 Open Access
Open Access
ARTICLE
A Low-Cost Network Topology Obfuscation Method for Critical Node Protection
1 School of Cyber Science and Engineering, Zhengzhou University, Zhengzhou, China
2 Key Laboratory of Cyberspace Situation Awareness of Henan Province, Zhengzhou, China
* Corresponding Author: Fuxiang Yuan. Email:
(This article belongs to the Special Issue: Cyberspace Mapping and Anti-Mapping Techniques)
Computers, Materials & Continua 2026, 87(2), 52 https://doi.org/10.32604/cmc.2026.075072
Received 24 October 2025; Accepted 18 December 2025; Issue published 12 March 2026
Abstract
Network topology obfuscation is a technique aimed at protecting critical nodes and links from disruptions such as Link Flooding Attack (LFA). Currently, there are limited topology obfuscation methods for protecting critical nodes, and the existing approaches mainly achieve obfuscation by extensively modifying network links, resulting in high costs. To address this issue, this paper proposes a low-cost network topology obfuscation method dedicated to critical node protection, with its core innovation lying in a lightweight obfuscation architecture based on Fake Node Clusters (FNCs). Firstly, the protected network is modeled as an undirected graph, and an adjacency matrix is constructed to quantify the network scale and structural characteristics. Then, a fake node cluster generation algorithm is designed to construct an FNC adapted to the target network. Finally, a heuristic obfuscated topology generation algorithm is proposed. By optimizing the deployment positions of Fake Nodes Clusters (FNCs) in the protected network, this algorithm effectively reduces the number of FNCs required to generate the obfuscated topology, further lowering the obfuscation cost. Extensive experiments were conducted on the public Topology Zoo dataset, categorizing network topologies by node count into small-scale ([0, 50)), medium-scale ([50, 100)), and large-scale ([100, 200)) groups. The experimental results demonstrate that the proposed approach achieves excellent obfuscation performance, reducing the critical node recognition rate toKeywords
The Internet is a complex network system composed of massive nodes interconnected via communication links [1]. As the core carrier for network operations, nodes undertake key tasks such as data reception, processing, storage, and forwarding. According to the differences in the importance of nodes within the network topology, they can be categorized into critical nodes and normal nodes. Among them, the failure or abnormality of critical nodes is highly likely to trigger network cascading failure [2], which in turn leads to the interruption of data transmission links and the deterioration of service quality and may even cause complete network paralysis in severe cases [3–5].
Prior to launching an attack, attackers tend to conduct network reconnaissance. By accurately identifying critical nodes and implementing targeted attacks, they aim to maximize the destructive effect, with typical attack methods including Link Flooding Attack (LFA) [6,7]. Specifically, attackers typically utilize topology probing tools such as Traceroute to scan the target network [8,9], locate critical nodes based on the topology information obtained through probing, and ultimately render them in a state of service unavailability by injecting attack traffic [10,11]. The cascading effects triggered by the failure of such nodes will further expand the scope of the attack’s impact, leading to large-scale network communication anomalies. Currently, systematic reconnaissance prior to attacks has become a core means for attackers to enhance their destructive effectiveness.
Network topology obfuscation is currently the main approach to defending against attacks such as LFA [12–15] and protecting critical nodes. As an active defense mechanism [16,17], its fundamental difference from traditional passive defense lies in the fact that this strategy determines critical nodes through node importance evaluation indicators before an attacker launches an attack [18,19], and then actively camouflages [20] the protected network according to the obfuscation strategy, preventing attackers from obtaining the real network topology. Studies have shown that the attack effect of LFA highly depends on the accuracy of the obtained topology information. If the topological information is distorted, attackers need to increase the traffic by at least five times to achieve the effect of blocking network communication [21]. In addition, since the attackers obtain a confused topology through network reconnaissance, they will identify the wrong critical nodes, and the attacks they launch against critical nodes will be redirected to normal nodes, thus effectively protecting the critical nodes [22].
Currently, research on topology obfuscation technology for critical node protection is relatively scarce. Traditional network topology obfuscation methods mainly use local indicators such as degree centrality [23] and betweenness centrality [20] in the stage of evaluating critical nodes. These indicators have played an important role in early network topology research. However, with the continuous evolution of network attack methods and the increasing complexity of network structures, the limitations of traditional indicators have gradually emerged. When determining critical nodes, the above indicators focus on the attributes of the nodes themselves and do not take into account the global characteristics of the network topology enough. However, attackers seem to pay more attention to nodes with high global importance during network attacks because their failures cause more serious damage to the entire network. This leads to the fact that the network topology defense systems built based on traditional indicators are difficult to achieve ideal defense effects when resisting attacks against globally important critical nodes. In addition, the deployment of confused topologies increases the cost for defenders. How to ensure the lowest operation complexity during the conversion from the original topology to the confused topology is the key to improving the practicality of defense.
Zhu et al. were the first to explore the value and potential of eigenvector centrality in evaluating the global importance of nodes. Eigenvector centrality [24] not only considers the importance of the node itself but also incorporates the importance weight of its adjacent nodes [25]. Based on a random link modification strategy, they designed a network topology obfuscation method called EigenObfu, which can defend against attack methods that determine critical nodes based on eigenvector centrality and is currently the only topology obfuscation method targeting attacks based on eigenvector centrality. However, this method has the problem of modifying a large number of original topology links when generating the confused topology, resulting in a high network adjustment cost.
To address the above problems, this paper proposes a low-cost network topology obfuscation method for critical node protection. It generates Fake Node Clusters (FNCs) through a fake node cluster generation algorithm and optimizes the insertion position of the FNCs using a confused topology generation algorithm to construct a low-cost confused topology. The main contributions of this paper are as follows:
• A low-cost network topology obfuscation framework based on the Fake Node Cluster (FNC) is proposed. The FNC is designed based on Software-Defined Networking (SDN) technology [26], and the confused topology is generated by optimizing the deployment strategy of the FNC. This framework can effectively resist LFA attacks that use ICMP Traceroute, TCP Traceroute, and UDP Traceroute for network reconnaissance and supports the obfuscation of critical nodes in any proportion.
• A low-cost fake node cluster generation algorithm is proposed. The FNC is designed as a chordal graph structure with multiple intermediate nodes in parallel, which can interfere with attackers’ identification of critical nodes at a low cost. Meanwhile, the use of fake nodes instead of traditional physical nodes in obfuscation clearly reduces the obfuscation cost.
• A heuristic obfuscated topology generation algorithm is proposed. It adopts a greedy strategy to select positions with the maximum hidden gain for critical nodes as FNC insertion positions to generate obfuscated topologies, effectively reducing the required number of FNCs and further lowering the obfuscation cost.
The rest of this paper is organized as follows: Section 2 analyzes the typical method EigenObfu [27]. Section 3 details the principle framework and main stages of the proposed method and provides an in-depth explanation of the core algorithms. Section 4 verifies the effectiveness of the proposed method, analyzes the algorithm complexity, and compares it with the existing typical method, EigenObfu, in terms of obfuscation cost. Section 5 summarizes the proposed method and looks forward to the next steps.
Zhu et al. proposed a network topology obfuscation method called EigenObfu for critical node protection. This method employs eigenvector centrality as the evaluation metric for critical nodes. Its advantage lies in the fact that eigenvector centrality can take into account the importance of both the node itself and its neighboring nodes, enabling a more comprehensive portrayal of the global importance of nodes [28]. Based on this, EigenObfu generates the obfuscated topology through a candidate topology generation stage and an obfuscated topology selection stage. Its input is the adjacency matrix A of the protected network topology, and the output is the obfuscated topology. The main process of EigenObfu is shown in Fig. 1).
• Candidate topology generation. First, the eigenvector centrality (EC) of each node is calculated, and the set of critical nodes K is determined accordingly. Subsequently, the network topology is randomly modified with a fixed probability
• Topology selection. First, the similarity of each obfuscated topology is measured based on the adjacency matrix and Laplacian matrix. Then, the one with the maximum similarity is selected as the optimal obfuscated topology and output as the final obfuscated topology.
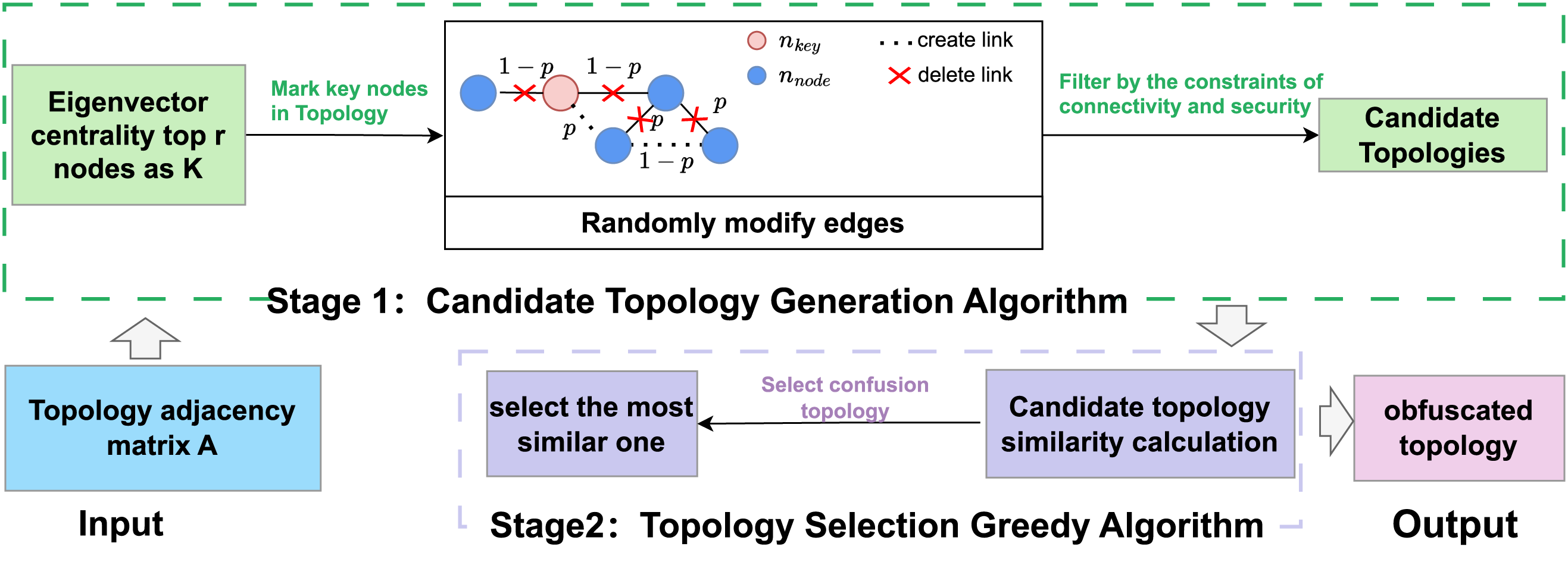
Figure 1: Key operations of EigenObfu.
