 Open Access
Open Access
ARTICLE
Design of Consensus Algorithm for UAV Swarm Identity Authentication Based on Lightweight Blockchain
1 Key Laboratory of Information and Network Security, Engineering University of the PAP, Xi’an, 710086, China
2 The School of Equipment Management and Support, Engineering University of PAP, Xi’an, 710086, China
* Corresponding Authors: Lijun Liu. Email: ; Long Lv. Email:
Computers, Materials & Continua 2026, 87(2), 27 https://doi.org/10.32604/cmc.2025.073837
Received 26 September 2025; Accepted 11 December 2025; Issue published 12 March 2026
Abstract
Aiming at the challenges of low throughput, excessive consensus latency and high communication complexity in the Practical Byzantine Fault Tolerance (PBFT) algorithm in blockchain networks, its application in identity verification for distributed networking of a drone cluster is limited. Therefore, a lightweight blockchain-based identity authentication model for UAV swarms is designed, and a Credit-score and Grouping-mechanism Practical Byzantine Fault Tolerance (CG-PBFT) algorithm is proposed. CG-PBFT introduces a reputation score evaluation mechanism, classifies the reputation levels of nodes in the network, and optimizes the consensus process based on grouping consensus and BLS aggregate signature technology. Experimental results demonstrate that under identical experimental conditions, compared with the PBFT algorithm, CG-PBFT achieves a 250% increase in average throughput, a 70% reduction in average latency, and simultaneous enhancement in security, thus making it more suitable for UAV swarm networks.Keywords
In recent years, research on unmanned aerial vehicle (UAV) swarms has developed rapidly, especially in the military field, where they have demonstrated significant effectiveness in performing tasks such as strikes, reconnaissance, and fire support. In these tasks, continuous data exchange is required between UAVs and between UAVs and the Ground Control Station (GCS). To prevent UAVs from being captured by the enemy during missions and ensure the confidentiality and security of communications, identity authentication is crucial as the primary line of defense. However, traditional identity authentication methods struggle to balance security and efficiency. Blockchain, as an emerging distributed infrastructure, adopts a block-chain data structure. Through encryption algorithms and consensus mechanisms, it stores data in a chained form of blocks, ensuring the characteristics of data such as immutability [1], transparency [2], and decentralization [3]. It also enables data editing and operations with the help of smart contracts. Leveraging these inherent advantages, blockchain technology offers a viable solution to address the security challenges confronting UAV swarms. As the core of blockchain technology, the key role of the consensus algorithm lies in ensuring that all nodes in the distributed network reach an agreement on the state of the blockchain, while maintaining the security, integrity, and immutability of data [4].
Currently, prevalent blockchain consensus mechanisms primarily encompass Proof of Stake (PoS) [5,6], Proof of Work (PoW) [7,8] and Practical Byzantine Fault Tolerance (PBFT) [9], etc. The PBFT consensus mechanism originates from the Byzantine Generals Problem,a concept formulated by Pease, Lamport, and others [10,11]. It was first proposed by Castro et al. [12] in 1999. Its core working principle is to achieve efficient consensus through multi-stage message interaction and division of node roles in an asynchronous network. When there are n nodes in the network system, it allows the existence of f Byzantine nodes, and the system can still operate normally, provided that the condition n
In recent years, research endeavors on PBFT have predominantly concentrated on aspects such as scalability optimization, security enhancement and performance improvement. Numerous academics have put forth diverse approaches to enhance PBFT’s performance, enabling its deployment in large-scale dynamic networks or networks with low computing power, thus expanding its application scenarios. Li et al. [13] introduced a novel “group-based” PBFT algorithm, which categorizes all nodes into distinct groups. Each group elects a primary node, reaches consensus internally first, and then achieves inter-group consensus. This method can markedly boost communication efficiency in scenarios with a substantial number of nodes, though it encounters certain issues regarding security performance.Additionally, Lao et al. [14] proposed a location-based scalable PBFT consensus algorithm. Given that mobile nodes generally have weaker computing capabilities than fixed nodes and are more prone to becoming malicious nodes, this algorithm can considerably reduce consensus overhead by selecting fixed and trusted nodes for consensus, albeit at the cost of increasing centralization. Wang et al. [15] devised a credit-based improved PBFT consensus algorithm (CPBFT). By modifying the original architecture and introducing a credit coefficient, nodes with high credit coefficients are chosen as primary nodes, which enhances the algorithm’s throughput and security to some extent. Xu and Wang [16] and Yang et al. [17] utilized hash algorithms to differentiate consensus nodes in the PBFT consistency protocol, thereby avoiding excessive inter-node communication and reducing communication complexity. However, this approach fails to identify Byzantine nodes.
Currently, there exists a wide variety of applied research on the use of blockchain for identity authentication in distributed networks. Cui et al. [18] constructed a local-public hybrid blockchain architecture in the IoT, classifying nodes in the IoT into cluster nodes and ordinary nodes. The local chain undertakes the identity authentication of ordinary nodes, while the public chain is tasked with the identity authentication of cluster nodes. NVSVS [19], Roman et al. [20] and Qashlan et al. [21] have deployed blockchain on servers with higher computing power to achieve efficient identity authentication. Haque et al. [22] enhanced network scalability by integrating the Delegated Proof of Stake (DPoS) consensus algorithm in blockchain with sharding technology. Kong et al. [23] proposed a stateless blockchain based on triple aggregated sub-vectors and a dynamic Proof of Authorized Trust (PoAT) consensus mechanism. By periodically selecting authorized nodes randomly, this mechanism ensures the credibility of mutual authentication among UAV nodes. Zhang [24] divided UAV identity authentication into two phases: a main blockchain for identity authentication of UAVs prior to network access, and a sub-blockchain for identity authentication among UAVs during mission execution, thus tackling various security threats.
In summary, due to the high-frequency data interaction required by UAV swarms in missions such as military strikes and reconnaissance, the use of blockchain for traditional distributed identity authentication faces the problem of an imbalance between security and efficiency. In particular, the PBFT algorithm in blockchain has drawbacks including high communication complexity and difficulty in eliminating malicious nodes, making it unable to adapt to the resource-constrained and dynamic topology characteristics of UAVs. Therefore, this paper designs a lightweight CG-PBFT algorithm and conducts multi-dimensional comparisons with other improved PBFT consensus algorithms, as shown in Table 1. These comparisons demonstrate its high adaptability to UAV swarm networks, enabling secure, efficient, and scalable identity authentication for UAV swarms.
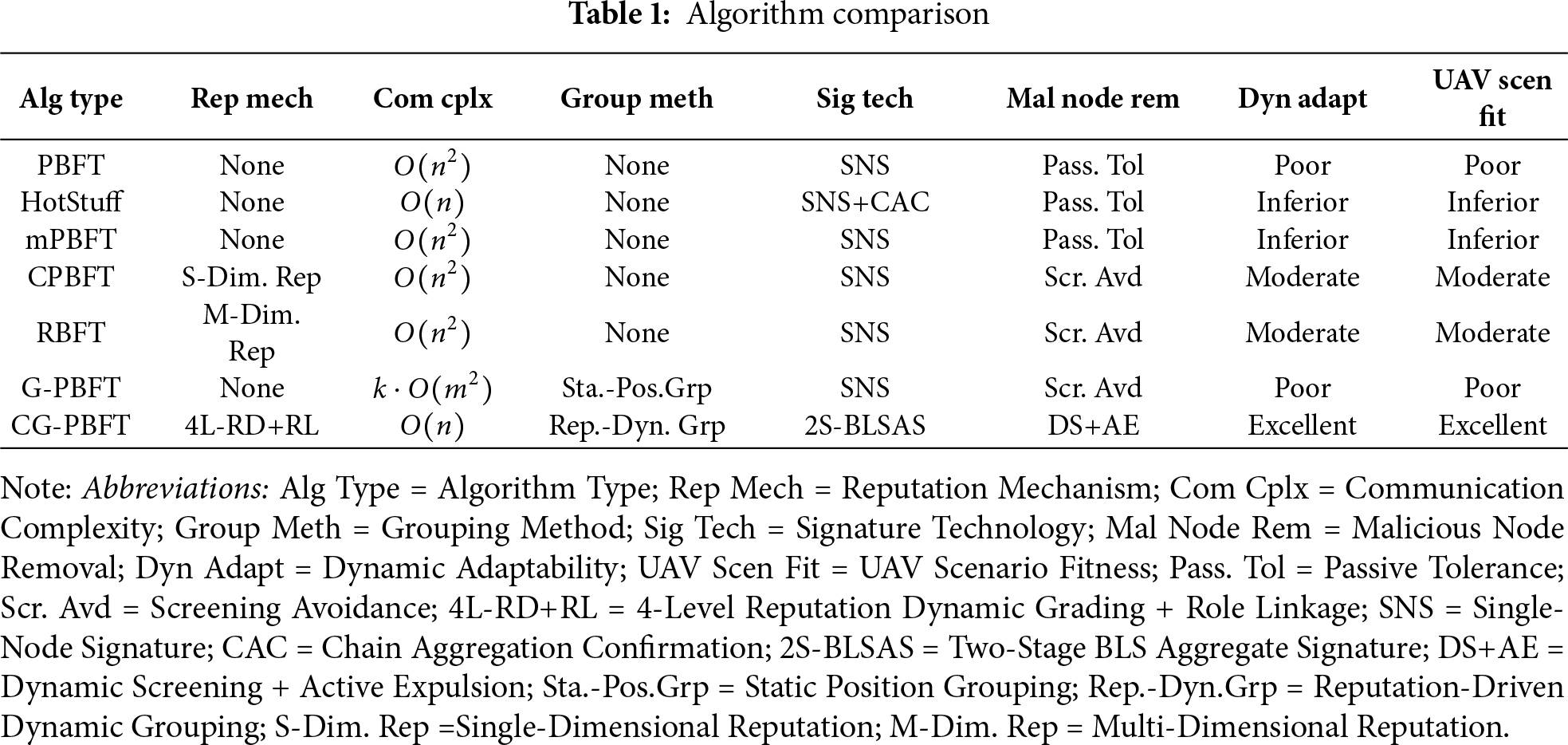
As shown in Table 1, the CG-PBFT consensus algorithm proposed in this paper has the following three unique contributions compared with other PBFT consensus algorithms:
1. Different from the single credit coefficient of CPBFT and the fixed grouping of G-PBFT, the CG-PBFT consensus algorithm designs a collaborative mechanism of four-level reputation grading and dynamic grouping targeting the “dynamic topology + resource-constrained” characteristics of UAV swarms. This mechanism improves system adaptability and consensus efficiency in dynamic scenarios, effectively reduces communication overhead, and enhances the stability of node collaboration.
2. Distinguished from existing algorithms that only use aggregate signatures in a single phase, the CG-PBFT consensus algorithm deeply integrates BLS aggregate signatures into the two-phase consensus of “intra-group + inter-group”. Meanwhile, it optimizes the signature verification process to improve consensus efficiency.
3. A reputation-role linked adjustment strategy is proposed, which designs mechanisms for decreasing rewards for high-reputation nodes, promotion of ordinary nodes, and expulsion of malicious nodes. This strategy avoids the monopoly of oligarch nodes, optimizes the network architecture, and improves network security.
