 Open Access
Open Access
ARTICLE
Enhancing Underwater Optical Wireless Communication with a High Efficiency Image Encryption System
1 Department of Mechatronics Engineering, Alexandria Higher Institute of Engineering and Technology, Alexandria, Egypt
2 Department of Electronics and Communications Engineering, Alexandria Higher Institute of Engineering and Technology, Alexandria, Egypt
3 Department of Electronics and Communication Engineering, University Institute of Engineering, Chandigarh University, Mohali, Punjab, India
4 Department of Electrical Engineering, College of Engineering in Wadi Alddawasir, Prince Sattam bin Abdulaziz University, Wadi Alddawasir, Saudi Arabia
5 Department of Mathematics, College of Science and Humanities in Al-Kharj, Prince Sattam bin Abdulaziz University, Al-Kharj, Saudi Arabia
* Corresponding Author: Abu Sufian A. Osman. Email:
Computers, Materials & Continua 2026, 87(2), 57 https://doi.org/10.32604/cmc.2026.075669
Received 05 November 2025; Accepted 29 December 2025; Issue published 12 March 2026
Abstract
This paper presents an image encryption scheme for underwater optical wireless communication (UOWC) systems based on dynamically generated hyperchaotic S-boxes, aiming to enhance both data security and transmission performance in underwater environments. The proposed encryption approach provides strong confusion and diffusion properties and is evaluated over five Jerlov water types with different optical attenuation characteristics. Security analysis demonstrates that the encrypted images achieve information entropy values close to the ideal value of 8 (7.9925–7.9993), with very low correlation coefficients in horizontal, vertical, and diagonal directions, as well as the system achieves high values in key metrics such as the Unified Average Changing Intensity (UACI) and Number of Pixel Change Rate (NPCR), ranging from 33.42 to 33.47 and from 99.58% to 99.62%, respectively, both near their theoretical optima. In addition to improving confidentiality, the hyperchaotic encryption process decorrelates pixel intensities and redistributes image spectral content, which enhances robustness against underwater absorption and scattering effects. As a result, improved transmission performance is observed; for example, in Jerlov type I (JI) water, the effective transmission distance is extended from 16 m for plain images to 24 m for encrypted images, while the Peak Signal to Noise Ratio (PSNR) at 24 m increases from 9.25 to 20.13 dB after decryption and enhancement. These results confirm that the proposed scheme provides a dual benefit of secure and reliable image transmission in UOWC systems.Keywords
Wireless communication is extensively utilized across numerous devices globally. Its application, both on land and underwater, holds significant interest for industrial, military, and scientific sectors [1,2]. Additionally, the challenging and dynamic nature of the ocean environment necessitates the development of robust underwater communication links capable of achieving high data rates and extended ranges to support the demands of ocean exploration [3].
Radio-frequency (RF) waves, mostly utilized in terrestrial communications, are ineffective for underwater applications. Underwater RF communication suffers from high attenuation due to the high conductivity of seawater, which increases the absorption loss, especially at higher frequencies. Consequently, RF waves are unsuitable for high-bandwidth and long-distance underwater applications [4–6].
While underwater acoustic communication offers a viable solution for long-range underwater data transmission, its inherent limitations, including low data rates (typically in the tens of kbps over km ranges) and high latency, pose significant challenges. These limitations hinder the ability to support a large number of underwater nodes or mobile vehicles, impeding the realization of real-time, high-capacity, and high-speed data exchange in underwater environments [7,8].
The increasing demand for high-quality video and high-resolution images in both permanent and temporary underwater applications, such as sea-shore surveillance, submarine teleoperation, oil rig protection, port security, and underwater equipment installation, necessitates communication systems capable of handling large data transmission at high speed. However, the limitations of both underwater RF and acoustic communication technologies render them inadequate for these demanding applications [9].
Alternatively, underwater wireless optical communication (UWOC) has emerged as a promising technology for underwater data transmission, offering advantages such as low cost, high bandwidth, and moderate transmission distances reaching hundreds of meters. This technology has witnessed significant advancements in both experimental studies and practical applications. Laser diodes (LDs), with their narrow divergence angles and high bandwidth capabilities, have become the preferred choice for transmitters in UWOC systems, enabling long-distance, high-data-rate communication. The LD’s narrow divergence angle ensures a concentrated optical power density over extended transmission distances, enhancing signal strength and improving overall system performance [10–12].
Recently, communication technology has taken many leaps, offering entities and people all over the globe easier, large-scale access to information. One of the disadvantages of such a process is the vulnerability of information transmitted through insecure channels, including the internet, to cyberattacks. Encryption and steganography are two of the methods scientists have used to secure data transmitted through various media of communication. Many advances have been made in these two fields. Different types of files are being secured by these methods. This includes videos, text, biomedical signals, and images, as well as satellite and medical imaging.
UOWC offers high data rates for underwater applications but suffers from significant limitations due to the aquatic medium. Optical signals are severely attenuated by absorption and scattering, which degrade signal strength and quality. These effects worsen with water turbidity, environmental variations, and distance, resulting in limited transmission range and high error rates. Moreover, in coastal waters, water currents often carry suspended particles such as sediments and plankton, which increase the scattering and absorption coefficients of the water and, consequently, the attenuation of optical signals [10]. While improving channel robustness is essential, securing transmitted data against interception and tampering is equally critical, especially given the increasing reliance on underwater networks for sensitive applications. Traditional encryption methods face challenges in this context because images, the predominant data type in many UOWC applications, exhibit high pixel correlation and redundancy, making them vulnerable to attacks and difficult to secure efficiently [13–15].
To effectively overcome the dual challenges of signal degradation and data vulnerability in UOWC systems, it is important to consider solutions that address both physical and security layers. While UOWC suffers from severe attenuation and distortion due to absorption, scattering, and environmental variability, it is also vulnerable to unauthorized access during transmission. Image encryption provides a promising approach, not only for safeguarding data, but also for increasing resilience to channel-induced impairments by transforming the statistical structure of the transmitted signal.
To this end, this paper proposes an image encryption scheme based on hyperchaotic maps, which possess strong dynamical properties, including multiple positive Lyapunov exponents, large key spaces, and high sensitivity to initial conditions. These characteristics make hyperchaotic systems ideal for secure image encryption. More importantly, by decorrelating image pixels and flattening spectral distributions, the encryption process enhances robustness to underwater propagation effects. Thus, the proposed cryptosystem simultaneously improves transmission performance and ensures secure delivery in challenging UOWC environments [16,17].
Several investigations were conducted in UOWC systems using light sources operating in the blue-green visible light spectrum, which provides the least attenuation in underwater. Shao et al. [18] implemented a real-time OWC system capable of transmitting 4K video at a data rate of 2.2 Gbps. The system utilized time-division multiplexing to transmit data over a 3.6 m underwater channel and an 8 m air-based optical wireless channel.
Abd El-Mottaleb et al. [19] presented a UOWC system integrated with optical code division multiple access (OCDMA) technology utilizing fixed right-shift codes. The system employed green LDs sources and was evaluated across five distinct Jerlov water types. Simulation results demonstrated successful data transmission over underwater distances of 35, 31, 21, 12, and 5.15 m for Jerlov water types I, IA, IB, II, and III, respectively, with each channel achieving a data rate of 10 Gbps.
Ali and Shaker [20] analyzed the performance of a UOWC system across different Jerlov water types. Their study demonstrated that employing an 8-pulse position modulation scheme with an LED at 550 nm enabled the system to achieve underwater communication ranges of 25 m for Jerlov types I and IA, 20 m for Jerlov type IB, and 10 m for Jerlov types II and III.
Wang et al. [21] made a practical UOWC system employing a 520 nm LD with non-return-to-zero (NRZ) modulation. While the system achieved an underwater range of 146 m at a data rate of 500 Mbps, this rate is insufficient for supporting high-data transmission demands in more challenging underwater applications.
Additionally, previous studies have explored the field of image encryption.
Chaotic systems have been explored in underwater applications beyond data transmission, particularly for signal detection and analysis. A grid-scroll memristive chaotic oscillator with infinite equilibrium points has been proposed for underwater signal detection. The oscillator, constructed using a cubic nonlinear memristor and piecewise linear functions, can generate infinitely coexisting multi-scroll attractors with controllable amplitude through parameter adjustment. A circuit model was developed to validate the oscillator’s feasibility. Based on this chaotic system, an underwater signal detection framework combining empirical mode decomposition, correlation analysis, and Hilbert transform was designed, enabling reliable detection of periodic signals across a wide frequency range. The proposed method demonstrates strong noise robustness, achieving accurate detection at signal-to-noise ratios as low as −28 dB and frequency extraction precision exceeding 99.9%, thereby confirming its effectiveness for practical underwater signal detection [22].
A grid-scroll memristive hyperchaotic system with infinite equilibrium points was proposed and applied to underwater acoustic signal detection. The system generates multi-scroll hyperchaotic attractors with controllable amplitude and was validated through numerical analysis and circuit implementation. Combined with the complete ensemble empirical mode decomposition with adaptive noise (CEEMDAN) and the Hilbert transform, the resulting detection model exhibits strong noise immunity and high sensitivity, achieving reliable signal detection at SNRs as low as −63 dB with frequency extraction accuracy exceeding 99.9%, demonstrating its practical feasibility [23].
A multi-layer security algorithm combining Least-Significant-Bit (LSB) steganography and chaos-based encryption (2-D Logistic map and chaotic Baker map) was proposed for securing image transmission over wireless AWGN channels. The method demonstrated effectiveness in concealing and encrypting confidential images, ensuring robust security during wireless communication [24].
Additionally, previous studies have explored the field of image encryption. Josephus scrambling and dynamic cross-diffusion were the two techniques proposed for use in image encryption in [25]. The first step in this process involved the generation of pseudo-random chaotic sequences through the design of a new hyperchaotic system with a broader chaotic interval. The scrambled images were further encrypted with the help of a dynamic Josephus scrambling methodology, using chaotic sequences.
A proposal was made to use the one-dimensional sine-cosine chaotic map (SCCM), since one-dimensional chaotic maps had disadvantages in such applications. Additionally, both SCCM and random DNA operations were used in this image encryption system. The effectiveness of this new technique was boosted when the SHA-512 value related to the plaintext was used to generate the chaotic map’s initial conditions [26].
DNA computing and a finite state machine (FSM) were combined to generate the design of a key schedule, which was the basis of a new algorithm for image encryption in [27]. This key is highly flexible and statistically random. The aim of this new technique was to achieve the properties of confusion and diffusion at the same time.
The algorithm proposed in [28], namely a highly sensitive cross-channel color image encryption, applied the Sine map and mathematical function to reach a two-dimensional hyper-chaotic map, for use in image encryption.
Intra bit-plane scrambling was proposed for use in an encryption technique for parallel images [29]. During permutation, to encrypt the images at the bit-level, four threads, each scrambling two bit-planes, were applied. To reduce the time of encryption, multiple threads were employed to generate the keystream during diffusion. Based on the chaos S-Box, researchers have designed a variety of techniques for image encryption. In [30], the authors presented an image cryptosystem based on a dynamic hyperchaotic S-Box. The proposed hyperchaotic map was utilized to generate a set of S-Boxes, which are subsequently combined in pairs to produce twelve unique S-Boxes. The plaintext image was partitioned into groups of pixels, and the sum of the pixel values in each group was computed. Modular arithmetic was then employed to determine the specific S-Box to be used for each group. The pixel groups were subsequently processed through a bitwise XOR operation with the corresponding S-Box. Finally, the encrypted image was generated by applying a scrambling process driven by a chaotic signal.
The authors in [31] introduced a cascade chaotic map, the 2D-Cosine-Logistic-Sine Map (2D-CLSM), designed to enhance image encryption. The initial values and parameters of the chaotic map were integrated with the original image to generate dynamic encryption features. The S-Box construction method was proposed, along with an S-Box-based encryption scheme comprising four stages: key generation, S-Box generation, bit-level encryption, and pixel-level encryption. In the bit-level encryption stage, the plaintext pixel values were converted from decimal to eight-bit binary format. The lower four bits were permuted, while the upper four bits underwent a diagonal diffusion process. In the pixel-level encryption stage, diffusion was achieved through a three-number XOR operation involving the chaotic sequence value, the current plaintext pixel, and the previously encrypted pixel. The resulting value was used to determine the row and column indices of the S-Box for pixel substitution, completing the encryption process.
Another image encryption scheme based on a two-phase mechanism was introduced in [32]. In the first phase, pixel values were diffused using a Pseudo-Random Number Sequence (PRNS) module. In the second phase, the diffused image was subjected to a confusion process using a proposed S-Box.
But in the proposed technique, this study proposes an efficient image encryption system utilizing S-Boxes derived from the properties of hyperchaotic maps. The encryption process begins with the generation of random sequences using the Chen hyperchaotic map. The input image is then subjected to the Integer Wavelet Transform (IWT), resulting in four sub-bands: the approximation sub-band (LL) and three detail sub-bands (HL, LH, HH). After that, the Chen hyperchaotic system produces two random sequences (x, y), which are resized, leading to the development of hyper S-boxes (X) and (Y). Values of the (X) and (Y) S-boxes are used to substitute the values of the pixels of the approximation (LL) and (HH) sub-bands, respectively. This substitution is followed by an XOR operation on both the LL and HH sub-bands, using random sequences generated by the Henon map. For the LH and HL sub-bands, diffusion is performed using additional random sequences (z and u) generated by the Chen hyperchaotic map. Finally, the approximation and detail sub-bands are recombined to produce the encrypted image.
Given these challenges, the use of encryption is not only a measure to secure data but also an approach to mitigate transmission-related issues in UOWC. By encrypting images before transmission, the system ensures data integrity and prevents unauthorized access, even when vulnerabilities at the physical layer exist. Furthermore, encryption can help preserve image quality by masking the original content from the effects of absorption and scattering coefficients during transmission.
The main contributions of this work are:
• Utilizing S-boxes developed from hyper-chaotic maps to enhance the security of image encryption systems.
• Proposing a digital, encrypted image transmission system for UOWC based on the hyper-chaotic map S-box algorithm.
• Analyzing the impact of attenuation in different Jerlov water types with varying optical properties.
• Evaluating system performance in terms of underwater transmission range, SNR, PSNR, and SSIM.
The rest of this paper is organized as follows. Section 2 outlines the proposed image encryption algorithm based on hyper chaotic S-boxes. Section 3 describes the digitally encrypted image transmission system using the S-boxes hyperchaotic maps algorithm within UOWC systems and includes a brief overview of attenuation in Jerlov waters. Section 4 presents the results and discussion, followed by the main conclusions in Section 5.
2 Hyper Chaotic S-Boxes: The Basis of the Proposed Image Encryption System
To encrypt images before they are communicated through transmission, an efficient system is devised using S-boxes, with the characteristics of hyper-chaotic maps. The new encryption system is highly efficient, has a complex structure, higher security, and can effectively resist attacks, compared to other algorithms. The algorithm can be seen in Fig. 1 and is developed following the steps below. Chaotic systems in general contain one positive Lyapunov exponent. Despite this fact, the use of this map need not necessarily improve the security of message encryption. As a result, higher-dimensional hyper-chaotic systems are resorted to in order to improve an encryption system’s security. This is due to these systems’ high randomness and unpredictability. Chaotic systems lead to hyper-chaotic systems when simple control techniques are applied. Hyper-chaotic sequences are reached, with the proposed technique, upon the use of the Chen hyper-chaotic system.
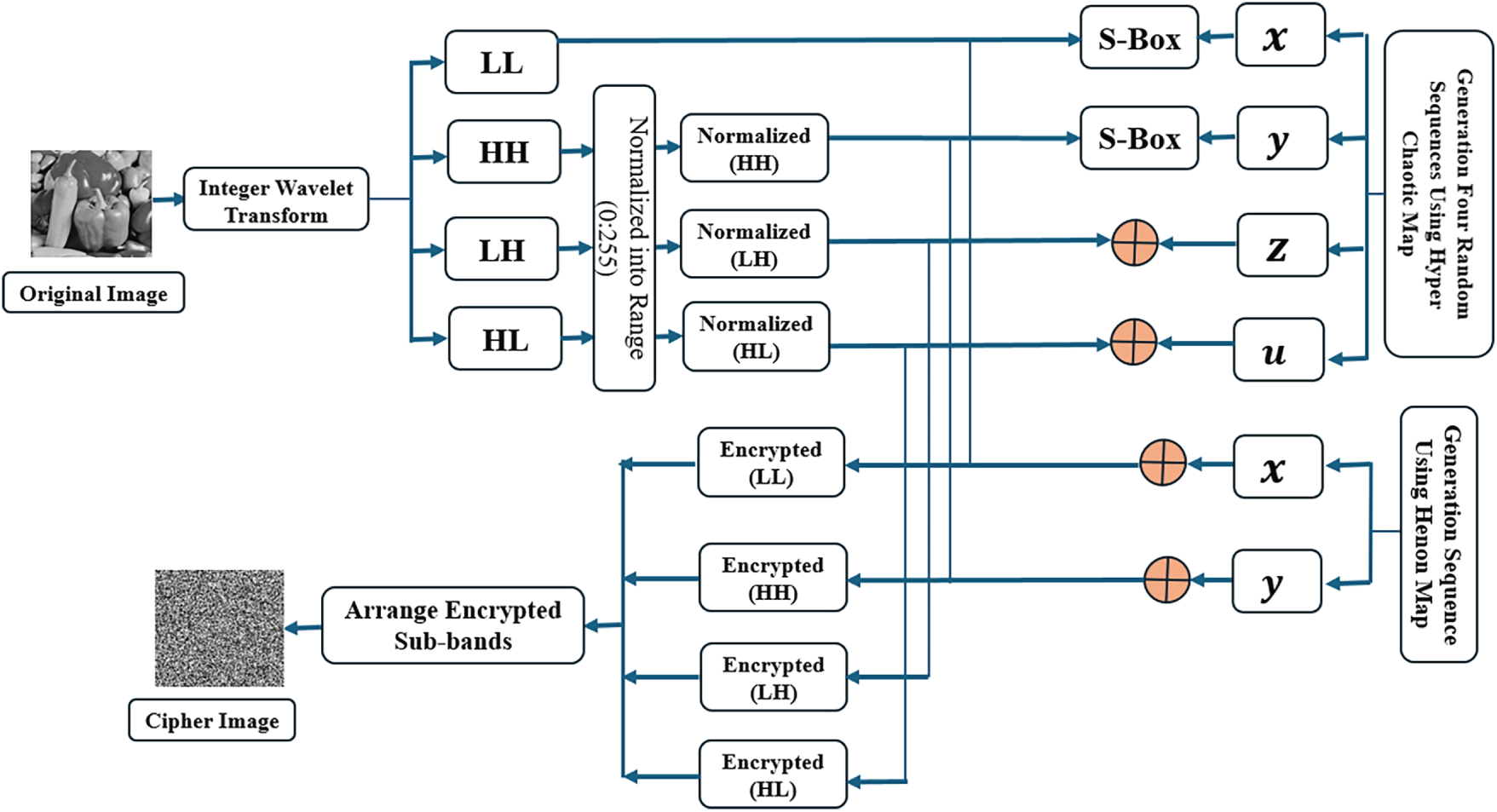
Figure 1: Block diagram of image encryption system.
