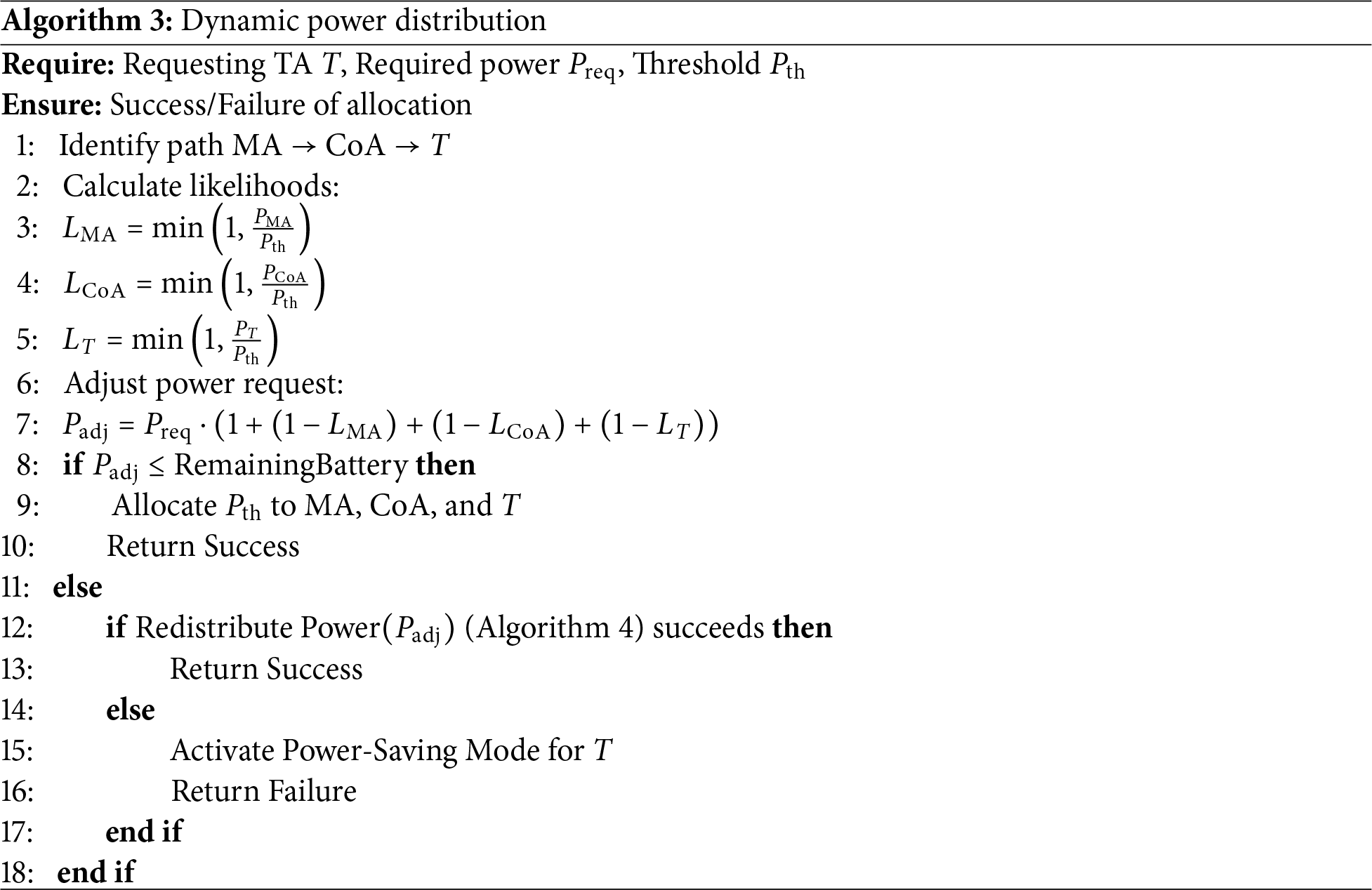
The dynamic power management module implements the power allocation model of Section 3.2.2 as per the Dynamic Power Distribution Algorithm 3. When a Task Agent (TA) requests power for a task, the Master Agent (MA) first evaluates the energy condition of the MA, CoA, and TA through likelihood ratios, then adjusts the requested power to obtain
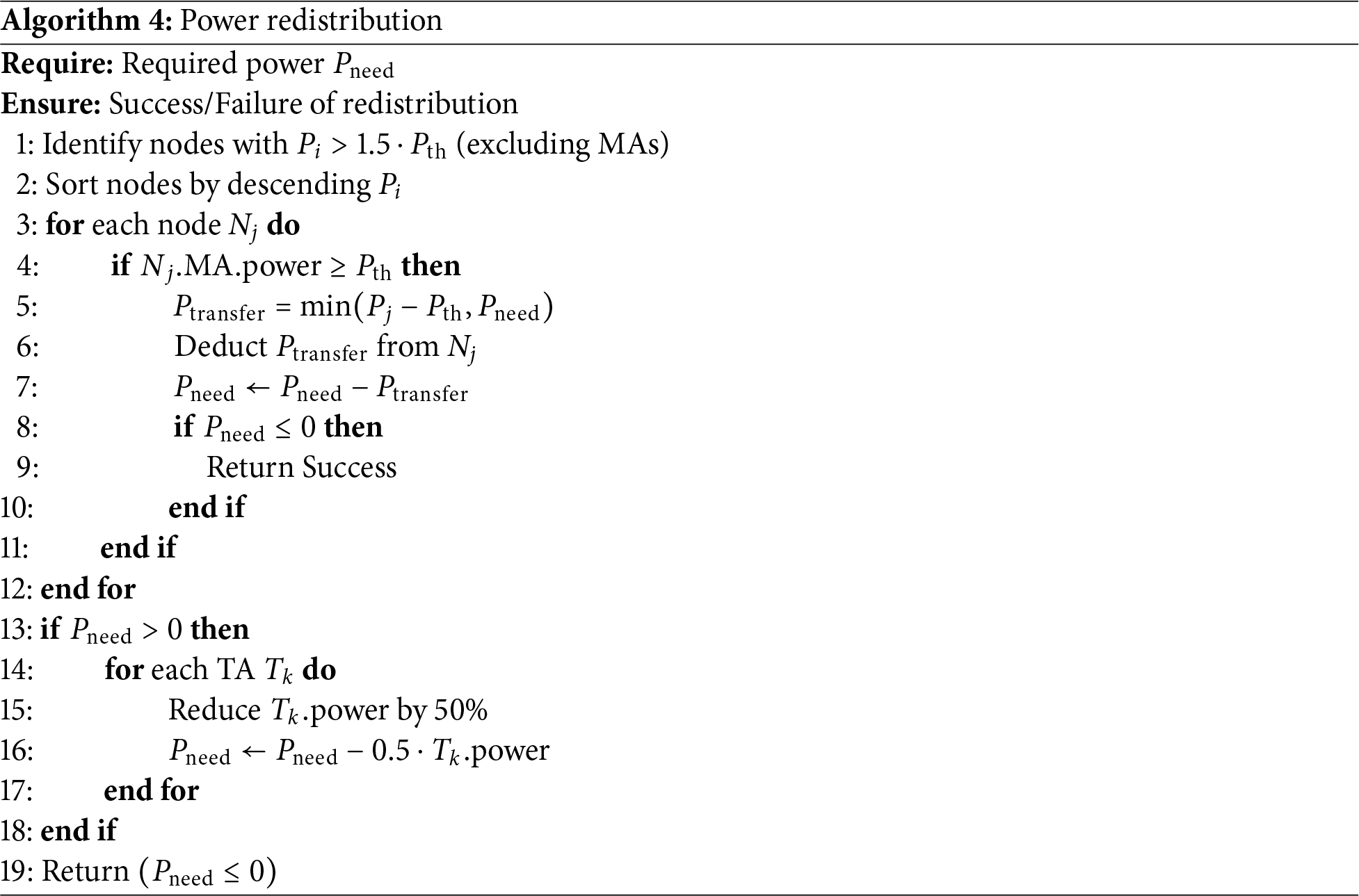
The Power Redistribution algorithm presents a systematic approach to reallocating power resources within a wireless sensor network when additional power (
In the first phase, the algorithm searches for donor nodes whose power exceeds
which prevents the donor from dropping below the threshold and reduces the remaining demand as much as possible. If this first phase does not fully satisfy the requirement (
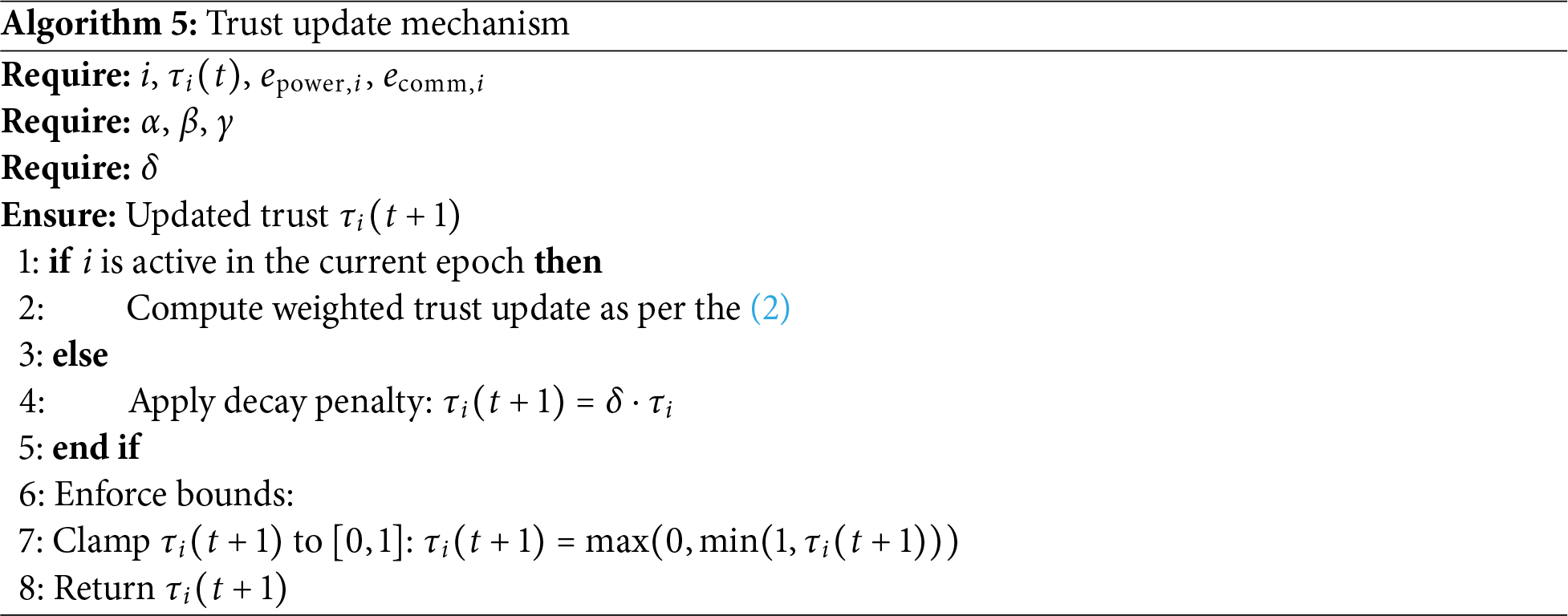
The trust update mechanism implements the behavior described in Section 3.2.1. Active nodes gain trust when they use power efficiently and maintain good-quality links, whereas inactive nodes gradually lose trust over time. After each update, the new trust value is clipped to lie within [0, 1]. The complete procedure is summarized in Algorithm 5.