The Practical Byzantine Fault Tolerance (PBFT) algorithm serves as a versatile solution in distributed networks, capable of tolerating malicious nodes and achieving consensus. Generally, in a distributed network with
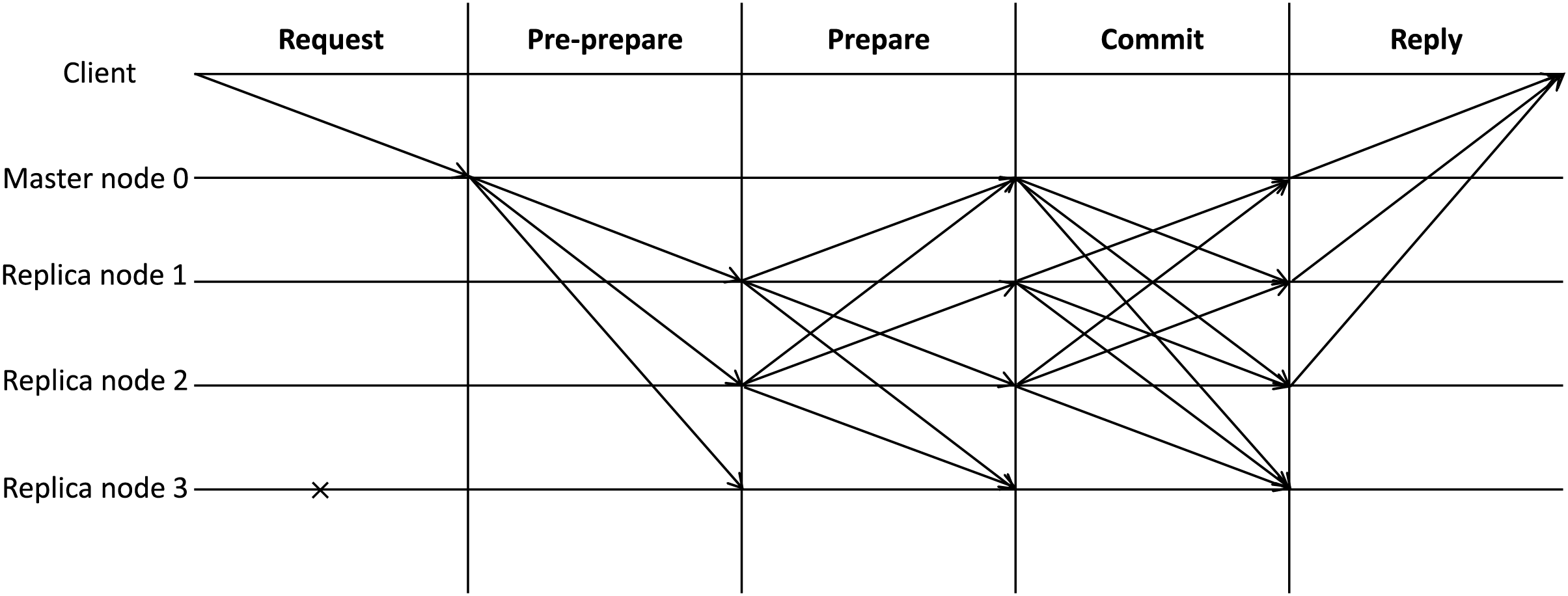
Figure 1: PBFT consensus process
(1) Request phase: The client transmits a request message to the primary node, which contains the request content, timestamp, and the client’s identity information.
(2) Pre-prepare phase: Upon receiving and verifying the client’s request message, the primary node assigns a corresponding proposal number and then dispatches a pre-prepare message to all replica nodes in the network.
(3) Prepare phase: After receiving and successfully verifying the pre-prepare message, the replica node sends prepare messages to the primary node and other replica nodes. Simultaneously, it validates the prepare messages from other replica nodes. When the node receives
(4) Commit phase: The primary node and replica nodes generate confirmation messages and broadcast them to all other nodes. After receiving these messages, the nodes perform verification. Once at least
(5) Reply phase: The primary node and replica nodes send reply messages to the client. When
During the entire consensus process, the messages received by nodes at each stage are stored in the local log, and Byzantine nodes do not feed back any information to other normal nodes. As shown in Fig. 1, replica node 3 is a Byzantine node. However, due to the PBFT consensus mechanism, as long as the number of Byzantine nodes does not exceed
Generally, the entire consensus process requires nodes to finish within a specific time period. However, if the primary node turns malicious or a consensus timeout occurs due to poor network conditions, the view change protocol will be triggered to replace the primary node and update the view number, thereby ensuring the liveness and security of the entire distributed network.
The BLS aggregate signature is a digital signature scheme based on elliptic curve pairing proposed by Boneh et al. [25] in 2001. It can realize the functions of signature generation and verification by using bilinear pairing, and its signature has the characteristics of short signature, security and uniqueness. The basic process of signature is as follows:
(1) Key Generation: Select a random number as the private key SK, and compute the public key PK as
(2) Signature Generation: For the message
(3) Signature Verification: Calculate the point
Introducing BLS aggregate signatures into the blockchain network of unmanned aerial vehicle (UAV) swarms can significantly reduce the transmission volume of signature data during communication among UAV swarms, lower communication latency, and improve consensus efficiency.
3 Design of Light-Weight Blockchain-Based Distributed Networking Identity Authentication System for UAV Swarms
3.1 Design of Lightweight Blockchain-Based Network Architecture for UAV Swarms
This paper constructs a network architecture, as shown in Fig. 2, which consists of three core modules: the ground base station, the UAV swarm, and the blockchain. The ground base station module is responsible for initial network configuration, task issuance, generating public-private key pairs and data certificates for UAVs in the network, and sending public keys and data certificates of the UAVs to the blockchain module for storage. The UAV swarm module is composed of UAVs that have been registered through the ground base station, and its main function is to receive the private keys and task requests sent from the ground base station. The blockchain module is composed of two sub-units, namely the ground base station chain unit and the UAV swarm chain unit. The two sub-units share data. The ground base station chain unit is used for mutual communication and distributed identity authentication between the UAV swarm module and the ground base station, while the UAV swarm chain unit is used for mutual communication and distributed identity authentication within the UAV swarm module.
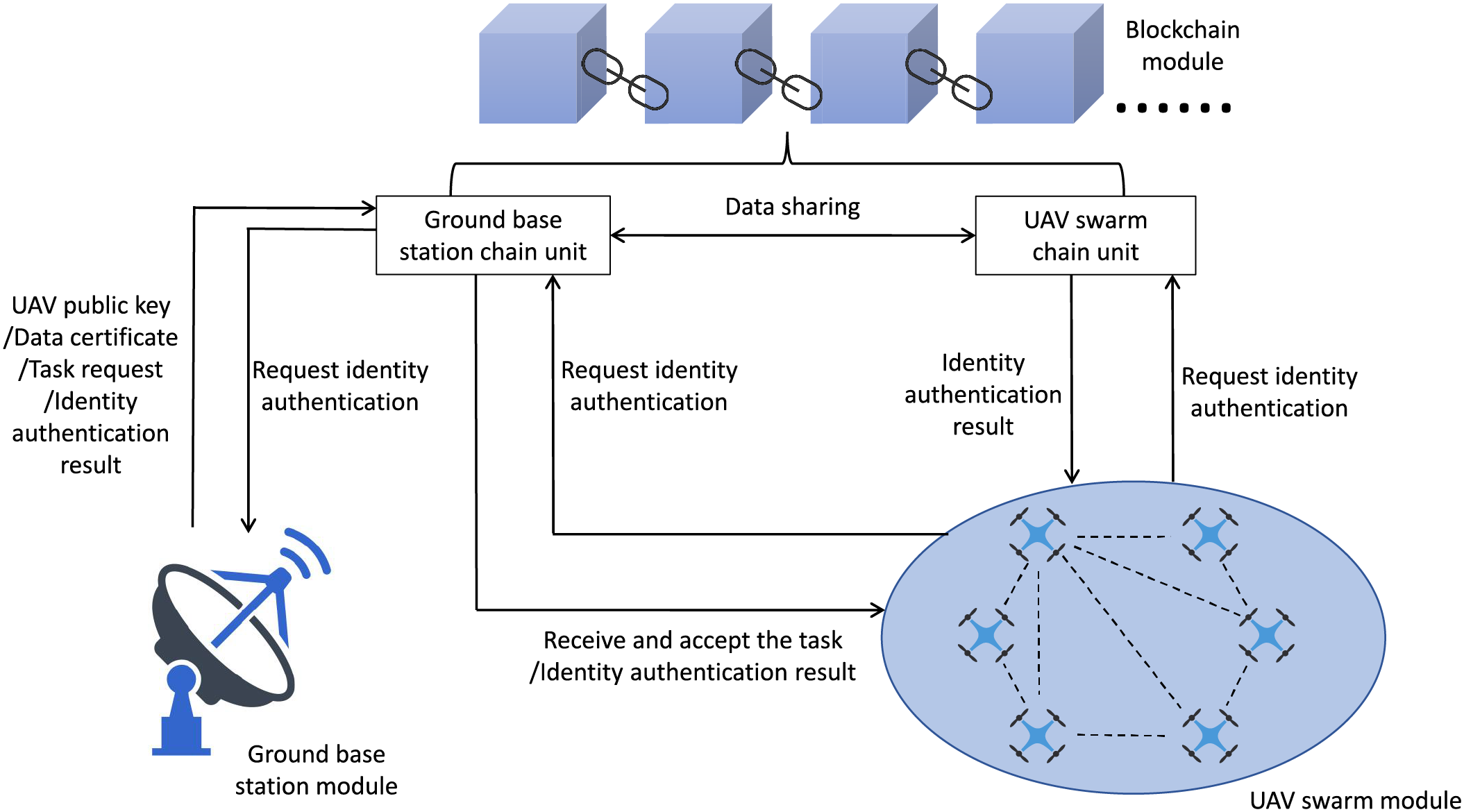
Figure 2: Drone cluster blockchain network architecture
3.2 Design of UAV Identity Authentication Process
Step 1: UAV Network Access Registration
Before a UAV accesses the network, it must first register with the ground base station module to obtain an asymmetric public-private key pair
Step 2: Drone Identity Authentication
When the UAV cluster modules conduct internal communication, identity authentication must be performed first. At this point, the sender needs to package its own digital certificate (
Step 3: The Addition Of New Drone Nodes
When a new drone intends to join the network, it first registers with the ground base station module, which generates a digital certificate (
Step 4: Deletion Of UAV Nodes
In the UAV cluster module, when a UAV node needs to be deleted or withdrawn from the network, the ground base station module adds an invalidation label to the node’s digital certificate (
In this system, by leveraging the immutability of blockchain to record the public keys, digital certificates, and behaviors of drones, any attempt to tamper with historical records on the chain can be detected at any time. Meanwhile, the identity authentication mechanism and message encryption method ensure the security of drone identities as well as the confidentiality and integrity of messages. Therefore, the security and credibility of the system have been significantly enhanced.