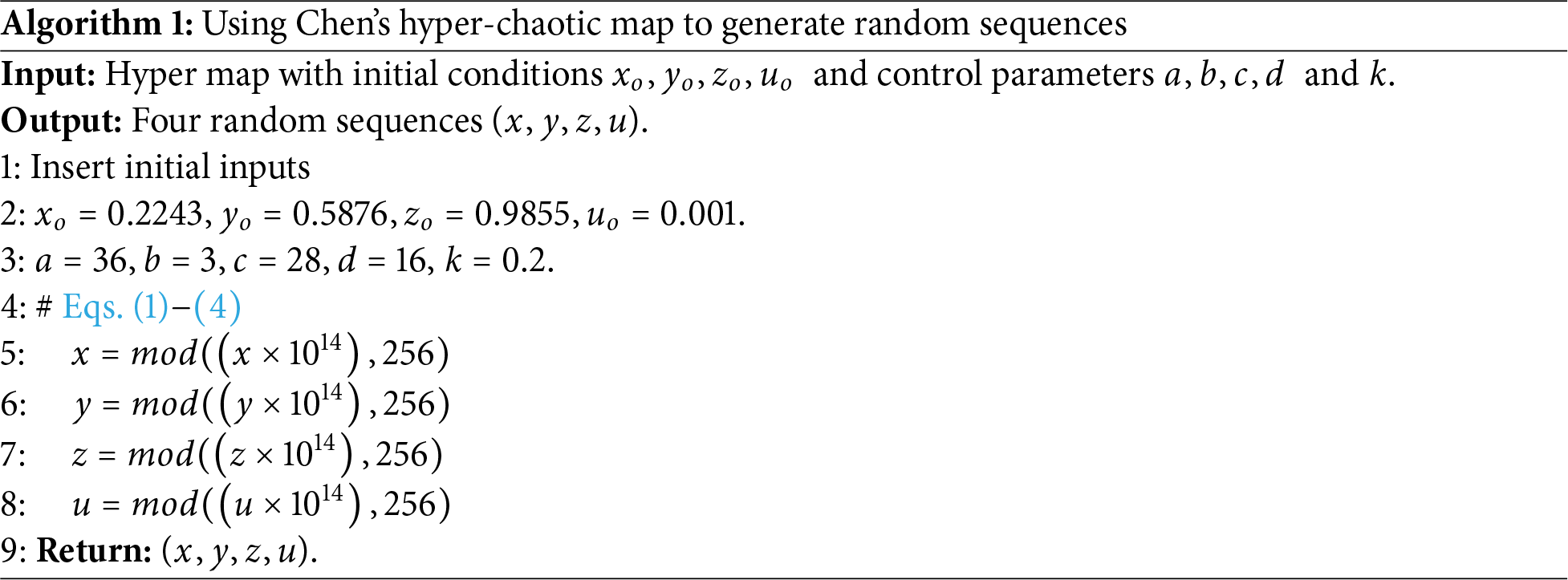
2.1 Using the Chen Hyper Chaotic Map to Generate Random Sequences
This system possesses a highly sensitive secret key, consisting of its initial conditions and control parameters. Chen’s hyper-chaotic system variables, x, y, z, u are representations of these conditions and parameters. Eq. (1) below is used to calculate them.
where,
2.2 Using Chen’s Hyper-Chaotic Map to Encrypt Images
Algorithm 1 explains the implementation of Chen’s hyper-chaotic map to generate random sequences as detailed in the following steps.
Step 1: This step begins with the insertion of the original 128 × 128 image and is followed by the application of an IWT operation. This leads to the approximation (LL) and the three detail sub-bands entitled (HL, LH, and HH). The latter undergo normalization of their pixel intensity, leading to them having values between 0 and 255.
Step 2: The Chen hyperchaotic system produces two random sequences (x, y), which are resized, leading to the development of hyper S-boxes (X) and (Y). These are 16 × 16 in size and consist of 256 integers divided into segments of 8 bits. These integers fall within the range of [0, 255].
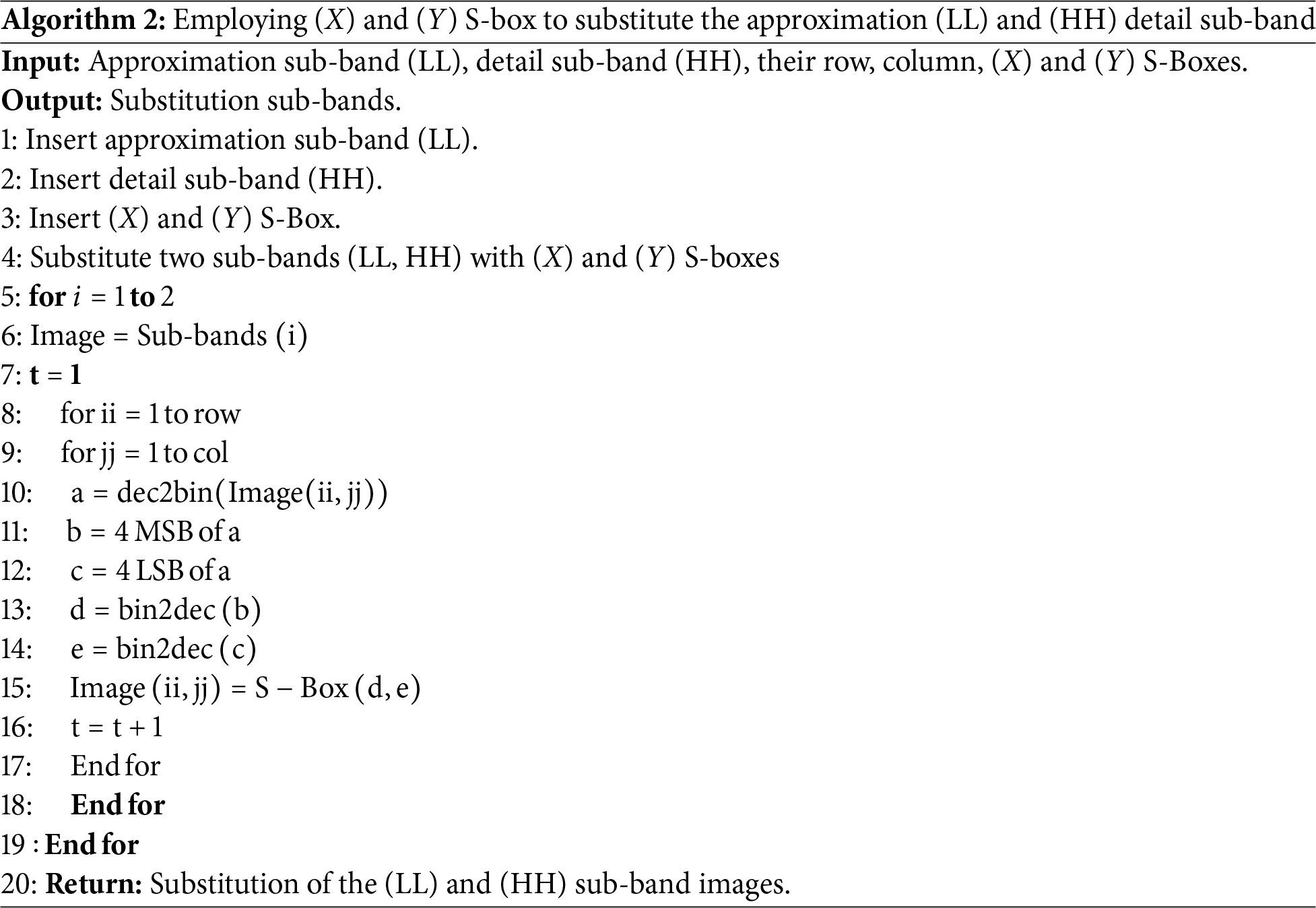
Step 3: Values of the (X) and (Y) S-boxes are used to substitute the values of the pixels of the approximation (LL) and (HH) sub-bands, respectively. Algorithm 2 below demonstrates the necessary steps for this process, which are as follows:
1. Pixel values of the sub-band represent the substitution input. It is a binary code with numbers from 0 to 255, 8 bits in length.
2. As for the two types of S-boxes, they are made of a 16 × 16 matrix, with rows and columns numbered from 0 to 15.
3. The value of each pixel is substituted by following the location of the 8 input bits on the S-box and finding the number of rows and columns it is housed in.
4. The first four bits are assigned to a row, while the second to a column.
Step 4: An XOR operation is applied to both LL and HH, i.e., the substituted sub-bands. This process involves the use of the different, random sequences produced by the two-dimensional chaotic system, known as the Henon chaotic map. This map has the initial conditions
The initial conditions, along with the parameters of the Henon map determine the output of its behavior. Pseudo-random sequences are obtained when the parameters of this system, namely a and b, take on the values 1.4 and 0.3, respectively.
Step 5: Random sequences resulting from the Chen hyper-chaotic map, (z) and (u), are responsible for the diffusion of the (LH) and (HH) sub-bands, respectively.
Finally: Upon arranging the approximation and detail sub-bands, the encryption image is reached.
Algorithm 2 details the process of employing (X) and (Y) S-box to substitute the approximation (LL) and (HH) detail sub-band.
In this work, a hyper-chaotic S-box–based encryption scheme is employed to enhance the security and robustness of image transmission over UOWC channels. Hyper-chaotic systems, owing to their higher dimensionality and increased complexity compared to conventional chaotic systems, provide improved resistance to cryptographic attacks through enlarged key space and high sensitivity to initial conditions, which are desirable properties for secure image encryption. Underwater optical channels are primarily impaired by absorption and scattering, which introduce random intensity fluctuations and spatial distortions in the received signal. Although the proposed encryption does not modify the physical characteristics of the optical carrier (532 nm green laser) or the channel signal-to-noise ratio, it introduces strong pixel decorrelation and a more uniform intensity distribution at the image level prior to transmission. As a result, channel-induced distortions that typically appear as structured artifacts in plain images are transformed into spatially distributed noise in the decrypted images. This reduces localized error propagation and enhances the robustness of image reconstruction, leading to improved post-detection image quality metrics such as PSNR and SSIM at the receiver.
3 Design of Digital Ciphered Peppers Image Transmission System with S-Boxes Featured with HyperChaotic Maps Based UOWC System
Fig. 2 depicts the proposed transmission system design for an encrypted digital peppers image using S-boxes hyperchaotic maps over the UOWC channel in various types of Jerlov waters. As with any communication system, this setup consists of three main components: a transmitter responsible for data generation and modulation, a channel through which the information signal propagates to its destination, and a receiver that demodulates and processes the received signal.
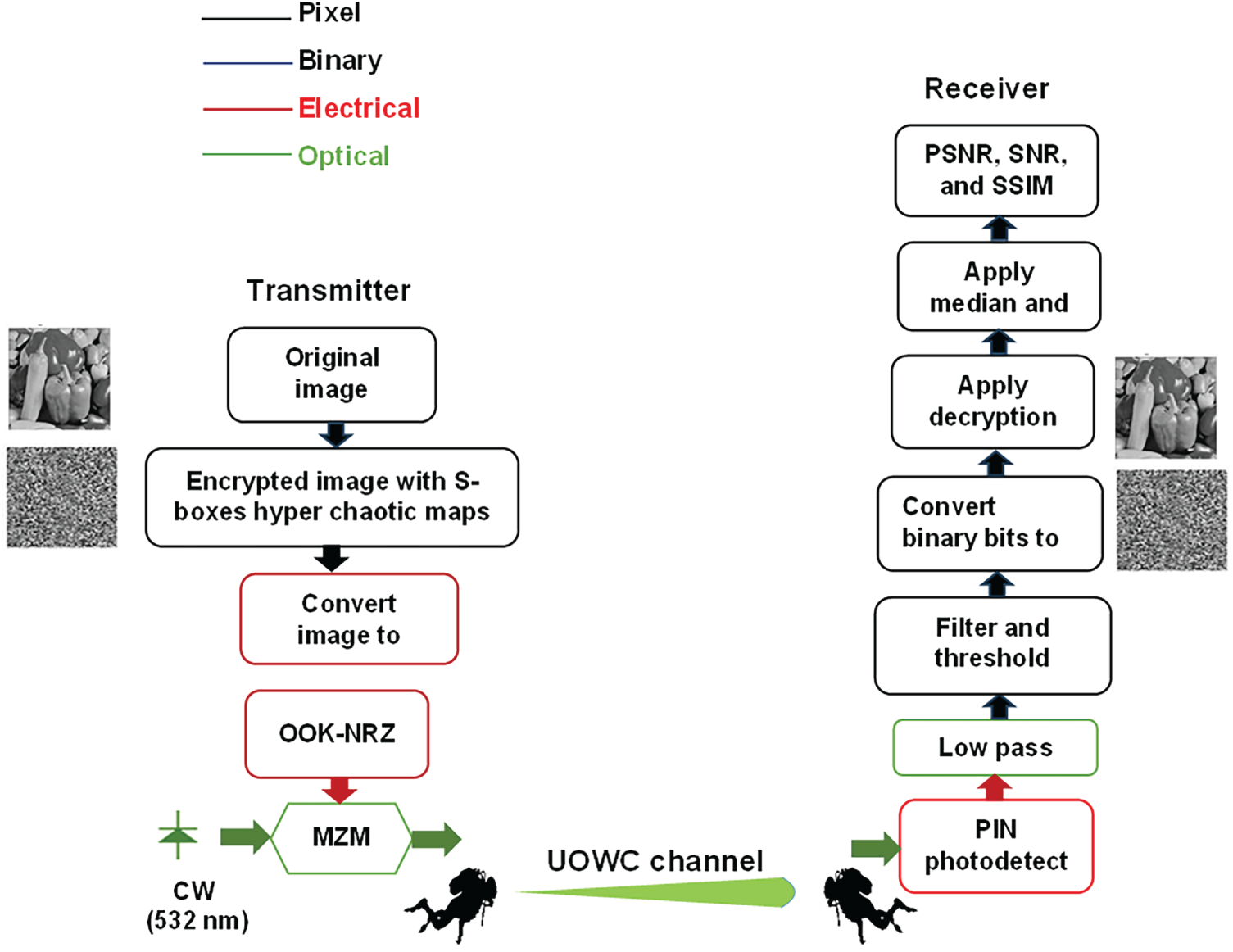
Figure 2: Structure of the proposed transmission system design for encrypted digital peppers image using S-boxes hyperchaotic maps over the UOWC channel in various types of Jerlov waters.
At the transmitter, a 128 × 128 gray-scale peppers image is initially encrypted using an S-box hyperchaotic maps algorithm, after which it is mapped directly into an 8-bit-per-pixel binary stream without compression, resulting in a total of 131,072 bits (
where
The propagation of optical signals through underwater channels is significantly impacted by the inherent properties of the water medium, namely absorption and scattering. These phenomena, arising from interactions between photons and particles within seawater, play a critical role in determining the performance of UOWC systems. Absorption, a process where photons are absorbed by water molecules and other constituents, leads to a reduction in signal intensity, thereby affecting the efficiency of the communication link. Concurrently, scattering redirects photon propagation, causing power loss as photons are dispersed away from the receiver aperture [34].
The combined effects of absorption,
where
This study assesses digital image transmission across five distinct water types: JI, JIA, JIB, JII, and JIII, each with unique optical properties at 532 nm. JI water, typically found in open ocean regions, exhibits minimal light attenuation of 0.0576
JIA water, commonly found in clearer coastal regions, exhibits slightly higher absorption and scattering of 0.0491 and 0.0112
JIB water is prevalent in coastal areas and regions with moderate biological activity. The presence of elevated levels of chlorophyll (0.4 mg/
Conversely, JII water, typically found in areas with significant biological activity and terrestrial runoff, exhibits higher concentrations of chlorophyll (1.25 mg/
Finally, JIII water represents the most turbid conditions, characterized by very high levels of chlorophyll (3 mg/
After propagating through the UOWC channel, the signal arrived at the receiver side with received power, considering line of sight link, expressed as [19,34]
where
At the receiver end, the distorted received optical signal is directed to the aperture, where it is collimated and focused onto the photodetector (PD). Here a positive-over-intrinsic (PIN) PD is used to convert the optical signal back to an electrical signal. The photodetector (PD) output electrical signal is given as [38]
where
where
The received signal is processed through a low pass filter (LPF) to suppress out-of-band noise. The filter cutoff frequency is set to 0.75× data rate, which provides sufficient bandwidth for OOK signal reconstruction while reducing noise outside the signal band. The filter is assumed to have negligible insertion loss within the passband and a high attenuation outside the cutoff frequency. Afterward, the signal is converted back into binary bits and reconstructed into an image. However, image transmission through the underwater channel results in distortion of the received image, causing a reduction in PSNR, SNR, and SSIM. This distortion introduces random fluctuations in pixel values, leading to significant deviations from the original pixel values and resulting in substantial errors. To mitigate this issue and enhance the quality of the decrypted images, a post-decryption enhancement stage employing both median and high-pass filters is applied. The median filter, as a nonlinear technique, suppresses noise introduced during underwater optical transmission by correcting pixel errors through the computation of the median value of neighbouring pixels. Following noise suppression, a high-pass filter is employed to enhance edges and fine structural details that may be degraded by channel impairments and filtering operations. The combined use of median and high-pass filtering improves the visual quality and structural fidelity of the reconstructed images.