4.3 Fault Detection and Recovery
The Fault Detection and Recovery Algorithm 6 provides a structured way to monitor node health and react to failures. Each node N sends heartbeat messages at regular intervals
• Heartbeat Monitoring: Node i is faulty if:
• Recovery Actions:
– Demote CoAs with
– Trigger Algorithm 7 for route recomputation
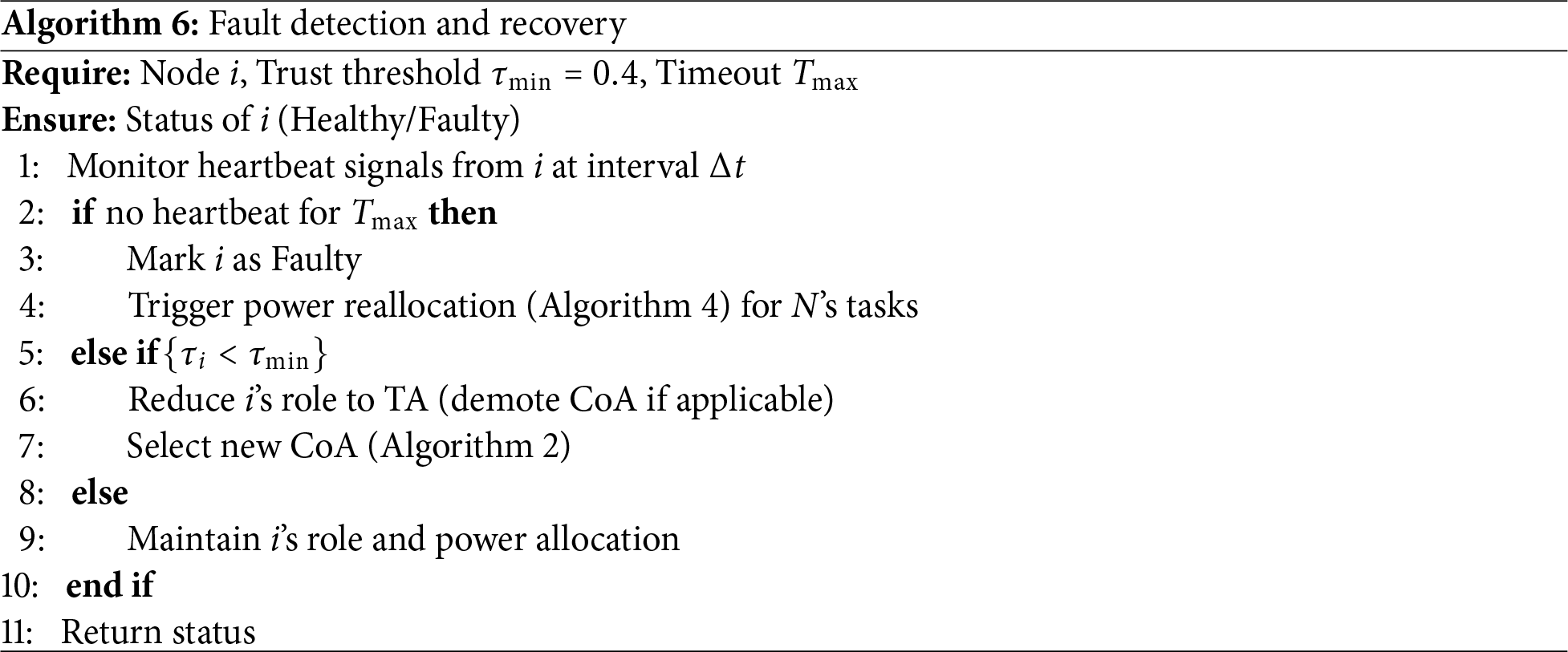
Sensitivity to Intermittent Link Failures (
To assess robustness under intermittent links, we conducted a sensitivity study by varying the heartbeat timeout
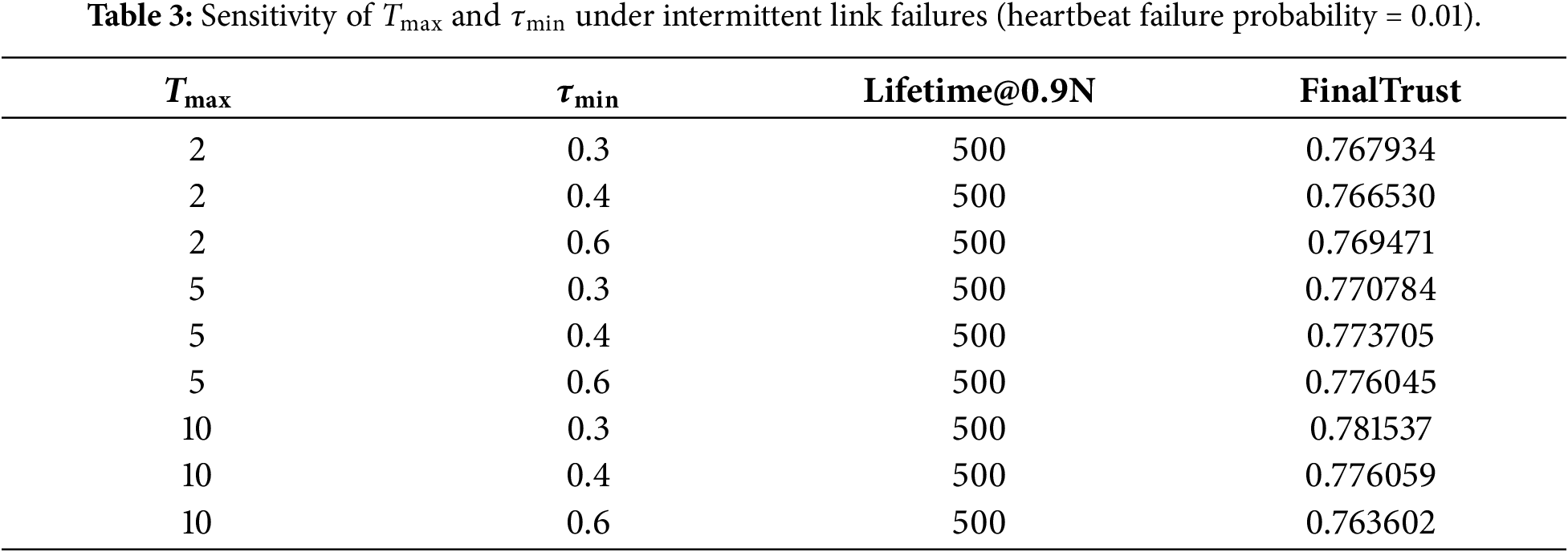
The Energy-Efficient Data Routing Alogorithm 7 computes routes using both distance and trust information. Given a packet P, a source node S, a destination D, and a hop limit
where
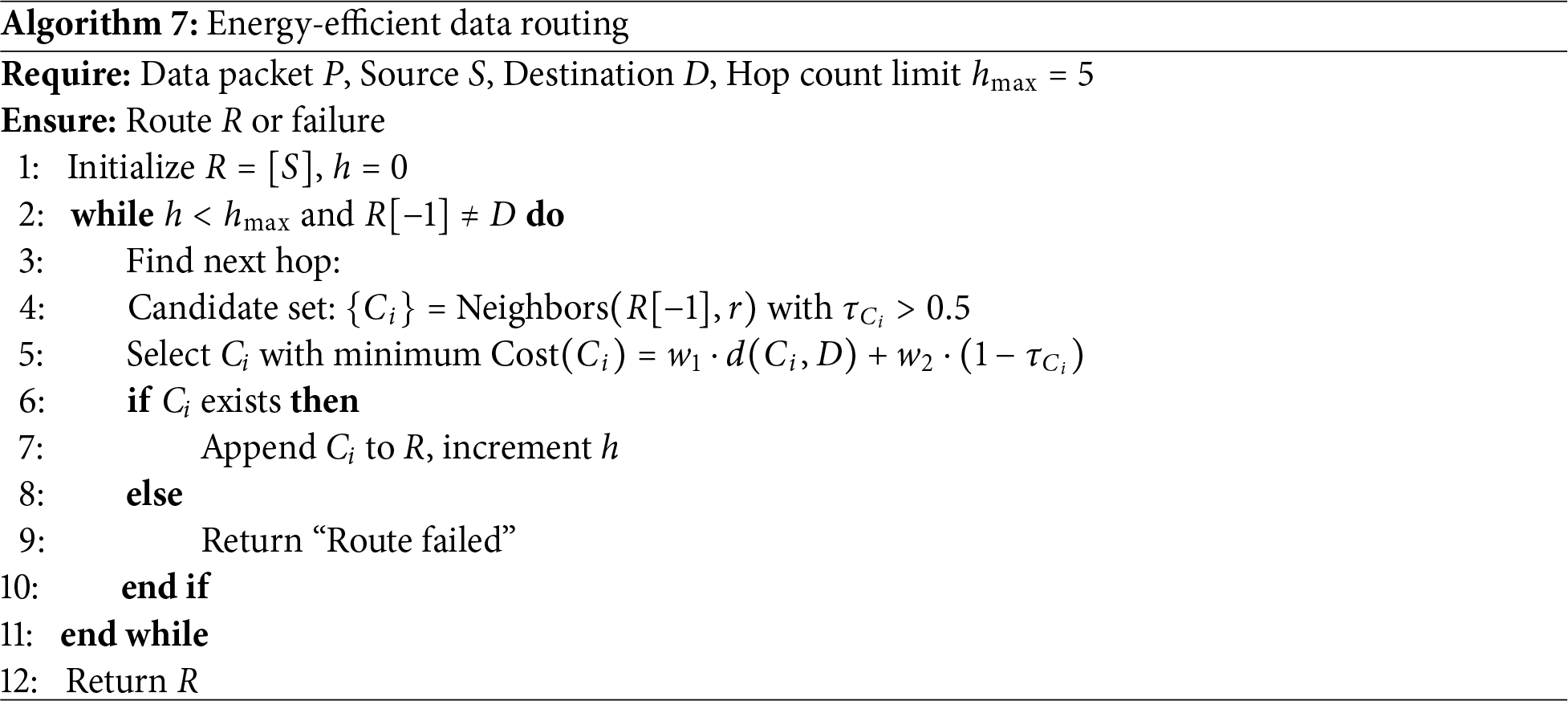
Routing Weight Sensitivity
Table 4 analyzes
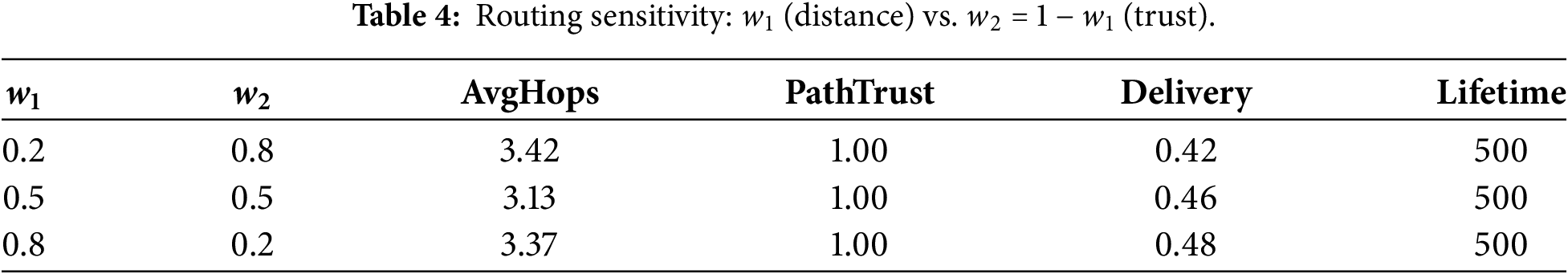
Fig. 3 visualizes the trade-off. This approach produces short, trustworthy paths reducing energy while maintaining reliability.