4 Design of CG-PBFT Consensus Algorithm Model
4.1 Node Reputation Grading And Grouping Mechanism
In the traditional PBFT consensus algorithm, the selection of the primary node is determined by the current view number
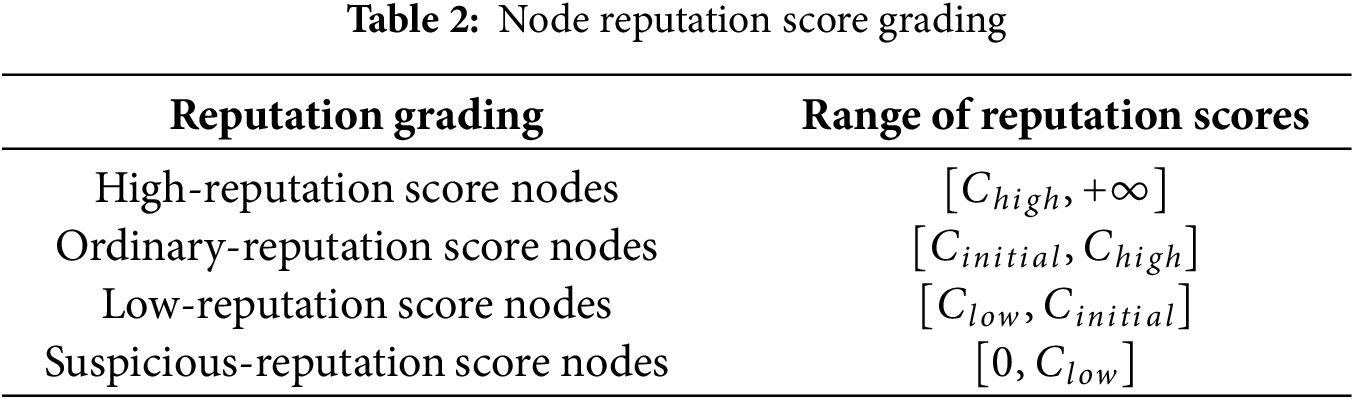
Among them, both
According to the four-level grouping criteria based on reputation scores, UAV cluster nodes are divided into four grades: high-reputation UAV nodes, ordinary-reputation UAV nodes, low-reputation UAV nodes, and suspicious UAV nodes. Based on this four-level classification, the specific grouping mechanism is shown in Fig. 3. All high-reputation UAV nodes form a leading group, among which the UAV node with the highest reputation score serves as the primary node and is responsible for leading the entire leading group. The remaining high-reputation UAV nodes act as leading nodes, each commanding a led group. The members of the led groups, as slave nodes, consist of randomly assigned ordinary-reputation UAV nodes and low-reputation UAV nodes. Suspicious UAV nodes with reputation scores lower than
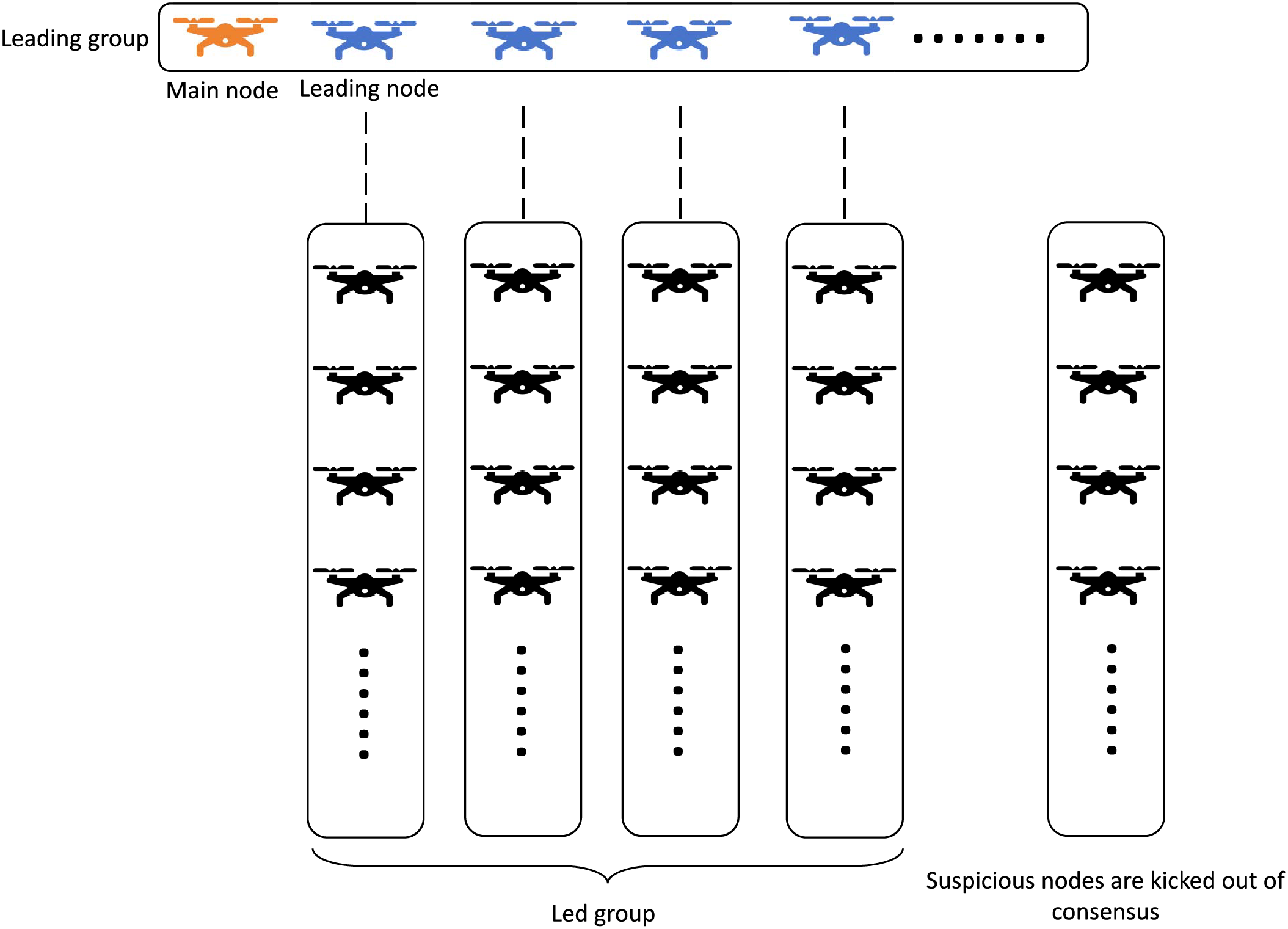
Figure 3: A four level grouping architecture based on reputation points of drone clusters
Meanwhile, in accordance with the requirements of the consensus mechanism, the number of nodes in the leading group must satisfy
4.2 Design of Reputation Score Evaluation Model
In the consensus process, considering the characteristics of UAV cluster networks, such as frequent dynamic changes, unstable message routing, and the vulnerability of UAVs to electromagnetic interference and malicious attacks, even when most nodes actively and normally participate in the consensus, there may be issues where some nodes fail to participate in the consensus in a timely or complete manner due to network problems, as well as the existence of malicious nodes. In response to the above situations, a reputation score evaluation model for nodes is designed.
Reputation score evaluation model:
Among them,
The direct trust value of a node is expressed as:
Among them, G is the number of times the node has successfully completed consensus, X represents the number of times the node has failed in the consensus, Y represents the total number of consensus times, and
The direct trust value is a key indicator for evaluating the reliability of a node. The higher the direct trust value, the more reliable the node.
The incentive and punishment parameter of a node is expressed as:
Among them, Q is a quantitative representation of whether the node
Among them,
When nodes participate in the consensus, the above formula is used for incentive and punishment control to better ensure the honest behavior of nodes. For high-reputation nodes serving as primary nodes or leading nodes, their rewards are reduced to prevent the emergence of oligopoly and avoid network centralization. For nodes with reputation scores around
The role indicator of a node is expressed as:
Due to the different tenure statuses of nodes in the consensus, the formula
4.2.1 Basis for Weight Setting
To address the repeatability issue of adjustable weights in the reputation score evaluation model, this paper clarifies the setting logic of each weight (
1.
2.
3.
4.
In this paper,
4.2.2 Improvement of Consensus Process
After the grouping of UAV nodes is completed, all UAV nodes in the network are divided into K groups, and BLS aggregate signatures are introduced into the consensus process to further reduce communication overhead. The entire consensus process is mainly divided into two parts: intra-group consensus and inter-group consensus. In the intra-group consensus, when the consensus starts, the master node in the entire network delivers messages to each leading node, and each leading node then forwards the messages to the slave nodes within their respective groups. Consensus is conducted within each group, and finally, the messages are updated to each leading node. After the completion of intra-group consensus, the inter-group consensus begins. The master node in the leading group leads the leading nodes within the group to complete the consensus, and each leading node updates the messages to the master node, thus finishing the entire consensus process, as shown in Fig. 4.
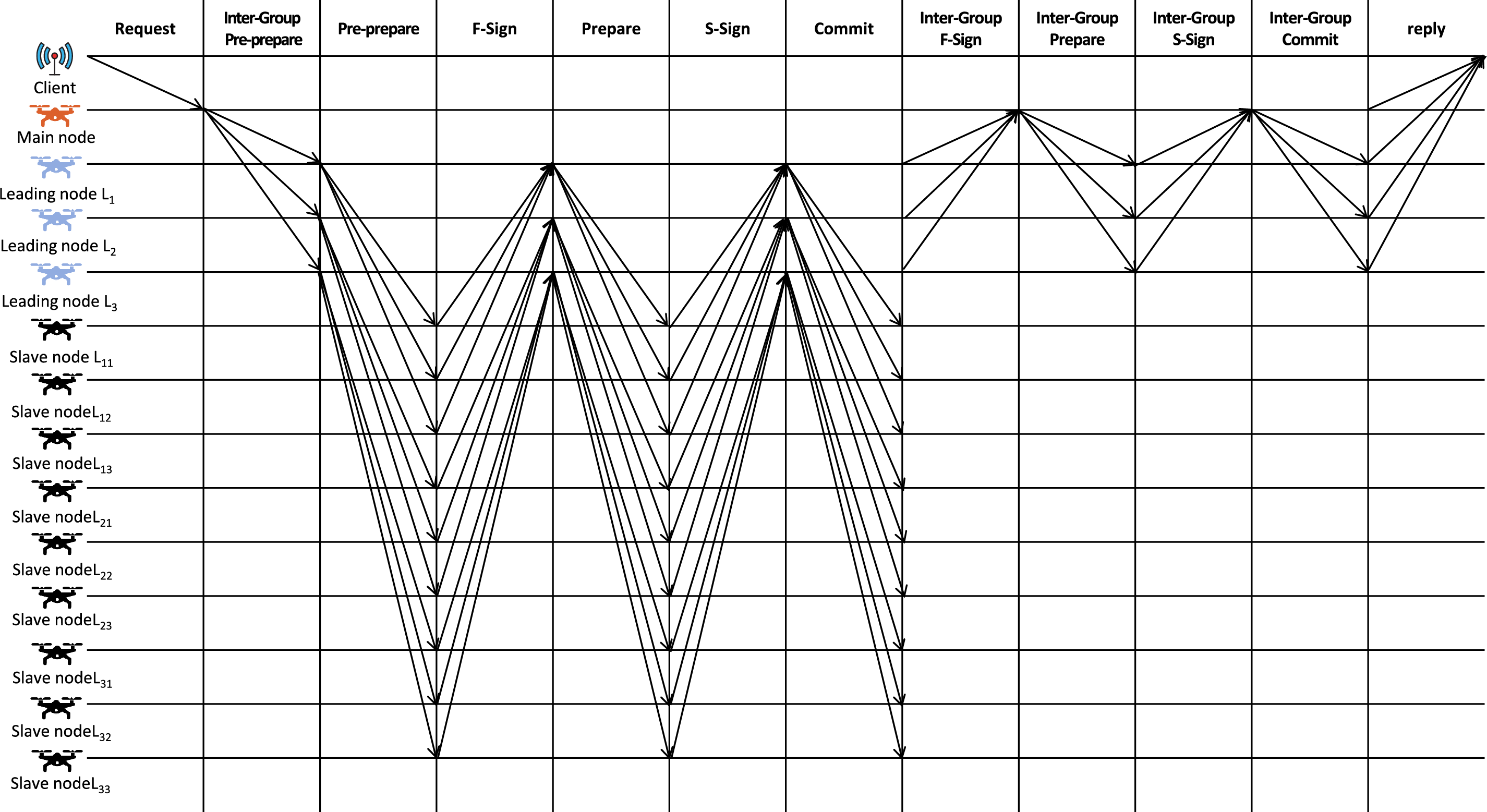
Figure 4: Consensus process of drone cluster nodes
(1) Request phase. The client sends a request to the master node, with the message formatted as
(2) Inter-Group Pre-prepare phase. After the master node receives and correctly verifies the request message, it sends a pre-prepare message to the leading nodes of each group. The message format is
(a) Pre-prepare phase. The leading node sends a pre-prepare message to the slave nodes in its group, using the format
(b) F-Sign phase. Upon receiving the message sent by the leading node, the slave nodes in the group verify it. If the verification is successful, they send a message to the leading node with the format
(c) Prepare phase. The leading node sends a message with an aggregated signature to the slave nodes within the group, and the message format is
(d) S-Sign phase. After the slave nodes in the group successfully verify the signature, they send an S-Sign message to the leading node, with the message format being
(e) Commit phase. The leading node broadcasts a message with an aggregated signature to all slave nodes within the group, and the message format is
(3) Inter-Group F-Sign phase. After each group completes the intra-group consensus, the leading node sends a message to the master node in the leading group, with the message format being
(4) Inter-Group Prepare phase. The master node broadcasts broadcasts the message to all leader nodes in the group. The message format is
(5) Inter-Group S-Sign phase. After the leading nodes in the group successfully verify the signature, they send an S-Sign message to the master node, with the message format being
(6) Inter-Group Commit phase. The master node broadcasts a message with an aggregated signature to all leading nodes in the group, and the message format is
(7) Reply phase. The master node and leading nodes send messages to the client, with the formats being
Although the probability that the master node or leading node selected by the reputation score evaluation mechanism becomes a Byzantine node is greatly reduced, in order to ensure the liveness and security of the system, this paper still designs a view switch protocol for cases where the master node or leading node is down or the consensus node exhibits Byzantine behavior, and the flow chart is shown in Fig. 5.
