 Open Access
Open Access
REVIEW
Federated Deep Learning in Intelligent Urban Ecosystems: A Systematic Review of Advancements and Applications in Smart Cities, Homes, Buildings, and Healthcare Systems
1 Department of Computer Science, COMSATS University Islamabad, Sahiwal Campus, Sahiwal, Pakistan
2 School of Computer Science, National College of Business Administration and Economics, Lahore, Pakistan
3 Department of Computer Science and Information Technology, School Education Department, Government of Punjab, Layyah, Pakistan
4 Department of Computer Engineering, COMSATS University Islamabad, Sahiwal Campus, Sahiwal, Pakistan
5 Department of Computer Science, Alshifa Institute of Health Sciences, Narowal, Pakistan
6 Department of Electrical and Electronic Engineering Science, University of Johannesburg, Auckland Park, Johannesburg, South Africa
7 Department of Software, Faculty of Artificial Intelligence and Software, Gachon University, Seongnam-Si, Republic of Korea
8 Faculty of Engineering, Université de Moncton, Moncton, NB, Canada
9 School of Electrical Engineering, University of Johannesburg, Johannesburg, South Africa
10 International Institute of Technology and Management (IITG), Av. Grandes Ecoles, Libreville, Gabon
11 Bridges for Academic Excellence—Spectrum, Tunis, Tunisia
* Corresponding Author: Muhammad Adnan Khan. Email:
Computer Modeling in Engineering & Sciences 2026, 146(3), 8 https://doi.org/10.32604/cmes.2026.078672
Received 06 January 2026; Accepted 02 March 2026; Issue published 30 March 2026
Abstract
The contemporary smart cities, smart homes, smart buildings, and smart health care systems are the results of the explosive growth of Internet of Things (IoT) devices and deep learning. Yet the centralized training paradigms have fundamental issues in data privacy, regulatory compliance, and ownership silo alongside the scaled limitations of the real-life application. The concept of Federated Deep Learning (FDL) is a privacy-by-design method that will enable the distributed training of machine learning models among distributed clients without sharing raw data and is suitable in heterogeneous urban settings. It is an overview of the privacy-preserving developments in FDL as of 2018–2025 with a narrow scope on its usage in smart cities (traffic prediction, environmental monitoring, energy grids), smart homes/buildings/IoT (non-intrusive load monitoring, HVAC optimization, anomaly detection) and the healthcare application (medical imaging, Electronic Health Records (EHR) analysis, remote monitoring). It gives coherent taxonomy, domain pipelines, comparative analyses of privacy mechanisms (differential privacy, secure aggregation, Homomorphic Encryption (HE), Trusted Execution Environments (TEEs), blockchain enhanced and hybrids), system structures, security/robustness defense, deployment/Machine Learning Operation (MLOps) issues, and the longstanding challenges (non-IID heterogeneity, communication efficiency, fairness, and sustainability). Some of the contributions made are structured comparisons of privacy threats, practical design advice on urban areas, recognition of open problems, and a research roadmap into the future up to 2035. The paper brings out the transformational worth of FDL in building credible, scalable, and sustainable intelligent urban ecosystems and the need to do further interdisciplinary research in standardization, real-world testbeds, and ethical governance.Keywords
Supplementary Material
Supplementary Material FileThe concept of smart city ecosystems integrates urban infrastructure, homes, businesses, and health plans within a data-driven framework powered by the Internet of Things (IoT) and Artificial Intelligence of Things (AIoT). This framework enhances real-time optimization across urban environments through diverse data streams, including traffic and air quality monitoring, energy efficiency via smart devices, and health tracking with wearables and Electronic Health Records (EHR). Data is processed through advanced neural network models to enable applications like predictive traffic management and energy forecasting. Developments projected for 2018–2025 highlight AIoT’s pivotal role in fostering sustainable urban growth, with estimates suggesting IoT connections will surpass 38 billion by 2030 [1], paving the way for smarter, more environmentally conscious cities using digital twins and predictive analytics.
1.1 Intelligent Urban Ecosystems and Deep Neural Intelligence
Smart city ecosystems combining urban infrastructure, residential homes, business buildings, and medical institutions, form an interconnected network of IoT-based urban intelligence, fueled by neural networks [2–4]. Such ecosystems are based on various streams of data collected by traffic sensors, air quality cameras, smart meters, surveillance cameras, wearables, Building Management System (BMS), and EHR/medical imaging to allow real-time optimization and sustainability [5]. Deep learning (DL) models, such as Graph Neural Network (GNN), transformers, and Convolutional Neural Network (CNN), are used to process this heterogeneous data to be used in traffic prediction, energy management, anomaly detection, and predictive healthcare [6,7]. The recent progress illustrates AIoT and DL to create smarter cities, with the number of IoT connections projected to surpass 30 billion by 2030, thus leading to the creation of smart cities that are environmentally friendly [8]. The worldwide market for IoT solutions has observed an annual growth rate of 20% CAGR, and IoT is expected to play a crucial role with significant cash flow in the upcoming years [9]. Fig. 1 provides a complex view of the general architecture of Federated Deep Learning (FDL) in the context of urban ecology, the main building blocks and the interdependence among them.
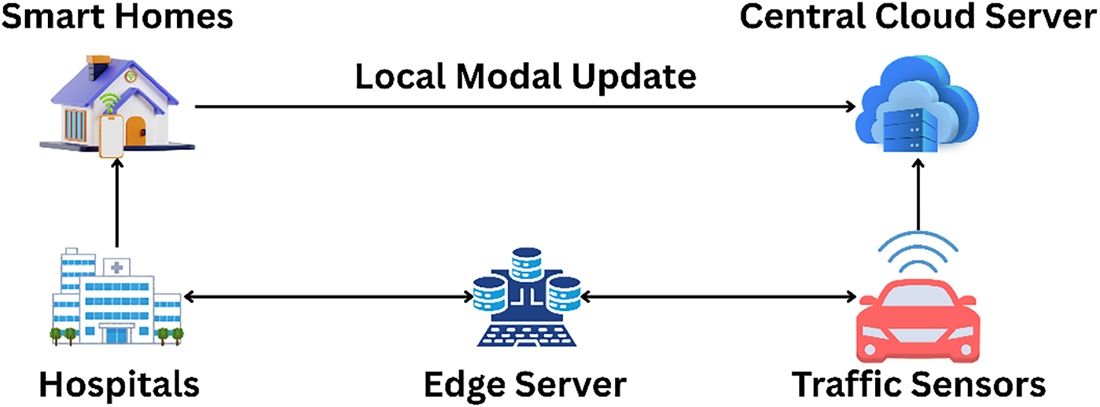
Figure 1: High-level architecture of FDL in urban ecosystems.
Fig. 1 illustrates Intelligent urban ecosystems combine urban infrastructure, cities, buildings, and healthcare into an interconnected urban intelligence fabric that is designed to act in real-time, optimize sustainably, efficiently, and resiliently through the use of multimodal data, comprising traffic and air quality sensors, Smart meters, BMS, and surveillance cameras, wearable devices, and EHR powered by medical imaging, such as predictive mobility management, energy-efficient building operations, anomaly detection, and personalized healthcare.
Over the past few decades, the urban population has been growing at a greater rate than ever before. The United Nations (2007) indicated that urban populations had already overtaken the rural populations in 2007 [10]. According to World Bank, 53.7% of the world population will be living in urban centers by 2020 [11]. The governments and local authorities of both the developed and developing countries distribute disproportionately more resources and funds to the urban areas, contributing to the urban growth at a faster rate. Although urbanization has created many income-generating resources, it is also accompanied by numerous challenges such as overpopulation, unemployment, lack of housing, urban congestion, shortage of water, poor urban planning, health risks, and environmental degradation, among other problems [12].
The sensors and IoT devices continuously scan and record data on vehicular traffic, garbage disposal, water and drainage systems, potholes, smart buildings, smart grids, burglary, environmental measurements, and future 6G networks in the smart cities setting [13]. Predictive models are determined by discovering latent patterns in these datasets through big-data analytics, Machine Learning (ML), and DL algorithms. These prognostications help the municipal administrators and urban planners to improve the quality of life of the residents [14,15].
Smart city applications, such as traffic predictions, smart industrial procedures, monitoring the environment, and disaster management, require immediate decision-making. With the use of ubiquitous and pervasive computing infrastructures, updates should always be accessible all over the world. Nevertheless, cloud storage can slow down analytics pipelines due to its latency [16–18]. At the same time, smart cities produce enormous amounts of data on a high-speed basis due to IoT gadgets and sensors [19]. Such big data has threats to its management, such as the loss of data, heavy-duty computation demands, data connection, and high-energy usage [20].
1.2 Federated Deep Learning (FDL): Motivation and Advantages
FDL provides an effective solution to the intrinsic drawbacks of the standard distributed training, as it allows collaborative optimization of geographically remote devices, such as edge nodes, IoT sensors, and institutional servers, without transmitting raw data. The fact that it only aggregates incremental model updates [21,22] allows it to maintain the privacy of information but leverages the non-IID heterogeneity of myriad urban data streams to improve scalability and reduce exposure risks [23,24]. Even though this does not provide a foolproof guarantee of privacy, FDL has been built using Differential Privacy (DP), reducing measures to reduce the vulnerability to inference attacks [25,26]. FL provides an opportunity to train machine learning models in a decentralized manner on edge devices that are decentralized, potentially solving the major issues of privacy, communication, and regulation in smart city settings [27].
Federated Learning (FL) is a relatively new paradigm in machine learning, a decentralization of the training procedure, where the core functional operation is not executed in a central system. Instead, it is executed in the unstable space of edge devices, instead of transferring raw data to a single cloud backend [28]. In this model, local device parameters are sent to a central orchestrator that breaks them down to a global model that, in turn, influences predictions throughout the network [29]. In contrast to the more traditional cloud-based models, which consolidate information in one place, FL relocates trained models to nodes, or the origin of the data, which alleviates privacy issues and datasets that are both enormous and difficult to process in real time that plague smart-city implementations, and makes decision-making virtually real-time [30]. The latter, therefore, avoids the need to upload personal information onto the cloud or to share it with other researchers, thus protecting sensitive information even in situations where many data scientists will follow similar training paradigms.
Due to its importance, much academic attention has been devoted to FL. Recent systematic reviews [31,32] have identified its uses in the Internet-of-Things space, whereas researchers [33] have focused on customized FL strategies for particular classes of clients. Other studies [34] have surveyed the design space, challenges and problem-solving techniques of FL, but a general overview of privacy-preserving strategies in FL [35] has been brought into the limelight. Explicit domains compendia, too, have become: a FL survey with a mobile-edge focus [36] and a close-up view of privacy preservation [37] have been released. Additional applications of FL include methodological schemes of smart-city sensing [38] and wireless networks using UAVs [39]. Specific surveys on healthcare applications [40], digital-twin applications in smart cities [41], and model-digital-twin interactions in smart-city settings highlight that it is multidisciplinary. The authors [42] evaluate recent developments and cross-sector applications, and the contemporary research is still exploring how they can be used in a smart-city environment.
The scope of review was the IoT, transportation, communication, and healthcare fields. Platforms of FL systems, mechanisms of operation, field deployments, as well as operational environments, are carefully documented in [43]. In [44], the authors explore blockchain-based FL applications to secure IoT devices, and they first explain the enabling technologies and then demonstrate how FL can be used to achieve improved security based on the enabling technologies. Later literature [45] emphasizes the usefulness of using a combination of FL and blockchain to secure smart-transport infrastructure. The survey discusses FL-driven real-world implementations augmented with blockchain after an examination of Vehicular Ad Hoc Network (VANET) and Smart Transport Infrastructure (STI) frameworks. This review was done explicitly since the previous surveys have primarily overlooked FL applications that are specific to smart-city conditions, despite the scope of FL studies in other verticals.
Centralized deep learning requires the concentration of vast amounts of data, which is a habit that triggers acute privacy concerns, considering the regulatory frameworks like General Data Protection Regulation (GDPR) and Health Insurance Portability and Accountability Act (HIPAA) that categorically prohibit the free flow of data across organizational borders [46–48]. These issues are further complicated by the presence of the concomitant barricades to data ownership, inter-organizational tension, and the very vulnerability of such a single point of failure, particularly when it comes to such a sensitive kind of data types as EHR and urban surveillance video footage [49,50]. In Fig. 2, we outline the taxonomy of FL and organize its dispersed models, methodological frameworks, and practical applications in a systematic way, in a larger context.
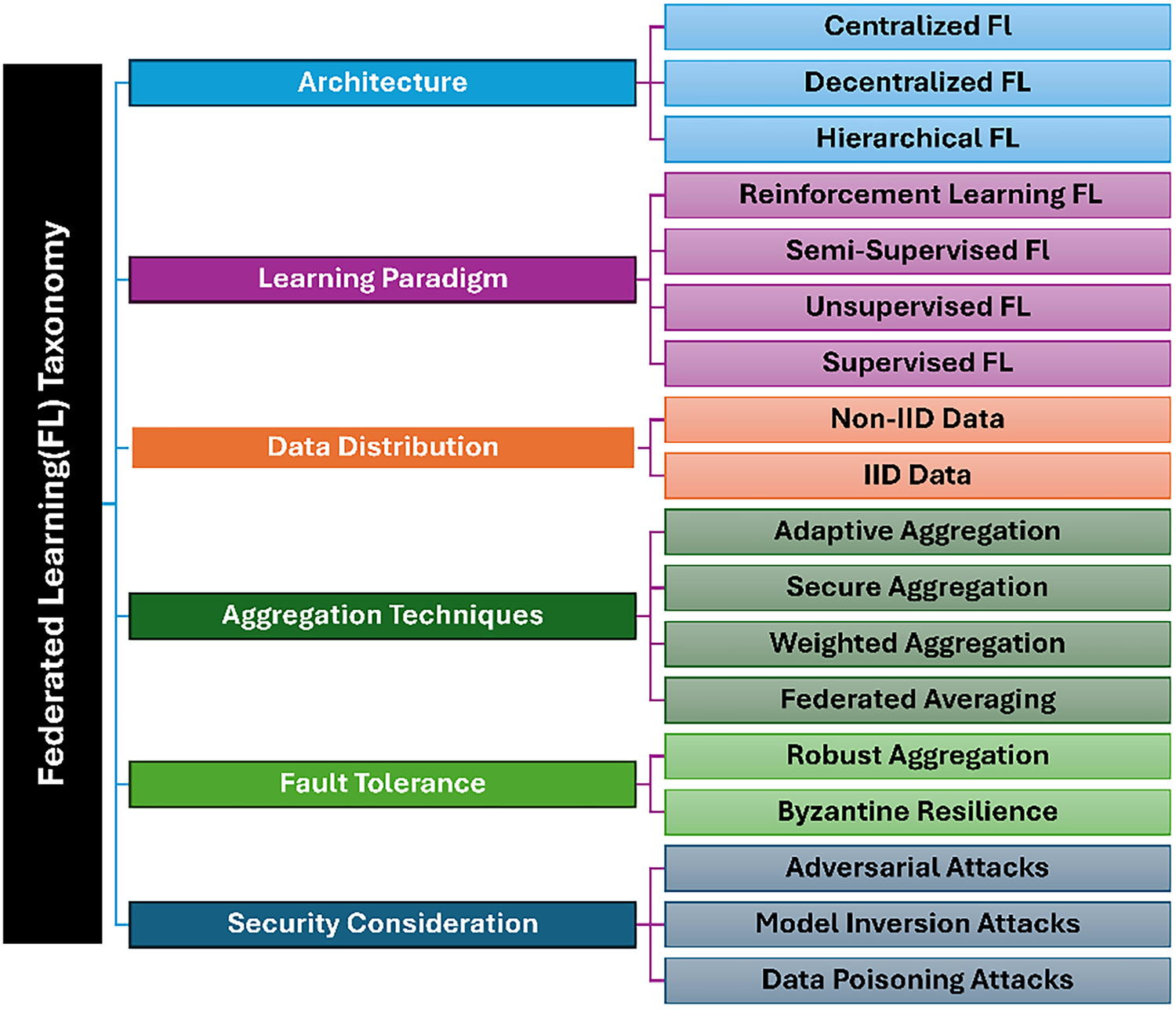
Figure 2: Federated learning taxonomy [51].
1.3 Scope, Review Questions, and Contributions
The proposed present research suggests a systematic review of the FDL innovations published between 2018–2025, especially focusing on the privacy-sensitive mechanisms and their implementation in intelligent urban ecosystems. These ecosystems will consist of smart cities that are optimized in terms of traffic flow and environmental monitoring, smart homes and buildings with IoT sensors that control energy usage and detect anomalies, and healthcare infrastructures that can protect medical imaging and allow patients to be monitored remotely. The review will question fundamental issues like data heterogeneity, security threats, and deployment limitations that are inherent to the domains, and thus, will not consider non-urban or non-privacy-oriented versions of FL, and hence, provide an exclusive analysis of sustainable, collaborative AI solutions tailored to fit into the context of modern city environments.
Following this extent, the literature analysis will respond to the following research questions, related to the newly emerged themes in recent research. Answering these questions will shed light on the nexus between privacy, scalability, and security, which will provide a roadmap on where future researchers and practitioners can move on sustainable urban AI systems.
• RQ1: Which privacy-preserving methods (DP, Secure Aggregation (SecAgg), HE, hybrids) are most effective for FDL in urban domains, and what are their privacy-utility trade-offs?
• RQ 2: Which FDL algorithms (FedAvg, FedProx, SCAFFOLD variants) best handle non-IID heterogeneity and concept drift in urban ecosystems?
• RQ 3: What are the primary deployment challenges (communication, energy, heterogeneity, compliance) in urban FDL and their current mitigations?
• RQ 4: What are the key open challenges (scalability, adversarial robustness, fairness) in urban FDL and research directions through 2035?
The remainder of this review is organized as follows: Section 2 outlines the review methodology used in this work and presents a coherent taxonomy of the FDL across urban ecosystems. Section 3 expounds upon fundamental concepts of FDL, its transition from the conventional centralized deep learning, core algorithms, their interaction with deep models and salient variants. Section 4 provides a survey of system architectures and deployment paradigms, focusing especially on the edge–fog–cloud continuum, federation topologies, methods to promote efficiency, and unique constraints that urban settings impose. Section 5 examines privacy-preserving schemes, threat models and multilayered defense strategies. Section 6 presents domain specific applications in smart cities, healthcare and smart homes/buildings/IoT. Section 7 addresses issues of security, robustness, and trustworthiness beyond pure privacy issues. Section 8 discusses ongoing challenges and open research issues. Section 9 describes application domains involving full-fledged pipelines and evaluation studies. Section 10 goes into greater detail regarding the discussion of limitations and suggests remedies. Finally, summarizes the review, noting some of the key insights and suggesting some of the prospective research directions.
2 Review Methodology and Taxonomy
This review adopts a systematic review method to add up the state-of-the-art in FDL in intelligent urban ecosystems to include a complete coverage of privacy-preserving developments and domain-specific applications without compromising the rigor and reproducibility. Fig. 3 shows the proposed methodology.
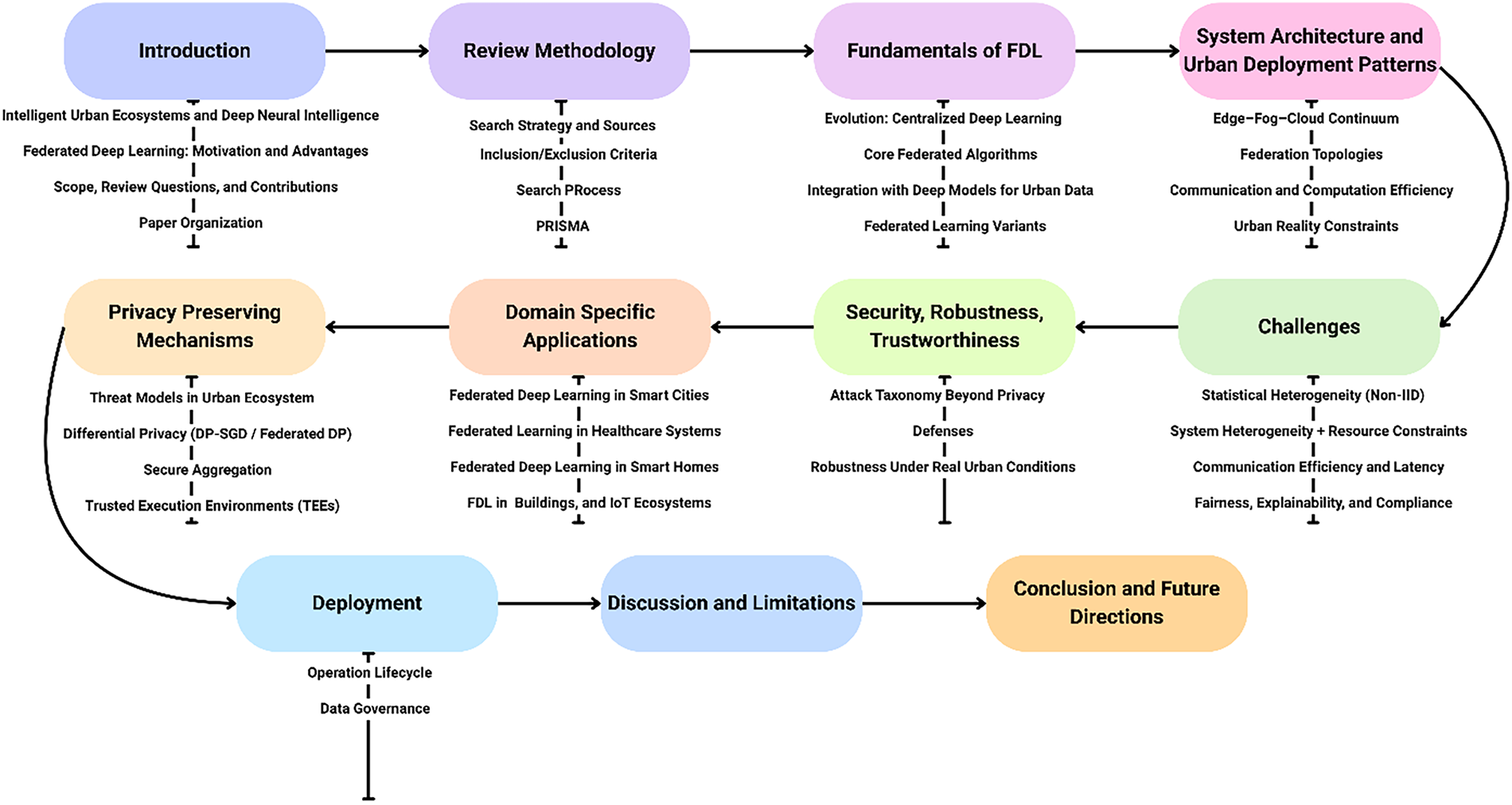
Figure 3: Proposed research methodology.
2.1 Search Strategy and Sources
The search of literature was carried out in the most topical academic databases and repositories in computer science, IoT, and biomedical: IEEE Xplore, ACM Digital Library, SpringerLink, ScienceDirect, and PubMed (respective to the FDL related to healthcare). The search queries were based on core terms (federated deep learning OR federated learning) and domain-specific terms (smart city OR smart cities, smart home OR smart building OR smart buildings) and privacy/security terms (differential privacy, secure aggregation, Homomorphic Encryption (HE), trusted execution environment, blockchain). Results were refined with the help of using Boolean operators (AND/OR) and phrase searches. The main time window was 2018–2025 to support the development of mature FDL over the past years and place a special emphasis on the high-impact works published 2019–2025 that would reflect the hybrid approaches, urban implementations, and sustainability emphasis.
2.2 Inclusion/Exclusion Criteria
To make sure that the review included the literature that is the most relevant, inclusion and exclusion criteria were formulated. The inclusion criteria were based on the key inclusion criteria of having a study that specifically discussed FL or FDL and had privacy or security considerations. The research should have been directly related to urban ecosystems with a specific focus on smart cities, smart buildings/homes, IoT and healthcare. Only empirical studies, verified works, and surveys which described real-life uses of FDL and privacy-saving measures were taken into consideration. Research papers where no information was found in the methodology section or research where no quantitative studies were conducted were filtered out, and so were those studies where no numbers or simulation and real data were tested. Also, low-quality and gray literature peer-reviewed preprints were not considered. Such a selective method resulted in the identification of 173 sources of interest, and they were high quality and straight to the point.
Several privacy-preserving methods and FL algorithms mentioned in the literature were compared to identify the differences and similarities between them. This discussion was related to the efficiency of various privacy measures, especially in cities, where information is usually heterogeneous and confidential. It further compared the performance of different FL algorithms such as FedAvg, FedProx, FedNova, and SCAFFOLD relative to the ability to deal with non-IID data, efficiency in communication, scalability and preservation of privacy. This was permitting us to get to know better the advantages and disadvantages of each strategy, showing the most promising solutions to be applied in the real world in smart cities, medical, and IoT contexts. To illustrate the comparative performance and applicability of each technique, the results of this analysis were presented in shape of tables and figures.
Fig. 4 represents the flowchart in the selection of a systematic review, showing the strict phases that will be applied to the selection of studies that will be included, screened, and chosen. PRISMA checklists are available in the supplementary materials. It started with the search phase during which the records were collected through a number of databases such as Elsevier, IEEE, SN, Wiley, and MDPI. 889 records were identified. After this, during the identification phase, 162 records were filtered out because of duplicates, irrelevant topics and other factors that rendered them inappropriate to be reviewed further. This left 727 records to the second stage.