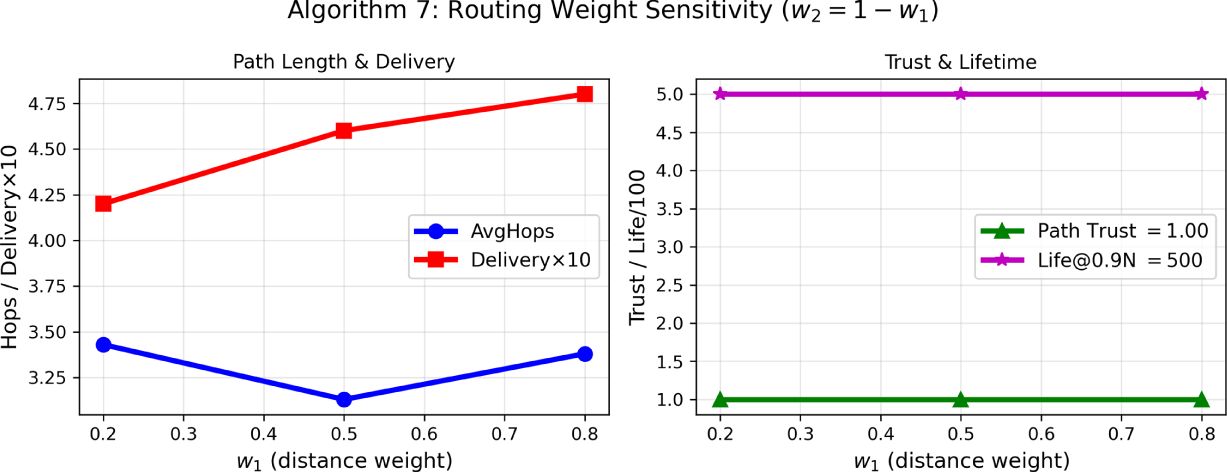
Figure 3: Routing weight sensitivity:
4.5 Role Rotation and Power-Saving
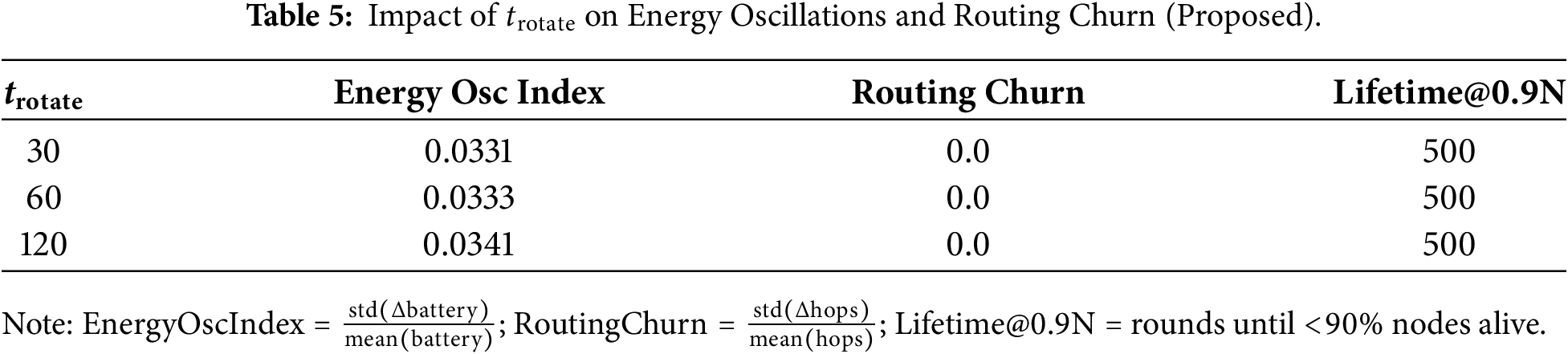
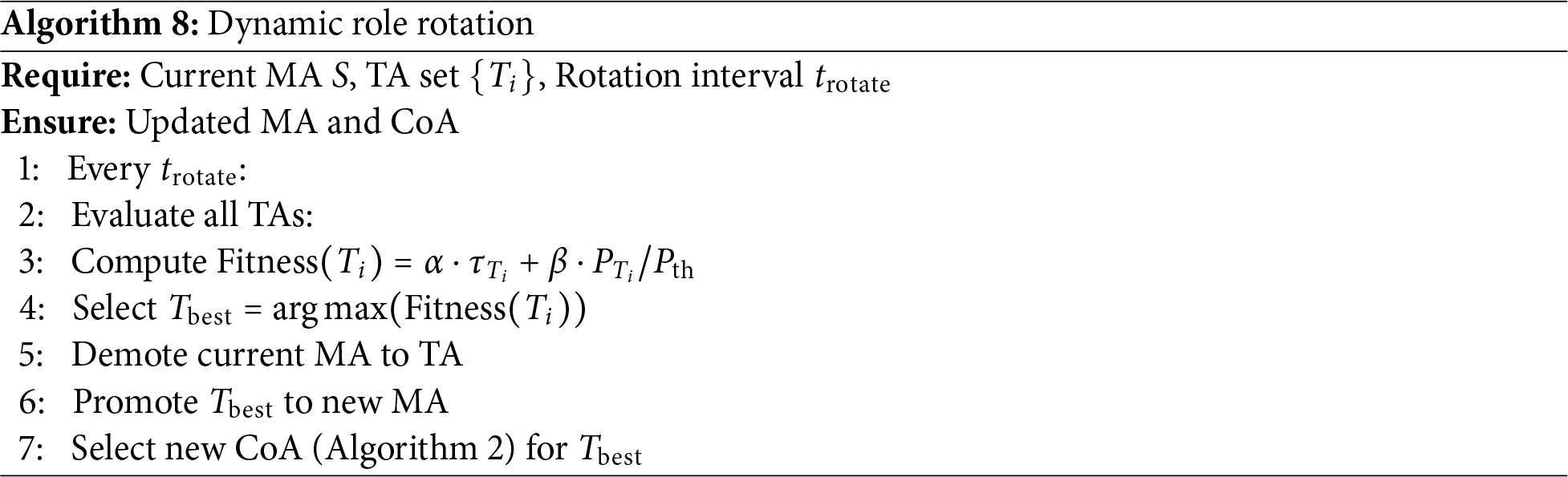
To avoid overusing particular nodes and to extend network lifetime, the framework periodically rotates roles Algorithm 8 and enables power-saving behavior for low-power TAs. In role rotation, well-powered, highly trusted TAs are promoted to MA positions, while exhausted nodes are relieved from leadership. The Dynamic Role Rotation algorithm formalizes this idea. At every interval
where
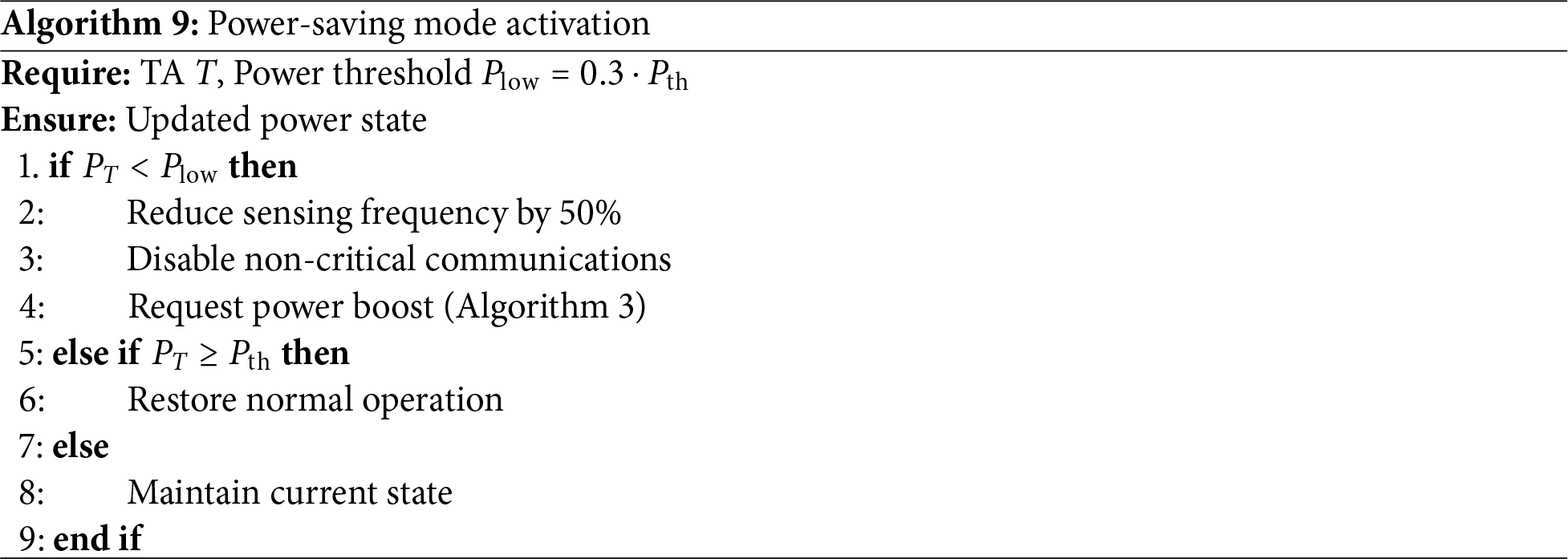
The Power-Saving Mode Activation Algorithm 9 provides an adaptive strategy for controlling TA activity based on energy levels. It uses two thresholds: a low-power threshold
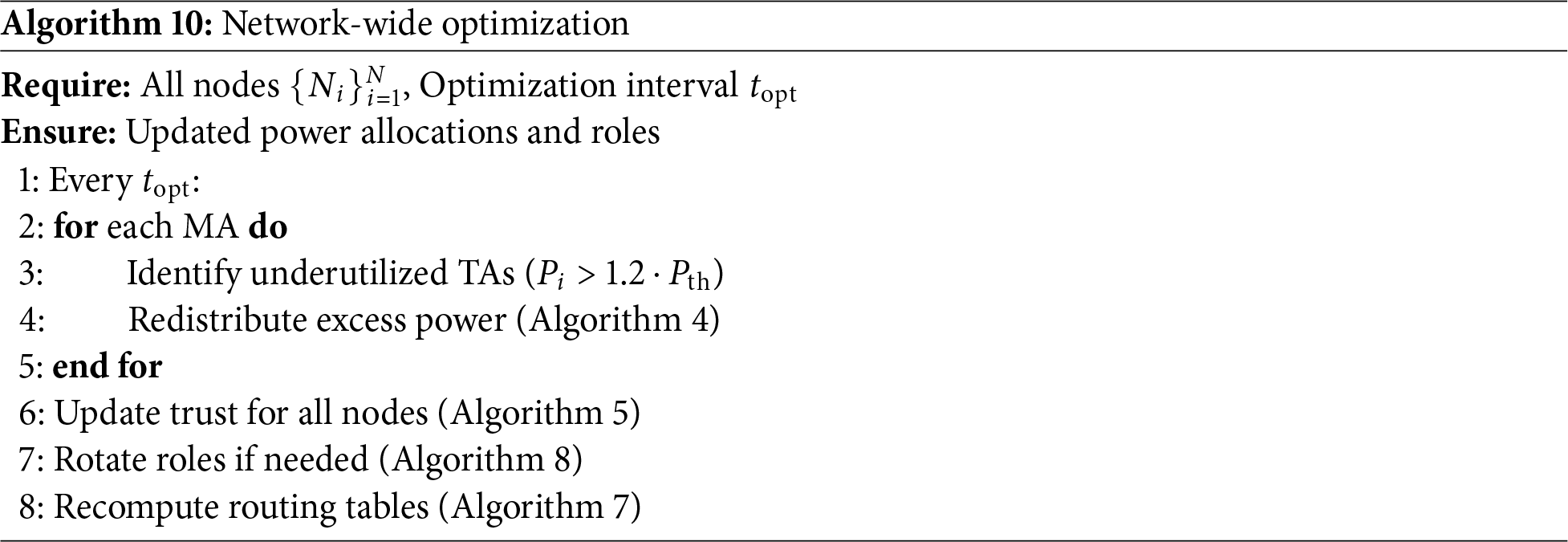
The Network-Wide Optimization Algorithm 10 coordinates resource management and role tuning across all N nodes,
4.7 Theoretical Analysis: Convergence, Stability, and Guarantees
4.7.1 Trust Evolution Convergence (Eq. (2))
Theorem 1: (Boundedness of Trust Values): For all nodes
Proof: Trust update (Eq. (2)):
Theorem 2: (Fixed-Point Convergence): Stationary
Proof: Recurrence:
4.7.2 Power Redistribution Invariants (Algorithm 4)
Theorem 3: (Global Energy Conservation):
Proof: Algorithm 4 conservative:
Theorem 4: (MA Safety Invariant): No Master Agent drops below
Proof: Induction: Algorithm 4 line 4 checks MA power