Although the EigenObfu method uses eigenvector centrality as the critical node evaluation standard, which can more comprehensively reflect the importance of critical nodes and can effectively obfuscate critical nodes, it has certain limitations in the candidate topology generation algorithm. This method disconnects and generates links with a fixed probability, ignoring the differences among different types of topologies. Meanwhile, the randomized link adjustment mechanism results in a high degree of uncertainty in the obfuscation of the generated candidate topologies. It is difficult to precisely guide the topology obfuscation towards the optimal obfuscation direction only through the security constraint and the connectivity constraint, resulting in a lack of targeted modifications to the original topology, excessive modifications to the original topology, and a high cost of network structure adjustment. The team has also recognized this problem. Therefore, in the obfuscated topology selection stage, the similarity is used to screen and reduce the modification range of the topology. However, the obfuscation cost remains at a relatively high level.
To address the issue of excessive modifications to the original network and high network adjustment costs during the obfuscation process in existing network topology obfuscation methods, this paper proposes a low-cost network topology obfuscation method for critical node protection.
Fig. 2 illustrates the proposed method’s framework. First, the protected network topology is modeled as an undirected graph G, and its adjacency matrix A is constructed to compute network size |V |. Then, by analyzing the impact of local topological structure changes in the network on the ranking of node importance, the FNC structure with multiple parallel intermediary nodes is designed, and based on this, a dynamic fake node cluster generation algorithm is proposed to generate the FNC that adapted to the protected network scale |V |. Finally, to protect any proportion of critical nodes while minimizing FNC deployments, a heuristic obfuscated topology generation algorithm is proposed. This algorithm determines the set of protected critical nodes K based on eigenvector centrality, selects and determines an effective sequence of FNC insertion positions
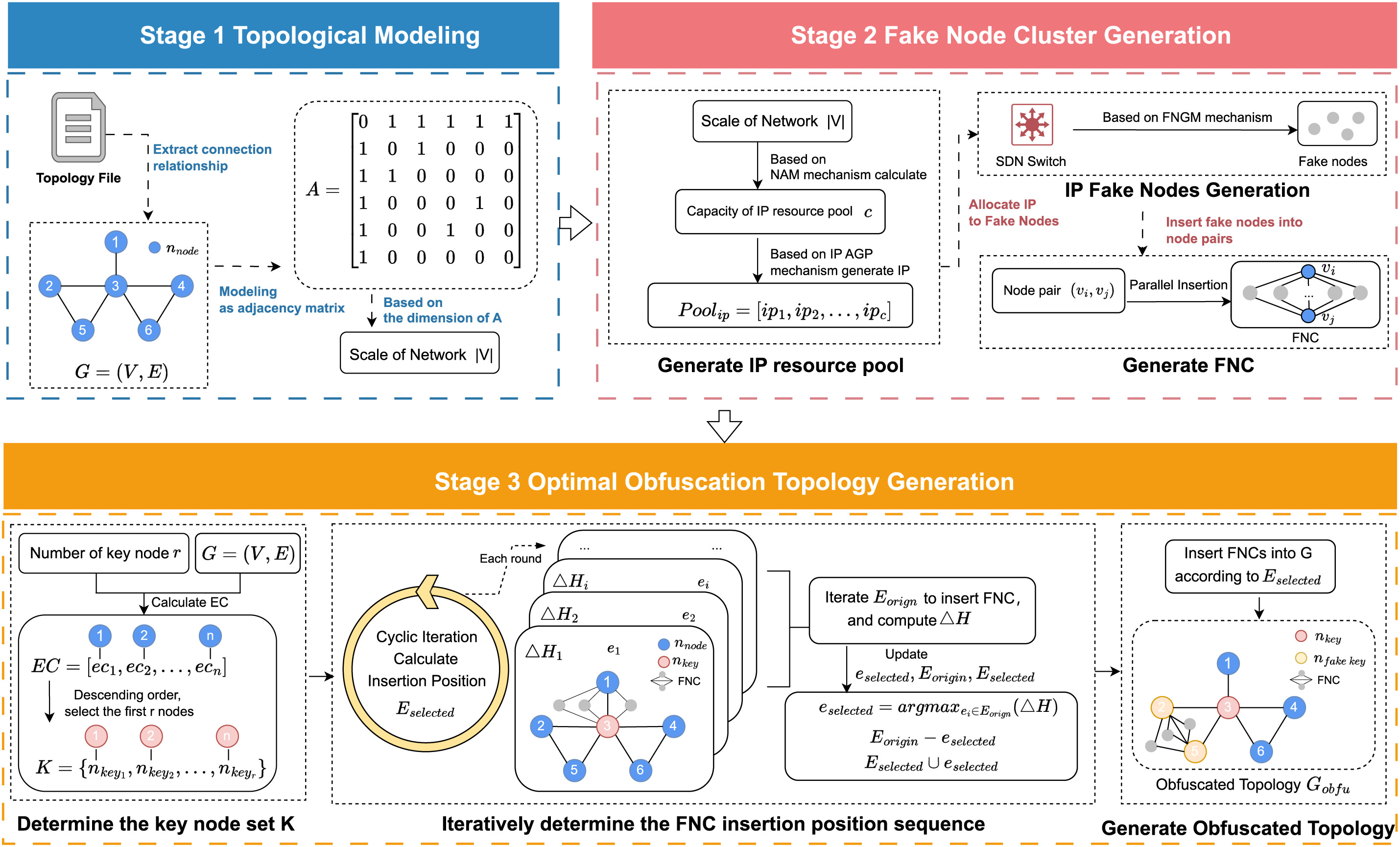
Figure 2: Method framework.
The proposed method mainly includes the following three stages. For the convenience of description, the mathematical symbols used in this paper and their meanings are shown in Table 1.
Stage 1: Topological Modeling. Read the file recording the topology of the protected network N, extract the nodes and connection relationships, and uniformly number them (
Stage 2: Fake Node Cluster Generation. The FNC is designed as a chordal graph structure with multiple parallel intermediary nodes. By constructing a large number of redundant paths with single parallel intermediary nodes between adjacent nodes, it can effectively disrupt key node identification methods based on EC. Based on this structure, this paper proposes a dynamic fake node cluster generation algorithm. Software-Defined Networking (SDN) switches are used to generate fake nodes instead of physical nodes to reduce hardware resource consumption.
