 Open Access
Open Access
REVIEW
Security and Privacy Challenges, Solutions, and Performance Evaluation in AIoT-Enabled Smart Societies
1 School of Arts and Creative Technology, University of Greater Manchester, Manchester Bolton, UK
2 School of Computer Science, National College of Business Administration and Economics, Lahore, Pakistan
3 Department of Computer Science and Information Technology, School Education Department, Government of Punjab, Layyah, Pakistan
4 Depertment of Computer Science, Virtual University of Pakistan, Lahore, Pakistan
5 Department of Computer and Software Technology, University of Swat, Swat, Pakistan
6 Faculty of Engineering, Université de Moncton, Moncton, NB, Canada
7 School of Electrical Engineering, University of Johannesburg, Johannesburg, South Africa
8 International Institute of Technology and Management (IITG), Av. Grandes Ecoles, Libreville, Gabon
9 Bridges for Academic Excellence-Spectrum, Tunis, Tunisia
* Corresponding Author: Tehseen Mazhar. Email:
(This article belongs to the Special Issue: Next-Generation Intelligent Networks and Systems: Advances in IoT, Edge Computing, and Secure Cyber-Physical Applications)
Computer Modeling in Engineering & Sciences 2026, 146(3), 7 https://doi.org/10.32604/cmes.2026.075882
Received 10 November 2025; Accepted 29 January 2026; Issue published 30 March 2026
Abstract
The convergence of Artificial Intelligence (AI) and the Internet of Things (IoT) has enabled Artificial Intelligence of Things (AIoT) systems that support intelligent and responsive smart societies, but it also introduces major security and privacy concerns across domains such as healthcare, transportation, and smart cities. This Systemic Literature Review (SLR) addresses three research questions: identifying major threats and challenges in AIoT ecosystems, reviewing state-of-the-art security and privacy techniques, and evaluating their effectiveness. An SLR covering the period from 2020 to 2025 was conducted using major academic digital libraries, including IEEE Xplore, ACM Digital Library, ScienceDirect, SpringerLink, and Wiley Online Library, with a focus on security- and privacy-enhancing techniques such as blockchain, federated learning, and edge AI. The SLR identifies key challenges including data privacy leakage, authentication, cloud dependency, and attack surface expansion, and finds that emerging techniques, while promising, often involve trade-offs related to latency, scalability, and compliance. The study highlights future directions including lightweight cryptography, standardization, and explainable AI to support secure and trustworthy AIoT-enabled smart societies.Keywords
The convergence of Artificial Intelligence (AI) and the Internet of Things (IoT) has resulted in the emergence of the Artificial Intelligence of Things (AIoT), a technological paradigm that enables intelligent, autonomous, and interconnected environments known as smart societies [1]. AIoT can be defined as an integrated paradigm in which IoT devices sense and exchange data while AI models perform learning, inference, and optimization—often at the edge and/or cloud—to enable context-aware and autonomous decision-making in real time. Internet of Things (IoT) began as networks of connected sensors and devices that mostly collected and transmitted data. The field has since evolved into Artificial Intelligence of Things (AIoT), where these devices also analyze, learn from, and act on data autonomously [2]. This shift is driven by advances in AI, edge computing, and cheap, powerful hardware [3]. These societies are underpinned by a network of AI-empowered IoT devices that collaborate to enhance life quality across domains such as healthcare, transportation, manufacturing, and urban infrastructure [4]. AIoT systems facilitate real-time data acquisition, contextual analysis, and autonomous decision-making, thus transforming conventional environments into responsive ecosystems [5]. In applications such as smart homes, intelligent healthcare systems, and autonomous transportation, AIoT significantly improves operational efficiency, predictive capabilities, and user personalization [6]. However, this convergence also raises serious concerns regarding security, privacy, and ethical data governance. The simultaneous integration of AI with the IoT has greatly accelerated the development of AI-of-Things (AIoT) systems, which assess and react to environmental stimuli more intelligently without the need for human intervention. However, the negative effects of data volume, velocity, and veracity, as well as catastrophic transmission latency on networking infrastructures, make processing large amounts of data on the cloud difficult or impossible [7].
AIoT systems are commonly described through a layered architecture that includes (i) a perception/sensing layer for data acquisition from heterogeneous devices, (ii) a communication/network layer for reliable data transfer, (iii) an edge/fog intelligence layer that performs low-latency analytics and on-device inference under resource constraints, (iv) a cloud layer that supports large-scale storage and model training, and (v) an application and decision layer that delivers services and automated actuation within smart society domains.
Despite the transformative potential of AIoT, the deployment of these systems in smart societies introduces new vulnerabilities [8]. The proliferation of devices increases the surface area for cyberattacks, while the sensitive nature of the data being exchanged especially in healthcare and smart governance exacerbates privacy risks [9]. Traditional security mechanisms such as centralized access control and standard encryption are often inadequate for heterogeneous, decentralized AIoT architectures [10]. Emerging attacks, including adversarial manipulation of AI models, data poisoning, and device spoofing, further complicate the deployment of secure AIoT systems [11]. These challenges necessitate a new generation of lightweight, scalable, and privacy-preserving solutions that are specifically designed for AIoT-enabled environments as shown in Fig. 1.
Figure 1: The importance of smart societies and key challenges in AIoT-enabled environments. This figure illustrates the role of AIoT as an enabling layer for smart societies across domains such as healthcare, transportation, smart cities, and industry. It highlights the major security and privacy challenges introduced by AIoT deployment, including data privacy leakage, authentication and access control issues, cloud dependency, scalability constraints, and attack surface expansion, which motivate the need for advanced security and privacy-preserving mechanisms.
As AIoT becomes a foundational technology in smart societies, ensuring its security and privacy remains a critical research problem. The dynamic and distributed nature of AIoT systems, coupled with limited computational resources of edge devices, renders conventional security approaches inefficient or infeasible [12].
Moreover, current literature lacks a consolidated understanding of how recent state-of-the-art mechanisms, such as blockchain, AI, machine learning (ML), federated learning, and trusted execution environments, can be applied effectively across application domains [13]. In addition, there is a need for a structured synthesis that links (i) AIoT applications, (ii) security and privacy challenges, and (iii) evidence reported in real-world or simulated evaluations to support design and deployment decisions in smart society environments [14].
1.5 Scope and Objectives of the Study
This systematic literature review (SLR) provides a comprehensive analysis of recent advancements in securing AIoT systems within the context of smart societies. The SLR is guided by three core research questions. First, it identifies the applications of AIoT in smart society environments and the emerging security and privacy challenges associated with deployment. Second, it examines state-of-the-art techniques and frameworks proposed to mitigate these challenges and considers their effectiveness across application domains. Third, it evaluates how these mechanisms perform under real-world or simulated conditions, with emphasis on scalability, reliability, and compliance with privacy and security standards, as shown in Fig. 2. This SLR analyzes peer-reviewed literature from 2020 to 2025 to extract key themes, classify solutions, assess efficacy, and identify open research challenges.
Figure 2: Motivation and primary research focus of the systematic literature review. This figure summarizes the motivation behind the study and its primary research focus by linking AIoT applications in smart societies with emerging security and privacy challenges. It visually connects the identified challenges to the three research questions (RQ1–RQ3), emphasizing the need to analyze applications, mitigation techniques, and performance evaluation in secure AIoT ecosystems.
1.6 Contributions of the Study
To clearly distinguish the manuscript’s contributions from the background and motivation, the contributions are summarized below in a compact form:
• Categorizes and synthesizes AIoT security and privacy challenges in smart society environments, with emphasis on encryption, access control, federated learning, and blockchain integration.
• Systematically analyzes emerging threats affecting large-scale AIoT deployments in domains such as smart cities, healthcare, and transportation.
• Compares state-of-the-art security and privacy frameworks for AIoT ecosystems, highlighting their effectiveness and limitations across application contexts.
• Synthesizes evidence from real-world and simulated evaluations, emphasizing scalability, reliability, latency, and regulatory compliance.
• Identifies research gaps and outlines future directions, including standardization, lightweight cryptographic protocols, and ethically aligned AI design for secure AIoT systems.
• Provides a multidisciplinary synthesis spanning AI, IoT, and cybersecurity, offering insights for researchers, system architects, and policy stakeholders.
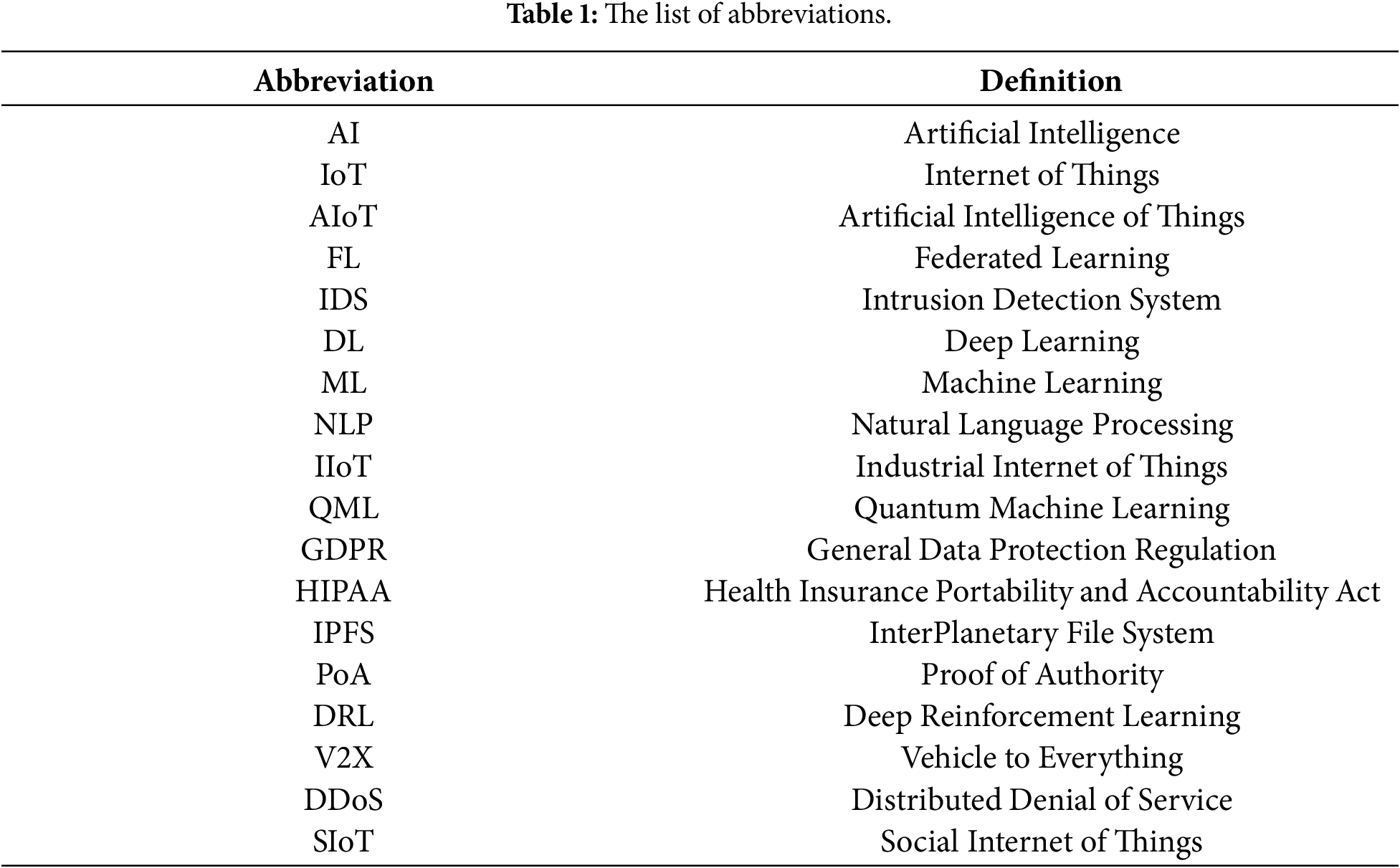
The remainder of the article is summarized as follows. Section 2 is a detailed the background of existing works related to AIoT in various domains like smart buildings, transportation, healthcare, and smart cities. It summarizes methodologies, limitations, and opportunities found in the literature using a comparison table. Section 3 is the detailed methodology. Section 4 outlines challenges, and each challenge is described along with its disadvantages and potential solutions. Section 5 presents blockchain, ML, and AI-based methods proposed by different researchers to overcome each challenge, which cover the solutions across domains like healthcare, transportation, and smart cities. It also discusses open challenges and research gaps that hinder the wide-scale deployment of secure AIoT. Fig. 3 represents the structure of the paper, and Table 1 represents the list of abbreviations.
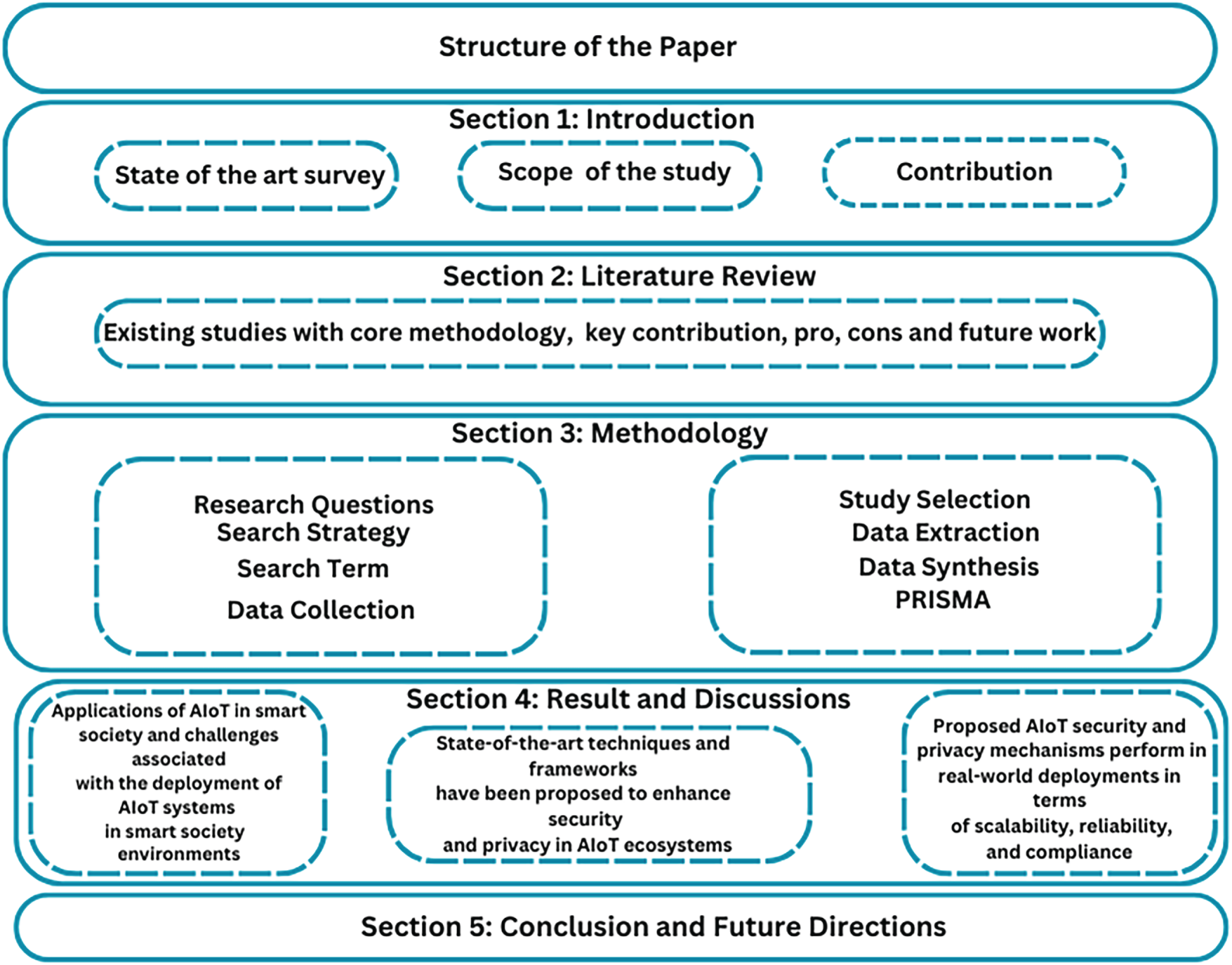
Figure 3: Structure of the paper.
In the evolving ecosystem of smart societies, the integration of AI and the AIoT has led to the emergence of new digital infrastructures. This section presents the existing studies of different authors and also presents the methods and techniques presented by them. Table 2 summarizes the existing studies with key contributions, advantages, disadvantages and future work and Fig. 4 is the importance of the SLR.
Figure 4: Overview of the SLR.
Positioning with respect to closely related surveys. Several recent surveys provide important foundations and are complementary to the scope of this SLR. “Artificial Intelligence of Things: A Survey” provides a broad AIoT taxonomy covering sensing, computing, networking/communication, and domain-specific AIoT systems [3] and organizes the literature accordingly [3]. This survey focuses on end–edge–cloud cooperation and enabling technologies that support AI inference/training in AIoT deployments [7]. Analysis of IoT Security Challenges and Its Solutions Using Artificial Intelligence” provides a comprehensive survey of IoT security challenges across application domains and discusses intelligent solution strategies based on machine learning and deep learning for protecting IoT systems [15]. Finally, “An integration perspective of security, privacy, and resource efficiency in IoT-Fog networks: A comprehensive survey” emphasizes integrated treatment of security, privacy, and resource efficiency and categorizes work by architectures, routing, and resource management [16]. The purpose of the study [16] is to outline upcoming research projects targeted at developing integrated IoT-Fog solutions. It investigates the perspective of an aggregated view and discusses the needs that motivate researchers to use them in IoT-Fog networks. Recent work has also provided an in-depth analysis of cybersecurity solutions for AI-driven IoT-enabled smart cities, highlighting layered defenses and advanced communication networks [17,18].
In contrast, our SLR complements these surveys by focusing specifically on security and privacy in AIoT-enabled smart societies, synthesizing domain-oriented challenges and blockchain/AI/federated-learning–based solution families, and consolidating evidence from peer-reviewed studies within the 2029–2025 time window defined by our research questions.
Recent literature on future communication systems emphasizes that AIoT is increasingly embedded within AI-native networking architectures envisioned for 5G-Advanced and 6G smart societies. Unlike earlier IoT-centric communication models focused primarily on connectivity, emerging systems integrate artificial intelligence, data science, and IoT to enable context-aware, self-optimizing, and autonomous network behavior. The author [19] highlight that AI-powered IoT systems are evolving toward distributed intelligence, where learning, inference, and security decisions are jointly performed across device, edge, and cloud layers to support smart cities, healthcare, and industrial automation. Similarly, reference [3] present a comprehensive AIoT survey showing how advances in AI accelerators, edge intelligence, and adaptive networking are reshaping communication infrastructures for latency-sensitive and privacy-aware applications.
Several studies further argue that future AIoT communication systems will rely on AI-driven network slicing, semantic communication, and intelligent resource orchestration to meet the scalability and reliability demands of dense smart-society deployments. The authors [20,21] show that semantic and task-oriented communications reduce bandwidth consumption while improving responsiveness, but they also introduce new security and trust challenges at the learning and inference layers. Smart grids face security risks from cyberattacks that threaten their reliability, availability, and privacy. Effective security solutions and novel approaches are needed to address these challenges and protect critical infrastructure from potential vulnerabilities. In parallel, reference [22] demonstrate that federated and edge-assisted learning are becoming essential for privacy-preserving intelligence in next-generation IoT networks, although they remain vulnerable to poisoning attacks and coordination overhead at scale.
More recent works extend this vision by incorporating blockchain, generative AI, and digital twins into future communication systems. The authors [21] discuss how blockchain-enabled AIoT networks can provide decentralized trust, auditable data exchange, and resilient coordination in 6G-oriented smart environments. The authors [23,24] further emphasize that generative AI and digital-twin-assisted networking offer powerful tools for adaptive optimization and fault prediction, but also raise concerns related to data provenance, model integrity, and regulatory compliance.