4.7.3 Coupled System Stability
Theorem 5: (Monotone Trust-Power Feedback): High-trust nodes prioritized (Eq. (5):
Low-trust deprioritized
Lemma 1: (Algorithm Complexities): Matches Section 5.8:
1. Trust: Bounded + exponential convergence.
2. Energy: Global conservation + MA protection.
3. Coupling: Beneficial feedback loop.
4. Complexity:
These explain constant lifetime and linear scaling.
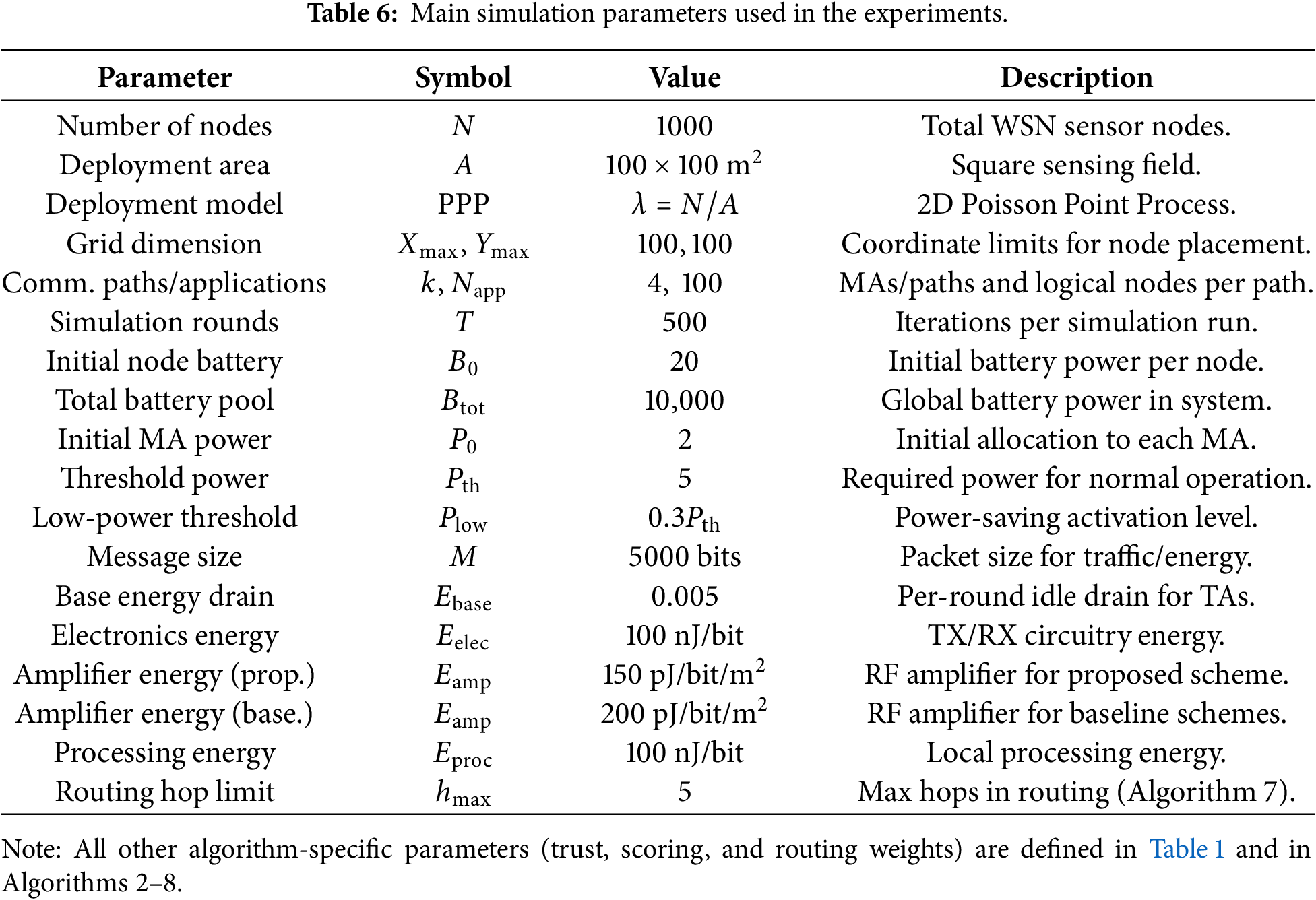
The effectiveness of the proposed agent based power management scheme is validated using simulation based experiments against established baselines: energy efficient low energy adaptive clustering hierarchy (EE-LEACH) [33], PEGASIS [34], and FEDLEARN [35]. The main simulation parameters are listed in Table 6. All the simulations are done in Python version 3.12.
5.1 Network Lifetime and Alive Nodes
The network lifetime of the network is shown with the number of alive nodes with respect to simulation rounds in Fig. 4. It can be seen the proposed method, along with EE-LEACH and FEDLEARN maintain all 1000 nodes alive for 500 rounds, demonstrating effective energy management and robustness. In contrast, PEGASIS breaks down much earlier: by around 130 rounds only 8 nodes are still alive, which shows how vulnerable a pure chain-based routing scheme is when power is limited. The Federated Learning baseline keeps all nodes alive for longer, but it does so at the cost of higher overall energy consumption.