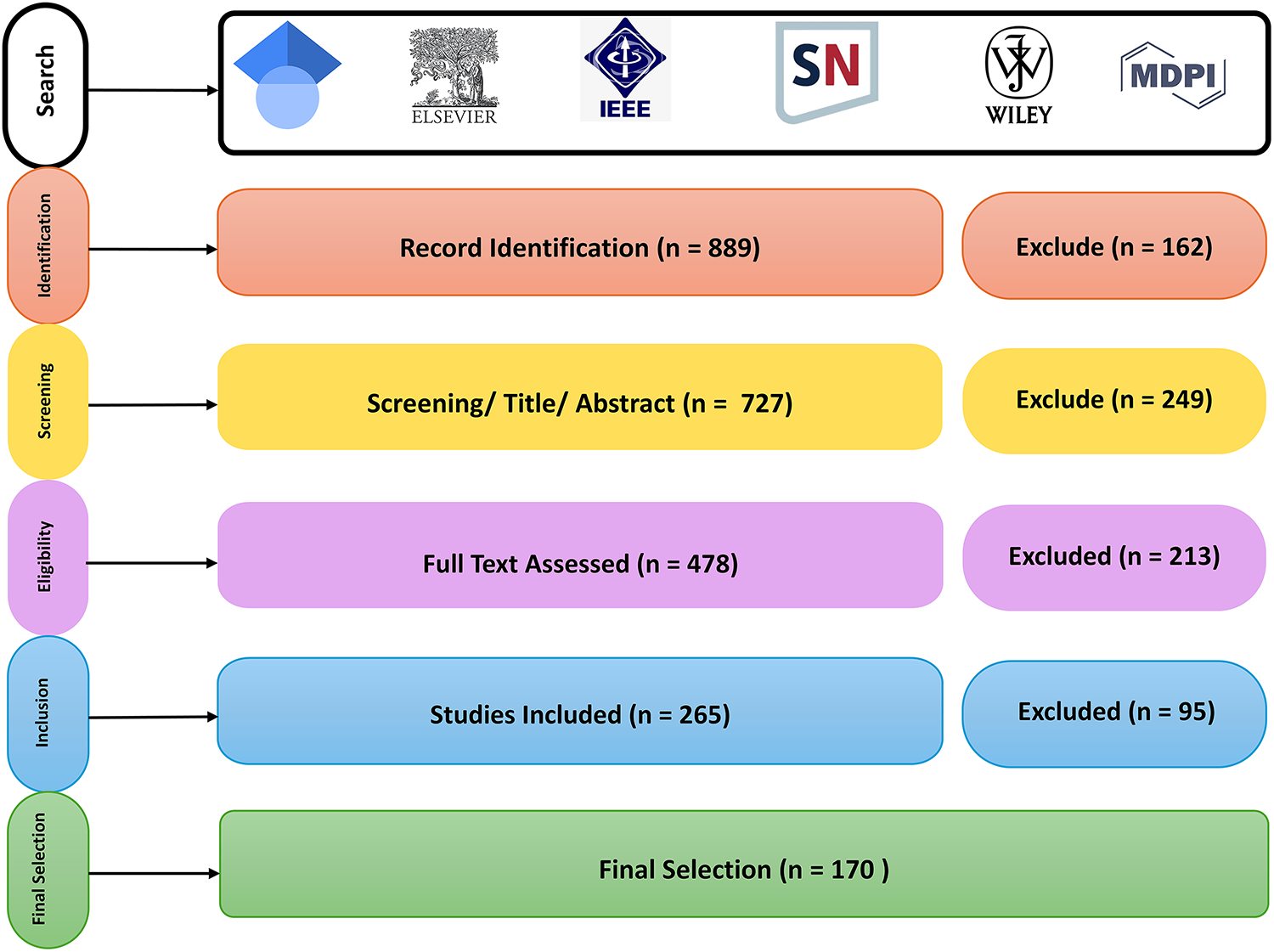
Figure 4: PRISMA-style study selection flow.
During the screening phase, the title and abstract of the 727 records have been thoroughly examined to determine their relevancy of the topic of the research. In the process, 249 records were filtered on the grounds that they failed to satisfy the inclusion criteria, including off-topic, receiving less than enough data, and having poor methodological quality. The number of records post this exclusion was 478 records, which proceeded to the eligibility stage to undergo a more detailed analysis.
During the eligibility phase the entire contents of each of the 478 records were evaluated to decide whether they fitted the particular eligibility inclusion criteria to be included in the systematic review or meta-analysis. This was the stage that entailed the verification of such aspects as study design, sample size, methodology, and data quality. Consequently, 213 records were discarded because they did not fulfill these criteria, including possessing a wrong study design, missing the right data, or not being consistent with the objectives of the research. This came down to 265 studies that met the eligibility test.
Next, the inclusion phase was followed during which the rest of the 265 studies were detected to be included in the analysis. The same level of scrutiny was carried out in this stage to determine whether each study had all the required standards and whether the findings were in tandem with the requirements of the research. In this step, however, 94 studies were eliminated because of one reason or another, including incomplete data, poor methodology, or some other reason, which rendered them inappropriate to include them in the final analysis. Following this exclusion, 170 studies were included in the analysis final result.
Finally, the figure presents a detailed, step-by-step approach of selection of a study, starting with a huge collection of 889 records, it was reduced to 170 studies that had to fit the inclusion criteria. Such a systematic and transparent method ensures that only the most important and rigorous studies are incorporated in systematic review or meta-analysis, and they are a credible source of conclusions or even recommendations.
One of the most important factors of the methodology was the creation of a taxonomy to thoroughly organize the numerous studies and contributions in the area of FDL. The taxonomy was about privacy-preserving systems, including differential privacy, SecAgg, HE, trusted execution environment, and blockchain. It also classified the various FL models and their performance, including FedAvg, FedProx, FedNova, and SCAFFOLD, especially in solving such issues as non-IID data and concept drift. The domain-specific applications such as smart cities, healthcare, and smart homes/buildings were also plotted in the taxonomy to determine how the models and privacy mechanisms can be used in real-world urban ecosystems. This hierarchical classification assisted in the realization of the variety of methods and their implementation into privacy-containing, scaled, and effective systems in cities.
2.5 Data Extraction and Categorization
Once all the relevant studies had been collected, the next thing to do was to extract the data, which involved the extraction of important data in each study. It entailed determining the privacy assumptions, system architecture, purpose of tasks like traffic prediction, medical imaging, or EHR analysis, aggregation procedures employed, and performance trade-offs such that privacy vs. model utility. Also models and datasets were extracted in the studies to understand the foundation of experiments and what type of data was applied in such urban applications. The papers were then divided according to their privacy schemes, FL schemes and their fields of application. This categorization enabled a profound comparative study of the various strategies and their strengths and weaknesses in the use of the strategies in various urban contexts.
A strict quality appraisal was carried out to make sure that the quality and relevance of reviews and articles incorporated were of high quality. The relevance of each paper to the research questions was evaluated based on the criteria of whether the study concerned FDL regarding urban ecosystems, and its privacy-saving mechanisms. Methodological rigor of the study was evaluated to make sure that the experiments and simulations were well validated and reproducible. Research studies which were more pertinent to the research questions and employed high and validated methods were selected to be further analyzed. The scope of application also counted—the former was given preference to studies which had practical, real-world use cases of FDL in urban settings as opposed to those with theoretical models. The issues of privacy and security were under scrutiny in such a way that the mechanisms that were suggested turned out to be realistic and applicable to privacy-sensitive urban systems.
3 Fundamentals of Federated Deep Learning (FDL)
The paradigm shift in the field of distributed machine learning is FDL. It allows the joint training of deep neural networks on the devices which are distributed in a decentralized manner and strictly protects the privacy of the data, as defined in references. Proposed study discusses here the principles underlying FDL, the development of FDL as a continuation of traditional centralized paradigms, the foundational algorithms of the model, the application to urban data and variations of the model.
3.1 Evolution: Centralized Deep Learning (CDL) → FL → Federated Deep Learning (FDL)
FL [28] is a decentralized machine learning model that can be used to train collaborative models using distributed clients such that peripheral servers, IoT devices without sharing data. The exchange of model updates only occurs with a central aggregator. The FDL is a particular extension of FL that trains deep learning models, such as CNNs, GNNs, Long Short-Term Memory (LSTMs), and Transformers, in complex and high dimensional urban data modalities including time-series traffic flows, surveillance imagery and medical imaging.
This evolutionary change of Centralized Deep Learning (CDL) to FL and then FDL [52–59] is intended to solve the increasing privacy, scalability and data distribution challenges of real-world deployments. CDL concentrates all the data within powerful servers to ensure effective optimization, however, this subjects sensitive data to breaches of regulations and intrusions (GDPR, HIPAA). FL moves training to periphery devices, which increases privacy with encrypted local updates and overcomes latency in massive IoT streams. The FDL generalizes deep models like Transformers with millions of weights, minimizing gradient divergence and non-IID biases in heterogeneous urban ecosystems, such as cross-city traffic or multi-hospital EHRs.
The shift towards centralized deep learning to FL and ultimately to FDL, is necessitated by the need to address privacy, scalability, and data distribution issues that are presented in real-life deployments [52,53]. To address weaknesses of Centralized Federated Learning (CFL) for example high latency, system failures, and trust issues, decentralized Federated Learning (DFL) arose to facilitate decentralized aggregation of models [54]. In centrally trained regime, all the information is centralized to one server that is easy to optimize but at the same time sensitive information is exposed to attacks and legal violations. FL also provides increased privacy and security whereby clients can train local sub models and transmit encrypted updates to a central server where aggregation into a global model is done [55]. Another solution to the issue of centralized training of AI models is FL, which combats the lack of efficiency and privacy concerns, but is susceptible to attackers who can access data privacy and system resilience [56].
This is worsened by the large parameter spaces of modern deep models, such as the millions of weights in Transformers which increase communication overhead in the process of communicating model updates in FL [57]. Moreover, distributed FL can be unstable because of gradient divergence, and data across heterogeneous devices are non-IID, will cause model bias. As an example, the urban data is variable across cities (traffic models) and household (health indicators) [58]. This evolutionary trend highlights a more general trend of credible, distributed artificial intelligence, and recent surveys in 2024–2025 show the ability of FDL to conduct heterogeneous urban data in an effective manner. In Table 1, a comparative analysis between.
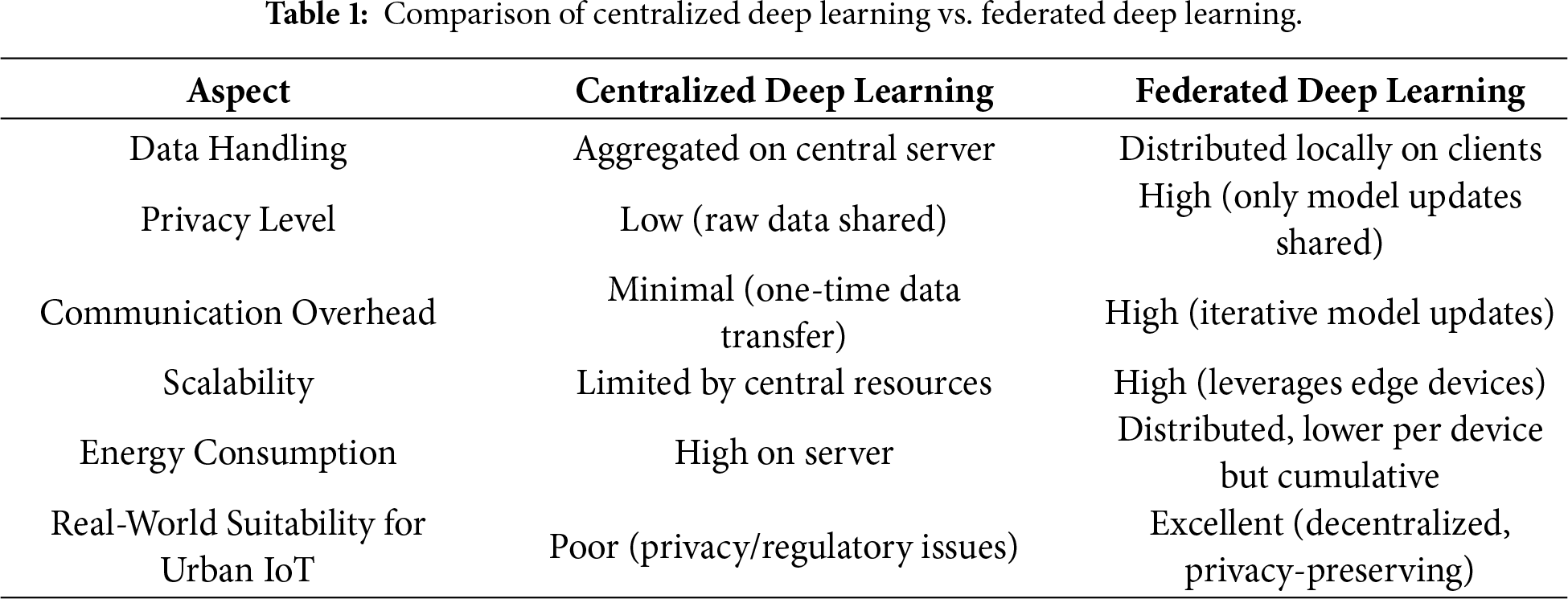
CDL and FDL is presented, outlining the respective differences between the two with regards to dimensions such as data processing paradigms, privacy considerations, model training methodologies and computational resource requisites.
Table 1 is clear and concise on the comparison between CDL and FDL, which shows the basic differences between the two in terms of data handling and functioning in real world urban IoT settings. In CDL, all information is gathered and concentrated on a single central host to train, provides no communication cost (just one-time transfer of raw information), and high computing capabilities when using powerful servers, however, it enables poor privacy because of raw data sharing, meaning it can be easily violated and not aligned with laws such as GDPR or HIPAA. This method has the disadvantage of low scalability, which is based on centralized resources and high-power consumption of the server. Conversely, FDL stores information locally on a smart sensor at home, a hospital device or on the camera on a traffic light and sends model updates only to a central or edge server to be aggregated. It allows very high privacy, as it never reveals raw data, high scalability, as it takes advantage of the power of many edge devices, and is more adaptable to urban IoT applications where the centrality of devices and regulatory oversight matter. The key trade-offs of FDL are reduced communication overhead due to the iterative updates and device-cumulative energy consumption, which are being alleviated by compression, scarification, and energy-sensitive methods. In general, centralized learning is still effective in regulated environments, but FDL is much more effective in respect of privacy-intensive distributed urban applications.
The fundamental methods of FDL are focused on the effective consolidation of models in the distributed environment. The basic methodology Federated Averaging (FedAvg) performs the training of local models at client devices and then aggregates them at a central location. Decentralized Federated Averaging with momentum (DFedAvgM) lowers the communication expense and enhances convergence rate by having clients communicate only with their neighbors overcoming the weaknesses of centralized FedAvg [59]. The new rule which is complementary in Eq. (1):
where
This is a strategy applied to reduce statistical heterogeneity. It presents terminologies that smooth out every local training loss and is based on FedAvg [60]. This model is also in control of the local model and deviation. Re-parameterization makes minor modification but is an improved version of FedAvg. It is significant to both theoretical and practical spheres. With regards to practical field, strong convergence is exhibited over FedAvg [61].
FedProx extends FedAvg by adding a proximal term [62] to handle heterogeneity is represented in Eq. (2):
where
FedNova normalizes updates to mitigate inconsistent local iterations [57], using Eq. (3):
where
A FL-Stochastic Controlled Averaging can also be referred to as Scaffold. The training process is synchronized among various nodes within the network as anticipated. This method minimizes numerous communication processes and eliminates the problem of heterogeneity [63]. SCAFFOLD employs control variants to reduce variance using Eq. (4):
The methodology of dealing with drift in volatile environments like mobile urban devices [64] is worth paying attention to. Use FedAvg in the baseline efficiency, FedProx or FedNova to reduce the effects of non-IID data and stragglers, and resort to SCAFFOLD when high variance is faced.
Gao et al. [65] analyzed not just FL models trained using well-known strategies like FedAvg, FedProx, and Scaffold, but also a model trained using the FedDC strategy they suggested. Since heterogeneous datasets necessitate a more convergent model, the effects of these approaches were investigated. The FedAvg method achieved the target accuracy with the highest degree of round numbers, according to the trials conducted using different datasets. Training was completed faster than FedAvg in some cases, even if more or almost the same number of rounds were gathered using FedProx. Although the accuracy rate was consistent across all methods, Scaffold’s training rate was lower and faster than both. The FedDC approach, which combines elements of the FedProx and Scaffold frameworks, outperformed its competitors on both IID and non-IID datasets. Final results showed that FedDC is effective with both full and partial client engagement; therefore, it must be powerful [65].
Nguyen et al. [66] used the CIFAR-10 dataset in their analysis, which included techniques like FedAdam, Scaffold, FedNova, FedAdagrad, FedYogi, and FedAvg in combination with one another. The collected test accuracy graph showed that the ProxYogi method, a hybrid of FedProx and FedYogi, had the best results [66]. Additionally, non-IID data were used in this investigation.
Another study applied medical data training to forecast in-hospital mortality and acute renal injury using FedAvg, FedAdam, FedYogi, FedAdagrad, FedProx, and FedAvgM. According to the findings, the training that included FedProx yielded the least accurate predictions of acute renal injury occurrence. Except for FedAdam, nearly all of them got training results on hospital mortality prediction that were extremely accurate. In addition, they highlighted that the IID datasets are good for using the simplest FL algorithms, FedAvg and FedAvgM, for machine learning tasks [67]. Table 2 lists some of the key FDL algorithms, of which it specifies salient features, domain-specific applications, and comparative performance metrics in decentralized machine learning ecosystems.
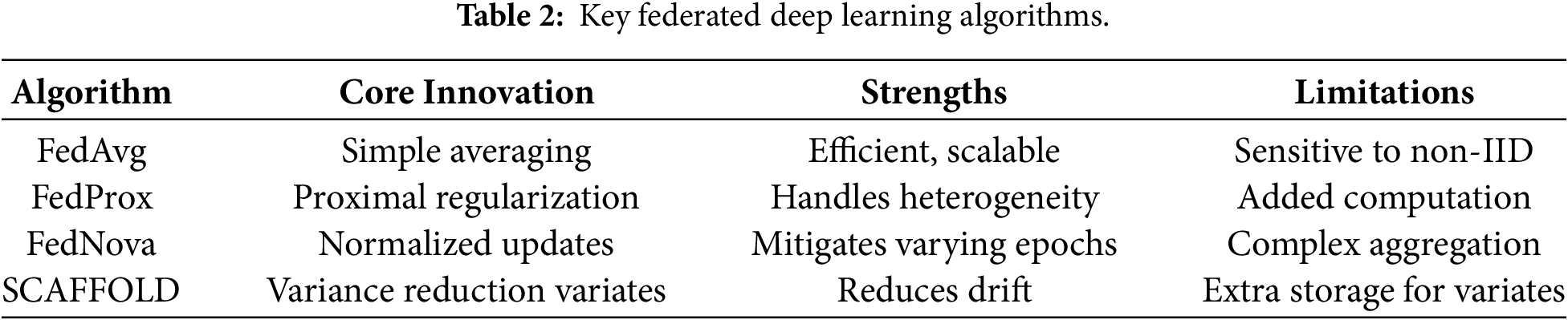
The simplest and least academic algorithm is FedAvg, which is beneficial because it serves as a baseline on which more complex algorithms can be built, or because it can be packed in-memory as control variates to achieve better convergence in non-IID conditions like cross-neighborhood traffic or multi-hospital healthcare data. More complex algorithms are based on FedProx, which can be used to add a proximal term to the underlying algorithm to enhance its resistance to non-IID.
3.3 Integration with Deep Models for Urban Data
FDL is compatible with deep architectures that are urban data modalities. Vision-based data, which were used in medical images or street surveillance, are processed using CNNs, thus allowing federated anomaly detection without any references to data sharing [51]. Federated deep-learning framework to predict the traffic flow in cities by combining graph learning and the trusted authority system to protect model data and enhance the quality of predictions [68]. Long short-term memory networks (LSTMs) or gated recurrent units (GRUs) process time-series data, such as traffic flow or energy use prediction, making sure that local sequences are private as has been reported in literature [69]. Transformer models are the best in long-horizon forecasts, such as forecasting events in urban areas, as they can capture dependencies between distributed sensors, as shown in examples. important progress on time series forecasting with Transformer-based architecture that demonstrates their applicability to long-term dependencies [70]. GNNs encode geometric structures of road networks or building graphs and are used to complete tasks such as optimization of a smart grid, and the evidence is provided by results. The GNNs, which in this case are Edge Convolutional Neural Networks (EdgeCNN), are superior to the traditional graph kernel algorithms in the classification of urban road networks with 85 percent precision [71].
These integrations are used in urban ecosystems to manage non-independent and identically distributed (non-IID) problems, and hybrid CNN-LSTM-Transformer GNN models are much more effective in federated environments, and this observation is supported by existing literature.
3.4 Federated Learning Variants
The variants of FL are adaptive to the data and system characteristics. Horizontal FL (sample-based) retains most of the shared attributes, but uses sampling; it is especially appropriate in urban IoT cross-device contexts (where devices have analogous sensors but produce different data in smart homes) [72]. Vertical FL (feature-based) partitions traverse between various parties and are therefore best suited to cross-silo situations, such that a hospital group analyzing patient records jointly, without sharing full records [73,74]. Federated Transfer Learning combines FL and transfer learning; it is commonly pretrained on publicly available corpora, followed by a fine-tuning step that is completed federated, a method that is also proven to be quite effective in urban settings with scarce local data [75,76]. Lastly, cross-device FL is developed to serve resource-limited wearable devices deployed in the home environment, and cross-silo FL is designed to meet the needs of institutional resources like hospitals [77]. Fig. 5 outlines the various variants of FL, making the various methodologies and tactics used to augment model training and create privacy protection in distributed environments.
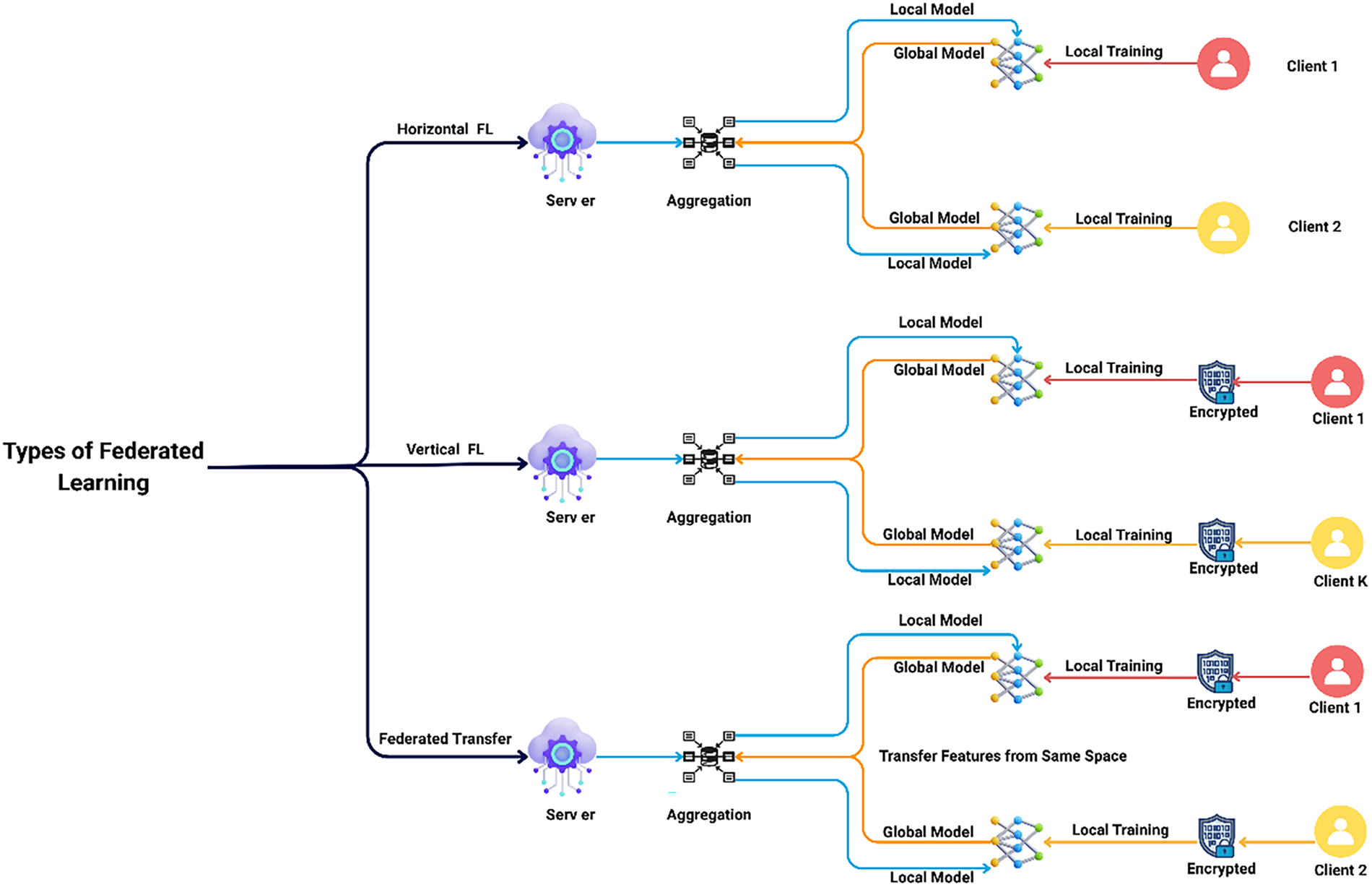
Figure 5: Variants of federated learning [51].
Fig. 5 presents the three main types of FL with their different strategies of data partitioning and application case situations. Horizontal FL entails clients with identical feature space but distinct sample space such that mobile phones and cameras (belonging to different people), where local models are fitted on personal user data and combined to create a global model, which is optimal to cross-device urban IoT such as smart homes. Vertical FL extends to clients with the same sample space but different feature spaces (i.e., complementary datasets with different entities), in which encryption is used to combine the different feature spaces and jointly train the model without revealing raw features. This approach is applicable to cross-silo collaborations (such as between organizations). Federated Transfer Learning offers the ability to transfer knowledge in one domain to targets in another one with different features and sample space (e.g., hospitals with dissimilar MRI equipment and patient cohorts). where encrypted local training and aggregation addresses the lack of data in a specialized healthcare imaging field. Overall, these variants enhance FL to be flexible in terms of privacy-conservative collaboration in heterogeneous urban ecology.
4 System Architectures and Urban Deployment Patterns
The implementation of FDL systems in smart urban ecosystems requires robust system designs to combine the principles of distributed computing to address the size, heterogeneity and limitations of IoT devices. Here, the edge-fog-cloud continuum, the topology of federation, computational and communication efficiency, and other urban-level constraints are in the context of smart cities, healthcare, and applications of the IoT.
The edge-fog-cloud continuum provides a rank-based structure of organizing FDL training on separate layers to optimize the latency and bandwidth consumption in urban IoT networks [78]. Intermediate aggregation is done by the fog layer, which consists of gateways, building-level edge servers, or regional aggregators, which allow clusters of devices to converge faster, hospital servers with electronic health record data or building management systems with occupancy and energy measurements [79,80]. A detailed explanation of the FL architecture for Personalized Health Care (PHC) is provided in Fig. 6, which emphasizes the power of decentralizing the processing of patient data and of training models in parallel, to both increase patient privacy and improve diagnostic precision for clinical applications.
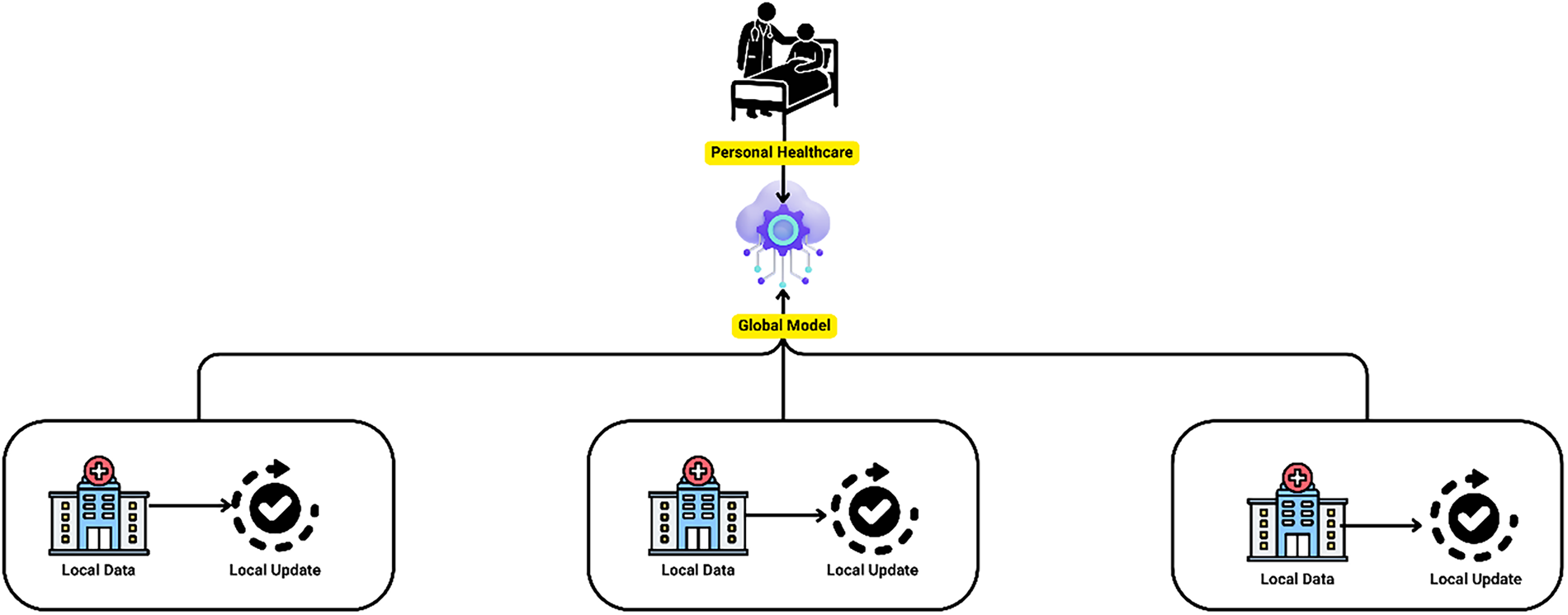
Figure 6: Federated learning framework for personal healthcare.
