 Open Access
Open Access
ARTICLE
Multisecurity GAN-Steganography-Blockchain for IoT-Cloud Self-Service Banking
1 Computer Science and Engineering, Jawaharlal Nehru Technological University Anantapur, Anantapuramu, India
2 Centre for Development of Advanced Computing, Pashan, Pune, India
3 Computer Science and Engineering, University of Visvesvaraya College of Engineering, Bangalore University, Bangalore, India
4 Cloud Computing and Distributed Systems Laboratory, University of Melbourne, Melbourne, VIC, Australia
5 Computer Science, Florida International University, Miami, FL, USA
6 Consciousness Studies Program, National Institute of Advanced Studies, Bangalore, India
* Corresponding Author: Mangala Natampalli. Email:
Journal on Internet of Things 2026, 8, 1-30. https://doi.org/10.32604/jiot.2026.067726
Received 11 May 2025; Accepted 18 December 2025; Issue published 24 February 2026
Abstract
Contemporary banking focuses on self-service and customer-centric experience by harnessing Internet of Things (IoT) and Cloud Computing. However, these systems remain vulnerable to multifaceted cyberattacks. The IoT-Cloud-based systems can be safeguarded through authentication, confidentiality, integrity, availability, privacy, and non-repudiation. This work proposes a multi-stage security consisting of Generative Adversarial Networks (GAN) for facial authentication, hybrid Curvelet and Least-Significant-Bit (LSB) Steganography for data protection, and Ethereum Blockchain for transactions and storage security to provide complete protection to the self-service pipeline. Customers are authenticated using live images from IoT cameras by GAN facial recognition. Improved data concealment is provided by combining Curvelet and LSB Steganography. Ethereum Blockchain is selected for use in off-chain mode to provide integrity, time-stamping, non-repudiation, and fraud resistance for banking transactions, along with immutable permanent data storage in the Cloud. The Frechet Inception Distance and Inception Score metrics show that the GAN-generated front angle images are accurate, and the Precision, Recall, and F-Measure of 90% ascertain that the facial authentication is correct. Superior imperceptibility of the hybrid Curvelet-LSB Steganography is ascertained by the Peak-Signal-to-Noise-Ratio metric and Histogram analysis. An upload time of less than 3 minutes for fairly large data sizes, and cost-free transactions make Ethereum off-chain a preferred choice. Thus, the proposed multisecurity pipeline assures a highly secure and convenient banking experience for customers.Keywords
Self-service is convenient for users as it provides immediate and individualized access to services. The self-service applications in domains such as banking, shopping, or IT support are becoming feasible due to the advancements in Internet of Things (IoT), Cloud Computing (CC), Artificial Intelligence (AI), Augmented Reality (AR), Robotics, and related technologies [1,2]. For example, in a self-service banking ecosystem, the IoT cameras perform biometric authentication of the customers and provide access control to smart lockers, card transactions, etc. [3]. Cloud Computing is used for real-time processing, control, and storage of Banking data. Advanced networking technologies [4] are used to seamlessly integrate the IoT devices and computing-storage technologies of Mist, Edge, Fog, and Cloud Computing [5,6].
Banking and financial applications have become particularly vulnerable to cyberattacks in recent years. In 2022, the UK reported 336,707 cases of credit-card and online-banking fraud, amounting to £184 million in financial losses [7]. Consequently, financial institutions are facing great pressure to strengthen data privacy and integrity safeguards [8]. Banking transactions are typically done through In-Person mode, such as ATM or Locker Access, Online mode over the internet, such as National Electronic Funds Transfer (NEFT), and Mobile Phone-based Unified Payments Interface (UPI), which have prompted several hackers to attack banking applications and steal clients’ money and data. Therefore, it is very important to provide robust security in self-service banking applications encompassing authentication, confidentiality, integrity, availability, privacy, and non-repudiation to counteract adversaries in the Banking system.
Security mechanisms such as authentication and access control, steganography, cryptography, and blockchain are capable of safeguarding financial applications [9–11]. While both Cryptography and Steganography offer security from unauthorized access, they operate through distinct approaches: Cryptography focuses on encrypting message content, whereas Steganography conceals the message’s very existence [12,13]. In Steganography, the secret message is transmitted by subtly hiding it in a media object, such that nobody other than the sender and receiver is aware of the presence of the message [14,15]. Steganography offers lower overhead data protection and is particularly convenient in banking applications, wherein confidential data can be inconspicuously concealed inside customer photos. The feature of message undetectability is a prime demotivator for adversaries to grope for sensitive information. Steganography can be synergistically combined with blockchain and complementary technologies to achieve enhanced security. Blockchain technology preserves the integrity and transparency of transactions. It functions as a distributed digital ledger that records all transactions onto a network of computers. Because the network is not controlled by a single entity, it is less vulnerable to hacking and fraud. Beyond cryptocurrencies, blockchain is used for various applications such as supply chain tracking, digital identity verification, and secure voting systems. Its robust security characteristics and transparency establish it as a dependable and trustworthy solution. The Generative Adversarial Network (GAN) comprises a Generator and a Discriminator and is capable of synthesizing text, generating images, and predicting subsequent video frames [16]. Given GAN’s ability to generate realistic frontal facial images, it is utilized in facial recognition applications [17].
The AutoThing framework [3] presents a secure transaction framework for a diverse self-service things (SST) environment. It demonstrates that traditional SST systems are not resilient against cyber-attacks and introduces an Offline Self-Service Things (OSST), which has higher attack resilience. Adee and Mouratidis [10] propose a four-step security consisting of RSA encryption, LSB steganography, data backup and recovery, and data sharing. Awotunde et al. [18] advocate for employing blockchain technology and multi-level authentication to secure transactions in banking platforms. Luo et al. [19] added blockchain to strengthen the security of steganographically concealed data transmission in covert communication. Jahnavi and Nandini [20] propose combining Steganography, Cryptography, and Blockchain to secure the Banking ecosystem. These aforementioned efforts represent multi-layered frameworks that integrate two or more security mechanisms to elevate protection levels for banking applications. However, limited research [19,20] specifically addresses banking data security through the combined application of steganography and blockchain. The present work distinguishes itself by delivering a practical, implementable solution for self-service banking applications through the strategic integration and adaptation of IoT-Cloud infrastructure, Generative Adversarial Networks (GAN), Steganography, and Blockchain paradigms.
In a self-service banking system, (i) only authorized persons should be permitted into the system, and (ii) the customers’ information/transactions should be completely secure. The main contributions of this paper include:
• IoT-Cloud-based secure architecture for self-service Banking
• Integrating GAN-based Authentication, Steganography, and Blockchain for robust security
• Designing an automatic authentication system using GAN facial recognition
• Improving data security by combining Curvelet steganography and LSB steganography
• Securing transactions and permanent data storage using off-chain Ethereum Blockchain
The rest of the paper is organized into the following sections. Section 2 describes the preliminaries of Generative Adversarial Networks, Steganography, and Blockchain, and Section 3 presents the background of security in the Banking domain. A review of recent Literature is presented in Section 4. Section 5 explains the proposed solution methodology. The experimentation and performance analysis are described in Section 6. Conclusion and future work are presented in Section 7.
2.1 Generative Adversarial Network-Overview
The Generative Adversarial Network comprises of two neural networks—a Generator and a Discriminator, that are trained simultaneously through an adversarial competing process. These networks engage in continuous opposition: the Generator network generates new data by taking as input random data, and the Discriminator classifies the Generator’s fake data from real data. This adversarial process drives both networks to improve over time. The objective of the GAN program is to achieve a Nash equilibrium, wherein the Generator produces data of such realism that the Discriminator cannot reliably differentiate between generated and genuine samples. Upon reaching this equilibrium state, the Generator has effectively learned to capture the underlying data distribution, producing high-quality synthetic output. GANs are used for a variety of data types, including images, music, and text. GANs have been successful in various tasks such as image generation, style transfer, super-resolution, and even generating realistic human-like text. Common applications of GAN include—facial recognition for contactless entry (DigiYatra), face-speech authenticated access control, emotion identification, rare disease diagnosis, student attention monitoring, and improved astronomical images [21].
In this research work, GAN is employed to produce accurate representations of human faces [22]. The preparatory step for face recognition involves generating clear frontal images of the customer from any-angle face images captured by the IoT camera. The Generator model learns to synthesize plausible frontal facial images while the Discriminator evaluates authenticity by comparing outputs against real customer images from the training dataset. The resultant frontal image is verified with the bank’s customer KYC-database to authenticate the customer to gain access to banking operations. The various components of the GAN face recognition are depicted in Fig. 1.
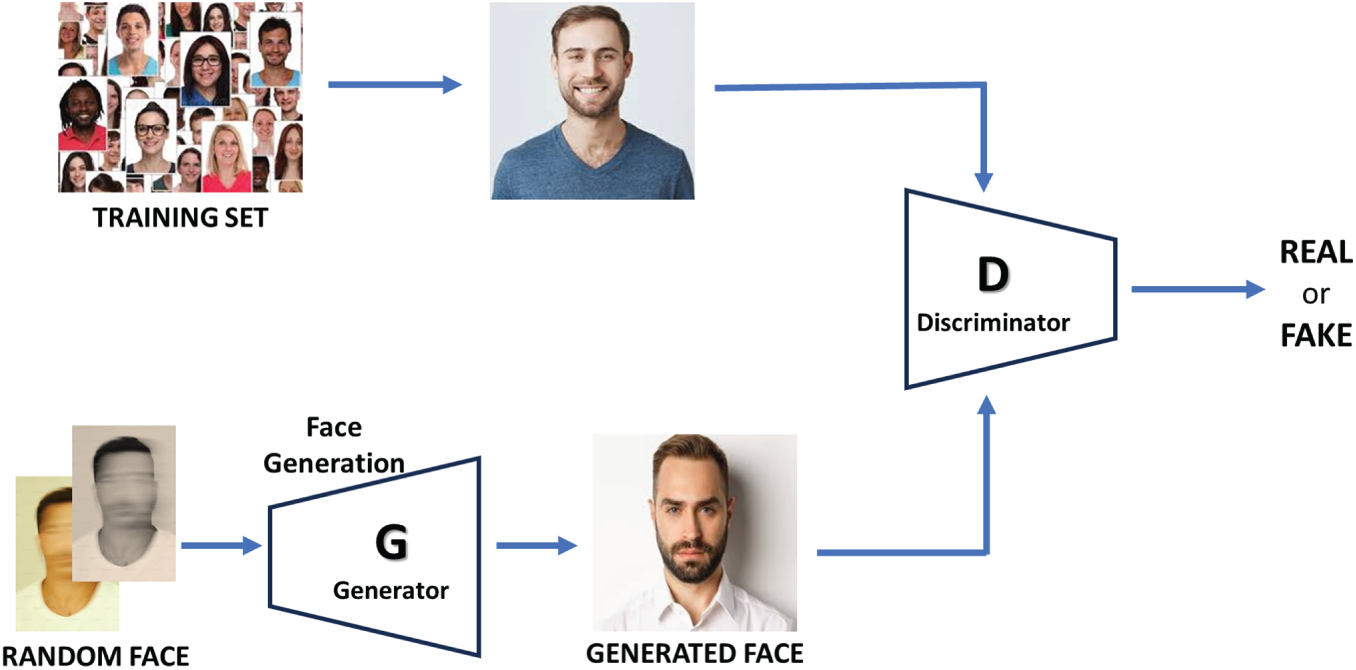
Figure 1: Architecture of GAN.
Steganography takes as input a secret digital message and a cover image, to generate imperceptible image perturbations and adds these perturbations to the cover image to get the steganographic (stego) image [23]. The basic model of image steganography encompasses several steps (Fig. 2).