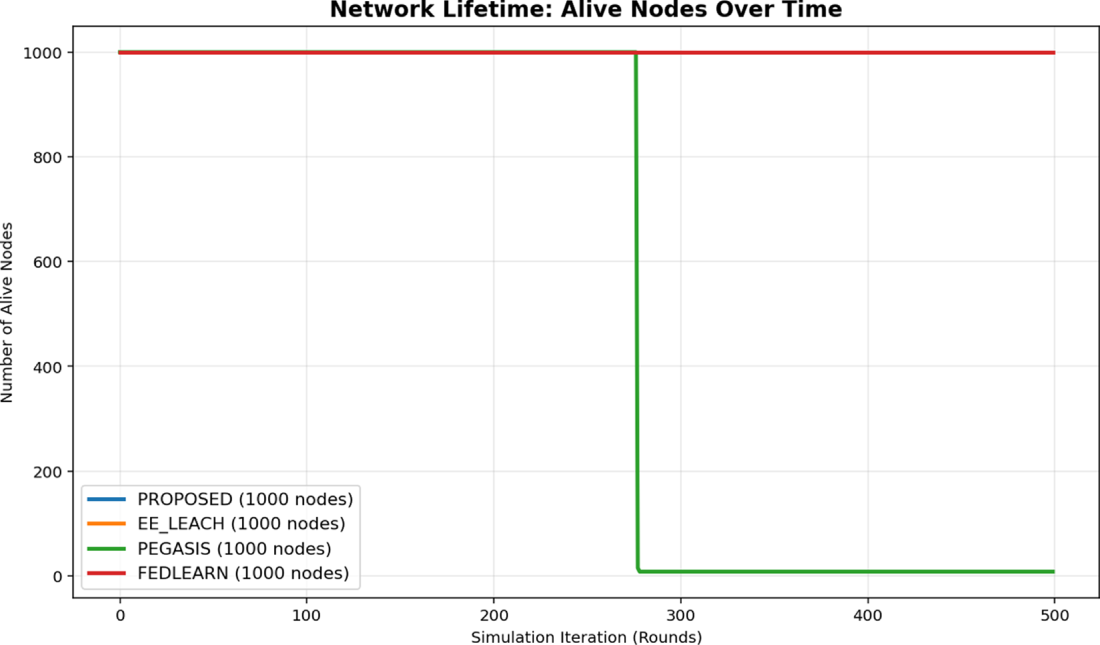
Figure 4: Network lifetime comparison.
The stability of the proposed scheme comes from how its main mechanisms work together. The hybrid CoA selection (Algorithm 2) places coordinators in energy-balanced locations so that no small region is overused, while the dynamic power redistribution (Algorithm 4) recovers and reallocates excess energy when needed. On top of this, the power-saving mode (Algorithm 9) prevents sudden failures of nodes by automatically throttling low-energy nodes, eventually help the network to maintain service for a longer time.
Th next Fig. 5 shows how the average trust value evolves over time. The proposed method keeps trust high and stable at around 0.78, which indicates reliable communication and a robust update process in Algorithm 5 that blends past behavior, power efficiency, and link quality. PEGASIS, on the other hand, cannot sustain trust because many nodes die early, so the average trust eventually drops to zero. EE-LEACH reaches the highest trust level (about 0.98), reflecting the benefits of clustering, but likely at the cost of higher energy use. The Federated Learning approach achieves a middle ground, maintaining trust at roughly 0.90 while still consuming more energy than the proposed scheme.
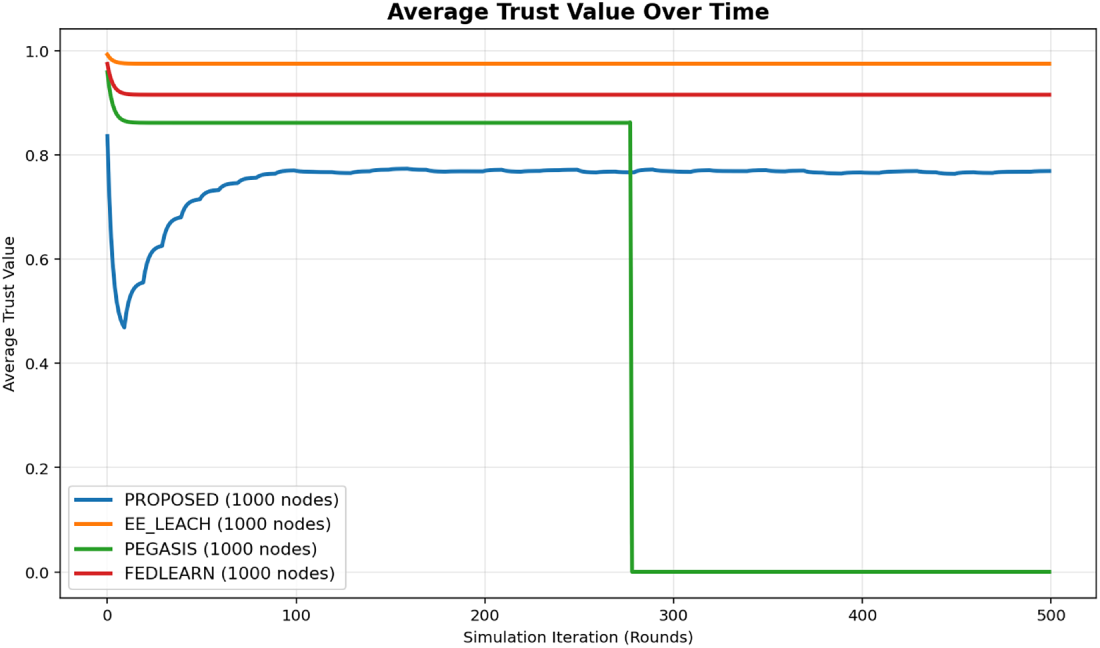
Figure 5: Average trust value evolution.
Therefore, by demoting low-trust nodes and reassigning their roles, the trust mechanism limits the influence of unreliable nodes and strengthens overall network reliability, which is crucial for consistent edge-computing performance.
It can be seen in Fig. 6 that the energy consumption the proposed method preserves battery power more effectively with balanced energy consumption compare to PEGASIS. In PEGASIS long chain transmissions drain nodes quickly, whereas EE-LEACH also performs well due to its clustering structure. But compare to all of these methods the Federated Learning approach introduces extra coordination overhead and therefore uses more energy overall.
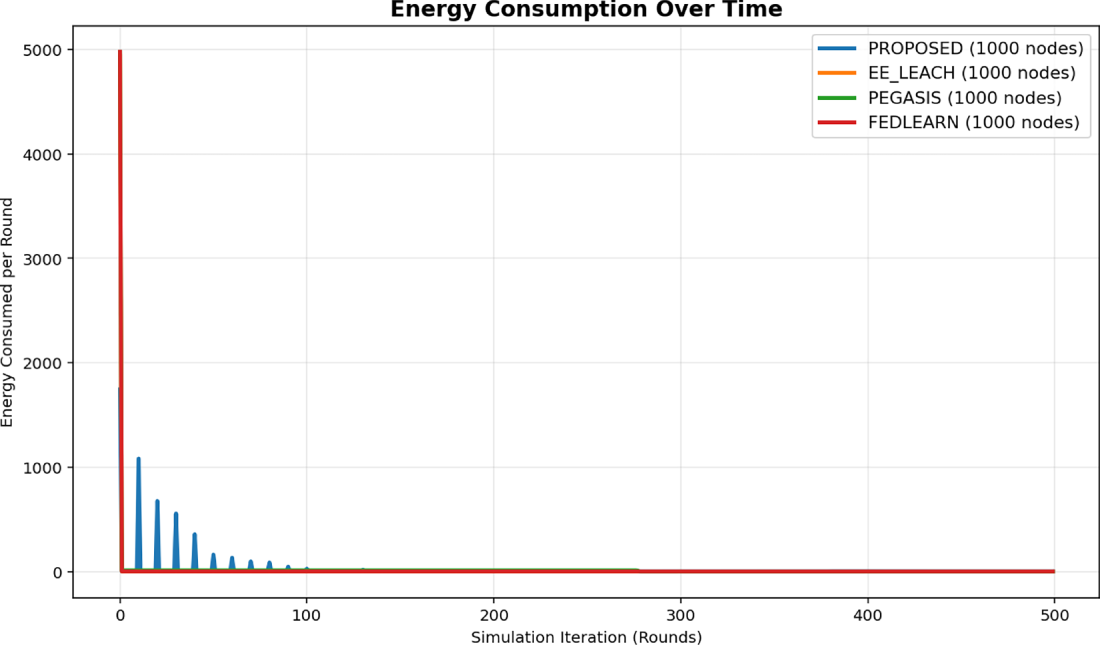
Figure 6: Comparison of energy consumption in the network.
In the proposed method combination of efficient power allocation, timely activation of power-saving mode, and dynamic redistribution of excess energy, extends node lifetime and cuts unnecessary energy use, which is an essential property for IoT edge devices that operate with very limited power budgets.
Fig. 7 shows the system throughput over time. PEGASIS reaches the highest peak throughput (about 18.94 Mbits) because it exploits long chain transmissions, but this behavior is short-lived and leads to an early network collapse, so it is not sustainable. The proposed scheme achieves a moderate throughput of roughly 1.96 Mbits per round, which ensures efficient data delivery rate and better energy efficiency for long-term operation at the edge. EE-LEACH and the Federated Learning baseline deliver higher throughput (around 4.9 Mbits), reflecting their different communication patterns, but they do so with additional costs in either scalability or resource usage.