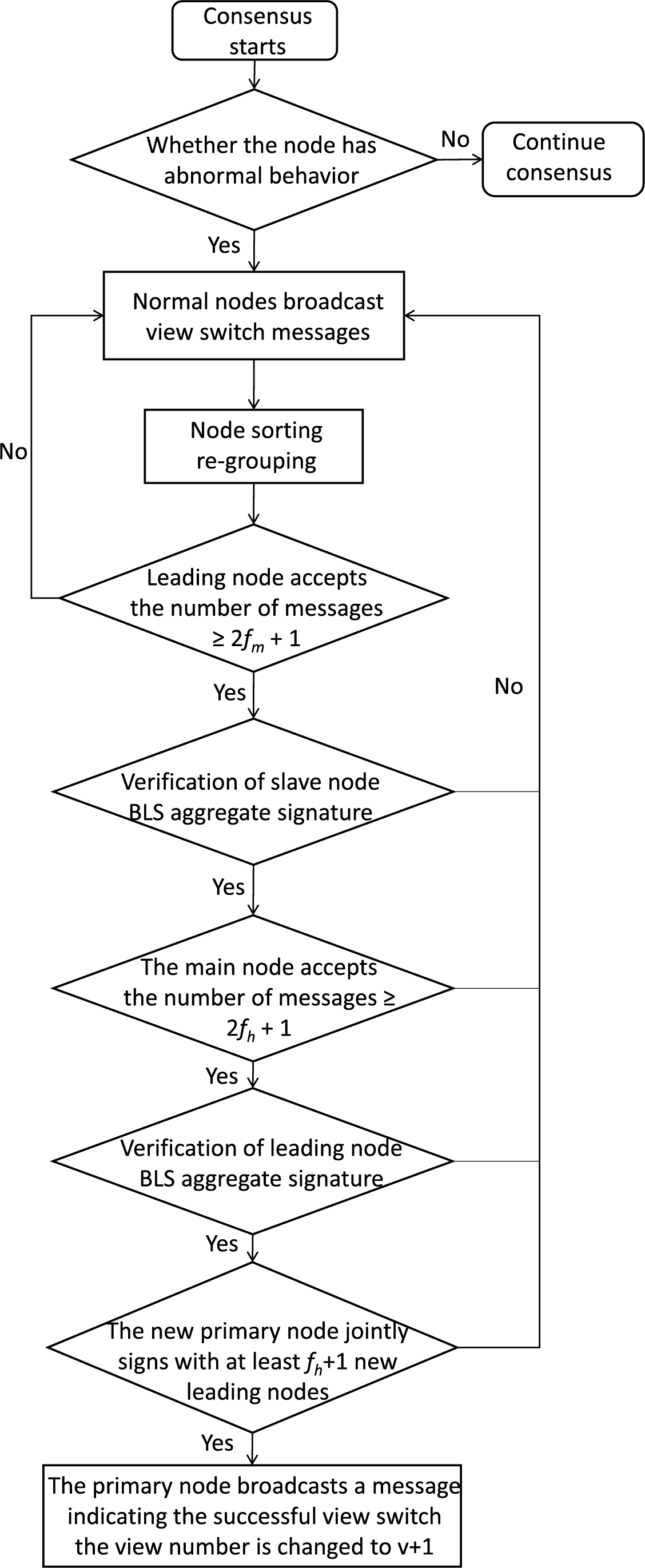
Figure 5: View switching process
(1) When a node in the network experiences a timeout while waiting, the view switch protocol is triggered. At this point, new master nodes and leading nodes are selected in sequence based on the reputation score rankings obtained from the previous round of consensus, with those having higher reputation scores taking up the positions. After the selection is completed, the normally operating nodes in the network continue to broadcast information, with the message format being
(2) After triggering the view change protocol, the view number is updated to
4.3 Proof of the Byzantine Fault Threshold of CG-PBFT under the Partially Synchronous Model
Based on the characteristics of the partially synchronous network and the design logic of the CG-PBFT algorithm, the following core assumptions are specified to lay the foundation for the threshold proof:
Partially Synchronous Network Assumption: There exists an unknown but fixed upper bound
Node and Behavior Assumption: Let the total number of nodes in the system be N, where the number of Byzantine nodes is
CG-PBFT Architecture Assumption: After node grouping, the number of group leader nodes is
4.3.2 Key Parameters and Consensus Validity Conditions
To quantify the fault tolerance capability of hierarchical consensus, the following parameters are defined as shown in Table 3:
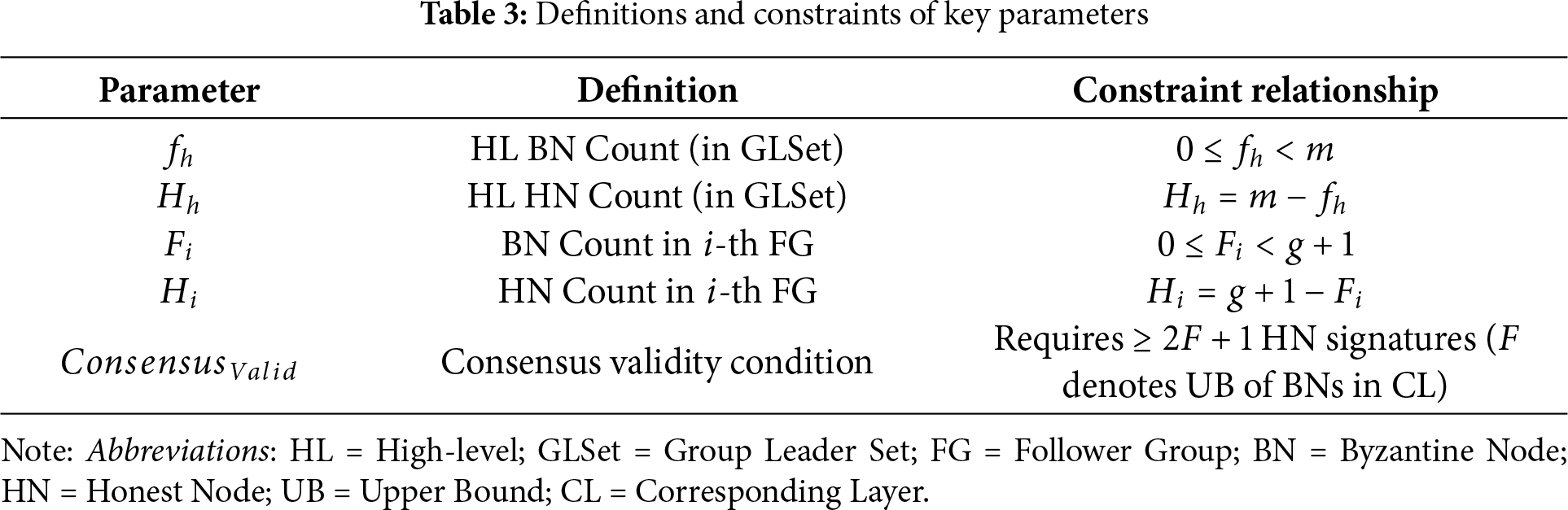
4.3.3 Derivation of the Byzantine Fault Threshold
The consensus process of CG-PBFT is divided into two levels: “intra-group consensus among follower groups” and “inter-group consensus across group leader nodes”. The fault tolerance thresholds for the two levels of consensus are derived separately, and finally integrated into the overall system fault tolerance threshold.
(1) Intra-group Fault Tolerance Threshold of Follower Groups. Each follower group is required to reach an intra-group consistent result, generate an aggregate signature, and submit it to the group leader set. Under partial synchrony, it is necessary to ensure that even in the presence of malicious nodes, honest nodes can still reach a verifiable consistent result, i.e.,
(2) Inter-group Fault Tolerance Threshold of the Group Leader Set. The group leader set is responsible for aggregating results from all follower groups and generating a system-level consensus, whose fault tolerance capability directly determines the global system consistency. For the validity of inter-group consensus, the number of honest nodes in the group leader set must satisfy
(3) Global Fault Tolerance Threshold of the System. The total number of Byzantine nodes in the system is
Furthermore, the system incorporates a reputation evaluation mechanism to dynamically exclude malicious nodes. Therefore, in practical consensus processes, the fault tolerance capability of the set of honest nodes will be superior to the theoretical threshold of the original system. This advantage stems from the fact that the reputation mechanism reduces the effective number of Byzantine nodes in the system, thereby enhancing the robustness of the consensus algorithm.
4.3.4 Proof of Safety and Liveness
(1) Consistency Proof: If the CG-PBFT algorithm satisfies the global fault tolerance condition
(a) Proof of Intra-group Consistency
Assume there exist two honest nodes P and Q in a certain follower group that confirm different intra-group proposals
(b) Proof of Inter-group Consistency
Assume there exist two honest leader nodes P and Q in the group leader set that confirm different global aggregated proposals
(c) Global Consistency Integration
The unique intra-group result is confirmed through intra-group consistency, and the unique global aggregated result is verified via inter-group consistency. Subsequently, the confirmed global aggregated result is synchronized to all nodes in the network by the leader nodes, thereby achieving the integration of global consistency.