Overall, this body of recent literature reinforces the need for a security- and privacy-centric AIoT analysis grounded in future communication systems. It confirms that smart-society AIoT deployments must be evaluated not only at the application level, but also within AI-native, data-driven, and highly distributed communication infrastructures, which motivates the focused scope of this SLR.
2.1 Domain-Oriented Literature Grouping
Smart buildings and smart homes. The authors [25] examine AIoT-enabled smart building systems and emphasize that interoperability issues and privacy risks remain dominant concerns when coordinated security strategies are absent. In the smart home context, reference [26] explore AI and blockchain synergy for secure local data exchange and show that blockchain-assisted protection can be effective at small scale; however, they highlight limitations when extending these solutions to city-scale AIoT deployments. Taken together, these studies agree that local protection mechanisms can be effective in constrained environments, but they differ in scalability assumptions, and they collectively indicate that extensible architectures and standardized interfaces are still missing for broader adoption.
Smart cities and urban governance. Several studies focus on smart city infrastructures and governance. The authors [27] identify cyber-policy gaps and weak interconnection between digital infrastructures and AI governance, noting the lack of technical implementation guidelines for security. Efficiency, innovation and sustainability of nations are among the objectives of smart governance to change nations into smart cities. The challenges are associated with administrative reform, development of infrastructure, and data security and big data management with a strategic frame required to implement and transition [28]. The authors [22] discuss AI and IoT deployment in smart urban systems but emphasize persistent vulnerabilities across the data lifecycle and the absence of unified security frameworks. The authors [29] similarly identify implementation barriers and conclude that the lack of integrated secure communication standards remains a key limitation. The authors [30] emphasize the benefits of AI in smart cities while noting that privacy-preserving tools remain inadequate at scale. Across these studies, a common theme is the gap between strategic smart-city planning and technical security implementation. While the works differ in emphasis—policy and governance [28], device-level and context-aware defenses [30], and data lifecycle protection [22] they consistently indicate that standardized, scalable, and technically actionable security frameworks are still lacking for smart society deployments [17].
Enterprise, industry, and agriculture AIoT. In enterprise environments, reference [31] proposes a privacy management framework based on risk analysis and highlights the need for AIoT-specific governance mechanisms; however, the study does not sufficiently address real-time autonomous threats without an integrated security layer. In broader industrial and agricultural AIoT settings, reference [32] report data leakage and inconsistent encryption practices as core challenges and recommend tighter integration between AI decision engines and network defense policies. Both studies converge on the need for stronger governance and consistent security practices, but they differ in orientation: enterprise privacy governance [31] vs. multi-sector technical challenges such as encryption inconsistency and integration fragmentation [32]. The missing element across both directions is an integrated approach that jointly addresses governance requirements and technical enforceability under real operational conditions.
2.2 Cross-Cutting Technical Grouping by Security Function
Architectures and system integration for secure AIoT. The Industrial Internet of Things (IIoT) is susceptible to numerous security threats, and they are divided into different groups in accordance with the tier to which the threats are directed. These attacks are breaking important security requirements. New technologies, such as AI and the use of edges, are under consideration to solve these security issues and improve system protection on the whole [33]. Semantic interoperability is also problematic in Industry 4.0 because of the complicated automation systems and a variety of standards. This paper examines how semantic interoperability and AI could overcome the impediments in the IoT framework. The paper centers on the topic of trying to use Named Entity Recognition (NER) AI models and Natural Language Processing (NLP) to enhance identification and processing of IoT data, and increase semantic interoperability [34]. These studies collectively show that architectural proposals can improve connectivity and interoperability, yet security analytics and integrated protection remain underdeveloped, indicating a gap in operational security integration across heterogeneous AIoT systems.
Blockchain- and ML-enabled security mechanisms. An architecture that integrates AI, machine/deep learning, and blockchain can be used to improve the security of IoT devices. Machine learning assists in detection of attacks, and blockchain is used to verify requests and provide cryptographic security. This method enhances protection of IoT system by predicting and preventing attack before it impacts on system [35]. A major issue in cybersecurity is side-channel attacks, which exploit the weaknesses, which include power consumption and acoustic emission of cryptographic systems.
This SLR is designed to critically analyze the role of AIoT in the development of secure and intelligent smart societies. The study first explores the diverse applications of AIoT in smart environments and identifies the emerging security and privacy challenges that arise during their deployment. It then investigates state-of-the-art techniques and frameworks such as blockchain, federated learning, and edge AI and ML, that have been proposed to enhance privacy and security, assessing their effectiveness across various application domains. Finally, the SLR evaluates the performance of these mechanisms with respect to scalability, reliability, and regulatory compliance, while also identifying the limitations of current solutions, persistent challenges, and research gaps that need to be addressed in future work. The process of planning the methodology is shown below in bullet points and Fig. 5, and the research questions are described in the next stage.
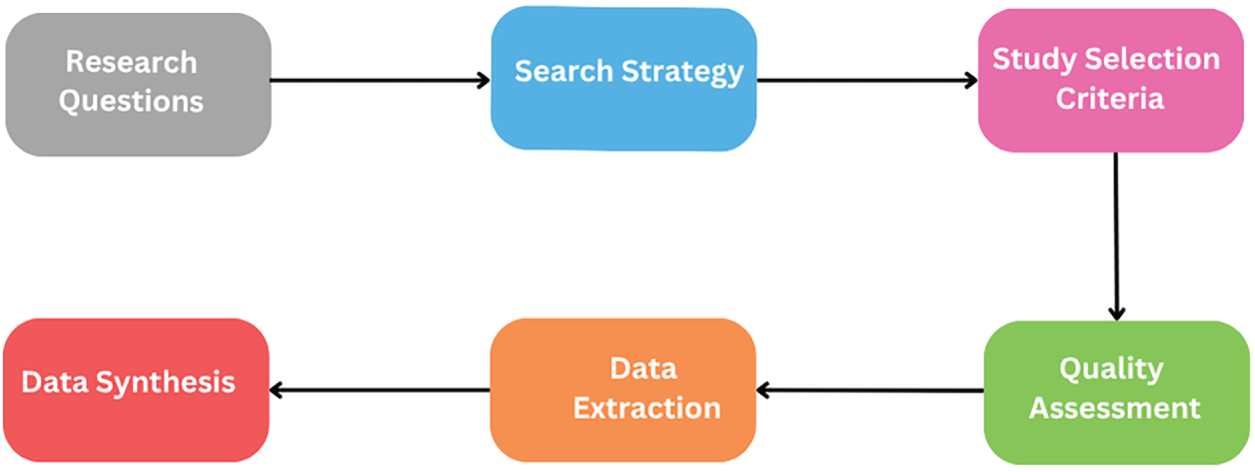
Figure 5: Process of planning the systematic literature review methodology. This figure presents the step-by-step methodology adopted in the systematic literature review, including research question formulation, data source selection, search string construction, application of inclusion and exclusion criteria, quality assessment, and final paper selection. It provides an overview of the structured and reproducible process used to identify and analyze relevant studies.
• Research Questions
• Select Data Source
• Search String
• Inclusion and Exclusion
• Quality Assessment
• Selection of Primary Study
• Selection of Final Papers
• Results
This SLR is driven by a set of focused research questions (RQs) designed to explore the core themes, applications, challenges, and solutions surrounding the deployment of AIoT systems in smart society environments. These questions help frame the review’s purpose, guide the search strategy, and support structured data extraction and synthesis. The research questions are:
• RQ1: What are the applications of AIoT and smart society and what are the emerging security and privacy challenges associated with the deployment of AIoT systems in smart society environments?
• RQ2: What state-of-the-art techniques and frameworks have been proposed to enhance security and privacy in AIoT ecosystems, and how effective are they across different application domains?
• RQ3: How do the proposed AIoT security and privacy mechanisms perform in real-world or simulated deployments in terms of scalability, reliability, and compliance, and what is the evaluation of current solutions, open challenges and research gaps?
The term actual source refers to the digital libraries and academic repositories from which the retrieved studies are obtained. For this study, we selected leading scholarly digital libraries, namely SpringerLink, ACM Digital Library, IEEE Xplore, ScienceDirect, and Wiley Online Library, to retrieve relevant peer-reviewed literature related to AIoT systems in smart society environments. Access to full-text articles from these databases was essential to ensure accurate extraction, analysis, and synthesis of prior research findings.
Different search strategies were adapted to the indexing structure and query syntax of each digital library to maximize coverage while maintaining relevance. The screening process was conducted progressively across multiple stages, including title and keyword screening, abstract screening, and full-text evaluation. Table 3 and Fig. 6 illustrate the distribution of retrieved studies across the selected digital libraries and show how the initial pool of publications was systematically reduced at each screening stage to obtain the final set of eligible studies.
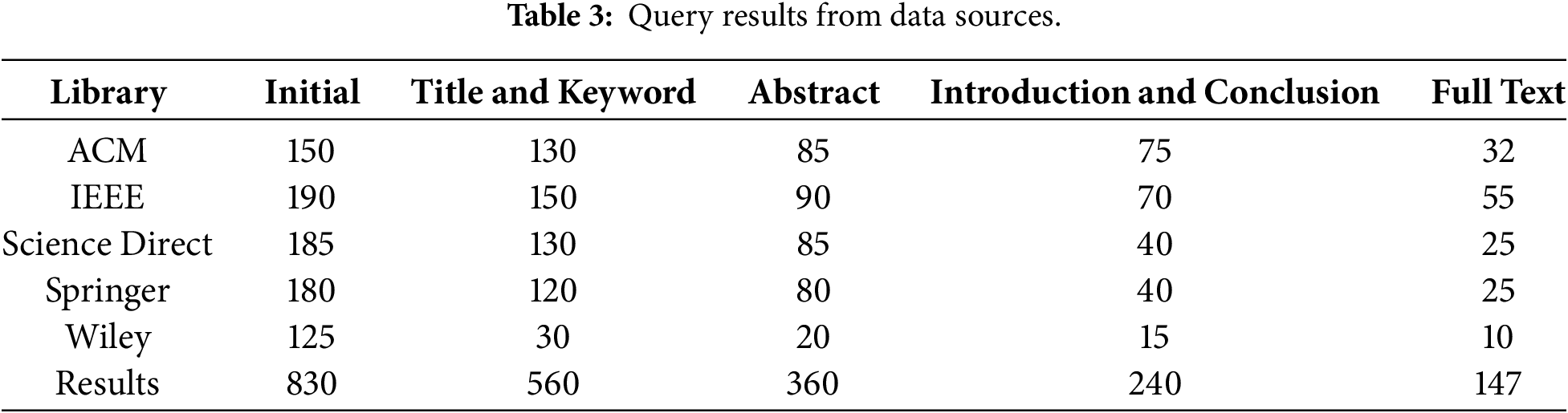
Figure 6: Distribution of retrieved studies across digital libraries during the search process. This figure shows the number of studies retrieved from each selected digital library (ACM, IEEE Xplore, ScienceDirect, Springer, and Wiley) at different screening stages. It illustrates how the initial pool of studies was progressively refined through title, abstract, and full-text screening to obtain the final set of eligible papers.
To ensure comprehensive and systematic retrieval of relevant literature, search strings were carefully designed using combinations of keywords, Boolean operators, “And”, “OR” and truncation where appropriate. The formulation of the search string was driven by the three predefined research questions, focusing on AIoT applications, security and privacy techniques, and evaluation metrics.
The search strategy included the following core keyword categories, and Table 4 shows the search string formulation, and Fig. 7 shows the process of formulating the search string:
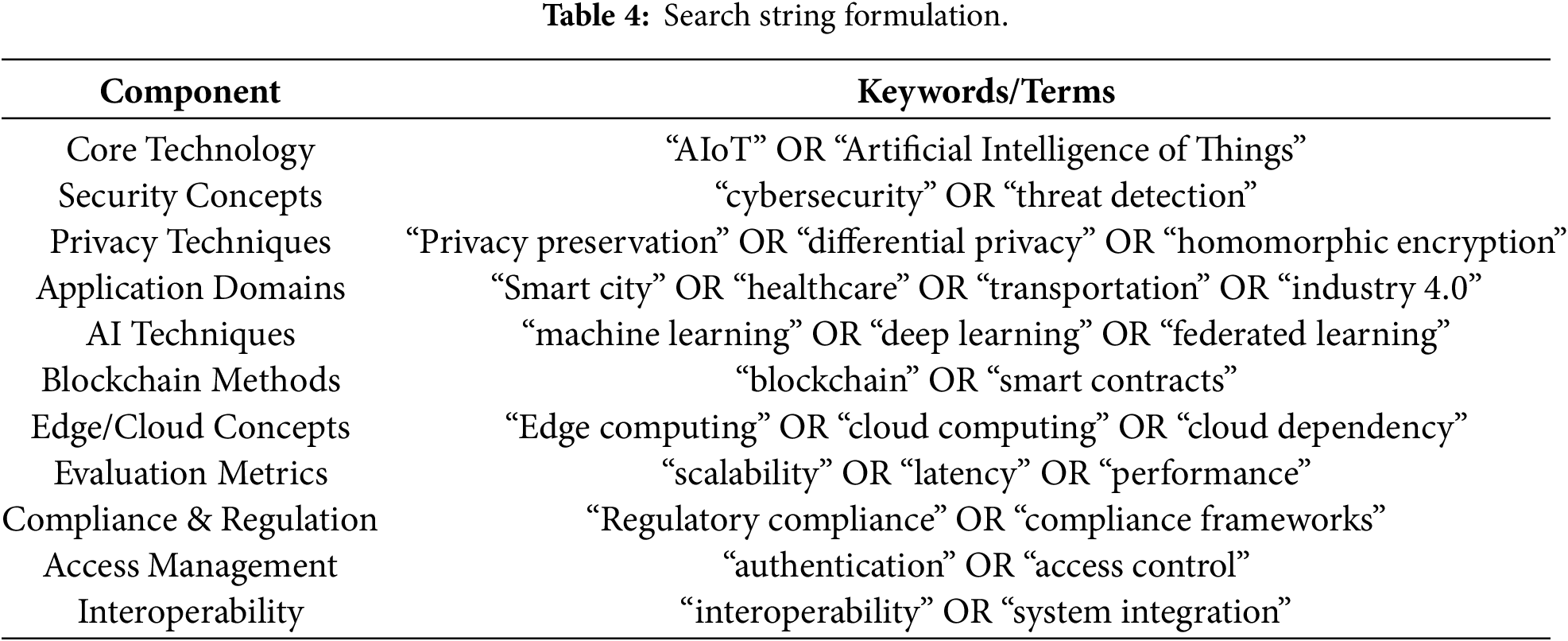
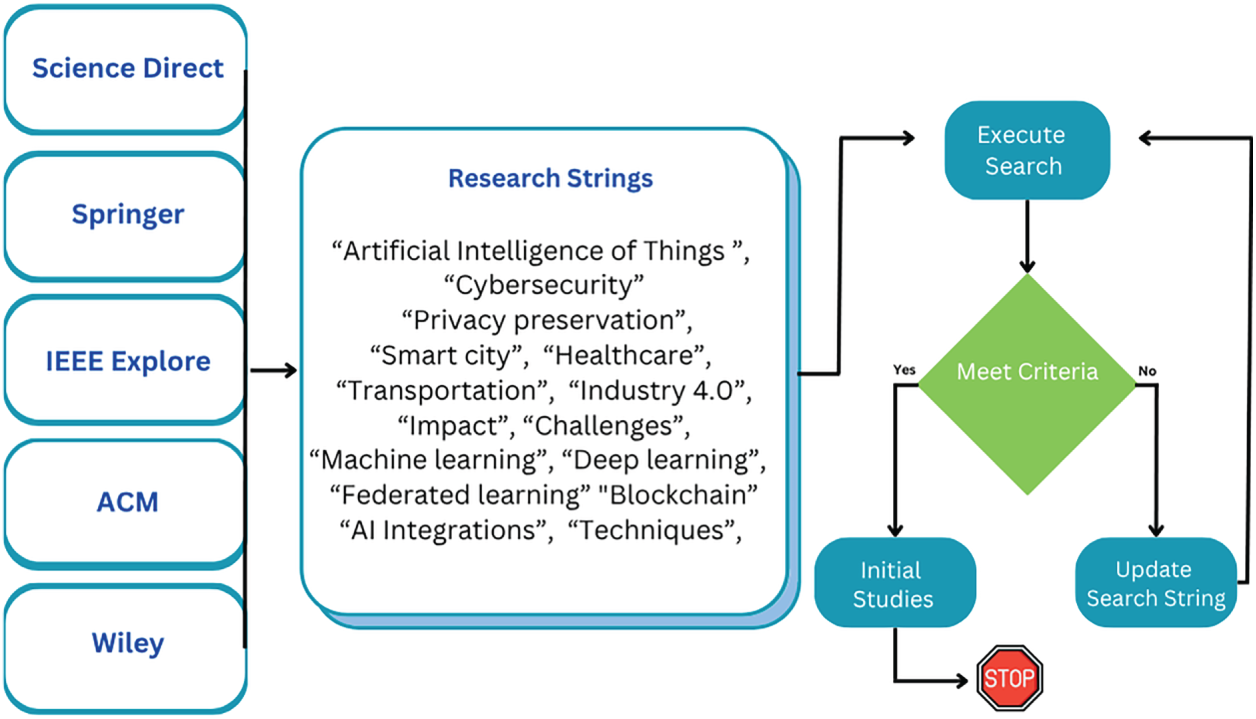
Figure 7: Search string formulation process for AIoT security and privacy studies. This figure depicts the process used to formulate the final search strings by combining AIoT core terms, application domains, security and privacy concepts, and enabling techniques using Boolean operators. It highlights how the search strategy was systematically derived from the research questions to ensure comprehensive and consistent literature retrieval.
• AIoT Technologies: “Artificial Intelligence of Things”, “AIoT”, “smart devices”.
• Application Domains: “smart city”, “smart healthcare”, “transportation”, “manufacturing”.
• Security & Privacy Aspects: “security”, “privacy”, “data protection”, “authentication”, “access control”, “encryption”.
• Techniques & Evaluation: “blockchain”, “machine learning”, “federated learning”, “AI integration”, “compliance”, “scalability”, “reliability”.
3.4 Define Inclusion and Exclusion Criteria
To ensure the relevance and quality of the selected studies, the following inclusion and exclusion criteria were applied during the systematic review process:
• Articles published between 2020 and 2025 to ensure recency and relevance to current AIoT technologies.
• Peer-reviewed journal articles and conference proceedings.
• Studies focusing on AIoT applications in domains such as healthcare, transportation, smart cities, industry, and energy.
• Papers addressing security, privacy, scalability, interoperability, or compliance within AIoT ecosystems.
• Research proposing frameworks, models, or techniques using AI, ML, or blockchain to mitigate AIoT security or privacy challenges.
• Studies presenting experimental evaluations, performance assessments, or comparative analysis in real or simulated environments.
• Non-English language papers.
• Editorials, tutorials, white papers, posters, and non-peer-reviewed literature.
• Studies published before 2020.
• Research unrelated to AIoT systems or lacking a focus on security and privacy.
• Duplicate entries or papers with insufficient technical depth or methodology description.
3.5 Quality Assessment Criteria
In literature reviews, SLRs and meta-analyses, qualitative methods are a specified set of techniques for judging the worthiness, credibility and quality of research attempts. Qualitative methods are accepted platforms or techniques for determining the validity, equivalence, and the structure of the quality asserts. By introducing quality control methods and proofs of results, we can ensure that the primary studies which we have selected are able to provide sufficient information to answer our research questions, as shown in Table 5. In this step, each research topic is compared with the standard.