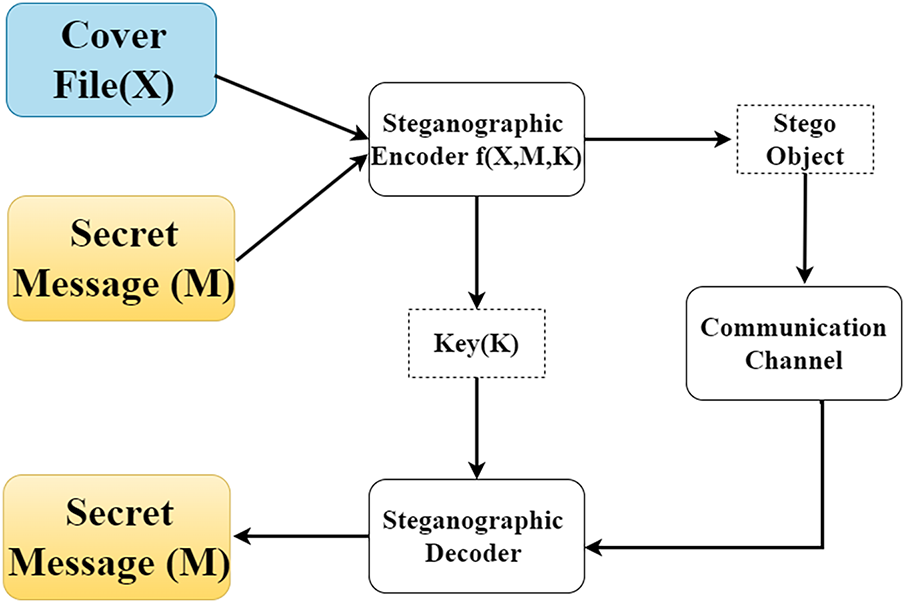
Figure 2: General block diagram of steganography.
(i) Cover Image Selection: The first step is to select an image that disguises the confidential information. It is often chosen so that it appears trustworthy to the viewers.
(ii) Selection of Secret Message: This could be a text message, another image, or any other type of data that the user wishes to conceal. It is important to ensure that the message is not too big in comparison to the cover image, or it may be impossible to hide it without apparent distortions to the cover image.
(iii) Embedding process: This is the actual steganography process which incorporates the secret information into the cover image.
• Least Significant Bit (LSB) Method: The least important bits of each pixel in the cover image are adjusted in this technique to include the data from the confidential message. Because only the lower-order bits are altered, the overall visual look of the image is unaltered.
• Domain Transformation Methods: These methods entail altering the cover image to a different domain, embedding the secret, and transforming back to the original domain. The Curvelet steganography and Discrete Cosine Transform are examples of this method.
(iv) Stego-Image Generation: When the embedding process is finished, the output is a new image known as the stego-image. This image should seem fairly equal to the original cover image. However, it now contains a concealed message which is imperceptible to the human eye.
(v) Transmission: The stego-image can then be transferred or saved as needed by the user. Anyone inspecting the stego-image should not suspect that it contains concealed data.
(vi) Extraction Method: The receiver can extract the hidden message from the stego-image if they are aware of the steganographic method that was applied. Reversing the embedding procedure is required.
(vii) Secret Message Retrieval: Following extraction, the recipient has access to the hidden information that has been previously stored within the image.
(viii) Additional Security: In some circumstances, it is also possible that the secret data is encrypted using cryptographic methods before embedding. This offers greater security so that even if someone finds and extracts the concealed message, they would not be able to comprehend it without the decryption key.
Curvelet transform steganography embeds the secret data into the curvelet-domain coefficients of a cover image. It exploits the curvelet transform’s ability to sparsely represent edges and curved features in images across multiple scales and several orientations [24]. There are two curvelet transform implementations available: FDCT-USFFT and FDCT-FW. The Fast Discrete Curvelet Transform (FDCT-USFFT) relies on an unequally-spaced fast Fourier transform, while the FDCT-FW is based on frequency wrapping of explicitly chosen Fourier samples. The spatial grid that is selected to translate curvelets at each scale and angle is substantially different between the two methods. In this work, the Fast Fourier Transform is applied to the cover picture in order to improve its quality and facilitate processing, as it offers better quality and easier processing.
2.2.2 Least Significant Bit Steganography
The Least Significant Bits (LSB) substitution is a very popular steganographic method that replaces the lower-order bits of the cover picture with the secret message bits [25]. It is also known as spatial domain embedding. While these alterations remain undetectable to the human eye, they can be discovered by steganalysis tools. To enhance security, the LSB can be employed with a stego key to randomize the data insertion in the cover image. Although the LSB approach is a large capacity embedding technique, it leaves statistical evidence behind, making it subject to assaults.
Blockchain technology is characterized by its decentralized architecture, open-source nature, anonymity (or pseudonymity), and immutability. Blockchain offers immutability, time-stamping, traceability, transparency, non-repudiation, and automation [26,27]. Blockchain technology is being increasingly explored across diverse businesses and sectors, and its specific effects in banking and financial services are examined [28]. The convergence of blockchain and cryptographic technologies has established a transformative commercial paradigm with enhanced security and superior features over real currency. Fundamentally, Blockchain is a decentralized, distributed digital ledger used to record and keep up to date various types of digital transactions in today’s world.
The general architecture of Blockchain is depicted in Fig. 3. The Blockchain distributed ledger mechanism is implemented using multiple blocks connected in a chain-like structure. Transactions are represented by creating new blocks that are connected with each other. Every new block contains the previous block’s hash, and every block has a unique hash; hence, the blockchain is tamper-proof. Each transaction contains the cryptographic hash, transaction date, transaction time, and transaction data. The important aspect of blockchain is that all blocks agree on a network-verified transaction using consensus mechanisms such as Proof-of-Work (PoW), Proof-of-Authority (PoA), Proof-of-Stake (PoS), etc.
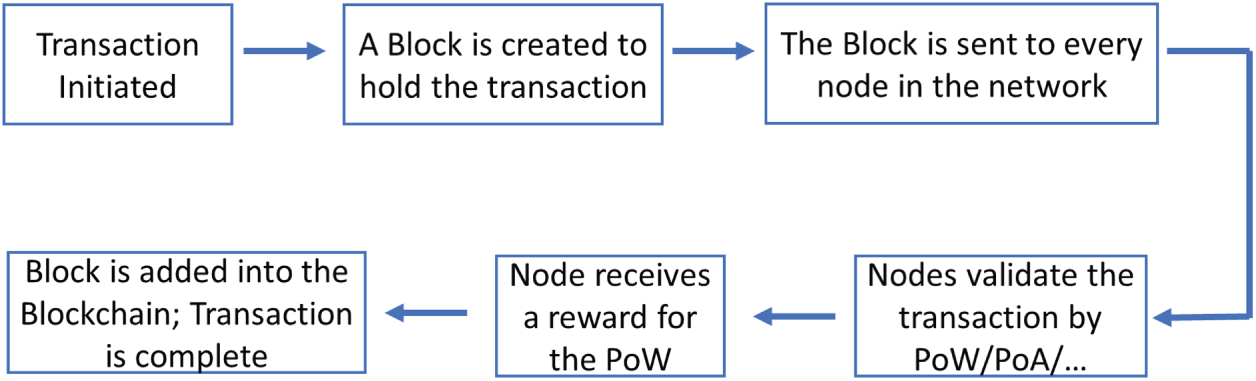
Figure 3: Blockchain architecture.
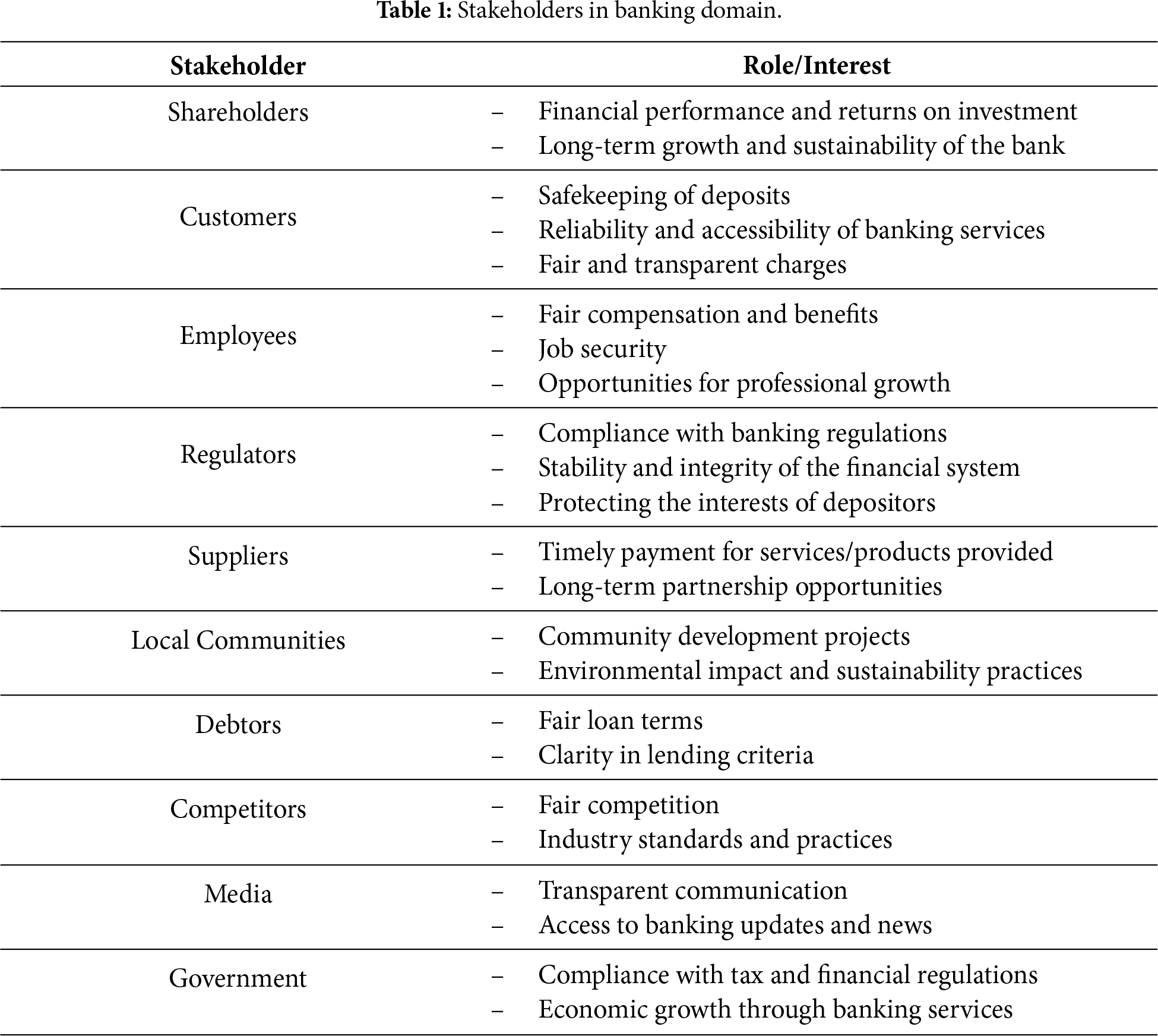
A. Stakeholders in Banking Domain
Banking involves various stakeholders each with multiple possible operations, as depicted in Table 1.
B. Technologies Useful for Self-Service Banking
Different technologies, as shown in Table 2, are required to create a superior and secure self-service banking application.