PSNR quantifies the peak error, indicating how closely the received image matches the original image. It is computed as [38,39]
where
where
The SNR is a measure of signal strength relative to noise. In this study, SNR is determined by comparing the power of the original image to the power of the distorted image, which represents the received image at varying underwater distances. It is computed as [38,39].
Furthermore, the Structural Similarity Index Measure (SSIM) assesses the similarity between two images by examining differences in structural information, brightness, and contrast. The SSIM generates a score that ranges from −1 to 1, where a score of 1 signifies perfect similarity. It is computed as [38,39]
where
MATLAB is used to perform image encryption and to convert the encrypted image into a binary bitstream of length
This study utilizes a simulation approach to assess the performance of a digital image transmission system in a UOWC system. The simulations are conducted using Optisystem version 21 and MATLAB software, comprising two distinct analysis phases. The OptiSystem simulations are performed on a workstation with an Intel Core i9 CPU, 64 GB RAM, and NVIDIA RTX 4080 GPU. The first phase focuses on encryption analysis, while the second phase evaluates the performance of digital image transmission within the UOWC system. Additionally, it is important to emphasize that the proposed hyperchaotic S-box–based image encryption scheme does not modify the optical carrier wavelength or the inherent absorption and scattering characteristics of the underwater channel, which are governed by the physical properties of water and are wavelength dependent. The optical signal is transmitted at a fixed wavelength of 532 nm under identical channel conditions for both encrypted and unencrypted cases. The improvements observed in PSNR, SNR, and SSIM are attributed to signal-domain effects introduced prior to transmission. Specifically, the encryption process reduces pixel correlation and redistributes the spatial frequency content of the image, resulting in a statistically uniform and noise-like representation. After direct detection and demodulation, this statistical restructuring mitigates spatially concentrated error propagation and enhances the effectiveness of post-decryption enhancement filters, leading to improved reconstructed image quality under the same received optical power conditions. Thus, the reported performance gains reflect improved robustness at the digital reconstruction level rather than any alteration of the physical underwater propagation mechanisms.
4.1 Security Analysis of Image Encryption
The dynamical properties of the Chen hyperchaotic system are investigated to validate its applicability in cryptographic schemes. The calculated Lyapunov exponents, presented in Table 1, reveal the presence of two positive values, which confirm the hyperchaotic nature of the system, as illustrated in Fig. 3. In addition, the phase space representations shown in Fig. 4 display a highly complex attractor, while the bifurcation analysis in Fig. 5 highlights the system’s rich and sensitive dependence on control parameters. These characteristics indicate that the generated sequences possess strong randomness and are well-suited for secure encryption applications.
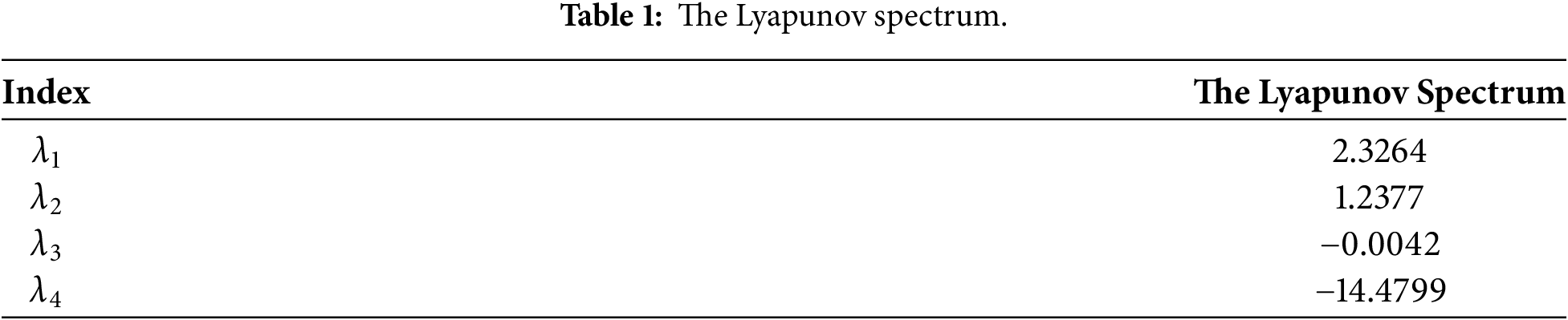
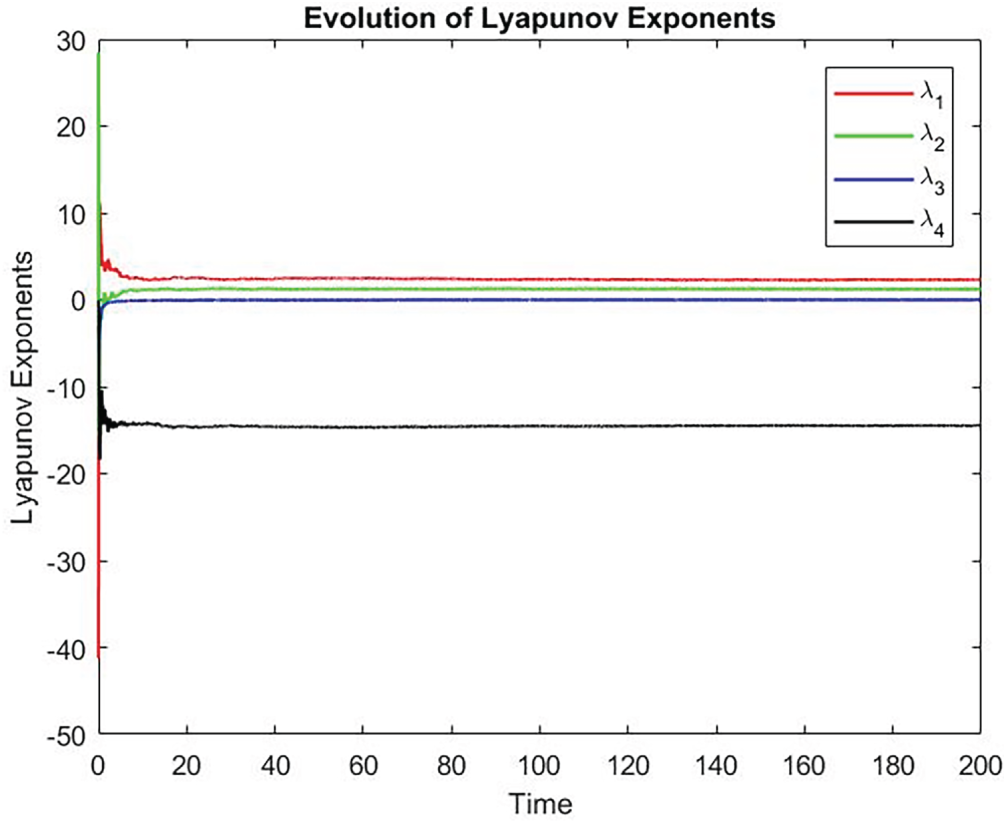
Figure 3: Evolution of Lyapunov exponents.
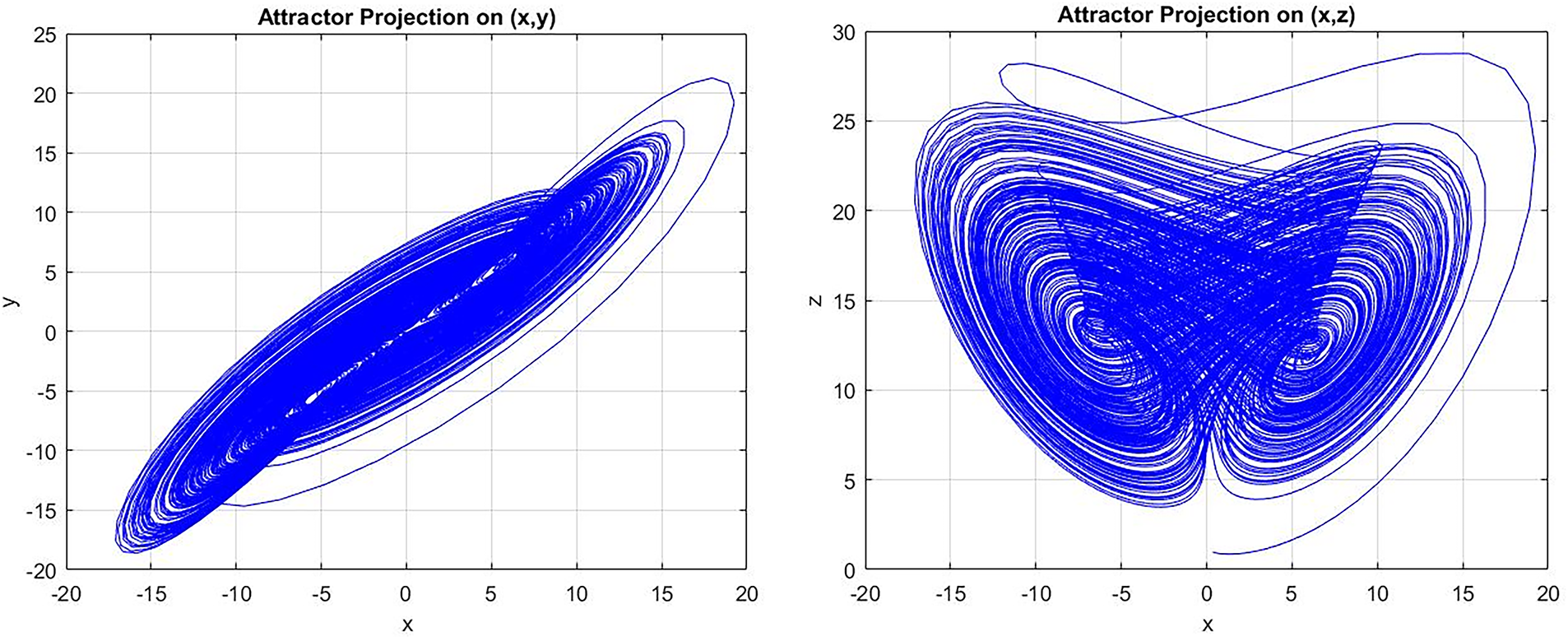
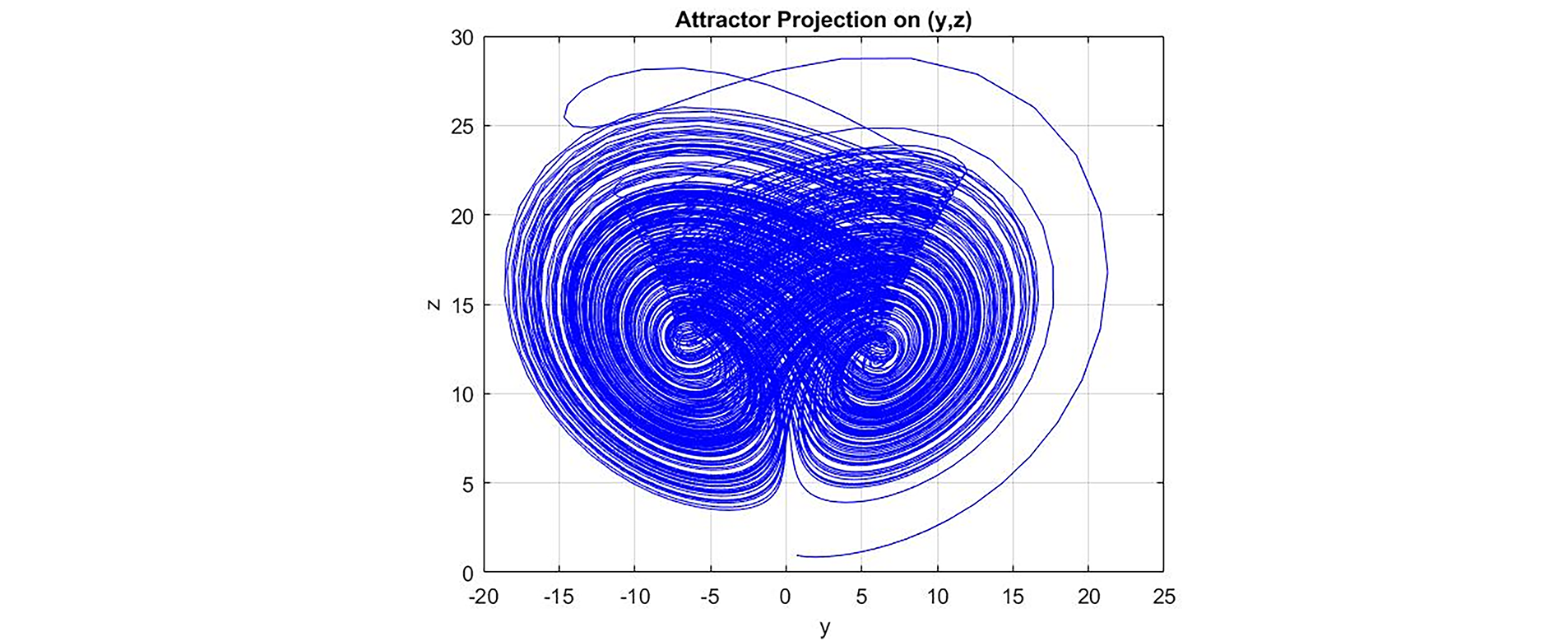
Figure 4: Hyperchaotic attractor of system.
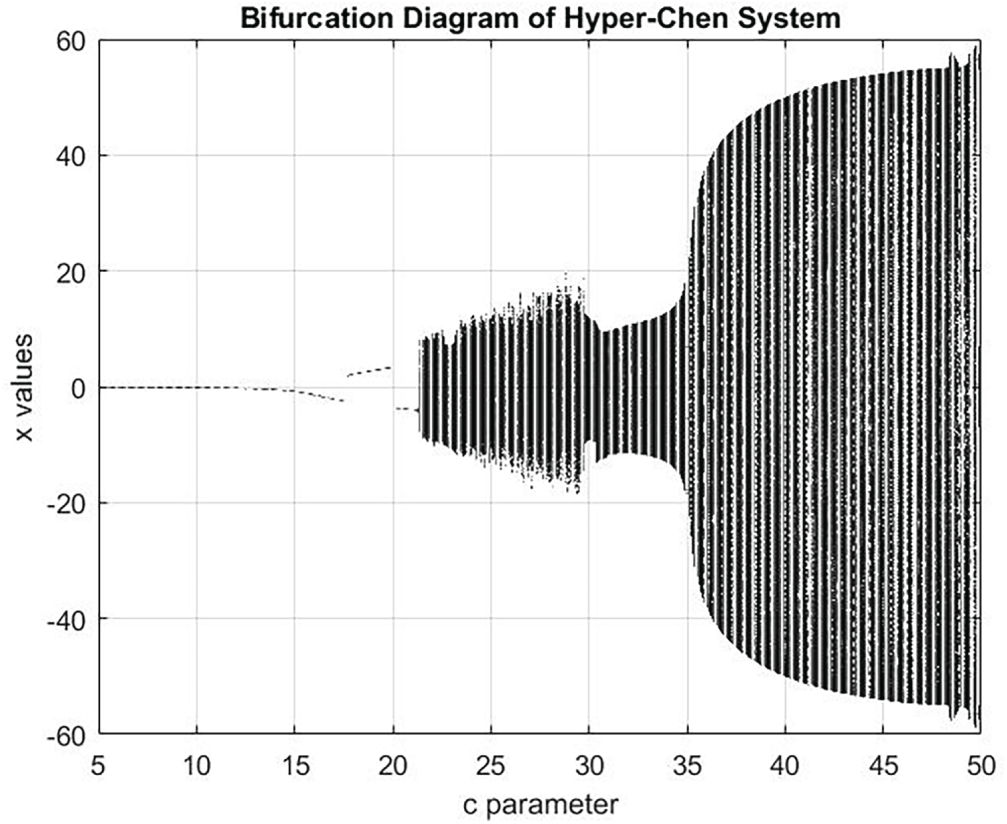
Figure 5: Bifurcation diagram of the hyper chen system.