First, according to the scale |V | of the protected network N, a Network Adaptation Model (NAM) is designed to determine the capacity
Stage 3: Obfuscated Topology Generation. To reduce the number of FNC insertions and achieve the protection of any proportion of critical nodes, a heuristic obfuscated topology generation algorithm is proposed. First, calculate each node’s EC in undirected graph G—EC is a widely recognized node importance metric integrating direct connections and neighbor influence. Nodes are sorted descendingly by EC, and the top
3.2 Fake Node Cluster Generation
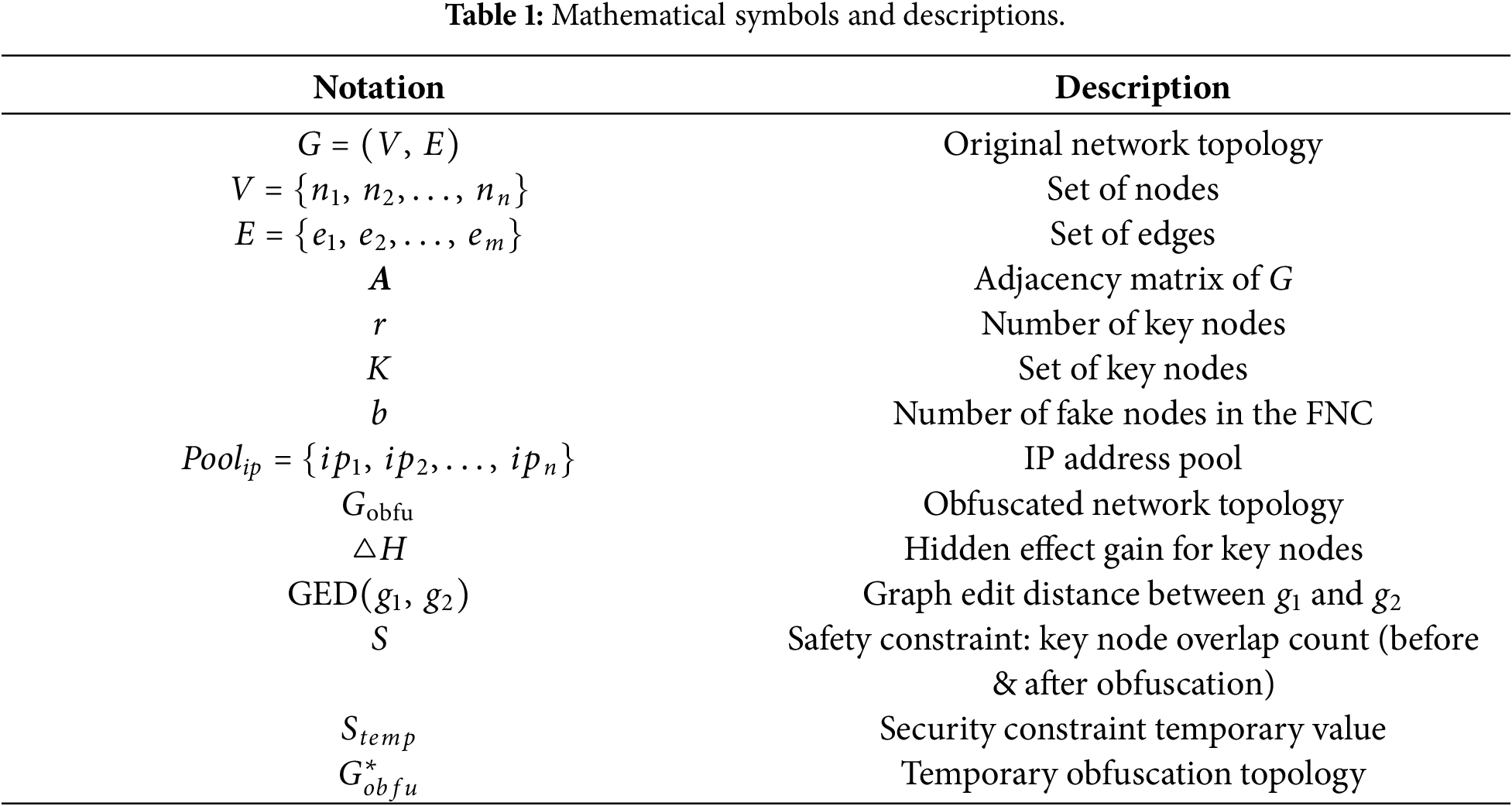
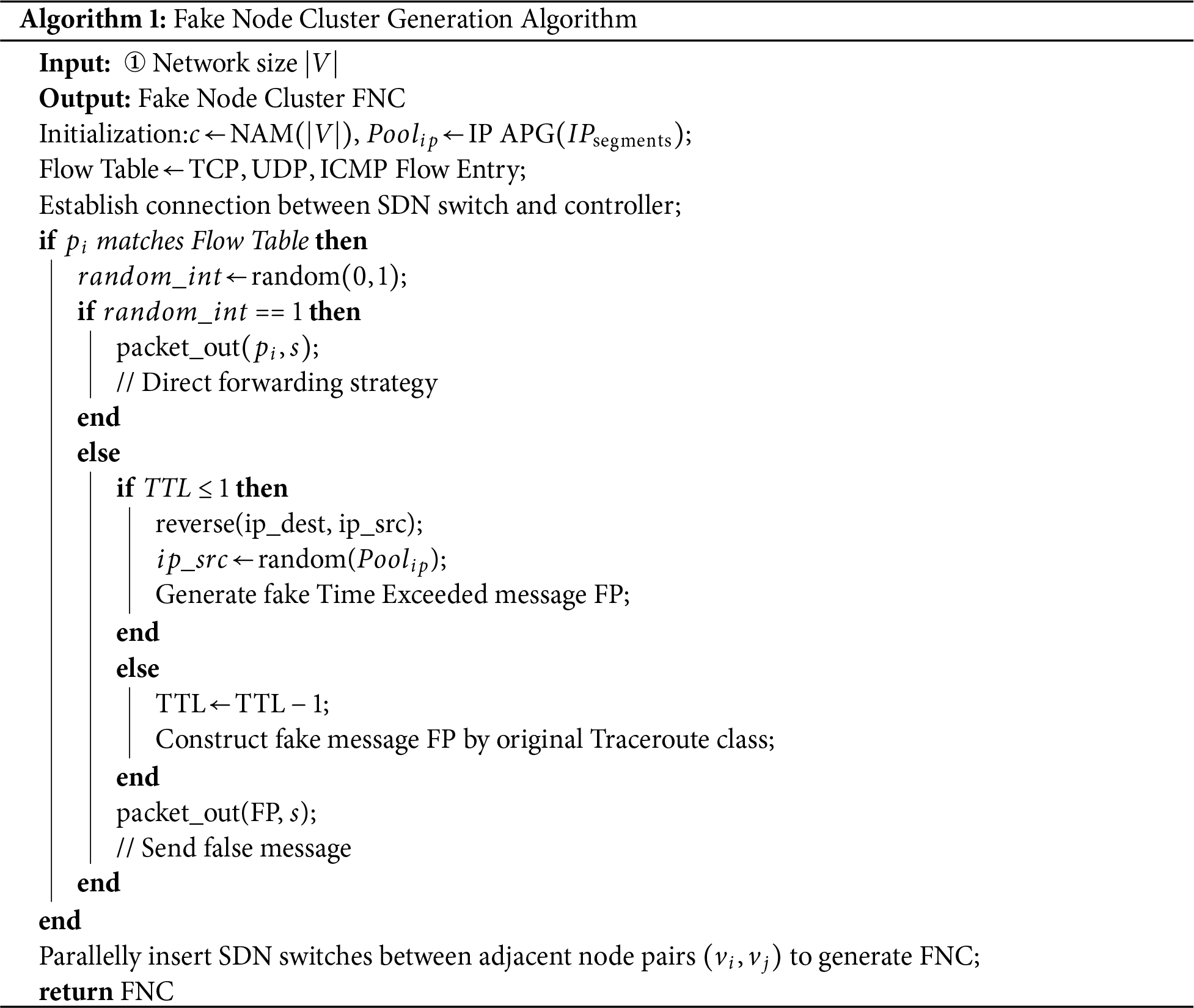
To disrupt attackers’ identification of critical nodes, this paper designs a Fake Node Cluster (FNC) with a chordal graph structure featuring multiple parallel intermediary nodes, as shown in Fig. 3. Its core mechanism lies in rapidly constructing multiple redundant paths with single parallel intermediary nodes between two adjacent nodes, which can effectively interfere with key node identification methods centered around EC. The implementation process of the FNC is presented in Algorithm 1, mainly including the following three steps.
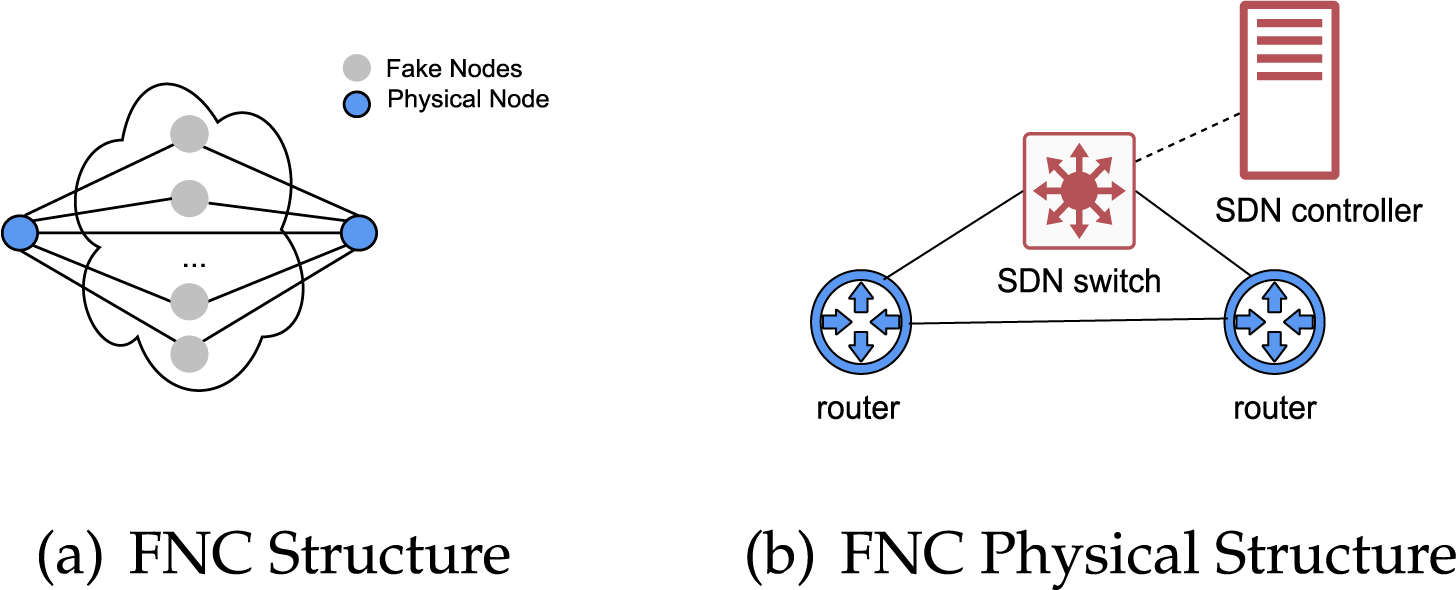
Figure 3: The FNC structure and its physical structure.
Step 1: Generate an IP Address Resource Pool. According to the scale |V | of the protected network N, the number
The NAM describes the relationship between the network scale |V | and the capacity
The reason for limiting the capacity
Here,
• When
• When
• When
This indicates that there is a marginal diminishing benefit characteristic between the capacity
The IP AGP aims to minimize fake node IP address similarity and consists of the following two policies.
• Segment Filtering Strategy. Addresses are preferentially allocated from business network segments with a large host address space (such as /16) and listed in a whitelist, and fake IPs are generated by changing the host number.
• Maximize IP Differentiation Strategy. Each fake IP is assigned to a different /30 subnet (host number digits
Step 2: IP Address Allocation and Fake Intermediary Node Generation. The SDN controller dynamically allocates the IP addresses in the
First, we design a flow table-based flow identification strategy, which can detect three types of active Traceroute detection traffic: TCP Traceroute, UDP Traceroute, and ICMP Traceroute. During the LFA reconnaissance phase, Traceroute is a common tool for obtaining network topology. When Traceroute detection packets are detected in the network, it can be determined as the preparatory behavior of an attacker before launching an LFA attack. The characteristics of the three types of traceroute detections are shown in Table 2.