Fig. 6 shows an FL system that is specific to the personal healthcare setting, where several hospitals or medical professionals jointly train a common global model whilst ensuring that all patient information is kept locally so as not to violate privacy laws. Every hospital has its Local Data (its own hospital icons with databases), conducts local training of own EHR, and transmits only model updates (not raw data) to a central cloud server, which consolidates them into a New global model. This enhanced international model is then returned to the hospitals themselves so that each can receive enhanced personal healthcare of acquiring a better predictive perspective. On the right, a set of insights (significant to the framework) include: the ability to predict health events, distributed EHR learning without engaging in privacy practices, and scalable privacy-preserving AI applications in sensitive medical uses, which is consistent with real-world uses of major companies to train edge-distributed.
The cloud layer assumes the functions of synchronization of the global model and final aggregation of the large-scale urban environment, including optimization of traffic across the city or monitoring of the environment of various districts [81]. This multifaceted design maintains serverless and hybrid-based designs, which can dynamically scale resources, significantly eliminate the data-transfer load and maintaining privacy in smart cities, medical and building IoT applications [82]. The latest 2024–2025 research have shown that edge-fog integration can increase energy efficiency and real-time responsiveness in urban deployments, especially in undertaking tasks with a high level of latency sensitivity such as detecting anomalies in smart buildings and remote patient monitoring. Fig. 7 presents the underlying intrinsic layered privacy architecture of FL explained in more detail with respect to the hierarchical structure of the privacy safeguards that are designed to ensure that the confidentiality of the data at the distributed nodes is maintained.
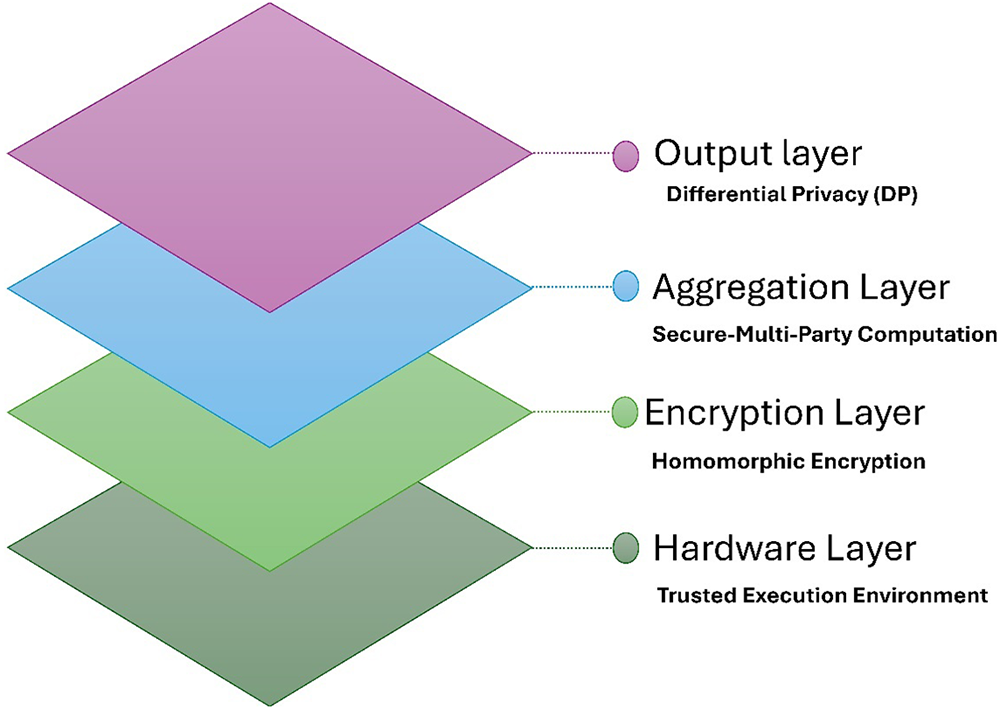
Figure 7: Layered privacy architecture in federated learning.
Fig. 7 shows the stratified privacy protection schemes in FL in the form of a pyramid with four stars to offer holistic coverage of both inference and leakage attacks on distributed systems. TEEs provide secure enclaves at the lowest level of hardware to ensure protection against either physical or operating systems threats. The encryption leverages HE to compute the operations in ciphertext without decryption and makes it possible to aggregate model updates confidentially. The aggregation layer applies the principles of secure Multi-Party Computation (MPC) to aggregate client inputs without leaving any single party with access to individual data, which is one of the possible risks in collaborative urban IoT setups. At the very top, the output layer applies DP through noise addition to the final models or gradients, providing mathematical privacy guarantees in case lower layers are corrupted. This is a multi-tiered solution on hybrid FL frameworks, which find a balance between utility and security on sensitive applications, such as healthcare imaging and smart urban monitoring, but has trade-offs of computational overhead.
Federation topology is the instantiation of the fabric of client-server interaction in federated distributed learning ecosystems, and the architectural decisions at this tier are implicitly scaled, fault-tolerant, and vicissitude privacy assurances in urban milieus.
The centralized or star topology, which is the second type, links all the participant devices to one all-knowing server, which pulls together their local updates. its implementational simplicity and its applicability to cross-silo partnerships, such as the collaborative training pipelines that unite hospitals in a healthcare network [83]. However, there is also one Achilles heel to this paradigm; the central node turns into one point of failure and load potential constraint, particularly when the number of clients explodes. To reduce these limitations, the hierarchical, or multi-level model adds intermediate aggregators, either in the form of fog nodes integrated into smart edifices or regional servers that cut across municipal lines. These relays reduce communication congestion, hence improving scalability over long-range urban-infrastructure systems like smart grids and traffic-management systems [84]. The peer-to-peer topology does not use any centralized arbiter whatsoever, and clients are free to communicate directly, which elevates resilience in indeed decentralized Internet-of-Things scenes such as smart home setups. However, it comes with its own decorum of tribulations, particularly, the administration of trust and coordination of dissimilar updates. IoT and Wireless Sensor Network (WSNs) integrated architecture applies P2P networks, tuple-space, and novel protocols to scale, make cross-networks, and effectively transfer sensor data to services on constrained devices [85]. Vigorous orchestration and scheduling are inseparable; they imply the selective choice of clients based on resource availability, battery life, or data quality, and the assistance of straggler mitigation by means of wise time-out or adaptive aggregation measures. It is only after paying attention to these mechanisms that we will be able to protect the stability of performance in learning within the whimsical dynamism of modern urban ecosystems. Fig. 8 outlines the various topology patterns inherent to FL, hence explaining the various network/structures and configurations used to fine-tune protocols used to exchange data and improve the efficacy of model training across distributed settings.
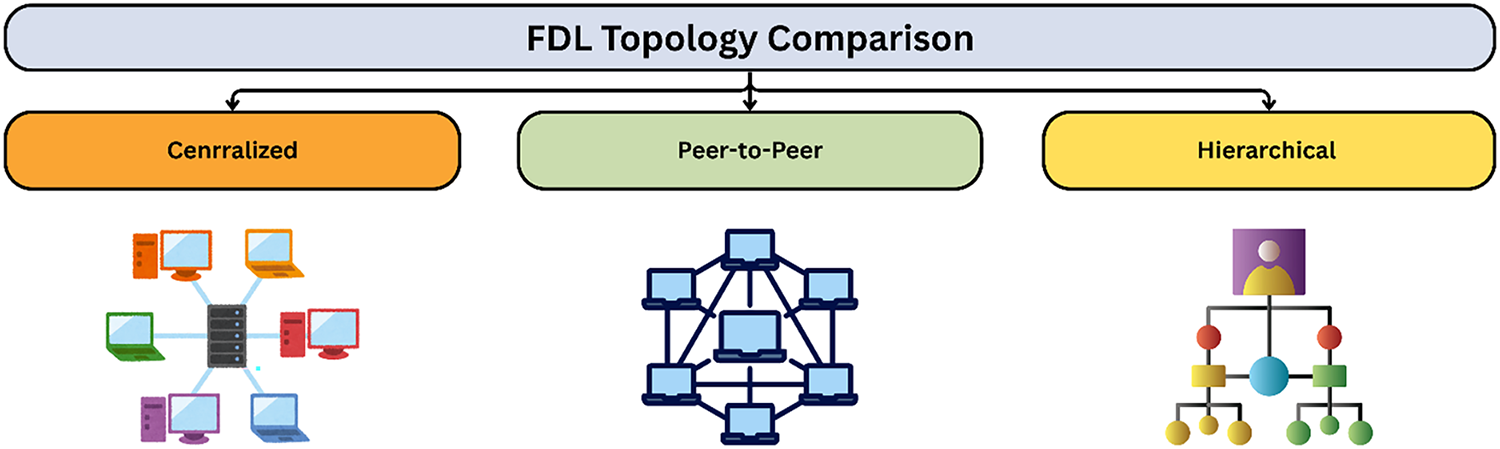
Figure 8: Topology patterns.
Fig. 8 gives an evident eye-catching comparison between three major topology patterns in FDL, and how they differ structurally and affect urban deployments. The centralized topology uses a star-like topology with all client devices (noted as laptops) connected directly to one central server to aggregate the models, which is simple and provides effective coordination with the disadvantage of single-point failure and heavily loaded servers-typical of simple cross-silo healthcare collaborations. The peer-to-peer topology indicates clients connected in a fully decentralized mesh network that does not have a central coordinator, which enhances resilience and fault tolerance suitable to changing smart home IoT clusters, but which has a higher complexity of communication and trust issues. The hierarchical topology uses a multi-level tree structure and uses intermediate aggregators (nodes) between clients and a top-level server, which scales slightly better and has lower energy consumption, as only local traffic or environmental sensor data is sent to a top-level server (regional edge servers). All these patterns point to the trade-offs of coordination, resilience, and overhead, which inform the choice of topology in heterogeneous urban ecosystems.
4.3 Communication and Computation Efficiency
Enhancing effective communication is one of the top issues in urban FDL settings, where many IoT nodes vie in limited bandwidth resources. FL lets AI train on separate IoT devices without sharing data, enabling several smart IoT apps [86]. The key measures that can be taken to reduce this problem include updating compression, also known as removing unneeded gradients, scarification, which is reducing unnecessary model parameters by pruning them using the top-k selection method, and quantization, which involves down-sampling numerical computations to 8-bit or even less. FL is a distributed ML method, which allows one to train models on a client device without compromising the privacy of the user data [81]. Most popular among them is the hybrid scheme called Qsparse-local-SGD: it a synergistic combination of sparsification and quantization with locally applied updates in Eq. (5):
Here,
Urban FDL systems face numerous constraints in practice which undermine reliability and performance. Hybridization of deep learning with Bayesian regularization to improve the efficacy and dependability of neural networks in operating urban planning [90]. Disruption in synchronization in mobile traffic sensors, intermittent loss of signals in mobile traffic sensors, vehicular and pedestrian node motion, and intermittent lack of sensors due to failure or maintenance of sensors all disrupt synchronization and require the implementation of robust algorithms, including asynchronous aggregation protocols and fault tolerant client-selection algorithms [91]. Federated learning can be used to provide a promising solution to the smart city problem as it can process data with decentralization, provide privacy, and solve such issues as the heterogeneity of data and resource limitations [92].
Mitigation solutions consequently include drift detection systems, ongoing online adaptation, and the implementation of federated split learning, which all play a role in maintaining the performance of the model in the environment of the dynamically changing city. He structure is tested on image classification problems with ImageNet and CIFAR-100 data sets with four model architectures and shows that it achieves much better concept drift adaptation and long-term stability in performance than baseline FL methods [93]. Concept-Drift-Aware Federated Averaging (CDA-FedAvg): This algorithm builds upon Federated Averaging (FedAvg) to pursue concept drift continual adaptation [94]. In proposed way, Table 3 the architectural patterns typical of urban environments, specifying their respective advantages, limitations and fields of optimal application, to help understand their applicability in various urban contexts.
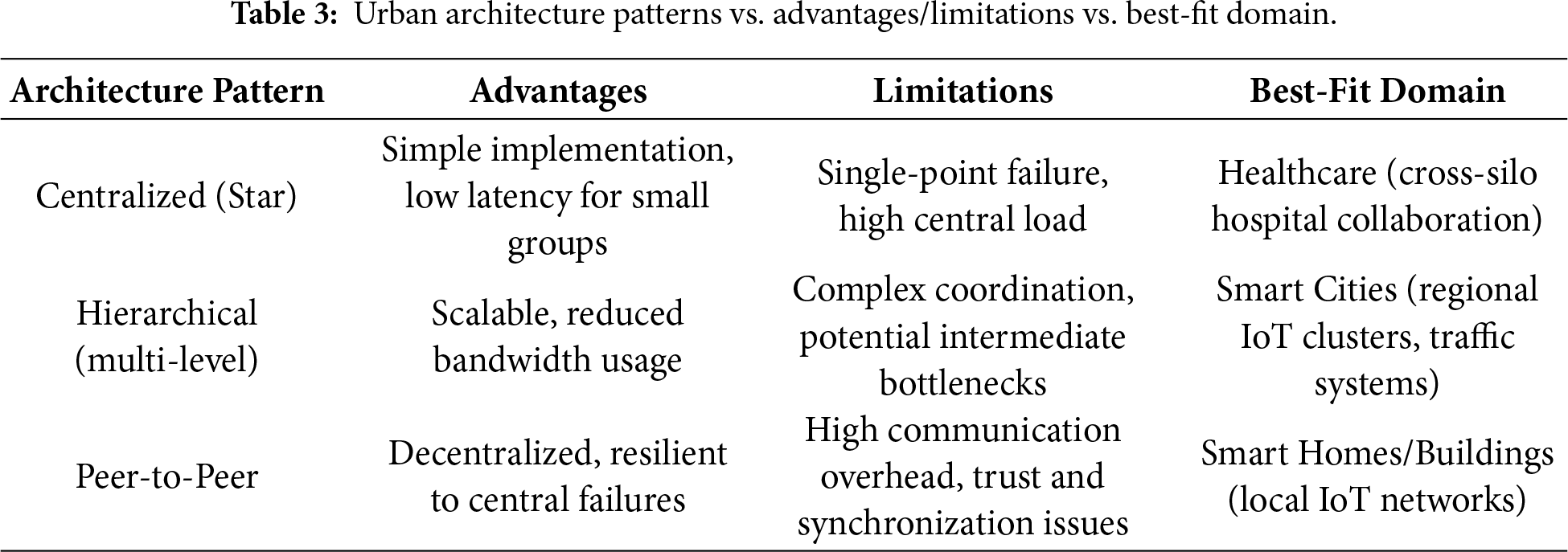
Table 3 compares three basic architecture patterns (topologies) in FDL applications in urban ecosystems and evaluates their pros, cons, and best uses. Due to direct client-server interaction, the Centralized (Star) pattern is easy to implement and has low latency for small-scale operations, but it causes single point failure and overloads the central server, so it is best used in healthcare environments with cross-silo hospital interactions and a trusted The hierarchical (multi-level) pattern is more scalable and lowers bandwidth by introducing intermediate aggregators (edge or fog nodes) to deal with local groups before global synchronization, but it has complex coordination and potential bottlenecks at intermediate levels, making it better for smart cities with regional IoT network clusters or traffic systems that need to be easy to manage in large scale. Finally, the peer-to-peer pattern allows direct client-to-client interactions and is decentralized and not vulnerable to central failure, but it has a higher communication overhead and is ineffective at managing trust and synchronization, making it less desirable in a smart home/building with a local IoT network where devices can function autonomously in smaller, trusted groups. In privacy-preserving urban FDL applications, the table trades efficiency, reliability, and complexity to choose topology.
4.5 Layered Privacy Deployment: A Concrete Cross-Silo Hospital EHR Example
To concretely illustrate how the layered privacy architecture presented in Fig. 7 is sequentially applied in real deployments, we consider a cross-silo federated learning setting involving hospital EHR data. The example specifies where each privacy mechanism is applied (client-side, during transmission, and at the aggregator) and clarifies the cumulative implications for privacy budget and model utility.
Assume
4.5.2 Sequential Application of Privacy Layers
Step 1—Client-Side: Secure Local Computation (TEE Layer)
At the beginning of each round, each hospital downloads the current global model
Step 2—Client-Side: Differential Privacy on Model Updates
Before any information leaves the hospital, the local update
This step ensures
Step 3—During Transmission: Secure Aggregation/HE/MPC
Hospitals transmit only the privatized updates
Step 4—Fog-Level Aggregation
Regional fog nodes aggregate updates across hospital clusters:
Only aggregated values are available at this stage, which reduces long-distance bandwidth consumption and improves scalability in urban deployments. Hierarchical aggregation can also improve the effective signal-to-noise ratio under DP by increasing cohort size at aggregation points, which helps recover utility when DP noise is applied at the client level.
Step 5—Cloud-Level Global Update
Finally, the cloud coordinator aggregates fog-level updates to compute the next global model:
If required, an additional central DP mechanism may be applied to the aggregated update and/or to the final released model to provide an auditable privacy guarantee at deployment.
If central DP is applied, the cumulative privacy budget can be expressed conceptually as:
where
4.5.3 Cumulative Impact on Privacy and Utility
The layered deployment yields systematic trade-offs between privacy guarantees, model utility, and operational cost. Table 4 summarizes where each layer is applied and its practical implications.
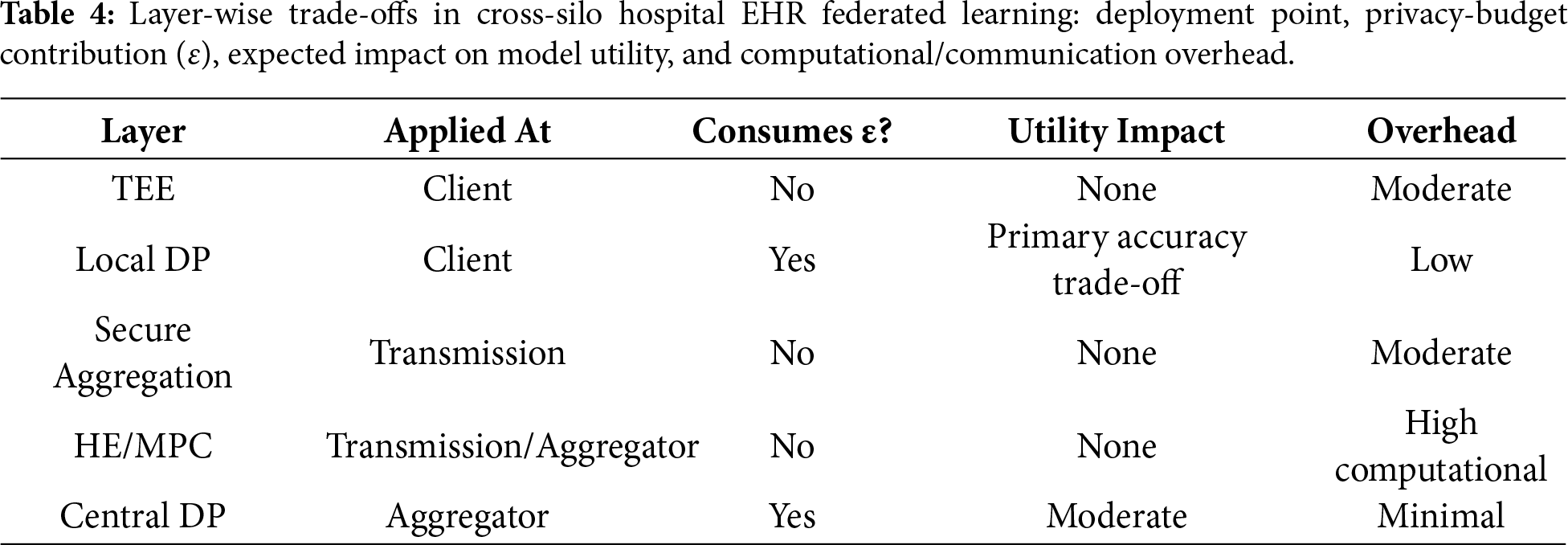
Overall, differential privacy governs the formal privacy guarantee, while cryptographic layers protect against structural leakage by preventing exposure of individual updates. Larger cohorts and hierarchical aggregation improve DP utility by averaging signals across more participants, and the edge–fog–cloud architecture mitigates communication and computation bottlenecks in urban-scale deployments.
4.5.4 Rationale for Layering in Urban Healthcare Federations
Layering is particularly important in hospital EHR federations because the threat model is multi-faceted. Regulatory compliance requires formal privacy guarantees (DP), institutional trust and collaboration benefit from cryptographic protection of updates, insider and platform threats motivate secure execution environments (TEEs), and urban-scale deployments require hierarchical aggregation to maintain scalability and responsiveness. As a result, the layered stack operates sequentially rather than redundantly, with each layer addressing a distinct class of threats while maintaining a controllable balance between privacy budget and model utility.
5 Privacy-Preserving Mechanisms in Federated Deep Learning
FDL in the city, in residential and commercial infrastructures, and healthcare are a significant privacy threat due to confidentiality of the processed data, including readings of traffic sensors, medical records, and personal device data. In this part, the key threat models, and, next, the key privacy-preserving methods are outlined, especially focusing on the developments and their implementation of urban settings.
5.1 Threat Models in Urban Ecosystems
The city federation of learning plans are susceptible to common-gradients or common-model inference attacks. Model-inversion attacks are based on the idea that it is possible to re-create the privately trained artifacts like patient images in healthcare or household-energy consumption traces with the help of model outputs or gradient data [95]. Membership-inference queries determine whether a specific record such as an electronic health record of a patient or a reading on a sensor of a device was used in the training corpus. The model of an inference attack uses a shadow model to model the division system of medical databases and can infer the private members with reasonable accuracy on the attack and suitable computation costs [96].
Transmitted gradient gradient-leakage or reconstruction methods extract substantive input data, which is a weakness that becomes especially dangerous when using non-IID data distributions in urban areas. It is suggested that a technique termed Deep Leakage from Compressed Gradients (DLCG) enables one to recreate images based on compressed gradients and shows that it is capable of reconstructing recognizable images with a high degree of sparsity and performs better than other algorithms [97]. Poisoning attacks disperse malicious data in the security sphere to reduce the model effectiveness, and backdoor exploits entangle hidden trigger activations that cause incorrect behavior on the targeted inputs, thus corrupting traffic predictions in smart city infrastructures [98]. The urban environment further increases these risks due to the heterogeneity of devices and regulatory processes that include GDPR and HIPAA. There is significant pressure of urbanization on the Urban Critical Zone (UCZ) because it influences Urban Critical Zone interfaces, bringing about the alteration of ecosystem structure, processes and functions which include land use alterations, loss of biodiversity and pollution [99]. Fig. 9 illustrates a layered defense framework that defines the range of privacy attacks that occur in FDL, and the corresponding mitigation strategies that have been developed to ensure data and model integrity.
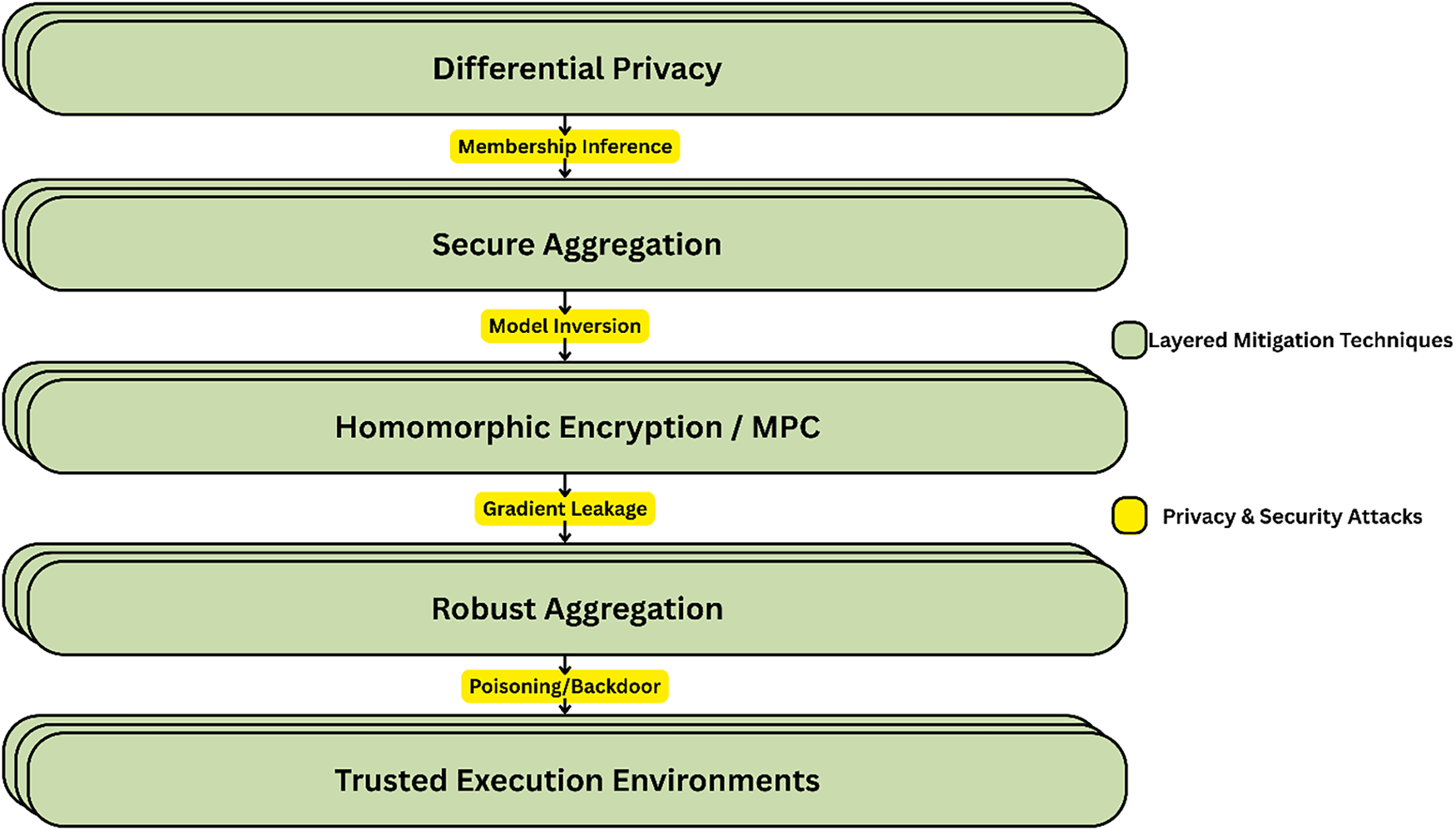
Figure 9: Layered defense framework illustrating privacy attacks and corresponding mitigation techniques in FDL.