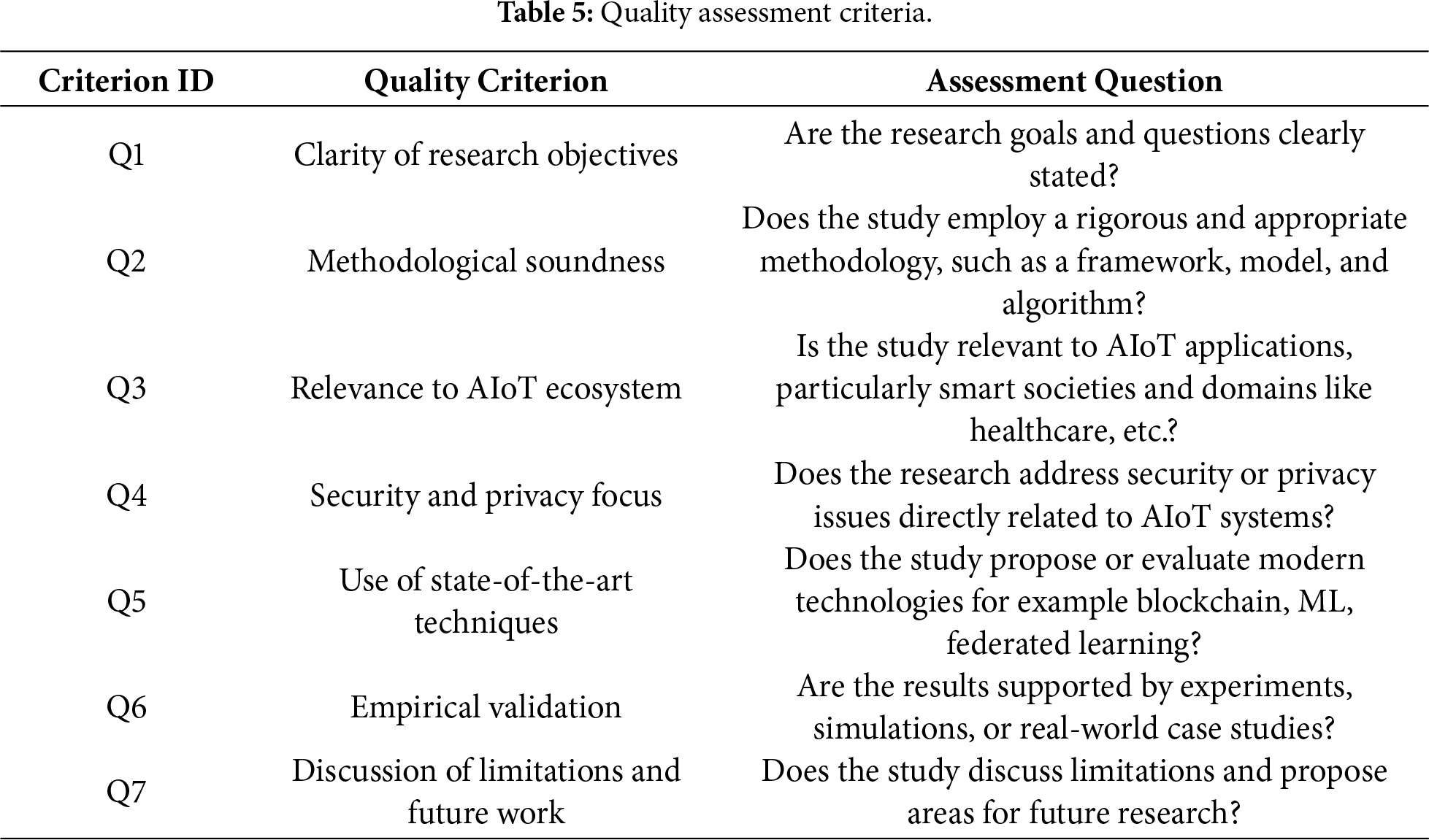
In this review, the quality assessment criteria (Q1–Q7) were applied as a structured qualitative checklist to verify the relevance and methodological adequacy of the candidate studies for addressing RQ1–RQ3. The assessment was used to support consistent inclusion decisions rather than to compute a numerical quality score or apply a quantitative threshold. Inter-rater agreement metrics (e.g., Cohen’s kappa) were not computed; this limitation is acknowledged in the “Limitations and Threats to Validity” subsection.
3.6 Selection of the Primary Study
The primary study selection process followed a systematic and structured approach. Initially, a comprehensive search was conducted across four leading digital libraries. The formulated search strings were applied consistently across all sources to retrieve literature relevant to AIoT applications in smart society environments, with a specific focus on security and privacy. Duplicates and irrelevant articles were excluded based on their titles and abstracts. The remaining studies were examined in full to assess their relevance to the predefined inclusion criteria and their ability to answer the three research questions. Eligible articles were subjected to a rigorous quality evaluation based on established criteria, ensuring methodological soundness and empirical relevance. Only studies that satisfied all inclusion criteria were included in the final synthesis. As a result, 147 primary studies were found that met the consistent quality criteria. The original studies are reported in Fig. 8 and Table 6, and Fig. 9 shows the procedure used in this study for the corresponding selection process in a schematic representation. This process ensured the selection of robust, high-quality research to inform the findings and insights of this SLR.
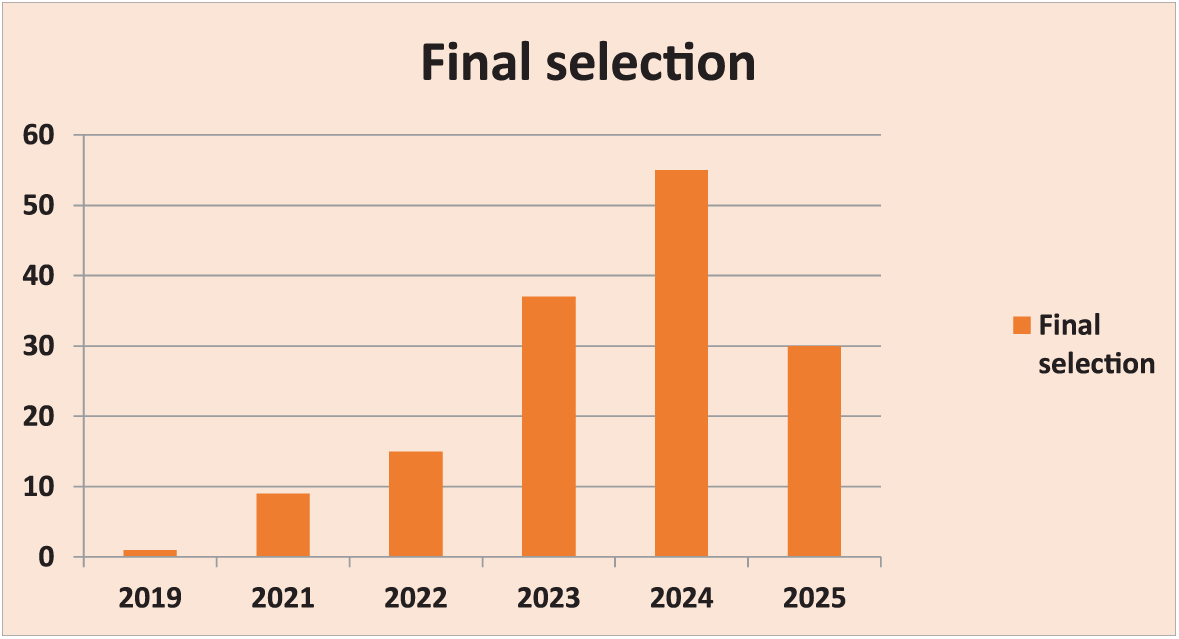
Figure 8: Final papers selection.
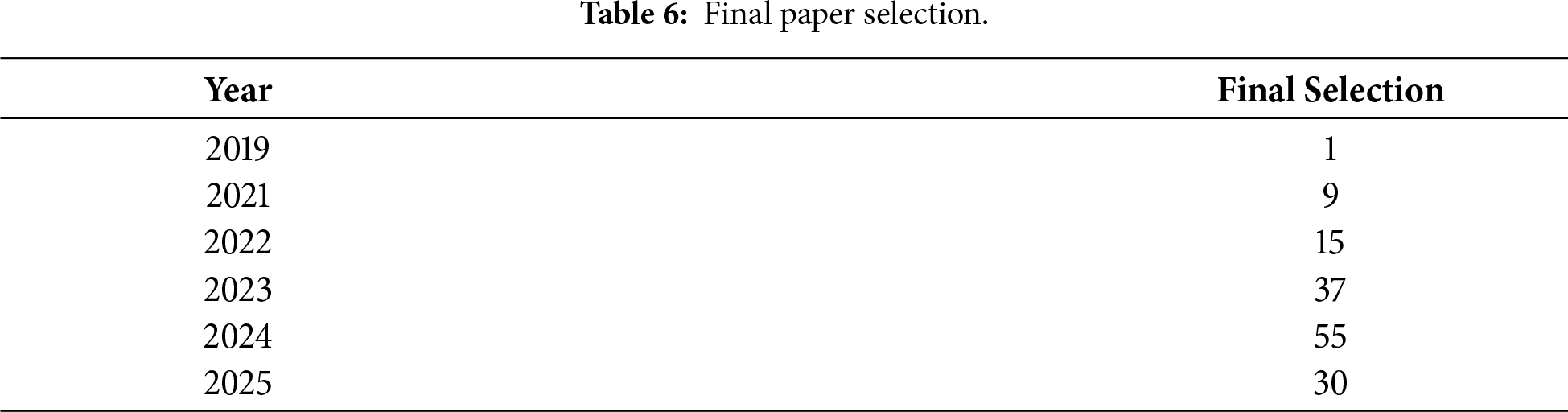
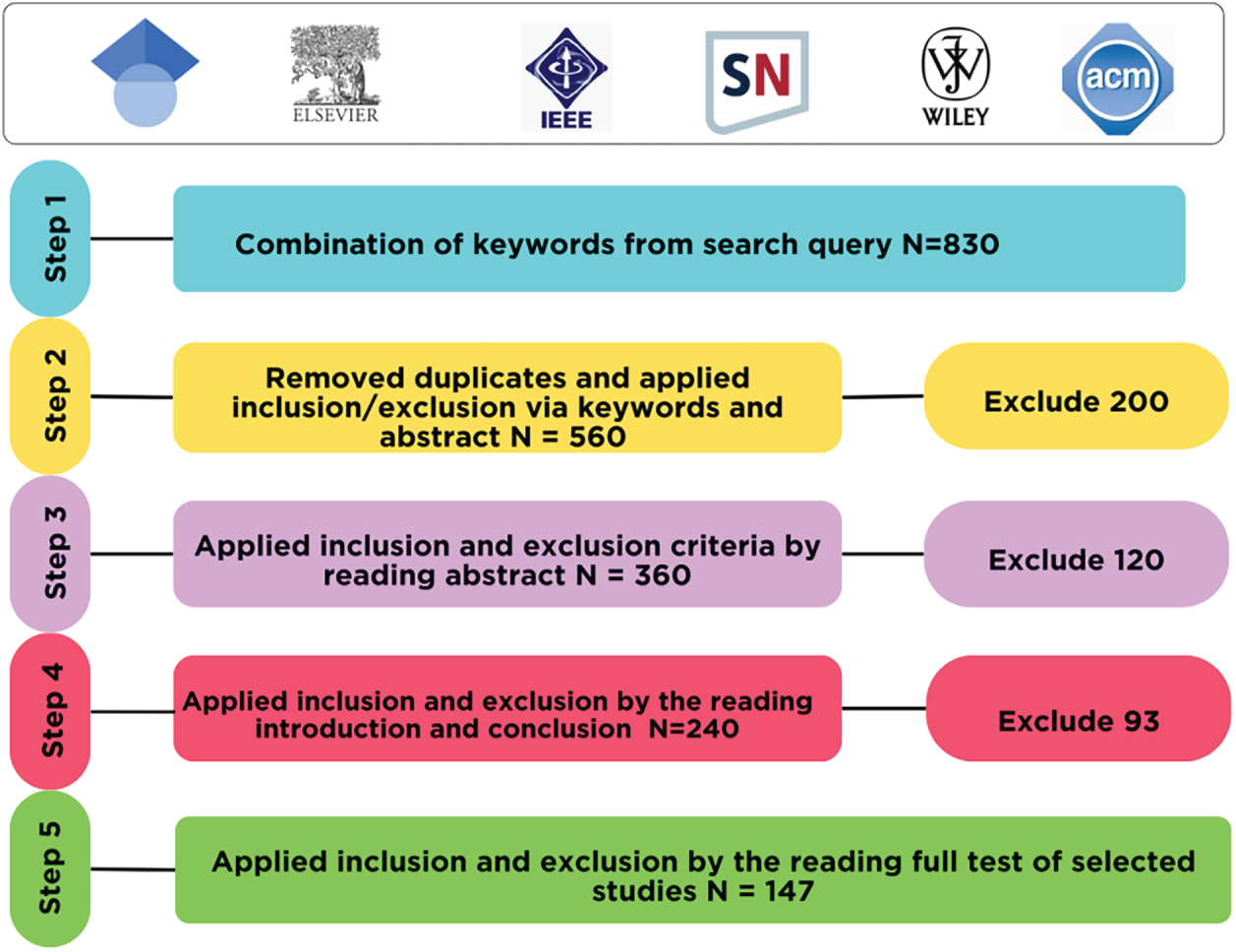
Figure 9: Prisma diagram.
3.7 Construction of the Final Search Strings
The final search strings were constructed from the three research questions (RQ1–RQ3) by mapping each question to four keyword categories: (i) AIoT core terms, (ii) application domains, (iii) security and privacy concepts, and (iv) techniques and evaluation terms. Candidate synonyms were collected for each category and then combined using Boolean operators (“AND”, “OR”) and truncation where applicable. The finalized terms and category mapping are summarized in Table 4, and the overall formulation process is illustrated in Fig. 7. The same structured logic was applied across the selected digital libraries to ensure consistent retrieval aligned with the scope of the review.
3.8 Step-by-Step Application of Inclusion and Exclusion Criteria
Study selection was performed in successive screening stages consistent with Table 3. First, the initial query results were collected from the selected digital libraries. Second, duplicates were removed. Third, title and keyword screening was applied to exclude clearly irrelevant studies. Fourth, abstract screening was conducted to apply the inclusion and exclusion criteria. Fifth, the introduction and conclusion were checked to verify that each study directly addressed AIoT in smart-society contexts with a security/privacy focus. Finally, full-text screening was performed to confirm eligibility before inclusion in the final synthesis.
3.9 Use of the Quality Assessment Criteria (Q1–Q7)
After full-text eligibility was confirmed, each candidate study was evaluated using the quality assessment questions Q1–Q7 (Table 5) as a structured checklist to ensure methodological soundness and relevance. Specifically, Q1 verified clarity of objectives; Q2 assessed methodological soundness (framework/model/algorithm); Q3 ensured direct relevance to AIoT smart-society applications; Q4 verified that security/privacy was addressed explicitly; Q5 checked the use or evaluation of state-of-the-art techniques (e.g., blockchain, ML, federated learning); Q6 verified empirical support (experiments, simulations, or real-world case studies); and Q7 confirmed that limitations and future work were discussed. Studies that did not adequately satisfy these quality criteria were excluded prior to final synthesis.
4.1 AIoT Applications in Smart Societies
AIoT applications are transforming smart societies across domains such as homes, healthcare, agriculture, cities, and industries as shown in the Fig. 10 [38]. These technologies improve efficiency, safety, and quality of life through real-time monitoring, automation, and intelligent decision-making. However, there are multiple challenges in AIoT deployment in different domains and these challenges are like data privacy, system scalability, reliability, and integration complexity, as shown in Fig. 11 and Table 7. Addressing these issues requires robust AI algorithms, blockchain integration and federated learning-based solutions to secure IoT infrastructures, and regulatory frameworks [39]. Continued innovation and cross-disciplinary collaboration are essential to realize the full potential of AIoT in smart environments.
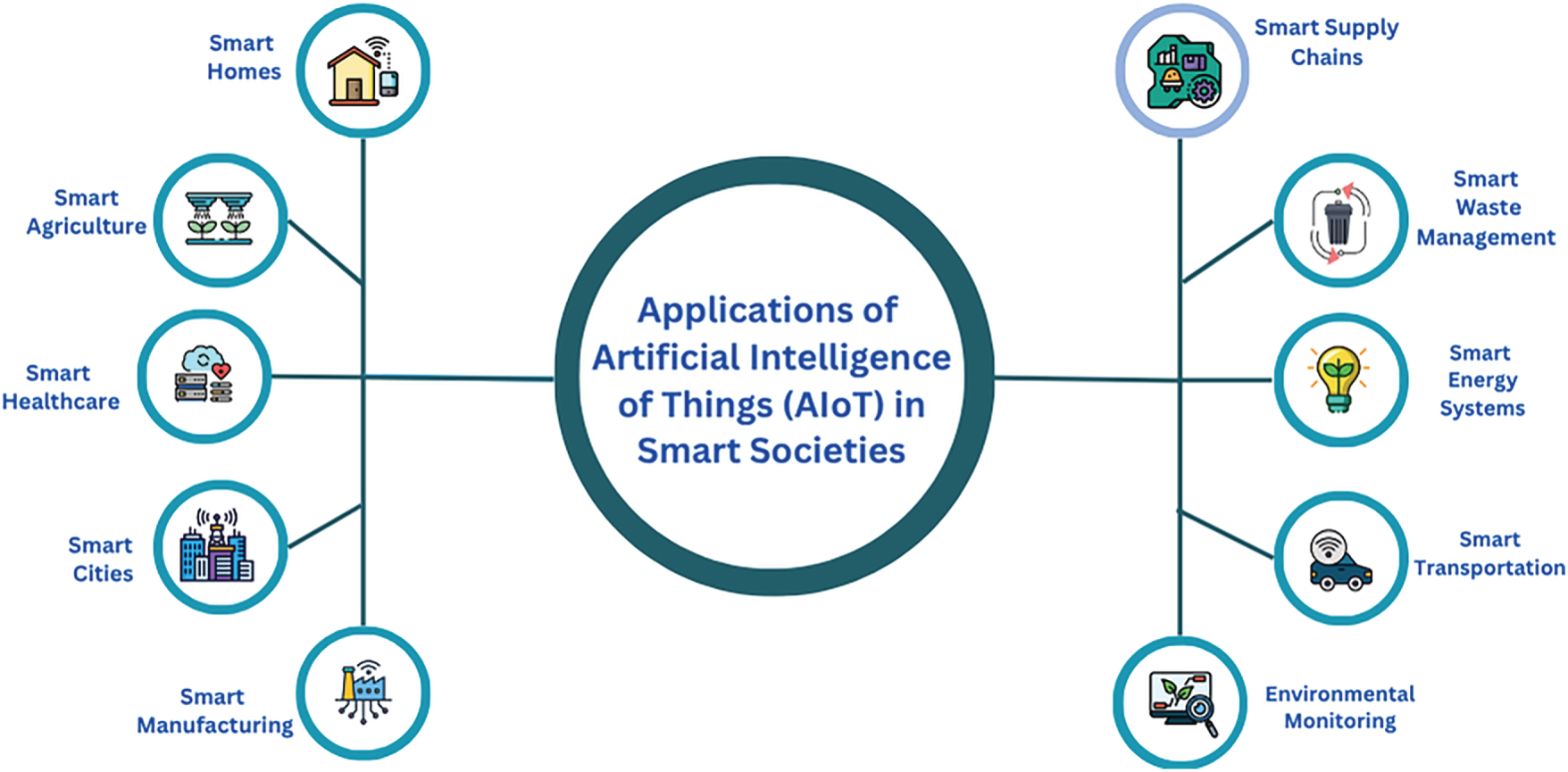
Figure 10: Applications of AIoT in smart society environments. This figure provides an overview of key AIoT application domains, including smart homes and ambient intelligence, smart healthcare and telemedicine, smart cities and urban infrastructure, smart transportation and autonomous mobility, smart agriculture, smart energy systems, environmental monitoring, and smart education and digital learning. It illustrates how AIoT technologies enable real-time data collection, intelligent decision-making, and automation across these domains.