(2) Liveness Proof: When the network delay eventually stabilizes within
(a) Termination of the Consensus Process
Based on the partial synchronous model and the CG-PBFT consensus process, under the premise of satisfying fault tolerance constraints and no malicious interference, any proposal initiated by an honest node will undergo the processes of proposal initiation (
(b) Liveness of View Change
When malicious interference exists or consensus times out, the view change protocol is triggered. Assuming the timeout waiting time is T, when an honest node undergoes the processes of broadcasting view change messages (
(c) Evasion of Malicious Node Blocking
Based on the reputation score evaluation mechanism, malicious nodes attempting to block the consensus process will experience a sharp drop in their own reputation scores and will eventually be kicked out of the network. This ensures that malicious nodes cannot block the consensus process for a long time.
5 Experimental Results and Analysis
This paper implements a multi-node and groupable blockchain system based on Python, simulating the identity registration and consensus process of an unmanned aerial vehicle (UAV) cluster on the blockchain. In the simulation experiment, the network adopts a distributed mesh topology; nodes are uniformly distributed in a 10 km
5.1 Analysis of Communication Overhead
Communication overhead refers to the total network resources consumed by message transmission between nodes to reach a consensus. The communication overhead of the PBFT algorithm consensus is based on its three consensus phases, namely the Pre-Prepare phase, the Prepare phase, and the Commit phase. The number of communications in these stages is
The CG-PBFT proposed in this paper reduces the communication overhead of consensus by implementing group consensus through reputation-based grouping of nodes participating in consensus and adding a signature phase in the consensus process.
Therefore, the communication overhead of CG-PBFT consensus includes the intra-group and inter-group consensus processes, which are respectively the Pre-Prepare phase, F-Sign phase, Prepare phase, S-Sign phase, and Commit phase of intra-group consensus, as well as the Inter-group Pre-Prepare phase, Inter-group F-Sign phase, Inter-group Prepare phase, Inter-group S-Sign phase, and Inter-group Commit phase of inter-group consensus. Due to the grouping mechanism of CG-PBFT, there will be schemes with different numbers of groups for consensus with the same number of nodes. To facilitate the explanation of its communication overhead, it is assumed that the number of nodes in the leading group is
Based on the above assumptions, the consensus between a led group and its leading node forms a set of intra-group consensus, involving a total of
The inter-group consensus is the consensus of the leading group, involving a total of m nodes. It is divided into 5 stages, with the number of communications in each stage being
In summary, the communication overhead of CG-PBFT is:
It can be seen that compared with the traditional PBFT, the communication complexity of CG-PBFT is reduced from
In blockchain networks, throughput refers to the number of transactions that the network can process and confirm within a unit of time, which is usually expressed in TPS (Transactions Per Second). Its calculation formula can be expressed as:
To verify the improvement of CG-PBFT in throughput, this paper sets up two experimental schemes. The first is to compare the throughput of the algorithm under different numbers of nodes but the same number of groups, and the second is to analyze the throughput changes of CG-PBFT under the same number of nodes but different numbers of groups. Based on the first experiment, the number of nodes set in this paper is 30, 40, 50, 60, 70, 80, 90, and 100 respectively, and the number of groups is set to 5. Consensus is carried out for each case, the experiment is repeated 100 times, and the calculated mean
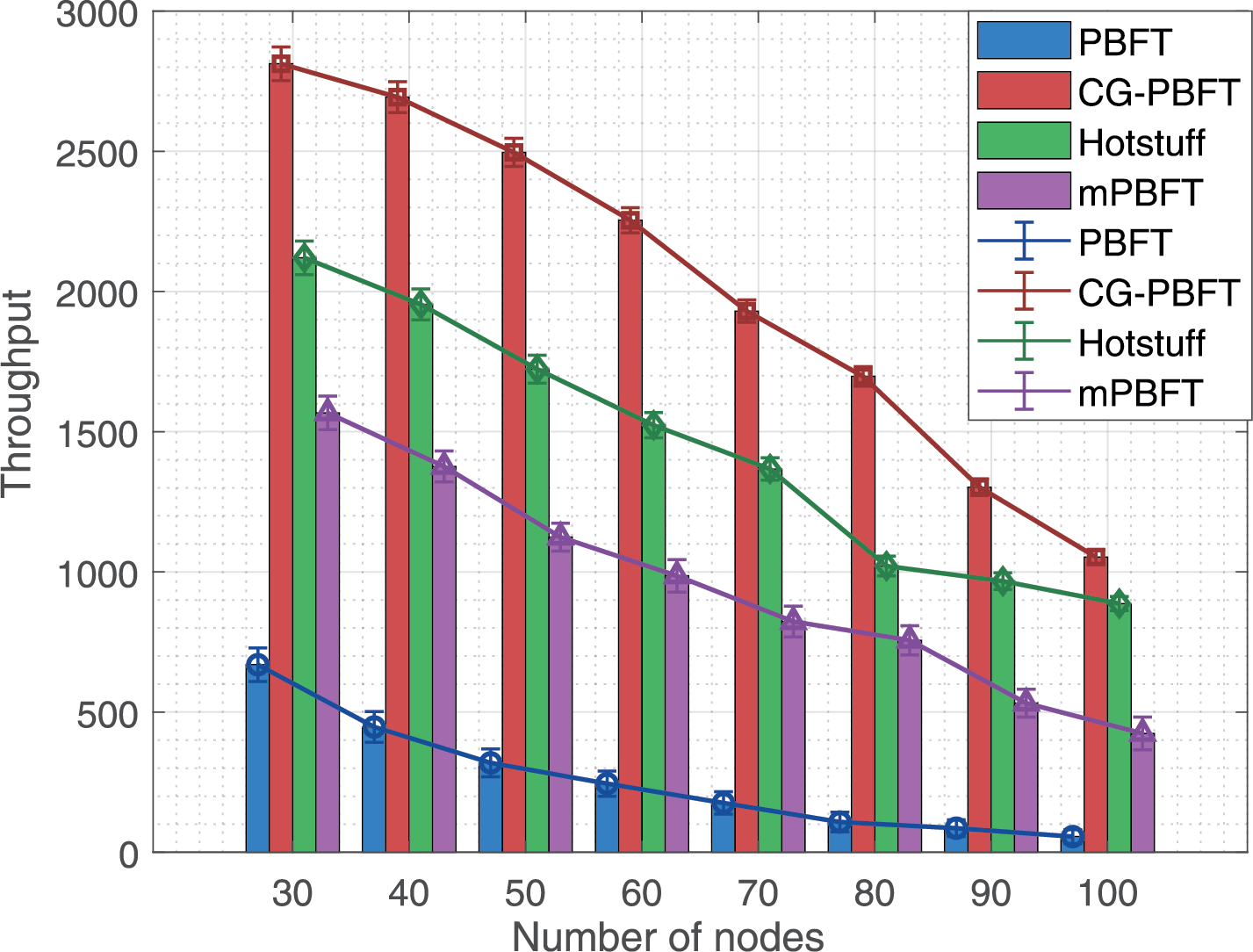
Figure 6: Experiment 1 throughput comparison
As shown in Fig. 6, as the number of nodes increases, the throughput of the four algorithms generally shows a downward trend, yet the throughput of CG-PBFT is notably higher than that of the other three algorithms under the same node count. This is because compared with the other three algorithms, CG-PBFT adopts a grouping consensus mechanism and uses aggregate signatures in the consensus phase, which greatly reduces its communication complexity, enabling the network system to maintain high throughput under a large number of nodes.
Based on Experiment 2, this paper selects 100 nodes and sets the number of groups to 4, 5, 10, 15, and 20 respectively. Consensus is performed 100 times for each setting, and the mean
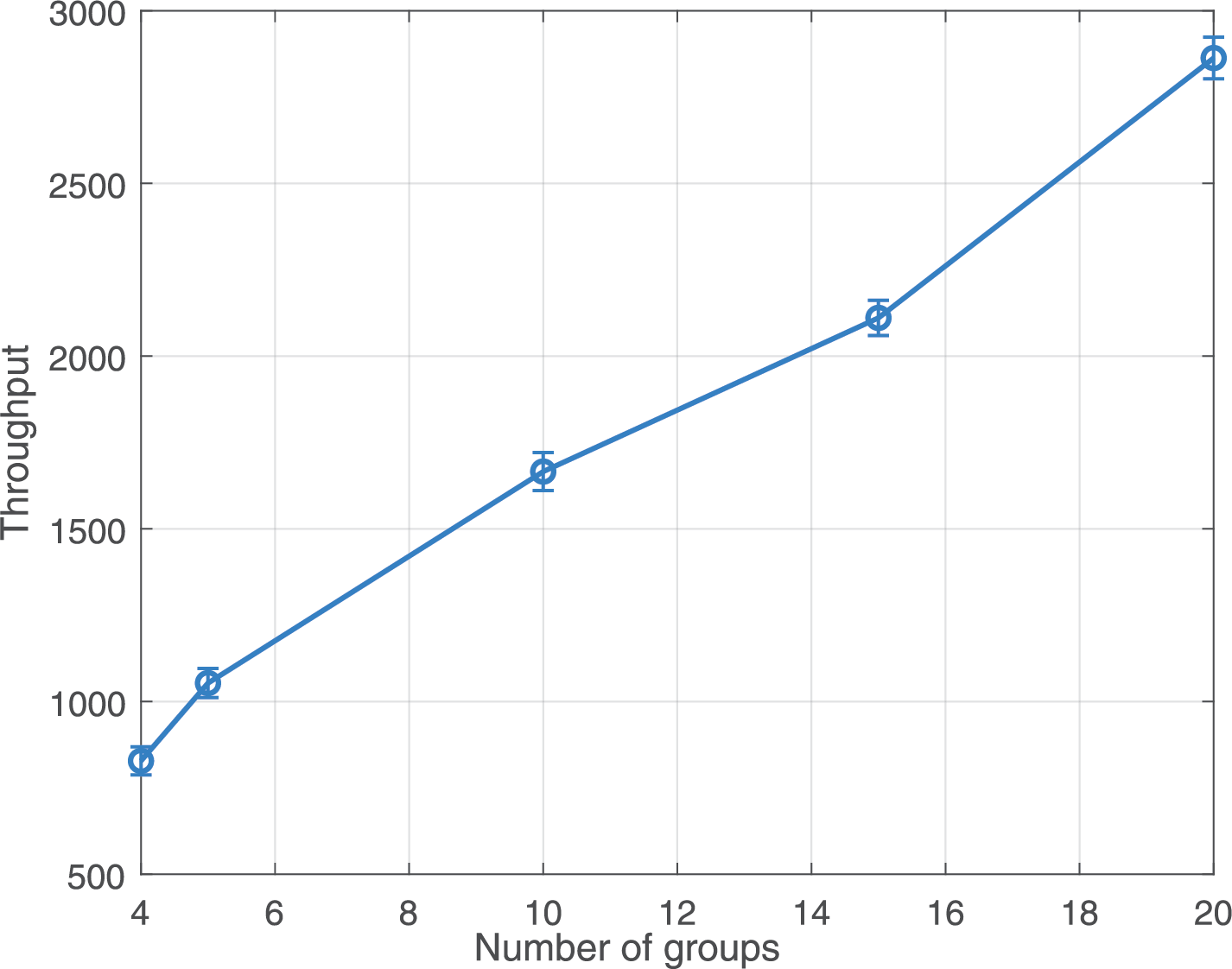
Figure 7: Experiment 2 throughput comparison
As can be observed from Fig. 7, when the number of nodes is identical, the throughput gradually rises as the number of groups increases. Therefore, for large-scale UAV clusters, according to the different throughput requirements of tasks, the maximum number of nodes in each group can be dynamically adjusted to achieve different numbers of groups, so as to adapt to the throughput required by tasks. CG-PBFT can be more suitable for the scenario application of large-scale UAV clusters.