A defense-in-depth approach to mitigating the threat of increasing attacks in distributed training is shown in FDL as a stack of mitigation strategies associated with individual privacy and security attacks. On the first level, DP prevents membership inference attacks by adding noise to output or gradients to prevent adversaries from determining which record was utilized during training. Secure Aggregation protects against model inversion attacks by hiding client updates, so the server sees the aggregated output. To prevent gradient leaking, HE and MPC are employed to compute encrypted data and ensure transmission and aggregate confidentially. Aggregation prevents poisoning and backdoor attacks by screening out harmful (or outlier) updates by infected clients. Finally, hardware-level Trusted Execution Environments (TEEs) secure the entire process against low-level attacks.
5.2 Differential Privacy (DP-SGD/Federated DP)
DP adds controlled noise to gradients or outputs hence providing strong mathematical guarantees against inference attacks. DP has become a promising method of safeguarding the privacy of neural networks, and it is prioritized on its boundaries with deep learning, privacy protection, fairness, robustness, and overfitting prevention [100]. When used with FL, local DP implements noise at the client-side, providing more significant privacy at the cost of a higher utility loss, and central DP implements noise at the aggregation phase. A noise addition method provides privacy and accuracy similar to DP approaches for privacy-preserving FL by looking at noise volume and direction [101]. In DP-SGD, however, the gradients are first clipped, and then a Gaussian or Laplace noise is injected depicted in Eq. (6):
where,
Secure Aggregation (SecAgg) protocols hide the individual updates, so that the central server only sees the sum of them; this eliminates the threat of gradient leakage. The use of SecAgg as a local differential privacy (LDP) scheme offers insufficient privacy to membership inference attacks, which explains the need to use noise injection in FL [102]. In resource-constrained environments, group verifiable secure aggregate FL (GVSAFL) is a safe aggregation technique that protects privacy, reduces computing costs, and speeds up FL training [103]. An additive secret sharing secure aggregation solution enhances computation speed by 557 times, cost of communication by 25 times, and accuracy of the model, as well as FedAvg and SCOTCH [104].
5.4 Homomorphic Encryption (HE) and Secure Multi-Party Computation (MPC)
HE is a type of encryption where computation is done on encrypted data; the Chaotic Krill Herd (CKKS) scheme supports approximate arithmetic; this way can be used to perform encrypted aggregation, but at a significant overhead as described in references. To meet emerging information security challenges, HE technology has evolved past Partially Homomorphic Encryption (PHE) to encompass fully HE and, with machine learning, to Approximate Homomorphic Encryption (AHE) [105]. Secure MPC shares the workload with multiple parties and never discloses any individual input and is often used with HE to attain secure aggregation or inference. The Neural Homomorphic Operation System (NHOS) against HE is a lightweight homomorphic addition of encrypted data with quantized weights, yielding 88.10% accuracy and 88.10% accuracy with homomorphic addition of encrypted data, which is a lightweight alternative to HE in FL [106]. However, the overhead is also a major impediment to the resource-limited urban IoT deployments.
5.5 Trusted Execution Environments (TEEs)
Trusted Execution Environments (TEEs), such as Intel SGX, ARM TrustZone, provide hardware-isolated enclaves for secure local training or aggregation. With remote attestation, through trusted execution environments such as Intel SGX, Arm TrustZone, AMD SEV, and RISC-V, the genuineness of code against attackers is ensured in sensitive applications [107]. Performance comparison of TDX, SEV, Gramine-SGX, and Occlum-SGX is conducted, evaluating computational overhead and resource usage under realistic conditions, with a unique focus on the recently released TDX [108]. They protect against OS-level attacks but assume hardware trust, vulnerable to side-channels.
Blockchain interacts with FDL to provide decentralized trust, immutable audit trails and incentives in urban IoT and healthcare systems. Unlike current trust management systems, a decentralized medical trust management system employing blockchain-based FL would ensure scalability, credibility, and resilience to malicious assault, allowing IoT data exchange safely [109]. It authenticates updates and makes it tamper-immune, though with the overhead costs limiting scaling. Critical overview of the key privacy-preserving strategies employed by FDL in four aspects: the nature of privacy assurance they provide, the additional effort they need, and the impact on model performance. DP provides a good mathematical guarantee by introducing noise, at the cost of increased work and some accuracy. It has been more recently applied in smart city anomaly detection and healthcare imaging [110,111]. Secure Aggregation retains single client updates off the server, which has no or minimal overhead and makes no difference to accuracy. HE/MPC is commonly employed in IoT sensor networks and highly secure yet quite costly and inaccurate computations on encrypted data [112,113]. It has been recognized to study trusted EHRs [114–116] Trusted Execution Environments offer hardware-based isolation with a small overhead and degradation in accuracy, and are thus a good choice when training edge devices in smart buildings [117]. Enhanced techniques with blockchain ensure that audits cannot be changed and have much overhead, and have no impact on accuracy. This is in favor of decentralized smart grids [118]. In the case of both DP and Secure Aggregation, Hybrids combine the best worlds to offer maximum protection with varying amounts of overhead. They are increasingly coming up in modern traffic and health surveillance [119]. The chart is used to select the most suitable strategy based on the strength of privacy, the performance trade-offs, and their performance in privacy-sensitive deployments in cities using the FDL.
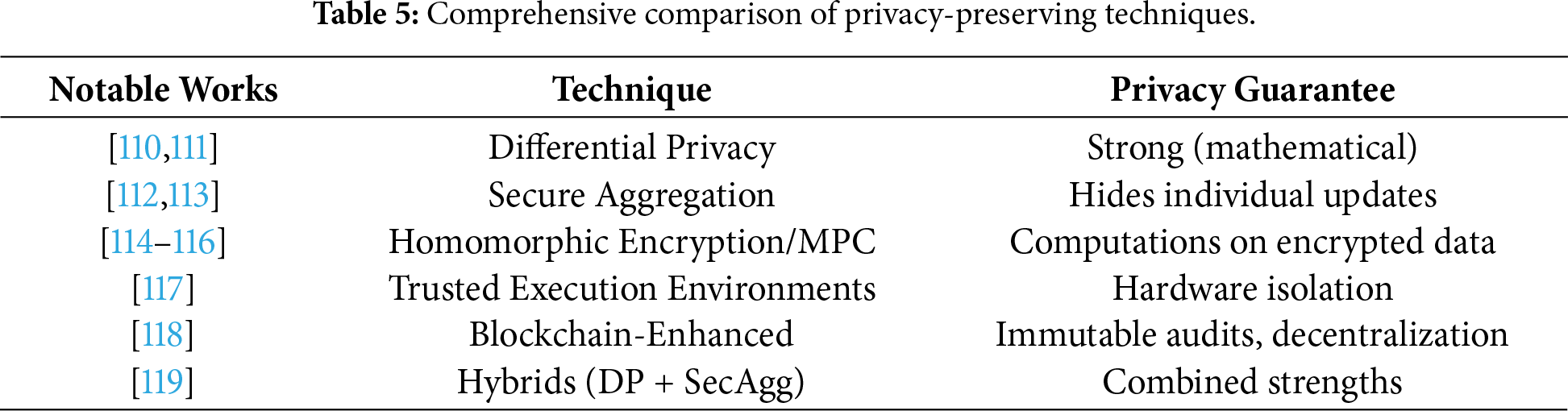
Table 5 provides privacy-preserving techniques, characterizing the efficacy, benefits, drawbacks, and applicability of the privacy-preserving techniques across a range of applications, focusing especially on FL systems.
The combination of different protective measures: DP with secure aggregation, which addresses noise and updates the models without revealing them; robust aggregation, which is reinforced with privacy protection, which addresses poisoning attacks; and split learning, which is complemented by FL, segregates models to reduce exposure.
Privacy measurement in FL assesses its ability to protect sensitive data during AI model training, detecting gaps and suggesting new methods [120]. Privacy and security improvement techniques of FL in healthcare discuss the Differential Privacy, HE, blockchain, hierarchical approaches, peer-to-peer sharing, intelligence on the edge device, and mixed approaches and their strengths, weaknesses, and prospects [121].
A hybrid technique that combines DP and FL (HDP-FL) is 9.39% more accurate in EMNIST and CIFAR-10 and balances privacy and utility in decentralized learning [122]. Hybrid AI systems outperform single-system cybersecurity systems on accuracy, privacy, scalability, explainability, and robustness, yet real-time implementation and interpretability still pose a problem [123]. FL privacy attacks, FL vs. HE, and FL as a scaling, efficient, and resilient privacy strategy in healthcare are compared [124]. Table 6 outlines the mapping between domains and the associated privacy risks and proposes, at a suitable level of calibration, a privacy stack that provides solutions specifically designed to address different security and privacy risks in different areas.
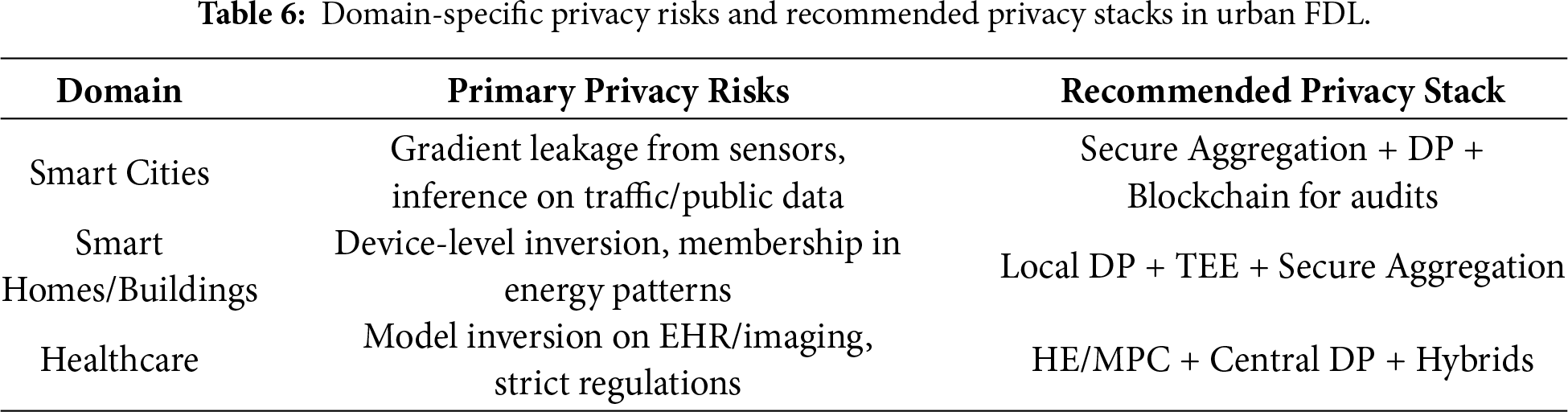
Table 6 enumerates the FDL privacy problems in urban ecosystems and suggests custom privacy-saving stacks to address the problems. The greatest threat to smart cities is gradient leakage of the public sensors and traffic or environmental data inference attacks. The best stack is SecAgg (to conceal updates), DP (to provide protection by noise), and blockchain (to obtain audits that cannot be changed in decentralized city networks). Smart Home/Building vulnerabilities include device-level model inversion and belonging to an individual energy pattern. Local DP (client-side noise), TEE (edge device hardware isolation) and SecAgg are recommended. Healthcare is the most restrictive area where there are issues with model inversion on sensitive EHR or imaging data. Optimal stack comprises HE/multi-Party computation, central DP (server-side noise), and hybrids. The table recommends urban FDL deployments make use of tiered privacy strategies that suit the threat environment and operational constraints of every domain.
HE/MPC provides lossless precision with computations of ciphertexts; but comes at a more compute cost such that CKKS aggregation is slower. Differential Privacy (DP) offers a light computation with noise, leading drop in utility like CIFAR-10/medical imaging.
New FDL discoveries (2019–2025):
• In adaptive noise, hybrids achieve better balances-DP + Secure Aggregation limits reduces.
• Breakthroughs in efficiency-NHOS-HE have increased.
• Urban validation-BraTS variants of segmentation reduce Dice loss to less on non-IID data.
See Tables 4 and 5, Healthcare HE + DP. There is no paradigm shift between the formation of conclusions and hybrids that enable scalable privacy-utility within heterogeneous ecosystems.
5.8 HE Practicality in Urban IoT
Implementation of smart cities generates volumes of sensitive data that presents privacy and security problems in the face of cyber threats. The Secure Privacy-Preserving Federated Learning with Homomorphic Encryption (SPP-FLHE) system is a combination of FL, optimized HE, and DP. It has a new HE schemes which minimizes latency, dynamic DP noise addition mechanism to improve privacy with less loss of accuracy, and model compression to reduce communication overhead. Experiments have shown that SPP-FLHE can provide 92.6% accuracy and reduce data transmission by 40%, as well as latency by 43% over traditional methods, and is effective in providing data analytics with high security in smart cities [115].
FL mechanism is applied to DL models for IoT-based healthcare, utilizing cryptographic methods like masks and HE to protect local medical models from attacks. The quality of datasets from different participants is highlighted as crucial for assessing local model contributions. A dropout tolerable scheme is presented to maintain FL despite exceeding client thresholds. Security analysis validates data privacy, alongside computational and communication cost evaluations. The method is illustrated through skin lesion classification with the HAM10000 dataset, showing effective privacy-preserving outcomes compared to prior approaches [125].
6 Domain-Specific Applications of Federated Deep Learning
Recent research on FDL has become a timely source of change in the urban ecosystem which enables privacy-preserving collaborative training on a diverse set of distributed IoT devices, environmental sensors, and institutional data repositories. This part will conduct a review of key applications across smart cities, healthcare systems, and smart homes or buildings that utilize spatio-temporal modeling frameworks, cross-institutional synergy, and energy-efficient schemes.
6.1 Federated Deep Learning in Smart Cities
FDL is an expert in smart cities in how it processes massive heterogeneous data from traffic sensors, environmental monitors, and public safety systems while maintaining the locality of sensitive information [27,126]. One of the main uses is traffic flow prediction and traffic congestion, where spatio-temporal GNNs can jointly model traffic road networks in city districts and achieve high accuracy in dynamic urban environments [127]. FDL is also helpful for environmental monitoring [128], air quality forecasting [129], smart energy-grid load balancing [130], and renewable energy integration, waste management route optimization, and public safety anomaly detection in surveillance feeds [131]. These cases point to FDL’s role in sustainable urban planning with increased IoT deployments.
6.2 Federated Learning in Healthcare Systems
In the healthcare sector, FDL serves as a tool for promoting inter-institutional collaboration, while at the same time meeting the privacy requirements imposed by regulatory bodies like HIPAA and GDPR [132]. Moreover, salient application of FDL is federated medical imaging used in the diagnosis of diseases, such as research in tumor segmentation in MRI, CT, and X-ray scans, which in turn allow hospitals to train robust models over heterogeneous datasets without requiring the exchange of patient images [133,134]. In addition, FDL provides an analytical backbone for EHR systems and enables to conduct of predictive modelling and accelerates drug discovery by joint genomics initiatives, as well as to support remote patient monitoring by wearable technologies [135,136]. Collectively, these modalities improve the generalizability of models across institutions with different platforms of scanners and patient demographics, which can advance the field of personalized medicine.
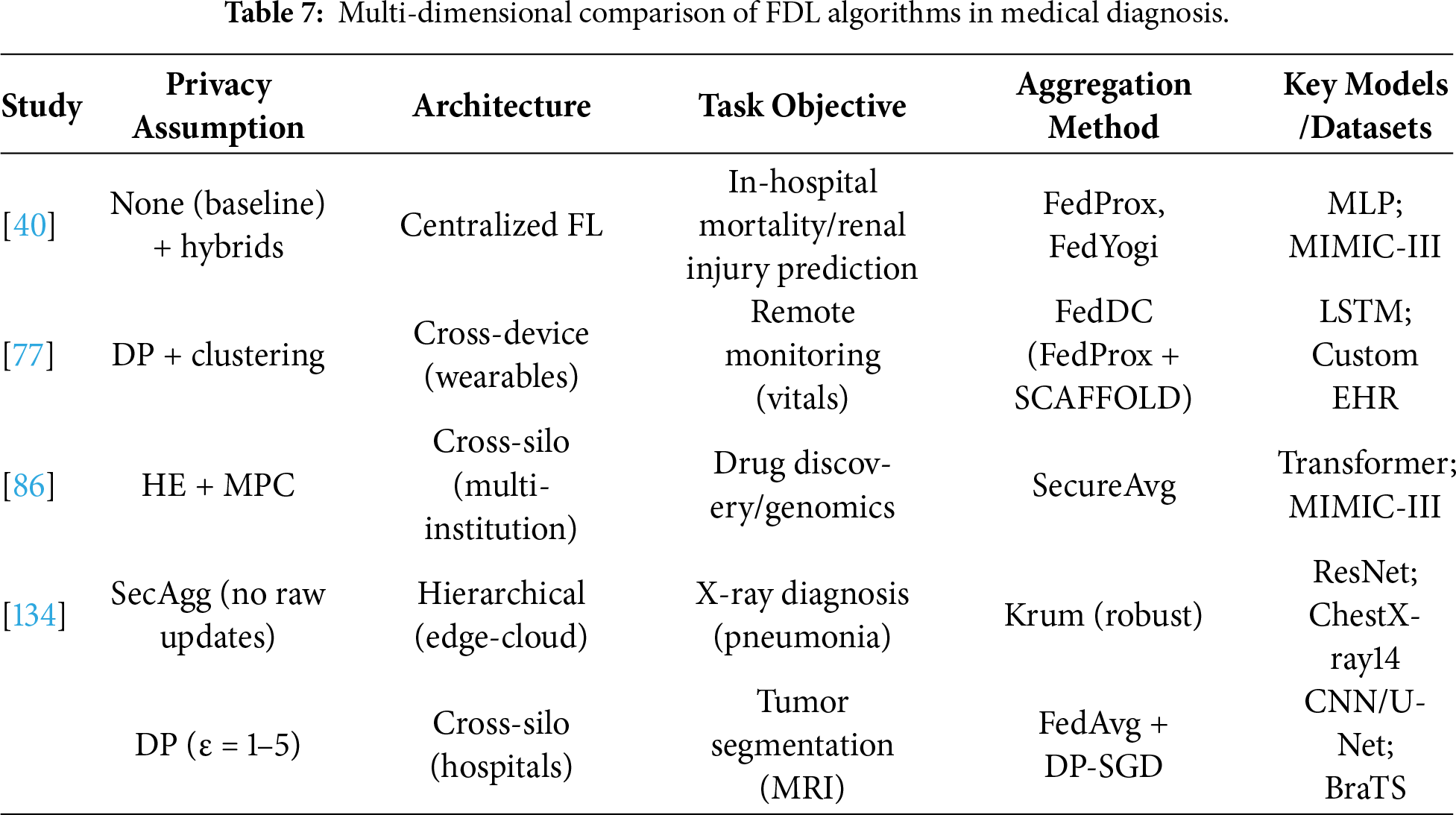
To highlight the differences between FDL works in healthcare, Table 6 will show a multi-dimensional comparison of representative studies on medical imaging tumor segmentation and X-ray diagnosis and EHR analysis. This can be in form of privacy assumptions, system architecture, task goals, aggregation techniques, essential models/data sets and tradeoffs between performance such as utility drop vs. baseline centralized DL.
Table 7 shows that the following trends exist: DP is highly applicable in the imaging to guarantee provable privacy, however it causes noise, which makes the utility drop. SecAgg is especially effective in strong aggregation of diagnosis with inhomogeneous hospital data. Hybrids including FedDC/FedProx are most capable of dealing with non IID EHR drift that is common in urban multi-hospital environments with minimal loss. The institutional silos lead to cross-silo dominance and the peripheral technology enables the use of wearables.
6.3 Federated Deep Learning in Smart Homes, Buildings, and IoT Ecosystems
The FDL framework maximizes the use of resources in both residential and commercial buildings by decentralized IoT data processing. Core tasks include Non-Intrusive Load Monitoring (NILM) as a form of energy disaggregation at an appliance level, HVAC optimization based on occupancy and user preferences, and occupancy prediction to implement efficient lighting and control strategies. Additional applications are in anomaly and intrusion detection in building networks and personalized automation aimed at achieving energy-efficient management. Recent development combined generative models and attention mechanisms with better NILM accuracy across heterogeneous home setups. Table 7 represents a detailed taxonomy of FDL applications across many domains. Each entry in the taxonomy is carefully classified based on its unique use cases, current challenges, and benefits derived under the respective application domain.
Table 8 contains a taxonomy of FDL applications in three main urban areas, that is, it groups applications based on their major sub-domains, their core tasks, the most prominent deep learning models thereof, representative datasets/benchmarks, and the up-to-date resources can be found in the literature. The activities targeted by FDL in the case of Smart Cities include traffic prediction [137]. Within the field of healthcare, a range of applications focus on medical imaging detection/segmentation, EHR analysis, and remote patient monitoring, where CNNs and U-Net variants can be applied to high-accuracy visual tasks on the dataset such as BraTS (brain tumors), MIMIC-III (clinical records), and ChestX-ray [138]. NILM, HVAC optimization, occupancy prediction, and anomaly detection are the main activities in Smart Homes/Buildings/IoT, and are often implemented with LSTM and attention-based sequential models on house-related data, like UK-DALE, REFIT, and REDD [139,140].
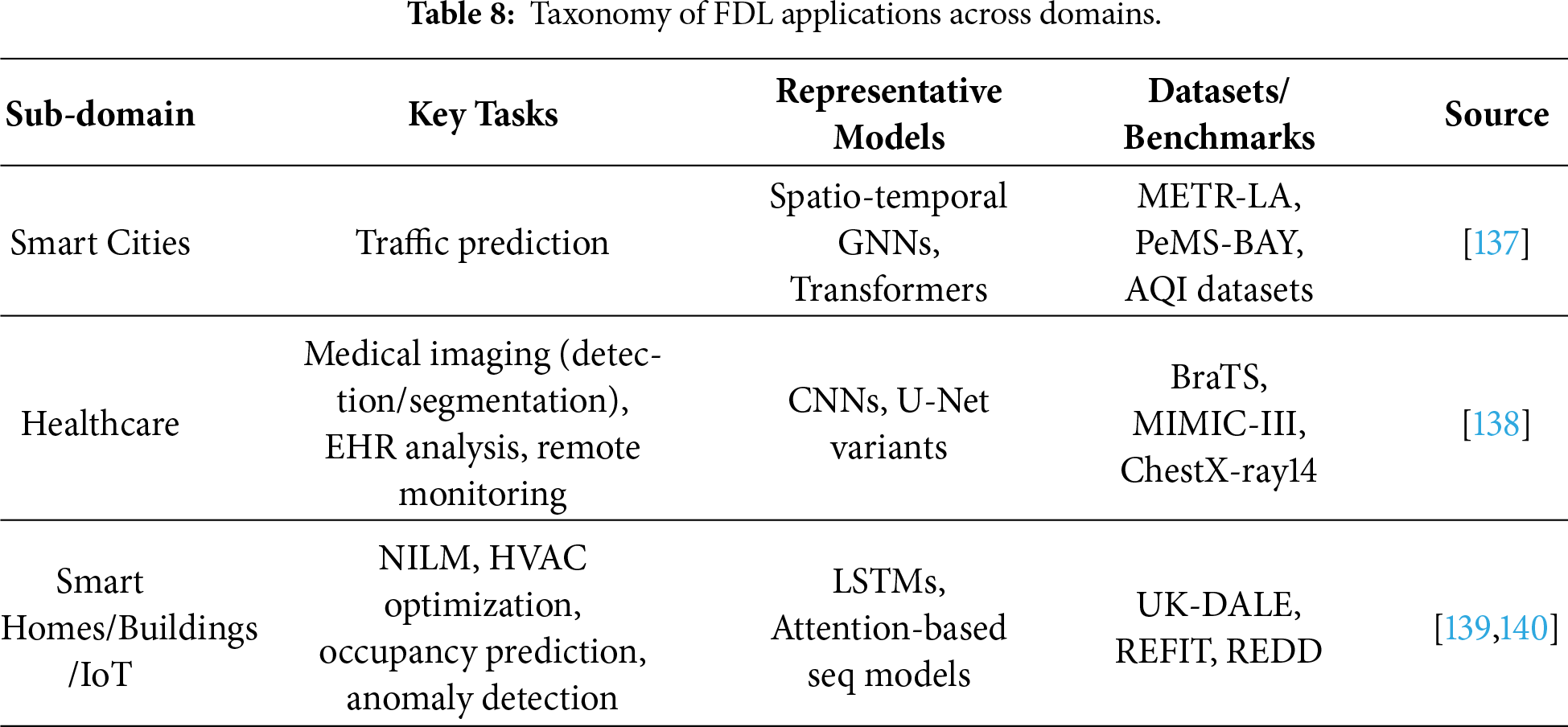
Fig. 10 provides a spectrum of FL applications and case studies, thus representing real implementations of FDL in a variety of industries and areas, and highlighting the ability of the method to solve industry-specific challenges.
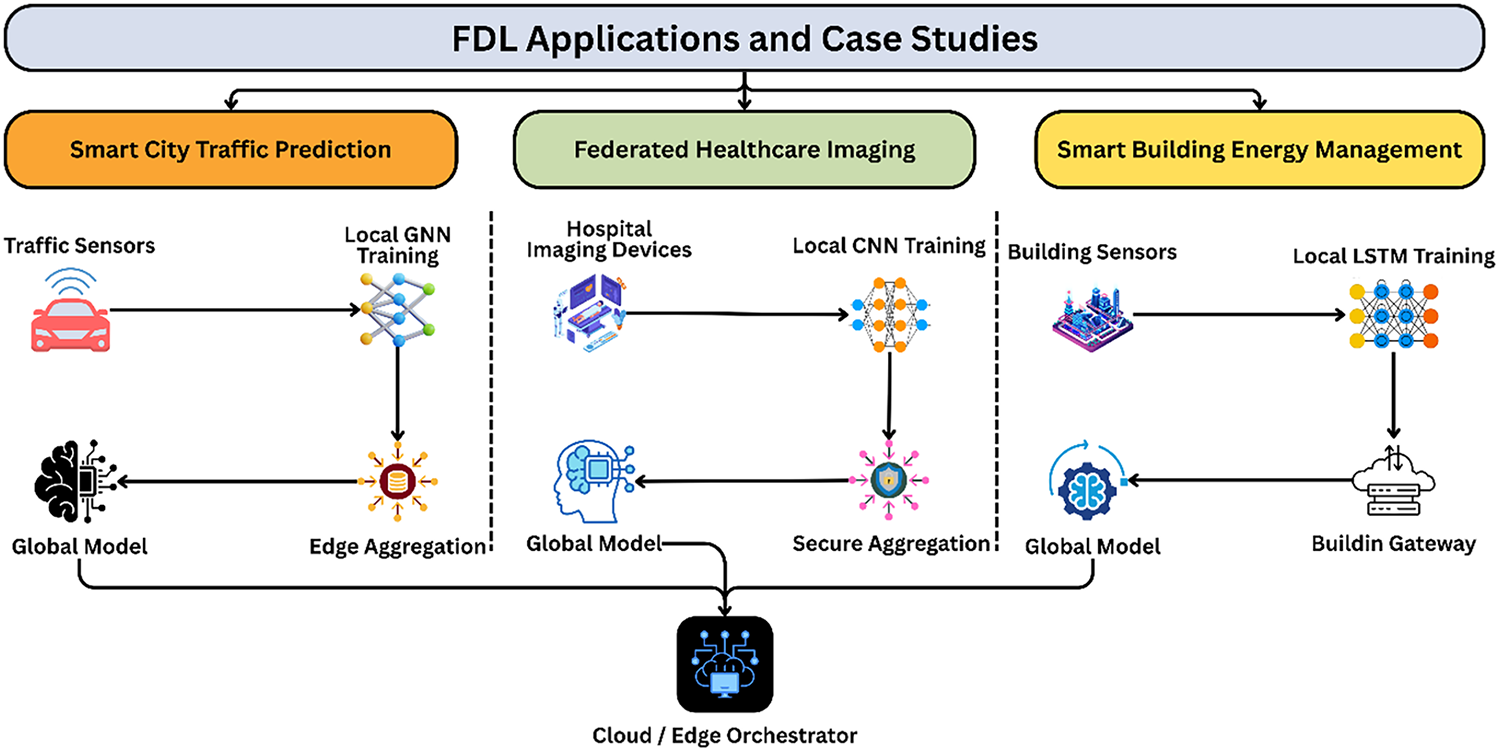
Figure 10: Federated learning applications and case studies.