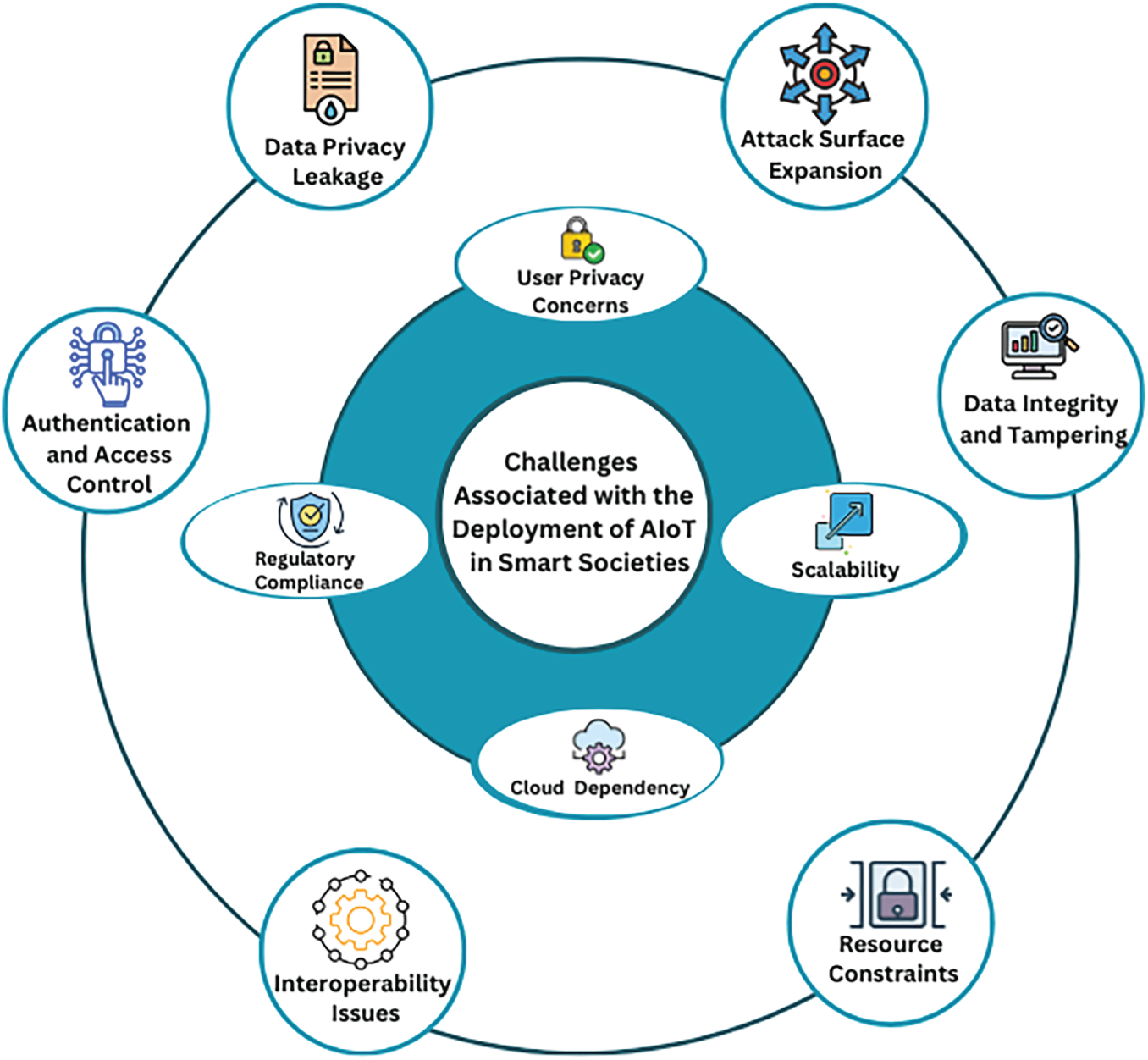
Figure 11: Security and privacy challenges associated with AIoT deployment in smart societies. This figure summarizes the major security and privacy challenges faced by AIoT systems, such as data privacy leakage, authentication weaknesses, interoperability issues, resource constraints, cloud dependency, scalability limitations, regulatory compliance, and data integrity risks. It provides a consolidated visual representation of the challenges discussed in the text and summarized in Table 7.
AIoT in smart homes enhances lifestyle convenience through intelligent automation, energy-efficient appliances, and context-aware systems [40]. Security systems equipped with AI-based cameras can distinguish between residents, guests, and intruders, improving safety while minimizing false alarms [41]. These applications rely on interconnected devices to optimize lighting, climate, and security, thereby promoting sustainable living and user comfort [42]. In addition, ambient intelligence extends smart homes by enabling continuous context-awareness (e.g., activity recognition, adaptive assistance, and proactive services) through multimodal sensing and on-device/edge inference, which further increases the importance of privacy-preserving and secure data handling. However, privacy concerns and device interoperability remain major challenges, as users are hesitant to trust devices with sensitive personal data, and incompatible standards hinder seamless integration [43].
In agriculture, AIoT enables precision farming by leveraging real-time data from sensors, drones, and satellite imagery to optimize irrigation, detect pests, and predict yields [44]. In smart agriculture, IoT devices continuously gather data from the field. AI algorithms then analyze this data to derive actionable insights predicting weather conditions, optimizing irrigation, and recommending precise fertilizer applications [45]. This results in enhanced resource utilization and crop productivity. Nonetheless, the sector faces challenges such as poor connectivity in remote areas and the high cost of setting up and maintaining intelligent infrastructure [46].
AIoT transforms healthcare by enabling remote monitoring, telemedicine, and personalized care using wearable sensors and intelligent diagnostics [47]. AIoT technologies connect medical devices, sensors, and wearables that continuously collect and it improves patient outcomes and reduces hospital loads [48,49]. The major issues include latency in data transmission, difficulties in data standardization, and ensuring secure transmission of sensitive health records [50]. Telemedicine-oriented workflows further require end-to-end confidentiality, strong authentication, and reliability guarantees to maintain trust in remote diagnosis and clinical decision-making.
Smart cities benefit from AIoT through real-time traffic management, smart lighting, and efficient waste disposal systems [51]. AIoT also transforms public safety and emergency response. Smart surveillance systems equipped with AI-based cameras can detect unusual activities, identify accidents, and alert authorities instantly, improving urban security. These technologies help streamline urban services and enhance citizen engagement. From an urban infrastructure perspective, AIoT also supports monitoring and optimization of critical assets (e.g., roads, bridges, water distribution, and public utilities), where resilience, integrity of sensed data, and secure service continuity are essential. Still, challenges such as ensuring scalability to accommodate city-wide deployments and protecting data privacy persist as barriers to full-scale adoption [29].
In industrial settings, AIoT integrates machine learning and robotics with IoT to improve quality control, predictive maintenance, and production efficiency [52]. AIoT also plays a key role in supply chain management and quality control. By analyzing sensor and logistics data, manufacturers can forecast demand, optimize inventory, and minimize waste [53]. It also boosts automation and reduces downtime, integrating legacy systems with new technologies and mitigating cyber threats remain critical challenges [54].
AIoT is revolutionizing supply chain operations by integrating blockchain, IoT sensors, and AI algorithms to monitor goods in real-time, predict disruptions, and improve logistics transparency [55]. This leads to enhanced traceability and operational efficiency. However, maintaining data integrity and mitigating cybersecurity risks in distributed and global supply networks remain significant hurdles [56].
Smart transportation systems utilize AIoT to facilitate traffic flow optimization, accident prediction, and vehicle-to-infrastructure (V2I) communication [57]. AIoT-enabled traffic systems rely on networks of IoT sensors, smart cameras, GPS devices, and connected vehicles that continuously collect real-time traffic data such as vehicle density, speed, and road conditions [58]. These systems contribute to reduced congestion, improved road safety, and energy savings. In autonomous mobility settings, safety-critical constraints amplify the need for low-latency decision-making, secure V2X communications, and robust defenses against spoofing and adversarial manipulation. The effectiveness of these systems is constrained by challenges such as sensor reliability, coordination among heterogeneous devices, and data fusion complexity [59].
4.1.8 Environmental Monitoring
In environmental applications, AIoT enables continuous surveillance of pollution levels, climate conditions, and hazardous events using distributed sensors and AI analytics [60]. AIoT-driven environmental monitoring also enhances resource management and sustainability. For example, smart water management systems use AIoT to detect leaks, monitor water quality, and optimize distribution networks. This supports proactive decision-making and ecological conservation. Nevertheless, issues like sensor accuracy, calibration drift, and the need for timely data processing hinder optimal deployment in dynamic outdoor environments [61,62].
AIoT improves the performance of smart grids through dynamic load balancing, renewable energy integration, and predictive fault detection [63]. AIoT-enabled smart energy systems use IoT sensors, smart meters, and connected devices to continuously monitor parameters such as electricity demand, load patterns, and grid performance. The data collected is analyzed by AI algorithms to forecast demand, detect anomalies, and optimize energy distribution [64]. These systems enhance energy efficiency and resilience. Yet, challenges related to scalability and data storage, especially during peak loads or decentralized energy exchanges, persist as bottlenecks [65].
AIoT in waste management introduces intelligent sorting mechanisms, bin-level monitoring, and route optimization for collection vehicles [66]. AIoT also supports predictive maintenance for waste management infrastructure, identifying potential equipment failures or overflowing bins before they occur. This improves service reliability and urban cleanliness [67]. These innovations reduce environmental impact and improve operational costs. However, practical limitations such as battery management in edge devices and ensuring real-time data flow from mobile units present ongoing challenges [68].
4.1.11 Smart Education and Digital Learning
AIoT also supports smart education and digital learning by enabling intelligent classrooms, adaptive learning platforms, and remote experimentation using connected devices (e.g., smart boards, wearables, attendance sensors, and environmental monitors). AI-driven analytics can personalize content delivery, support student engagement monitoring, and optimize resource usage in educational facilities. However, these deployments raise privacy and governance challenges due to sensitive learner data, as well as security risks related to authentication, access control, and safe integration of heterogeneous campus devices. Ensuring secure data sharing, compliant storage, and reliable connectivity is therefore essential for trustworthy AIoT-enabled education services.
4.2 Security and Privacy Challenges in AIoT Systems
As these systems become more interconnected and data-intensive, they expose new security and privacy vulnerabilities [69]. Addressing these challenges is critical to prevent data breaches, ensure user trust, and maintaining the safe operation of essential services. Below is the table, which is the conclusion of the challenges and provides a description of each challenge for deployment in AIoT systems in smart society environments.
These vulnerabilities can erode public trust and create compliance challenges with privacy regulations. To mitigate this, research emphasizes the use of latest techniques and, differential privacy, and decentralized encryption mechanisms to protect data across distributed nodes [70]. The heterogeneity and scale of AIoT systems make robust authentication and access control a daunting task. In a smart healthcare setup, unauthorized control over sensors or actuators can cause devastating disruptions [71]. There is a need for the latest techniques and identity frameworks to address these vulnerabilities. Smart society environments are characterized by a high degree of heterogeneity in device types, manufacturers, and communication protocols. Lack of interoperability limits cross-system integration, data sharing, and coordinated responses in scenarios such as smart transportation and emergency management. Researchers have emphasized the need for unified communication models [72].
Most AIoT devices deployed at the edge operate with limited computational resources and energy supplies [7]. This restricts the implementation of advanced encryption, real-time analytics, and AI inference on-device [73]. Emerging solutions should focus on on-device intelligence, and hardware-level optimization for energy-efficient AI processing [64]. Many AIoT systems rely on centralized cloud platforms for data storage and processing, which introduces single points of failure and increased latency [74]. If the cloud server or network connection experiences downtime, the entire AIoT ecosystem may become inoperative. This dependency also raises cybersecurity and privacy risks, as sensitive data must travel across networks to the cloud, making it susceptible to interception or breaches [75]. In mission-critical applications such as traffic control and response, delays caused by cloud dependency can lead to catastrophic consequences [76]. AIoT ecosystems are expected to accommodate billions of interconnected devices in future smart cities [77]. However, current infrastructure struggles with bandwidth, processing overload, and inefficient routing as networks scale. Scalable solutions such as modular architectures, decentralized AI processing, and adaptive routing protocols are proposed to meet the demands of expanding smart societies [78].
As AIoT applications expand, aligning with regional and international data protection laws has become increasingly complex [79]. Recent studies, such as [80] emphasize that this regulatory inconsistency poses one of the greatest challenges for AIoT adoption, urging the development of harmonized global standards to ensure secure, lawful, and interoperable data management. Non-compliance may not only result in legal repercussions but also hinder cross-border system integration and trust [81]. Every device added to an AIoT ecosystem introduces a new vector for potential attacks. DDoS, spoofing, and zero-day exploits become increasingly difficult to prevent as the system expands [82]. In smart transportation, such breaches could paralyze city infrastructure or endanger lives. Decentralized intrusion detection systems and AI-driven threat intelligence platforms are critical for real-time detection and mitigation [83]. Public apprehension about being monitored and profiled by AIoT systems poses a barrier to widespread adoption [84]. People are especially concerned about data collected in private settings such as smart homes or personal health monitorsData flowing through AIoT systems must remain accurate and tamper-proof to ensure reliable decision-making. If attackers alter data streams in smart healthcare or safety systems, it can result in false alarms and missed warnings [85]. There is need of validation and secure audit trails, which are emerging as promising approaches to guarantee data integrity and traceability [86]. Implementing secure validation and audit trail mechanisms is essential for building trustworthy, transparent, and compliant AIoT systems that support ethical data governance [87].
4.3 State-of-the-Art Security and Privacy Techniques for AIoT
Below, State-of-the-art techniques are described to enhance security and privacy in AIoT ecosystems. These approaches reduce cloud dependency, protect sensitive data, and enable secure decentralized processing across domains. Fig. 12 shows the pictorial representation of the different techniques to overcome the challenges in AIoT deployment in smart societies, and Table 8 describes a summary of the different solutions with their purpose, domain and effectiveness. Their effectiveness has been demonstrated in healthcare, smart cities, transportation and other domains by improving data integrity, reducing latency, and enabling compliance with privacy regulations.
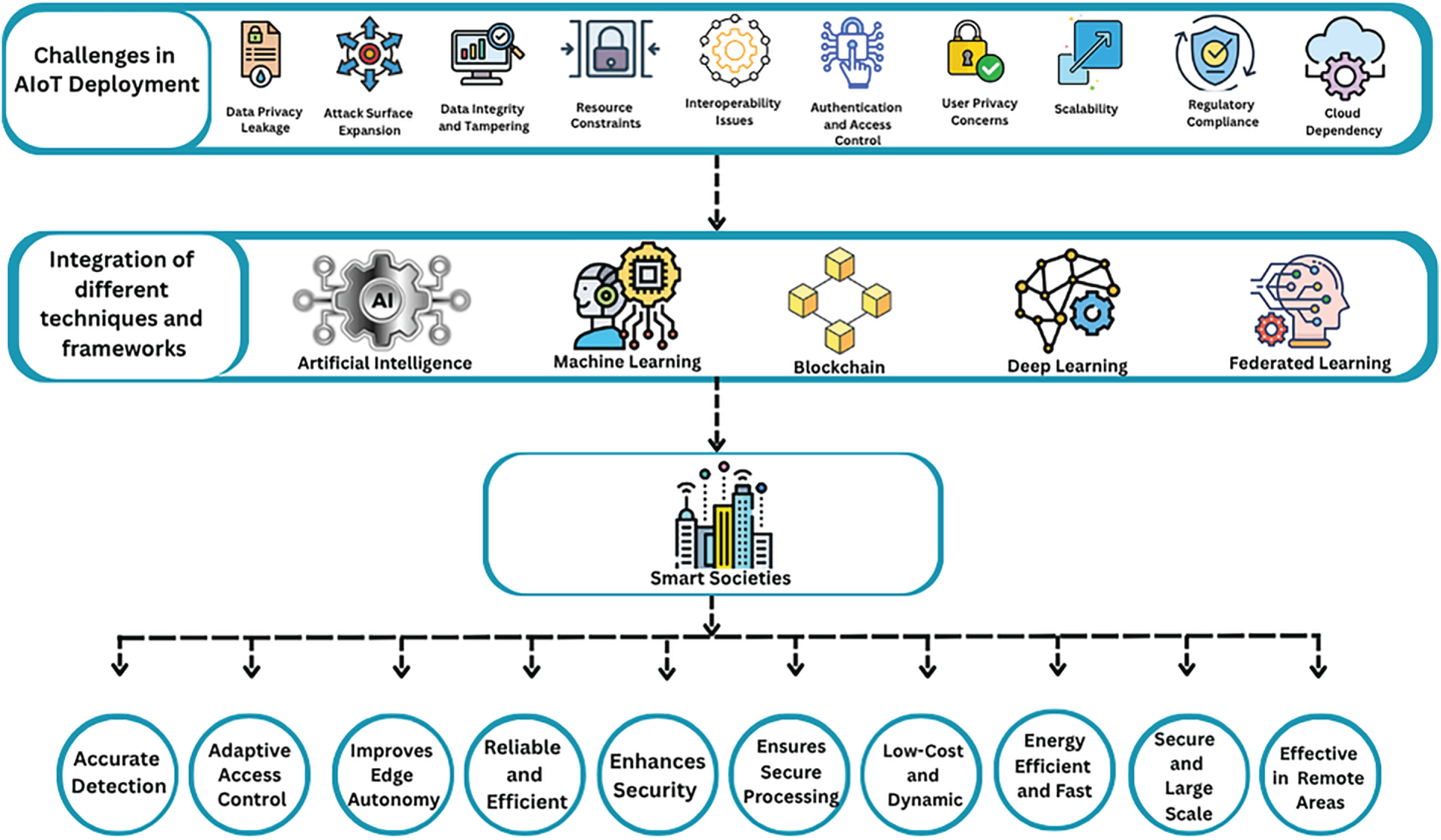
Figure 12: Different AI, Blockchain and Federated learning-based techniques and methods to overcome challenges in AIoT deployment in smart societies.
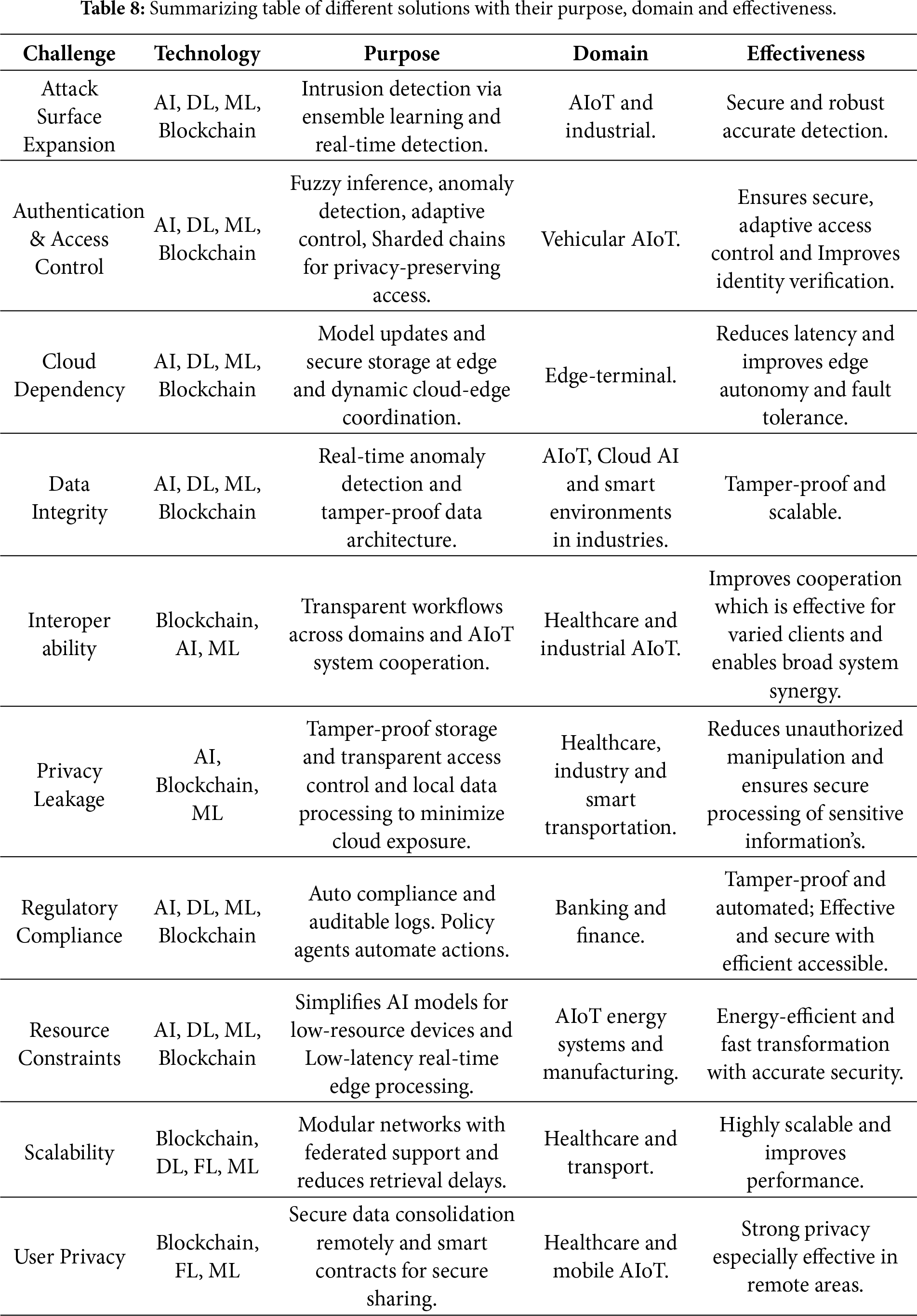
4.3.1 Blockchain- and AI-Based Solutions for Privacy Leakage
To address data privacy leakage in AIoT ecosystems, various blockchain, machine learning (ML), and artificial intelligence (AI) techniques have been developed. Blockchain-based decentralized architectures provide tamper-proof data storage and transparent access control, effectively reducing the risks of unauthorized data manipulation [88]. Federated learning enables distributed model training without sharing raw data, preserving local privacy while still enabling collaborative AI development [92]. Homomorphic encryption allows computation on encrypted data, ensuring that sensitive information remains secure during processing [93]. Differential privacy is often integrated into AI models to add noise and prevent individual data identification [94]. Edge MLOps frameworks further support data privacy by processing and training data locally, minimizing cloud exposure [95]. These combined approaches create a layered defence mechanism against privacy leakage in AIoT environments.