4.1.1 Information Entropy Analysis
To check the uncertainty of the information of an image and evaluate its grey value distribution, the information entropy analysis is undertaken. Results of information entropy for an encrypted image can be any figure, but it has to fall between zero and eight. The best result obtained for information entropy is eight and by reaching this figure or a figure close to it, the encryption is deemed successful. Eq. (17) is used to calculate the information entropy of an image [40,41].
where, N is the total number of (X), while
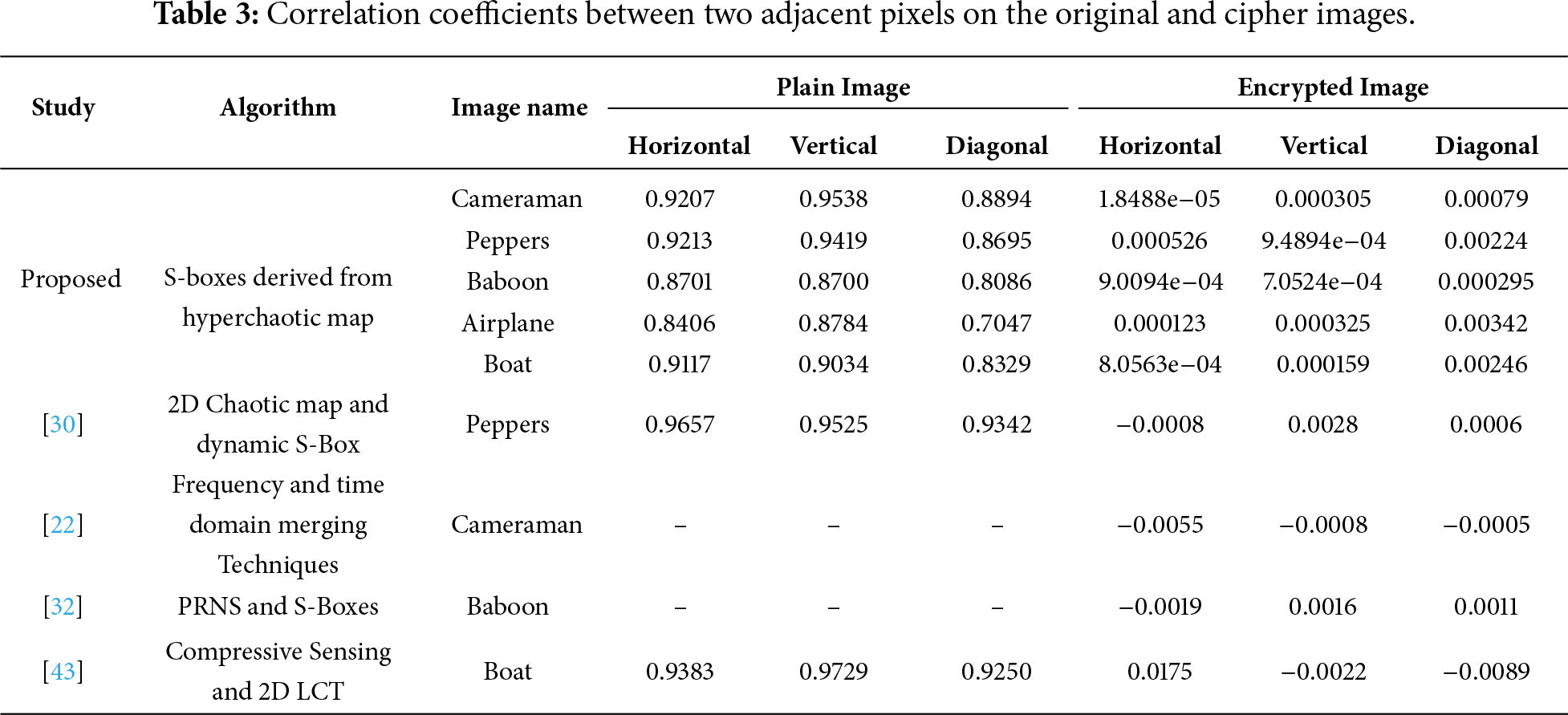
Researchers conduct correlation analysis to check the similarities available between an original image and its encrypted version. In general, two neighboring pixels share a lot of similarity, thus the correlation coefficient between them is large. An encryption algorithm is considered effective when it is able to negatively affect this resemblance and bring the correlation coefficient between two adjacent pixels to a value close to zero. Eq. (18) is employed to calculate the correlation coefficient of two pixels on the horizontal, vertical, and diagonal planes [41,44,45].
where,
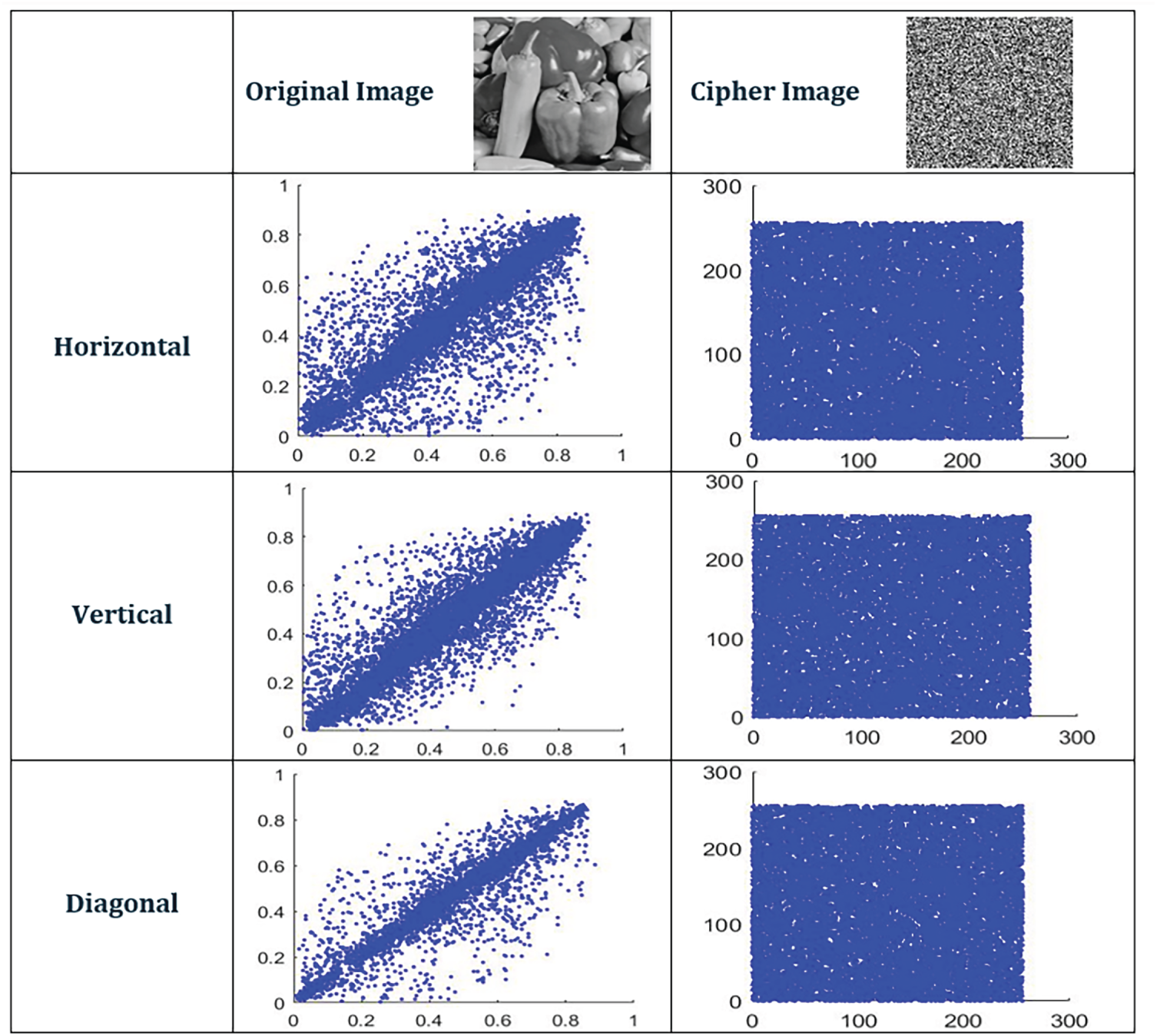
Figure 6: Correlation of two adjacent pixels of the original peppers image and its cipher version. In each scatter plot, the x-axis denotes the pixel intensity value at position
4.1.3 Analysis of Key Sensitivity
To ensure robustness against brute-force attacks, the cryptosystem must demonstrate high sensitivity to the secret key. In this study, a plain image was encrypted with the original key and subsequently decrypted using a slightly altered key. Due to the inherent sensitivity of hyperchaotic maps to initial conditions, even a minor modification in the key produces a drastically different decrypted image. These results confirm that the encryption algorithm is key-sensitive, as any small deviation from the correct key leads to failed decryption and erroneous output. The corresponding experimental outcomes are illustrated in Fig. 7.
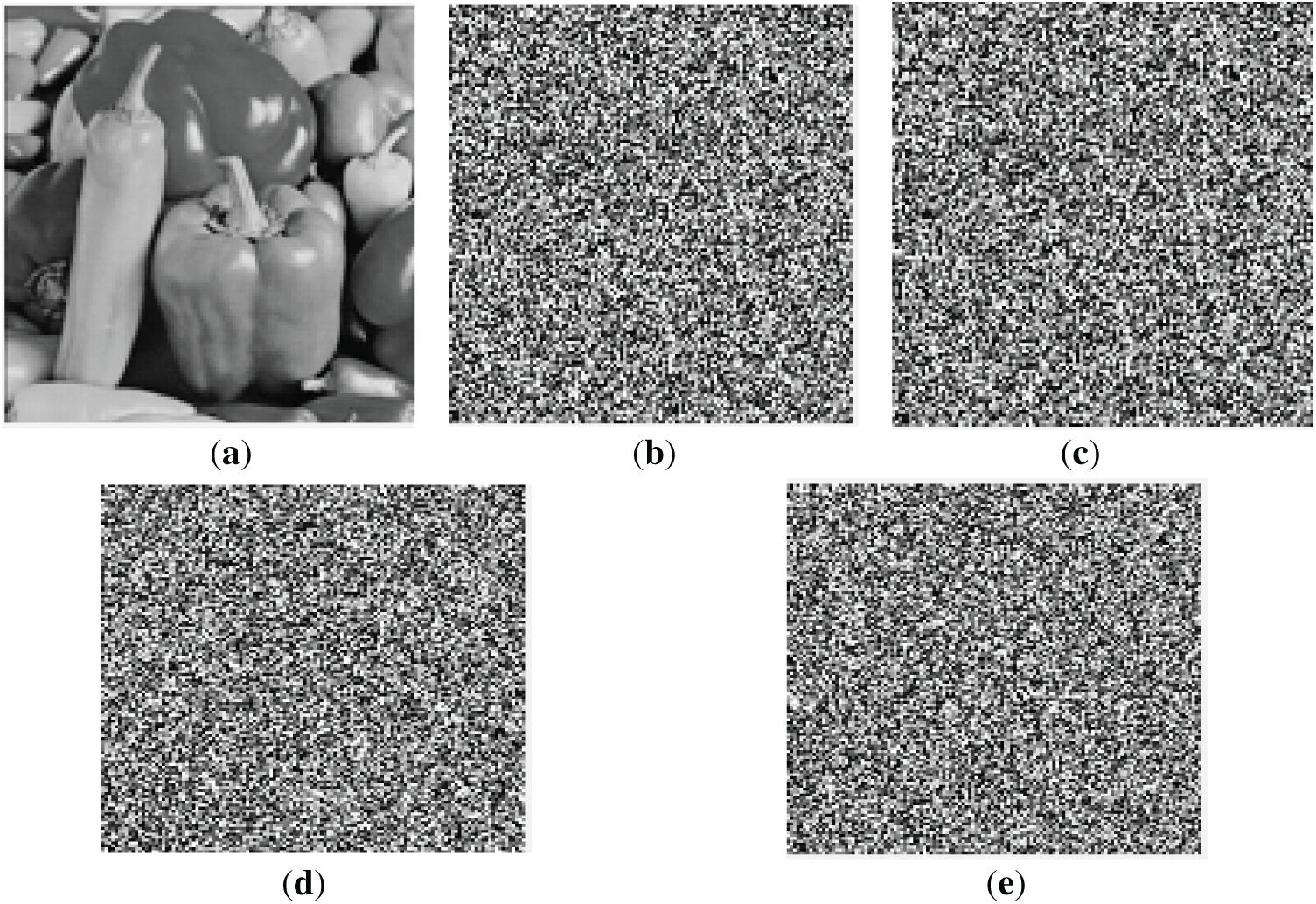
Figure 7: Key sensitivity. (a) Plain image. (b) Cipher image. (c–e) Image decrypted with change keys of the hyper map.
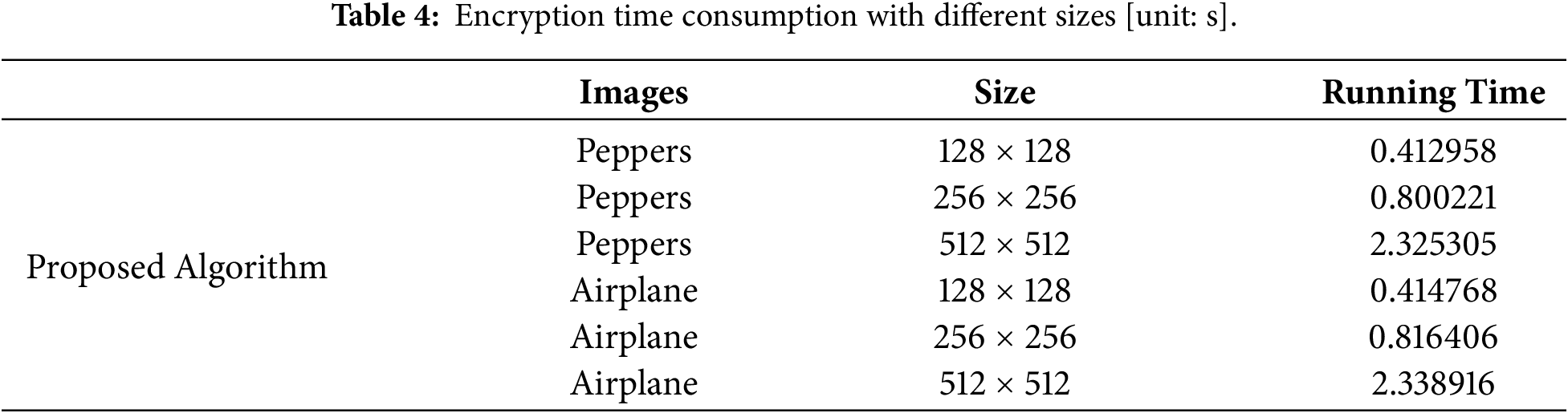
4.1.4 Running Time for Encryption vs. Image Size Scaling
The computational performance of the proposed encryption method was assessed by recording the encryption time for gray-level images of various sizes. The results show that the encryption time increases steadily as the image size becomes larger, which reflects the expected growth in computational load with the number of processed pixels. As presented in Table 4, the method achieves fast execution across all tested sizes, demonstrating its efficiency and suitability for practical real-time applications.
4.1.5 Analysis of Resistance to Cropping Attacks
Noise is an unavoidable factor in communication systems and may affect image transmission and processing. To examine the robustness of the proposed encryption scheme, noise disturbance experiments were applied to the encrypted images. In these experiments, salt-and-pepper noise with densities of 0.002, 0.01, 0.1, and 0.4, as well as Gaussian noise with zero mean and variances of 0.0002, 0.002, and 0.02, were added to the cipher-images. The corrupted encrypted images were then decrypted, and the corresponding results are illustrated in Figs. 8 and 9. The experimental observations show that the decrypted images remain visually recognizable under both noise types. Nevertheless, increasing noise levels lead to a gradual reduction in image quality, indicating the inherent trade-off between noise robustness and reconstruction accuracy.
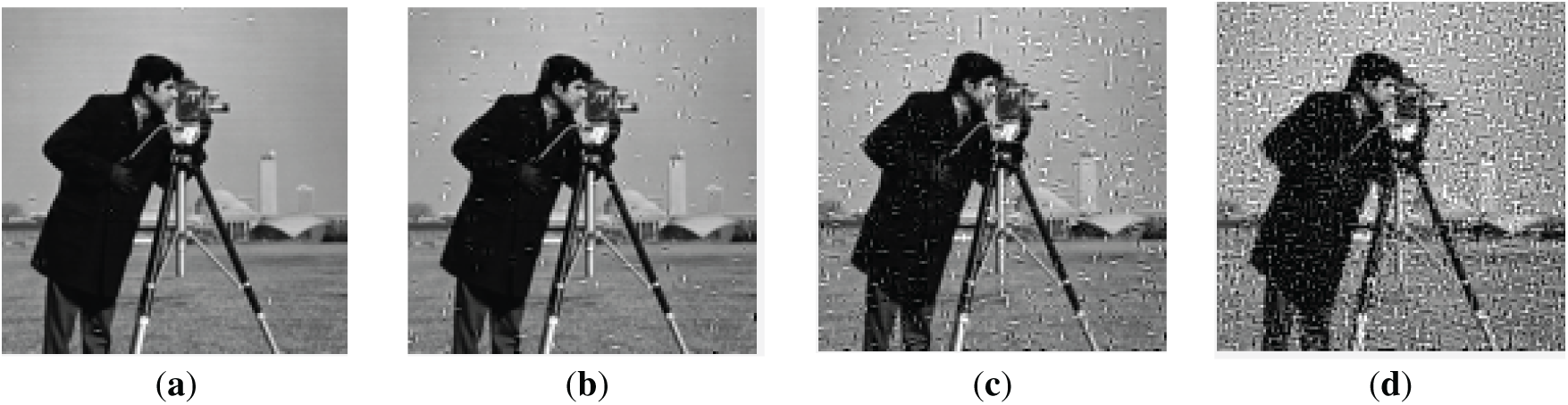
Figure 8: Decrypted images under Salt & Peppers noise: (a) 0.002; (b) 0.01; (c) 0.1; (d) 0.4.
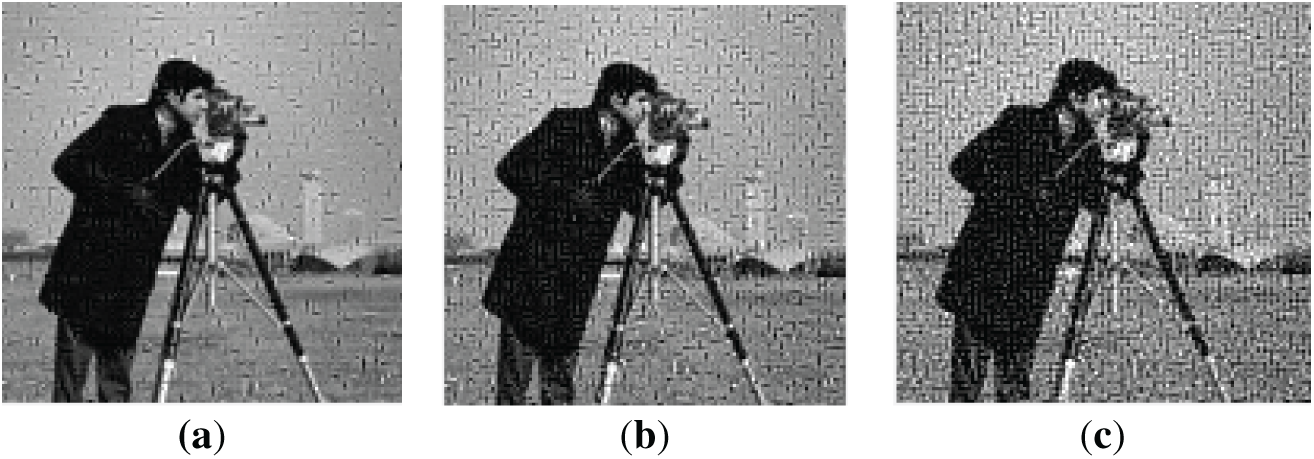
Figure 9: Decrypted images under Gaussian noise with variances of (a) 0.0002, (b) 0.002, and (c) 0.02.
Cropping attacks remove parts of the encrypted image, leading to loss of information and degradation in the decrypted result. Therefore, resistance to such attacks is an important measure of an encryption algorithm’s robustness. While the original algorithm is vulnerable to cropping attacks, the improved algorithm shows significantly better resilience, preserving the main visual content even after partial data removal. Fig. 10 demonstrates the strong anti-cropping capability of the proposed method.