These domain-specific applications demonstrate FDL’s transformative potential for privacy-preserving, scalable AI in urban ecosystems in above illustration, there are 3 parallel urban FDL case studies featuring customizable pipelines with central Cloud/Edge coordination. Distributed traffic Sensor training local GNN on spatio-temporal data and send updates to an edge aggregator for city-wide congestion prediction without raw data centralization in smart city traffic prediction. Hospital devices teach local CNNs on sensitive scans for federated healthcare imaging, safe aggregation to build a privacy compliant global diagnosis model across hospitals. In the case of smart building energy management, sensors train local Long Short-Term Memory (LSTM) on time-series of a building’s consumption, and route through a building gateway to better energy disaggregation and HVAC control across buildings. The figure illustrates the flexibility of FDL in terms of privacy preserving, scalable AI in heterogeneous urban ecosystems using domain-specific (spatial traffic—GNN, imaging—CNN, sequential energy—LSTM) and specific aggregation mechanisms (edge, secure, gateway).
7 Security, Robustness, Trustworthiness
Beyond the privacy issue, FDL in urban ecosystems faces serious security threats that undermine the integrity, robustness and overall trustworthiness of the models, particularly in sensitive areas such as medical diagnostics and smart city infrastructure. In this discussion, we define the main attack vectors that go beyond the mere privacy leak, and we assess state-of-the-art defense mechanisms and robustness under real conditions in urban areas, which imply the importance of byzantine and poisoning resilience.
7.1 Attack Taxonomy beyond Privacy
Malicious participants take advantage of the distributed setup of the FL to inject faults or manipulate outcomes, a phenomenon that can be systematically classified as data poisoning, model poisoning, backdoor attacks, sybil and byzantine adversaries and collusion [141]. Data poisoning refers to the intentional poisoning of local training data so that it has a degrading effect on global performance, while model poisoning refers to submitting fake data updates [142,143]. Backdoor attacks, which involve inserting hidden triggers or certain patterns in the sensor data, cause misclassifications only when the trigger is activated to be stealthy in dense cities where IoT devices are deployed [144]. Sybil attacks flood the system with fake clients to magnify the malicious influence, and Byzantine clients spread arbitrary harmful updates which, though not targeted, cause havoc in heterogeneous network settings [145]. Collusion scenarios occur when the multiple attackers coordinate their activities, essentially bypassing the defenses for a single client throughout the structure of cross-institutional healthcare implementation or city-scale sensor federations. Although these adversarial strategies have some overlaps with the privacy threats, the main goal related to compromising privacy is the compromise of availability and integrity.
Defenses are in resilient aggregation and detection, robust aggregation techniques based on the trimmed mean/median family involve removing outliers in the coordinates, while methods like Krum and Multi-Krum choose the updates that are most like their neighbors, and thus are robust to Byzantine faults. RFOut-1d is a powerful federated aggregation operator, which is a highly resistant backdoor model to model-poisoning attacks through filtering undesirable client updates, allowing it to maintain the model performance [146]. An alternative to the conventional schemes for FL is a group-wise robust aggregation framework, which is intended to increase the resilience of the model against Byzantine failures by clustering the model parameters in a systematic manner and then using a robust aggregation technique within each cluster [147]. Anomaly detection for updates uses distance measures or clustering which are used to signal anomalies [148]. Secure validation protocols are used to authenticate the updates using signatures or cryptographic proofs. Reputation/trust scoring systems give weight to clients based on their historical behavior, essentially down-weighting participants that may be suspicious. Hybrid approaches are a combination of these techniques that constitute a layered protection strategy.
7.3 Robustness under Real Urban Conditions
Urban FDL needs to be resilient to non-IID changes and drift from changing data such as seasonal traffic patterns and changing patient demographics, and address client drift through personalized models or drift regularization [149]. Sensor spoofing involves corrupting data as in the case of fake traffic information, while the unreliable devices pertain to missingness which affects training processes and require imputation or asynchronous handling techniques. A channel-spatial-temporal attention-based autoencoder network detects sensor data spoofing attacks better than existing methods and is more resilient to noise and attacks [150]. Table 9 shows an Attacks x Defenses matrix, which maps the various types of attacks in FL and their corresponding defense mechanisms, which helps recognize the effectiveness of each defense mechanism against the corresponding threats.
Table 9 shows an organized attack-defense matrix for FDL security vulnerabilities, including five major attack types organized by main attack goal, detectable signal/cue, and mitigation strategy. Data/Model Injecting controlled inputs or modifications degrades model accuracy, as shown by high gradient deviations. Strong aggregation methods like trimmed mean or median can reduce attack success and accuracy loss [151,152]. Backdoored attacks on subtle triggers like urban sensor data patterns are mitigated by anomaly detection and norm clipping. Evaluation compares backdoor and clean accuracy [153]. To prevent the byzantine attack induced by inconsistent/outlier updates by faulty/malicious clients, Krum/Multi-Krum algorithms or reputation scoring track convergence rate and final accuracy [154]. Sybil assaults magnify the terrible features of fake identities with equivalent upgrades in safety, identity verification, fake detection trust rating, and model stability [155]. Multiple attackers coordinate the poisoning or backdoor, causing anomalous patterns that clustering-based detection and secure validation cannot identify [156].
8 Challenges and Open Issues in Federated Deep Learning
Despite great advancements, FDL in intelligent urban ecosystems faces ongoing challenges that hinder adoption and optimal performance. These shortcomings are caused by the inherent heterogeneity in urban data and devices, resource constraints typical for the IoT, growing concerns about security, and the high requirements for sustainability imposed by managed and large-scale environments under regulation. Fig. 11 outlines the main challenges inherent to FL that include data heterogeneity, communication inefficiency, privacy apprehension, and impediments to model convergence. The ramifications of the adversities on the holistic performance of FDL systems are also enlightened.
Figure 11: Federated learning challenges.
8.1 Statistical Heterogeneity (Non-IID)
Statistical heterogeneity-commonly known as non-IID or non-independent and identically distributed data—is ubiquitous where local data sets vary in their distributions of features, label skews, or sample sizes. In urban environments, for instance, heterogeneous neighborhood traffic patterns, heterogeneous building energy usage profiles, and heterogeneous patient demographics or disease prevalence across hospitals engender pronounced non-IID conditions. An approach is outlined for the construction of a non-IID. datasets from a single source collection, in the context of advancing machine learning classification in FL frameworks. By carefully splitting the data into subsets that each reflect different distributional features, it’s possible to get a systematic improvement of training regimes and hence allow for a more nuanced model development [157]. Batch Normalization (BN) layers are useful for faster convergence and superior performance for decentralized peer-to-peer (P2P) learning frameworks that are faced with non-IID data distributions. Empirical studies run on Reddit and Stack Overflow datasets show that the introduction of BN with early stopping criteria results in a significant improvement of the decentralized learning efficacy with non-identically independent distribution [158]. FL well handles the heterogeneity caused by non-IID client data distributions and therefore solves the problem that such disparate data distributions create for the learning process. In order to reduce the negative effects of non-IID data on communication efficiency, model convergence, and prediction accuracy, FL employs techniques such as data partitioning, selective client sampling, or secure aggregation [159]. This heterogeneity leads to client drift, a biased global model, and slow convergence, resulting in larger gaps in performance for privacy-sensitive applications.
8.2 System Heterogeneity + Resource Constraints
System heterogeneity presents substantial differences in computing, memory and battery endurance among IoT devices, thereby creating stragglers, as well as frequent dropouts and naturally unbalanced participation patterns in FL deployments involving edge sensors in smart homes or wearables in healthcare. FL is a solution that combines artificial intelligence and wireless communication and collaboratively trains models without any local data residency. The inherent heterogeneity engendered by disparate device capabilities, non-identically independently distributed data, and participant behavior adds to the training process complication. This review discusses these heterogeneities, explains their consequences, describes the challenges and opportunities of FL and future research paths, including a simulation through the LEAF framework [160]. Heterogeneous Federated Learning (HFL) solves the many challenges related to data heterogeneity, model disparity, network variability, and device heterogeneity in large industrial deployments [161].
The DFL-MKF framework, a decentralized federated learning architecture designed for cognitive IoT ecosystems and specifically tailored to address the susceptibilities that central server failures can impose, the prohibitive communication overhead that may be incurred, and the pervasive heterogeneity of cognitive IoT ecosystems, is a direct counter to the issues that can be introduced during the deployment of cognitive IoT ecosystems. By making the edge devices assimilate knowledge from their neighboring peers with dynamic aggregation of information in them, DFL-MKF not only improves the fidelity of the locally trained model but also makes communication more efficient, thus outperforming the existing methodologies of image classification [162]. Normalizing and de-normalizing the data at the network and transport layer of the IoT using IPv6, User Datagram Protocol (UDP) is a key approach to managing the heterogeneity of the IoT devices. This approach encourages interoperability between equipment from different vendors and thus allows for flexible and scalable automation. In practice, the combination of Contiki OS and Cooja simulator is often used by scholars to prototype and test such solutions [163]. Resource constraints compound these challenges, especially in battery-powered urban IoT scenarios, where prolonged local training cycles consume energy resources of devices, thus resulting in their decreased overall availability.
8.3 Communication Efficiency and Latency
In the context of vast federations of large numbers of urban networked environments, the inclusion of thousands to millions of devices leads to the emergence of critical bottlenecks, including iterative model update exchanges, significant bandwidth consumption, and increased latency in time-critical operations, including real-time traffic governance and remote situational awareness. FL presents an appealing way to address the great heterogeneity of the edge computing environments and the randomness of network connectivity. By providing edge devices with the capability to train self-distilled neural networks that can be dynamically pruned to support a range of model topologies and unpredictable network conditions, FL significantly improves both resilience and communication efficiency, which is beyond the state of the art [164]. Indeed, over-the-air computation protocols and intrinsic network variability plot to increasing these delays further.
Large-scale federations in an urban network consist of thousands, even millions, of devices, thus creating bottlenecks based on the high exchange of model updates, strong bandwidth requirements, and latency problems inherent to time-critical tasks such as the orchestration of real-time traffic flow or remote surveillance. Moreover, over-the-air computation combined with network heterogeneity inherent to the networks further exacerbates these delays.
8.4 Fairness, Explainability, and Compliance
Non-ignorance of this in data—non-IID data leads to further exacerbation of inherent biases, causing non-equitable results between disparate demographic groups or geographical regions; opacity (Black box?) model of DL Since DL models are often built as black boxes, it hinders the faith people have in very regulated sectors; compliance with GDPR and HIPAA compliance—In decentralized training environments there needs to be implementation of auditable procedures. Fig. 12 captures the complex trade-offs that are embedded with FL and outlines the balance between model accuracy, communication costs, privacy protection and computational costs in decentralized learning environments.
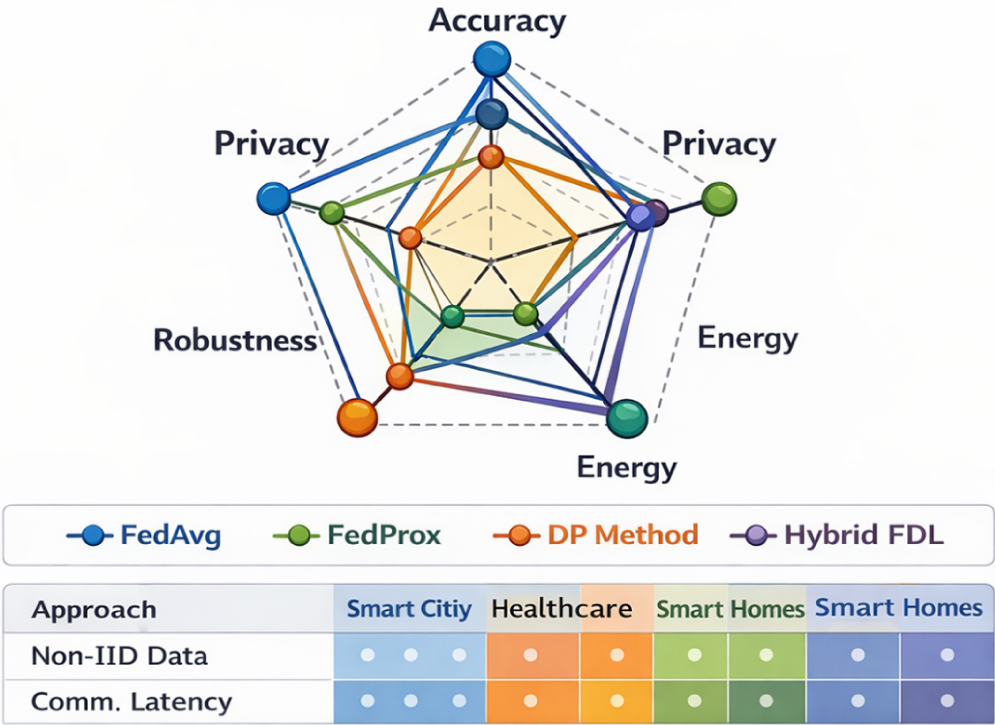
Figure 12: Multi-dimensional trade-off visualization.
Fig. 12 demonstrates multi-dimensional performance trade-offs of four FDL algorithms, such that FedAvg, FedProx DP Method, and Hybrid FDL, using 5 axes, like, Accuracy, Privacy, Robustness, Energy (higher scores indicate better efficiency/lower consumption) and Communication. Hybrid FDL has the largest and most balanced polygonal area which leads to good privacy and robustness score, accurate results, and energy/communication efficiency. FedAvg puts accuracy and communication efficiency first but neglects privacy and robustness. FedProx is better than FedAvg in terms of robustness and moderate privacy, and accuracy suffers. The DP method has the highest level of privacy protection and the lowest level of accuracy, energy efficiency and communication performance. Along with the radar chart is a small dot-rating table assessing algorithms in terms of Non-IID Data handling and the Communication Latency for three urban domains (smart city, healthcare, smart homes). Hybrids and FedProx are better in non-IID resilience but communication latency performance in different domains. Overall, visualization makes the trade-offs inherent in FDL approaches very clear and puts hybrid methods in the most versatile and promising position for hybrid approaches that are required for real-world urban applications that require a well-balanced combination of privacy, robustness, and practical efficiency.
Fig. 13 shows a heatmap of the severity of challenges faced in different domains, which gives an impression of the different degrees of difficulty in dealing with specific problems in each domain in the context of federate learning.
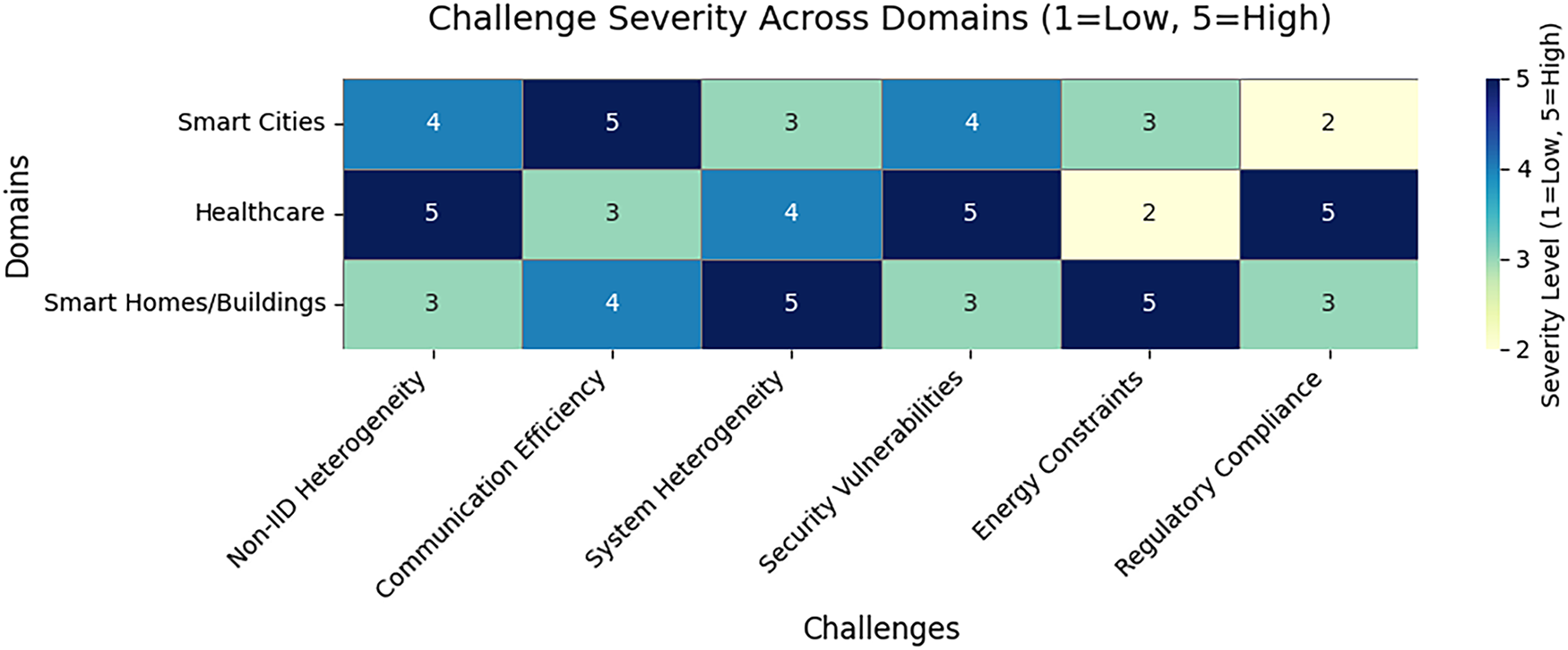
Figure 13: Heatmap of challenge severity across domains.
The heatmap of the figure rates six challenges of FDL (1 = low to 5 = high severity) in three urban domains. Healthcare has the largest overall severity (especially security = 5, non-IID = 5, regulation = 5), smart homes/buildings have the most trouble with system heterogeneity (5) and energy (5), while smart Cities struggle with communication efficiency (5) and non-IID (4). Visualization brings out domain-specific priorities as it is regulatory/security focus for healthcare, device/energy for buildings/homes, and scale-related communication/heterogeneity for cities.
8.5 Energy Consumption and Sustainability
The process of training models on distributed, often battery constrained devices lead to increased energy consumption and carbon emissions, thereby going against the goals of green city development and in the case of large federations of cities, inefficient scheduling amplifies these effects. Federated machine learning, commonly called Fed ML, allows for the joint realization of predictive models by using the locally stored data, thus avoiding the need to send raw data sets, thus respecting strict privacy requirements—especially important in the fields of the IoT and mobile applications ecosystems. In the particular case of power-constrained devices, this lecture attempts to outline some of the existing methodological frameworks while to outline cogent recommendations on how to streamline the training efficacy and to reduce energy usage [165].
Latency, energy utilization, and device battery limits must be optimized in federated edge learning (FEEL) deployed across UAV-enabled IoT networks in next-generation 5G/6G infrastructures. Deep deterministic policy gradient (DDPG) technique to allocate computing resources and wireless bandwidth simultaneously. This solution lowers system cost and ensures that edge devices can complete FEEL iterations despite battery limits, outperforming conventional methods [166]. FL supports the collaborative model training across edge devices while maintaining privacy, yet there are some inherent challenges that hamper its performance and adoption, such as client heterogeneity and varying energy consumption. EAFL (Energy-Aware FL), the selection mechanism that prioritizes clients according to their energy reserves, improves the accuracy by up to 85%, and reduces the drop outs of clients by up to 2.45, thus enhancing the system efficiency [167]. In this paper, we introduce an optimized multi-UAV assisted FL framework used for AIoT applications in which UAV serves local and global aggregation tasks and addresses the constraints associated with limited resources and finite battery capacity on board the UAVs. To address these issues, the framework also includes an online resource allocation (ORA) algorithm and a deep reinforcement learning (DRL) scheme, which together minimize the training latency and the energy consumption of the training process. Simulation results show that the performance is significantly improved in a variety of system configurations [168]. FL in the urban application context is confronted with challenges such as statistical and system heterogeneity, communication inefficiencies, security vulnerabilities, fairness issues, and energy consumption, and several solutions have been proposed to address these problems illustrated in Table 10.
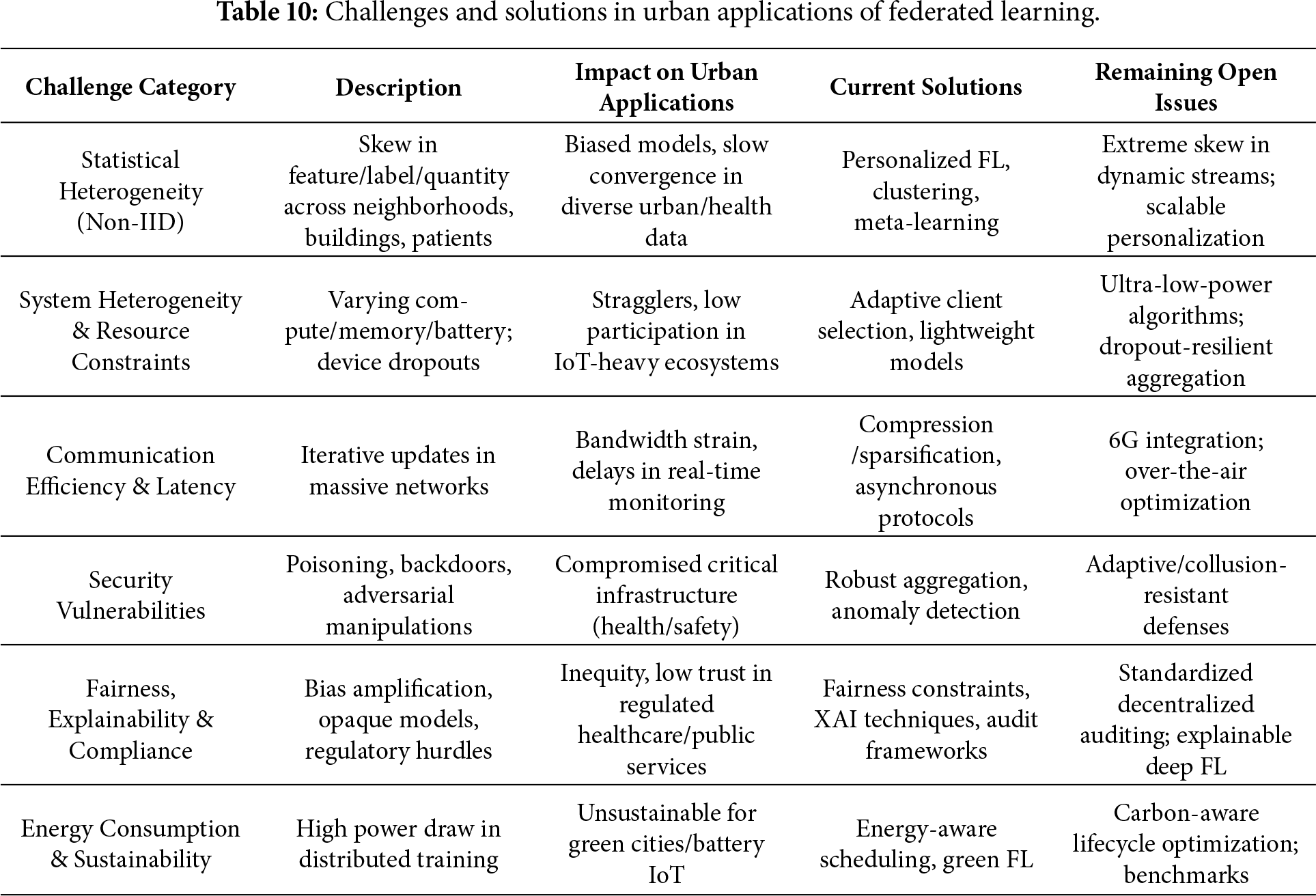
Table 10 presents difficulties concerning the application of FL in urban settings, such as heterogeneity in the statistics and system, communication inefficiencies, security concerns, fairness and explainability, as well as high energy usage. Proposed solutions such as personalized FL, adaptive client selection, compression techniques, robust aggregation, and energy-aware scheduling help solve these problems, but challenges such as dynamic skew, ultra-low-power algorithms, collusion-resistant defenses, and sustainability benchmarks are left open for another development.
FDL Privatization Privacy (RQ1) As privacy (P) gets better, so does the convergence in FDL based on clustering schemes pFedMe but at the cost of model privacy such that non-IID heterogeneity, RQ2.
The literature review comprises 25 or more works, accounting for approximately 20% of the corpus.
• DP-augmented clustering (PrivClust) Local DP (1/ = 1) on client embeddings; achieves 10-percent convergence rate at provable privacy on the urban EHR non-IID data.
• Meta-learning hybrids (Per-FedAvg): Individualized models through meta-gradients + DP; half leakage 30% with 5% cost to accuracy.
• Aggregation resistant to drift/poisoning (FedDC): FedProx + SCAFFOLD + SecAgg are faster on non-IID with hidden updates.
Solutions are mapped in Table 9 cluster collusion and dynamic ε-budgets have gaps. Hybrids can be used to optimize the deployment in cities.
8.6 Linking Challenges to Prior Literature
Section 8 challenges link directly to Sections 3–7 literature:
• Statistical heterogeneity (non-IID): The FedProx, FedNova, and SCAFFOLD techniques and the hybrid FedDC/ProxYogi are specifically aimed at convergence delays and client drift. Also provided in Table 2 and Section 3.4 is a summary of personalized FL and clustering/personalization. However, it has not yet been answered whether non-IID streams of large cities can be personalized at scale or whether extreme and dynamic streams such as seasonal traffic or changing patient cohorts, can be served.