4.3.2 Blockchain- and AI-Based Solutions for Authentication and Access Control
Several techniques have been proposed to address authentication and access control in the AIoT ecosystem. The study of [96] introduced AI-HybridChain, combining image-based authentication, fuzzy inference systems, and deep reinforcement learning for secure access control. In another study, the authors [97] emphasized AI-driven identity and access management using biometrics, anomaly detection, and adaptive permission control. The authors of reference [98] proposed a hierarchical sharding blockchain model integrating federated learning for privacy-preserving and fine-grained access control in vehicular AIoT systems. In another study [99], the authors developed a policy decision point using supervised ML for distributed and accurate access control.
4.3.3 Blockchain- and AI-Based Solutions for Interoperability
There are different solutions provided by different authors to tackle interoperability issues across domains in the AIoT ecosystem. The authors of the study [100] proposed integrating smart contracts with ML workflows to improve cooperation and transparency across heterogeneous systems in different sectors. The authors of [101] developed a federated clustered multi-domain learning model using graph neural networks to address cross-client data variability in healthcare AIoT. In [102], the researchers suggested multimodal federated learning to enable cooperation among AIoT systems with different sensors and model architectures across transportation, agriculture, and healthcare domains. The study of [103] reviewed how combining AI, blockchain, and quantum cryptography can bridge interoperability and scalability gaps in industrial AIoT environments.
4.3.4 Blockchain- and AI-Based Solutions for Resource-Constrained AIoT Devices
The authors of [104] ntroduced manual pruning techniques to reduce model complexity and fit AI solutions within limited device capacities in energy systems. The reseachers of [105] developed a blockchain-enabled federated learning system that offloads computation from centralized servers and distributes tasks across mobile edge devices for efficient AIoT analytics. In another study [106], the researchers proposed using lightweight AI models and hardware accelerators for low-latency, energy-efficient real-time data processing at the edge. The research of [107] introduced a Property Preservation Framework using Markov chains to ensure efficient model transformation while minimizing resource usage in AIoT development. In [108], the authors created a blockchain-supported resource-sharing scheme for constrained manufacturing IoT devices, using smart contracts and semantic privacy-preserving rules. The reseachers of [109] proposed a blockchain-enabled digital twin framework for efficient botnet detection using deep learning without excessive data transmission in smart factories.
4.3.5 Blockchain- and AI-Based Solutions for Reducing Cloud Dependency
To reduce this dependency, reference [110] proposed a decentralized predictive maintenance system integrating deep learning and blockchain with IPFS, enabling edge-based model updates and secure storage. The authors of the study [111] developed QuAsyncFL, which enhances cloud-edge-terminal collaboration with asynchronous federated learning and quantization, reducing communication loads and dependency. Additionally, the authors of the study [112] proposed a carbon-aware AIoT framework that optimizes data acquisition and computation across local and edge nodes, decreasing reliance on centralized systems. The authors of [113] demonstrated how AI-driven orchestration across cloud-edge layers enhances resource distribution and fault tolerance while reducing latency.
4.3.6 Blockchain- and AI-Based Solutions for Scalability
Scalability in AIoT refers to the system’s ability to efficiently expand and manage increasing numbers of connected devices and data volumes without performance degradation [114]. The study of [115] proposed a federated modular neural network architecture supported by blockchain and 5G slicing to enable scalable AIoT in healthcare systems. New technologies including blockchain and hybrid deep learning are enhancing scalability, security, and efficiency of different systems. The author of [116] proposed a blockchain-based hybrid AI architecture for IoMT-enabled intelligent healthcare systems, demonstrating improved scalability, secure data processing, and efficient system orchestration. These technologies contribute to safe sharing of data, teamwork and improved performance, but such issues as the complexity of computations and the compliance with regulations should be mitigated to have a successful implementation. In another study, the researchers of [117] developed a distributed ML and blockchain-based system in Internet of Vehicles for secure and scalable model training across vehicles. The authors of [118] introduced a two-tier multi-zone blockchain consensus to overcome AIoT’s scalability and security bottlenecks by supporting interoperable and sharded blockchains. The study of the authors [119] proposed FedSwarm, an adaptive federated learning model using dynamic server-device interactions to improve AIoT scalability and efficiency. Additionally, The authors of [120] designed a sharding-based PoA blockchain with edge AI integration to address retrieval delays and improve scalability in healthcare AIoT applications.
4.3.7 Blockchain- and AI-Based Solutions for Regulatory Compliance
Regulatory compliance refers to adhering to laws, regulations, and standards applicable to industries and technologies, which in AIoT is complex due to cross-domain data handling, privacy, and ethical concerns [121]. The authors of [122] developed CAF-BEML, combining ML algorithms with blockchain to automate compliance auditing, risk prediction, and secure regulatory logs. In [123], the authors introduced Compliance-as-Code 2.0, embedding AI agents and blockchain in dynamic policy engines to automate regulatory actions and reduce compliance costs. The study of [124] proposed a predictive AI-based risk assessment framework that models regulatory impact, enabling preemptive compliance in AIoT finance systems.
4.3.8 Blockchain- and AI-Based Solutions for Attack Surface Reduction
The study of [116] addressed this by proposing a deep transfer learning-based intrusion detection system using ensemble techniques and quantization to enhance detection accuracy in IoT and IIoT networks. The research of [125] advocated AI-driven threat detection systems with anomaly detection and NLP for real-time defense against advanced persistent threats. The authors of [126] used defense distillation in AI-enhanced Intelligent Reflecting Surface networks to counter adversarial ML attacks in IIoT environments. The researchers of [127] proposed SmarterChain, which embeds ML models into blockchain to provide secure model execution and threat detection in AIoT environments.
4.3.9 Blockchain- and AI-Based Solutions for User Privacy Protection
User privacy concerns in AIoT involve fears over how sensitive personal data is collected, used, and potentially misused across connected smart environments. Federated learning (FL) prevents raw data from leaving devices, helping to preserve user privacy in mobile AI applications [128]. In industrial AIoT, reference [104] has been proposed secure federated meta-learning with drones for remote, privacy-preserving data consolidation. The research of [129] proposed a trusted cloud–edge decision model using blockchain and MLP enhances local data processing while securing user information at the edge. The study of [130] developed BioChainReward applies smart contracts and AI for privacy-aware biomedical data sharing, incentivizing users to contribute securely. Smart environments are sources of massive data, handled by blockchain technologies (BT) in a dependable and transparent manner. Nonetheless, BT also struggles with such security issues as attacks and malware, which demand AI-driven anomaly detection systems [10].
4.3.10 Blockchain- and AI-Based Solutions for Data Integrity and Tamper Resistance
Data integrity and tampering refer to the protection of data from unauthorized modifications, ensuring that information remains accurate, complete, and trustworthy throughout its lifecycle, especially critical in AIoT systems [131]. The research of [132] introduced AIAS, which leverages Ethereum smart contracts and IPFS to ensure decentralized application integrity. The research of [133] integrated blockchain with federated learning and secure multiparty computation to protect ML training data against unauthorized tampering. The study of [134] proposed a smart contract-based integrity framework aligned with NIST standards for tamper-resistant AI cloud systems. Lastly, the study of [91] presented a generalized blockchain-based AIoT architecture for tamper-proof data security in smart environments.
4.4 Performance Evaluation, Open Challenges, and Research Gaps
The blockchain- and AI-based mechanisms demonstrate strong performance in simulated and real-world deployments, particularly in terms of scalability, reliability, and regulatory compliance.These solutions enhance reliability through tamper-proof data handling and low-latency decision-making [135]. Fig. 13 represents the general benefits and real-world deployment and Table 9 is the comparison table of summarizing methods, threats addressed, and limitations.
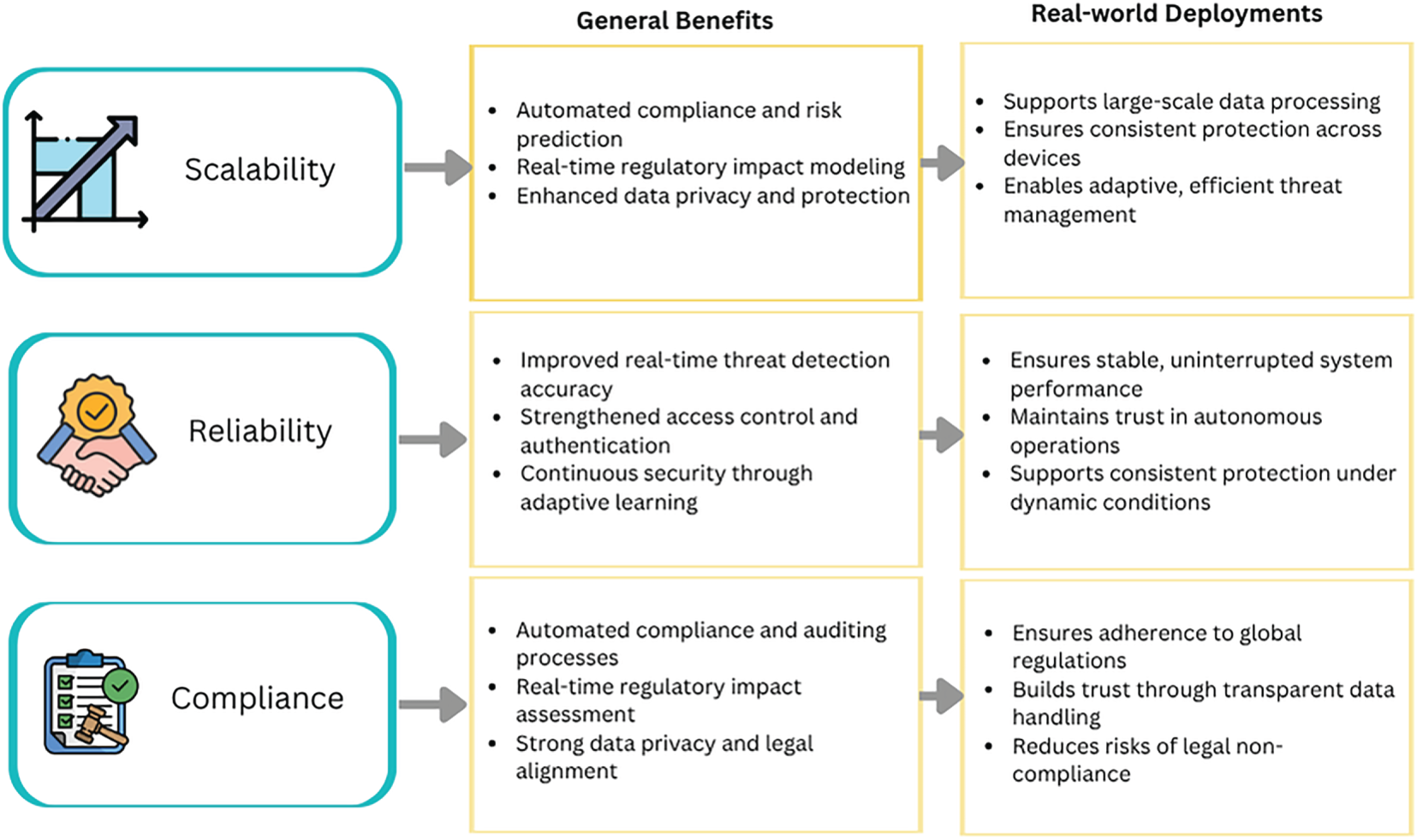
Figure 13: Benefits and real-world deployment impact of AI- and blockchain-based AIoT security mechanisms. This figure illustrates the practical benefits of AI- and blockchain-enabled security solutions in real-world AIoT deployments, highlighting improvements in scalability, reliability, data integrity, and regulatory compliance across application domains such as healthcare, smart cities, and industrial environments.
The scalability of the proposed AIoT security and privacy mechanisms is significantly enhanced through decentralized computing, federated learning, and blockchain sharding techniques [136]. For example, federated modular neural networks supported by blockchain and 5G slicing have proven effective in healthcare AIoT by enabling parallel, scalable data processing across distributed devices [115]. Sharding-based PoA blockchains integrated with edge AI reduce retrieval delays in large-scale healthcare environments [120]. Similarly FedSwarm utilizes dynamic server-device interactions to maintain scalability and efficiency in large AIoT networks [119]. In smart manufacturing and smart cities, scalable deployment has been enabled through lightweight AI models and blockchain-supported resource sharing, which reduce computation burden and central dependency [105].
In terms of reliability, these mechanisms utilize a multi-layered defense strategy combining AI-driven detection, smart contracts, and secure data distribution [137]. AI-HybridChain’s integration of deep reinforcement learning, image-based authentication, and fuzzy inference ensures robust access control in real-time environments [96]. Intrusion detection systems using deep transfer learning and ensemble techniques enhance detection accuracy for IoT and IIoT networks [116]. Blockchain-enabled digital twins support real-time, low-latency security monitoring in resource-constrained environments [109]. Furthermore, systems like Smarter Chain ensure continuous security by embedding ML models into blockchain for threat detection and secure model execution [127].
CAF-BEML and Compliance-as-Code 2.0 automate compliance auditing and risk prediction through machine learning and blockchain integration [122]. In financial and healthcare domains, predictive frameworks allow for preemptive compliance by modeling regulatory impacts in real-time [124]. Privacy-preserving techniques like federated learning [92], homomorphic encryption [93] and differential privacy [94], ensure user data remains compliant with laws like GDPR and HIPAA. Combined, these mechanisms offer robust tools for regulatory alignment in real-world AIoT deployments.
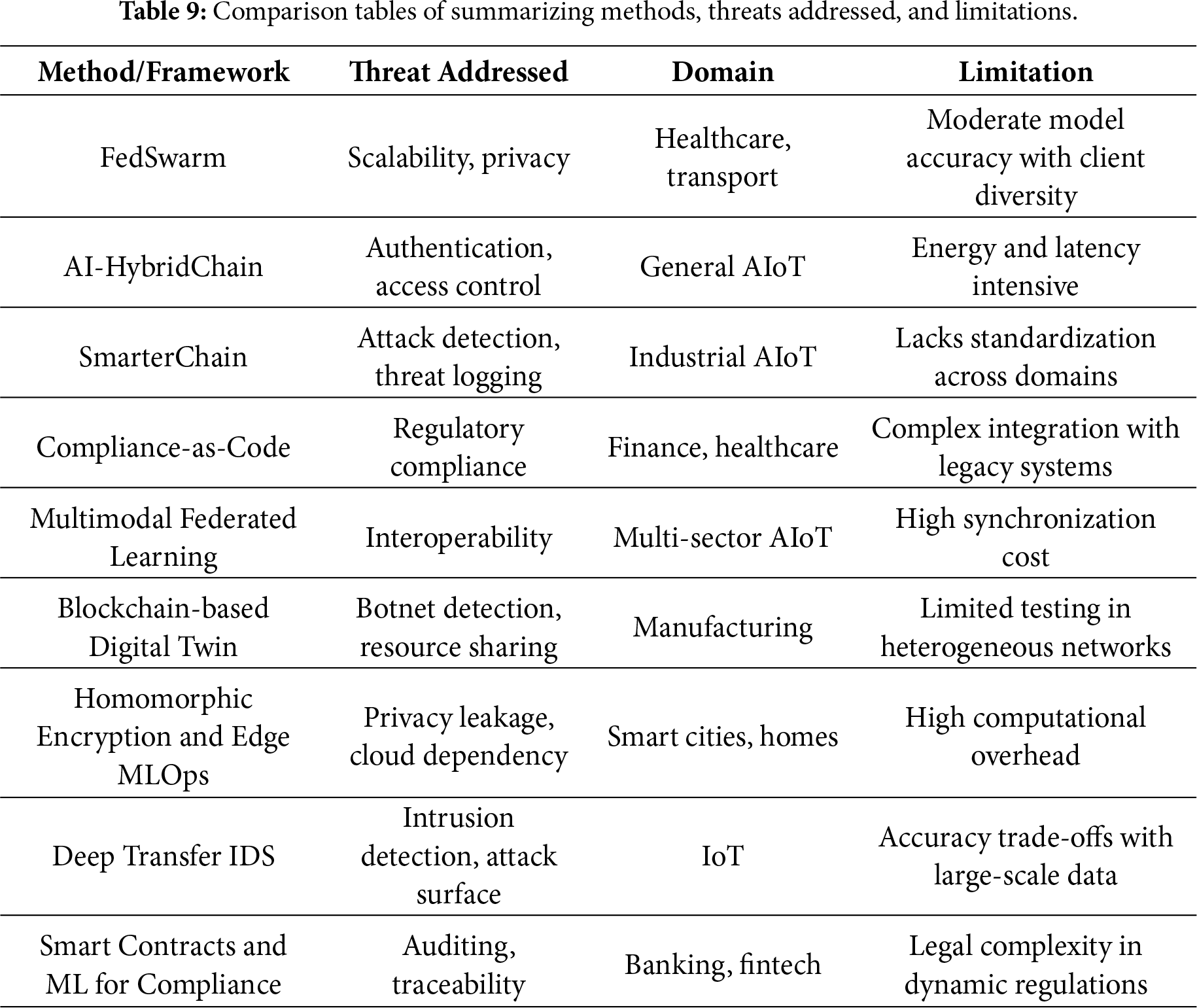
4.5 Evaluation of Current Solutions, Open Challenges, and Research Gaps
Evaluation of current solutions involves assessing how existing AIoT security and privacy methods perform in real-world and simulated settings. Research gaps highlight areas lacking sufficient study, such as dynamic threat adaptation and standardized compliance frameworks. Table 9 below shows the summarizing methods, threats addressed, and limitations and Fig. 14 shows the impact of current solutions, open challenges and research gaps.
Figure 14: The impact of current solutions, open challenges and research gaps.
4.5.1 Evaluation of Current Solutions
The performance of state-of-the-art AIoT security mechanisms has been evaluated across real-world and simulated settings using key metrics such as latency, accuracy, energy efficiency, and resilience to attacks. Federated learning models such as FedSwarm demonstrate strong scalability with low communication overhead and adaptive client-server interactions, making them suitable for healthcare and transportation domains. AI-HybridChain and SmarterChain frameworks provide robust authentication and access control using image-based deep learning and ML-embedded blockchains, respectively, showing high resilience to adversarial attacks and intrusion attempts. However, latency and energy consumption remain challenges in deep learning-based frameworks due to the need for real-time processing across distributed edge devices. Additionally, privacy-preserving techniques like homomorphic encryption and differential privacy introduce computational overhead that impacts performance on constrained AIoT hardware.