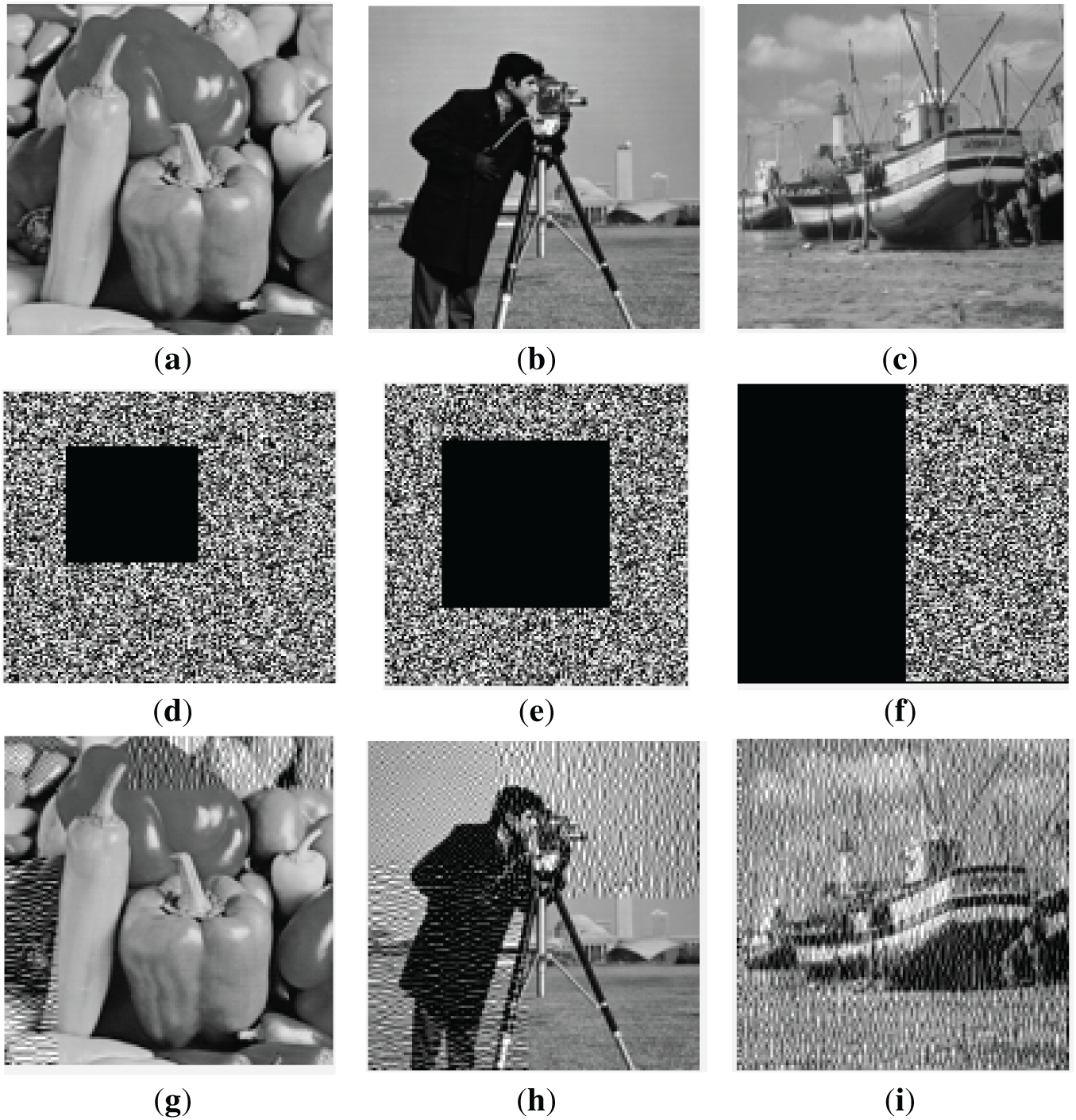
Figure 10: Resistance to cropping attacks (a) Original peppers image, (b) Original cameraman image, (c) Original boat image, (d) Cropping attack for peppers image, (e) Cropping attack for cameraman image, (f) Cropping attack for boat image, (g) Decrypted peppers image after cropping attack, (h) Decrypted cameraman image after cropping attack, and (i) Decrypted boat image after cropping attack.
Histogram analysis was undertaken for all original and encrypted images of this research, and the results will be seen in this section. When examined from a statistical point of view, structural differences are noticed between the original and encrypted versions of each image. Results of the histogram analysis for original images show that they have tilts and spikes, which are completely different from the flat and uniform histogram of encrypted images, marking the difference between the two versions. Fig. 11 shows the histogram of an original, as well as an encrypted image with the proposed algorithm. The proposed algorithm ensures the randomness of the information of images encrypted with its help, which can be seen in the histogram results. While performing quantity analysis, variance (x) of the histogram is calculated to determine the randomness of the image.
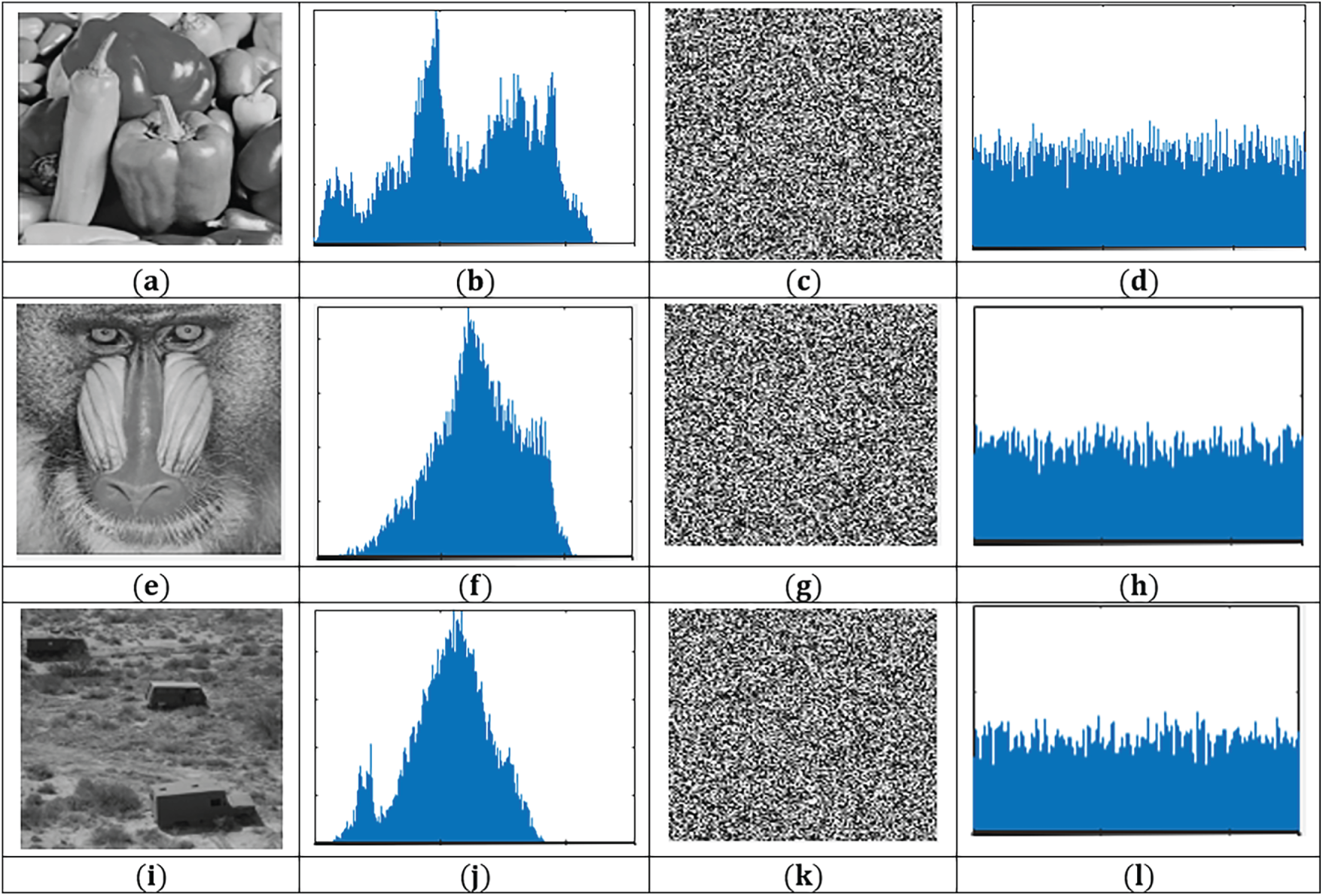
Figure 11: Histogram of test images and corresponding ciphered images (a) Original peppers image, (b) Histogram of original peppers image, (c) Ciphered peppers image, (d) Histogram of ciphered peppers image, (e) Original baboon image, (f) Histogram of original baboon image, (g) Ciphered baboon image, (h) Histogram of ciphered baboon image, (i) Original truck image, (j) Histogram of original truck image, (k) Ciphered truck image, and (l) Histogram of ciphered truck image.
If the value of variance (x) is small, the image is deemed uniform. Table 5 lists the variance of all images encrypted with the proposed technique. The conclusion drawn from the simulation undertaken is that the proposed algorithm gives way to encrypted images having uniform histograms.
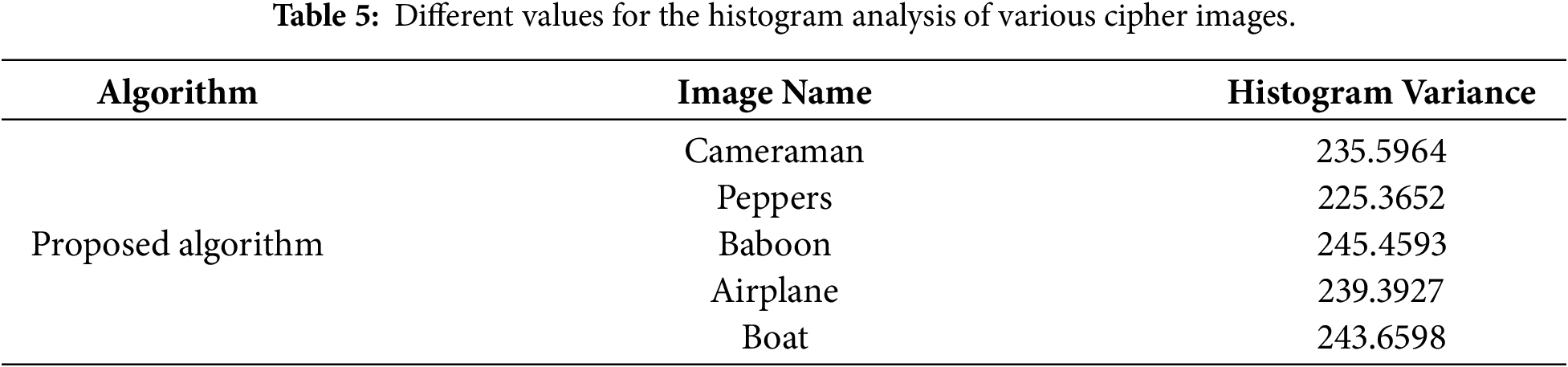
Table 6 shows the comparison between our proposed encryption algorithm that use hyperchaotic S-box and previous studies that used similar methods.
4.2 Evaluation of Digital Peppers Image Transmission in the UOWC System
In this part, we discuss the performance of digital image transmission in UOWC systems for the following five types of Jerlov waters as follows:
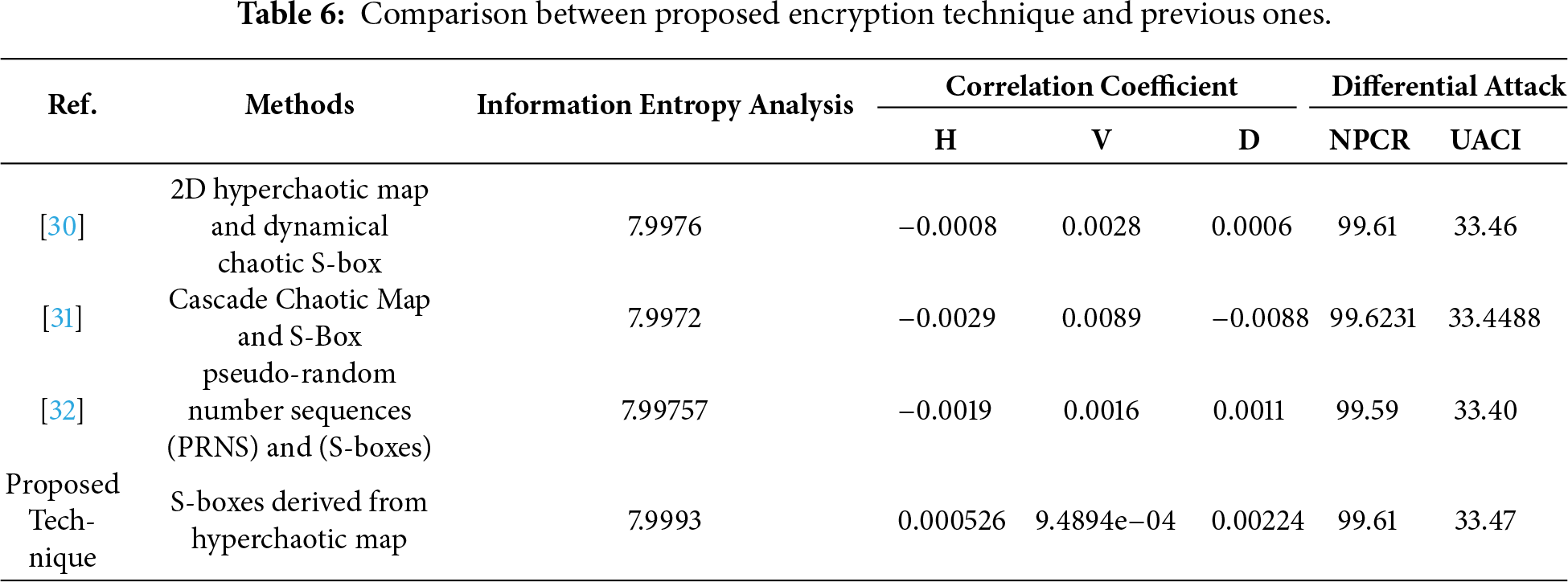
Fig. 12 shows the PSNR performance in JI water for three different transmission scenarios as a function of underwater distance. The first scenario corresponds to the received peppers image transmitted without encryption and without any post-reception enhancement, representing direct image transmission through the underwater channel. This case exhibits the lowest PSNR values across all distances due to severe channel-induced distortions. The second scenario represents the decrypted peppers image without post-decryption enhancement, reflecting the effect of the encryption–decryption process alone on image recovery. The third scenario corresponds to the decrypted peppers image with post-decryption enhancement using median and high-pass filtering, which is included to evaluate post-processing-assisted reconstruction under underwater channel impairments. As the transmission distance increases, the decrypted and enhanced images consistently achieve higher PSNR values. For example, at 24 m, the PSNR increases from 9.25 dB for the unencrypted received image to 20.13 dB for the decrypted and decrypted with median and high pass filter. This significant difference underscores the effectiveness of the proposed encryption and enhancement techniques in mitigating the detrimental effects of underwater transmission on image quality, particularly at extended ranges.
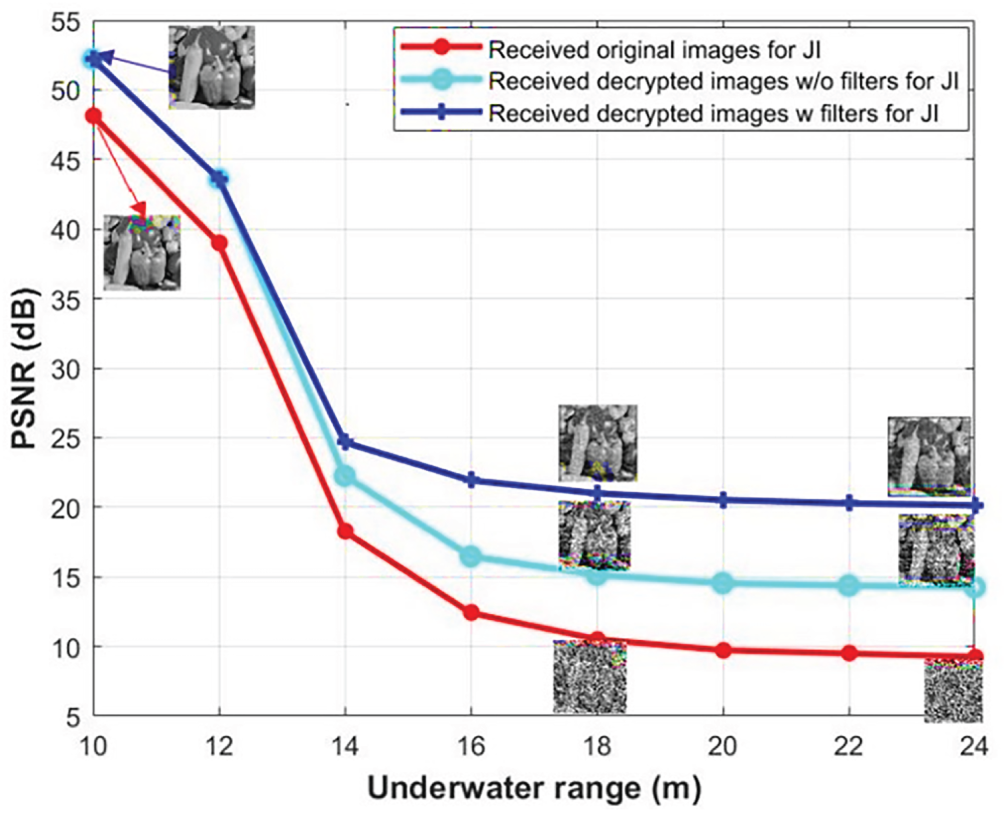
Figure 12: PSNR for the received digital transmission of the plain, ciphered, and enhanced peppers image against underwater range in JI water.