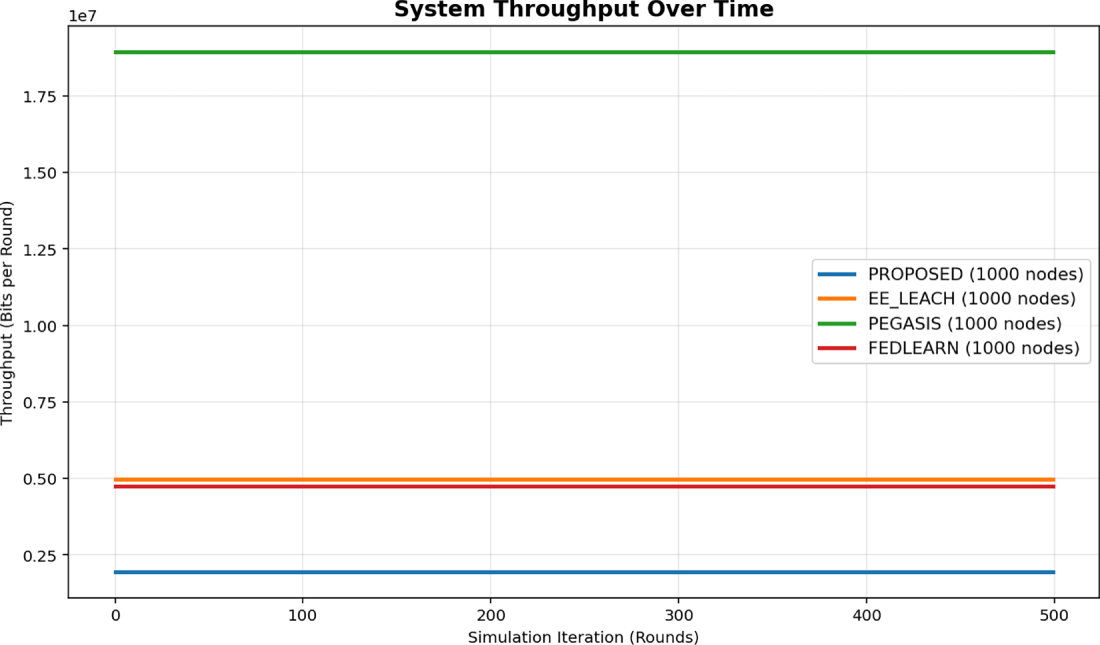
Figure 7: System throughput evolution.
This trade-off demonstrates a critical multi-objective optimization, where acceptable throughput is maintained while keeping the network alive for much longer, rather than maximizing data rate at the expense of network lifetime.
In Fig. 8, comparison of the average number of hops per data path is shown. The proposed scheme keeps the hop count at a moderate level (about 102), which is roughly 59% fewer hops than Federated Learning (249) and about 90% fewer than PEGASIS (996), showing that the CoA-based routing finds much shorter routes. EE-LEACH achieves the smallest hop count (around 20) because clustered nodes often communicate almost directly.
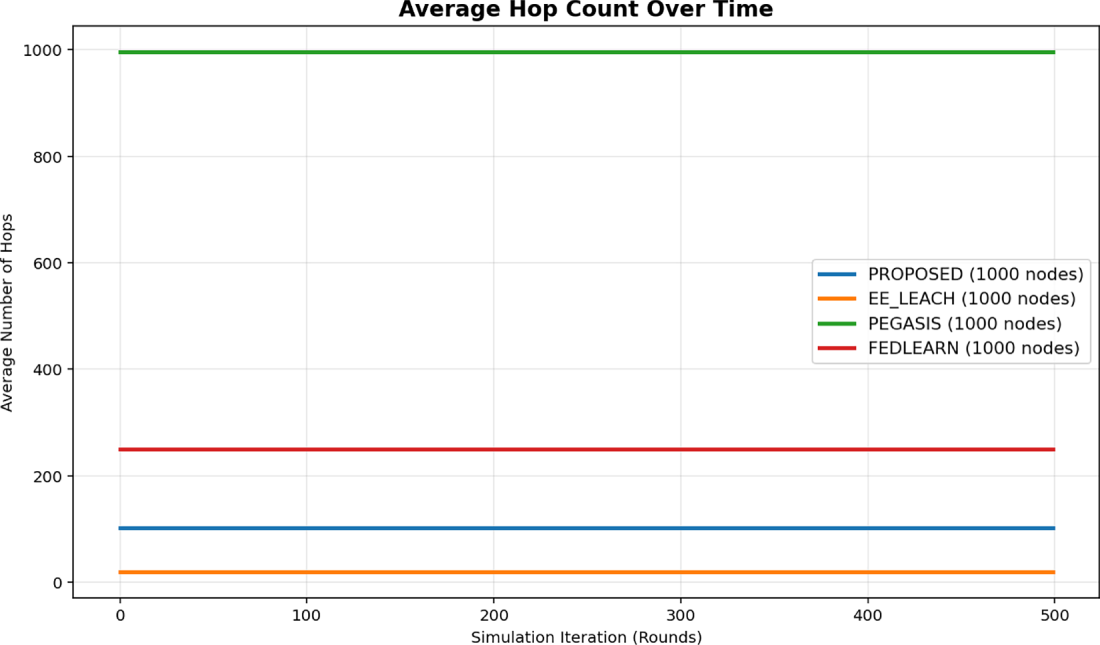
Figure 8: Average hop count comparison.
Fewer hops translate into lower delay and less cumulative energy use, indicating that the proposed routing successfully balances trust, distance, and power.
Fig. 9 shows how often nodes enter power-saving mode. In the proposed method, about 20%–30% of nodes are typically in power-saving state, which helps conserve energy and extend the network lifetime while still keeping the topology connected. PEGASIS, by contrast, rarely benefits from power-saving because nodes die quickly, leaving little opportunity for controlled savings.
Figure 9: Fraction of nodes in power-saving mode.
This behavior illustrates how the scheme reacts dynamically to node energy levels and traffic demand.
Fig. 10 plots the remaining global battery power. The proposed method preserves more residual energy throughout the simulation than both Federated Learning and PEGASIS, while EE-LEACH also performs well in terms of battery conservation. Effective power redistribution and fault-tolerant operation prevent unnecessary drain, which is critical for prolonging the lifetime of IoT edge nodes.
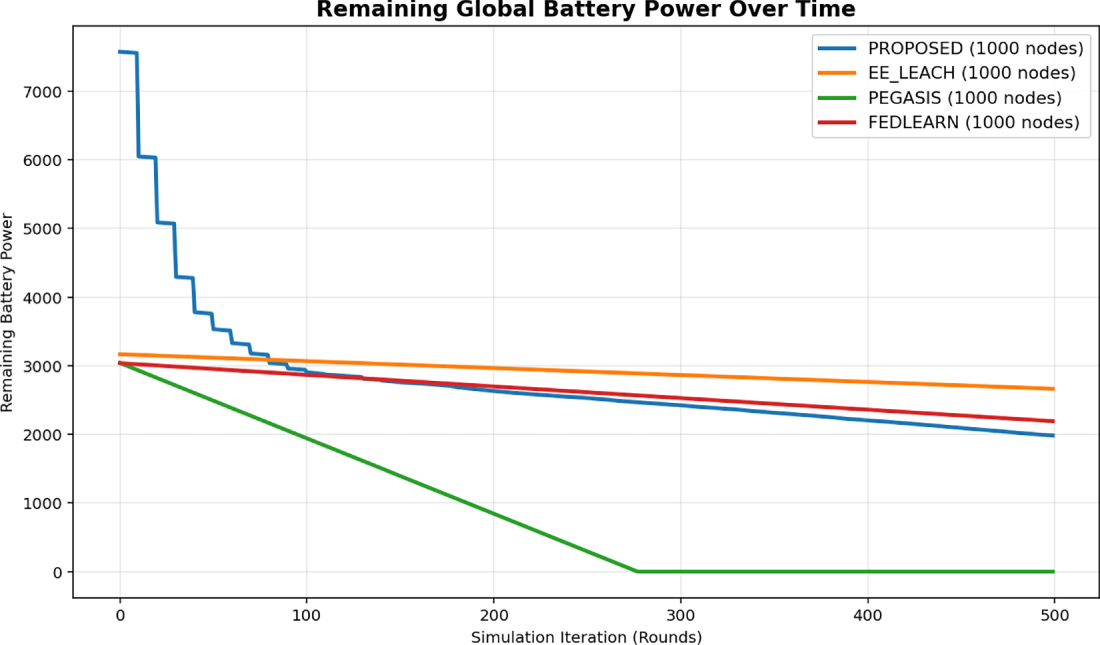
Figure 10: Remaining global battery power by different method.
5.8 Complexity and Scalability Analysis
Core algorithms exhibit the following per-round complexities:
Total:
5.8.2 Empirical Microbenchmarks
Microbenchmarks (Table 7) via ‘timeit' (200K iterations, N = 1000) confirm theoretical bounds. Algorithm 4 redistribution dominates 97% runtime (O(N) scans across 996 TAs), while CoA (Algorithm 2) identifies pruning opportunity. Total 387 ms/round scales linearly, enabling
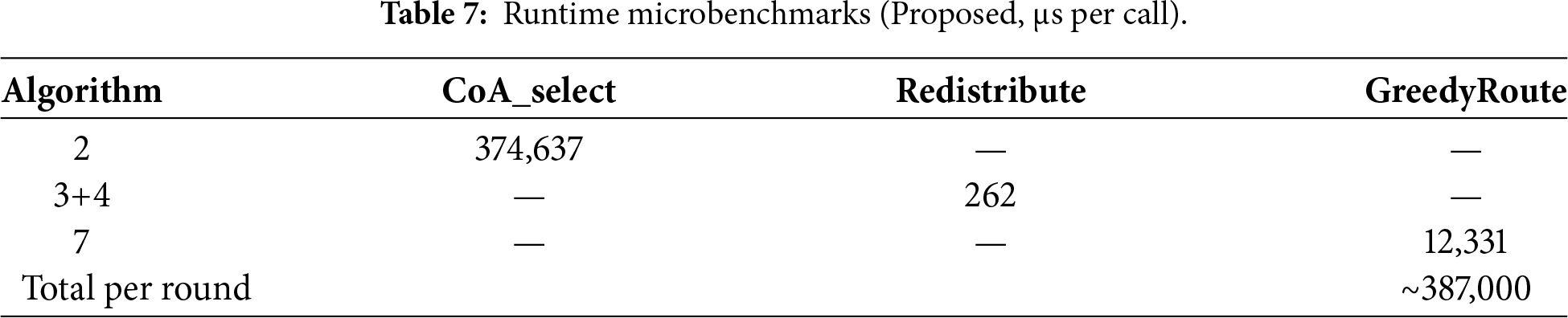
Table 7 shows ‘timeit’ results (200K iterations, N = 1000).