4.5.2 Open Challenges and Research Gaps
Despite these advancements, several open challenges remain. First, there is a trade-off between AI model explainability and robust security as AI models become more complex, understanding and validating their decisions becomes harder, which reduces trust in critical applications. Second, the lack of standardized protocols and unified security frameworks limits cross-domain interoperability and makes benchmarking difficult across use cases. Third, resource-constrained environments struggle with deploying real-time AI and encryption mechanisms simultaneously, demanding further innovation in lightweight cryptography and on-device intelligence. Another gap is in privacy-preserving data sharing across domains current federated models assume uniform privacy standards, which may not hold in global systems. Finally, adversarial defenses in federated and edge AI are still in early development and often fail against sophisticated poisoning or evasion attacks.
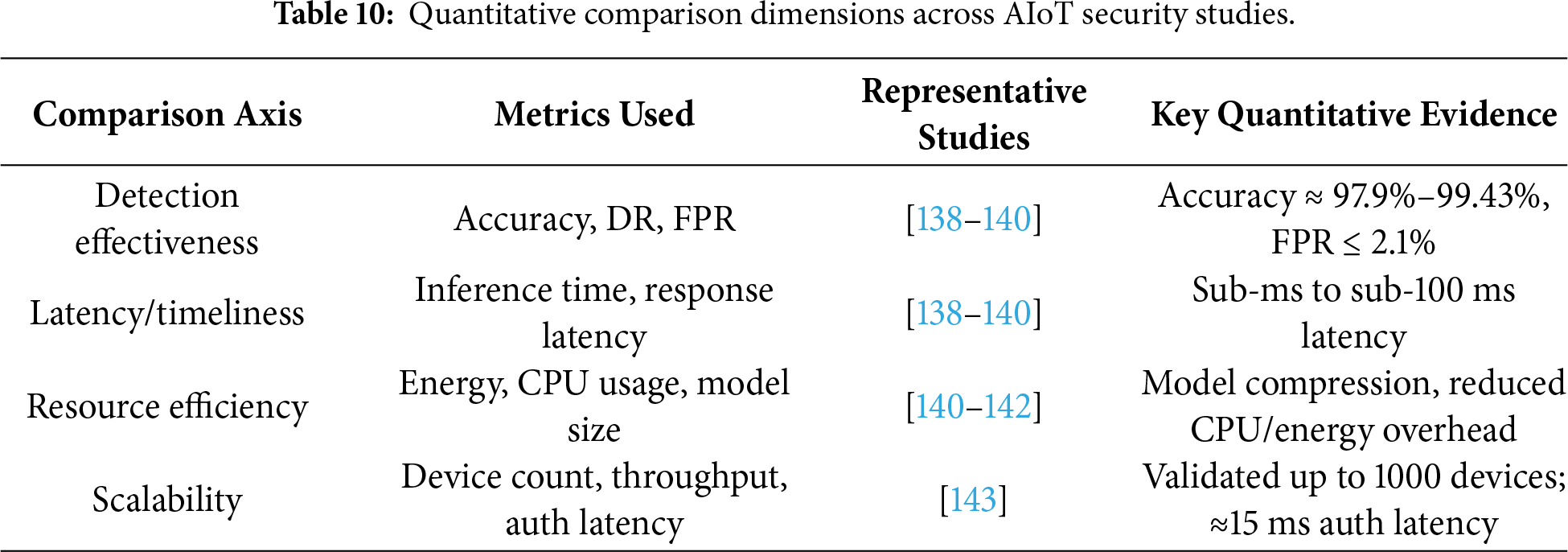
4.6 Quantitative Comparative Synthesis of Reported Performance Metrics
Although this SLR primarily follows a qualitative synthesis approach, it is complemented by a structured quantitative comparison based on performance metrics explicitly reported in the selected primary studies. This comparison focuses on four deployment-critical dimensions for AIoT-enabled smart societies: detection effectiveness, latency, resource efficiency, and scalability.
Several recent AIoT and IIoT security studies report quantitative detection performance metrics such as accuracy, detection rate, and false positive rate. For example, the authors [138] report an intrusion detection framework for IoT-enabled healthcare achieving 98.1% accuracy, 2.1% false positive rate, and 85–95 ms latency, demonstrating suitability for time-sensitive medical environments. The authors [139] present an edge-deployable decision-tree-based IDS evaluated on IIoT traffic, achieving 97.9%–98.2% accuracy with sub-millisecond inference time (≈0.8 ms), highlighting the feasibility of real-time protection on constrained edge devices. Similarly, reference [140] demonstrate a compressed DNN-KDQ intrusion detection model with 99.43% accuracy, 0.07 ms inference time per sample, and a significant model size reduction from 196.77 to 20.18 KB, making it well suited for resource-limited AIoT nodes.
From a resource-efficiency perspective, multiple studies explicitly quantify energy and computational overhead. The authors [141] show that a microservice-based privacy-preserving AIoT analytics framework reduces CPU usage and latency at the edge while maintaining analytical accuracy. The author [142] evaluates edge-assisted task offloading in smart environments and reports measurable reductions in energy consumption and execution delay compared to cloud-centric baselines. These results indicate that edge-centric and lightweight AI designs are increasingly capable of meeting AIoT energy constraints.
Scalability is quantitatively validated in several studies through experiments involving increasing numbers of devices or nodes. The authors [143] further demonstrate a hybrid AI–blockchain authentication framework achieving ≈15 ms authentication latency at 1000 devices, confirming scalability in dense AIoT deployments. In blockchain-enabled architectures, references [144,145] report throughput improvements and reduced consensus overhead using sharding-based designs, while references [146,147] emphasize scalability gains enabled by federated and edge-to-cloud AIoT architectures. Smart home systems apply modern machine learning, including ensemble learning and neural networks, in automated decision-making, such as the management of IoT devices in accordance with their usual routine. The adoption of blockchain technology, guaranteed decentralized authentication and attention to cost-effective components and the design oriented on security will help to reduce the threat of privacy and cyber-attacks.
Overall, this quantitative comparative synthesis—based on reported metrics rather than recomputed statistics—grounds the review’s findings in measurable evidence (Table 10). It enables cross-study comparison of effectiveness, timeliness, resource efficiency, and scalability while avoiding unsupported statistical aggregation across heterogeneous datasets and evaluation protocols.
4.7 Limitations and Threats to Validity
This systematic literature review is subject to several limitations that should be acknowledged when interpreting the findings. First, the review considers peer-reviewed publications published between 2020 and 2025, which may exclude earlier foundational works and very recent studies published after the search cutoff date. While this time window was intentionally selected to capture recent and relevant advances in AIoT security and privacy, it may limit the longitudinal perspective of the analysis.
Second, the literature search was conducted using a predefined set of major academic digital libraries. Although these sources are widely recognized and cover a large portion of high-quality AIoT research, relevant studies published in other venues, industrial white papers, standards documents, or preprint repositories may not have been captured, introducing potential selection bias.
Third, the inclusion and exclusion criteria, as well as the quality assessment process, rely on structured but inherently qualitative judgment. Despite the use of clearly defined assessment questions (Q1–Q7), some degree of subjectivity in study selection and evaluation cannot be fully eliminated.
Finally, due to the heterogeneity of application domains, evaluation metrics, and experimental settings across AIoT studies, the review emphasizes qualitative and comparative synthesis rather than quantitative meta-analysis. As a result, direct statistical comparison across studies is limited. These constraints do not undermine the validity of the review but should be considered when generalizing the results and identified research gaps.
This study has comprehensively explored the security and privacy challenges in AIoT-enabled smart societies by addressing three key research questions: identifying application-specific threats, evaluating state-of-the-art mitigation techniques and analyzing their real-world performance. It found that AIoT systems though transformative across healthcare, transportation, smart cities, and beyond are highly susceptible to threats such as privacy leakage, cloud dependency, and attack surface expansion. Blockchain, federated learning, edge AI, and smart contracts emerged as prominent tools for enhancing security, resilience, and compliance across these domains. However, performance trade-offs remain in latency, energy efficiency, and synchronization. To strengthen the trustworthiness and scalability of AIoT systems, future research should prioritize lightweight, explainable AI models, unified security standards, and real-time analytics tailored for constrained edge environments. It is also essential to develop dynamic compliance frameworks that adapt to evolving global regulations and support automated auditing. Embedding privacy and security-by-design principles into the lifecycle of AIoT architectures is crucial to realize the vision of a secure, privacy-preserving, and reliable smart society.
Acknowledgement: Not applicable.
Funding Statement: The authors received no specific funding for this study.
Author Contributions: Shahab Ali Khan, Syed Faisal Abbas Shah and Tehseen Mazhar perform the original writing part, software, and methodology; Wasim Ahmad and Tehseen Mazhar perform rewriting, investigation, design methodology, and conceptualization; Sunawar Khan, Habib Hamam and Afsha BiBi perform the related work part and manage results and discussions; Tehseen Mazhar, Usama Shah and Habib Hamam perform related work part and manage results and discussion; Shahab Ali Khan, Tehseen Mazhar and Habib Hamam perform rewriting, design methodology, and visualization; Sunawar Khan and Wasim Ahmad performs rewriting, design methodology, and visualization. All authors reviewed and approved the final version of the manuscript.
Availability of Data and Materials: Not applicable.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declares no conflicts of interest.
References
1. Alakkari K, Ali B. Artificial intelligence of things: a review. BJIoT. 2025;2025:113–20. doi:10.58496/bjiot/2025/006. [Google Scholar] [CrossRef]
2. Vivek Menon U, Babu Kumaravelu V, Vinoth Kumar C, Rammohan A, Chinnadurai S, Venkatesan R, et al. AI-powered IoT: a survey on integrating artificial intelligence with IoT for enhanced security, efficiency, and smart applications. IEEE Access. 2025;13:50296–339. doi:10.1109/access.2025.3551750. [Google Scholar] [CrossRef]
3. Siam SI, Ahn H, Liu L, Alam S, Shen H, Cao Z, et al. Artificial intelligence of things: a survey. ACM Trans Sen Netw. 2025;21(1):1–75. doi:10.1145/3690639. [Google Scholar] [CrossRef]
4. Elhoseny M, Abdel-Basset M, Shankar K. Artificial intelligence applications for smart societies. In: Artificial Intelligence Applications for Smart Societies. Berlin/Heidelberg, Germany: Springer; 2021. p. 1–18. doi:10.1007/978-3-030-63068-3_1. [Google Scholar] [CrossRef]
5. Adli HK. AIoT: bridging the gap between artificial intelligence and the Internet of Things. J Artif Intell Robot. 2023;1(1):1–3. doi:10.61577/jaiar.2024.100001. [Google Scholar] [CrossRef]
6. Mei Y, Wang W, Liang Y, Liu Q, Chen S, Wang T. Privacy-enhanced cooperative storage scheme for contact-free sensory data in AIoT with efficient synchronization. ACM Trans Sen Netw. 2024;20(4):1–19. doi:10.1145/3617998. [Google Scholar] [CrossRef]
7. Chang Z, Liu S, Xiong X, Cai Z, Tu G. A survey of recent advances in edge-computing-powered artificial intelligence of things. IEEE Internet Things J. 2021;8(18):13849–75. doi:10.1109/JIOT.2021.3088875. [Google Scholar] [CrossRef]
8. Ezam Z, Totakhail A, Ghafory H, Hakimi M. Transformative impact of artificial intelligence on IoT applications: a systematic review of advancements, challenges, and future trends. Int J Acad Pract Res. 2024;3(1):155–64. [Google Scholar]
9. Keshta I. AI-driven IoT for smart health care: security and privacy issues. Inform Med Unlocked. 2022;30:100903. doi:10.1016/j.imu.2022.100903. [Google Scholar] [CrossRef]
10. Chou SF, Kuo YL, Shih YY. A privacy preserving blockchain based framework for AIoT data exchange. In: 2022 IEEE Wireless Communications and Networking Conference (WCNC); 2022 Apr 10–13; Austin, TX, USA. p. 1170–5. doi:10.1109/WCNC51071.2022.9771669. [Google Scholar] [CrossRef]
11. Rathee G, Kumar A, Garg S, Choi BJ, Hassan MM. ART: active recognition trust mechanism for Augmented Intelligence of Things (AIoT) in smart enterprise systems. Alex Eng J. 2023;80:417–24. doi:10.1016/j.aej.2023.08.043. [Google Scholar] [CrossRef]
12. Rupanetti D, Kaabouch N. Combining edge computing-assisted Internet of Things security with artificial intelligence: applications, challenges, and opportunities. Appl Sci. 2024;14(16):7104. doi:10.3390/app14167104. [Google Scholar] [CrossRef]
13. Zhuang Y, Wang C, Zheng W, Victor N, Gadekallu TR. ERACMA: expressive and revocable access control with multi-authority for AIoT-enabled human centric consumer electronics. IEEE Trans Consum Electron. 2024;70(1):1102–11. doi:10.1109/TCE.2023.3306752. [Google Scholar] [CrossRef]
14. Meenal H, Kishor Kumar Reddy C, Malve D, Atthar MS, Doss S. AIoT and the governance of security. In: Information security governance using artificial intelligence of things in smart environments. Boca Raton, FL, USA: CRC Press; 2025. p. 23–40. doi:10.1201/9781003606307-2. [Google Scholar] [CrossRef]
15. Hassija V, Chamola V, Saxena V, Jain D, Goyal P, Sikdar B. A survey on IoT security: application areas, security threats, and solution architectures. IEEE Access. 2019;7:82721–43. doi:10.1109/access.2019.2924045. [Google Scholar] [CrossRef]
16. Javanmardi S, Nascita A, Pescapè A, Merlino G, Scarpa M. An integration perspective of security, privacy, and resource efficiency in IoT-Fog networks: a comprehensive survey. Comput Netw. 2025;270:111470. doi:10.1016/j.comnet.2025.111470. [Google Scholar] [CrossRef]
17. Ali J, Kumar Singh S, Jiang W, Alenezi AM, Islam M, Ibrahim Daradkeh Y, et al. A deep dive into cybersecurity solutions for AI-driven IoT-enabled smart cities in advanced communication networks. Comput Commun. 2025;229:108000. doi:10.1016/j.comcom.2024.108000. [Google Scholar] [CrossRef]
18. Ghadi YY, Mazhar T, Shah SFA, Haq I, Ahmad W, Ouahada K, et al. Integration of federated learning with IoT for smart cities applications, challenges, and solutions. PeerJ Comput Sci. 2023;9:e1657. doi:10.7717/peerj-cs.1657. [Google Scholar] [PubMed] [CrossRef]
19. Uddin B. Development of intelligent Internet of Things systems for real-time data processing and decision making. Int J Sci Rev. 2025;2(6):369–77. doi:10.71364/ijfsr.v2i6.48. [Google Scholar] [CrossRef]
20. Pei J, Li S, Yu Z, Ho L, Liu W, Wang L. Federated learning encounters 6G wireless communication in the scenario of Internet of Things. IEEE Comm Stand Mag. 2023;7(1):94–100. doi:10.1109/mcomstd.0005.2200044. [Google Scholar] [CrossRef]
21. Zuo Y, Guo J, Gao N, Zhu Y, Jin S, Li X. A survey of blockchain and artificial intelligence for 6G wireless communications. IEEE Commun Surv Tutorials. 2023;25(4):2494–528. doi:10.1109/comst.2023.3315374. [Google Scholar] [CrossRef]
22. Alahi MEE, Sukkuea A, Tina FW, Nag A, Kurdthongmee W, Suwannarat K, et al. Integration of IoT-enabled technologies and artificial intelligence (AI) for smart city scenario: recent advancements and future trends. Sensors. 2023;23(11):5206. doi:10.3390/s23115206. [Google Scholar] [PubMed] [CrossRef]
23. Ogenyi FC, Ugwu CN, Ugwu OP. A comprehensive review of AI-native 6G: integrating semantic communications, reconfigurable intelligent surfaces, and edge intelligence for next-generation connectivity. Front Commun Netw. 2025;6:1655410. doi:10.3389/frcmn.2025.1655410. [Google Scholar] [CrossRef]
24. Alghamedy FH, El-Haggar N, Alsumayt A, Alfawaer Z, Alshammari M, Amouri L, et al. Unlocking a promising future: integrating blockchain technology and FL-IoT in the journey to 6G. IEEE Access. 2024;12:115411–47. doi:10.1109/access.2024.3435968. [Google Scholar] [CrossRef]
25. Sleem A, Elhenawy I. Survey of artificial intelligence of things for smart buildings: a closer outlook. J Intell Syst Internet of Things. 2023;8(2):63–71. doi:10.54216/jisiot.080206. [Google Scholar] [CrossRef]
26. Shah K, Jadav NK, Tanwar S, Singh A, Pleşcan C, Alqahtani F, et al. AI and blockchain-assisted secure data-exchange framework for smart home systems. Mathematics. 2023;11(19):4062. doi:10.3390/math11194062. [Google Scholar] [CrossRef]
27. Oliha JS, Biu PW, Obi OC. Securing the smart city: a review of cybersecurity challenges and strategies. Eng Sci Technol J. 2024;5(2):496–506. doi:10.51594/estj.v5i2.827. [Google Scholar] [CrossRef]
28. Chouraik C, El-founir R, Taybi K. Comprehensive review of smart city cybersecurity strategies. Int J Appl Res Soc Sci. 2024;6(9):2112–20. doi:10.51594/ijarss.v6i9.1560. [Google Scholar] [CrossRef]