• Heterogeneity in systems and communication efficiency: Sections 4.1 and 4.3 represent the minimization of bandwidth and straggler effects by using compression, sparsification, Qsparse-local-SGD and partial participation, and asynchronous protocols and hierarchical/edge-fog-cloud architectures. Nevertheless, the concept of ultra-low power scheduling of battery IoT and 6G-native over-the-air optimization in the city scale are under-researched.
• Security and robustness: In Section 7 and Table 7, five main types of attacks (poisoning, backdoor, Byzantine, Sybil, collusion) are matched to the five different types of defenses (trimmed mean/median, Krum/Multi-Krum, RFOut-1d, and group-wise robust aggregation). The problem of collusion-resistant and adaptive defenses in realistic urban threat models has not been addressed primarily.
• Fairness, explainability, and compliance: Table 8 and Section 8.4 discuss the issues of bias, the performance difference in demographics, and explainability, respectively. Section 5 (Table 5) shows the domain-specific privacy stacks, which are required to follow the GDPR/HIPAA regulations. Despite this, cross-city/cross-hospital FDL and auditable privacy budget accounting lack standardized measures of fairness.
• Energy and sustainability: The energy-conscious scheduling and green FL models in Sections 4.3 and 8.5 in big city IoT federations. Carbon-aware orchestration (Table 9) and life-cycle carbon accounting are open research problems.
This cross-linking makes Section 8, an synthesis of surveyed solutions (Sections 3–7, Tables 2–5, 7 and 8) and the explanation of what sub-problems are having concrete methods and what are parts of the open research roadmap.
8.7 Urban-Specific Challenge: Drifting Concept Temporal in FDL
FedProx and SCAFFOLD can solve the non-IID heterogeneity that exists in the proximal terms and control variates to address the static non-IID heterogeneity (RQ2). Nevertheless, the temporal concept drift that presupposes the changes of the urban data distributions with time is not yet studied in a significant manner (RQ3). This difficulty is particularly acute in dynamic city eco systems, relationships that are subject to alteration due to external events, seasonality or policy interventions.
• Traffic Flow Prediction: The effect of the remote working on rush-hours in large cities had irreversible outcomes, with the peak loads decreasing by approximately 25%–35% during the post-COVID-19 pandemic. Conventional FedAvg models, which were trained on 2019 data, miss by 15%–25% on 2022+ streams when not adapted, since spatial-temporal GNNs cannot model sudden policy-induced changes.
• Smart Building Energy: Seasonal HVAC demand varies considerably leading to a change in occupancy-based loads of 30%–40% in summer and 20%–28% in winter. The result of this shift is 20%–28% prediction errors of non-intrusive load monitoring (NILM). FedProx can support initial heterogeneity, but it cannot keep track of behavioral changes that are monthly.
• Healthcare Imaging: BraTS MRI tumor segmentation models degrade by 12%–18% when the patient demographics vary across networks such as when geriatric urban populations are considered.
9 Deployment, Governance, and MLOps for FDL
Real-world deployment of FDL in intelligent urban ecosystems requires robust MLOps pipelines, governance frameworks, and operational practices to ensure reliability, compliance, and sustainability at scale. Unlike centralized ML, FDL introduces distributed complexities in lifecycle management, privacy budgeting, secure operations, and data governance, particularly in regulated domains like healthcare and smart cities.
The operational lifecycle of federated distribution learning is a generalization of the traditional MLOps framework in the distributed manner that includes model versioning, which keeps track of global and local versions of a model across clients, rollout and rollback strategies, with phased deployment and fallback strategies, monitoring, which captures performance metrics per client and at the global scale, and drift detection, which detects statistical or conceptual drift in an urban data stream. Continuous monitoring identifies breakdowns caused by shifts other than IID or device failures, which results in retraining cycles. Tools such as Flower, FedML and OpenFL support federated pipelines, with integrated versioning and drift-alert capabilities.
FL is a decentralized paradigm of machine learning, which is made specifically to protect privacy by avoiding transmission of raw data to a central server. To overcome the inherent intricacies involved when the practical implementation of FL is overcome, we introduce FedOps, an integrative platform that augments MLOps tailored for FL initiatives, overseeing the entire life cycle all the while preserving the integrity of its core processes. FedOps includes a separate utility, chunk-bench, which is used for the systematic evaluation of client heterogeneity, which has resulted in significant decreases in communication cost-to-accuracy ratios by 13% to 43% and time-to-accuracy measurements by 20% to 68%, remarkably improving both computational and communicative efficiencies within FL projects [169].
In the process of deploying DP, a careful accounting of the privacy budget, i.e., tracking cumulative values of e, d over successive training iterations, will be crucial to maintain the prescribed privacy guarantees. Such accounting mechanisms, such as the Rényi DP, or the framework of moments accountant, direct budget consumption on a client level, and aggregate level; thus, governance protocols intervene to terminate training process once allocated privacy budget is exhausted. In the case of urban deployments, a dynamic allocation strategy adjusts the magnitude of injected noise as a function of the sensitivity profile of each client, thereby providing a higher level of protection for especially sensitive data, such as healthcare data.
SecAgg and cryptographic protocols must be carefully key managed-that is, generated, distributed, rotated and revoked-over heterogeneous clients. Auditing logs allow locating of correct aggregation without exposing individual updates [24]. Hardware-based solutions are used to improve key security, while lifecycle-in-edge devices can be handled using protocols, such as trust zone or SGX.
The FDL requires robust data governance frameworks to simultaneously address consent, i.e., dynamic opt-in/out mechanisms for devices, ownership, with well-articulated policies for local data retention, accountability, traceable contributions without compromising data privacy, and cross-organization agreements, legally binding contracts for collaboration within healthcare consortia or city-wide partnerships. FL allows to decentralize the training, thus addressing the privacy concerns and the cost of transferring the data; however, incorporating FL into existing MLOps pipelines presents significant challenges related to model versioning, synchronization over time, and scalability. In response, the adoption of a centralized model—management paradigm, specifically designed for FL, with the goal of stitching together seamlessly with industrial MLOps workflows, without requiring an overhaul of the entire infrastructural architecture, enabled by the agile and open-source platform MLflow. This architecture provides a lot of freedom to incorporate Transfer Learning (TL) and other advanced techniques in a future work, and also maximizes the resource efficiency [170]. Fig. 14 gives a holistic picture of the FDL-MLOps lifecycle with the following sequential stages that cover the development, deployment and continuous maintenance of FDL systems, with a strong focus on the pillars of continuous integration, strict monitoring and iterative optimization in a decentralized operational setting.
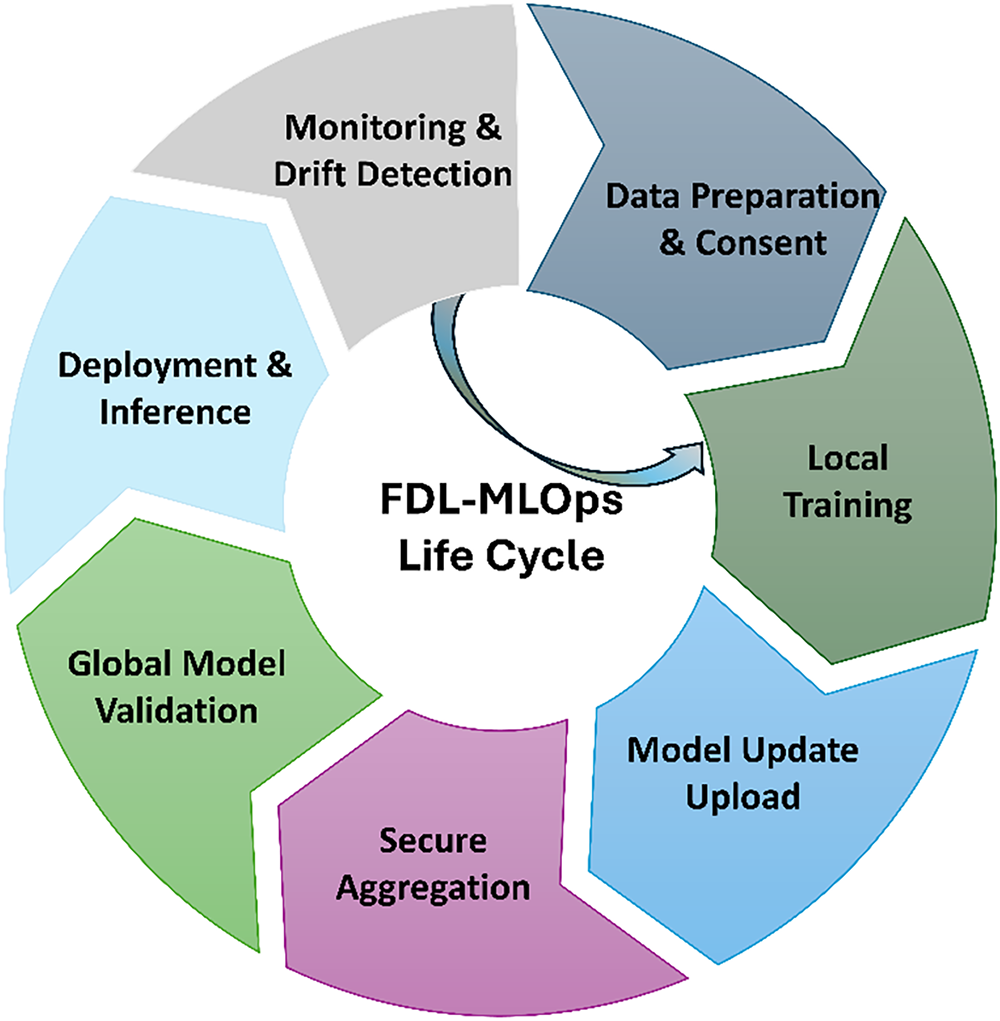
Figure 14: FDL-MLOps lifecycle.
With the circular FDL-MLOps lifetime for FDL deployments for ongoing privacy-preserving operation for urban clients. Beginning with data preparation & consent, participants are ensuring data preparation & explicit consent locally. Local training involves training the model of devices using private data. model update upload sends updates followed by secure aggregation that combines contributions without disclosing data. The result of this aggregation is sent for quality verification to global model validation. Deployment and inference on client for real-world application comes after model validation. Performance drift or data drift is detected through continuous monitoring and drift checks, leading to the need for retraining. This cyclic framework brings the principles of MLOps and FDL processes such as safe aggregation and consent management to make the model lifecycle dependable, consistent and flexible for privacy-sensitive urban applications, such as healthcare and smart cities.
FDL has emerged as a transformative framework for privacy-preserving collaborative intelligence in intelligent urban ecosystems. It addresses the competing requirements of privacy and data intensity inherent in deep neural networks when implemented in distributed IoT environments within smart cities, residential and commercial buildings, and healthcare systems. FDL mitigates weaknesses in centralized training, including data breaches and non-compliance with GDPR and HIPAA requirements, by retaining raw data locally on client devices and transmitting only model changes. Furthermore, it employs information from a variety of sources, including traffic sensors, building meters, wearables, and EHR.
The most recent advancements in the field, documented between 2018 and 2025, demonstrate progress in fundamental algorithms (e.g., FedProx, SCAFFOLD), which alleviate non-IID drift and enhance convergence by 15%–20% in artificial urban environments; system architectures such as hierarchical edge-fog-cloud topologies, which decrease communication latency by 30%–50% in large-scale IoT federations; and privacy methodologies like hybrid privacy solutions, which integrate DP and secure aggregation to provide privacy assurances. Domain-specific applications have illustrated the concrete efficacy of FDL: Spatio-temporal graph neural networks in smart cities for traffic prediction on benchmarks like METR-LA; federated CNN/U-Net variants for medical imaging attain on multi-institutional BraTS data; and LSTMs for NILM in smart buildings.
Despite these achievements, FDL is not yet prepared for extensive application in urban environments due to several limitations and unresolved issues. Statistical and systemic heterogeneity pose significant challenges, as non-IID distributions among neighborhoods or patient groups result in client drift and a drop in accuracy in extreme instances, as highlighted in systematic reviews. Customized clustering may mitigate certain issues; nonetheless, it incurs an additional computational expense.
Communication efficiency continues to be a constraint on scaling, for instance. Communication efficiency continues to be a constraint for scalability, such as with millions of devices. Urban networks squander an enormous quantity of bandwidth (about 100 times more than centralized networks prior to compression), however employing sparsity and quantization can mitigate this waste at the expense of a minor increase in error. Security vulnerabilities Adversarial assaults, including poisoning and backdoor exploits, can diminish the accuracy of global aggregation by 30%–50% due to security flaws. Consequently, robust aggregation techniques like Krum, which exhibit success rates below 10% and entail increased delay, are essential. The absence of fairness and explainability exacerbates the bias in non-IID urban statistics, leading to inequality, such as performance disparities of 15%–25% among demographic groups. To adhere to legislative mandates, privacy budgets must be auditable, a challenge under existing accounting procedures. Energy sustainability is becoming vital in the realm of green cities; training for battery-powered devices consumes 2 to 5 times more energy per epoch than centralized installations, underscoring the significance of carbon-aware job scheduling. Deployment and MLOps limitations, including fragmented toolchains and absence of standardized testbeds, impede real-world implementations, with just a few pilot projects, such as Singapore’s traffic monitoring and multi-hospital imaging, demonstrating viability.
These restrictions expose substantial deficiencies in research, encompassing the management of extensive unpredictability at scale, the adaptive counteraction of adversaries, the formulation of metrics for justice and explainability, and the execution of lifecycle carbon accounting. Nonetheless, the impetus of forward momentum, represented by novel connections with 6G/edge intelligence, privacy-conscious large language models, verified robustness, positions FDL to surmount these obstacles by fostering interdisciplinary collaboration to establish standards, pragmatic benchmarks, and ethical governance frameworks. By 2035, surmounting these obstacles will allow FDL’s full potential to be actualized, fostering equitable, resilient, and sustainable urban intelligence, hence advancing smarter cities and an environment that harmonizes innovation with societal trust.
In the process of maturation of DL for intelligent urban ecosystems, it becomes imperative for future research to confront the conjoined conundrums of integrating all the nascent technologies, of pursuing personalization and robustness, imperatives of sustainability, challenges of standardization, and exigencies of ethical conduct, all in the service of the deployment of scalability and trustworthiness. In Fig. 15 we explore the prospective paths of FL, tracing some emergent trends, prospective research directions, and technological developments that may help shape the path of FDL in a variety of industrial settings.
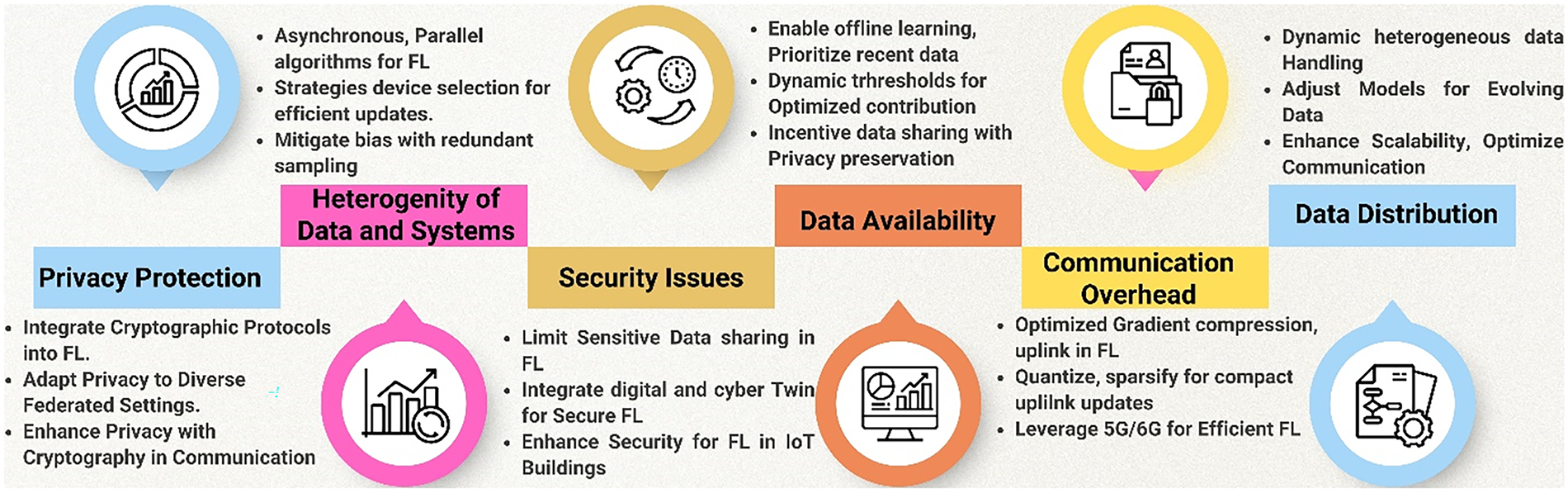
Figure 15: Federated learning future directions.
The convergence of the FDL with the upcoming 6G networks is bound to open the doors to ultra-low-latency, massive connectivity for the IoT in urban environments, which will provide over-the-air aggregation capabilities and dynamic client orchestration in smart cities, as defined in the latest research. Advances in edge intelligence including device inference and hierarchical fog processing are promising to reallocate computational resources as near to the point of data origin in municipal buildings, healthcare wearables, to attenuate latency and protect privacy, a proposition substantiated. By adding privacy-centered modalities to large language models, the research community is providing a natural language interface for urban services, from asking cities for services to aiding in finding health insights, using the federated fine tuning and prompt-based learning methodologies to maintain data locality.
In a personalized paradigm of FDL subject to privacy regulations, models would be adapted to local urban dynamics neighborhood traffic flows or phenotypic profiles of the patients using meta-learning frameworks or unsupervised clustering techniques, while at the same time respecting the DP guarantees. On the contrary, certified robustness aims at providing mathematically certified defenses against adversarial perturbations; this task is carried out by verification methodologies and robust aggregation schemes backed by theoretical performance bounds. Such an approach is indispensable for the integrity of safety critical systems in healthcare and public infrastructure.
A sophisticated paradigm-carbon-aware training optimizes scheduling according to temporal availability of renewable energies and dynamically changing carbon intensity of electric grid while energy constrained algorithms are designed to prioritize low power devices in eco-centric urban landscape. Future work will include full lifecycle carbon accounting as well as the development of green benchmarks for urban IoT federations.
Uncharted evaluation protocols as well as realistic federated testbeds, simulating urban non-IID data, heterogeneity of devices and device drift, are indispensable for reproducible comparisons. Large-scale real deployments in the form of multi-city consortia or hospital networks will be used to validate these frameworks, based on open-source platforms such as Flower and FedML.
Addressing fairness through bias mitigation in heterogeneous urban datasets combined with explainability mechanisms such as those based on interpretable surrogate models or attention visualizations, and supported by robust urban governance frameworks, will together lead to public trust in AI-Driven Qcities and healthcare. As shown in the research roadmap below Fig. 16, for the period between 2026 and 2035, the roadmap for the FDL research is well defined, with a list of key milestones, emerging trends and areas of focus in FDL and associated technologies to set the path for the next decade.
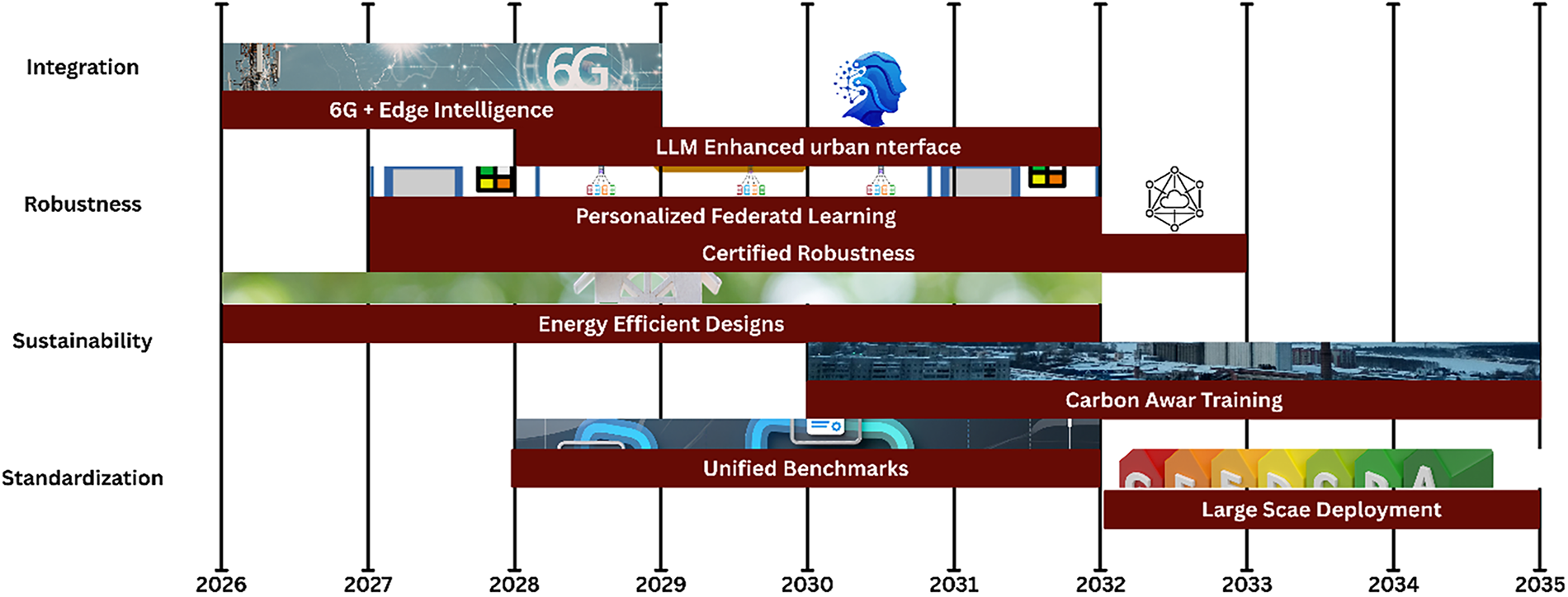
Figure 16: Research roadmap timeline (2026–2035).
Fig. 16 timeline for research objectives on FDL enhancements to the urban ecosystem from 2026 to 2035. The goals are divided into four tracks with overlapping goals. Integration will begin in 2026 with 6G + Edge Intelligence for ultra-low latency networking. Large Language Model (LLM)enhanced Urban Interfaces will take place in 2028 for natural language service that is privacy-conscious. The Robustness track begins the Personalized FL in 2027 and Certified Robustness in 2029. Sustainability includes things such as Energy-Efficient Designs (2026), Carbon-Aware Training (2030). Standardization means that there will be Unified Benchmarks in 2028 and Large-Scale Deployments by 2032. The timeline shows that FDL systems will slowly become more mature, resilient and good for the environment by 2035.
Table 11 outlines the prospective trajectories in FDL, listing the motivating factors that are set to drive future advances, the consequential effects of such advancements, and the first principles that will catalyze future advances in the field.
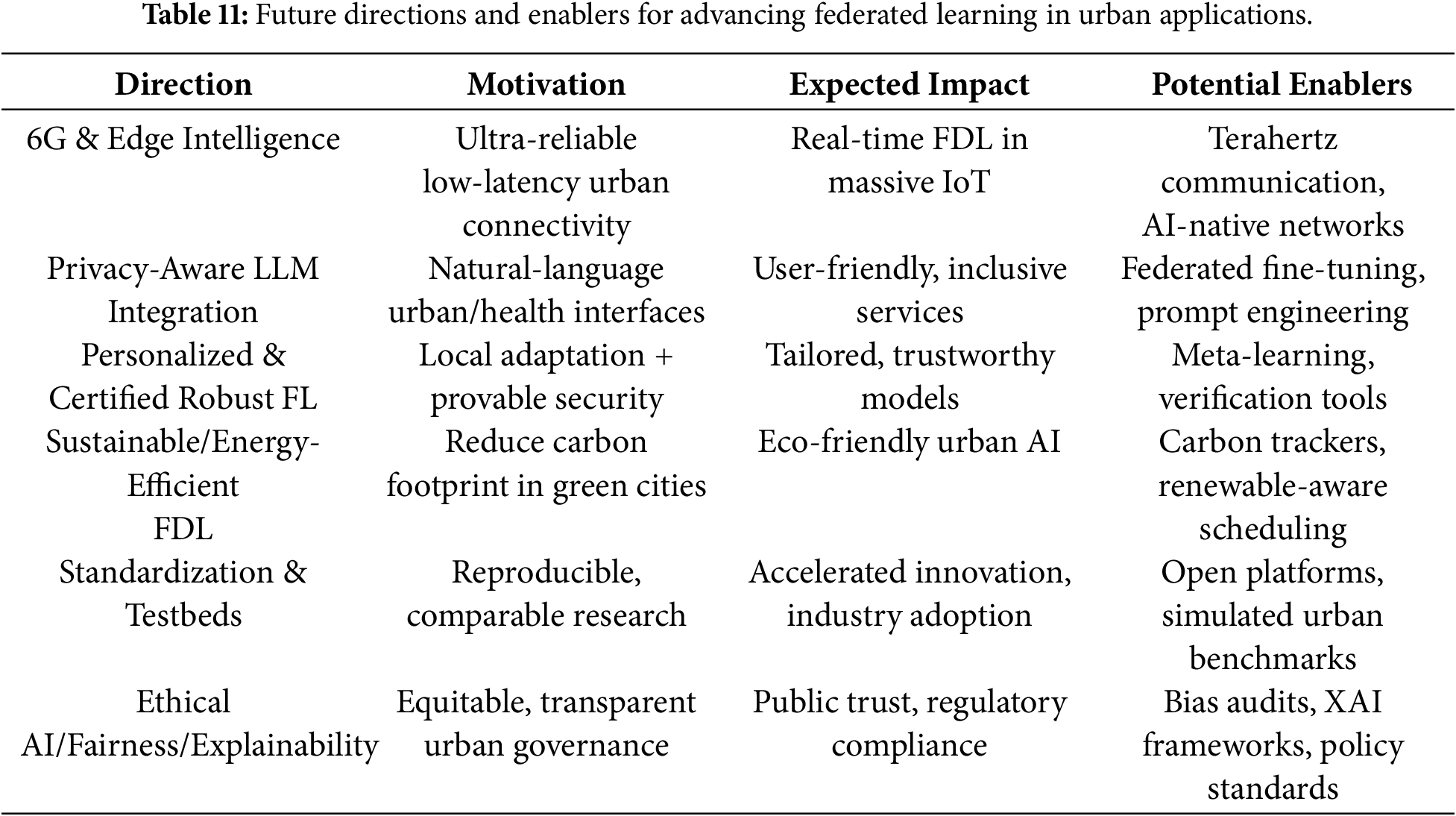
Table 11 presents future directions of advancing FL in urban applications with a focus on aspects such as 6G & Edge Intelligence for low latency connectivity in IoT, privacy-aware natural language interfaces for user-friendly services and personalized, secure FL models. It also focuses on sustainable energy-efficient FL to mitigate carbon footprints in green cities, the need for standardization and testbeds for reproducible research, and ethical AI practices to ensure fairness, explainability, and public trust. These advancements are supported by enablers such as AI-native networks, federated fine-tuning, meta-learning, carbon trackers, open platforms and XAI frameworks with the goal of accelerating innovation and making sure to comply with regulations.