5.3 Analysis of Consensus Delay
Consensus delay
In this paper, similar to the throughput analysis, two experiments are also conducted. The first experiment compares the consensus delay of each algorithm under varying node counts but a fixed group count. The node counts are set to 30, 40, 50, 60, 70, 80, 90, and 100, with the group count fixed at 5. Consensus is performed for each case, the experiment is repeated 100 times, and the calculated mean
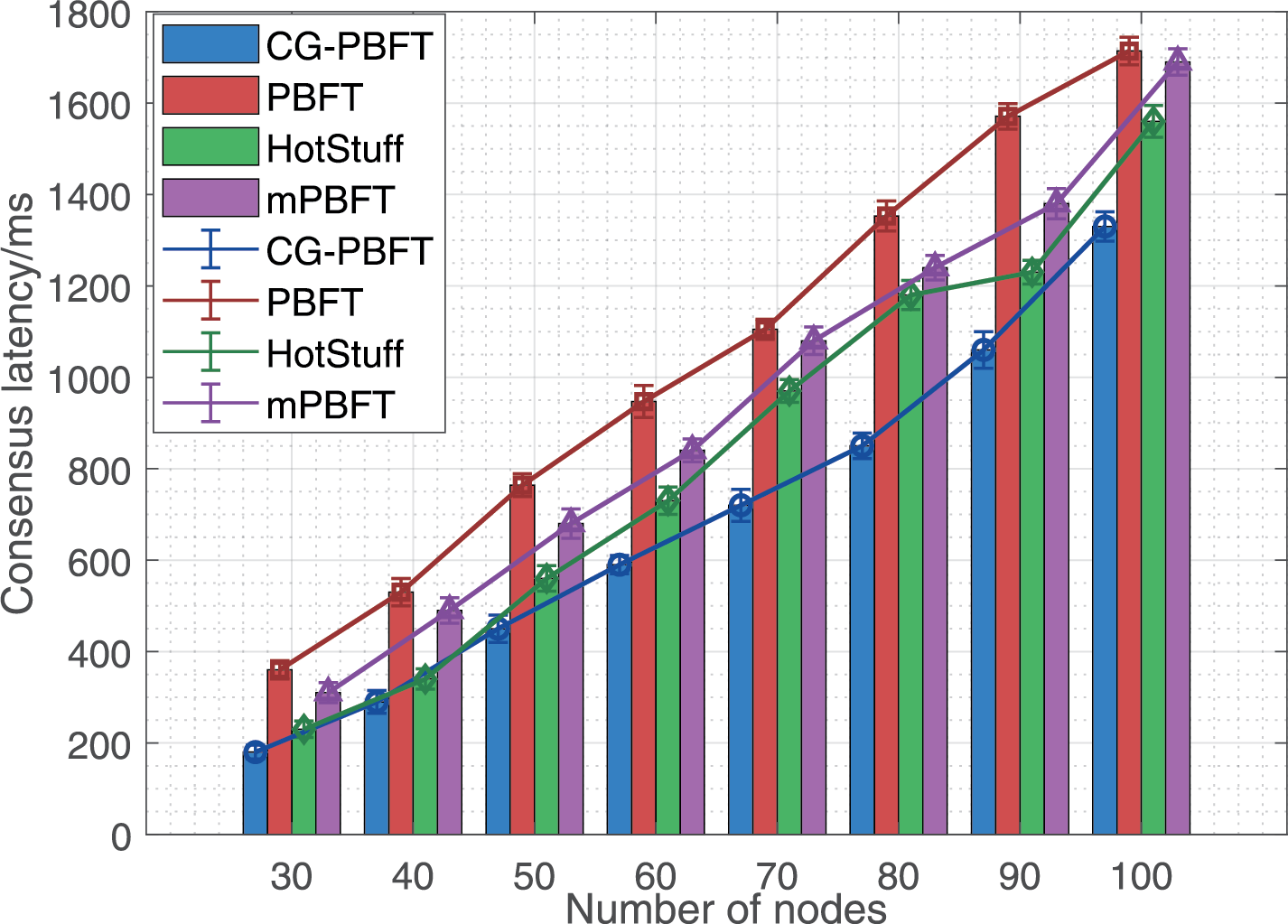
Figure 8: Experiment 1 comparison of consensus latency
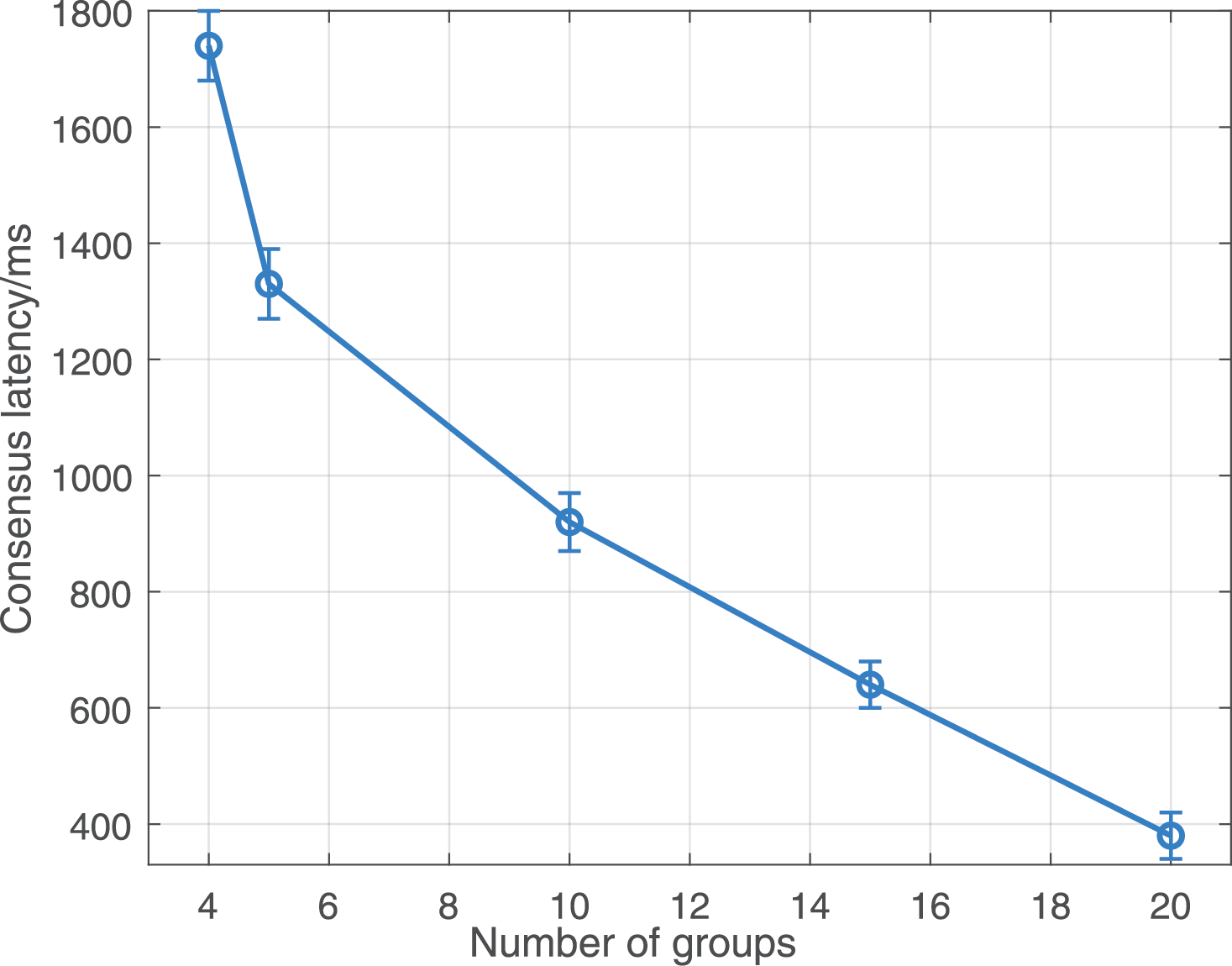
Figure 9: Experiment 2 comparison of consensus latency
Based on Experiment 1, it can be observed from Fig. 8 that while the consensus delay of all four algorithms rises with the increase in the number of consensus nodes, the consensus delay of CG-PBFT is considerably lower than that of the other three algorithms under the same node count and group count. From Fig. 9, it is evident that with the same number of consensus nodes, the consensus delay of CG-PBFT gradually decreases as the number of groups increases. According to the experimental results in Figs. 8 and 9, it can be concluded that the consensus delay performance of CG-PBFT outperforms the other three algorithms. Moreover, with the same number of nodes, CG-PBFT can optimize the number of groups to reduce consensus delay, making it adaptable to diverse task scenarios.