29. Prabha C, Mittal P, Sharma A, Singh J. AIoT emerging technologies, use cases, and its challenges in implementing smart cities. In: 2022 IEEE North Karnataka Subsection Flagship International Conference (NKCon); 2022 Nov 20–21; Vijaypur, India. p. 1–5. doi:10.1109/NKCon56289.2022.10126917. [Google Scholar] [CrossRef]
30. Ullah A, Quddusi S, Haider I. Incorporation of artificial intelligence in enhancing quality of life in smart cities. Am J Artif Intell. 2024;8(2):48–54. doi:10.11648/j.ajai.20240802.13. [Google Scholar] [CrossRef]
31. Pengyu E. Construction of a privacy management framework for AIoT enterprises based on risk analysis. In: Proceedings of the 2023 3rd International Conference on Big Data, Artificial Intelligence and Risk Management. New York, NY, USA: The Association for Computing Machinery (ACM); 2023. p. 599–608. doi:10.1145/3656766.3656867. [Google Scholar] [CrossRef]
32. Aouedi O, Vu TH, Sacco A, Nguyen DC, Piamrat K, Marchetto G, et al. A survey on intelligent Internet of Things: applications, security, privacy, and future directions. IEEE Commun Surv Tutorials. 2025;27(2):1238–92. doi:10.1109/comst.2024.3430368. [Google Scholar] [CrossRef]
33. Christou AG, Stergiou CL, Memos VA, Ishibashi Y, Psannis KE. Revolutionizing connectivity: the power of AI, IoT, and edge computing for smart and autonomous systems. In: 2023 6th World Symposium on Communication Engineering (WSCE); 2023 Sep 27–29; Thessaloniki, Greece. p. 56–60. doi:10.1109/WSCE59557.2023.10365771. [Google Scholar] [CrossRef]
34. Manivannan RSM, Surendiran J. AI-Siot hybrid architecture for seamless integration of IoT in smart cities. In: 2024 IEEE 13th International Conference on Communication Systems and Network Technologies (CSNT); 2024 Apr 6–7; Jabalpur, India. p. 393–9. doi:10.1109/CSNT60213.2024.10546157. [Google Scholar] [CrossRef]
35. Moawad MM, Madbouly MM, Guirguis SK. Leveraging blockchain and machine learning to improve IoT security for smart cities. In: The 3rd International Conference on Artificial Intelligence and Computer Vision (AICV2023). Cham, Switzerland: Springer Nature; 2023. p. 216–28. doi:10.1007/978-3-031-27762-7_21. [Google Scholar] [CrossRef]
36. Bharathi M, Srinivas TAS, Bhuvaneswari M. Decentralized intelligence in smart industry: federated learning for enhanced manufacturing. J Data Struct Comput. 2024;1(2):19–36. doi:10.48001/jodsc.2024.1219-36. [Google Scholar] [CrossRef]
37. Barletta VS, Caivano D, De Vincentiis M, Pal A, Scalera M. Hybrid quantum architecture for smart city security. J Syst Softw. 2024;217:112161. doi:10.1016/j.jss.2024.112161. [Google Scholar] [CrossRef]
38. Adli HK, Remli MA, Wan Salihin Wong KNS, Ismail NA, González-Briones A, Corchado JM, et al. Recent advancements and challenges of AIoT application in smart agriculture: a review. Sensors. 2023;23(7):3752. doi:10.3390/s23073752. [Google Scholar] [PubMed] [CrossRef]
39. Issa W, Moustafa N, Turnbull B, Sohrabi N, Tari Z. Blockchain-based federated learning for securing Internet of Things: a comprehensive survey. ACM Comput Surv. 2023;55(9):1–43. doi:10.1145/3560816. [Google Scholar] [CrossRef]
40. Bugeja J, Jacobsson A. Green intelligent homes: a perspective on the future of smart homes and their implications. In: Proceedings of the 8th International Conference on Internet of Things, Big Data and Security; 2023 Apr 21–23; Prague, Czech Republic. p. 186–93. doi:10.5220/0011964800003482. [Google Scholar] [CrossRef]
41. Taiwo O, Ezugwu AE. Internet of Things-based intelligent smart home control system. Secur Commun Netw. 2021;2021:9928254–17. doi:10.1155/2021/9928254. [Google Scholar] [CrossRef]
42. Anubha A, Narang D, Raj A. AIoT-enabled smart homes solution to security, comfort, and energy efficiency. In: Merging artificial intelligence with the internet of things. Hershey, PA, USA: IGI Global Scientific Publishing; 2025. p. 239–68. doi:10.4018/979-8-3693-8547-0.ch008. [Google Scholar] [CrossRef]
43. Yan J. AIoT in smart homes: challenges, strategic solutions, and future directions. Highlights Sci Eng Technol. 2024;87:59–65. doi:10.54097/8hzgaf51. [Google Scholar] [CrossRef]
44. Miller T, Mikiciuk G, Durlik I, Mikiciuk M, Łobodzińska A, Śnieg M. The IoT and AI in agriculture: the time is now—a systematic review of smart sensing technologies. Sensors. 2025;25(12):3583. doi:10.3390/s25123583. [Google Scholar] [PubMed] [CrossRef]
45. Pierre N, Viviane I, Lambert U, Viviane I, Shadrack I, Erneste B, et al. AI based real-time weather condition prediction with optimized agricultural resources. Eur J Technol. 2023;7(2):36–49. doi:10.47672/ejt.1496. [Google Scholar] [CrossRef]
46. Muhammed D, Ahvar E, Ahvar S, Trocan M, Montpetit MJ, Ehsani R. Artificial Intelligence of Things (AIoT) for smart agriculture: a review of architectures, technologies and solutions. J Netw Comput Appl. 2024;228:103905. doi:10.1016/j.jnca.2024.103905. [Google Scholar] [CrossRef]
47. Hemalatha J, Balasubramanian C, Sekar M, Pandian PS, Rajeswari S. AIoT-powered proactive elderly healthcare: wearable monitoring. In: Rehabilitation engineering, assistive technologies and the future of healthcare using robotics. Amsterdam, The Netherlands: Elsevier; 2025. p. 165–82. doi:10.1016/b978-0-443-31624-1.00009-5. [Google Scholar] [CrossRef]
48. Dutta Z. Artificial intelligence in wearable technology for enhanced healthcare monitoring: challengesand innovations. Int J Artif Intell Mach Learning. 2019;6(5):385–90. doi:10.1002/9781394389131.ch23. [Google Scholar] [CrossRef]
49. Ghadi YY, Shah SFA, Waheed W, Mazhar T, Ahmad W, Saeed MM, et al. Integration of wearable technology and artificial intelligence in digital health for remote patient care. J Cloud Comput. 2025;14(1):39. doi:10.1186/s13677-025-00759-4. [Google Scholar] [CrossRef]
50. Ji G, Woo J, Lee G, Msigwa C, Bernard D, Yun J. AIoT-based smart healthcare in everyday lives: data collection and standardization from smartphones and smartwatches. IEEE Internet Things J. 2024;11(16):27597–619. doi:10.1109/JIOT.2024.3400509. [Google Scholar] [CrossRef]
51. Dawale SV, Kanaga Suba Raja S, Darsan RV. Urban living through AIoT integration in smart cities. In: AIoT. Boca Raton, FL, USA: Auerbach Publications; 2025. p. 312–39. doi:10.1201/9781003482338-14. [Google Scholar] [CrossRef]
52. Rahmayanti D. Artificial intelligence of things (AIoT) to improve efficiency and automation in industrial 4.0. Sci Tech J. 2024;3(3):255–70. doi:10.56709/stj.v3i3.656. [Google Scholar] [CrossRef]
53. Ogunyankinnu T, Osunkanmibi AA, Onotole EF, Ukatu CE, Ajayi OA, Adeoye Y. AI-powered demand forecasting for enhancing JIT inventory models. J Front Multidiscip Res. 2024;5(1):184–96. doi:10.54660/.ijfmr.2024.5.1.184-196. [Google Scholar] [CrossRef]
54. Singh AK. Smart eco-friendly manufacturing system with AIoT applications. J Adv Artif Intell. 2025;3(2);109–21. [Google Scholar]
55. Eyo-Udo NL. Leveraging artificial intelligence for enhanced supply chain optimization. Open Access Res J Multidiscip Stud. 2024;7(2):1–15. doi:10.53022/oarjms.2024.7.2.0044. [Google Scholar] [CrossRef]
56. Nozari H,Tavakkoli-Moghaddam R, Rohaninejad M, Hanzálek Z. Artificial intelligence of things (AIoT) strategies for a smart sustainable-resilient supply chain. In: IFIP International Conference on Advances in Production Management Systems. Berlin/Heidelberg, Germany: Springer; 2023. p. 805–16. [Google Scholar]
57. Ud Din I, Almogren A, Rodrigues JJPC. AIoT integration in autonomous vehicles: enhancing road cooperation and traffic management. IEEE Internet Things J. 2024;11(22):35942–9. doi:10.1109/JIOT.2024.3387927. [Google Scholar] [CrossRef]
58. Elbasha AM, Abdellatif MM. AIoT-based smart traffic management system. arXiv:2502.02821. 2025. [Google Scholar]
59. Nadar A, Härri J. An AI-as-a-service platform for an artificial intelligence of things (AIoT). In: 2024 IEEE 99th Vehicular Technology Conference (VTC2024-Spring); 2024 Jun 24–27; Singapore. p. 1–7. doi:10.1109/VTC2024-Spring62846.2024.10683357. [Google Scholar] [CrossRef]
60. Popescu SM, Mansoor S, Ali Wani O, Kumar SS, Sharma V, Sharma A, et al. Artificial intelligence and IoT driven technologies for environmental pollution monitoring and management. Front Environ Sci. 2024;12:1336088. doi:10.3389/fenvs.2024.1336088. [Google Scholar] [CrossRef]
61. Bibri SE, Huang J, Krogstie J. Artificial intelligence of things for synergizing smarter eco-city brain, metabolism, and platform: pioneering data-driven environmental governance. Sustain Cities Soc. 2024;108:105516. doi:10.1016/j.scs.2024.105516. [Google Scholar] [CrossRef]
62. Gupta AD, Pandey P, Feijóo A, Yaseen ZM, Bokde ND. Smart water technology for efficient water resource management: a review. Energies. 2020;13(23):6268. doi:10.3390/en13236268. [Google Scholar] [CrossRef]
63. Alaba FA, Sani U, Dada EG, Mohammed BH. AIoT-enabled smart grids: advancing energy efficiency and renewable energy integration. In: Artificial intelligence of things for achieving sustainable development goals. Cham, Switzerland: Springer Nature; 2024. p. 59–79. doi:10.1007/978-3-031-53433-1_4. [Google Scholar] [CrossRef]
64. Mazhar T, Irfan HM, Haq I, Ullah I, Ashraf M, Al Shloul T, et al. Analysis of challenges and solutions of IoT in smart grids using AI and machine learning techniques: a review. Electronics. 2023;12(1):242. doi:10.3390/electronics12010242. [Google Scholar] [CrossRef]
65. Salama AK, Abdellatif MM. AIoT-based smart home energy management system. In: 2022 IEEE Global Conference on Artificial Intelligence and Internet of Things (GCAIoT); 2022 Dec 18–21; Alamein New City, Egypt. p. 177–81. doi:10.1109/GCAIoT57150.2022.10019091. [Google Scholar] [CrossRef]
66. Shennib F, Eicker U, Schmitt K. OpenWasteAI—open data, IoT, and AI for circular economy and waste tracking in resource-constrained communities. IEEE Technol Soc Mag. 2024;43(1):39–53. doi:10.1109/MTS.2024.3372610. [Google Scholar] [CrossRef]
67. Mishra S, Jena L, Tripathy HK, Gaber T. Prioritized and predictive intelligence of things enabled waste management model in smart and sustainable environment. PLoS One. 2022;17(8):e0272383. doi:10.1371/journal.pone.0272383. [Google Scholar] [PubMed] [CrossRef]
68. Sung WT, Vilia Devi I, Hsiao SJ, Nurul Fadillah F. Smart garbage Bin based on AIoT. Intell Autom Soft Comput. 2022;32(3):1387–401. doi:10.32604/iasc.2022.022828. [Google Scholar] [CrossRef]
69. Kumar S, Singh SK, Gupta BB, Psannis KE, Wu J. Homomorphic encryption in smart city applications for balancing privacy and utility. In: Innovations in modern cryptography. Hershey, PA, USA: IGI Global; 2024. p. 241–69. doi:10.4018/979-8-3693-5330-1.ch010. [Google Scholar] [CrossRef]
70. Yang Z, Xiong B, Chen K, Yang LT, Deng X, Zhu C, et al. Differentially private federated tensor completion for cloud-edge collaborative AIoT data prediction. IEEE Internet Things J. 2024;11(1):256–67. doi:10.1109/jiot.2023.3314460. [Google Scholar] [CrossRef]
71. Ali G, Mijwil MM. Cybersecurity for sustainable smart healthcare: state of the art, taxonomy, mechanisms, and essential roles. Mesopot J CyberSecur. 2024;4(2):20–62. doi:10.58496/mjcs/2024/006. [Google Scholar] [CrossRef]
72. Liu K, Wang C, Zhou X. Decentralizing access control system for data sharing in smart grid. High Confid Comput. 2023;3(2):100113. doi:10.1016/j.hcc.2023.100113. [Google Scholar] [CrossRef]
73. Sun K, Wang X, Zhao Q. A comprehensive review of AIoT-based edge devices and lightweight deployment Authorea Preprints. 2022. doi:10.36227/techrxiv.21687248. [Google Scholar] [CrossRef]
74. Rong G, Xu Y, Tong X, Fan H. An edge-cloud collaborative computing platform for building AIoT applications efficiently. J Cloud Comput. 2021;10(1):36. doi:10.1186/s13677-021-00250-w. [Google Scholar] [CrossRef]
75. Sharma V, Tan TG, Singh S, Sharma PK. Optimal and privacy-aware resource management in artificial intelligence of things using osmotic computing. IEEE Trans Ind Inf. 2022;18(5):3377–86. doi:10.1109/tii.2021.3102471. [Google Scholar] [CrossRef]
76. Khyzer H, Zhang Y, Rashid RM. Towards smarter cities: an adaptive AIoT solution with dynamic sensor group selection for real-time traffic monitoring and energy efficiency. In: 2024 10th International Conference on Computer and Communications (ICCC); 2024 Dec 13–16; Chengdu, China. p. 2450–5. doi:10.1109/ICCC62609.2024.10941814. [Google Scholar] [CrossRef]
77. Dwivedi B, Behl R. Case study successful artificial intelligence (AI) and the internet of things (IoT)(AIoT) implementation in smart cities. In: Merging artificial intelligence with the internet of things. Hershey, PA, USA: IGI Global Scientific Publishing; 2025. p. 167–202. doi:10.4018/979-8-3693-8547-0.ch006. [Google Scholar] [CrossRef]
78. Kurde A, Singh SK. Next-generation technologies for secure future communication-based social-media 3.0 and smart environment. IECE Trans Sens Commun Control. 2024;1(2):101–25. doi:10.62762/tscc.2024.322898. [Google Scholar] [CrossRef]
79. Shafik W. Governance frameworks for artificial intelligence of things (AIoT) security. In: Information security governance using artificial intelligence of things in smart environments. Boca Raton, FL, USA: CRC Press; 2025. p. 86–110. doi:10.1201/9781003606307-4. [Google Scholar] [CrossRef]
80. Sani AI. Regulatory framework and standards for sustainable IoT, Fog, computing, and blockchain. In: Energy-efficient deep learning approaches in IoT, fog, and green blockchain revolution. Hershey, PA, USA: IGI Global Scientific Publishing; 2025. p. 321–52. doi:10.4018/979-8-3373-0300-0.ch013. [Google Scholar] [CrossRef]
81. Chang Q. The legal and regulatory issues of AI technology in cross-border data flow in international trade. Trans Econ Bus Manage Res. 2024;8:111–7. doi:10.62051/cyw9y102. [Google Scholar] [CrossRef]
82. Rajasekaran AS, Al-Turjman F. AIoT: Artificial Intelligence of Things. Boca Raton, FL, USA: CRC Press; 2025. [Google Scholar]
83. Tan L, Yu K, Ming F, Cheng X, Srivastava G. Secure and resilient artificial intelligence of things: a HoneyNet approach for threat detection and situational awareness. IEEE Consum Electron Mag. 2022;11(3):69–78. doi:10.1109/MCE.2021.3081874. [Google Scholar] [CrossRef]
84. Ishengoma FR, Shao D, Alexopoulos C, Saxena S, Nikiforova A. Integration of artificial intelligence of things (AIoT) in the public sector: drivers, barriers and future research agenda. Digit Policy Regul Gov. 2022;24(5):449–62. doi:10.1108/dprg-06-2022-0067. [Google Scholar] [CrossRef]
85. Ali D, Iqbal S, Rafique S, Khan FR. Securing healthcare with AIoT. In: Information security governance using artificial intelligence of things in smart environments. Boca Raton, FL, USA: CRC Press; 2025. p. 206–26. doi:10.1201/9781003606307-10. [Google Scholar] [CrossRef]
86. Ikhalea N, Chinonso Chianumba E, Yetunde Mustapha A, Yeboah Forkuo A. A conceptual framework for enhancing healthcare data security using blockchain and AI. Int J Adv Multidisc Res Stud. 2024;4(6):1573–90. doi:10.62225/2583049x.2024.4.6.4061. [Google Scholar] [CrossRef]
87. Regueiro C, Seco I, Gutiérrez-Agüero I, Urquizu B, Mansell J. A blockchain-based audit trail mechanism: design and implementation. Algorithms. 2021;14(12):341. doi:10.3390/a14120341. [Google Scholar] [CrossRef]