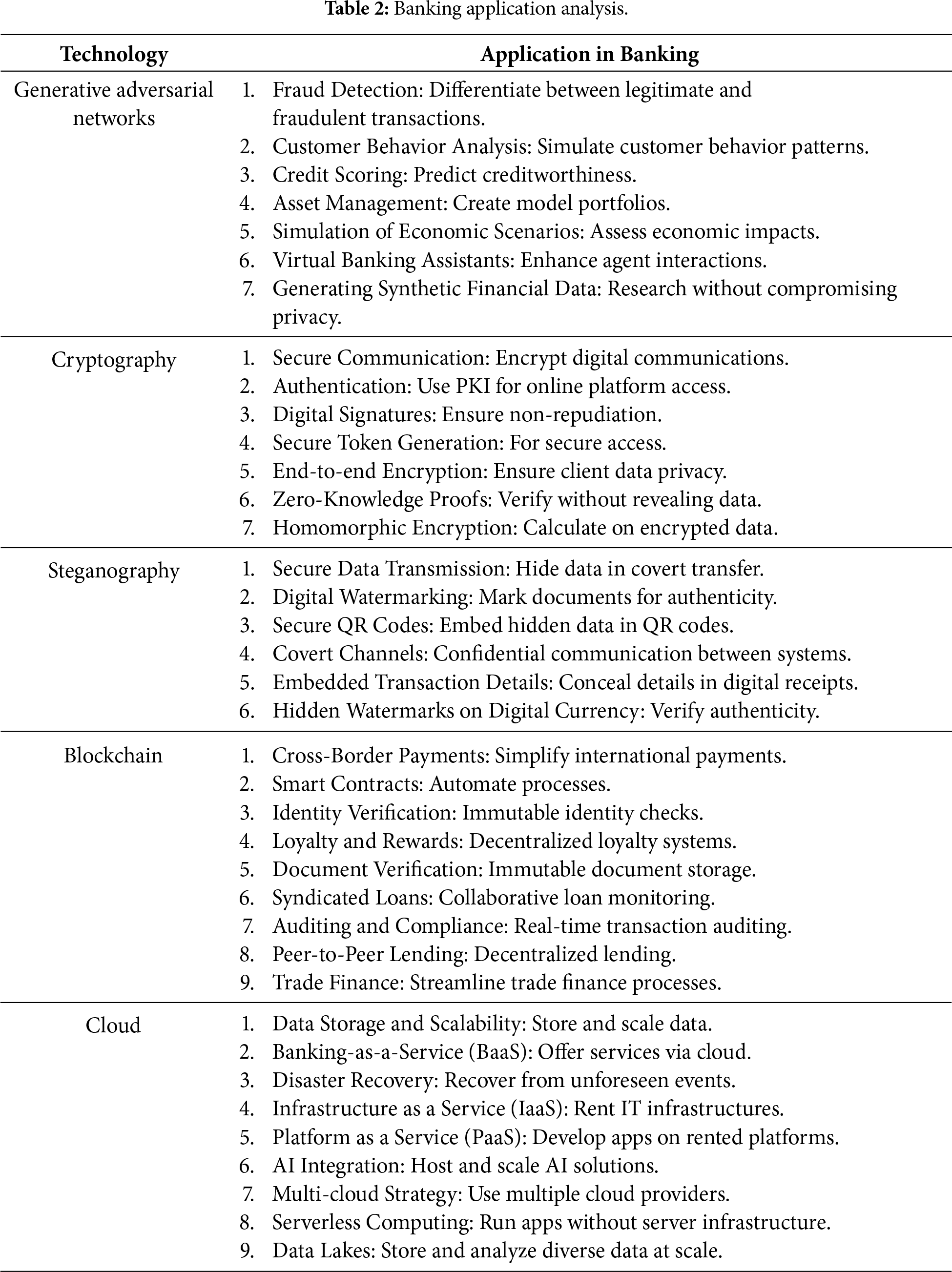
Table 3 summarizes the recent research in GAN, Steganography, Blockchain, and Self-service technologies. Ivanov and Yan [3] propose a security protocol to provide resilience against cyberattacks in self-service things. Dirgantoro et al. [11] demonstrate that IoT-based automated self-service systems use GAN face recognition in Edge for authentication and Blockchain Smart Contracts to automate operations such as opening door locks. Pandey et al. [29] and Tang et al. [30] have applied GAN to improve Banking system authentication; however, there is the need to protect the clients’ data during both transit and storage in the system. Yu et al. [31] discuss face image synthesis leveraging unpaired and paired facial images to learn a strong cross-modality synthesis model. Lee and Lee [32] propose a GAN model with backpropagation to lower the Frechet Inception Distance (FID) value, i.e., reduce the difference in distribution for real images against the distribution for generated fake images. Liu et al. [33] propose GAN training models for realistic image generation. The use of GAN to detect defects in Fabric is presented by Liu et al. in [34].
A four-step data security model in IoT-Cloud systems using encryption (RSA/AES), steganography (LSB), data backup and recovery, and data sharing (RSA/AES/IBE) is proposed by Adee and Mouratidis [10]. Luo et al. [19] add blockchain with steganography to enhance the security of data in communication channels. Modern Generative Steganography techniques to improve imperceptibility are discussed in [35–38]. Secure JPEG steganography based on a uniform embedding distortion function to improve imperceptibility against steganalysis is described in [39]. Abdel Wahab et al. [40] and Khari et al. [13] have implemented hybrid Cryptography and Steganography to provide increased confidentiality, hiding, and compressed stego-images. Jahnavi and Nandini [20] have combined Steganography, Cryptography, and Blockchain to ensure confidentiality, integrity, tamper-resistance, and non-repudiation for banking application.
Literature review indicates a need to combine multiple security mechanisms for ensuring comprehensive security in IoT-Cloud Banking applications. The impetus to create a self-service banking application with robust security is drawn from [10,11,20,29]. Blockchain helps to improve the security aspects of Cloud applications and the reliable transmission of data. Multimodal steganography offers good confidentiality and privacy of data. The security of self-service banking can be further augmented by using GAN-based authentication and Blockchain-based immutable permanent data storage in the Cloud.
This section describes the requirements of a self-service banking problem and the method to solve the same using state-of-the-art technologies.
The problem is to design a seamless and secure self-service banking system. Every customer who desires to perform any banking operation should first be properly authenticated. His/her data and transactions should be confidential and immutable. The key requirements and proposed solution for the problem is as depicted in Fig. 4.
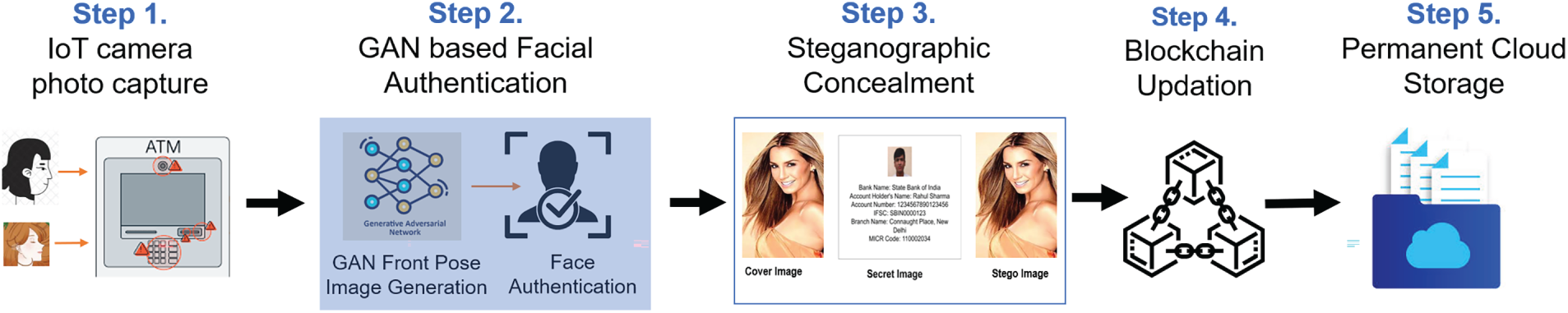
Figure 4: Stages in secure self-service banking pipeline.
Step 1: The IoT camera captures the facial image of the customer as he approaches the terminal for commencing his/her transaction. Since the customer may not pose in a perfectly straight orientation, the face angle may be tilted to the left, right or facing upwards or downwards. This IoT camera will be rendered as a standardized frontal image for biometric authentication in Step 2.
Step 2: A highly accurate frontal orientation image of the customer is generated using GAN. This image is matched with the customer KYC image and the customer gets authenticated to access his/her account.
Step 3: The customers data should be protected during transmission in network channels as well as during storage in Cloud. An improved hybrid Curvelet-LSB steganography is used to conceal the confidential data (producing a stego-image). The embedded data can be extracted on the other side to retrieve the original data.
Step 4: Blockchain is used for transactions and storage security. Customer transactions are uploaded to Blockchain, providing time-stamping, traceability, non-repudiation and immutability.
Step 5: Finally, the confidential data is stored in the Cloud permanent storage using Blockchain process.
The proposed solution offers a practicable, secure self-service Banking mechanism. For instance, when a customer comes to a Bank, he seamlessly enters the premises by automated GAN facial authentication; he can go to his smart locker inside the Bank and access it without the need for any escort staff. Similarly, a customer can carry out mobile internet banking or access the ATM with biometric facial authentication. His transactions are secure with Steganography and Blockchain.
5.3 GAN for Customer Authentication
A customized GAN for this application is described in the accompanying pseudocode. A Generator and a Discriminator are the two basic elements in this arrangement. The Generator constructs the frontal image that seems like a real image. The Discriminator, on the other hand, tries to tell the difference between the image that came from the Generator and the real image. The training procedure is iterative and spreads over several rounds (epochs). The Discriminator is trained to recognize actual data during each epoch before being trained to recognize fake data produced by the Generator. The Generator is then taught to improve the data it generates, based on the Discriminator’s input. The Generator tries to fool the Discriminator with its created data, while the Discriminator seeks to get better at detecting the Generator’s outputs. In short, GAN is a continual game between the two. The various components of the GAN system (Algorithm 1) are as follows:
(i) Random Input: It is the input to the Generative models. In this case, it is the different angled facial images of a person. Using this, the GAN can be trained to generate a wide range of synthetic data.
(ii) Generator: This creates data from random input. The output is the data that is ideally similar to the genuine data you are attempting to replicate. The generator takes the camera-captured image as input and transforms it into an output front-angled 600 × 600 pixels passport-size color image. The transformation is based on deep convolutional generative adversarial networks. The first step is a dense layer as the first hidden layer that has enough nodes to represent a low-resolution version of the output image. The next step involves upsampling the low-resolution image to a higher-resolution version of the image. The weights in the Generator model are updated based on the performance of the Discriminator model. The Generator model generates images with specific pixel values.
(iii) Discriminator: The input to the Discriminator is a standard-size image, and the output is a binary classification of whether the image is real or fake. The train discriminator() function implements this, using a batch size of 128 images, where 64 are real, and 64 are fake in each iteration.
(iv) Training the GAN: Both the Discriminator and Generator need to be trained.
• Training the Discriminator: The Generator produces fake data. The Discriminator is trained to distinguish between real and fake (generated) data.
• Training the Generator: First, produce fake data. Use the Discriminator to evaluate the fake data. However, the issue here is that the Generator is trying to trick the Discriminator. The Generator’s weights are updated to make the Discriminator more likely to classify the fake data as real.
The Generator-Discriminator model is updated in batches, specifically with a collection of real samples and a collection of generated samples. An epoch is defined as one pass through the entire training dataset. The discriminator model is updated twice per batch, once with real samples and once with fake samples, which is a best practice as opposed to combining the samples and performing a single update. The front-angle image generated by GAN should be accurate for the authentication of the customer.
For Face Authentication, a normalized size (240 × 320 pixels), frontal orientation proper image of the customer is input to the Discrete Wavelet Transform (DWT) for comparison. DWT decomposes the input face image into LL, LH, HL, and HH subbands (Lower Lows, Lower Highs, Higher Lows, and Higher Highs) to represent the horizontal, vertical, diagonal, and approximation coefficients, respectively. The steps in face recognition (Algorithm 1) are—feature extraction, classification using a GAN model, and comparison of images [44].
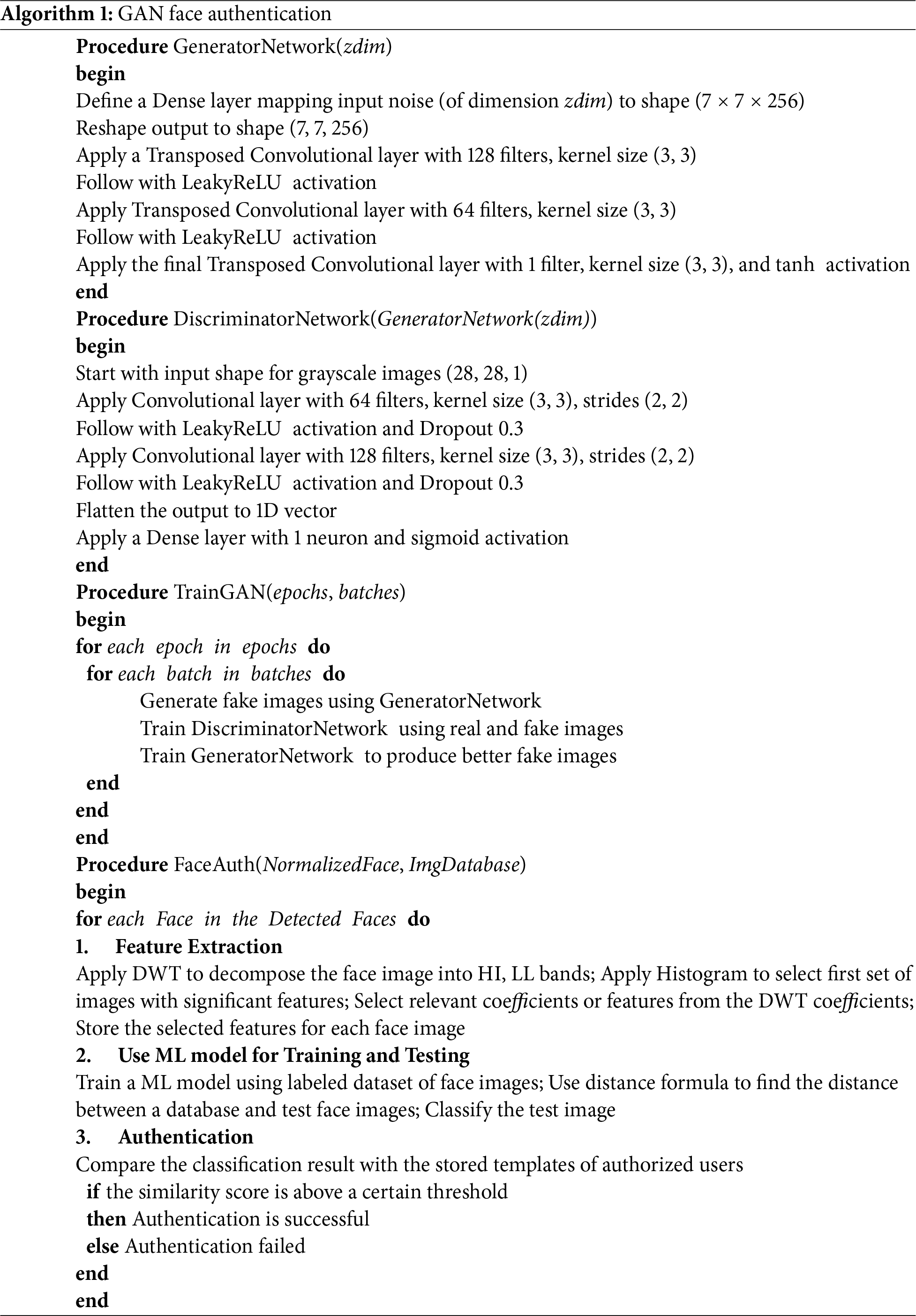
Thus, the GAN Biometric Authentication is applied in two phases: first to transform a customer’s any-angled picture into a frontal image, and second to identify the customer.