The CG-PBFT consensus algorithm designed in this paper incorporates a reputation score evaluation mechanism, selecting nodes with high reputation scores as primary nodes and leading nodes. Nodes with a reputation score below
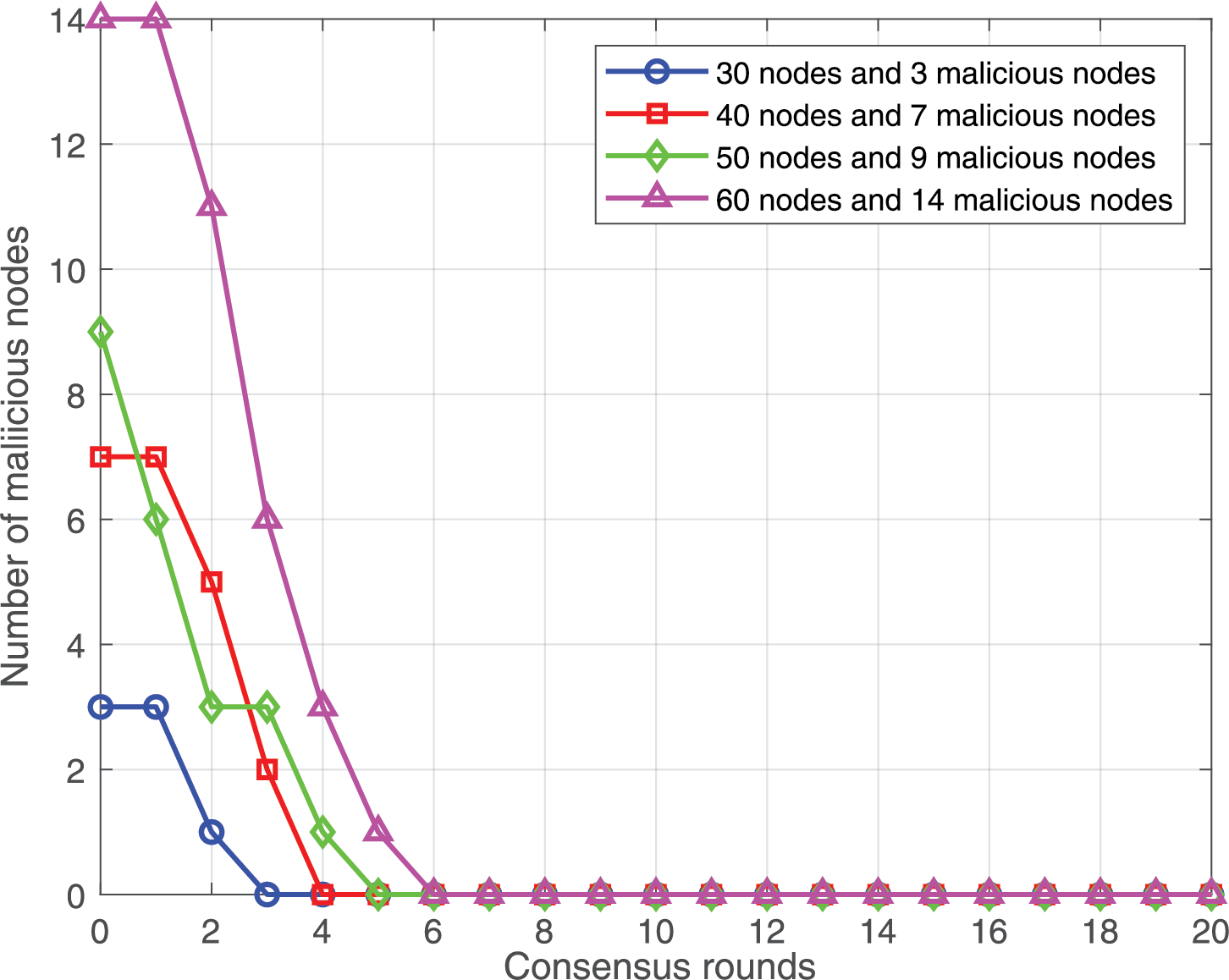
Figure 10: Comparison of the number of malicious nodes
According to the experimental results, the count of malicious nodes will gradually decline as the number of consensus rounds increases. Eventually, CG-PBFT can eliminate malicious nodes in the entire network within 6 consensus rounds. In comparison to PBFT, the CG-PBFT consensus algorithm can notably enhance the system network’s security.
Meanwhile, this paper conducts quantitative experiments targeting specific security threat models, such as the Sybil attack model, replay attack model, and DoS attack model. To verify its security, the CG-PBFT algorithm is compared with traditional PBFT, CPBFT, and RBFT.
For the Sybil attack model, this paper designs the following experiment: 5%, 10%, and 15% Sybil nodes are injected into networks with 30, 50, and 80 nodes, respectively. The security is verified through 100 consensus rounds, and the experimental results are presented in Table 4.
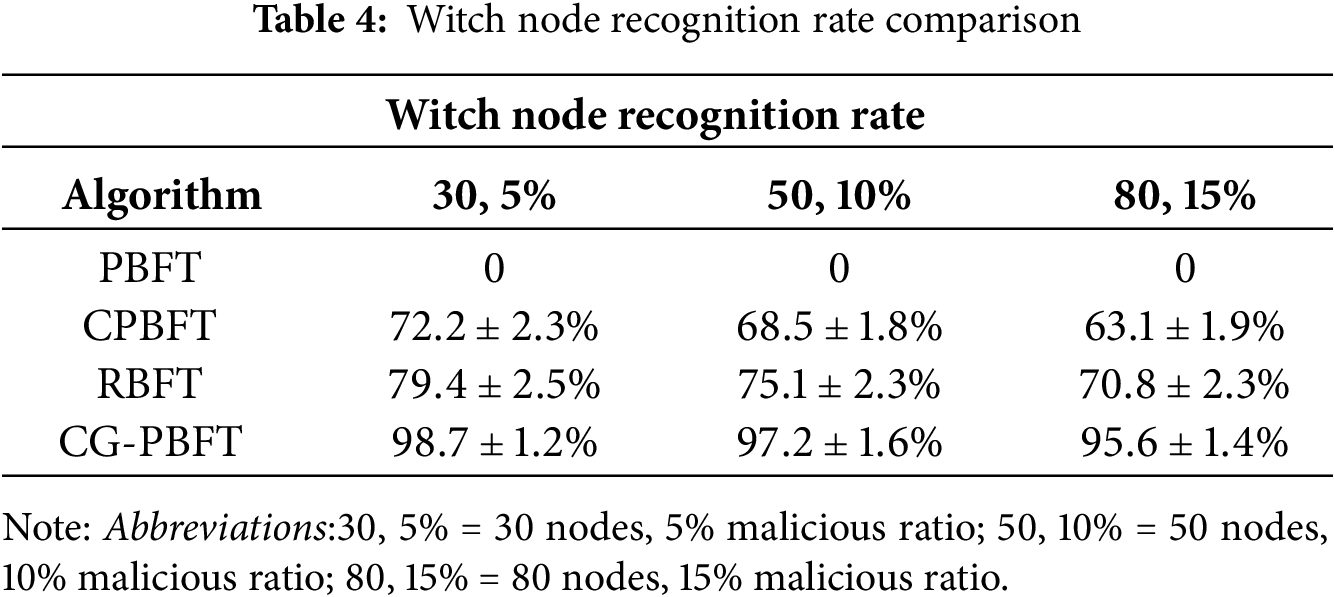
According to the experimental results, CG-PBFT consistently maintains a high Sybil node identification rate through reputation score evaluation, node authentication, and grouping mechanisms, enabling it to effectively resist Sybil attacks.
For the replay attack model, this paper designs the following experiment: 30 legitimate identity authentication messages are intercepted, and an attacker is simulated to resend them. The experimental intervals are set to 1, 5, and 10 s, and the experiment is repeated 100 times to verify the defense effect of CG-PBFT. The experimental results are shown in Table 5.
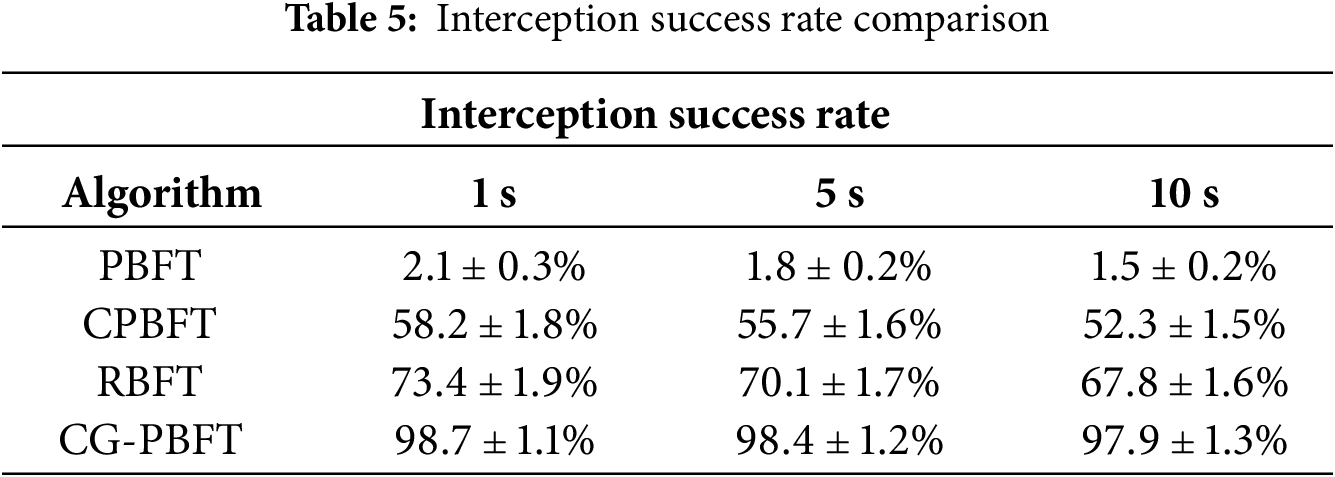
From the experimental findings, it is evident that CG-PBFT achieves a higher interception success rate than the other three algorithms and can effectively intercept replay messages.
For the DoS attack model, this paper designs the following experiment: 100 nodes are divided into 5 groups, and 500 invalid consensus requests are sent per second to 20% of the nodes for 30 min. The experiment is repeated 100 times to verify the performance changes of CG-PBFT, with the experimental results presented in Table 6.
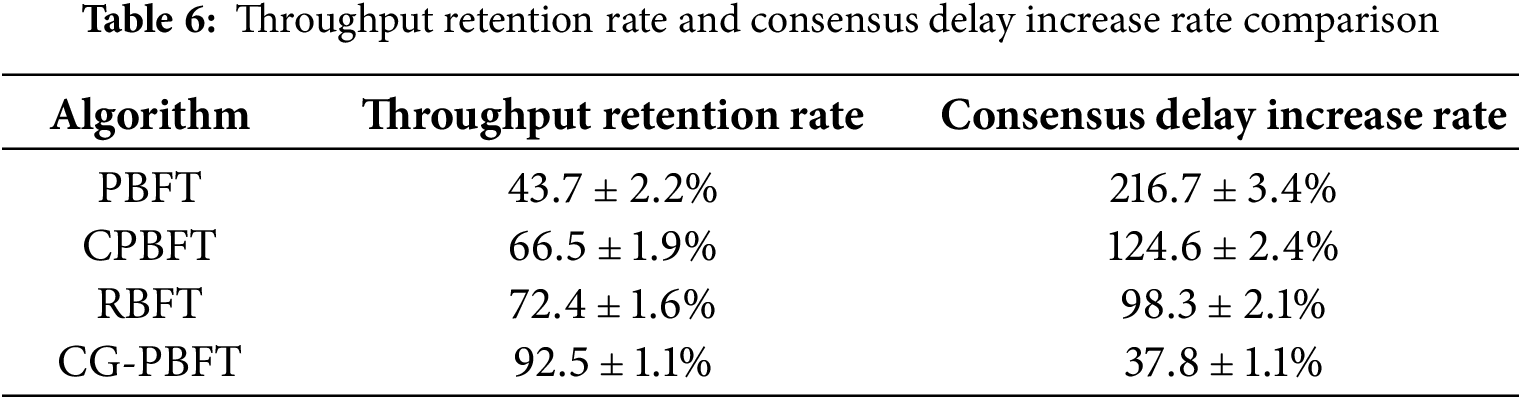
As can be seen from the table, CG-PBFT can maintain a low consensus latency increase rate and a high throughput retention rate under DoS attacks, enabling it to effectively resist DoS attacks.
In summary, the CG-PBFT consensus algorithm can notably enhance the security of the system network.
5.5 Computational Cost Analysis
To confirm the practical feasibility of the algorithm, we strictly simulate the UAV embedded hardware environment (NVIDIA Jetson Xavier NX processor with 2 GB memory). Experiments are conducted 100 times under 30, 50, and 70 nodes to analyze its CPU utilization and memory usage, and the experimental results are displayed in Table 7.