88. Wazid M, Das AK, Park Y. Blockchain-envisioned secure authentication approach in AIoT: applications, challenges, and future research. Wirel Commun Mob Comput. 2021;2021:3866006. doi:10.1155/2021/3866006. [Google Scholar] [CrossRef]
89. Stanko A, Duda O, Mykytyshyn A, Totosko O, Koroliuk R. Artificial intelligence of things (AIoTintegration challenges, and security issues. In: Proceedings of the 1st International Workshop on Bioinformatics and Applied Information Technologies (BAIT 2024); 2024 Oct 2–4; Zboriv, Ukraine. [Google Scholar]
90. Hou KM, Diao X, Shi H, Ding H, Zhou H, de Vaulx C. Trends and challenges in AIoT/IIoT/IoT implementation. Sensors. 2023;23(11):5074. doi:10.3390/s23115074. [Google Scholar] [PubMed] [CrossRef]
91. Arora P, Makani R. Blockchain integration with AIoT data security and privacy for sustainability. J Artif Intell Syst. 2024;6(1):112–23. doi:10.33969/ais.2024060108. [Google Scholar] [CrossRef]
92. Islam A, Karimipour H, Fapojuwo AO. A federated meta learning-based secure data consolidation scheme for industrial AIoT leveraging drone. IEEE Trans Veh Technol. 2025;74(1):1702–7. doi:10.1109/TVT.2024.3456029. [Google Scholar] [CrossRef]
93. Tang X, Zhu L, Shen M, Peng J, Kang J, Niyato D, et al. Secure and trusted collaborative learning based on blockchain for artificial intelligence of things. IEEE Wirel Commun. 2022;29(3):14–22. doi:10.1109/mwc.003.2100598. [Google Scholar] [CrossRef]
94. Wang Z, Liu X, Shao X, Alghamdi A, Alrizq M, Munir MS, et al. An optimized and scalable blockchain-based distributed learning platform for consumer IoT. Mathematics. 2023;11(23):4844. doi:10.3390/math11234844. [Google Scholar] [CrossRef]
95. Raj E, Buffoni D, Westerlund M, Ahola K. Edge MLOps: an automation framework for AIoT applications. In: 2021 IEEE International Conference on Cloud Engineering (IC2E); 2021 Oct 4–8; San Francisco, CA, USA. p. 191–200. doi:10.1109/ic2e52221.2021.00034. [Google Scholar] [CrossRef]
96. Krishnan SC. AI-HybridChain: picturized authentication and DRL based access control method with secure two fold revocation for ensuring cloud computing security. Future Gener Comput Syst. 2024;160:389–405. doi:10.1016/j.future.2024.04.054. [Google Scholar] [CrossRef]
97. Rebouças Filho WL. The role of AI in enhancing identity and access management systems. Int Seven J Multidiscip. 2022;1(2):1–6. doi:10.56238/isevmjv1n2-011. [Google Scholar] [CrossRef]
98. Zhai M, Wu Q, Liu Y, Qin B, Yang Y, Muhammad G, et al. Privacy preservation in AI-driven IoT for vehicles via hierarchical sharding blockchain. IEEE Internet Things J. 2025;12(8):10278–92. doi:10.1109/jiot.2024.3513770. [Google Scholar] [CrossRef]
99. Shanmugavelan USAR. Revolutionizing role-based access control: the impact of AI and machine learning in identity and access management. J Artif Intell Cloud Comput. 2023:1–7. doi:10.47363/jaicc/2023(2)236. [Google Scholar] [CrossRef]
100. Jopate R, DivyaJyothi MG, Zuwayid Juma Alhasani AS. Blockchain technology integration across diverse domains in machine learning applications. In: 2024 2nd International Conference on Computing and Data Analytics (ICCDA); 2024 Nov 12–13; Shinas, Oman. p. 1–4. doi:10.1109/ICCDA64887.2024.10867350. [Google Scholar] [CrossRef]
101. Jiang S, Li Y, Firouzi F, Chakrabarty K. Federated clustered multi-domain learning for health monitoring. Sci Rep. 2024;14:903. doi:10.1038/s41598-024-51344-9. [Google Scholar] [PubMed] [CrossRef]
102. Anagnostopoulos C, Gkillas A, Mavrokefalidis C, Pikoulis EV, Piperigkos N, Lalos AS. Multimodal federated learning in AIoT systems: existing solutions, applications, and challenges. IEEE Access. 2024;12:180864–902. doi:10.1109/access.2024.3508030. [Google Scholar] [CrossRef]
103. Ali G, Samuel A, Kabiito SP, Morish Z, Thomas A, Robert W, et al. Integration of artificial intelligence, blockchain, and quantum cryptography for securing the industrial Internet of Things (IIoTrecent advancements and future trends. Appl Data Sci Anal. 2025;2025:19–82. doi:10.58496/adsa/2025/004. [Google Scholar] [CrossRef]
104. Weber MP. AIoT chances in resource-constrained environments via manual pruning. In: Innovations for community services. Cham, Switzerland: Springer Nature; 2023. p. 334–44. doi:10.1007/978-3-031-40852-6_19. [Google Scholar] [CrossRef]
105. Alghamdi A, Zhu J, Yin G, Shorfuzzaman M, Alsufyani N, Alyami S, et al. Blockchain empowered federated learning ecosystem for securing consumer IoT features analysis. Sensors. 2022;22(18):6786. doi:10.3390/s22186786. [Google Scholar] [PubMed] [CrossRef]
106. Arjunan G. Optimizing edge AI for real-time data processing in IoT devices: challenges and solutions. Int J Sci Res Manage. 2023;11(6):944–53. doi:10.18535/ijsrm/v11i06.ec2. [Google Scholar] [CrossRef]
107. Jadoon G, Ahmed A, Ud Din I, Almogren A, Zareei M, Biswal RR, et al. Dynamic property preservation in AIoT: a machine learning approach for data-efficient model transformation. IEEE Access. 2024;12:130707–22. doi:10.1109/access.2024.3454717. [Google Scholar] [CrossRef]
108. Tan J, Shi J, Wan J, Dai HN, Jin J, Zhang R. Blockchain-based data security and sharing for resource-constrained devices in manufacturing IoT. IEEE Internet Things J. 2024;11(15):25558–67. doi:10.1109/jiot.2024.3363013. [Google Scholar] [CrossRef]
109. Salim MM, Comivi AK, Nurbek T, Park H, Park JH. A blockchain-enabled secure digital twin framework for early botnet detection in IIoT environment. Sensors. 2022;22(16):6133. doi:10.3390/s22166133. [Google Scholar] [PubMed] [CrossRef]
110. Alabadi M, Habbal A. Next-generation predictive maintenance: leveraging blockchain and dynamic deep learning in a domain-independent system. PeerJ Comput Sci. 2023;9:e1712. doi:10.7717/peerj-cs.1712. [Google Scholar] [PubMed] [CrossRef]
111. Liu Y, Huang P, Yang F, Huang K, Shu L. QuAsyncFL: asynchronous federated learning with quantization for cloud–edge–terminal collaboration enabled AIoT. IEEE Internet Things J. 2024;11(1):59–69. doi:10.1109/JIOT.2023.3290818. [Google Scholar] [CrossRef]
112. Song Z, Xie M, Luo J, Gong T, Chen W. A carbon-aware framework for energy-efficient data acquisition and task offloading in sustainable AIoT ecosystems. IEEE Internet Things J. 2024;11(24):39103–13. doi:10.1109/JIOT.2024.3472669. [Google Scholar] [CrossRef]
113. Ramamoorthi V. Exploring AI-driven cloud-edge orchestration for IoT applications. Int J Sci Res Comput Sci Eng Inf Technol. 2023;9:385–93. doi:10.32628/cseit239072. [Google Scholar] [CrossRef]
114. Klemetti A, Räsänen E. Foundations and case studies on the scalable intelligence in AIoT domains. Open Eng. 2022;12(1):878–89. doi:10.1515/eng-2022-0381. [Google Scholar] [CrossRef]
115. Djoudi A, Guellouma Y, Cherroun H, Brik B. A scalable federated modular neural network architecture for edge-enabled beyond-5G complex systems. IT Prof. 2024;26(6):62–9. doi:10.1109/mitp.2024.3486105. [Google Scholar] [CrossRef]
116. Ahmad B, Wu Z, Huang Y, Rehman SU. Enhancing the security in IoT and IIoT networks: an intrusion detection scheme leveraging deep transfer learning. Knowl Based Syst. 2024;305:112614. doi:10.1016/j.knosys.2024.112614. [Google Scholar] [CrossRef]
117. Zamanirafe M, Mansourian P, Zhang N. Blockchain and machine learning in Internet of vehicles: applications, challenges, and opportunities. IEEE Internet Things Mag. 2023;6(3):98–103. doi:10.1109/IOTM.001.2300073. [Google Scholar] [CrossRef]
118. Liu W, Cao B, Peng M. Two-tier multi-zone consensus: enable intelligence sharing for AIoT with enhanced security. In: 2024 IEEE Annual Congress on Artificial Intelligence of Things (AIoT); 2024 Jul 24–26; Melbourne, VIC, Australia. p. 232–8. doi:10.1109/AIoT63253.2024.00052. [Google Scholar] [CrossRef]
119. Du H, Ni C, Cheng C, Xiang Q, Chen X, Liu X. FedSwarm: an adaptive federated learning framework for scalable AIoT. IEEE Internet Things J. 2024;11(5):8268–87. doi:10.1109/jiot.2023.3321325. [Google Scholar] [CrossRef]
120. Jun M. Platform framework for blockchain-enhanced healthcare AIoT systems. Front Commun Netw. 2025;6:1538965. doi:10.3389/frcmn.2025.1538965. [Google Scholar] [CrossRef]
121. Solanke B, Onita FB, Ochulor OJ, Iriogbe HO. The impact of artificial intelligence on regulatory compliance in the oil and gas industry. Int J Sci Technol Res Arch. 2024;7(1):61–72. doi:10.53771/ijstra.2024.7.1.0058. [Google Scholar] [CrossRef]
122. Jain A, Praveena K, Anandhi RJ, Kumar S, Alabdely H, Srivastava AP. Blockchain and machine learning for automated compliance in regulatory technology. In: 2024 IEEE 13th International Conference on Communication Systems and Network Technologies (CSNT); 2024 Apr 6–7; Jabalpur, India. p. 1–6. doi:10.1109/CSNT60213.2024.10546202. [Google Scholar] [CrossRef]
123. Sardana A, Sethuraman S, Kalyanasundaram PD. Compliance-as-code 2.0: orchestrating regulatory operations with agentic AI. J Artif Intell Gen Sci. 2024;5(1):546–63. doi:10.60087/jaigs.v5i1.366. [Google Scholar] [CrossRef]
124. Deshpande A. Regulatory compliance and AI: navigating the legal and regulatory challenges of AI in finance. In: 2024 International Conference on Knowledge Engineering and Communication Systems (ICKECS); 2024 Apr 18–19; Chikkaballapur, India. p. 1–5. doi:10.1109/ICKECS61492.2024.10616752. [Google Scholar] [CrossRef]
125. Sivakumar J. AI-driven cyber threat detection: enhancing security through intelligent engineering systems. J Inform Syst Eng Manage. 2025;10(19s):790–8. doi:10.52783/jisem.v10i19s.3116. [Google Scholar] [CrossRef]
126. Muthusamy R, Kannan C, Mani J, Govindharajan R, Ayyasamy K. Artificial intelligence-powered intelligent reflecting surface systems countering adversarial attacks in machine learning. Int J Reconfigurable Embed Syst IJRES. 2024;13(2):414. doi:10.11591/ijres.v13.i2.pp414-423. [Google Scholar] [CrossRef]
127. Hajlaoui R, Moulahi T, Zidi S, El Khediri S, Alaya B, Zeadally S. Towards smarter cyberthreats detection model for industrial Internet of Things (IIoT) 4.0. J Ind Inf Integr. 2024;39:100595. doi:10.1016/j.jii.2024.100595. [Google Scholar] [CrossRef]
128. Aslam A, Qureshi KN, Newe T. Future privacy and trust challenges for AIoT networks. In: Artificial intelligence of things (AIoT). Boca Raton, FL, USA: CRC Press; 2024. p. 198–216. doi:10.1201/9781003430018-14. [Google Scholar] [CrossRef]
129. Chi C, Yin Z, Liu Y, Chai S. A trusted cloud-edge decision architecture based on blockchain and MLP for AIoT. IEEE Internet Things J. 2024;11(1):201–16. doi:10.1109/JIOT.2023.3300845. [Google Scholar] [CrossRef]
130. Elkhodr M, Gide E, Darwish O, Al-Eidi S. BioChainReward: a secure and incentivised blockchain framework for biomedical data sharing. Int J Environ Res Public Health. 2023;20(19):6825. doi:10.3390/ijerph20196825. [Google Scholar] [PubMed] [CrossRef]
131. Duggineni S. Impact of controls on data integrity and information systems. Sci Technol. 2023;13(2):29–35. [Google Scholar]
132. Lee H, Park Y, Lee S, Chae Y. AIAS: ensuring application integrity through ethereum blockchain. IEEE Access. 2024;12:167990–9. doi:10.1109/ACCESS.2024.3480128. [Google Scholar] [CrossRef]
133. Siddika A, Zhao L. Enhancing trust and reliability in AI and ML: assessing blockchain’s potential to ensure data integrity and security. In: 2023 IEEE Intl Conf on Dependable, Autonomic and Secure Computing, Intl Conf on Pervasive Intelligence and Computing, Intl Conf on Cloud and Big Data Computing, Intl Conf on Cyber Science and Technology Congress (DASC/PiCom/CBDCom/CyberSciTech); 2023 Nov 14–17; Abu Dhabi, United Arab Emirates. p. 312–6. doi:10.1109/DASC/PiCom/CBDCom/Cy59711.2023.10361446. [Google Scholar] [CrossRef]
134. Ghosh S. Ensuring compliance integrity in AI ML cloud environments: the role of data guardianship. J Artif Intell Gen Sci. 2024;3(1):303–22. doi:10.60087/jaigs.v3i1.122. [Google Scholar] [CrossRef]
135. Bhumichai D, Smiliotopoulos C, Benton R, Kambourakis G, Damopoulos D. The convergence of artificial intelligence and blockchain: the state of play and the road ahead. Information. 2024;15(5):268. doi:10.3390/info15050268. [Google Scholar] [CrossRef]
136. Xu H, Seng KP, Ang LM, Smith J. Decentralized and distributed learning for AIoT: a comprehensive review, emerging challenges, and opportunities. IEEE Access. 2024;12:101016–52. doi:10.1109/ACCESS.2024.3422211. [Google Scholar] [CrossRef]
137. Wasif N. Smart contracts and AI: enhancing blockchain security against cyber attacks. 2022. doi:10.13140/RG.2.2.35564.88962. [Google Scholar] [CrossRef]
138. Samant PK, Pathak V, Ahmad W, Alabdultif A. A lightweight trusted framework for secure data exchange and threat mitigation in IoT-enabled healthcare environments. Sci Rep. 2025;15(1):39248. doi:10.1038/s41598-025-22797-3. [Google Scholar] [PubMed] [CrossRef]
139. Pandey VK, Sahu D, Prakash S, Rathore RS, Dixit P, Hunko I. A lightweight framework to secure IoT devices with limited resources in cloud environments. Sci Rep. 2025;15:26009. doi:10.1038/s41598-025-09885-0. [Google Scholar] [PubMed] [CrossRef]
140. Ahmad Umar HG, Yasmeen I, Aoun M, Mazhar T, Khan MA, Jaghdam IH, et al. Energy-efficient deep learning-based intrusion detection system for edge computing: a novel DNN-KDQ model. J Cloud Comput. 2025;14(1):32. doi:10.1186/s13677-025-00762-9. [Google Scholar] [CrossRef]
141. Murala DK, Prasada Rao KV, Vuyyuru VA, Assefa BG. A service-oriented microservice framework for differential privacy-based protection in industrial IoT smart applications. Sci Rep. 2025;15(1):29230. doi:10.1038/s41598-025-15077-7. [Google Scholar] [PubMed] [CrossRef]
142. Almuseelem W. Energy-efficient and security-aware task offloading for multi-tier edge-cloud computing systems. IEEE Access. 2023;11:66428–39. doi:10.1109/ACCESS.2023.3290139. [Google Scholar] [CrossRef]
143. Villegas-Ch W, Govea J, Gutierrez R, Mera-Navarrete A. Optimizing security in IoT ecosystems using hybrid artificial intelligence and blockchain models: a scalable and efficient approach for threat detection. IEEE Access. 2025;13:16933–58. doi:10.1109/ACCESS.2025.3532800. [Google Scholar] [CrossRef]
144. Sonavane SM, Prashantha GR, Nikam PD, AVR M, Chauhan J, Sountharrajan S, et al. Optimizing QoS and security in agriculture IoT deployments: a bioinspired Q-learning model with customized shards. Heliyon. 2024;10(2):e24224. doi:10.1016/j.heliyon.2024.e24224. [Google Scholar] [PubMed] [CrossRef]
145. Baniata H, Anaqreh A, Kertesz A. Distributed scalability tuning for evolutionary sharding optimization with Random-equivalent security in permissionless Blockchain. Internet Things. 2023;24:100955. doi:10.1016/j.iot.2023.100955. [Google Scholar] [CrossRef]
146. Gill SS, Golec M, Hu J, Xu M, Du J, Wu H, et al. Edge AI: a taxonomy, systematic review and future directions. Clust Comput. 2024;28(1):18. doi:10.1007/s10586-024-04686-y. [Google Scholar] [CrossRef]
147. Pournazari J, Ullah A, Al-Dubai A, Liu X. Computation offloading in the edge-to-cloud compute continuum: a survey of federated architectural solutions. Clust Comput. 2025;28(13):839. doi:10.1007/s10586-025-05577-6. [Google Scholar] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF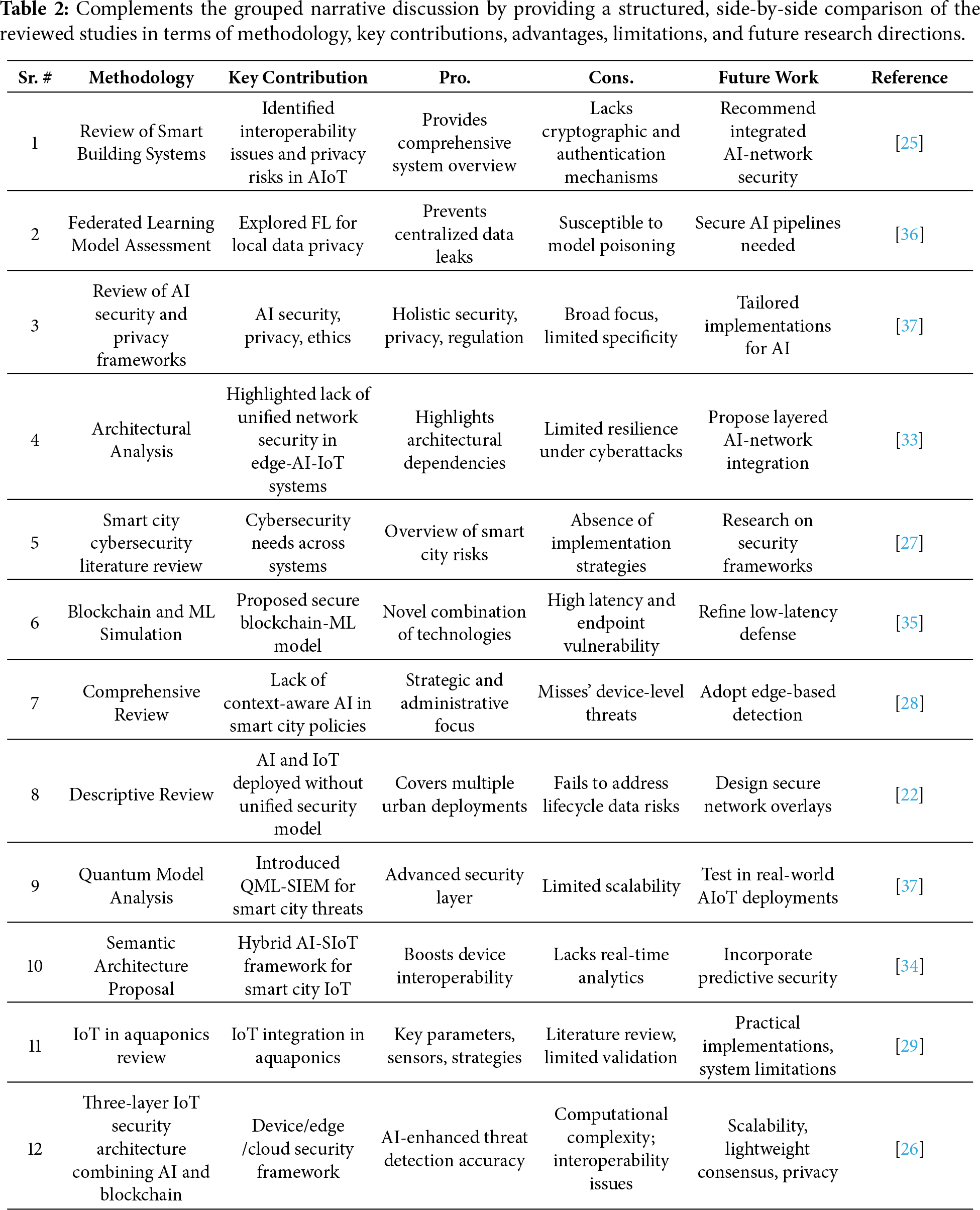
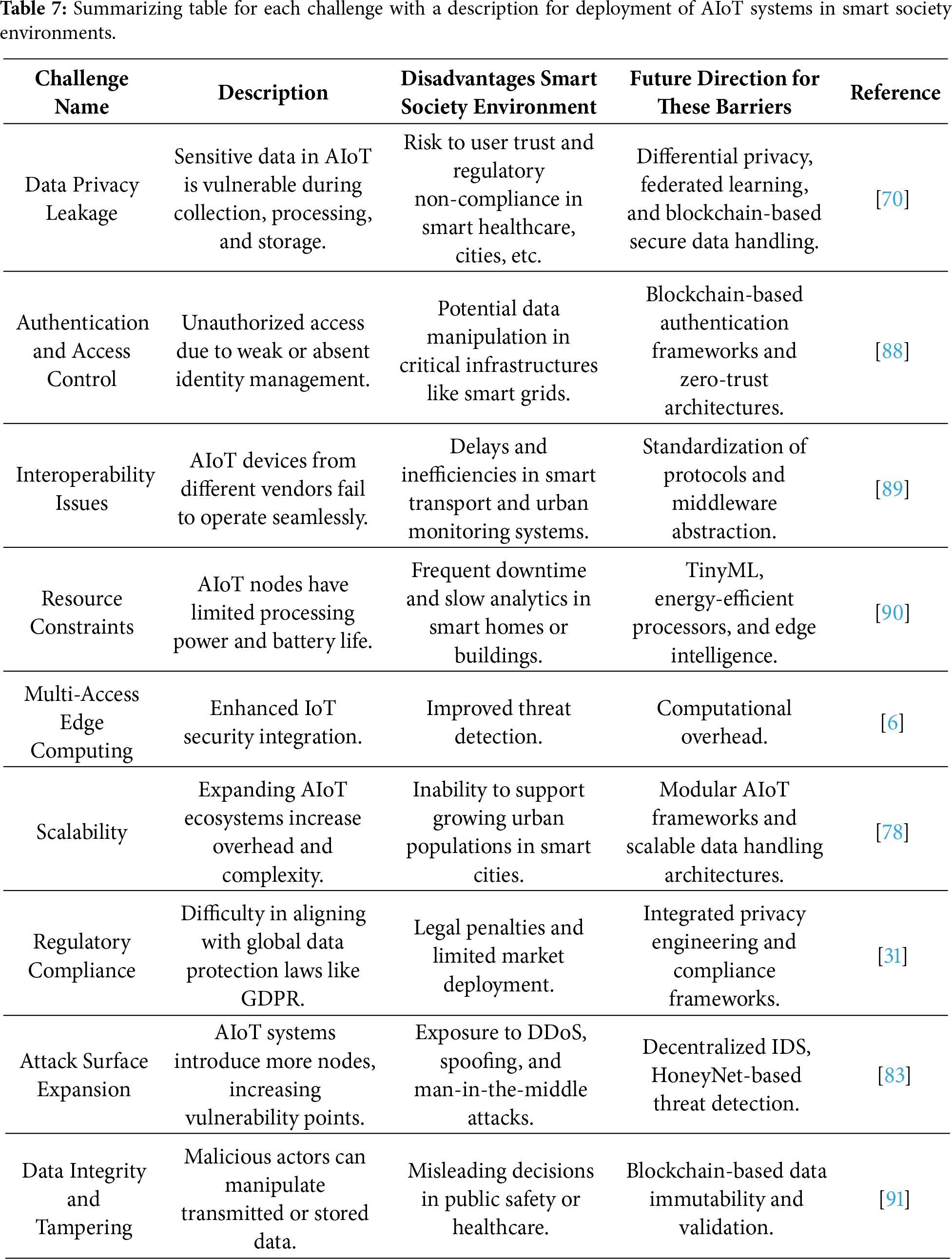
 Downloads
Downloads
 Citation Tools
Citation Tools