5.4 Steganographic Security Mechanism
A hybrid method combining Curvelet transform and LSB techniques is developed to hide the confidential information inside a cover image without affecting the visual quality and size of the cover image. The corresponding stego image containing the secret data can be transmitted without being found out. This method allows the intended receiver to recover secret information without much loss of data. Before applying LSB steganography, the curvelet based denoising step is applied as a preprocessing step to eliminate noise from the cover picture, which is an undesirable by-product that adds false and unnecessary information. This improves the image quality. Edge preservation is improved by the curvelet transform, which also offers superior denoising than the wavelet method. The curvelet transform is a multiscale geometric analysis technique that displays image features at every scale and in different directions. providing better curve handling and overcoming the wavelet shortage problem at higher frequencies.
This work uses the least significant bit (LSB) to conceal data inside discrete curvelet coefficients. As a preprocessing step before steganography, this method uses the curvelet denoising technique to eliminate noise from the cover image. Using the Curvelet Matlab toolbox, it applies a rapid discrete curvelet transform to the cover picture, based on the unequally spaced rapid Fourier Transform (FDCT- USFFT). The LSB method is employed to insert the secret message into the transformed coefficients, and then the inverse fast discrete curvelet transform (IFDCT-USFFT) is used to recover the message and reconstruct the image.
The proposed Steganographic method (Algorithm 2) details the process of embedding secret data into a cover image using a hybrid curvelet transform and least significant bit (LSB) technique.
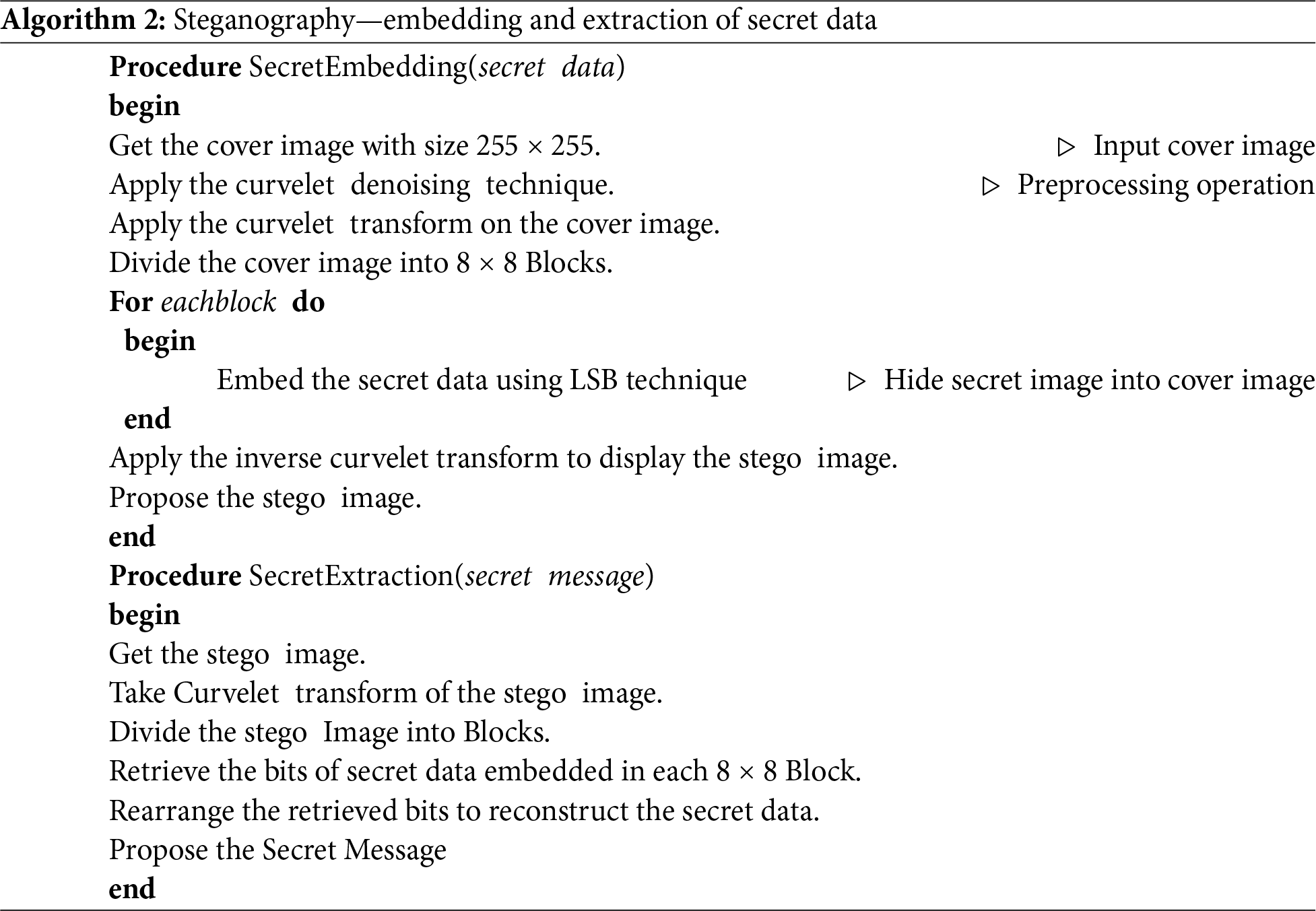
A cover image of size 255 × 255 is obtained. As a preprocessing step, the curvelet denoising is done on this cover image. It helps to remove noise and make the embedding process smoother. The curvelet transform is then applied to the denoised cover image. This transformation helps in extracting features or enhancing the properties of the image, which makes it more suitable for embedding. After transformation, the cover image is divided into multiple blocks, each of size 8 × 8. The secret image is then embedded into these blocks using the LSB technique. LSB embedding is a popular method for steganography where the least significant bits of an image’s pixels are altered to embed secret data. This embedding continues until all blocks of the cover image have been visited. Once the embedding process is complete, the inverse curvelet transform is applied to convert the transformed image back to its original spatial domain. The final result is the stego image, which is the cover image containing the embedded secret.
Procedure Extraction describes how to extract the secret data from a stego image. It begins by acquiring the stego image, which contains the embedded secret. A curvelet transform is applied to this stego image for feature extraction or to get it in a form where extraction becomes feasible. This transformed image is divided into blocks, similar to the embedding process. For each 8 × 8 block of the transformed stego image, the bits of the embedded secret data are retrieved essentially reversing the LSB embedding process. After retrieving the bits from all blocks, they are rearranged or recompiled to reconstruct the original secret. The final result is the extracted secret message. In essence, the Embedding algorithm hides secret data within a cover image using curvelet transforms and LSB embedding. The Extraction algorithm extracts the hidden secret from the stego image.
Blockchain is a promising technology that has the potential to overcome fundamental issues that have long been hampering the banking and finance sector. By reducing expenses, increasing efficiency, and adhering to legal requirements, blockchain technology enables an organization to become more secure, transparent, decentralized, and efficient. Blockchain technology, generates an unchangeable record of transactions, helps to deter theft and other types of illegal fraud. Traditional banking services have seen significant change thanks to blockchain technology advancements. Decentralisation and security are guaranteed by the blockchain ledger’s distribution throughout the bank’s network nodes. As fewer or no middlemen are involved, transactions are completed more rapidly. Processing transactions takes less time and money when blockchain is used. The immutability of blockchain adds more security against fraud. The various functionalities of Blockchain in IoT-Cloud Banking application are explained in Algorithm 3.
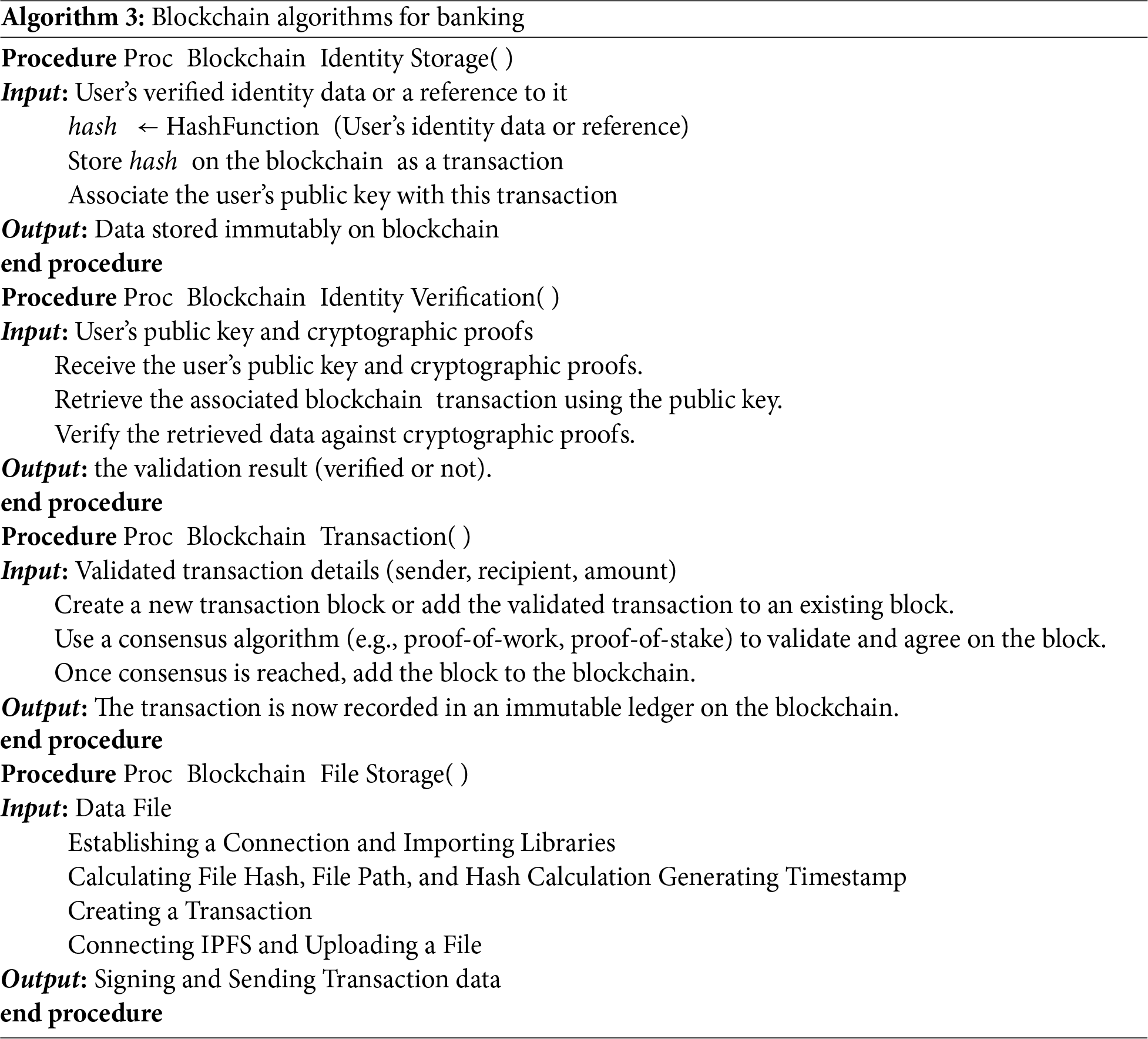
In Banking, customers’ identities should first be obtained and verified through KYC processes to prevent fraud. The verified customers can conduct their banking operations. Blockchain is used to ensure traceability, immutability, and non-repudiation of all customer transactions, and store the resulting data in the Cloud. This process is achieved by the following four steps.