FDL has become an irreplaceable paradigm of privacy-preserving intelligence in interconnected urban ecosystems, the de facto channel to bridge the enormous possibilities of deep neural networks and the urgent demands of data sovereignty, regulatory compliance and scalability. In this review, we have outlined how the advancements in the field for the years 2018–2025 have made it possible to provide substantive applications in the smart city, residential and commercial buildings, IoT, and healthcare. These applications range from spatio-temporal traffic forecasting to energy efficient building management, secure, cross-institutional medical imaging and remote patient monitoring. By maintaining data locality while leveraging collaborative training approaches, FDL helps overcome the most basic shortcomings of centralized systems and is better suited to the requirements of heterogeneous, privacy-conscious urban environments. Nevertheless, despite all of this, there are still several formidable challenges. Chief among them is statistical and system heterogeneity, communication bottlenecks, security vulnerabilities, deficiencies in fairness and explainability, and concerns regarding energy sustainability issues that must be surmounted to achieve widespread and trustworthy deployment. Progress in layered privacy mechanisms, robust security defenses, and domain-specific MLOps frameworks offers a solid foundation, but the road ahead requires concerted efforts in standardization, realistic benchmarking, ethical governance, and seamless integration with emerging technologies such as 6G, edge intelligence, and privacy-aware large language models. Looking at 2035, FDL has transformative potential for resilient, equitable, and sustainable urban intelligence. Realizing this vision will require ongoing interdisciplinary collaboration between researchers, policy makers, industry stakeholders, and urban planners to develop certified, robust, carbon-aware aware and publicly accountable federated systems. Ultimately, FDL not only protects individual privacy but also presents an opportunity to harness collective intelligence, hence opening the doors to smarter, safer, and more inclusive cities on a global scale.
Acknowledgement: Not applicable.
Funding Statement: The authors received no specific funding for this study.
Author Contributions: Muhammad Adnan Tariq and Sunawar Khan perform the Original—Writing Part, Software, and Methodology; Tariq Shahzad and Tehseen Mazhar perform Rewriting, investigation, Design Methodology, and Conceptualization; Tariq Shahzad, Habib Hamam and Sahar Arooj perform the Related Work Part and Manage Results and Discussions; Tehseen Mazhar, Muhammad Adnan Khan and Habib Hamam perform Related Work Part and Manage Results and Discussion; Muhammad Adnan Khan, Sunawar Khan and Khmaies Ouahada perform Rewriting, Design Methodology, and Visualization; Tariq Shahzad and Muhammad Adnan Tariq performs Rewriting, Design Methodology, and Visualization. All authors reviewed and approved the final version of the manuscript.
Availability of Data and Materials: All data used in this review is included within the article itself.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest.
Supplementary Materials: The supplementary material is available online at https://www.techscience.com/doi/10.32604/cmes.2026.078672/s1.
References
1. Iji M, Gurung R. IoT connections forecast to, GSMA Intelligence. 2030 [cited 2026 Jan 4]. Available from: https://www.gsmaintelligence.com/research/iot-connections-forecast-to-2030. [Google Scholar]
2. Ragab M, Ashary EB, Alghamdi BM, Aboalela R, Alsaadi N, Maghrabi LA, et al. Advanced artificial intelligence with federated learning framework for privacy-preserving cyberthreat detection in IoT-assisted sustainable smart cities. Sci Rep. 2025;15(1):4470. doi:10.1038/s41598-025-88843-2. [Google Scholar] [PubMed] [CrossRef]
3. Farooq MS, Saleem M, Khan MA, Khan MF, Siddiqui SY, Aslam MS, et al. Interpretable federated learning model for cyber intrusion detection in smart cities with privacy-preserving feature selection. Comput Mater Contin. 2025;85(3):5183–206. doi:10.32604/cmc.2025.069641. [Google Scholar] [CrossRef]
4. Rojek I, Mikołajewski D, Galas K, Piszcz A. Advanced deep learning algorithms for energy optimization of smart cities. Energies. 2025;18(2):407. doi:10.3390/en18020407. [Google Scholar] [CrossRef]
5. Hurrah NN, Khan E, Parah SA. Smart ecosystems for sustainable development: opportunities, challenges, and solutions. In: Intelligent multimedia signal processing for smart ecosystems. Cham, Switzerland: Springer International Publishing; 2023. p. 3–28. doi:10.1007/978-3-031-34873-0_1. [Google Scholar] [CrossRef]
6. Balakrishnan TS, Banerjee JS. Scalable and intelligent smart cities: integrating deep learning with IoT for urban optimization. SGS Eng Sci. 2025;1(5). [cited 2026 Jan 1]. Available from: https://spast.org/techrep/article/view/5784. [Google Scholar]
7. Gedawy HK, Harras KA, Bui T, Tanveer T. RealFL: a realistic platform for federated learning. In: Proceedings of the Int’l ACM Conference on Modeling Analysis and Simulation of Wireless and Mobile Systems; 2023 Oct 30–Nov 3; Montreal, QC, Canada. p. 313–7. doi:10.1145/3616388.3623799. [Google Scholar] [CrossRef]
8. Ghadi YY, Mazhar T, Shah SFA, Haq I, Ahmad W, Ouahada K, et al. Integration of federated learning with IoT for smart cities applications, challenges, and solutions. PeerJ Comput Sci. 2023;9(5):e1657. doi:10.7717/peerj-cs.1657. [Google Scholar] [PubMed] [CrossRef]
9. Al-Sarawi S, Anbar M, Abdullah R, Al Hawari AB. Internet of Things market analysis forecasts, 2020–2030. In: Proceedings of the 2020 Fourth World Conference on Smart Trends in Systems, Security and Sustainability (WorldS4); 2020 Jul 27–28; London, UK. p. 449–53. doi:10.1109/worlds450073.2020.9210375. [Google Scholar] [CrossRef]
10. Ritchie H, Samborska V, Roser M. Urbanization. [cited 2026 Jan 4]. Available from: https://ourworldindata.org/urbanization. [Google Scholar]
11. World Bank Group. Rural population (% of total population). [cited 2026 Jan 4]. Available from: https://data.worldbank.org/indicator/SP.RUR.TOTL.ZS. [Google Scholar]
12. Wang Q, Li L. The effects of population aging, life expectancy, unemployment rate, population density, per capita GDP, urbanization on per capita carbon emissions. Sustain Prod Consum. 2021;28(1):760–74. doi:10.1016/j.spc.2021.06.029. [Google Scholar] [CrossRef]
13. Jiang D. The construction of smart city information system based on the Internet of Things and cloud computing. Comput Commun. 2020;150(1):158–66. doi:10.1016/j.comcom.2019.10.035. [Google Scholar] [CrossRef]
14. Soomro K, Bhutta MNM, Khan Z, Tahir MA. Smart city big data analytics: an advanced review. WIREs Data Min & Knowl. 2019;9(5):e1319. doi:10.1002/widm.1319. [Google Scholar] [CrossRef]
15. Bhattacharya S, Somayaji SRK, Gadekallu TR, Alazab M, Maddikunta PKR. A review on deep learning for future smart cities. Internet Technol Lett. 2022;5(1):e187. doi:10.1002/itl2.187. [Google Scholar] [CrossRef]
16. Javadzadeh G, Rahmani AM. Fog computing applications in smart cities: a systematic survey. Wirel Netw. 2020;26(2):1433–57. doi:10.1007/s11276-019-02208-y. [Google Scholar] [CrossRef]
17. Vincent S, Reddy SS, Jain T, Suryawanshi VM, Madan R, Mohanty A, et al. Smart city traffic management system using IoT. In: Tiwari M, Singh G, Ismail T, Singh N, editors. Proceedings of the International Conference on Sensors and Microsystems (ICSM 2024). Lecture notes in electrical engineering. Vol. 1381, Singapore: Springer; 2025. p. 47–53. doi:10.1007/978-981-96-3644-0_6. [Google Scholar] [CrossRef]
18. Javed AR, Faheem R, Asim M, Baker T, Beg MO. A smartphone sensors-based personalized human activity recognition system for sustainable smart cities. Sustain Cities Soc. 2021;71(5):102970. doi:10.1016/j.scs.2021.102970. [Google Scholar] [CrossRef]
19. Alazab M, Lakshmanna K, Thippa Reddy G, Pham QV, Reddy Maddikunta PK. Multi-objective cluster head selection using fitness averaged rider optimization algorithm for IoT networks in smart cities. Sustain Energy Technol Assess. 2021;43(1):100973. doi:10.1016/j.seta.2020.100973. [Google Scholar] [CrossRef]
20. Silva BN, Khan M, Jung C, Seo J, Muhammad D, Han J, et al. Urban planning and smart city decision management empowered by real-time data processing using big data analytics. Sensors. 2018;18(9):2994. doi:10.3390/s18092994. [Google Scholar] [PubMed] [CrossRef]
21. Alamir RH, Noor A, Almukhalfi H, Almukhlifi R, Noor TH. SecFedDNN: a secure federated deep learning framework for edge–cloud environments. Systems. 2025;13(6):463. doi:10.3390/systems13060463. [Google Scholar] [CrossRef]
22. Yurdem B, Kuzlu M, Gullu MK, Catak FO, Tabassum M. Federated learning: overview, strategies, applications, tools and future directions. Heliyon. 2024;10(19):e38137. doi:10.1016/j.heliyon.2024.e38137. [Google Scholar] [PubMed] [CrossRef]
23. Zhang Y, Zeng D, Luo J, Xu Z, King I. A survey of trustworthy federated learning with perspectives on security, robustness and privacy. In: Proceedings of the Companion Proceedings of the ACM Web Conference 2023; 2023 Apr 30–May 4; Austin, TX, USA. p. 1167–76. doi:10.1145/3543873.3587681. [Google Scholar] [CrossRef]
24. Jiang Y, Ma B, Wang X, Yu G, Yu P, Wang Z, et al. Blockchained federated learning for Internet of Things: a comprehensive survey. ACM Comput Surv. 2024;56(10):1–37. doi:10.1145/3659099. [Google Scholar] [CrossRef]
25. Ge L, Li H, Wang X, Wang Z. A review of secure federated learning: privacy leakage threats, protection technologies, challenges and future directions. Neurocomputing. 2023;561(12):126897. doi:10.1016/j.neucom.2023.126897. [Google Scholar] [CrossRef]
26. Wang X, Li J, Ding X, Zhang H, Sun L. A survey of differential privacy techniques for federated learning. IEEE Access. 2025;13(1):6539–55. doi:10.1109/access.2024.3523909. [Google Scholar] [CrossRef]
27. Alterkawi L, Dib FK. Federated learning for smart cities: a thematic review of challenges and approaches. Future Internet. 2025;17(12):545. doi:10.3390/fi17120545. [Google Scholar] [CrossRef]
28. Deepa N, Pham QV, Nguyen DC, Bhattacharya S, Prabadevi B, Gadekallu TR, et al. A survey on blockchain for big data: approaches, opportunities, and future directions. Future Gener Comput Syst. 2022;131:209–26. doi:10.1016/j.future.2022.01.017. [Google Scholar] [CrossRef]
29. Li T, Sahu AK, Talwalkar A, Smith V. Federated learning: challenges, methods, and future directions. IEEE Signal Process Mag. 2020;37(3):50–60. doi:10.1109/msp.2020.2975749. [Google Scholar] [CrossRef]
30. Alazab M, Swarna Priya RM, Parimala M, Maddikunta PKR, Gadekallu TR, Pham QV. Federated learning for cybersecurity: concepts, challenges, and future directions. IEEE Trans Ind Inf. 2022;18(5):3501–9. doi:10.1109/tii.2021.3119038. [Google Scholar] [CrossRef]
31. Khan LU, Saad W, Han Z, Hossain E, Hong CS. Federated learning for Internet of Things: recent advances, taxonomy, and open challenges. IEEE Commun Surv Tutorials. 2021;23(3):1759–99. doi:10.1109/comst.2021.3090430. [Google Scholar] [CrossRef]
32. Imteaj A, Thakker U, Wang S, Li J, Amini MH. A survey on federated learning for resource-constrained IoT devices. IEEE Internet Things J. 2022;9(1):1–24. doi:10.1109/jiot.2021.3095077. [Google Scholar] [CrossRef]
33. Kulkarni V, Kulkarni M, Pant A. Survey of personalization techniques for federated learning. In: Proceedings of the 2020 Fourth World Conference on Smart Trends in Systems, Security and Sustainability (WorldS4); 2020 Jul 27–28; London, UK. p. 794–7. doi:10.1109/worlds450073.2020.9210355. [Google Scholar] [CrossRef]
34. Jawadur Rahman KM, Ahmed F, Akhter N, Hasan M, Amin R, Aziz KE, et al. Challenges, applications and design aspects of federated learning: a survey. IEEE Access. 2021;9:124682–700. doi:10.1109/access.2021.3111118. [Google Scholar] [CrossRef]
35. Yin X, Zhu Y, Hu J. A comprehensive survey of privacy-preserving federated learning: a taxonomy, review, and future directions. ACM Comput Surv. 2022;54(6):1–36. doi:10.1145/3460427. [Google Scholar] [CrossRef]
36. Lim WY, Luong NC, Hoang DT, Jiao Y, Liang YC, Yang Q, et al. Federated learning in mobile edge networks: a comprehensive survey. IEEE Commun Surv Tutor. 2020;22(3):2031–63. doi:10.1007/978-3-031-07838-5_1. [Google Scholar] [CrossRef]
37. Li Q, Wen Z, Wu Z, Hu S, Wang N, Li Y, et al. A survey on federated learning systems: vision, hype and reality for data privacy and protection. IEEE Trans Knowl Data Eng. 2023;35(4):3347–66. doi:10.1109/tkde.2021.3124599. [Google Scholar] [CrossRef]
38. Jiang JC, Kantarci B, Oktug S, Soyata T. Federated learning in smart city sensing: challenges and opportunities. Sensors. 2020;20(21):6230. doi:10.3390/s20216230. [Google Scholar] [PubMed] [CrossRef]
39. Brik B, Ksentini A, Bouaziz M. Federated learning for UAVs-enabled wireless networks: use cases, challenges, and open problems. IEEE Access. 2020;8:53841–9. doi:10.1109/ACCESS.2020.2981430. [Google Scholar] [CrossRef]
40. Nguyen DC, Pham QV, Pathirana PN, Ding M, Seneviratne A, Lin Z, et al. Federated learning for smart healthcare: a survey. ACM Comput Surv. 2023;55(3):1–37. doi:10.1145/3501296. [Google Scholar] [CrossRef]
41. Ramu SP, Boopalan P, Pham QV, Maddikunta PKR, Huynh-The T, Alazab M, et al. Federated learning enabled digital twins for smart cities: concepts, recent advances, and future directions. Sustain Cities Soc. 2022;79(1):103663. doi:10.1016/j.scs.2021.103663. [Google Scholar] [CrossRef]
42. Zheng Z, Zhou Y, Sun Y, Wang Z, Liu B, Li K. Applications of federated learning in smart cities: recent advances, taxonomy, and open challenges. Connect Sci. 2022;34(1):1–28. doi:10.1080/09540091.2021.1936455. [Google Scholar] [CrossRef]
43. Alam T, Gupta R. Federated learning and its role in the privacy preservation of IoT devices. Future Internet. 2022;14(9):246. doi:10.3390/fi14090246. [Google Scholar] [CrossRef]
44. Issa W, Moustafa N, Turnbull B, Sohrabi N, Tari Z. Blockchain-based federated learning for securing Internet of Things: a comprehensive survey. ACM Comput Surv. 2023;55(9):1–43. doi:10.1145/3560816. [Google Scholar] [CrossRef]
45. Javed AR, Hassan MA, Shahzad F, Ahmed W, Singh S, Baker T, et al. Integration of blockchain technology and federated learning in vehicular (IoT) networks: a comprehensive survey. Sensors. 2022;22(12):4394. doi:10.3390/s22124394. [Google Scholar] [PubMed] [CrossRef]
46. Hoofnagle CJ, van der Sloot B, Borgesius FZ. The European Union general data protection regulation: what it is and what it means. Inf Commun Technol Law. 2019;28(1):65–98. doi:10.1080/13600834.2019.1573501. [Google Scholar] [CrossRef]
47. Hartsfield SB. Artificial intelligence and health privacy. New Orleans, LA, USA: Loyola Law Review; 2024. p. 1–6. [Google Scholar]
48. Almutairi S, Barnawi A. Federated learning vulnerabilities, threats and defenses: a systematic review and future directions. Internet Things. 2023;24(3):100947. doi:10.1016/j.iot.2023.100947. [Google Scholar] [CrossRef]
49. Hameed RT, Mohamad OA. Federated learning in IoT: a survey on distributed decision making. Babylon J Internet Things. 2023;2023:1–7. doi:10.58496/bjiot/2023/001. [Google Scholar] [CrossRef]
50. Al-Huthaifi R, Li T, Huang W, Gu J, Li C. Federated learning in smart cities: privacy and security survey. Inf Sci. 2023;632:833–57. doi:10.1016/j.ins.2023.03.033. [Google Scholar] [CrossRef]
51. Berkani MRA, Chouchane A, Himeur Y, Ouamane A, Miniaoui S, Atalla S, et al. Advances in federated learning: applications and challenges in smart building environments and beyond. Computers. 2025;14(4):124. doi:10.3390/computers14040124. [Google Scholar] [CrossRef]
52. Tabrizchi H, Aghasi A. Introduction to federated learning. In: Federated cyber intelligence. Cham, Switzerland: Springer Nature; 2025. p. 1–11. doi:10.1007/978-3-031-86592-3_1. [Google Scholar] [CrossRef]
53. Alsharif MH, Kannadasan R, Wei W, Nisar KS, Abdel-Aty AH. A contemporary survey of recent advances in federated learning: taxonomies, applications, and challenges. Internet Things. 2024;27:101251. doi:10.1016/j.iot.2024.101251. [Google Scholar] [CrossRef]
54. Martínez Beltrán ET, Pérez MQ, Sánchez PMS, Bernal SL, Bovet G, Pérez MG, et al. Decentralized federated learning: fundamentals, state of the art, frameworks, trends, and challenges. IEEE Commun Surv Tutorials. 2023;25(4):2983–3013. doi:10.1109/comst.2023.3315746. [Google Scholar] [CrossRef]
55. Shen S, Zhu T, Wu D, Wang W, Zhou W. From distributed machine learning to federated learning: in the view of data privacy and security. Concurr Comput Pract Exp. 2022;34(16):e6002. doi:10.1002/cpe.6002. [Google Scholar] [CrossRef]
56. Lyu L, Yu H, Ma X, Chen C, Sun L, Zhao J, et al. Privacy and robustness in federated learning: attacks and defenses. IEEE Trans Neural Netw Learning Syst. 2024;35(7):8726–46. doi:10.1109/tnnls.2022.3216981. [Google Scholar] [PubMed] [CrossRef]
57. Wang J, Liu Q, Liang H, Joshi G, Poor HV. Tackling the objective inconsistency problem in heterogeneous federated optimization. Adv Neural Inf Process Syst. 2020;33:7611–23. [Google Scholar]
58. Sattler F, Wiedemann S, Muller KR, Samek W. Robust and communication-efficient federated learning from non-i.i.d. data. IEEE Trans Neural Netw Learning Syst. 2020;31(9):3400–13. doi:10.1109/tnnls.2019.2944481. [Google Scholar] [PubMed] [CrossRef]
59. Sun T, Li D, Wang B. Decentralized federated averaging. IEEE Trans Pattern Anal Mach Intell. 2023;45(4):4289–301. doi:10.1109/tpami.2022.3196503. [Google Scholar] [PubMed] [CrossRef]
60. Albarqouni S, Andreux M, Avestimehr S, Ayed SS, Bellet A, Cyffers E, et al. FLamby: datasets and benchmarks for cross-silo federated learning in realistic healthcare settings. In: Proceedings of the Advances in Neural Information Processing Systems 35; 2022 Nov 28–Dec 9; New Orleans, LA, USA. p. 5315–34. doi:10.52202/068431-0384. [Google Scholar] [CrossRef]
61. Li T, Sahu AK, Zaheer M, Sanjabi M, Talwalkar A, Smith V. Federated optimization in heterogeneous networks. Proc Mach Learn Syst. 2020;2:429–50. [Google Scholar]
62. Su L, Xu J, Yang P. A non-parametric view of FedAvg and FedProx: beyond stationary points. J Mach Learn Res. 2023;24(203):1–48. [Google Scholar]
63. Karimireddy SP, Kale S, Mohri M, Reddi S, Stich S, Suresh AT. Scaffold: stochastic controlled averaging for federated learning. In: Proceedings of the 37th International Conference on Machine Learning; 2020 Jul 13–18; Virtual. [Google Scholar]
64. Liu T, Di B, An P, Song L. Privacy-preserving incentive mechanism design for federated cloud-edge learning. IEEE Trans Netw Sci Eng. 2021;8(3):2588–600. doi:10.1109/tnse.2021.3100096. [Google Scholar] [CrossRef]
65. Gao L, Fu H, Li L, Chen Y, Xu M, Xu CZ. FedDC: federated learning with non-IID data via local drift decoupling and correction. In: Proceedings of the 2022 IEEE/CVF Conference on Computer Vision and Pattern Recognition (CVPR); 2022 Jun 18–24; New Orleans, LA, USA. p. 10102–11. doi:10.1109/CVPR52688.2022.00987. [Google Scholar] [CrossRef]
66. Nguyen H, Warrier H, Gupta Y. A novel approach for federated learning with non-IID data. In: Proceedings of the 2022 9th International Conference on Soft Computing & Machine Intelligence (ISCMI); 2022 Nov 26–27; Toronto, ON, Canada. p. 62–7. doi:10.1109/ISCMI56532.2022.10068456. [Google Scholar] [CrossRef]
67. Dang TK, Lan X, Weng J, Feng M. Federated learning for electronic health records. ACM Trans Intell Syst Technol. 2022;13(5):1–17. doi:10.1145/3514500. [Google Scholar] [CrossRef]
68. Djenouri Y, Michalak TP, Lin JC. Federated deep learning for smart city edge-based applications. Future Gener Comput Syst. 2023;147(2):350–9. doi:10.1016/j.future.2023.04.034. [Google Scholar] [CrossRef]
69. Al-Selwi SM, Hassan MF, Abdulkadir SJ, Muneer A, Sumiea EH, Alqushaibi A, et al. RNN-LSTM: from applications to modeling techniques and beyond—Systematic review. J King Saud Univ Comput Inf Sci. 2024;36(5):102068. doi:10.1016/j.jksuci.2024.102068. [Google Scholar] [CrossRef]
70. Su L, Zuo X, Li R, Wang X, Zhao H, Huang B. A systematic review for transformer-based long-term series forecasting. Artif Intell Rev. 2025;58(3):80. doi:10.1007/s10462-024-11044-2. [Google Scholar] [CrossRef]
71. Tian L, Rao W, Zhao K, Vo HT. Quantifying the non-isomorphism of global urban road networks using GNNs and graph kernels. Sci Rep. 2025;15(1):6485. doi:10.1038/s41598-025-90839-x. [Google Scholar] [PubMed] [CrossRef]
72. Yang Q, Liu Y, Cheng Y, Kang Y, Chen T, Yu H. Horizontal federated learning. In: Federated Learning. Cham: Springer International Publishing; 2020. p. 49–67. doi:10.1007/978-3-031-01585-4_4. [Google Scholar] [CrossRef]
73. Saadati Y, Imteaj A, Amini MH. Vertical federated learning: principles, applications, and future frontiers. In: Distributed machine learning and computing. Cham, Switzerland: Springer International Publishing; 2024. p. 111–27. doi:10.1007/978-3-031-57567-9_5. [Google Scholar] [CrossRef]
74. Liu Y, Kang Y, Zou T, Pu Y, He Y, Ye X, et al. Vertical federated learning: concepts, advances, and challenges. IEEE Trans Knowl Data Eng. 2024;36(7):3615–34. doi:10.1109/tkde.2024.3352628. [Google Scholar] [CrossRef]
75. Drosatos G, Efraimidis PS, Arampatzis A. Federated and transfer learning applications. Appl Sci. 2023;13(21):11722. doi:10.3390/app132111722. [Google Scholar] [CrossRef]
76. Guo W, Zhuang F, Zhang X, Tong Y, Dong J. A comprehensive survey of federated transfer learning: challenges, methods and applications. Front Comput Sci. 2024;18(6):186356. doi:10.1007/s11704-024-40065-x. [Google Scholar] [CrossRef]
77. Gao D, Chen D, Li Z, Xie Y, Pan X, Li Y, et al. FS-real: a real-world cross-device federated learning platform. Proc VLDB Endow. 2023;16(12):4046–9. doi:10.14778/3611540.3611617. [Google Scholar] [CrossRef]
78. Hasan MM, Sultana T, Hossain MD, Mandal AK, Ngo TT, Lee GW, et al. The journey to cloud as a continuum: opportunities, challenges, and research directions. ICT Express. 2025;11(4):666–89. doi:10.1016/j.icte.2025.04.015. [Google Scholar] [CrossRef]
79. Hurbungs V, Bassoo V, Fowdur TP. Fog and edge computing: concepts, tools and focus areas. Int J Inf Tecnol. 2021;13(2):511–22. doi:10.1007/s41870-020-00588-5. [Google Scholar] [CrossRef]