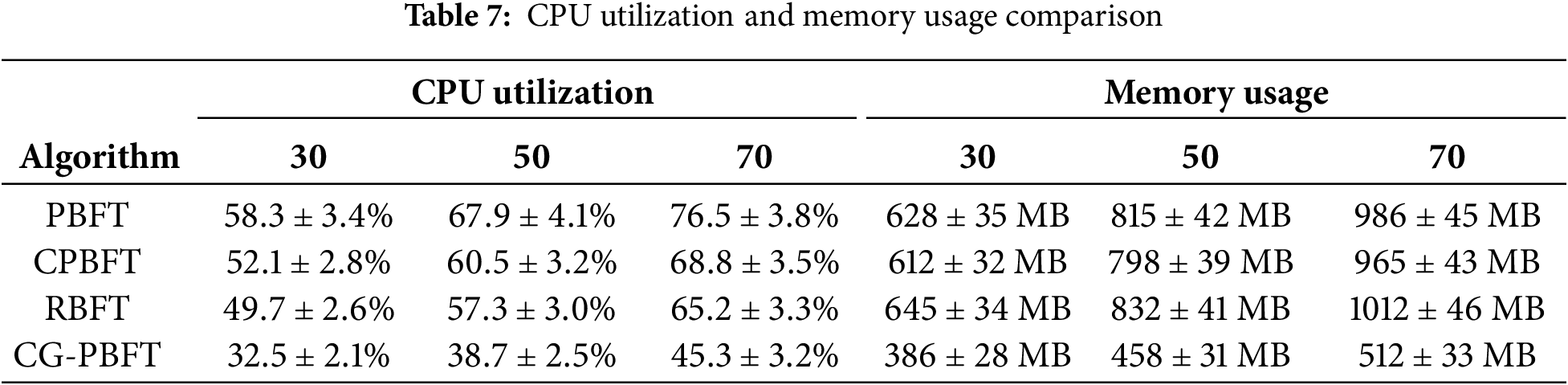
According to the experimental results, the CPU utilization and memory usage of CG-PBFT are superior to those of the other three algorithms. It meets the requirements of the UAV embedded hardware environment and possesses certain practical feasibility.
Based on the task scenarios of large-scale UAV clusters, this paper tackles the limitations of PBFT, including excessive communication overhead, low throughput, and difficulty in eliminating malicious nodes. It thus devises a PBFT consensus algorithm named CG-PBFT, which integrates reputation scoring and a grouping mechanism. Firstly, CG-PBFT introduces a reputation scoring evaluation framework atop the original PBFT consensus algorithm. Experimental verification shows that it can maximize the reliability of selecting primary and leading nodes,diminish the count of malicious nodes within the network, and bolster the network system’s security. Secondly, it employs group consensus methodologies and BLS aggregate signatures to optimize the consensus process and curtail communication complexity. Experimental outcomes reveal that, in comparison to the conventional PBFT consensus algorithm, CG-PBFT improves throughput, reduces consensus delay, and enhances the overall consensus efficiency. Finally, this paper indicates that CG-PBFT has a better effect than the traditional PBFT in the application scenarios of large-scale UAV clusters. However, the view change protocol of CG-PBFT still suffers from high latency when facing concentrated attacks by malicious nodes; moreover, it is currently only applicable to homogeneous UAV swarms, and its adaptability to heterogeneous nodes needs further optimization. In future research, we will optimize the view change mechanism and introduce predictive primary node election; extend it to the cross-cluster UAV consensus scenario; and integrate edge computing to reduce the local computational overhead of UAVs, thereby providing a more comprehensive solution for the consensus mechanism of distributed intelligent unmanned systems.
Acknowledgement: The authors are grateful to all the editors and anonymous reviewers for their comments and suggestions.
Funding Statement: This work was jointly supported by the following projects:Fund for technical areas of infrastructure strengthening plan projects under Grant 2023-JCJQ-JJ-0772.
Author Contributions: The authors confirm contribution to the paper as follows: study conception and design: Yuji Sang, Lijun Liu, Long Lv; data collection: Yuji Sang, Hemin Yin, Long Lv; analysis and interpretation of results: Yuji Sang, Husheng Wu, Long Lv; draft manuscript preparation: Yuji Sang, Lijun Liu, Long Lv. All authors reviewed the results and approved the final version of the manuscript.
Availability of Data and Materials: The data are contained within the article. And the authors confirm that the data supporting the findings of this study are available within the article.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest to report regarding the present study.
References
1. Zheng Z, Xie S, Dai HN, Chen X, Wang H. Blockchain challenges and opportunities: a survey. Int J Web Grid Serv. 2018;14(4):352–75. doi:10.1504/IJWGS.2018.095381. [Google Scholar] [CrossRef]
2. Alsunaidi SJ, Alhaidari FA. A survey of consensus algorithms for blockchain technology. In: Proceedings of the 2019 International Conference on Computer and Information Sciences (ICCIS); 2019 Apr 3–4; Sakaka, Saudi Arabia. p. 1–6. doi:10.1109/ICCISci.2019.8716424. [Google Scholar] [CrossRef]
3. Song J, Zhang P, Alkubati M, Bao Y, Yu G. Research advances on blockchain-as-a-service: architectures, applications and challenges. Digit Commun Netw. 2022;8(4):466–75. doi:10.1016/j.dcan.2021.02.001. [Google Scholar] [CrossRef]
4. Alghamdi TA, Khalid R, Javaid N. A survey of blockchain based systems: scalability issues and solutions, applications and future challenges. IEEE Access. 2024;12:79626–51. doi:10.1109/ACCESS.2024.3408868. [Google Scholar] [CrossRef]
5. Proof of stake [EB/OL]. [cited 2022 Sep 26]. Available from: https://en.bitcoin.it/wiki/Proof_of_Stake. [Google Scholar]
6. Saad SMS, Radzi RZRM. Comparative review of the blockchain consensus algorithm between proof of stake (POS) and delegated proof of stake (DPOS). Int J Innov Comput. 2020;10(2):27–32. doi:10.11113/IJIC.V10N2.272. [Google Scholar] [CrossRef]
7. Xiong Y, Hu C. Comparative research on blockchain consensus algorithms. In: Proceedings of the 2022 International Confer-ence on Blockchain Technology and Information Security (ICBCTIS); 2022 Jul 15–17; Huaihua City, China. p. 160–4. doi:10.1109/ICBCTIS55569.2022.00045. [Google Scholar] [CrossRef]
8. Yan S. Analysis on blockchain consensus mechanism based on proof of work and proof of stake. In: Proceedings of the 2022 International Conference on Data Analytics, Computing and Artificial Intelligence (ICDACAI); 2022 Aug 15–16; Zakopane, Poland. p. 464–7. doi:10.1109/ICDACAI57211.2022.00098. [Google Scholar] [CrossRef]
9. Ferdous MS, Chowdhury MJM, Hoque MA. A survey of consensus algorithms in public blockchain systems for cryptocurrencies. J Netw Comput Appl. 2021;182:103035. doi:10.1016/j.jnca.2021.103035. [Google Scholar] [CrossRef]
10. Pease M, Shostak R, Lamport L. Reaching agreement in the presence of faults. J ACM. 1980;27:228–34. doi:10.1145/322186.322188. [Google Scholar] [CrossRef]
11. Lamport L, Shostak R, Pease M. The Byzantine generals problem. ACM Trans Program Lang Syst. 1982;4(3):382–401. doi:10.1145/357172.357176. [Google Scholar] [CrossRef]
12. Castro M, Liskov B. Practical byzantine fault tolerance and proactive recovery. ACM Trans Comput Syst. 2002;20(4):398–461. doi:10.1145/571637.571640. [Google Scholar] [CrossRef]
13. Li J, Jia YY, Zhang L. Practical Byzantine fault tolerance consensus algorithm of MuSig multi-signature. Appl Res Comput. 2025;42(2):352–6. doi:10.19734/j.issn.1001-3695.2024.06.0227. [Google Scholar] [CrossRef]
14. Lao L, Dai X, Xiao B, Guo S. G-PBFT: a location-based and scalable consensus protocol for IoT-blockchain applications. In: Proceedings of the 2020 IEEE International Parallel and Distributed Processing Symposium (IPDPS); 2020 May 18–22; New Orleans, LA, USA. New York, NY, USA: IEEE; 2020. doi:10.1109/IPDPS47924.2020.00074. [Google Scholar] [CrossRef]
15. Wang Y, Song Z, Cheng T. Improvement research of PBFT consensus algorithm based on credit. Singapore: Springer; 2019. doi:10.1007/978-981-15-2777-7_4. [Google Scholar] [CrossRef]
16. Xu GX, Wang YS. Improved PBFT algorithm based on vague sets. Secur Commun Netw. 2022;2022:6144664. doi:10.1155/2022/6144664. [Google Scholar] [CrossRef]
17. Yang J, Jia Z, Su R, Wu X, Qin J. Improved fault-tolerant consensus based on the PBFT algorithm. IEEE Access. 2022;10:30274–83. doi:10.1109/ACCESS.2022.3153701. [Google Scholar] [CrossRef]
18. Cui Z, Xue F, Zhang S, Cai X, Cao Y, Zhang W, et al. A hybrid blockchain-based identity authentication scheme for multi-WSN. IEEE Trans Serv Comput. 2020;13(2):241–51. doi:10.1109/TSC.2020.2964537. [Google Scholar] [CrossRef]
19. Raghav, Andola N, Venkatesan S, Verma S. PoEWAL: a lightweight consensus mechanism for blockchain in IoT. Pervasive Mob Comput. 2020;69(1):101291. doi:10.1016/j.pmcj.2020.101291. [Google Scholar] [CrossRef]
20. Roman N, Vrabi R, Corn M, Požrl T, Diaci J. Distributed logistics platform based on blockchain and IoT. Procedia CIRP. 2019;81:826–31. doi:10.1016/j.procir.2019.03.207. [Google Scholar] [CrossRef]
21. Qashlan A, Nanda P, He X, Mohanty M. Privacy-preserving mechanism in smart home using blockchain. IEEE Access. 2021;9:103651–69. doi:10.1109/ACCESS.2021.3098795. [Google Scholar] [CrossRef]
22. Haque EU, Abbasi W, Almogren A, Choi J, Altameem A, Rehman AU, et al. Performance enhancement in blockchain based IoT data sharing using lightweight consensus algorithm. Sci Rep. 2024;14:26561. doi:10.1038/s41598-024-77706-x. [Google Scholar] [PubMed] [CrossRef]
23. Kong L, Chen B, Hu F, Zhang J. Lightweight mutual authentication scheme enabled by stateless blockchain for UAV networks. Secur Commun Netw. 2022;2022:2330052. doi:10.1155/2022/2330052. [Google Scholar] [CrossRef]
24. Zhang L. A cross network identity authentication scheme for UAVs based on layered blockchain technology. In: Advances in intelligent networking and collaborative systems. Cham, Switzerland: Springer; 2024. doi:10.1007/978-3-031-72322-3_13. [Google Scholar] [CrossRef]
25. Boneh D, Lynn B, Shacham H. Short signatures from the weil pairing. In: International Conference on the Theory and Application of Cryptology And Information Security. Berlin/Heidelberg, Germany: Springer; 2001. p. 514–32. doi:10.1007/3-540-45682-1_30. [Google Scholar] [CrossRef]
26. Zhu W, Shi L, Li J, Cao B, Wei K, Wang Z, et al. Trustworthy blockchain-assisted federated learning: decentralized reputation management and performance optimization. IEEE Internet Things J. 2025;12(3):2890–905. doi:10.1109/JIOT.2024.3480995. [Google Scholar] [CrossRef]
27. Ye Z, Wen T, Liu Z, Song X, Fu C. An efficient dynamic trust evaluation model for wireless sensor networks. J Sens. 2017;2017:7864671. doi:10.1155/2017/7864671. [Google Scholar] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF Downloads
Downloads
 Citation Tools
Citation Tools