5.5.1 Blockchain Identity Storage
The Blockchain Identity Storage outlines a procedure for storing a user’s confirmed identity data on a blockchain securely and transparently. To do this, the system either keeps a reference to the user’s identification information or first generates a cryptographic hash of it. Then, a transaction containing this reference or hashed data is uploaded to the blockchain. The identification data may be connected to a specific person by linking the transaction to the user’s public key. The user’s identification data becomes immutable when this transaction is uploaded to the blockchain, meaning it cannot be changed without leaving a trail. Additionally, anybody may confirm the veracity of the recorded data by looking up the related transaction on the blockchain because the blockchain is transparent. This makes sure that user identity information is safe and simple to verify.
5.5.2 Blockchain Identity Verification
The Blockchain Identity Verification procedure is a way to validate a user’s identification within a blockchain ecosystem using their public key and cryptographic evidence. It starts by obtaining the user’s public key and any associated cryptographic proofs, such as digital signatures or other forms of cryptographic documentation. The relevant blockchain transaction linked to the supplied public key is then retrieved. The user’s identification or authentication information is probably included in this transaction. The procedure next checks to see if the information obtained from the blockchain agrees with the user-provided cryptographic proofs. The system delivers a positive result indicating that the user’s identity has been properly validated if the data matches the proofs. In contrast, the verification method yields a negative result if the data and the cryptographic proofs differ, indicating that the identification could not be verified. This strategy uses the transparency and immutability of blockchain technology to create a safe and dependable method of identity verification.
The Blockchain Transaction process begins with the validation of transaction parameters, such as the sender, receiver, and amount to be sent. Upon acquiring this information, the transaction is either integrated into a newly created block or appended to an existing block. A consensus method is employed to ensure the transaction’s integrity and legitimacy. This mechanism, which may utilize proof-of-work or proof-of-stake, requires network participants to check and reach a consensus on the validity of the transaction-containing block. Once consensus is established, the block—now containing the validated transaction, is appended to the blockchain [45]. Consequently, the transaction becomes permanently and irreversibly recorded on the blockchain, guaranteeing its immutability and serving as proof of its existence.
The blockchain immutable decentralized ledger technology is useful for securing data storage [46]. The positive features of Ethereum Blockchain, such as free-usage off-chain mode, instantaneous settlement and anonymity are beneficial for storing files. Using the Web3 library and the Infura API, the file’s contents are hashed and stored with a timestamp on the Ethereum blockchain. The off-chain mode is advantageous for storing non-transactional data that are too large to be saved, deleted or modified in the on-chain blockchains. The steps for storing files in Ethereum are:
• Establishing a Connection and Importing Libraries: For the Ethereum interface, the necessary libraries are imported, including time for timestamp retrieval, hashlib for hashing, and the web3 libraries. Both the Ethereum address and the Endpoint URL are provided for the Infura API. An Ethereum network connection is established, and its status is confirmed through the use of the Infura service.
• Calculating File Hash: Using the calculate file hash function the SHA-256 hash of the data in a given file is calculated. The file is read in nominal sizes (4096 bytes), updating the hash on the fly, and the hexadecimal formatted hash values are returned. This helps to reduce the memory problems with huge files.
• File Path and Hash Calculation: The actual file path must be contained in the file path variable. The calculated file hash function is then used to compute the contents of the file. With the use of this hash, the file’s integrity is verified.
• Generating Timestamp: The Unix timestamp is created using the time.time() function. This timestamp indicates the number of seconds that have elapsed since the Unix epoch (or 01 January 1970). It provides a timestamp for the file’s blockchain entry.
• Creating a Transaction: Now, the Ethereum block is ready to hold the hash and timestamp for the file. The Ethereum transaction dictionary comprises the following important data:
• to: Address of the recipient (i.e., to whom the transaction data should be sent).
• data: The data to be include. The web3.toHex() is used to convert the string (concatenation of file hash and timestamp) into hexadecimal datatype.
• gas: The maximum gas fees that can be used for the transaction.
• gasPrice: The cost for one unit of gas, i.e., the standard unit used to determine transaction cost.
• nonce: A unique number associated with the user account that prevents repeat transaction attacks.
• Connecting IPFS: The ipfshttpclient library is used to establish a connection to the InterPlanetary File System (IPFS) network. IPFS is a decentralized and content-addressable file system useful for storing and distributing files.
• Uploading File to IPFS: The ipfs_client.add method and the calculated hash are used to upload the file into the IPFS network. The ipfs_client.add uploads the file to the IPFS network and returns a unique hash of the uploaded data. This hash is useful to retrieve the file’s content from the IPFS at any time.
• Signing and Sending Transaction: The user can only send transactions from their respective Ethereum address since the transaction is signed using their private key. The sendRawTransaction method sends the signed transaction to the Ethereum network. A transaction’s unique identifier and the corresponding transaction hash are displayed on the console.
5.6 Cloud Computing for Banking Applications
The proposed design uses a centralized cloud infrastructure taking into consideration the particular needs of the bank. Preliminary study assists in estimating costs and creating a design for the centralized structure, making sure it incorporates redundancy, data storage strategies, and strong security measures [47]. The next crucial step is choosing a reliable cloud infrastructure (or cloud service provider) that complies with legal and regulatory norms. To prevent duplication or mistakes from being sent during the transition, data purification is performed before migration to the centralized system. Importantly, rigorous access restrictions and strong security mechanisms are used throughout this process. The infrastructure is frequently checked for regulatory compliance and periodically evaluated to maintain compatibility with the bank’s developing goals and needs, especially given the sensitive nature of the business.
The secure self-service banking application is implemented by a sequence of modules including—GAN frontal face generation from any angled face photos, face identification using Discrete Wavelet Transform, customers’ personal data concealment using hybrid LSB Curvelet steganography, and secure data storage using Ethereum Blockchain technology. Performance of each of the security mechanisms is explained in this section.
The system used for the experiment is an Intel Core i5/2.7 GHz/16 GB/1 TB/4 GB NVIDIA GeForce RTX 3050 Ti PC with a 1 Gbps internet link. The program is written in Python, running on Java Eclipse Environment with PyTorch and Keras; Matlab is used for simulations and plotting.
The different metrics to validate the performance are as follows:
(i) GAN Facial Authentication: Until recently, most GAN developers fell back on the qualitative evaluation of GAN generators via manual assessment or visual inspection of the images synthesized by a generator model, as there were no objective functions defined for the Generator Model to compare the performance. However, the difference between the generated image vs. the real image gives the quantitative measure of GAN success using Frechet Inception Distance (FID) and Inception Score (IS). Precision, Recall, and Fmeasure assess the accuracy of facial recognition systems.
(ii) Steganography: The quality of the steganographic reconstructed image is measured by the difference between the original signal and the reconstructed signal, i.e., how much the noise (hidden message) has affected the fidelity of the reconstruction. The metrics for evaluating Steganography are Peak Signal-to-Noise Ratio (PSNR), Mean Square Error (MSE), Bit Error Rate (BER), and Histogram Analysis.
(iii) Blockchain: The primary factors of Blockchain are its time and cost for consensus and data storage capacity. It is measured by Upload Time, and Transaction Fees (which has a bearing on the amount of data that can be uploaded into the blocks and permanent storage).
6.3 Generative Adversarial Network
The GAN facial authentication is tested with the Indian face dataset [48], comprising 61 Indian facial images (39 male faces and 22 female faces). Typically, the larger facial datasets comprise movie celebrities, but since it is better to test with common Indian faces, the Indian face dataset is considered. There are eleven different images at different angles and expressions for each subject, with a total of 671 images. The Discriminator is trained with these images, considering this pool as real images, and 600 random images from internet sources, which are treated as fake. A sample of different angled facial images of a particular male is shown in Fig. 5a, and a sample of six different angles of the facial image of a particular female in the dataset is shown in Fig. 5b.
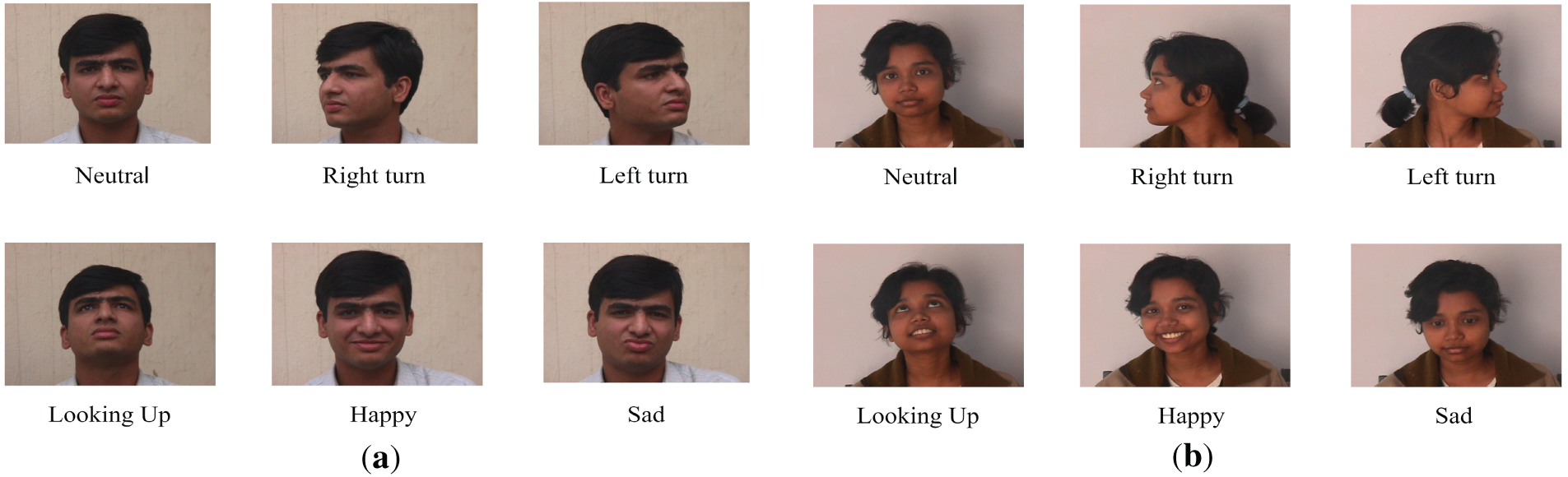
Figure 5: (a) Different angled images of an Indian male. (b) Different angled images of an Indian female.
6.3.2 GAN Face Generation—Result Analysis
The GAN should first produce an accurate front view of customers from the input IoT camera images. A clear front-angle facial image is essential for authenticating the customer using the DWT and ML face recognition algorithm.
The GAN generated front-facing image of a person as depicted in Fig. 6. The final output of the GAN front angle face generation for 30 faces from the Indian male database set is depicted in Fig. 7. The success of GAN face generation is verified by the common GAN metrics of Frechet Inception Distance (FID) and Inception Score (IS) parameters. The FID measures the similarity between the feature distributions of the real and fake data, while the IS measures the diversity and clarity of the fake data. Both metrics use a pre-trained Inception model to extract features from the data, and a lower FID and a higher IS imply a better realism in the generated images [49].