The SSIM provides a comprehensive assessment of image quality by evaluating structural, contrast, and luminance attributes. This study employs SSIM to compare the visual quality of received plain, decrypted, and enhanced images of peppers at various underwater distances relative to the original image. Fig. 13 illustrates the SSIM of received images in JI water. As the transmission distance increases, SSIM values generally decline. However, the highest SSIM values are consistently observed for enhanced peppers images. Initially, all received images achieve a perfect SSIM value of 1. This value decreases to a minimum of 0.02 for the received plain digital peppers image at 24 m. In the case of the received decrypted image at the same distance, the SSIM value improves to 0.24. Furthermore, the SSIM value reaches its highest value of 0.48 for the enhanced peppers image at 24 m. These results underscore the significant improvement in image clarity achieved through filtering, particularly at longer distances, where it surpasses the visual quality of the other received images.
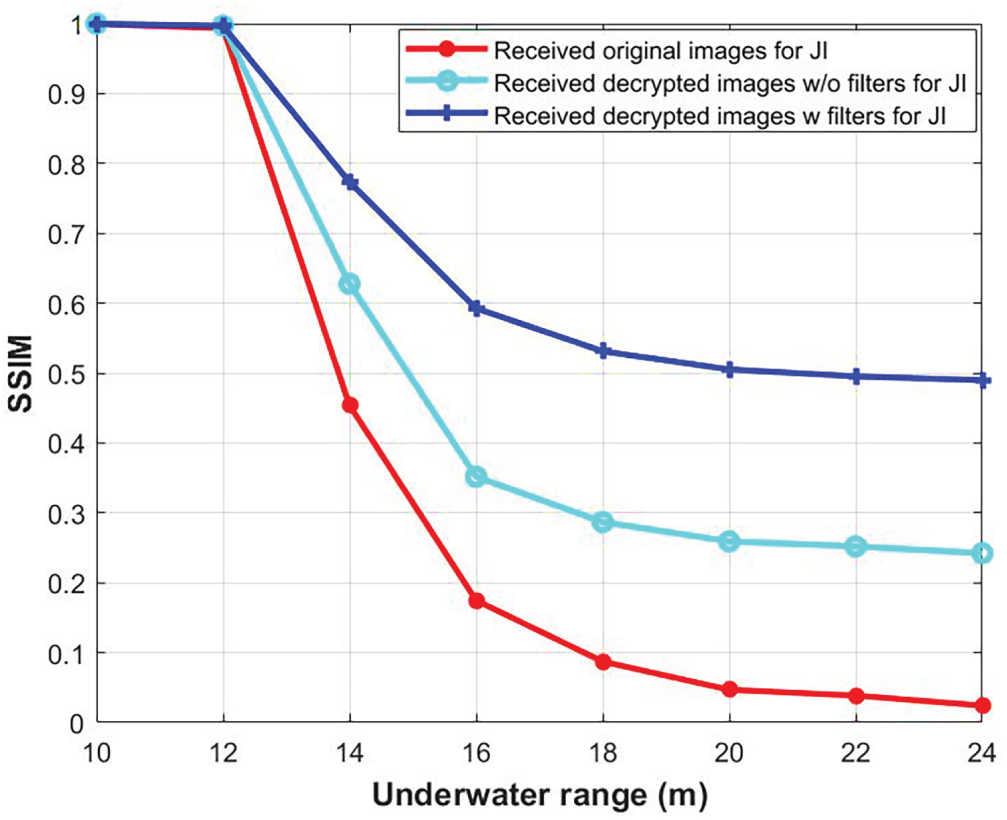
Figure 13: SSIM for the received digital transmission of the plain, ciphered, and enhanced peppers image against underwater range in JI water.
JIA water exhibits slightly higher attenuation than JI water, although the attenuation remains relatively low. This difference in attenuation affects the underwater transmission distance, resulting in shorter achievable ranges compared to JI. Figs. 14–16 present the visual quality of received plain, decrypted, and enhanced peppers images at various underwater distances when the system operates in JIA water. As shown in Fig. 14, the visual quality of the received original peppers image degrades at longer distances. The received plain peppers image maintains slightly good quality up to 14.5 m; beyond this distance, the visual quality deteriorates until it completely vanishes at 22.5 m. Applying the S-box hyper-chaotic maps encryption technique effectively protects the data integrity of the images and improves the visual quality of the received peppers images, as evident in Fig. 15, which displays the received decrypted peppers images at underwater distances ranging from 8.5 to 22.5 m. Furthermore, the visual quality of the decrypted peppers images is further enhanced when filters are applied, particularly at underwater spans of 20.5 and 22.5 m, as depicted in Fig. 16.
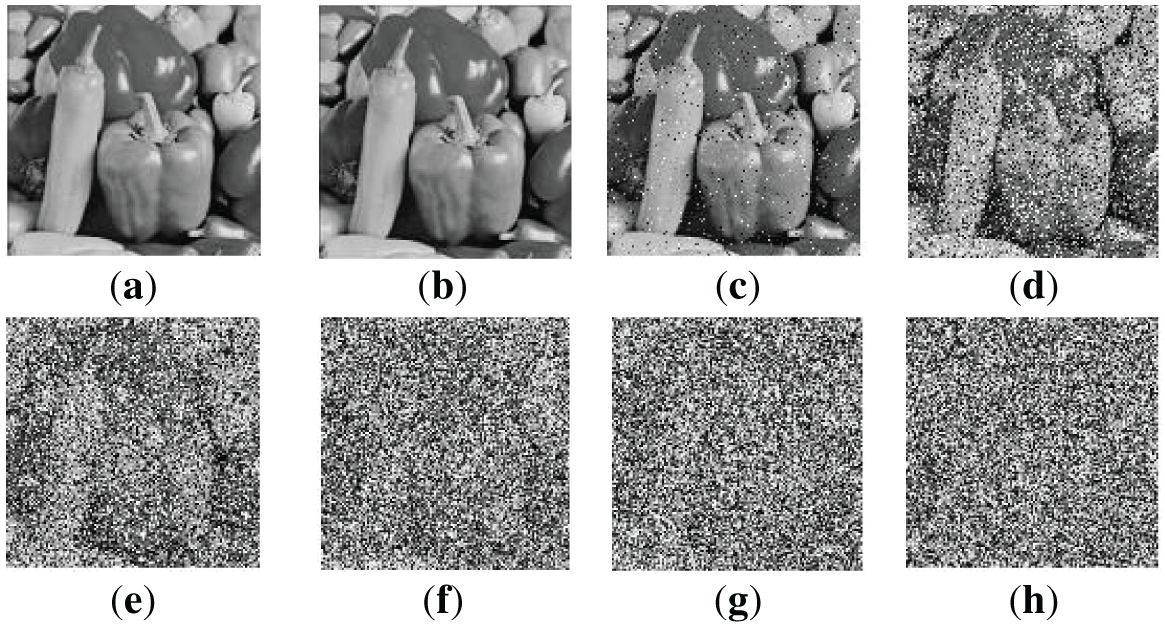
Figure 14: Received plain peppers images for JIA water at underwater span of (a) 8.5 m, (b) 10.5 m, (c) 12.5 m, (d) 14.5 m, (e) 16.5 m, (f) 18.5 m, (g) 20.5 m, and (h) 22.5 m.
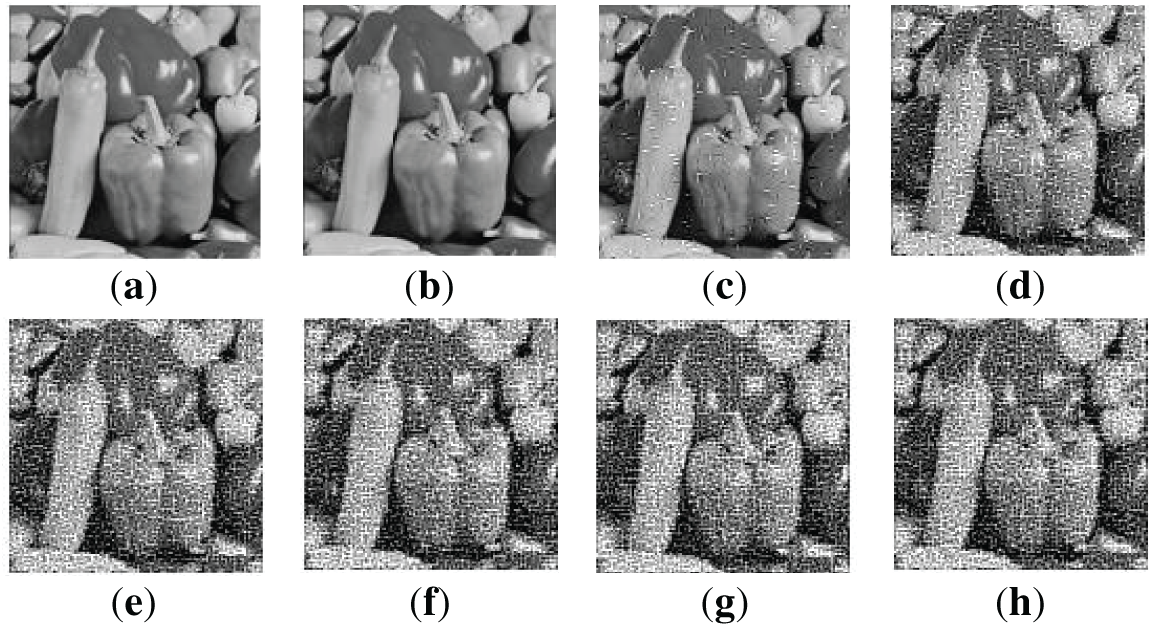
Figure 15: Received decrypted peppers images for JIA water at underwater span of (a) 8.5 m, (b) 10.5 m, (c) 12.5 m, (d) 14.5 m, (e) 16.5 m, (f) 18.5 m, (g) 20.5 m, and (h) 22.5 m.
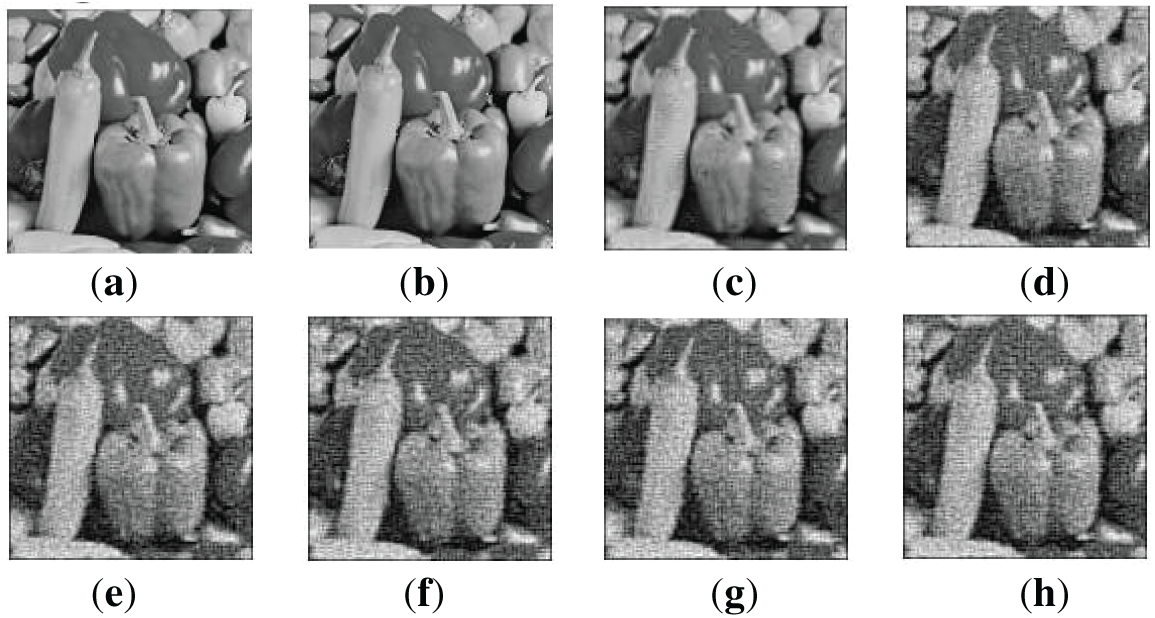
Figure 16: Enhanced received decrypted peppers images for JIA water at underwater span of (a) 8.5 m, (b) 10.5 m, (c) 12.5 m, (d) 14.5 m, (e) 16.5 m, (f) 18.5 m, (g) 20.5 m, and (h) 22.5 m.
Table 7 presents the SNR values for received peppers images at various underwater distances in JIA water. Decrypted peppers images consistently exhibit higher SNR values compared to the received original peppers images. Furthermore, enhanced images demonstrate the highest SNR values. For instance, at an underwater distance of 22.5 m, the SNR for the plain received peppers image is 4.42 dB. This value increases to 8.89 dB for the decrypted image and 14.26 dB for the enhanced image at the same distance. This translates to a 101.13% improvement in SNR for decrypted peppers images and a 222.62% improvement for enhanced peppers images at an underwater transmission distance of 22.5 m. These findings underscore the significant enhancement in image quality and SNR achieved through encryption and filtering techniques, particularly at longer distances.
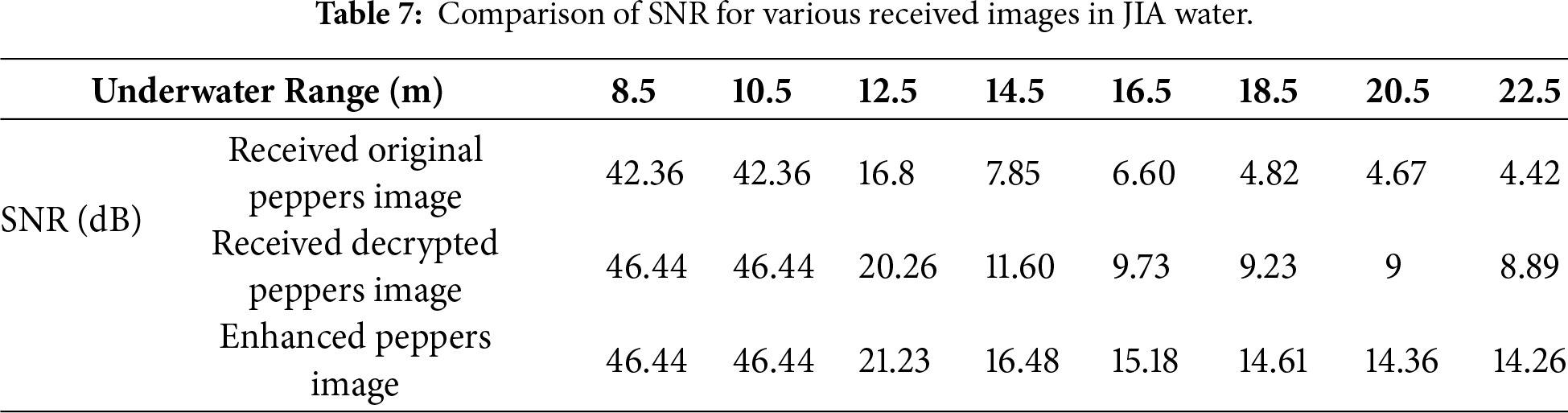
Fig. 17a,b illustrates the PSNR and SSIM values for the received peppers images in JIA water at underwater ranges from 8.5 to 22.5 m. It is evident that transmitting images without encryption leads to significantly lower PSNR and SSIM values, particularly at greater distances. However, applying encryption and enhancement techniques significantly improves both PSNR and SSIM values, especially over extended ranges. For example, at 22.5 m underwater distance, the PSNR for the enhanced image is 20.08 dB, which is substantially higher than that of the plain image (9.19 dB). Additionally, the SSIM value for the enhanced image at the same underwater distance is 0.49, which is considerably greater than those of the plain (0.02) and decrypted images (0.24).
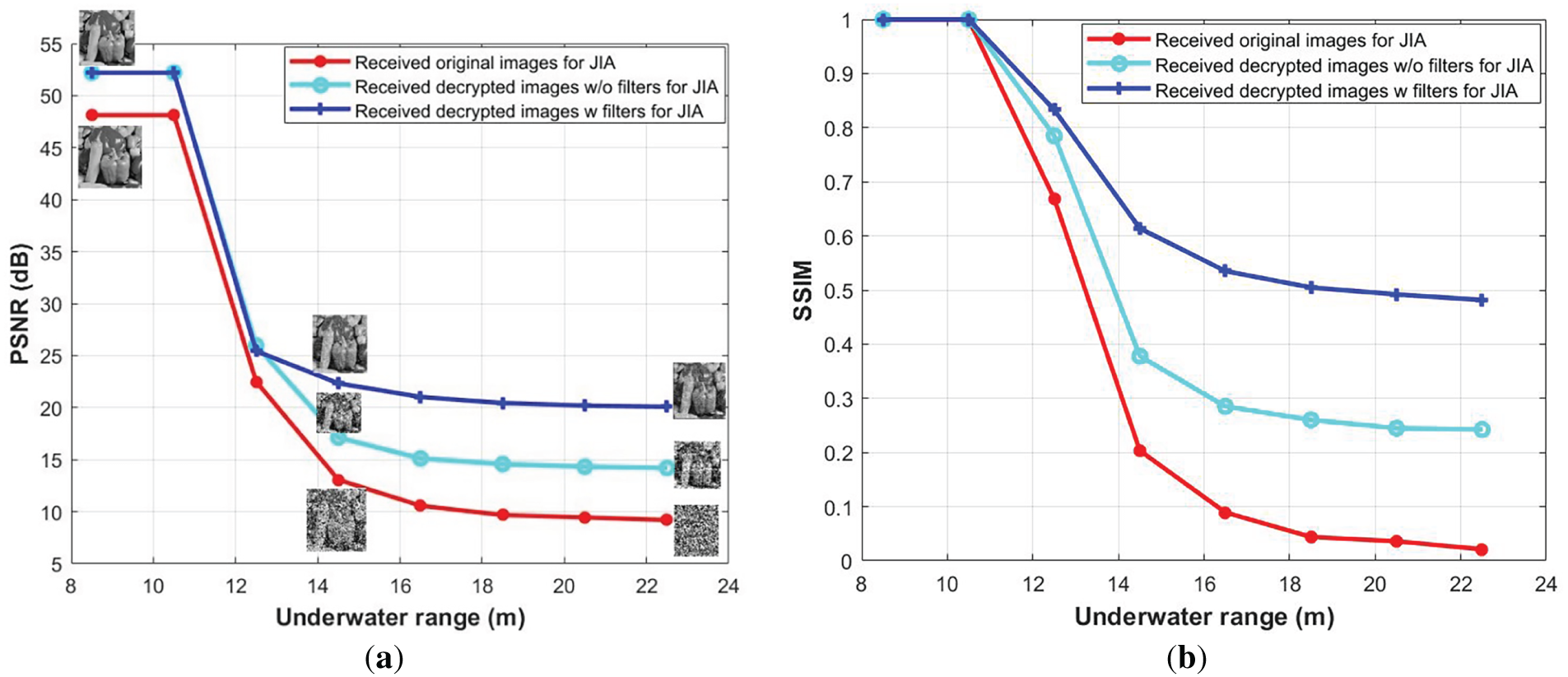
Figure 17: (a): PSNR for the received digital transmission of the plain, ciphered, and enhanced peppers image against underwater range in JIA water. (b): SSIM for the received digital transmission of the plain, ciphered, and enhanced peppers image against underwater range in JIA water.