Dominant messages per round total
• Power requests:
• Heartbeats:
• Role updates:
• Data packets:
Empirical validation: constant 102 hops across N = 500–1500 (Table 8) confirms
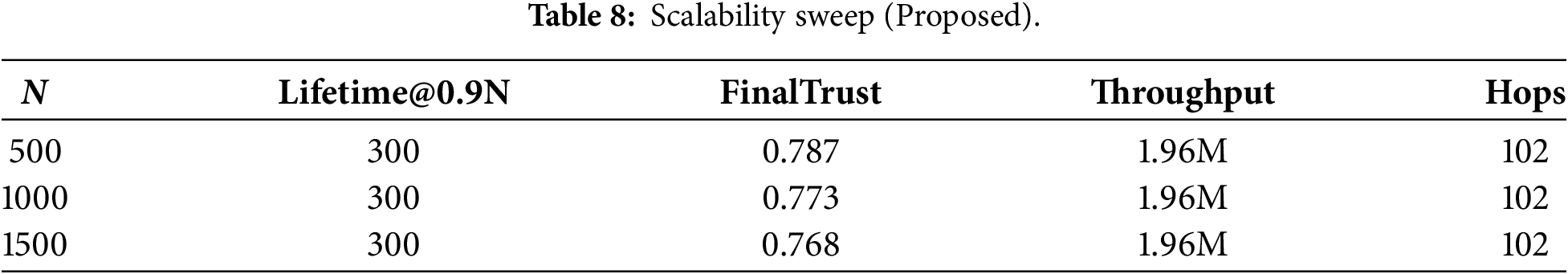
Table 8 validates scalability for
5.9 Adversarial Robustness Analysis
To evaluate resilience against malicious behavior, we implemented a composite attack combining trust inflation (malicious nodes initialize
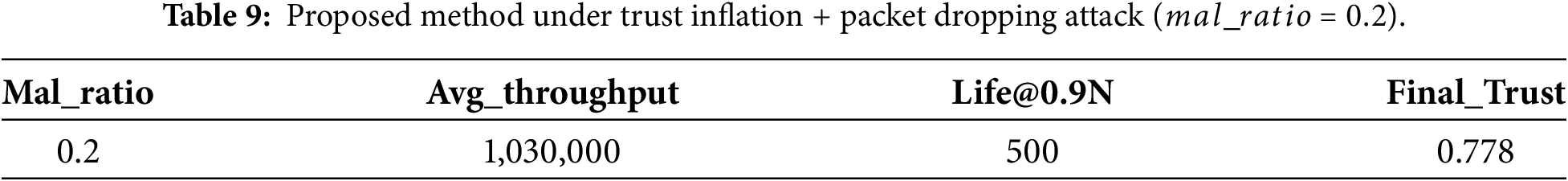
The scheme maintains stable trust (0.778) and full lifetime despite attack, confirming that the weighted trust update (Eq. (2)) and periodic decay effectively counter inflation attacks. Packet dropping reduces throughput proportionally to malicious density, but does not cascade to premature node death or trust collapse.
5.10 Performance Summary and Discussion
The baseline performance comparison metrics after 500 rounds are summarized in Table 10.
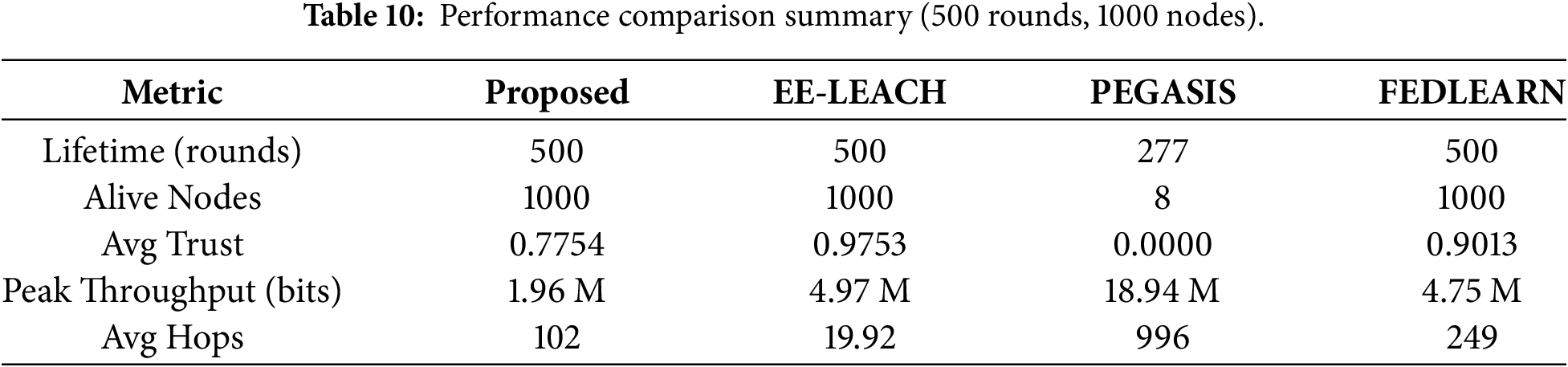
From the earlier discussed simulation results, analysis, and performance table, it can be found that the proposed scheme is robust and mainly contributes with three key advantages, which are essential for scalable, energy-efficient edge WSNs:
• It provides an optimal tradeoff between network longevity and throughput rates, which offers more sustainable operation compared to PEGASIS, which quickly drains the network with short bursts of high throughput.
• The lower number of hop counts compared to FEDLEARN and PEGASIS defines the reduction of packet forwarding cost by building shorter paths. Also trust-based node selection in path establishment ensures network stability simultaneously.
• The power-saving mode in the proposed scheme preserves energy by scaling back a specific node’s activity when the battery is low, which prevents disruption of the service. This phenomenon supports WSNs at the edge to adapt dynamic topologies over several applications in resource-constrained network.
Therefore, this non-cluster, agent-based approach delivers better results compared to cluster-based EE-LEACH in terms of greater flexibility for heterogeneous, multi-path deployments and also cost-effectiveness with respect to the overhead cost and longer routes compared to the Federated Learning baseline. These strong claims with comprehensive results validate the applicability and advantages of the agent-based power management framework as a multi-objective solution for real-world wireless sensor networks operating in energy-constrained edge computing environments.
This paper proposed an agent-based power management scheme for wireless sensor networks operating in edge computing environments. The framework organizes nodes into Master Agents (MAs), Coordination Agents (CoAs), and Task Agents (TAs), and combines Poisson-based deployment, hybrid CoA selection, trust-aware power allocation, and energy-efficient routing. This integrated approach provides a flexible alternative to traditional cluster-based approaches for heterogeneous, multi-path WSNs. The proposed scheme is justified with simulation results, which confirm its importance as robust and energy efficient by balancing moderate throughput and trust levels and significantly extending network lifetime. Compared with the relevant previous works and baseline approaches, it outperforms PEGASIS and Federated Learning baselines in terms of preserving a larger fraction of alive nodes over time, sustaining higher residual battery energy, and reducing the average hop count, all while keeping the average trust value stable. Also, it shows that as a non-cluster-based scheme, the proposed method is more efficient in WSNs over edge compared to EE-LEACH. The hybrid CoA selection and dynamic power redistribution modules were particularly effective in avoiding energy hotspots and reallocating excess power, whereas the trust update and fault recovery mechanisms limited the impact of unreliable nodes.
Overall, the proposed agent-based scheme offers a practical multi-objective solution that jointly optimizes energy efficiency, reliability, and routing performance for real-world WSN deployments in energy-constrained edge computing environments. Future work can be extended by considering extended mobility-aware framework by integrating learning-based prediction of traffic and energy demand and validating the approach on hardware testbeds for larger-scale deployments.
Acknowledgement: None.
Funding Statement: This research received no external funding.
Author Contributions: Conceptualization, Pratik Goswami, and Hamid Naseem; methodology, Pratik Goswami and Khizar Abbas; software, Pratik Goswami, and Khizar Abbas; validation, Pratik Goswami, Hamid Naseem, and Kwonhue Choi; formal analysis, Pratik Goswami; investigation, Pratik Goswami, Hamid Naseem, and Khizar Abbas; resources, Kwonhue Choi; data curation, Pratik Goswami; writing—original draft preparation, Pratik Goswami, and Khizar Abbas; writing—review and editing, Pratik Goswami, Kwonhue Choi, and Hamid Naseem; visualization, Pratik Goswami, and Khizar Abbas; supervision, Kwonhue Choi; project administration, Kwonhue Choi; funding acquisition, Khizar Abbas. All authors reviewed and approved the final version of the manuscript.
Availability of Data and Materials: The data supporting the findings of this study were generated through in-house simulations using the agent-based WSN power management framework described in this article. The simulation code and generated datasets are available from the corresponding authors on reasonable request.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest.
Appendix A
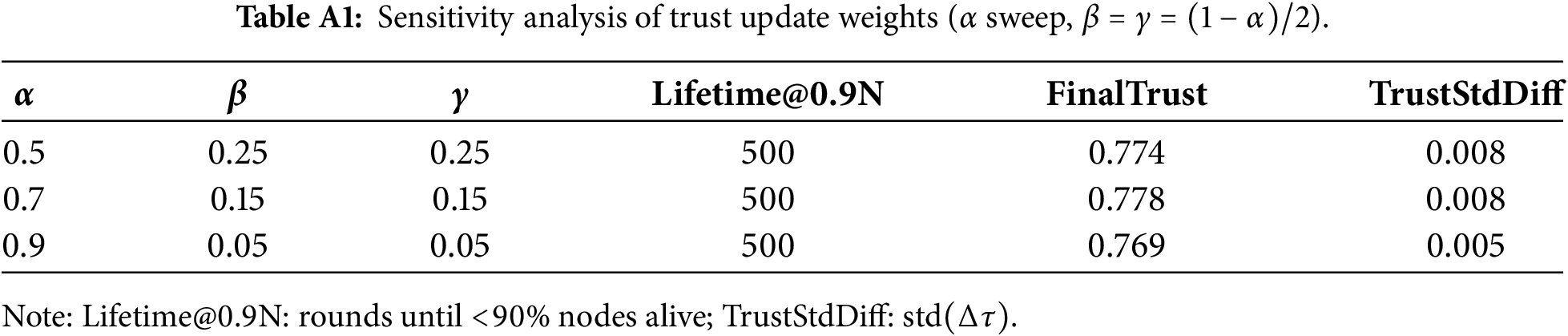
Appendix A.1 Trust Update Weights Selection:
Sensitivity analysis: (Table A1) over
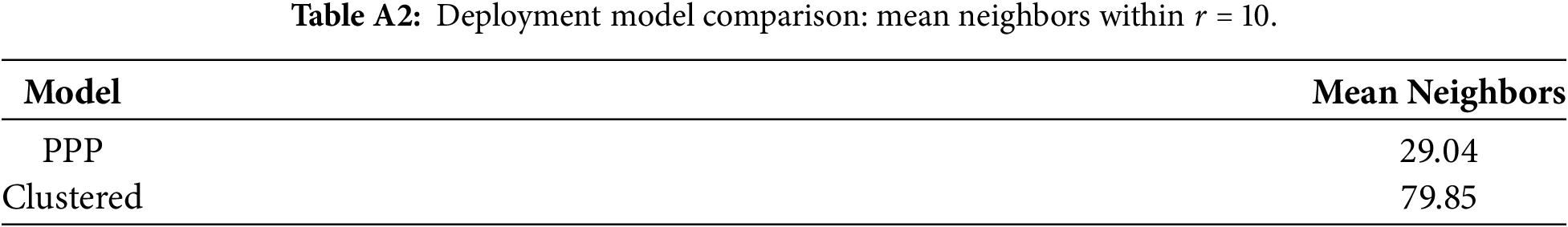
Appendix A.2 PPP under Clustered or Mobility-Aware Deployments (Non-Homogeneous Nodes):
While PPP provides a spatial baseline, V-IoT scenarios exhibit clustered (vehicles/hotspots) and mobile topologies. We extended the simulator with:
1. Clustered deployment: 3 Gaussian clusters (
2. Mobility model: Random walk (step radius = 5 every 10 rounds)
Table A2 confirms CoA selection adapts to heterogeneity, with clustered deployments yielding richer neighbor sets for improved coordination.