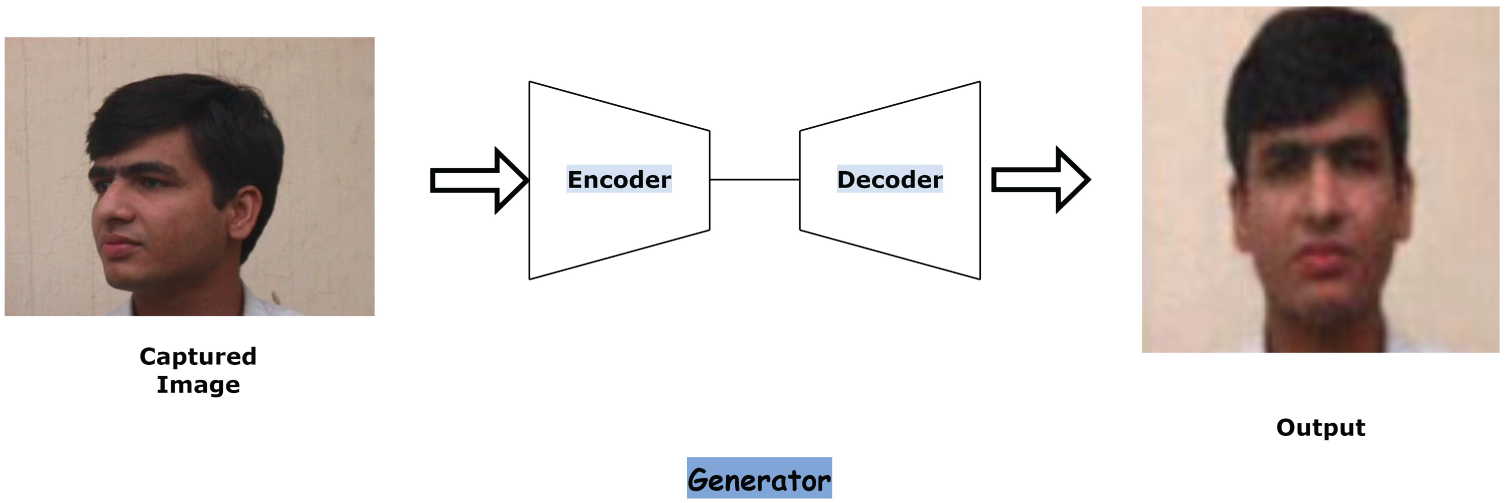
Figure 6: Generated output using GAN.
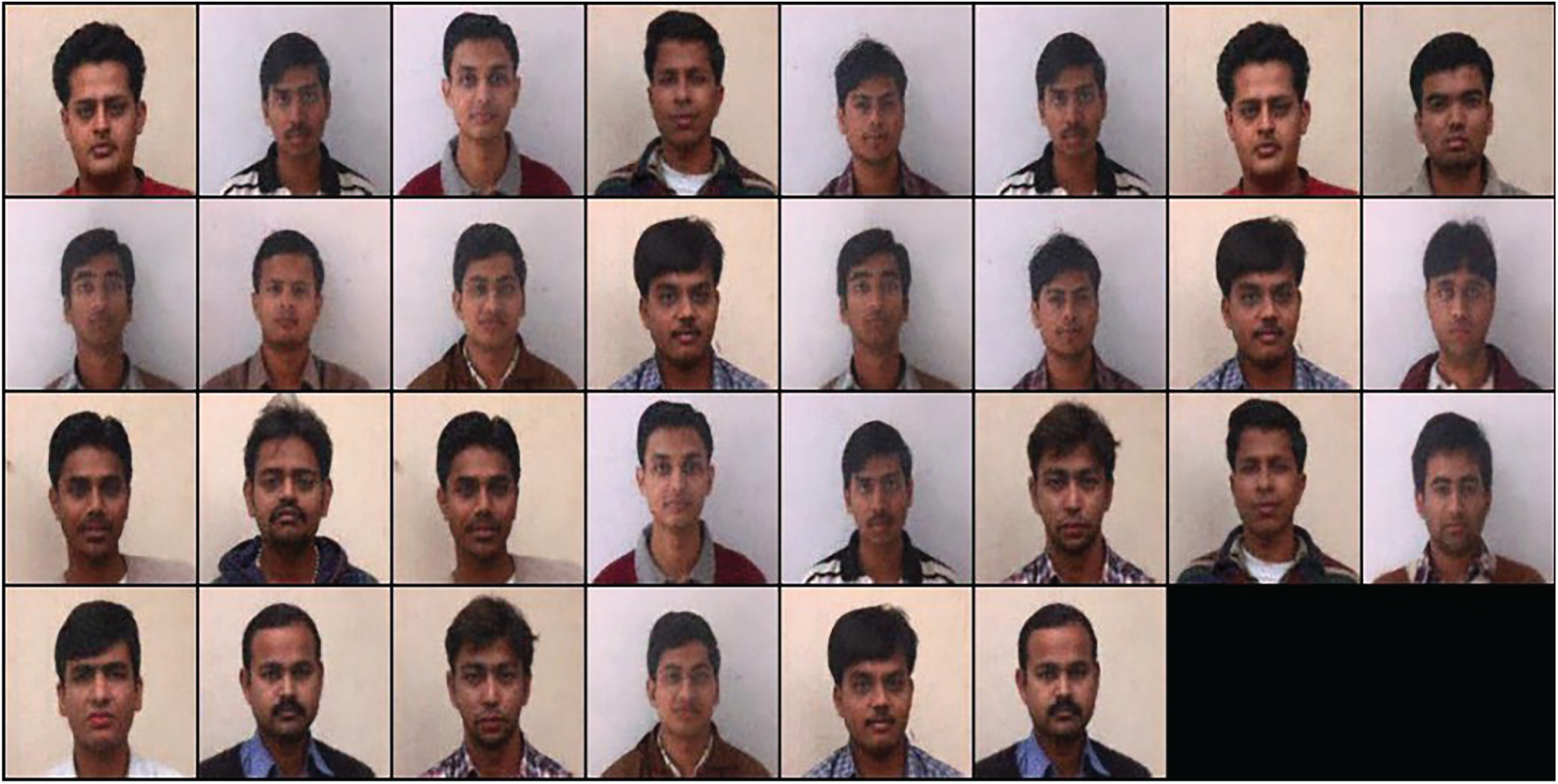
Figure 7: Generator output for entire datasets.
Executing the program establishes the model, loads the customer training dataset, and then trains the Discriminator Model. The Discriminator model quickly learns to tell the difference between real and randomly generated images. As the number of epochs increases, the visual quality of the frontal image increases, but the processing time also increases. Since it is required to provide the facial authentication in a reasonable time, it was found that 20 epochs provided a reasonable accuracy within a short response time.
FID and IS:
The Frechet distance quantifies the similarity of two curves. The steps involved in FID include: (i) Preprocessing the images to make them compatible for comparison, (ii) Calculating statistics to determine the mean and covariance matrix of the features, (iii) Computing the Frechet distance for mean and covariance matrices, and (iv) Obtaining the FID between the real and generated images. Lower FID numbers indicate the images are more similar.
Inception Score (IS) is a mathematical metric to evaluate the quality of images generated by GAN. It indicated two aspects—(i) the quality (or clarity) of the generated images and (ii) the diversity of the generated images distribution. A higher IS implies better quality and higher diversity in the generated samples.
The FID values for different numbers of epochs trained for the GAN experiment are depicted in Fig. 8. Fig. 9 shows the plot of the corresponding Inception Score. As the GAN gets trained over a larger number of epochs, the curve evolves from underfitting to overfitting, passing through the ideal fit. When the number of epochs increases, the FID value (i.e., the difference between the real and generated images) decreases. Initially, when the GAN is trained for 20–50 epochs, the images are slightly distorted, and the FID value is quite high. As the training progresses, the quality of GAN-generated images improves, indicated by lower FID values. The Frechet Inception Distance is 15.2 and reduces to 4.8 when the GAN is run till 500 epochs. The Inception Score is the inverse of FID. When the GAN is initially trained for 20 epochs, the IS is around 4, and it reaches 9.5 after 500 epochs. The graphs of FID and IS show that running around 200 epochs made the GAN to be optimally trained for this dataset and gives a good precision of over 90%.
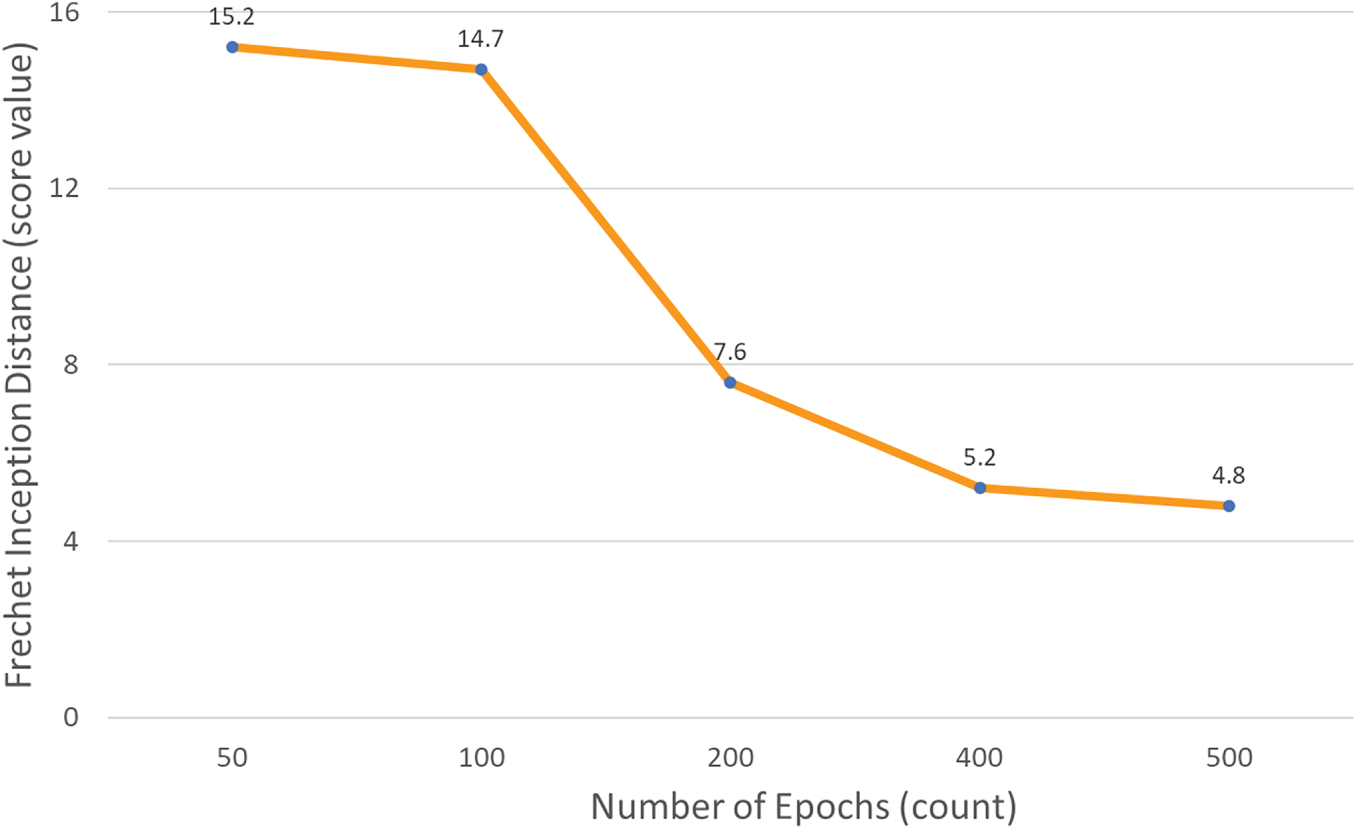
Figure 8: Frechet inception distance for GAN face generation.