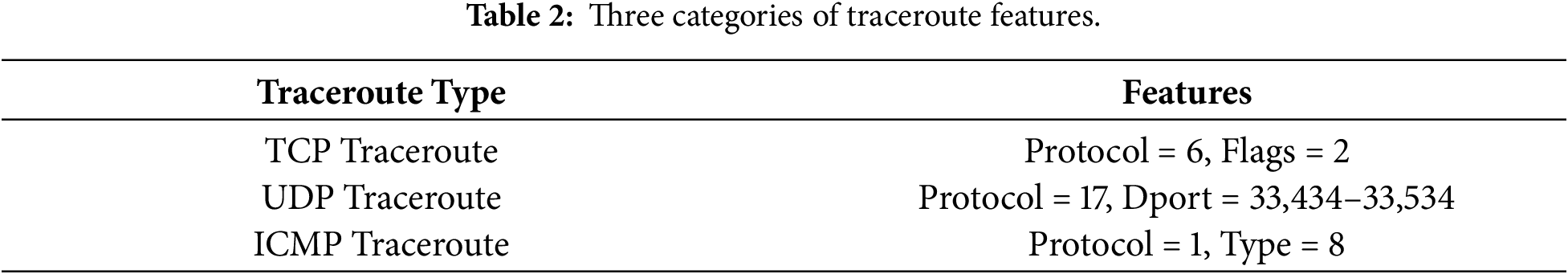
For the above characteristics of Traceroute detection, the algorithm creates a flow table in the SDN controller. Flow table entries for identifying the three types of traceroute detections (TCP Flow Entry, UDP Flow Entry, and ICMP Flow Entry) are designed and configured based on the protocol number and key field values, as shown in Eqs. (3)–(5).
When designing the UDP Flow Entry, while traditional UDP Traceroute uses a destination port (dport) range of 33,434–33,534, attackers can bypass detection by altering this number. Therefore, all UDP messages are recognized when designing this flow table entry.
The second component is a dual-strategy dynamically switched message forgery strategy, where the selection between the two strategies is determined by a random number,
• Direct Forwarding Strategy. Traceroute probe messages forwarded to the controller are re-routed to switch
• Fake Jamming Strategy. This strategy employs differentiated processing based on the Time-to-Live (TTL) field value: For packets with a TTL value less than or equal to 1, the original source IP address is set as the destination IP address. Concurrently, an IP address is randomly selected from the IP address pool and assigned as the source IP address. A fake Time Exceeded packet (FP) is then generated using packet forgery techniques and returned to switch
Step 3: Fake Node Cluster Construction. To achieve persistent perturbation of the local topology, FNC must be permanently introduced into the protected network topology. For neighboring node pairs
3.3 Obfuscated Topology Generation
To generate effective obfuscated topologies and minimize FNCs, thus reducing obfuscation cost, a heuristic obfuscated topology generation algorithm is designed, consisting of three main steps.
Step 1: Determine the set of key nodes to be protected.
First, the EC value of each node in the undirected graph
where
where
Step 2: lteratively determine the FNC insertion position sequence.
Firstly, remove
Here,
Repeat iteration until the maximum number of iterations,
Step 3: Generate the obfuscation topology. If the generated FNC insertion location sequence
4 Experimental Results and Analysis
To validate the effectiveness of the proposed method, we employed the Topology Zoo dataset [29] and built a prototype system of the proposed method on the open-source SDN controller Ryu [30,31] and the network simulator Mininet [32]. The experiments were conducted in two aspects:
• Evaluating the obfuscation effectiveness of the proposed method on network topologies of different scales.
• Comparing the obfuscation costs with the typical method EigenObfu [27].
The experimental setup of this paper is shown in Table 3, which includes experimental categories, data sources, parameter settings, involved methods, and evaluation metrics.
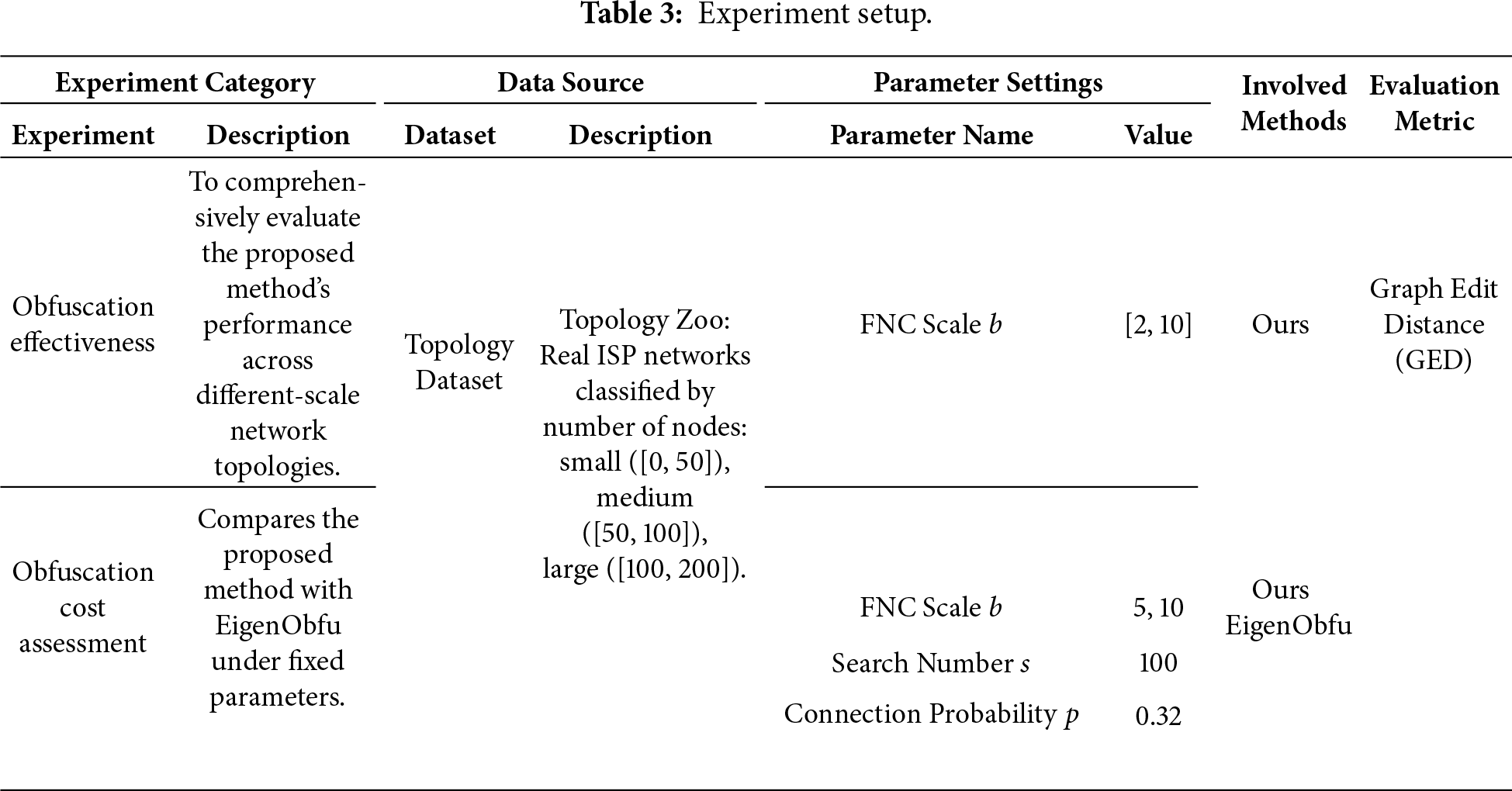
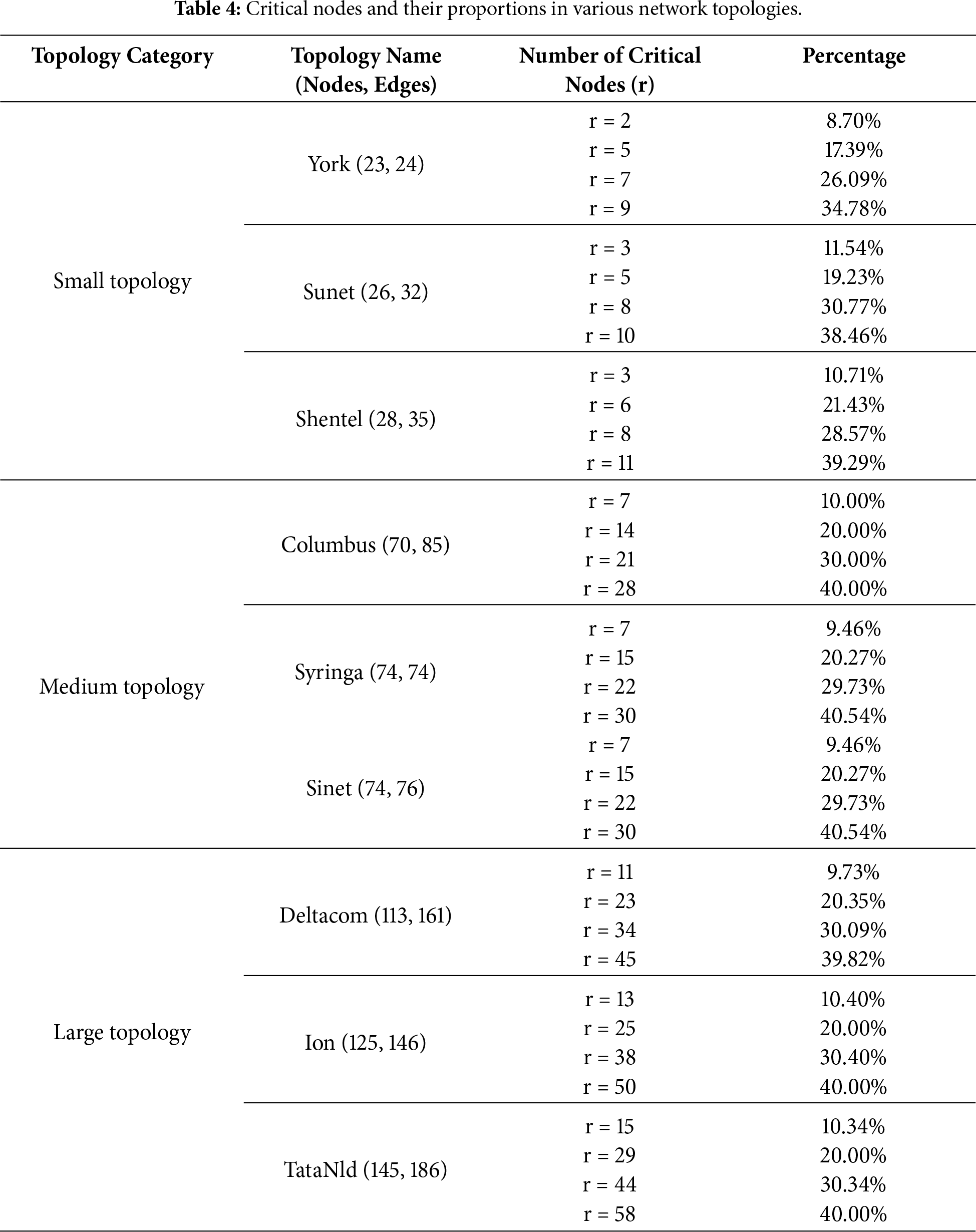
The Topology Zoo, a public dataset of real ISP network topologies, is recognized for its representativeness and practical value. To comprehensively evaluate our method’s obfuscation effect and cost across network scales, we selected nine representative real ISP topologies from this dataset. These topologies are categorized by node counts: small
In the experiment on obfuscation effectiveness, the obfuscation effect of the proposed method mainly depends on the FNC scale
In the experiment on obfuscation cost evaluation, since the obfuscation effect of the proposed method is closely related to the FNC scale, to ensure its adaptability under different network scales, the FNC scale
We quantify network topology obfuscation cost using Graph Edit Distance (GED) [33]. GED represents the minimum edit path cost to transform graph
Here,
4.2 Topology Obfuscation Validity
In this subsection, experiments are conducted on network topologies of varying scales retrieved from the Topology Zoo dataset (as shown in Table 4), with an emphasis on evaluating the obfuscation capability of the proposed method under different network scales and critical node proportions and conducting numerical simulations on the key simulation parameter of the proposed method—FNC scale b—to explore its influence on the obfuscation effect of network topologies.