References
1. Martalò M, Pettorru G, Atzori L. A cross-layer survey on secure and low-latency communications in next-generation IoT. IEEE Trans Netw Serv Manag. 2024;21(4):4669–85. doi:10.1109/TNSM.2024.3390543. [Google Scholar] [CrossRef]
2. Porambage P, Okwuibe J, Liyanage M, Ylianttila M, Taleb T. Survey on multi-access edge computing for internet of things realization. IEEE Commun Surv Tutor. 2018;20(4):2961–91. doi:10.1109/comst.2018.2849509. [Google Scholar] [CrossRef]
3. Römer K, Mattern F. The design space of wireless sensor networks. IEEE Wirel Commun. 2004;11(6):54–61. doi:10.1109/mwc.2004.1368897. [Google Scholar] [CrossRef]
4. Akyildiz IF, Su W, Sankarasubramaniam Y, Cayirci E. A survey on sensor networks. IEEE Commun Mag. 2002;40(8):102–14. doi:10.1109/mcom.2002.1024422. [Google Scholar] [CrossRef]
5. Culler D, Estrin D, Srivastava M. Overview of sensor networks. IEEE Comput. 2004;37(8):41–9. [Google Scholar]
6. Heinzelman WB, Murphy AL, Carvalho HS, Perillo MA. Middleware to support sensor network applications. IEEE Netw. 2004;18(1):6–14. doi:10.1109/mnet.2004.1265828. [Google Scholar] [CrossRef]
7. Chang JH, Tassiulas L. Maximum lifetime routing in wireless sensor networks. IEEE/ACM Trans Netw. 2004;12(4):609–19. doi:10.1109/tnet.2004.833122. [Google Scholar] [CrossRef]
8. Chase J. The evolution of the internet of things. Dallas, TX, USA: Texas Instruments; 2013. [Google Scholar]
9. Bandyopadhyay D, Sen J. Internet of things: applications and challenges in technology and standardization. Wirel Pers Commun. 2011;58(1):49–69. doi:10.1007/s11277-011-0288-5. [Google Scholar] [CrossRef]
10. Stankovic JA. Research directions for the internet of things. IEEE Internet Things J. 2014;1(1):3–9. doi:10.1109/jiot.2014.2312291. [Google Scholar] [CrossRef]
11. Maiti M, Ghosh U. Next generation internet of things in fintech ecosystem. IEEE Internet Things J. 2021;10(3):2104–11. doi:10.1109/JIOT.2021.3063494. [Google Scholar] [CrossRef]
12. Goswami P, Mukherjee A, Maiti M, Tyagi SKS, Yang L. A neural network based optimal resource allocation method for secure IIoT network. IEEE Internet Things J. 2021;9(4):2538–44. doi:10.1109/JIOT.2021.3084636. [Google Scholar] [CrossRef]
13. Li X, Zhu L, Chu X, Fu H. Edge computing-enabled wireless sensor networks for multiple data collection tasks in smart agriculture. J Sens. 2020;1(1):1–9. doi:10.1155/2020/4398061. [Google Scholar] [CrossRef]
14. Abu Salem AO, Shudifat N. Enhanced LEACH protocol for increasing a lifetime of WSNs. Pers Ubiquitous Comput. 2019;23(5):901–7. doi:10.1007/s00779-019-01205-4. [Google Scholar] [CrossRef]
15. Aslam N, Phillips W, Robertson W, Sivakumar S. A multi-criterion optimization technique for energy efficient cluster formation in wireless sensor networks. Inf Fusion. 2011;12(3):202–12. doi:10.1016/j.inffus.2010.11.001. [Google Scholar] [CrossRef]
16. Ali A, Ming Y, Si T, Iram S, Chakraborty S. Enhancement of RWSN lifetime via firework clustering algorithm validated by ANN. Information. 2018;9(3):1–13. doi:10.3390/info9030060. [Google Scholar] [CrossRef]
17. Kang SH, Nguyen T. Distance based thresholds for cluster head selection in wireless sensor networks. IEEE Commun Lett. 2012;16(9):1396–9. doi:10.1109/LCOMM.2012.072012.120712. [Google Scholar] [CrossRef]
18. Xu Z, Chen L, Chen C, Guan X. Joint clustering and routing design for reliable and efficient data collection in large-scale wireless sensor networks. IEEE Internet Things J. 2016;3(4):520–32. doi:10.1109/JIOT.2016.2553121. [Google Scholar] [CrossRef]
19. Hosseingholizadeh A, Abhari A. A new agent-based solution for wireless sensor networks management. In: Proceedings of the 12th Communications and Networking Simulation Symposium (CNS); 2009 Mar 22–27; San Diego, CA, USA. [Google Scholar]
20. Sardouk A, Rahim-Amoud R. A strategy for multi-agent based wireless sensor network optimization. In: Proceedings of the Third International Conference on Autonomous Infrastructure, Management and Security, AIMS 2009; 2009 Jun 30–Jul 2; Enschede, The Netherlands. [Google Scholar]
21. Lee J, Kao T. An improved three-layer low-energy adaptive clustering hierarchy for wireless sensor networks. IEEE Internet Things J. 2016;3(6):951–8. doi:10.1109/JIOT.2016.2565519. [Google Scholar] [CrossRef]
22. Saleh A, Joshi P, Rathore RS, Sengar SS. Trust-aware routing mechanism through an edge node for IoT-Enabled sensor networks. Sensors. 2022;22(20):820. doi:10.3390/s2220820. [Google Scholar] [CrossRef]
23. Zhou Z, Qian L, Xu H. Decentralized multi-agent reinforcement learning for large-scale mobile wireless sensor network control using mean field games. In: 33rd International Conference on Computer Communications and Networks (ICCCN); 2024 Jul 29–Aug 1; Kailua-Kona, HI, USA. p. 1–6. doi:10.1109/ICCCN61486.2024.10637582. [Google Scholar] [CrossRef]
24. Soltani P, Eskandarpour M, Ahmadizad A, Soleimani H. Energy-efficient routing algorithm for wireless sensor networks based on multi-agent reinforcement learning. arXiv:2508.14679. 2025. [Google Scholar]
25. Liu J, Shou G, Liu Y, Hu Y, Guo Z. Performance evaluation of integrated multi-access edge computing and fiber-wireless access networks. IEEE Access. 2018;6:30269–79. doi:10.1109/access.2018.2833619. [Google Scholar] [CrossRef]
26. Luo R, Jin H, He Q, Wu S, Xia X. Cost-effective edge server network design in mobile edge computing environment. IEEE Trans Sustain Comput. 2022;7(4):839–50. doi:10.1109/TSUSC.2022.3178661. [Google Scholar] [CrossRef]
27. Shabariram CP, Shanthi N, Ponnuswamy PP, Subramaniyaswamy V, Sathana V. Resource allocation in edge computing environment using deterministic policy gradient algorithm. In: Proceedings of the 2024 10th International Conference on Advanced Computing and Communication Systems (ICACCS); 2024 Mar 14–15; Coimbatore, India. p. 473–8. doi:10.1109/ICACCS60874.2024.10717103. [Google Scholar] [CrossRef]
28. Zhou J, Pal S, Dong C, Wang K. Enhancing quality of service through federated learning in edge-cloud AIoT systems. Ad Hoc Netw. 2024;153:103346. doi:10.1016/j.adhoc.2024.103346. [Google Scholar] [CrossRef]
29. Qi Y, Feng Y, Wang X, Li H, Tian J. Leveraging federated learning and edge computing for recommendation systems within cloud computing networks. arXiv:2403.03165. 2024. [Google Scholar]
30. El-Sayed HH, Abd-Elgaber EM, Zanaty EA, Alsubaei FS, Almazroi AA, Bakheet SS. An efficient neural network LEACH protocol to extended lifetime of wireless sensor networks. Sci Rep. 2024;14(1):26943. doi:10.1038/s41598-024-75904-1. [Google Scholar] [PubMed] [CrossRef]
31. Mukherjee A, Goswami P, Ayoub Khan M, Li M, Yang L, Pillai P. Energy efficient resource allocation strategy in massive IoT for industrial 6G applications. IEEE Internet Things J. 2021;8(7):5194–201. doi:10.1109/JIOT.2020.3035608. [Google Scholar] [CrossRef]
32. Mukherjee A, Goswami P, Yang L. Distributed artificial intelligence based cluster head power allocation in cognitive radio sensor networks. IEEE Sensor Lett. 2019;3(8):1–4. doi:10.1109/LSENS.2019.2933908. [Google Scholar] [CrossRef]
33. Heinzelman W, Chandrakasan A, Balakrishnan H. An application-specific protocol architecture for wireless microsensor networks. IEEE Trans Wirel Commun. 2002;1(4):660–70. doi:10.1109/TWC.2002.804190. [Google Scholar] [CrossRef]
34. Lindsey S, Raghavendra CS. PEGASIS: Power-efficient gathering in sensor information systems. In: Proceedings of IEEE Aerospace Conferences; 2002 Mar 9–16; Big Sky, MT, USA. doi:10.1109/AERO.2002.1035242. [Google Scholar] [CrossRef]
35. Sattler F, Wiedemann S, Müller K-R, Samek W. Robust and communication-efficient federated learning from non-i.i.d. data. IEEE Trans Neural Netw Learn Syst. 2020;31(9):3400–13. doi:10.1109/TNNLS.2019.2944481. [Google Scholar] [PubMed] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF Downloads
Downloads
 Citation Tools
Citation Tools