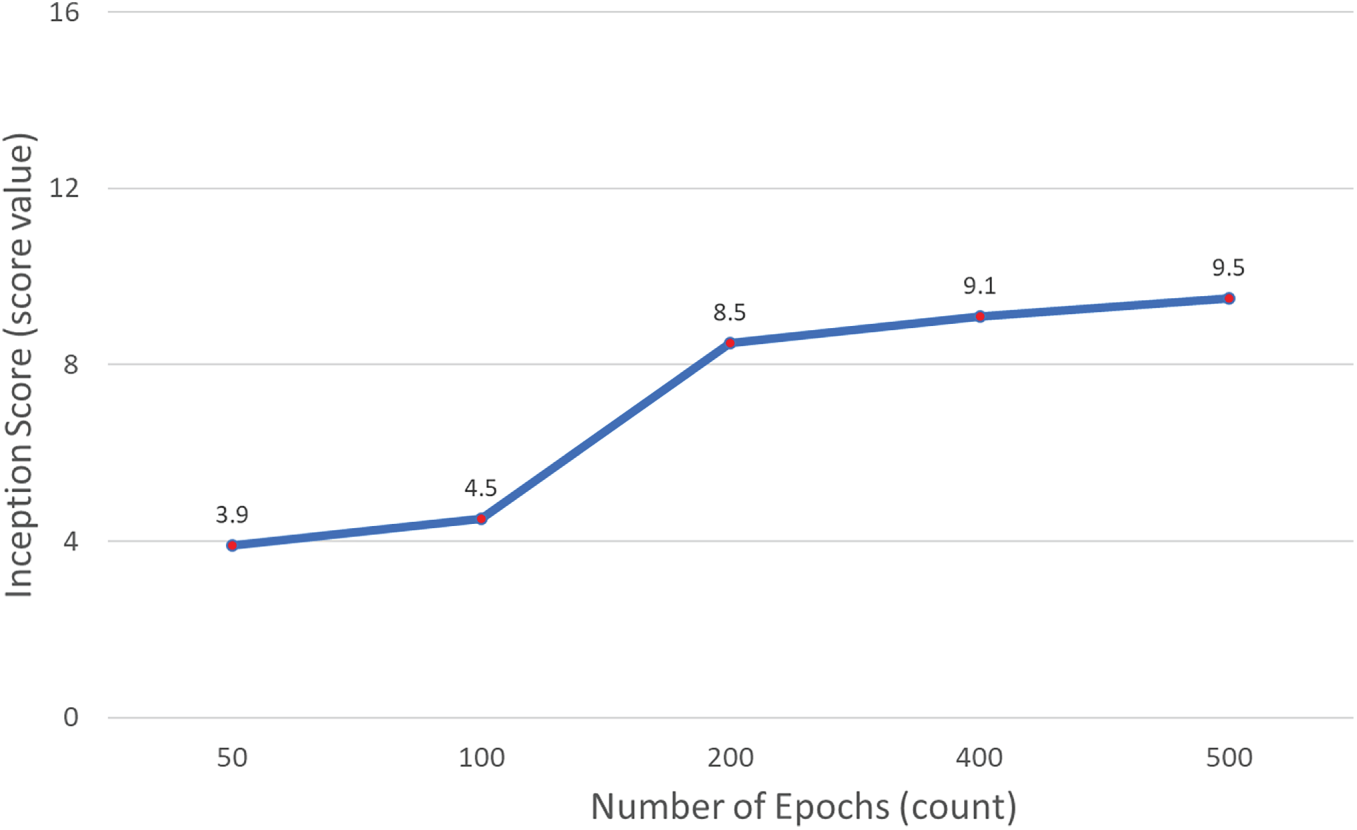
Figure 9: Inception score for GAN face generation.
6.3.3 GAN Facial Authentication—Result Analysis
The GAN is trained with both real and fake images to make the training complete. To test the GAN facial authentication, false images are also included in the test cases to make sure that fake images are detected and rejected by the system during the facial authentication. The module successfully rejected such negative samples, showing that GAN-based facial authentication is robust. TP (True Positive) is the number of frontal images that are correctly classified under the positive class. FP (False Positive) is the number of wrong images classified under the positive class. FN (false Negatives) are undetected images classified as false negatives.
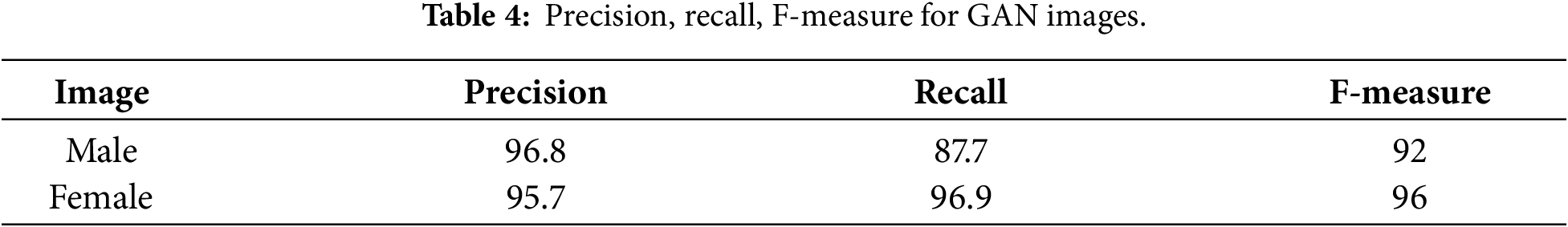
Precision, Recall, F-Measure:
The metrics of Precision, Recall, and F-measure are used to measure the accuracy of GAN facial authentication, and their formulae are as follows:
Sample images are tested for Precision, Recall, and F-measure, and the results are tabulated in Table 4. The values of over 95% for the Precision, Recall, and F-Measure imply that the image identification is very successful.
It is difficult to detect the difference between a stego-image and a cover-image by visual inspection. Hence, the PSNR, MSE, and Histogram metrics are employed to evaluate the success of the steganographic technique. For testing and analysis of the hybrid steganography, a file containing basic information such as the customer’s image, name, account number, and transaction details, which is about 67 KB in size, is taken as a constant secret message (confidential data), in this experiment.
PSNR (Peak Signal-to-Noise Ratio) compares the image quality to that of a reference image. It is calculated by measuring the difference in pixel intensity between two images and determining their maximum value. The higher the PSNR value, the better the match between the two images, which means they are of higher quality. In steganography, PSNR calculates the invisibility of the image, that is, to assess the extent of image degradation caused by embedding the secret within the cover image. It is mathematically expressed as:
where MAX2 is the maximum pixel value of the image (for a grayscale image, it is 255). MSE stands for Mean Squared Error between the original and stego-image. It gives the average value of the pixel-by-pixel difference between the original image and stego-image. MSE is inversely proportional to PSNR.
A histogram is a bar graph where the x-axis represents the range of possible pixel values (e.g., 0 to 255 for grayscale images) and the y-axis represents the frequency count of pixels for each intensity. If there is a significant difference between the histogram of the original image vs. the stego-image, it indicates the presence of hidden content in the stego-image.
The robustness of steganography is measured by Bit Error Rate (BER), i.e., (number of incorrect recovered bits)/(total payload bits). When the receiver extracts the hidden message from the stego file, some of the bits may be incorrect compared to the original secret message. Hence, it is desirable to have a lower BER. The errors may be introduced by the steganographic algorithm when it embeds the secret data into the cover image or get introduced due to noisy communication channels.
Steganography Result Analysis
The confidential message is embedded into different types of cover images, and the imperceptibility is evaluated. Standard publicly available grayscale and color images are chosen as cover images. A constant-size secret message mentioned above is concealed in all the cover images used in this experiment. Table 5 shows the PSNR, MSE, and BER for stego images from 6 different standard cover images (3 grayscale and 3 colored) after embedding the said customer’s secret data. The histogram graphs of different cover images and the corresponding stego images after embedding an unchanging secret message is shown in Fig. 10.
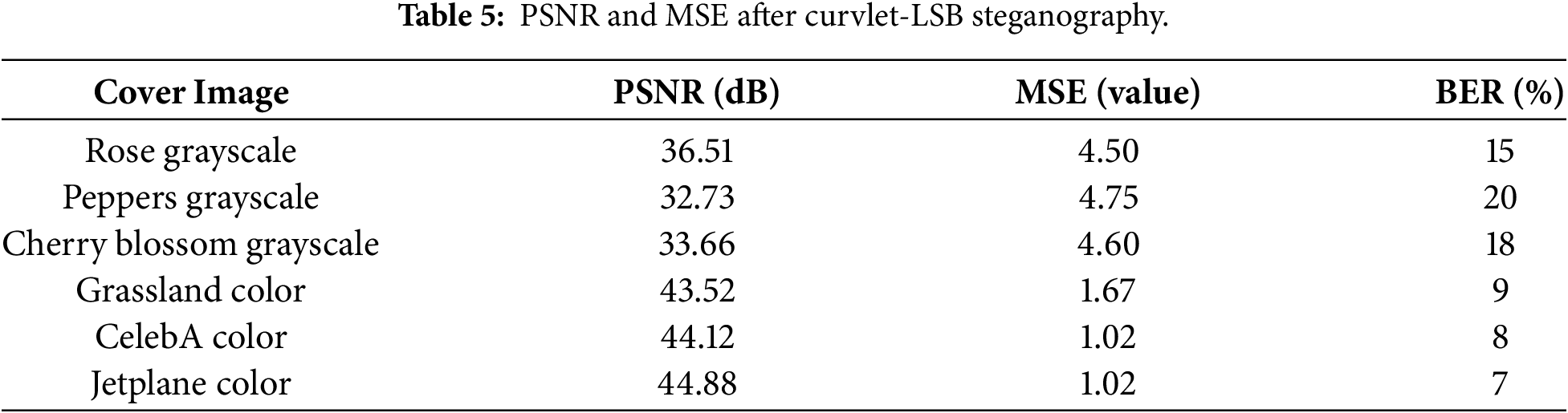
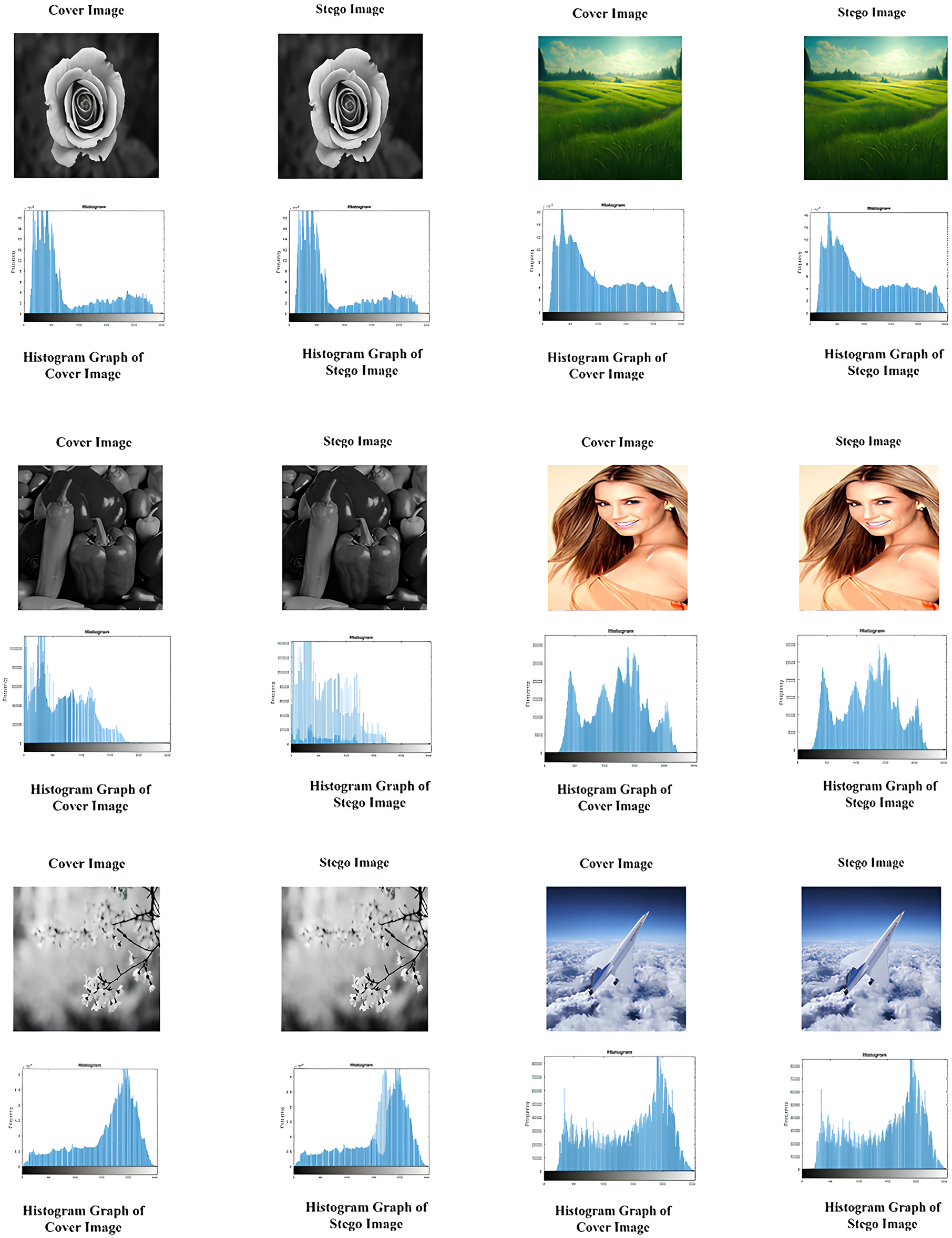
Figure 10: Histogram analysis for hybrid LSB-curvelet steganography.