Since the proposed method incorporates security constraints during its design, results are only output when all critical nodes are fully obfuscated. Therefore, the presence of an obfuscation cost (GED) indicates successful obfuscation. The experimental results are shown in Fig. 4.
• Small topologies (York, Sunet, Shentel). Across different critical node ratios, setting
• Medium-sized topologies (Columbus, Syringa, Sinet). Columbus and Syringa exhibit stable GED when
• Large topologies (Deltacom, Ion, TataNld). Effective obfuscation requires
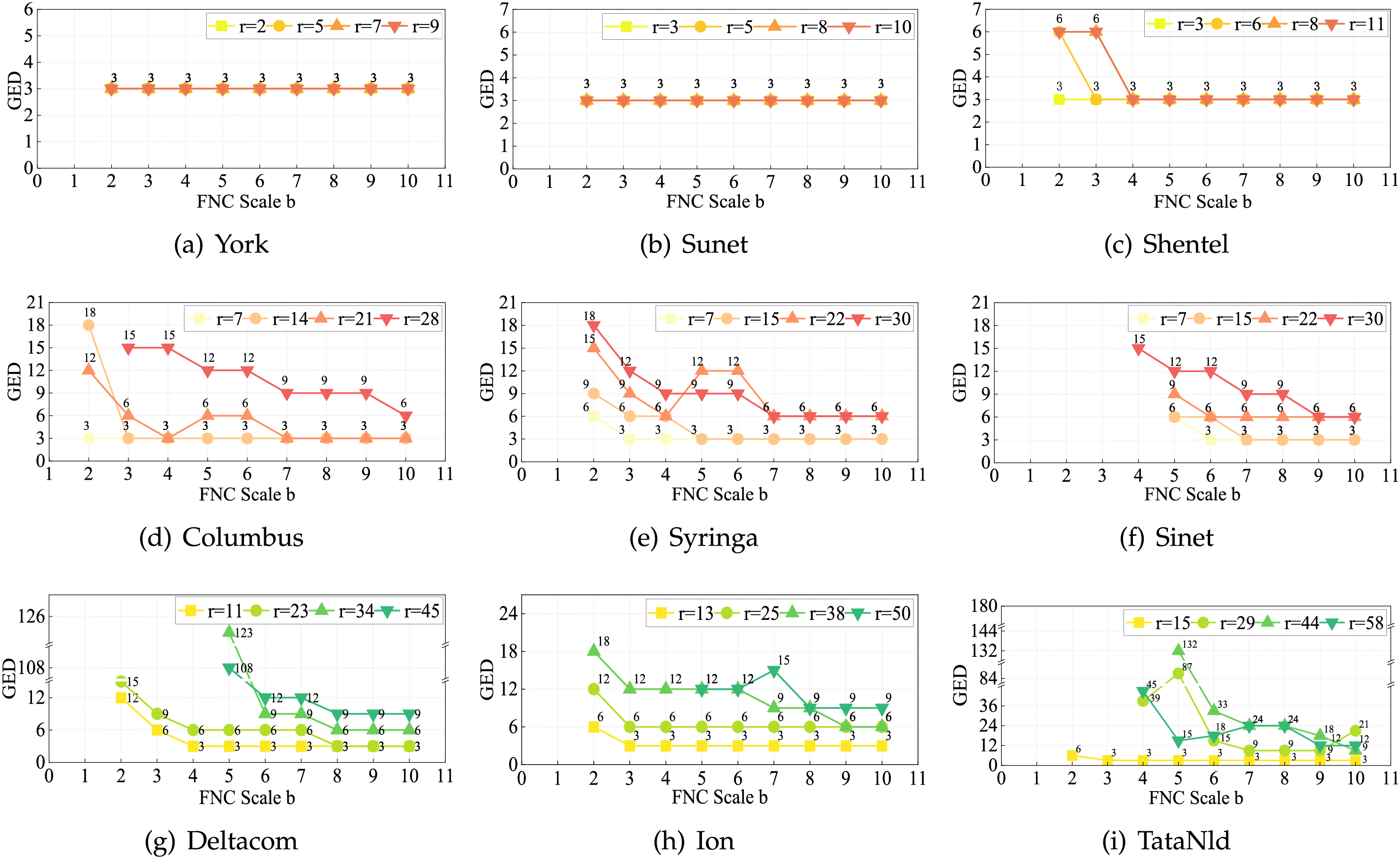
Figure 4: Relationship between different network sizes and FNC: (a)–(c) small topologies; (d)–(f) medium topologies; (g)–(i) large topologies.
Based on these experimental conclusions, quantitative analysis of the obfuscation effect and cost equilibrium suggests that for small, medium, and large topologies, FNC scales
4.3 Comparison of the Cost of Topology Obfuscation
Since network topology obfuscation methods employing different critical node evaluation criteria exhibit fundamental differences in their optimization strategies for generating obfuscated topologies, direct comparison between methods becomes challenging. To ensure experimental rigor and validate the effectiveness of the proposed method, EigenObfu [27]—a typical approach that similarly utilizes EC for critical node evaluation—was selected as the baseline for comparison.
The experimental results are shown in Tables 5–7. To present the data intuitively, Fig. 5 compares the obfuscation effects of networks with different topology scales.