JIB water is typically found in coastal regions and areas with moderate biological activity. This water type has higher concentrations of chlorophyll and suspended particles, resulting in greater attenuation compared to JI and JIA. Consequently, the underwater transmission range is adversely affected. Fig. 18 displays received plain (at the top), decrypted (at the middle), and enhanced (at the bottom) peppers images at various underwater links for JIB. Without employing any encryption technique, the digital peppers image preserves its quality when transmitted underwater over 11.2 m. In contrast, the S-boxes hyperchaotic maps encryption technique allows the encrypted digital peppers image to maintain its visual integrity over an underwater distance of 14.4 m, exceeding the range achievable by the unencrypted image by 3.2 m. Moreover, the incorporation of median and high-pass filters substantially enhances the visual clarity of received encrypted images, especially when transmitted over longer underwater distances.
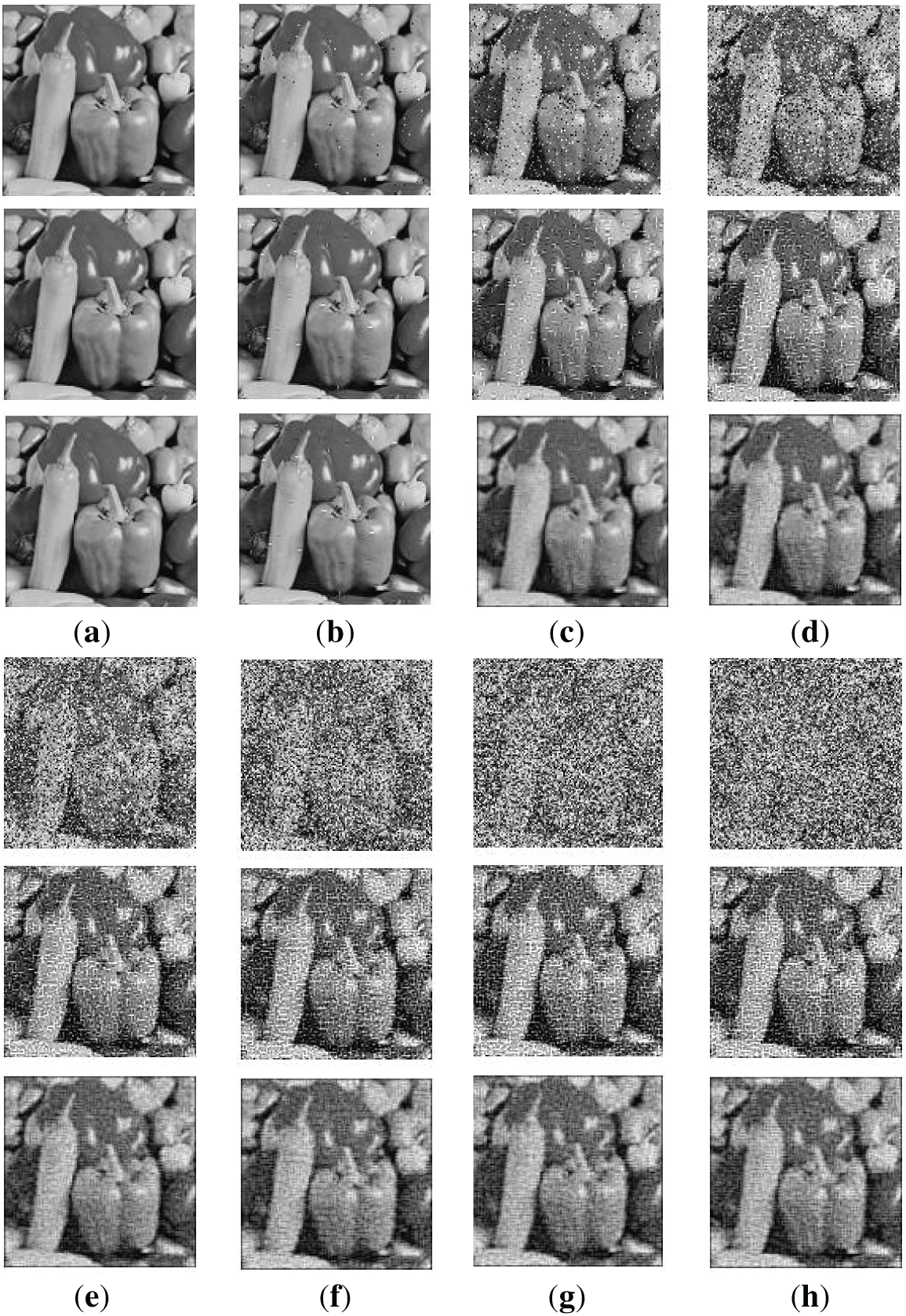
Figure 18: Received plain, decrypted, and enhanced peppers images for JIB water at underwater span of (a) 8.8 m, (b) 9.6 m, (c) 10.4 m, (d) 11.2 m, (e) 12 m, (f) 12.8 m, (g) 13.6 m, and (h) 14.4 m.
Table 8 shows the SNR values for received pepper images from different underwater distances in JIB water. Decrypted peppers images regularly have greater SNR values than the received original peppers images. Furthermore, the highest SNR values are obtained for enhanced peppers images.
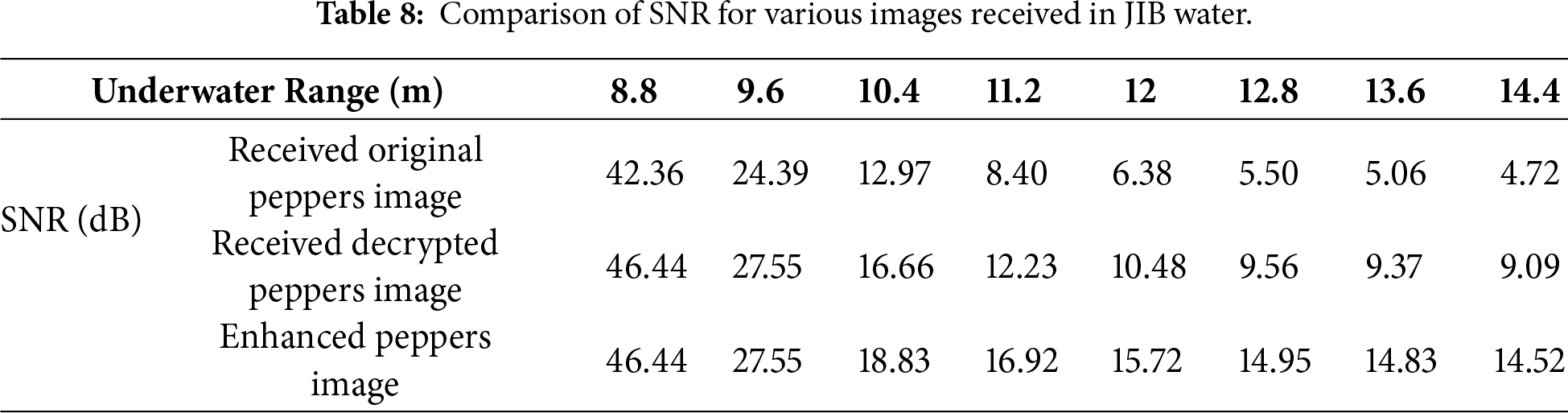
Fig. 19a,b depicts the effect of different underwater transmission distances on the PSNR and SSIM, respectively, for JIB water. PSNR and SSIM values are higher for shorter underwater distances. Transmission of the original digital peppers image causes a considerable decline in image quality as the link between transmitter and receiver sides increases, with the PSNR and SSIM values dropping abruptly from 48.13 dB and 0.99 at 8.8 m to 9.57 dB and 0.04 at 14.4 m, respectively. In contrast, the encrypted digital peppers image delivered via the UOWC channel retains higher quality and SSIM values than the unencrypted version. The PSNR and SSIM values increased from 9.57 dB and 0.04 for the unencrypted image to 14.41 dB and 0.25, respectively, for the decrypted image. Furthermore, the use of filters improves the PSNR and SSIM values, emphasizing the efficiency of encryption and filtering techniques in preserving image quality over longer underwater transmission distances.
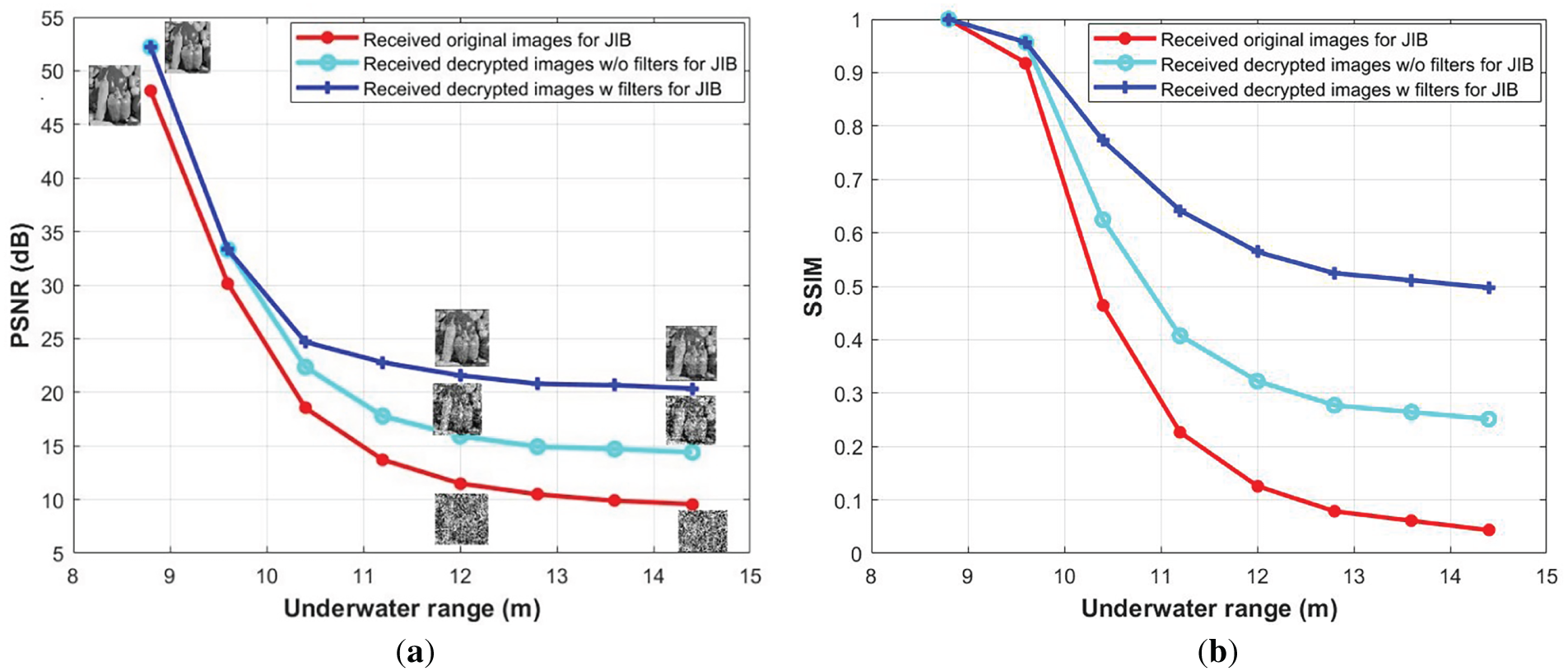
Figure 19: (a): PSNR for the received digital transmission of the plain, ciphered, and enhanced peppers image against underwater range in JIB water. (b): SSIM for the received digital transmission of the plain, ciphered, and enhanced peppers image against underwater range in JIB water.
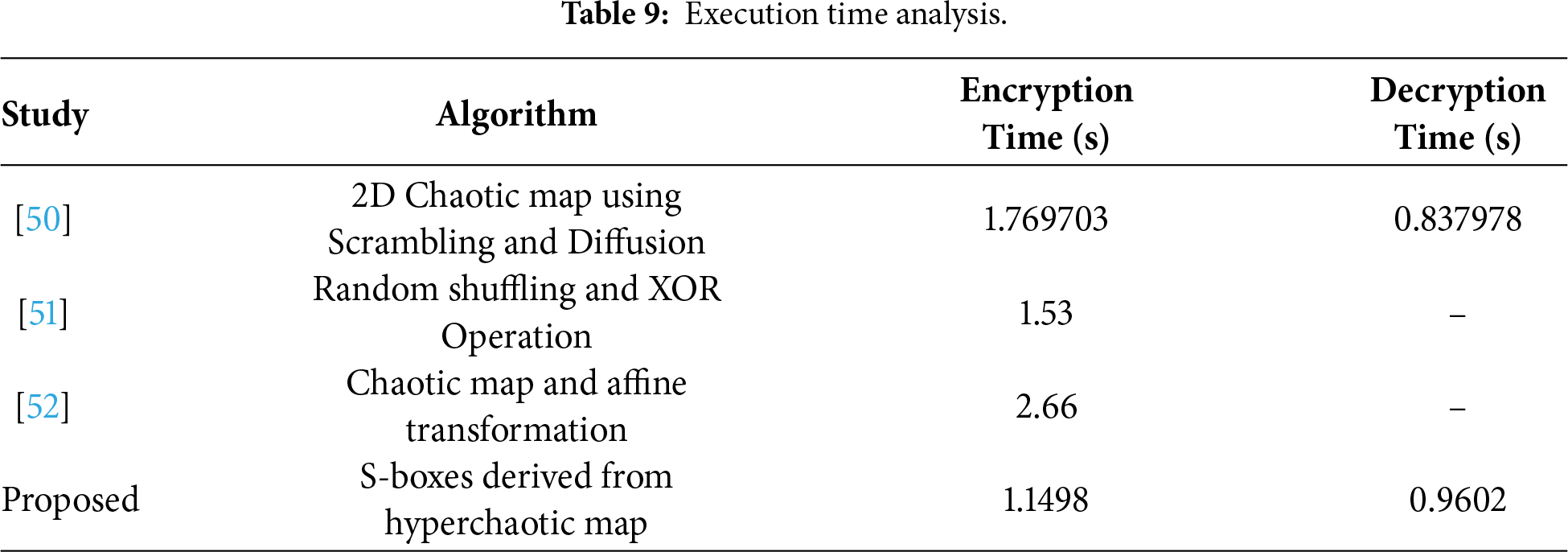
The computational complexity of the proposed technique is evaluated by analyzing the time and resource consumption associated with the encryption and decryption processes, while ensuring that the desired security thresholds are met. The proposed encryption scheme is tested for computational efficiency using a 128 × 128 image as the plaintext input.
The timing complexity analysis is conducted on a system with the following specifications: a 3.0 GHz processor, 8 GB of RAM, Windows 10 operating system, and MATLAB R2017b. Table 9 provides a comparative analysis of the execution time of the proposed algorithm against other methods. The results demonstrate that the proposed scheme achieves lower computational complexity for encryption while maintaining a competitive decryption time. These findings highlight the efficiency of the proposed approach in comparison to existing methods.
This paper presents a secure digital image transmission framework for UOWC systems by integrating hyper-chaotic map–based S-box encryption with realistic underwater channel modeling. The proposed scheme demonstrates strong robustness against underwater channel impairments across different Jerlov water types. Performance evaluation confirms reliable transmission with acceptable underwater ranges while maintaining high image quality, as verified by SNR, PSNR, and SSIM metrics. The obtained results indicate that the proposed approach effectively enhances both transmission security and visual quality in UOWC environments, making it a promising solution for secure underwater imaging and communication applications. This is particularly advantageous for underwater surveillance, mine detection, and secure communication between submerged units or autonomous underwater vehicles (AUVs) in contested environments. Although the current work focuses on still image encryption, the algorithm’s efficiency and structure make it a promising candidate for extension to real-time video encryption. Future research will explore hardware optimization and streaming adaptations to enable secure, real-time underwater video transmission.
Acknowledgement: The authors extend their appreciation to Prince Sattam bin Abdulaziz University for funding this research work through the project number (PSAU/2025/01/34620).
Funding Statement: This research was funded by Prince Sattam bin Abdulaziz University, grant number PSAU/2025/01/34620.
Author Contributions: Somia A. Abd El-Mottaleb: Writing—review & editing, Writing—original draft, Validation, Methodology, Investigation, Formal analysis, Data curation, Conceptualization. Amira G. Mohamed: Writing—review & editing, Writing—original draft, Validation, Methodology, Investigation, Formal analysis, Data curation, Conceptualization. Mehtab Singh: Writing—review & editing original draft, Validation, Methodology, Investigation, Formal analysis, Data curation, Conceptualization. Hassan Yousif Ahmed: Writing—original draft, Validation. Medien Zeghid: Writing—original draft, Validation, Methodology, Investigation, Formal analysis. Abu Sufian A. Osman: Methodology, Investigation, Formal analysis, Data curation. Sami Mourou: Conceptualization, Data curation. All authors reviewed and approved the final version of the manuscript.
Availability of Data and Materials: Data available on request from the authors. The data that support the findings of this study are available from the Corresponding Author, [Abu Sufian A. Osman], upon reasonable request.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest.