80. Muneeb M, Ko KM, Park YH. A fog computing architecture with multi-layer for computing-intensive IoT applications. Appl Sci. 2021;11(24):11585. doi:10.3390/app112411585. [Google Scholar] [CrossRef]
81. Qi P, Chiaro D, Guzzo A, Ianni M, Fortino G, Piccialli F. Model aggregation techniques in federated learning: a comprehensive survey. Future Gener Comput Syst. 2024;150:272–93. doi:10.1016/j.future.2023.09.008. [Google Scholar] [CrossRef]
82. Rauniyar A, Hagos DH, Jha D, Håkegård JE, Bagci U, Rawat DB, et al. Federated learning for medical applications: a taxonomy, current trends, challenges, and future research directions. IEEE Internet Things J. 2024;11(5):7374–98. doi:10.1109/JIOT.2023.3329061. [Google Scholar] [CrossRef]
83. Wu J, Dong F, Leung H, Zhu Z, Zhou J, Drew S. Topology-aware federated learning in edge computing: a comprehensive survey. ACM Comput Surv. 2024;56(10):1–41. doi:10.1145/3659205. [Google Scholar] [CrossRef]
84. Kanellopoulos D, Sharma VK, Panagiotakopoulos T, Kameas A. Networking architectures and protocols for IoT applications in smart cities: recent developments and perspectives. Electronics. 2023;12(11):2490. doi:10.3390/electronics12112490. [Google Scholar] [CrossRef]
85. Tracey D. A holistic architecture using peer to peer (P2P) protocols for the Internet of Things and wireless sensor networks [Ph.D. thesis]. Cork, Republic of Ireland: University College Cork; 2020. [Google Scholar]
86. Nguyen DC, Ding M, Pathirana PN, Seneviratne A, Li J, Poor HV. Federated learning for Internet of Things: a comprehensive survey. IEEE Commun Surv Tutorials. 2021;23(3):1622–58. doi:10.1109/comst.2021.3075439. [Google Scholar] [CrossRef]
87. Liu B, Jiang W, Zhao S, Jin H, He B. GradSA: gradient sparsification and accumulation for communication-efficient distributed deep learning. In: Green, pervasive, and cloud computing. Cham, Switzerland: Springer International Publishing; 2020. p. 77–91. doi:10.1007/978-3-030-64243-3_6. [Google Scholar] [CrossRef]
88. Lee S, Zhang T, Prakash S, Niu Y, Avestimehr S. Embracing federated learning: enabling weak client participation via partial model training. IEEE Trans Mobile Comput. 2024;23(12):11133–43. doi:10.1109/tmc.2024.3392212. [Google Scholar] [CrossRef]
89. Al-Taie RR, Hesselbach X. Cost-effective power management for smart homes: innovative scheduling techniques and integrating battery optimization in 6G networks. Electronics. 2024;13(21):4231. doi:10.3390/electronics13214231. [Google Scholar] [CrossRef]
90. Wu P, Zhang Z, Peng X, Wang R. Deep learning solutions for smart city challenges in urban development. Sci Rep. 2024;14(1):5176. doi:10.1038/s41598-024-55928-3. [Google Scholar] [PubMed] [CrossRef]
91. Tomar I, Sreedevi I, Pandey N. State-of-art review of traffic light synchronization for intelligent vehicles: current status, challenges, and emerging trends. Electronics. 2022;11(3):465. doi:10.3390/electronics11030465. [Google Scholar] [CrossRef]
92. Kapoor A, Kumar D. Enhancing smart cities with federated learning: a framework for secure, scalable, and intelligent urban sensing systems. IEEE Internet Things Mag. 2026;9(1):96–103. doi:10.1109/MIOT.2025.3581347. [Google Scholar] [CrossRef]
93. Zhou S, Shekhar S, Chhokra A, Dubey A, Gokhale A. Drift detection and adaptation for federated learning in IoT with adaptive device management. In: Proceedings of the 2024 IEEE International Conference on Big Data (BigData); 2024 Dec 15–18; Washington, DC, USA. p. 8088–97. doi:10.1109/bigdata62323.2024.10826139. [Google Scholar] [CrossRef]
94. Casado FE, Lema D, Criado MF, Iglesias R, Regueiro CV, Barro S. Concept drift detection and adaptation for federated and continual learning. Multimed Tools Appl. 2022;81(3):3397–419. doi:10.1007/s11042-021-11219-x. [Google Scholar] [CrossRef]
95. Rodríguez-Barroso N, Jiménez-López D, Luzón MV, Herrera F, Martínez-Cámara E. Survey on federated learning threats: concepts, taxonomy on attacks and defences, experimental study and challenges. Inf Fusion. 2023;90(6):148–73. doi:10.1016/j.inffus.2022.09.011. [Google Scholar] [CrossRef]
96. Xu T, Liu C, Zhang K, Zhang J. Membership inference attacks against medical databases. In: Neural information processing. Singapore: Springer Nature; 2023. p. 15–25. doi:10.1007/978-981-99-8138-0_2. [Google Scholar] [CrossRef]
97. Ding X, Liu Z, You X, Li X, Vasilakos AV. Improved gradient leakage attack against compressed gradients in federated learning. Neurocomputing. 2024;608(3):128349. doi:10.1016/j.neucom.2024.128349. [Google Scholar] [CrossRef]
98. Aljanabi M, Omran AH, Mijwil MM, Abotaleb M, El-kenawy ES, Mohammed SY, et al. Data poisoning: issues, challenges, and needs. In: Proceedings of the 7th IET Smart Cities Symposium (SCS 2023); 2023 Dec 3–5; Bahrain. p. 359–63. [Google Scholar]
99. Yu P, Wei Y, Ma L, Wang B, Yung EHK, Chen Y. Urbanization and the urban critical zone. Earth Crit Zone. 2024;1(1):100011. doi:10.1016/j.ecz.2024.100011. [Google Scholar] [CrossRef]
100. Wang Y, Wang Q, Zhao L, Wang C. Differential privacy in deep learning: privacy and beyond. Future Gener Comput Syst. 2023;148(3):408–24. doi:10.1016/j.future.2023.06.010. [Google Scholar] [CrossRef]
101. Wu X, Chen Y, Yu H, Yang Z. Privacy-preserving federated learning based on noise addition. Expert Syst Appl. 2025;267:126228. doi:10.1016/j.eswa.2024.126228. [Google Scholar] [CrossRef]
102. Ngo KH, Östman J, Durisi G, Graell i Amat A. Secure aggregation is not private against membership inference attacks. In: Machine learning and knowledge discovery in databases. Cham, Switzerland: Springer Nature; 2024. p. 180–98. doi:10.1007/978-3-031-70365-2_11. [Google Scholar] [CrossRef]
103. Zhou S, Wang L, Chen L, Wang Y, Yuan K. Group verifiable secure aggregate federated learning based on secret sharing. Sci Rep. 2025;15(1):9712. doi:10.1038/s41598-025-94478-0. [Google Scholar] [PubMed] [CrossRef]
104. Fazli Khojir H, Alhadidi D, Rouhani S, Mohammed N. FedShare: secure aggregation based on additive secret sharing in federated learning. In: Proceedings of the Proceedings of the 27th International Database Engineered Applications Symposium; 2023 May 5–7; Heraklion, Crete Greece. p. 25–33. doi:10.1145/3589462.3589504. [Google Scholar] [CrossRef]
105. Liu W, You L, Shao Y, Shen X, Hu G, Shi J, et al. From accuracy to approximation: a survey on approximate homomorphic encryption and its applications. Comput Sci Rev. 2025;55(11):100689. doi:10.1016/j.cosrev.2024.100689. [Google Scholar] [CrossRef]
106. Sele E, Catak FO, Seo J, Kuzlu M. Secure federated learning via neural cryptography with homomorphic operations. Discov Artif Intell. 2025;5(1):392. doi:10.1007/s44163-025-00630-0. [Google Scholar] [CrossRef]
107. Ménétrey J, Göttel C, Khurshid A, Pasin M, Felber P, Schiavoni V, et al. Attestation mechanisms for trusted execution environments demystified. In: Distributed applications and interoperable systems. Cham, Switzerland: Springer International Publishing; 2022. p. 95–113. doi:10.1007/978-3-031-16092-9_7. [Google Scholar] [CrossRef]
108. Coppolino L, D’Antonio S, Mazzeo G, Romano L. An experimental evaluation of TEE technology: benchmarking transparent approaches based on SGX, SEV, and TDX. Comput Secur. 2025;154:104457. doi:10.1016/j.cose.2025.104457. [Google Scholar] [CrossRef]
109. Bi L, Muazu T, Samuel O. IoT: a decentralized trust management system using blockchain-empowered federated learning. Sustainability. 2023;15(1):374. doi:10.3390/su15010374. [Google Scholar] [CrossRef]
110. Shukla S, Rajkumar S, Sinha A, Esha M, Elango K, Sampath V. Federated learning with differential privacy for breast cancer diagnosis enabling secure data sharing and model integrity. Sci Rep. 2025;15(1):13061. doi:10.1038/s41598-025-95858-2. [Google Scholar] [PubMed] [CrossRef]
111. Ni Z, Zhou Q. Differential privacy in federated learning: an evolutionary game analysis. Appl Sci. 2025;15(6):2914. doi:10.3390/app15062914. [Google Scholar] [CrossRef]
112. Kumar M, Sethi M, Rani S, Sah DK, AlQahtani SA, Al-Rakhami MS. Secure data aggregation based on end-to-end homomorphic encryption in IoT-based wireless sensor networks. Sensors. 2023;23(13):6181. doi:10.3390/s23136181. [Google Scholar] [PubMed] [CrossRef]
113. Said G, Ghani A, Ullah A, Azeem M, Bilal M, Kwak KS. Light-weight secure aggregated data sharing in IoT-enabled wireless sensor networks. IEEE Access. 2022;10(1):33571–85. doi:10.1109/access.2022.3160231. [Google Scholar] [CrossRef]
114. Zhu B, Niu L. A privacy-preserving federated learning scheme with homomorphic encryption and edge computing. Alex Eng J. 2025;118:11–20. doi:10.1016/j.aej.2024.12.070. [Google Scholar] [CrossRef]
115. Alqazzaz A. Federated learning with homomorphic encryption: a privacy-preserving solution for smart cities. Int J Comput Intell Syst. 2025;18(1):304. doi:10.1007/s44196-025-00829-0. [Google Scholar] [CrossRef]
116. Park J, Lim H. Privacy-preserving federated learning using homomorphic encryption. Appl Sci. 2022;12(2):734. doi:10.3390/app12020734. [Google Scholar] [CrossRef]
117. Chen C, Liu J, Tan H, Li X, Wang KI, Li P, et al. Trustworthy federated learning: privacy, security, and beyond. Knowl Inf Syst. 2025;67(3):2321–56. doi:10.1007/s10115-024-02285-2. [Google Scholar] [CrossRef]
118. Ngoupayou Limbepe Z, Gai K, Yu J. Blockchain-based privacy-enhancing federated learning in smart healthcare: a survey. Blockchains. 2025;3(1):1. doi:10.3390/blockchains3010001. [Google Scholar] [CrossRef]
119. Liu Z, Guo J, Yang W, Fan J, Lam KY, Zhao J. Privacy-preserving aggregation in federated learning: a survey. IEEE Trans Big Data. 2024:1–20. doi:10.1109/tbdata.2022.3190835. [Google Scholar] [CrossRef]
120. Jagarlamudi GK, Yazdinejad A, Parizi RM, Pouriyeh S. Exploring privacy measurement in federated learning. J Supercomput. 2024;80(8):10511–51. doi:10.1007/s11227-023-05846-4. [Google Scholar] [CrossRef]
121. Gu X, Sabrina F, Fan Z, Sohail S. A review of privacy enhancement methods for federated learning in healthcare systems. Int J Environ Res Public Health. 2023;20(15):6539. doi:10.3390/ijerph20156539. [Google Scholar] [PubMed] [CrossRef]
122. Ibrahim Khalaf O, Ashokkumar SR, Algburi S, Anupallavi S, Selvaraj D, Sharif MS, et al. Federated learning with hybrid differential privacy for secure and reliable cross-IoT platform knowledge sharing. Secur Priv. 2024;7(3):e374. doi:10.1002/spy2.374. [Google Scholar] [CrossRef]
123. Moussaoui JE, Kmiti M, El Gholami K, Maleh Y. A systematic review on hybrid AI models integrating machine learning and federated learning. J Cybersecur Priv. 2025;5(3):41. doi:10.3390/jcp5030041. [Google Scholar] [CrossRef]
124. Mahesh Babu K, Nagendranath MS. Privacy preservation in distributed healthcare systems: a review of differential privacy, homomorphic encryption, and hybrid approaches. In: Proceedings of the 2025 4th International Conference on Innovative Mechanisms for Industry Applications (ICIMIA); 2025 Sep 3–5; Tirupur, India. p. 976–83. doi:10.1109/icimia67127.2025.11200738. [Google Scholar] [CrossRef]
125. Zhang L, Xu J, Vijayakumar P, Sharma PK, Ghosh U. Homomorphic encryption-based privacy-preserving federated learning in IoT-enabled healthcare system. IEEE Trans Netw Sci Eng. 2023;10(5):2864–80. doi:10.1109/tnse.2022.3185327. [Google Scholar] [CrossRef]
126. Jarour A. Empowering smart cities through federated learning an overview. In: Proceedings of the 2024 28th International Conference on System Theory, Control and Computing (ICSTCC); 2024 Oct 10–12; Sinaia, Romania. p. 551–7. doi:10.1109/icstcc62912.2024.10744688. [Google Scholar] [CrossRef]
127. Mystakidis A, Koukaras P, Tjortjis C. Advances in traffic congestion prediction: an overview of emerging techniques and methods. Smart Cities. 2025;8(1):25. doi:10.3390/smartcities8010025. [Google Scholar] [CrossRef]
128. Miller T, Durlik I, Kostecka E, Puszkarek A. Federated learning for environmental monitoring: a review of applications, challenges, and future directions. Appl Sci. 2025;15(23):12685. doi:10.3390/app152312685. [Google Scholar] [CrossRef]
129. Kulkarni V, Lakshmi AS, Lakshmi CBN, Panneerselvam S, Kanan M, Flah A, et al. Air quality decentralized forecasting: integrating IoT and federated learning for enhanced urban environmental monitoring. Eng Technol Appl Sci Res. 2024;14(4):16077–82. doi:10.48084/etasr.7869. [Google Scholar] [CrossRef]
130. Mishra V. Federated learning for enhancing cybersecurity resilience in distributed energy systems. In: Proceedings of the Abu Dhabi International Petroleum Exhibition and Conference (ADIPEC); 2025 Nov 3–6; Abu Dhabi, United Arab Emirates. doi:10.2118/229330-ms. [Google Scholar] [CrossRef]
131. Shrestha R, Mohammadi M, Sinaei S, Salcines A, Pampliega D, Clemente R, et al. Anomaly detection based on LSTM and autoencoders using federated learning in smart electric grid. J Parallel Distrib Comput. 2024;193(13):104951. doi:10.1016/j.jpdc.2024.104951. [Google Scholar] [CrossRef]
132. Karamat F, Rahman AU, Saqia B, Zafar A, Ali Khan W. Addressing privacy-preservation in healthcare using federated learning: a survey. Artif Intell Appl. 2025;1–12. doi:10.47852/bonviewaia52023976. [Google Scholar] [CrossRef]
133. Guan H, Yap PT, Bozoki A, Liu M. Federated learning for medical image analysis: a survey. Pattern Recognit. 2024;151:110424. doi:10.1016/j.patcog.2024.110424. [Google Scholar] [PubMed] [CrossRef]
134. Sandhu SS, Gorji HT, Tavakolian P, Tavakolian K, Akhbardeh A. Medical imaging applications of federated learning. Diagnostics. 2023;13(19):3140. doi:10.3390/diagnostics13193140. [Google Scholar] [PubMed] [CrossRef]
135. Abbas SR, Abbas Z, Zahir A, Lee SW. Federated learning in smart healthcare: a comprehensive review on privacy, security, and predictive analytics with IoT integration. Healthcare. 2024;12(24):2587. doi:10.3390/healthcare12242587. [Google Scholar] [PubMed] [CrossRef]
136. Naithani K, Raiwani YP, Tiwari S, Chauhan AS. Artificial intelligence techniques based on federated learning in smart healthcare. In: Federated learning for smart communication using IoT application. Boca Raton, FL, USA: Chapman and Hall/CRC; 2024. p. 81–108. doi:10.1201/9781003489368-5. [Google Scholar] [CrossRef]
137. Ma J, Zhao J, Hou Y. Spatial-temporal transformer networks for traffic flow forecasting using a pre-trained language model. Sensors. 2024;24(17):5502. doi:10.3390/s24175502. [Google Scholar] [PubMed] [CrossRef]
138. Ashburn M. Advances of deep learning in healthcare from diagnosis to decision support. Trans Comput Sci Methods. 2025;5(7):1–15. doi:10.5281/zenodo.16512875. [Google Scholar] [CrossRef]
139. El Husseini F, Noura HN, Salman O, Chahine K. Machine learning in smart buildings: a review of methods, challenges, and future trends. Appl Sci. 2025;15(14):7682. doi:10.3390/app15147682. [Google Scholar] [CrossRef]
140. Zhang S, Kong C. Deep learning and multi-objective optimization for real-time occupancy-based energy control in smart buildings. Sci Rep. 2025;15(1):39466. doi:10.1038/s41598-025-23134-4. [Google Scholar] [PubMed] [CrossRef]
141. Kolasa D, Pilch K, Mazurczyk W. Federated learning secure model: a framework for malicious clients detection. SoftwareX. 2024;27:101765. doi:10.1016/j.softx.2024.101765. [Google Scholar] [CrossRef]
142. Kasyap H, Tripathy S. Beyond data poisoning in federated learning. Expert Syst Appl. 2024;235(2):121192. doi:10.1016/j.eswa.2023.121192. [Google Scholar] [CrossRef]
143. Ma W, Zhao Q, Tian W. A defense method against multi-label poisoning attacks in federated learning. Sci Rep. 2025;15(1):26197. doi:10.1038/s41598-025-09672-x. [Google Scholar] [PubMed] [CrossRef]
144. Gong X, Chen Y, Wang Q, Kong W. Backdoor attacks and defenses in federated learning: state-of-the-art, taxonomy, and future directions. IEEE Wirel Commun. 2023;30(2):114–21. doi:10.1109/mwc.017.2100714. [Google Scholar] [CrossRef]
145. Islam MS, Rahman MA, Ariff Bin Ameedeen M, Ajra H, Binti Ismail Z, Mohamad Zain J. Blockchain-enabled cybersecurity provision for scalable heterogeneous network: a comprehensive survey. Comput Model Eng Sci. 2024;138(1):43–123. doi:10.32604/cmes.2023.028687. [Google Scholar] [CrossRef]
146. Rodríguez-Barroso N, Martínez-Cámara E, Luzón MV, Herrera F. Backdoor attacks-resilient aggregation based on Robust Filtering of Outliers in federated learning for image classification. Knowl Based Syst. 2022;245:108588. doi:10.1016/j.knosys.2022.108588. [Google Scholar] [CrossRef]
147. Yu L, Wu L. Towards Byzantine-resilient federated learning via group-wise robust aggregation. In: Federated learning. Cham, Switzerland: Springer International Publishing; 2020. p. 81–92. doi:10.1007/978-3-030-63076-8_6. [Google Scholar] [CrossRef]
148. Weller-Fahy DJ, Borghetti BJ, Sodemann AA. A survey of distance and similarity measures used within network intrusion anomaly detection. IEEE Commun Surv Tutorials. 2015;17(1):70–91. doi:10.1109/comst.2014.2336610. [Google Scholar] [CrossRef]
149. Zhang F, Zhang Y, Ji S, Han Z. Secure and decentralized federated learning framework with non-IID data based on blockchain. Heliyon. 2024;10(5):e27176. doi:10.1016/j.heliyon.2024.e27176. [Google Scholar] [PubMed] [CrossRef]
150. Zhou M, Han L. Sensor spoofing detection on autonomous vehicle using channel-spatial-temporal attention based autoencoder network. Mob Netw Appl. 2024;29(6):1839–52. doi:10.1007/s11036-023-02284-7. [Google Scholar] [CrossRef]
151. Wang Z, Ma J, Wang X, Hu J, Qin Z, Ren K. Threats to training: a survey of poisoning attacks and defenses on machine learning systems. ACM Comput Surv. 2023;55(7):1–36. doi:10.1145/3538707. [Google Scholar] [CrossRef]
152. Tian Z, Cui L, Liang J, Yu S. A comprehensive survey on poisoning attacks and countermeasures in machine learning. ACM Comput Surv. 2023;55(8):1–35. doi:10.1145/3551636. [Google Scholar] [CrossRef]
153. Hanif MA, Chattopadhyay N, Ouni B, Shafique M. Survey on backdoor attacks on deep learning: current trends, categorization, applications, research challenges, and future prospects. IEEE Access. 2025;13:93190–221. doi:10.1109/access.2025.3571995. [Google Scholar] [CrossRef]
154. Cajaraville-Aboy D, Fernández-Vilas A, Díaz-Redondo RP, Fernández-Veiga M. Byzantine-robust aggregation for securing decentralized federated learning. IEEE Access. 2025;13:190947–63. doi:10.1109/access.2025.3629864. [Google Scholar] [CrossRef]
155. Chang W, Wu J. Survey of sybil attacks in networks. In: Sensor networks for sustainable development. Boca Raton, FL, USA: CRC Press; 2017. p. 497–533. doi:10.1201/b17124-21. [Google Scholar] [CrossRef]
156. Song X, Li H, Hu K, Zai G. Backdoor federated learning by poisoning key parameters. Electronics. 2025;14(1):129. doi:10.3390/electronics14010129. [Google Scholar] [CrossRef]
157. Torra V. A systematic construction of non-i.i.d. data sets from a single data set: non-identically distributed data. Knowl Inf Syst. 2023;65(3):991–1003. doi:10.1007/s10115-022-01785-3. [Google Scholar] [CrossRef]
158. Šajina R, Tanković N, Ipšić I. Peer-to-peer deep learning with non-IID data. Expert Syst Appl. 2023;214(9):119159. doi:10.1016/j.eswa.2022.119159. [Google Scholar] [CrossRef]
159. Lu Z, Pan H, Dai Y, Si X, Zhang Y. Federated learning with non-IID data: a survey. IEEE Internet Things J. 2024;11(11):19188–209. doi:10.1109/jiot.2024.3376548. [Google Scholar] [CrossRef]
160. Barona López LI, Borja Saltos T. Heterogeneity challenges of federated learning for future wireless communication networks. J Sens Actuator Netw. 2025;14(2):37. doi:10.3390/jsan14020037. [Google Scholar] [CrossRef]
161. Ye M, Fang X, Du B, Yuen PC, Tao D. Heterogeneous federated learning: state-of-the-art and research challenges. ACM Comput Surv. 2024;56(3):1–44. doi:10.1145/3625558. [Google Scholar] [CrossRef]
162. Ge H, Yang X, Wang J, Lyu Z. A decentralised federated learning scheme for heterogeneous devices in cognitive IoT. Int J Cogn Comput Eng. 2024;5(2):357–66. doi:10.1016/j.ijcce.2024.08.001. [Google Scholar] [CrossRef]
163. Rashma BM, Macherla S, Jaiswal A, Poornima G. Handling heterogeneity in an IoT infrastructure. In: Advances in machine learning and computational intelligence. Singapore: Springer; 2020. p. 635–43. doi:10.1007/978-981-15-5243-4_60. [Google Scholar] [CrossRef]
164. Zhu Z, Hong J, Drew S, Zhou J. Resilient and communication efficient learning for heterogeneous federated systems. Proc Mach Learn Res. 2022;162:27504–26. doi:10.1109/tcad.2023.3346274/mm1. [Google Scholar] [CrossRef]
165. El Mokadem R, Ben Maissa Y, El Akkaoui Z. Federated learning for energy constrained devices: a systematic mapping study. Clust Comput. 2023;26(2):1685–708. doi:10.1007/s10586-022-03763-4. [Google Scholar] [CrossRef]
166. Tang S, Zhou W, Chen L, Lai L, Xia J, Fan L. Battery-constrained federated edge learning in UAV-enabled IoT for B5G/6G networks. Phys Commun. 2021;47(1):101381. doi:10.1016/j.phycom.2021.101381. [Google Scholar] [CrossRef]
167. Arouj A, Abdelmoniem AM. Towards energy-aware federated learning on battery-powered clients. In: Proceedings of the 1st ACM Workshop on Data Privacy and Federated Learning Technologies for Mobile Edge Network; 2022 Oct 17; Sydney, Australia. p. 7–12. doi:10.1145/3556557.3557952. [Google Scholar] [CrossRef]
168. Tang J, Nie J, Zhang Y, Xiong Z, Jiang W, Guizani M. Multi-UAV-assisted federated learning for energy-aware distributed edge training. IEEE Trans Netw Serv Manage. 2024;21(1):280–94. doi:10.1109/tnsm.2023.3298220. [Google Scholar] [CrossRef]
169. Moon J, Yang S, Lee K. FedOps: a platform of federated learning operations with heterogeneity management. IEEE Access. 2024;12(1):4301–14. doi:10.1109/ACCESS.2024.3349691. [Google Scholar] [CrossRef]
170. Krau T, Huber F, Chirakal T, Ricken T, Lüdemann-Ravit B, Heieck F. Efficient federated learning integration into existing MLOps pipelines via centralized model management. In: Database and Expert Systems Applications-DEXA 2025 Workshops; Cham, Switzerland: Springer Nature; 2025. p. 47–56. doi:10.1007/978-3-032-02003-1_4. [Google Scholar] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF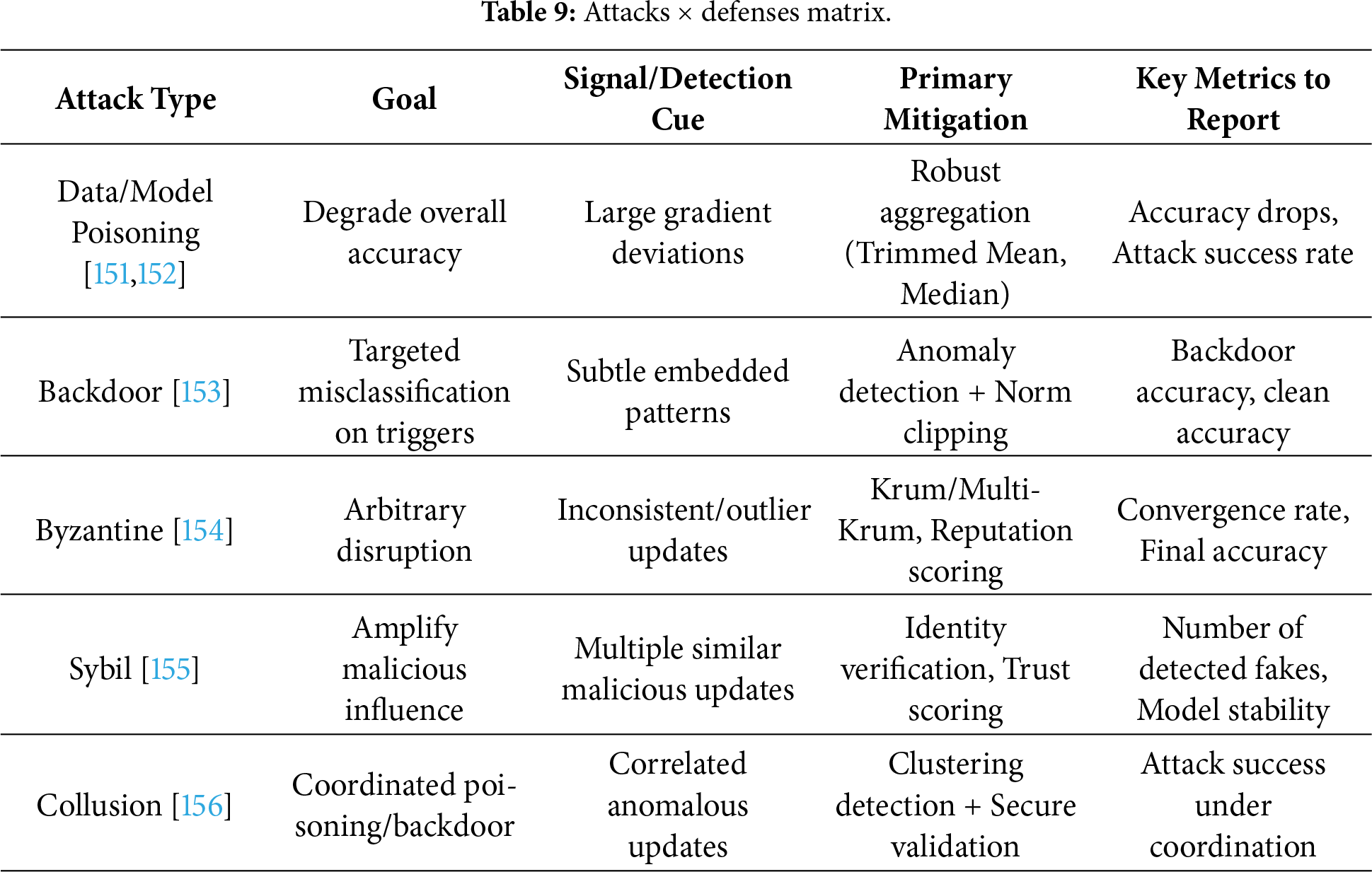
 Downloads
Downloads
 Citation Tools
Citation Tools