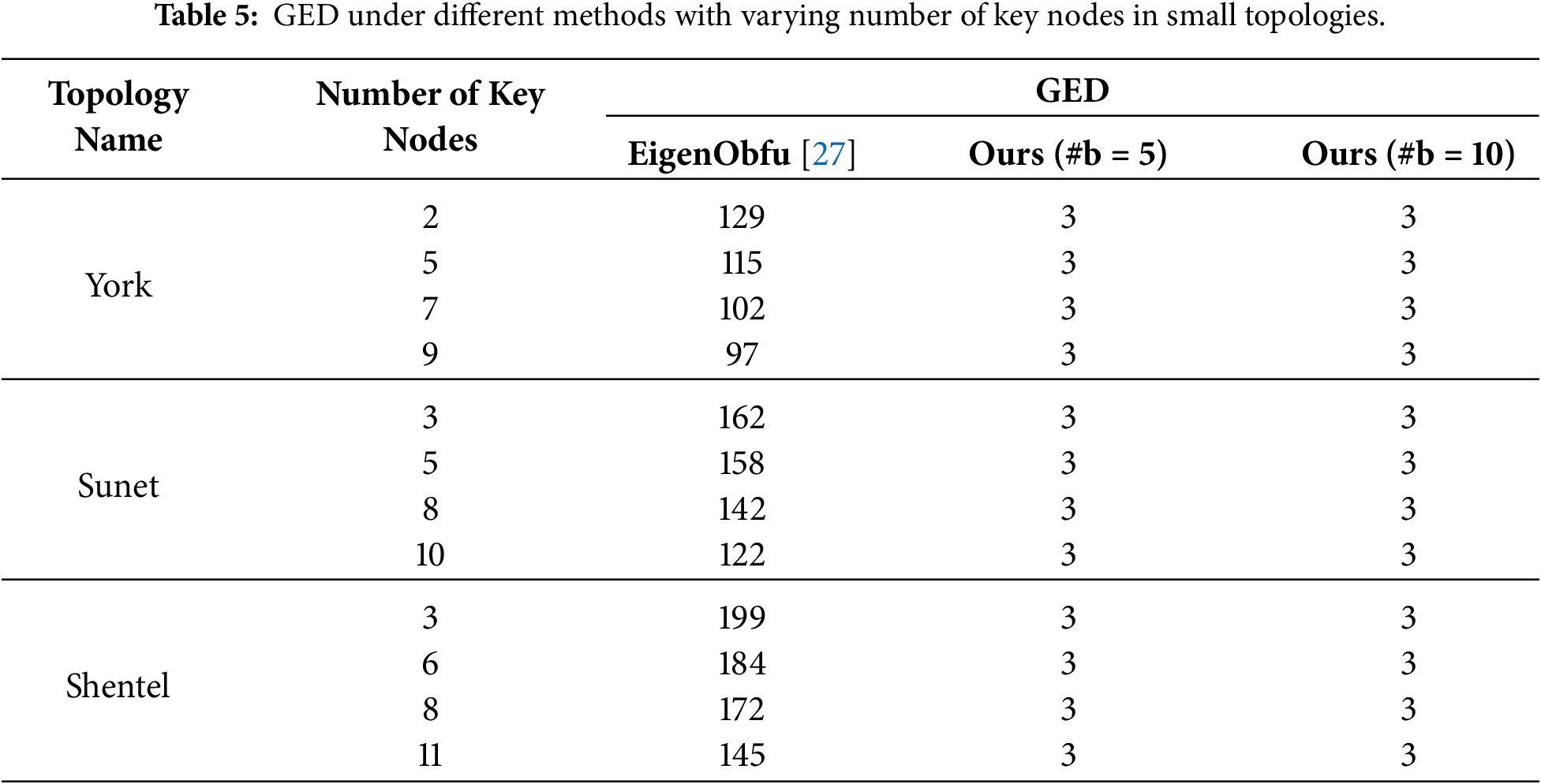
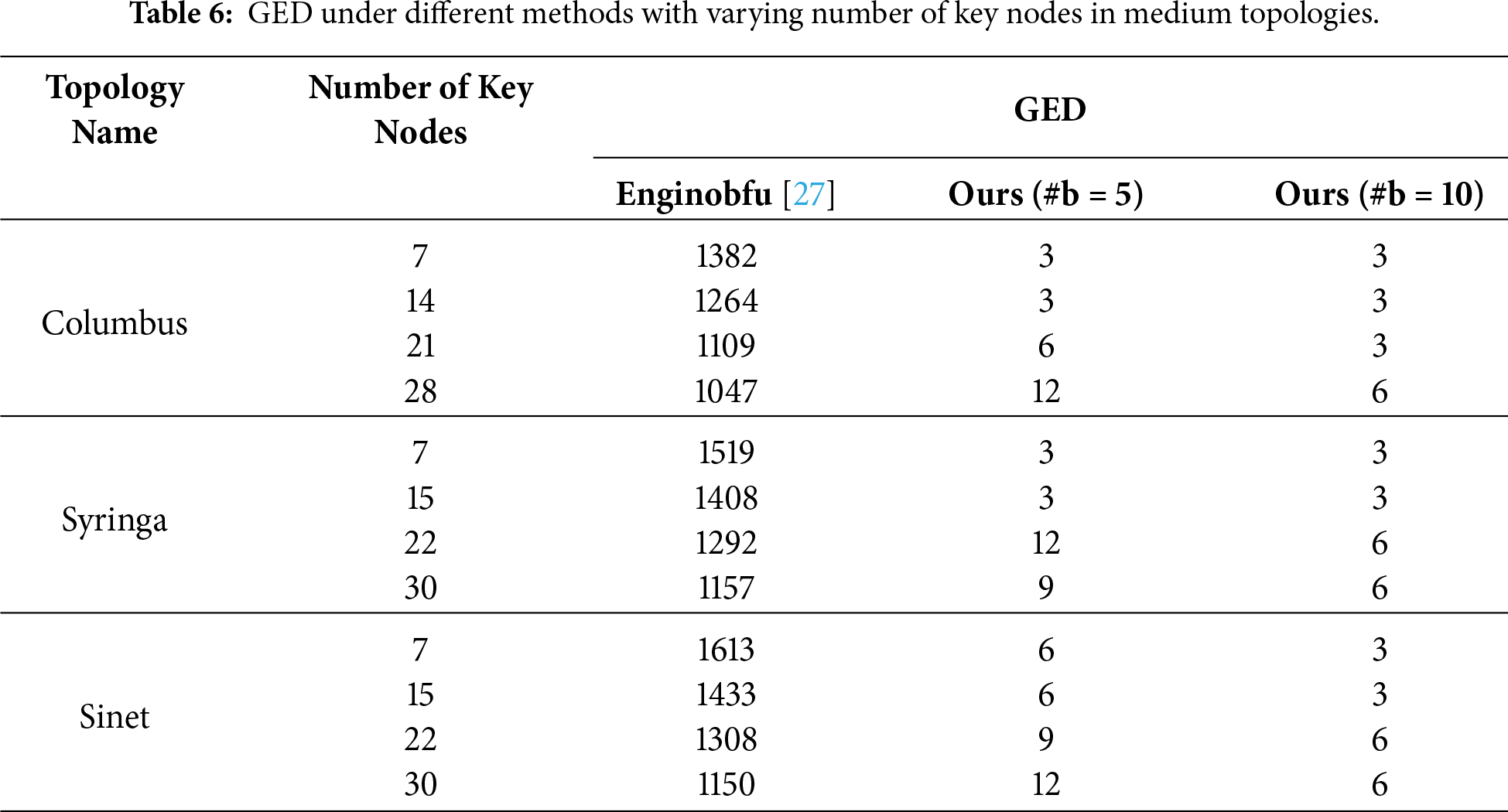
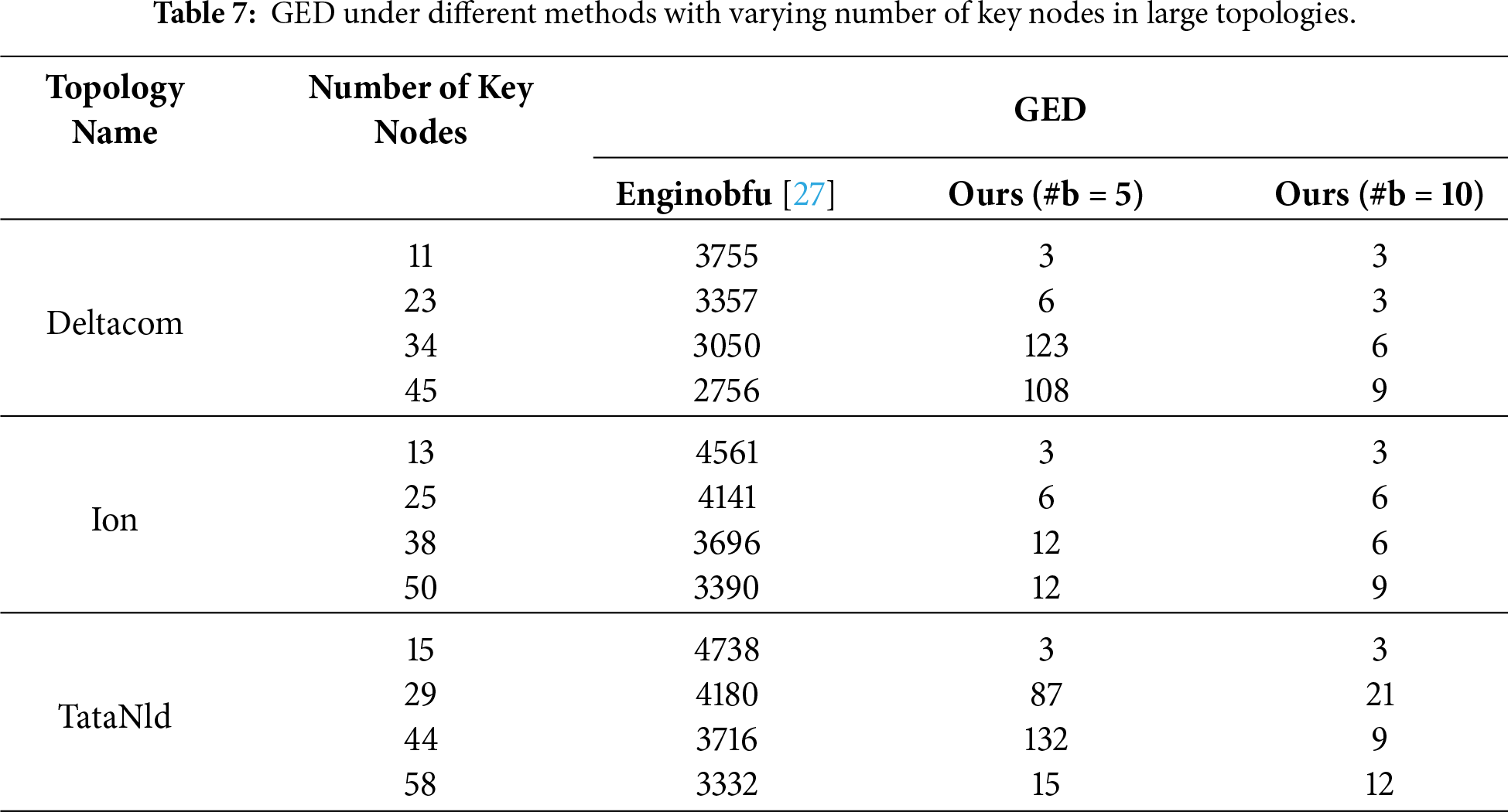
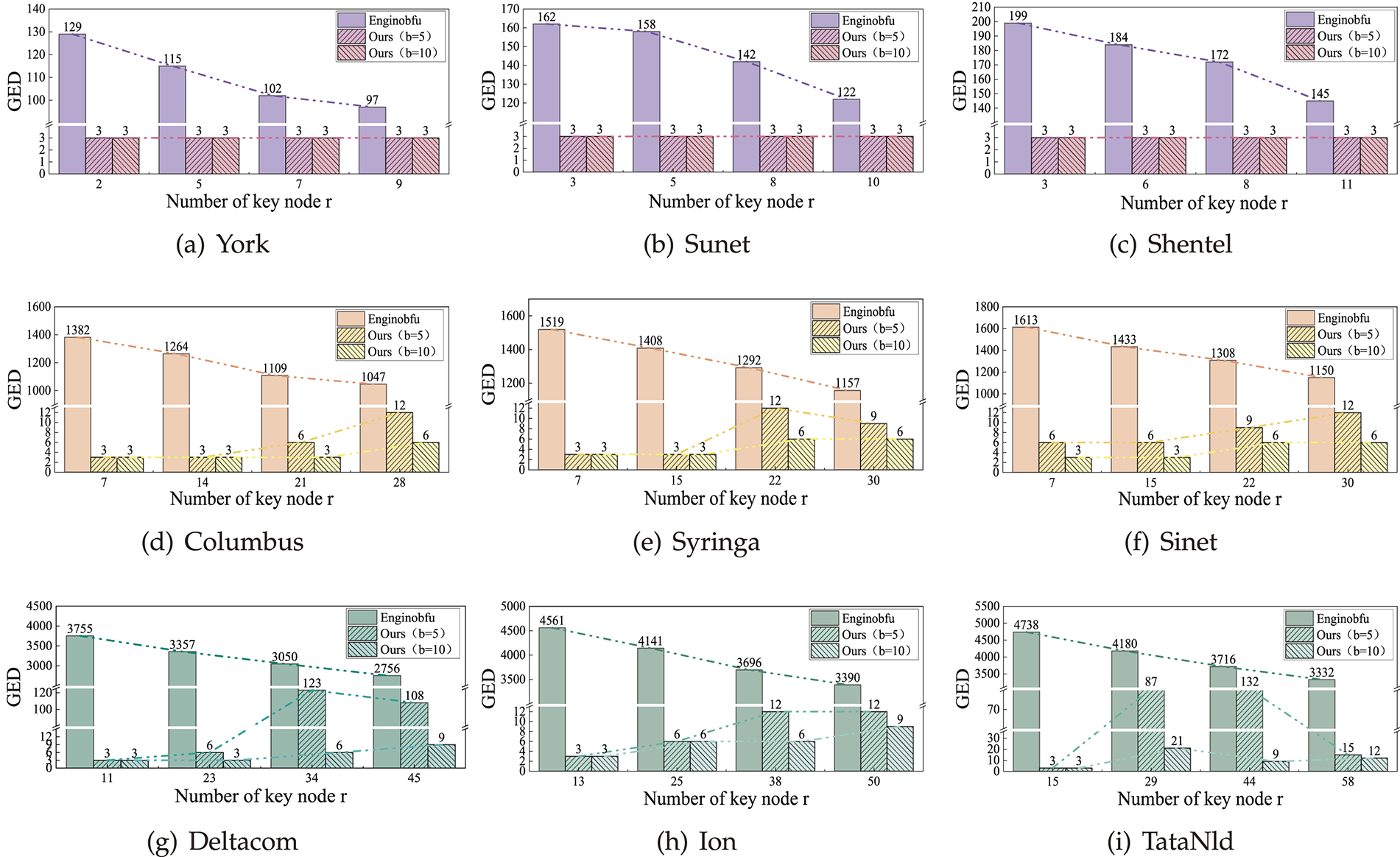
Figure 5: Comparison of EigenObfu’s GED across network sizes and key node counts: (a)–(c) small topologies; (d)–(f) medium topologies; (g)–(i) large topologies.
In small-scale topologies, the proposed method with two different parameter settings consistently achieved a GED of
In large-scale topologies, the maximum GED of the proposed method with two parameter settings was
Experimental results demonstrate that across all topology environments, the proposed method generates obfuscated topologies with significantly lower GED values than EigenObfu when the FNC scale
4.4 Algorithm Complexity Analysis
This paper involves two primary algorithms. The Fake Node Cluster Generation Algorithm functions as a resident process for continuous monitoring and identification of probe traffic; its computational overhead has a negligible impact on the overall performance of the proposed method and is therefore not detailed here. The system’s performance is mainly determined by Algorithm 2 (Heuristic Obfuscated Topology Generation).
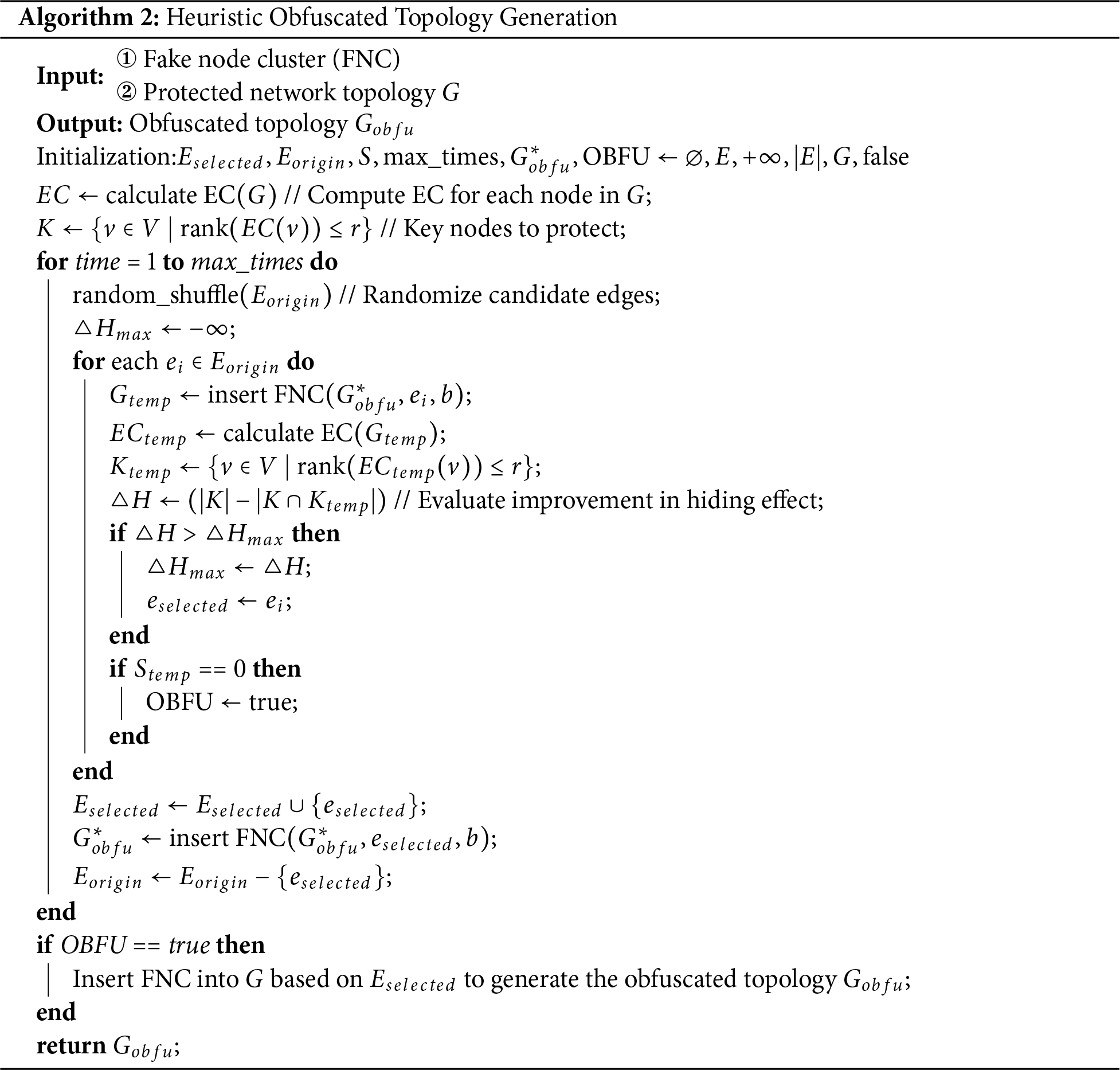
Let the target network topology be an undirected graph
• Time Complexity: The initialization phase involves constant-time operations. The identification of critical nodes requires calculating EC and sorting the results. The EC calculation takes
• Space Complexity: The memory consumption is primarily determined by the storage of the adjacency matrix for the current topology. Thus, the space complexity is
To address the problem of excessively high obfuscation costs in existing network topology obfuscation methods for critical node protection, this paper proposes a novel low-cost network topology obfuscation approach. The method first performs topological modeling on the network to be protected, then constructs target-specific fake node clusters with particular structures, and inserts these clusters into the network based on a greedy strategy to generate the obfuscated topology, thereby disrupting the importance ranking of nodes. Experimental results demonstrate that the proposed method can achieve network topology obfuscation and critical node protection for different-scale networks with low costs.
The limitation of the proposed method is that it is only applicable to the obfuscation of critical nodes evaluated based on eigenvector centrality. Currently, our method mainly resists attack approaches that evaluate critical nodes based on eigenvector centrality. In future work, we will design diverse fake node cluster structures to realize network topology obfuscation in various adversarial scenarios.
Acknowledgement: We thank Dr. Ziliang Zhu from Harbin Institute of Technology for providing valuable assistance in the reproduction of the EigenObfu method.
Funding Statement: This research was funded by the National Key Research and Development Program of China (Grant No. 2022YFB3102900), the Key Science and Technology Project of Henan Province, China (No. 252102211091).