References
1. Álvarez-Roa C, Álvarez-Roa M, Raddo TR, Jurado-Navas A, Castillo-Vázquez M. Cooperative terrestrial-underwater FSO system: design and performance analysis. Photonics. 2024;11(1):58. doi:10.3390/photonics11010058. [Google Scholar] [CrossRef]
2. Shen C, Guo Y, Oubei HM, Ng TK, Liu G, Park KH, et al. 20-meter underwater wireless optical communication link with 1.5 Gbps data rate. Opt Express. 2016;24(22):25502–9. doi:10.1364/OE.24.025502. [Google Scholar] [PubMed] [CrossRef]
3. Yang X, Zhang Y, Hua Y, Tong Z, Wang R, Song G, et al. 50-m/300-mbps underwater wireless optical communication using incoherent light source. J Lightwave Technol. 2023;41(22):6939–48. doi:10.1109/jlt.2023.3295343. [Google Scholar] [CrossRef]
4. Palmeiro A, Martín M, Crowther I, Rhodes M. Underwater radio frequency communications. In: Proceedings of the OCEANS 2011; 2011 Jun 6–9; Santander, Spain. p. 1–8. doi:10.1109/Oceans-Spain.2011.6003580. [Google Scholar] [CrossRef]
5. Geldard CT, Guler E, Hamilton A, Popoola WO. An empirical comparison of modulation schemes in turbulent underwater optical wireless communications. J Light Technol. 2022;40(7):2000–7. doi:10.1109/JLT.2021.3134090. [Google Scholar] [CrossRef]
6. Al-Shamma’a AI, Shaw A, Saman S. Propagation of electromagnetic waves at MHz frequencies through seawater. IEEE Trans Anntenas Propag. 2004;52(11):2843–9. doi:10.1109/TAP.2004.834449. [Google Scholar] [CrossRef]
7. Stojanovic M, Preisig J. Underwater acoustic communication channels: propagation models and statistical characterization. IEEE Commun Mag. 2009;47(1):84–9. doi:10.1109/MCOM.2009.4752682. [Google Scholar] [CrossRef]
8. Sendra S, Lloret J, Jimenez JM, Parra L. Underwater acoustic modems. IEEE Sens J. 2016;16(11):4063–71. doi:10.1109/JSEN.2015.2434890. [Google Scholar] [CrossRef]
9. Shen T, Guo J, Liang H, Li Y, Li K, Dai Y, et al. Research on a blue–green LED communication system based on an underwater mobile robot. Photonics. 2023;10(11):1238. doi:10.3390/photonics10111238. [Google Scholar] [CrossRef]
10. Ata Y, Yao J, Korotkova O. BER variation of an optical wireless communication system in underwater turbulent medium with any temperature and salinity concentration. Opt Commun. 2021;485:126751. doi:10.1016/j.optcom.2021.126751. [Google Scholar] [CrossRef]
11. Xu J. Underwater wireless optical communication: why, what, and how? Chin Opt Lett. 2019;17(10):100007. doi:10.3788/col201917.100007. [Google Scholar] [CrossRef]
12. Liu X, Yi S, Zhou X, Fang Z, Qiu ZJ, Hu L, et al. 34.5 m underwater optical wireless communication with 2.70 Gbps data rate based on a green laser diode with NRZ-OOK modulation. Opt Express. 2017;25(22):27937–47. doi:10.1364/OE.25.027937. [Google Scholar] [PubMed] [CrossRef]
13. Azam NA, Zhu J, Hayat U, Shurbevski A. Towards provably secure asymmetric image encryption schemes. Inf Sci. 2023;631:164–84. doi:10.1016/j.ins.2023.02.057. [Google Scholar] [CrossRef]
14. Daoui A, Yamni M, Chelloug SA, Ahmad Wani M, El-Latif AAA. Efficient image encryption scheme using novel 1D multiparametric dynamical tent map and parallel computing. Mathematics. 2023;11(7):1589. doi:10.3390/math11071589. [Google Scholar] [CrossRef]
15. Hao W, Zhou X, Chen X, Zhang T. A hybrid NEQR image encryption cryptosystem using two-dimensional quantum walks and quantum coding. SSRN J. 2022. doi:10.2139/ssrn.4224115. [Google Scholar] [CrossRef]
16. Wen W, Wei K, Zhang Y, Fang Y, Li M. Colour light field image encryption based on DNA sequences and chaotic systems. Nonlinear Dyn. 2020;99(2):1587–600. doi:10.1007/s11071-019-05378-8. [Google Scholar] [CrossRef]
17. El-Khamy SE, Mohamed AG. An efficient DNA-inspired image encryption algorithm based on hyper-chaotic maps and wavelet fusion. Multimed Tools Appl. 2021;80(15):23319–35. doi:10.1007/s11042-021-10527-6. [Google Scholar] [CrossRef]
18. Shao Y, Deng R, He J, Wu K, Chen LK. Real-time 2.2-Gb/s water-air OFDM-OWC system with low-complexity transmitter-side DSP. J Light Technol. 2020;38(20):5668–75. doi:10.1109/JLT.2020.3001864. [Google Scholar] [CrossRef]
19. Abd El-Mottaleb SA, Singh M, Atieh A, Aly MH. Performance evaluation of a UOWC system based on the FRS/OCDMA code for different types of Jerlov waters. Appl Opt. 2024;63(3):762–71. doi:10.1364/AO.507674. [Google Scholar] [PubMed] [CrossRef]
20. Ali MAA, Shaker FK. Performance of an underwater non-line-of-sight (NLOS) wireless optical communications system utilizing LED. J Opt. 2024;53(2):1429–37. doi:10.1007/s12596-023-01289-5. [Google Scholar] [CrossRef]
21. Wang J, Lu C, Li S, Xu Z. 100 m/500 Mbps underwater optical wireless communication using an NRZ-OOK modulated 520 nm laser diode. Opt Express. 2019;27(9):12171–81. doi:10.1364/OE.27.012171. [Google Scholar] [PubMed] [CrossRef]
22. Shen Y, Chen Z, Li Y, Li W. Multi-directional extended attractors, coexisting attractors, circuit implementation of grid-scroll memristive chaotic oscillator with application to underwater signal detection. Mech Syst Signal Process. 2025;238:113257. doi:10.1016/j.ymssp.2025.113257. [Google Scholar] [CrossRef]
23. Shen Y, Chen Z, Li Y, Li W. Coexisting attractors, amplitude control, circuit implementation of grid-scroll memristive hyperchaotic oscillator and its application in underwater signal detection. Mech Syst Signal Process. 2025;229:112525. doi:10.1016/j.ymssp.2025.112525. [Google Scholar] [CrossRef]
24. Nassar SS, Ayad NM, Kelash HM, El-sayed HS, El-Bendary MAM, Abd El-Samie FE, et al. Secure wireless image communication using LSB steganography and chaotic baker ciphering. Wirel Pers Commun. 2016;91(3):1023–49. doi:10.1007/s11277-016-3387-5. [Google Scholar] [CrossRef]
25. Zhang Z, Tang J, Zhang F, Huang T, Lu M. Medical image encryption based on Josephus scrambling and dynamic cross-diffusion for patient privacy security. IEEE Trans Circuits Syst Video Technol. 2024;34(10):9250–63. doi:10.1109/TCSVT.2024.3394951. [Google Scholar] [CrossRef]
26. Liang Q, Zhu C. A new one-dimensional chaotic map for image encryption scheme based on random DNA coding. Opt Laser Technol. 2023;160:109033. doi:10.1016/j.optlastec.2022.109033. [Google Scholar] [CrossRef]
27. Alawida M, Teh JS, Alshoura WH. A new image encryption algorithm based on DNA state machine for UAV data encryption. Drones. 2023;7(1):38. doi:10.3390/drones7010038. [Google Scholar] [CrossRef]
28. Lai Q, Liu Y. A cross-channel color image encryption algorithm using two-dimensional hyperchaotic map. Expert Syst Appl. 2023;223:119923. doi:10.1016/j.eswa.2023.119923. [Google Scholar] [CrossRef]
29. Song W, Fu C, Zheng Y, Tie M, Liu J, Chen J. A parallel image encryption algorithm using intra bitplane scrambling. Math Comput Simul. 2023;204:71–88. doi:10.1016/j.matcom.2022.07.029. [Google Scholar] [CrossRef]
30. Zhou S, Qiu Y, Wang X, Zhang Y. Novel image cryptosystem based on new 2D hyperchaotic map and dynamical chaotic S-box. Nonlinear Dyn. 2023;111(10):9571–89. doi:10.1007/s11071-023-08312-1. [Google Scholar] [CrossRef]
31. Zheng J, Bao T. An image encryption algorithm using cascade chaotic map and S-box. Entropy. 2022;24(12):1827. doi:10.3390/e24121827. [Google Scholar] [PubMed] [CrossRef]
32. Haider MI, Shah T, Ali A, Shah D, Khalid I. An innovative approach towards image encryption by using novel PRNs and S-boxes Modeling techniques. Math Comput Simul. 2023;209(1):153–68. doi:10.1016/j.matcom.2023.01.036. [Google Scholar] [CrossRef]
33. El-Mottaleb SAA, Mohamed AG, Chehri A, Singh M, Atieh A, Ahmed HY, et al. Performance of cipher image transmission in free space optics under foggy weather. IEEE Access. 2023;11:139478–97. doi:10.1109/ACCESS.2023.3338168. [Google Scholar] [CrossRef]
34. Kaushal H, Kaddoum G. Underwater optical wireless communication. IEEE Access. 2016;4:1518–47. doi:10.1109/ACCESS.2016.2552538. [Google Scholar] [CrossRef]
35. Kandouci C. Investigation of Jervol water types properties effects on underwater optical wireless OCDMA system performances for different modulation techniques. Opt Quantum Electron. 2021;54(1):3. doi:10.1007/s11082-021-03390-0. [Google Scholar] [CrossRef]
36. Gabriel C, Khalighi MA, Bourennane S, Léon P, Rigaud V. Monte-Carlo-based channel characterization for underwater optical communication systems. J Opt Commun Netw. 2013;5(1):1–12. doi:10.1364/jocn.5.000001. [Google Scholar] [CrossRef]
37. El-Mottaleb SAA, Singh M, Atieh A, Aly MH. Performance analysis of 3 × 10 Gb/s UOWC transmission system based on OCDMA using a DPS code. Opt Quantum Electron. 2023;56(2):217. doi:10.1007/s11082-023-05815-4. [Google Scholar] [CrossRef]
38. El-Mottaleb SAA, Mohamed AG, Ahmed HY, Zeghid M. Performance enhancement of FSO communication system under rainy weather environment using a novel encryption technique. IEEE Access. 2024;12:13729–46. doi:10.1109/ACCESS.2024.3357396. [Google Scholar] [CrossRef]
39. Singh M, Singh ML, Singh G, Kaur H, Priyanka, Kaur S. Real-time image transmission through underwater wireless optical communication link for Internet of Underwater Things. Int J Commun. 2021;34(16):e4951. doi:10.1002/dac.4951. [Google Scholar] [CrossRef]
40. Liu M, Ning C, Zhu C. A secure image encryption scheme based on a new hyperchaotic system and 2D compressed sensing. Entropy. 2024;26(7):603. doi:10.3390/e26070603. [Google Scholar] [PubMed] [CrossRef]
41. Zhang J, Liu E. Circuit design and image encryption of CNN chaotic system based on memristor. Eur Phys J B. 2024;97(7):100. doi:10.1140/epjb/s10051-024-00743-y. [Google Scholar] [CrossRef]
42. AlShaikh M, Alzaqebah M, Gmati N, Alrefai N, Alsmadi MK, Almarashdeh I, et al. Image encryption algorithm based on factorial decomposition. Multimed Tools Appl. 2024;83(40):88447–67. doi:10.1007/s11042-023-17663-1. [Google Scholar] [CrossRef]
43. Li YM, Jiang M, Wei D, Deng Y. A novel image encryption algorithm based on compressive sensing and a two-dimensional linear canonical transform. Fractal Fract. 2024;8(2):92. doi:10.3390/fractalfract8020092. [Google Scholar] [CrossRef]
44. Kumar A, Dua M. A novel exponent–sine–cosine chaos map-based multiple-image encryption technique. Multimed Syst. 2024;30(3):141. doi:10.1007/s00530-024-01334-8. [Google Scholar] [CrossRef]
45. Li P, Qian J, Xu TT. New chaotic systems and application in DNA colored image encryption. Multimed Tools Appl. 2024;83(17):50023–45. doi:10.1007/s11042-023-17605-x. [Google Scholar] [CrossRef]
46. Mohamed AG, Korany NO, El-Khamy SE. New DNA coded fuzzy based (DNAFZ) S-boxes: application to robust image encryption using hyper chaotic maps. IEEE Access. 2021;9:14284–305. doi:10.1109/ACCESS.2021.3052161. [Google Scholar] [CrossRef]
47. Durdu A. Image transfer with secure communications application using a new reversible chaotic image encryption. Multimed Tools Appl. 2024;83(2):3397–424. doi:10.1007/s11042-023-15707-0. [Google Scholar] [CrossRef]
48. Su Y, Wang X, Gao H. Chaotic image encryption algorithm based on bit-level feedback adjustment. Inf Sci. 2024;679(1):121088. doi:10.1016/j.ins.2024.121088. [Google Scholar] [CrossRef]
49. Wang P, Ding L. Research on variable parameter color image encryption based on five-dimensional tri-valued memristor chaotic system. Entropy. 2024;26(7):536. doi:10.3390/e26070536. [Google Scholar] [PubMed] [CrossRef]
50. Teng L, Wang X, Yang F, Xian Y. Color image encryption based on cross 2D hyperchaotic map using combined cycle shift scrambling and selecting diffusion. Nonlinear Dyn. 2021;105(2):1859–76. doi:10.1007/s11071-021-06663-1. [Google Scholar] [CrossRef]
51. Masood F, Driss M, Boulila W, Ahmad J, Rehman SU, Jan SU, et al. A lightweight chaos-based medical image encryption scheme using random shuffling and XOR operations. Wirel Pers Commun. 2022;127(2):1405–32. doi:10.1007/s11277-021-08584-z. [Google Scholar] [CrossRef]
52. Ahmad J, Hwang SO. A secure image encryption scheme based on chaotic maps and affine transformation. Multimed Tools Appl. 2016;75(21):13951–76. doi:10.1007/s11042-015-2973-y. [Google Scholar] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF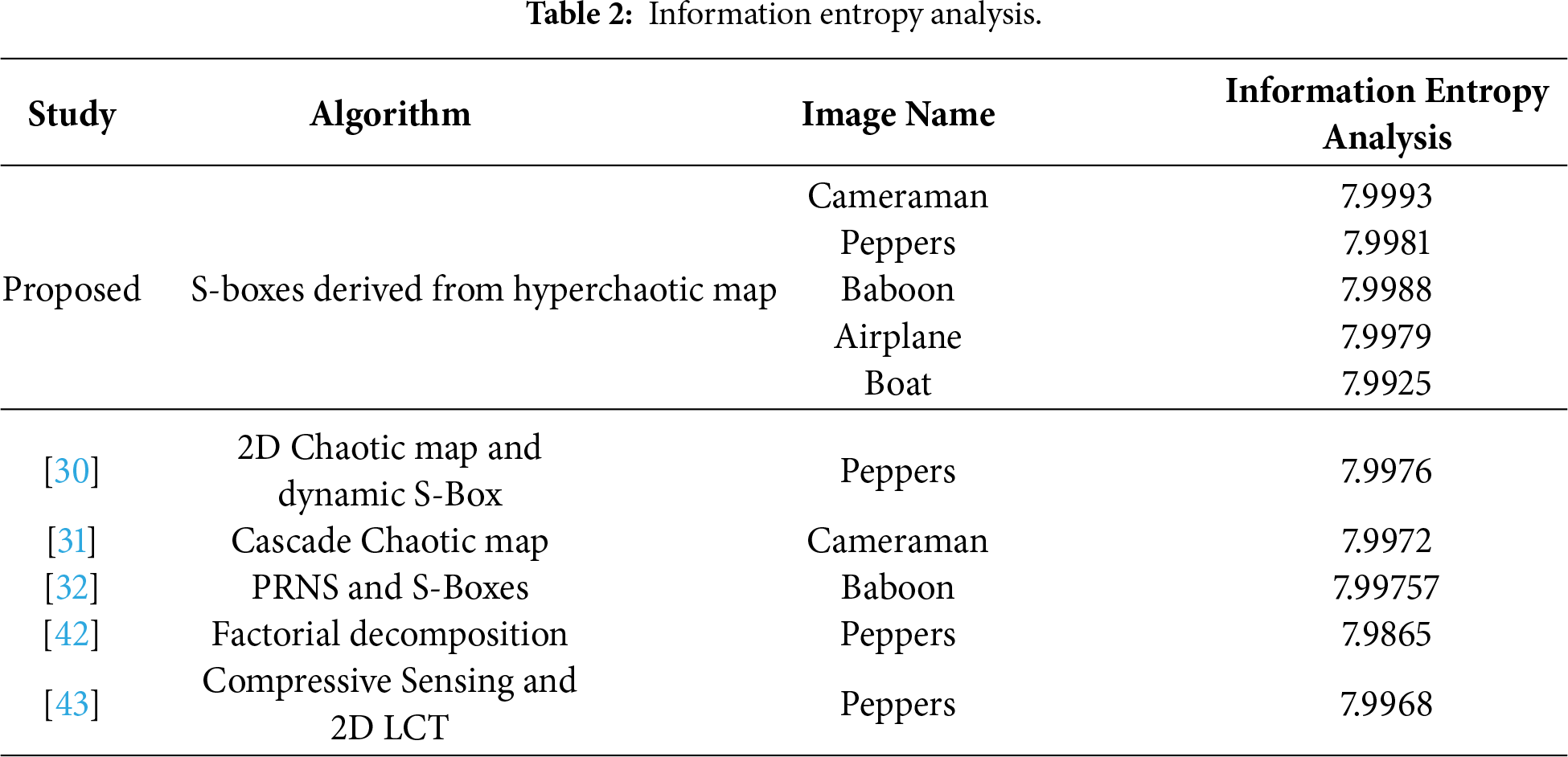
 Downloads
Downloads
 Citation Tools
Citation Tools