Author Contributions: The authors confirm contribution to the paper as follows: Conceptualization, Yanming Chen and Fuxiang Yuan; Methodology, Yanming Chen; Software, Yanming Chen; Investigation, Yanming Chen; Formal analysis, Yanming Chen; Data curation, Yanming Chen; Writing—original draft preparation, Yanming Chen; Writing—review and editing, Yanming Chen, Fuxiang Yuan and Zekang Wang; Supervision, Fuxiang Yuan and Zekang Wang; Resources, Fuxiang Yuan. All authors reviewed the results and approved the final version of the manuscript.
Availability of Data and Materials: The data that support the findings of this study are available from the corresponding author, upon reasonable request.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest.
References
1. Wang Z, Yuan F, Li R, Zhang M, Luo X. Hidden AS link prediction based on random forest feature selection and GWO-XGBoost model. Comput Netw. 2025;262(1):111164. doi:10.1016/j.comnet.2025.111164. [Google Scholar] [CrossRef]
2. Xing L. Cascading failures in Internet of Things: review and perspectives on reliability and resilience. IEEE Internet of Things J. 2020;8(1):44–64. doi:10.1109/jiot.2020.3018687. [Google Scholar] [CrossRef]
3. Pastor-Satorras R, Vespignani A. Epidemic spreading in scale-free networks. Phys Rev Lett. 2023;31(14):97–111. doi:10.1103/physrevlett.86.3200. [Google Scholar] [PubMed] [CrossRef]
4. Fu X, Yang Y. Modeling and analyzing cascading failures for internet of things. Inform Sci. 2021;545:753–70. doi:10.1016/j.ins.2020.09.054. [Google Scholar] [CrossRef]
5. Zhu L, Fu X, Liu X, Du S. Modeling and analysis of cascade failures in Industrial Internet of Things based on task decomposition and service communities. Comput Ind Eng. 2025;74(2):2723–37. doi:10.1016/j.cie.2025.111177. [Google Scholar] [CrossRef]
6. Zhang M, Li G, Wang S, Liu C, Chen A, Hu H, et al. Poseidon: mitigating volumetric ddos attacks with programmable switches. In: Proceedings of the 27th Network and Distributed System Security Symposium (NDSS). Reston, VA, USA: Internet Society; 2020. p. 1–18. [Google Scholar]
7. Xia Y, Zhang W, Liu Y, Kang J, Zhang H. Learning-based proactive and adaptive link flooding attack mitigation in AIoT. IEEE Internet of Things J. 2025;12(13):23373–88. doi:10.1109/jiot.2025.3553250. [Google Scholar] [CrossRef]
8. Sakuma K, Asahina H, Haruta S, Sasase I. Traceroute-based target link flooding attack detection scheme by analyzing hop count to the destination. In: Proceedings of the 23rd Asia-Pacific Conference on Communications (APCC). Piscataway, NJ, USA: IEEE; 2017. p. 1–6. [Google Scholar]
9. Li S, Lan T. From network inference errors to utility suboptimality: how much is the impact? IEEE Trans Netw Sci Eng. 2022;9(6):4075–86. doi:10.1109/tnse.2022.3195805. [Google Scholar] [CrossRef]
10. Ravi N, Shalinie SM, Danyson J, Theres D. Balance: link flooding attack detection and mitigation via hybrid-SDN. IEEE Trans Netw Serv Manage. 2020;17(3):1715–29. doi:10.1109/tnsm.2020.2997734. [Google Scholar] [CrossRef]
11. Xing J, Wu W, Chen A. Ripple: a programmable, decentralized link-flooding defense against adaptive adversaries. In: Proceedings of the 30th USENIX Security Symposium. Berkeley, CA, USA: USENIX Association; 2021. p. 3865–81. [Google Scholar]
12. Meier R, Tsankov P, Lenders V, Vanbever L, Vechev M. NetHide: secure and practical network topology obfuscation. In: Proceedings of the 27th USENIX Security Symposium. Berkeley, CA, USA: USENIX Association; 2018. p. 693–709. [Google Scholar]
13. Huang X, Xue K, Huang Z, Han J, Chen L, Wei DS, et al. SpiderNet: enabling bot identification in network topology obfuscation against link flooding attacks. IEEE/ACM Trans Netw. 2024;33(1):4075–86. doi:10.1109/tnet.2024.3473742. [Google Scholar] [CrossRef]
14. Ding X, Xiao F, Zhou M, Wang Z. Active link obfuscation to thwart link-flooding attacks for internet of things. In: Proceedings of the 19th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom). Piscataway, NJ, USA: IEEE; 2020. p. 217–24. [Google Scholar]
15. Liu Y, Zhao J, Zhang G, Xing C. NetObfu: a lightweight and efficient network topology obfuscation defense scheme. Comput Secur. 2021;110(C):102447. doi:10.1016/j.cose.2021.102447. [Google Scholar] [CrossRef]
16. Wang J, Liu Y, Zhang W, Yan X, Zhou N, Jiang Z. ReLFA: resist link flooding attacks via renyi entropy and deep reinforcement learning in SDN-IoT. China Commun. 2022;19(7):157–71. doi:10.23919/jcc.2022.07.013. [Google Scholar] [CrossRef]
17. Kim J, Shin S. Software-defined HoneyNet: towards mitigating link flooding attacks. In: Proceedings of the 47th Annual IEEE/IFIP International Conference on Dependable Systems and Networks Workshops (DSN-W). Piscataway, NJ, USA: IEEE; 2017. p. 99–100. [Google Scholar]
18. Hou T, Qu Z, Wang T, Lu Z, Liu Y. Proto: proactive topology obfuscation against adversarial network topology inference. In: Proceedings of the 39th IEEE Conference on Computer Communications. Piscataway, NJ, USA: IEEE; 2020. p. 1598–607. [Google Scholar]
19. Liu Y, Xing C, Zhang G, Song L, Lin H. AntiTomo: network topology obfuscation against adversarial tomography-based topology inference. Comput Secur. 2022;113:102570. doi:10.1016/j.cose.2021.102570. [Google Scholar] [CrossRef]
20. Trassare ST, Beverly R, Alderson D. A technique for network topology deception. In: Proceedings of the 32th IEEE Military Communications Conference. Piscataway, NJ, USA: IEEE; 2013. p. 1795–800. [Google Scholar]
21. Kim J, Marin E, Conti M, Shin S. EqualNet: a secure and practical defense for long-term network topology obfuscation. In: Proceedings of the 29th Annual Network and Distributed System Security Symposium. Reston, VA, USA: Internet Society; 2022. p. 1–18. [Google Scholar]
22. Yan D, Xie W, Zhang Y, He Q, Yang Y. Hypernetwork dismantling via deep reinforcement learning. IEEE Trans Netw Sci Eng. 2022;9(5):3302–15. doi:10.1109/tnse.2022.3174163. [Google Scholar] [CrossRef]
23. Kim J, Nam J, Lee S, Yegneswaran V, Porras P, Shin S. BottleNet: hiding network bottlenecks using SDN-based topology deception. IEEE Trans Inform Forens Secur. 2021;16:3138–53. doi:10.1109/tifs.2021.3075845. [Google Scholar] [CrossRef]
24. Frost HR. A generalized eigenvector centrality for multilayer networks with inter-layer constraints on adjacent node importance. Appl Netw Sci. 2024;9:14. doi:10.1007/s41109-024-00620-8. [Google Scholar] [PubMed] [CrossRef]
25. Elnour M, Atat R, Takiddin A, Ismail M, Serpedin E. Eigenvector centrality-enhanced graph network for attack detection in power distribution systems. Elect Power Syst Res. 2025;241:111339. doi:10.1016/j.epsr.2024.111339. [Google Scholar] [CrossRef]
26. Zhou H, Hong S, Liu Y, Luo X, Li W, Gu G. Mew: enabling large-scale and dynamic link-flooding defenses on programmable switches. In: Proceedings of the 44th IEEE Symposium on Security and Privacy (SP). Piscataway, NJ, USA: IEEE; 2023. p. 3178–92. [Google Scholar]
27. Zhu Z, Zhu G, Zhang Y, Shi J, Huang X, Fang Y. Eigenobfu: a novel network topology obfuscation defense method. IEEE Trans Netw Sci Eng. 2025;12(1):451–62. doi:10.1109/tnse.2024.3501396. [Google Scholar] [CrossRef]
28. He F, Wang Z, Gu X. Network topology generation based on eigenvector centrality with real-time guarantee. Concurr Comput: Pract Exp. 2023;35(21):1524–40. doi:10.1002/cpe.6955. [Google Scholar] [CrossRef]
29. Knight S, Nguyen HX, Falkner N, Bowden R, Roughan M. The internet topology zoo. IEEE J Selected Areas Commun. 2011;29(9):1765–75. doi:10.1109/jsac.2011.111002. [Google Scholar] [CrossRef]
30. Albu-Salih AT. Performance evaluation of ryu controller in software defined networks. J Al-Qadisiyah Comput Sci Math. 2022;14(1):1–7. doi:10.29304/jqcm.2022.14.1.879. [Google Scholar] [CrossRef]
31. Asadollahi S, Goswami B, Sameer M. Ryu controller’s scalability experiment on software defined networks. In: Proceedings of the IEEE International Conference on Current Trends in Advanced Computing (ICCTAC). Piscataway, NJ, USA: IEEE; 2018. p. 1–5. [Google Scholar]
32. Lantz B, Heller B, McKeown N. A network in a laptop: rapid prototyping for software-defined networks. In: Proceedings of the 9th ACM Workshop on Hot Topics in Networks. New York, NY, USA: ACM; 2010. p. 1–6. [Google Scholar]
33. Abu-Aisheh Z, Raveaux R, Ramel JY, Martineau P. An exact graph edit distance algorithm for solving pattern recognition problems. In: Proceedings of the 4th International Conference on Pattern Recognition Applications and Methods. Setubal, Portugal: Scitepress; 2015. p. 271–8. [Google Scholar]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF Downloads
Downloads
 Citation Tools
Citation Tools