A higher the PSNR value, indicates better the match between the two images, and they are of higher quality. And a lower value of MSE implies that the error is less. Typically, the PSNR for color images is higher than the PSNR for grayscale as the depth of hiding is 24 for color pixels. The PSNR value depends on the size of the secret data being concealed. In this experiment, the secret message is kept constant, and hence the PSNR compares the concealment capacities of different cover images for the hybrid Curvelet-LSB steganography algorithm. It is observed that the PSNR values for many stego images are above 40 dB, which indicates that the steganographic algorithm is very effective in hiding the secret data. In this experiment, the average PSNR is 39.57 dB, and the Standard Deviation is 5.58 dB. Hence, the color images (like Jetplane) handle embedding very well with minimal distortion, while others (like Peppers or Cherry Blossom) degrade more noticeably.
The histogram analysis compares the overall shape, intensities of peaks and troughs, distortions, and shifts in the graphical plots for the original against the stego image. The different grayscale intensities or color values are depicted on the horizontal x-axis, and the frequencies of occurrence of the colors are represented on the vertical y-axis. The input host images can be Grayscale images (8-bit image per pixel) or RGB color images (24-bit image per pixel), which impact the hiding capacity of the cover.
A comparison of cover vs. stego histographs for grayscale images for a secret message of 67 KB is performed. The distortion is very high in the histograms of Peppers’ grayscale for the given small secret message. The distortion of histograms for Cherry Blossom grayscale and Rose grayscale is slightly less than Peppers grayscale (Fig. 10). Among the three grayscale cover images, the histogram analysis shows the least difference for the Rose grayscale. From this histogram analysis, it is observed that opaque, dark images have more similar cover-stego histograms. Hence, using dark and opaque images provides better security.
Similarly, histogram analysis of cover vs. stego histographs for color images for a secret message (67 KB) are performed. The cover vs. stego histograms pairs for each of the color images are similar. The frequency values at all pixels are very similar, implying that the imperceptibility is very good for all color cover images. The hiding capacity of color images is high. The grayscale images show more differences between the histograms of cover and steganographic images, whereas the color images have fewer differences in the histograms of corresponding cover and stego images. This is due to the higher hiding capacity of the color images. Overall, it is observed that the size of the secret to be concealed, the steganographic algorithm, and the hiding capacity of the cover image determine the quality of steganographic imperceptibility.
The robustness of hybrid Curvelet-LSB Steganography can be analyzed from the Bit Error Rate (BER). The grayscale images show higher BER (15%–20%) while the color images show lower BER (7%–9%).
The server authorizes the transaction to proceed after successful authentication. Every transaction, including money transfers, is noted on a blockchain database. An aggregation of banking data is periodically uploaded to the Cloud using Blockchain security. The important aspects to be considered while choosing a Blockchain for an application are—public or private mode of operation, consensus mechanism used, upload time, upload data size and transaction fees.
Blockchain Result Analysis
(i) Upload Time: In the context of Blockchain, the upload time is the total time taken to send the file from a device to the server. It is dependent on the data size, network bandwidth/speed and blocktime (time required to store the data inside each block on the blockchain). In other words, upload time is dependent on the type of consensus algorithm that needs to be executed before a block gets committed. The Ethereum Blockchain platform is used in this experiment, as it supports fees-free off-chain mode, in addition to the public on-chain mode. Fig. 11 shows the upload time in Ethereum for different sizes of data. For on-chain mode a gas price of 44 Gwei was incurred. The upload time is less than 3 mins for 100 KB data while it is slightly more than 3 min for 800 KB data. Besides, the off-chain mode (leveraging IPFS) is around 7% faster than the on-chain mode. Typically, a secure color stego image with embedded secret customer information is about 700 KB, while the grayscale stego image is around 300 KB. An upload time of about 3 mins for 800 KB data size is a nominal time to safely store the stego-image by Ethereum blockchain in the cloud.
(ii) No Transaction Fees: Public blockchains charge a fee for executing transactions in their networks, viz. Bitcoin cryptocurrency (BTC) and Ether (ETH) Transaction Fee units for Bitcoin and Ethereum, respectively. The fees are levied as per the Bitcoin/Ethereum tariff slabs. Ethereum offers On-chain mode with nominal fees and Off-chain mode with no cost. Since Bitcoin charges are quite costly to be employed for the experimental stage, the free Ethereum Off-chain mode is used in this experiment. Therefore, it does not invoke transaction fees.
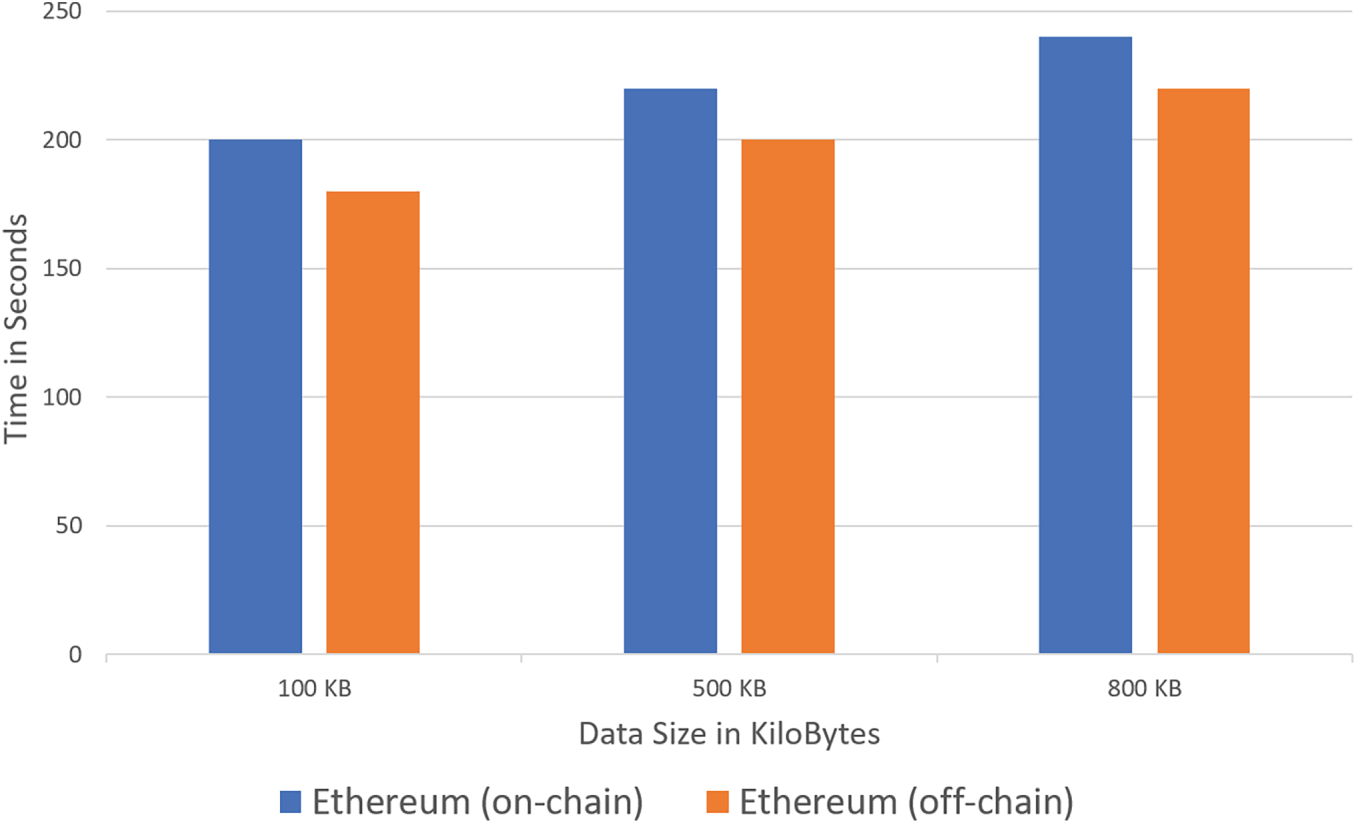
Figure 11: Upload time in ethereum blockchain.
This research designed and demonstrated a three-stage GAN-Steganography-Blockchain framework to deliver secure self-service banking services in IoT-Cloud systems. The GAN component generates a normalized frontal pose customer image used to authenticate the customer. The GAN produced accurate results for frontal images in the given dataset. A hybrid Curvelet-LSB image steganographic technique ensures the protection of customers’ confidential information during both transmission and storage phases. The imperceptibility of the hybrid Curvelet-LSB steganographic concealment is demonstrated by the statistical similarity between the cover-image histograms and the stego-image histograms, achieving a robust Peak Signal-to-Noise Ratio (PSNR) of approximately 40 dB for color images. Ethereum Blockchain is used for secure transactions and immutable data storage in the Cloud. Empirical observations indicate that Ethereum off-chain implementation is optimal for this application, with an upload time of less than 3 min for approximately 800 KB of data, accommodating large data volumes, and eliminating transaction fees. Hence, the proposed system delivers both operational convenience and comprehensive security for customer data and operations throughout the entire banking lifecycle by ensuring authentication, confidentiality, integrity, and non-repudiation. Security is constantly evolving, and new threat models such as GAN spoofing, GAN inversion attacks, stego-image tampering, and blockchain key compromise shall be vetted in the future. Presently, this system is tested with a limited Indian dataset; future work will focus on generalizing it to other ethnicities, testing for real-life conditions, and conducting detailed testing of GAN facial authentication without frontalization, varied epoch sizes, and different feature recognition algorithms. Utilizing GAN Steganography for improving the indiscernibility of data embedding is also planned as future work.
Acknowledgement: None.
Funding Statement: The authors received no specific funding for this study.
Author Contributions: Mangala Natampalli: Writing—original draft, review & editing, project administration, methodology, investigation, conceptualization. Kruthika Gottikere Channagangaiah: Software, resources. Bodi Eswara Reddy: Conceptualization, supervision. Rajkumar Buyya: Supervision, review. Venugopal Kupanna Rajuk: Conceptualization, supervision, writing—review & editing. Sundaraja Sitharama Iyengar: Supervision. Lalit Mohan Patnaik: Supervision. All authors reviewed and approved the final version of the manuscript.
Availability of Data and Materials: Data available on request from the authors.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest.
References
1. Manimuthu A, Dharshini V, Zografopoulos I, Priyan MK, Konstantinou C. Contactless technologies for smart cities: big data, IoT, and cloud infrastructures. SN Comput Sci. 2021;2(4):334. doi:10.1007/s42979-021-00719-0. [Google Scholar] [PubMed] [CrossRef]
2. Li F, Lu H, Hou M, Cui K, Darbandi M. Customer satisfaction with bank services: the role of cloud services, security, e-learning and service quality. Technol Soc. 2021;64(5):101487. doi:10.1016/j.techsoc.2020.101487. [Google Scholar] [CrossRef]
3. Ivanov N, Yan Q. AutoThing: a secure transaction framework for self-service things. IEEE Trans Serv Comput. 2023;16(2):983–95. doi:10.1109/tsc.2022.3185114. [Google Scholar] [CrossRef]
4. Venugopal KR, Ezhil Rajan E, Sreenivasa Kumar P. Impact of wavelength converters in wavelength routed all-optical networks. Comput Commun. 1999;22(3):244–57. doi:10.1016/s0140-3664(98)00244-8. [Google Scholar] [CrossRef]
5. Venugopal KR, Mangala N, Reddy BE. An integrated computing storage system and method of security related thereto. Indian Patent Application No. 202341088532. 2024. [Google Scholar]
6. Mangala N, Reddy BE, Venugopal KR. Enhanced response and security of iot cloud smart applications. J Technol. 2024;12(3):410–22. [Google Scholar]
7. Kadar T. Global banking fraud index 2023. London, UK: SEON Technologies Ltd.; 2023. [Google Scholar]
8. Wang S, Asif M, Shahzad MF, Ashfaq M. Data privacy and cybersecurity challenges in the digital transformation of the banking sector. Comput Secur. 2024;147(6):104051. doi:10.1016/j.cose.2024.104051. [Google Scholar] [CrossRef]
9. Ntalianis K, Tsapatsoulis N. Remote authentication via biometrics: a robust video-object steganographic mechanism over wireless networks. IEEE Trans Emerg Topics Comput. 2016;4(1):156–74. doi:10.1109/tetc.2015.2400135. [Google Scholar] [CrossRef]
10. Adee R, Mouratidis H. A dynamic four-step data security model for data in cloud computing based on cryptography and steganography. Sensors. 2022;22(3):1109. doi:10.3390/s22031109. [Google Scholar] [PubMed] [CrossRef]
11. Dirgantoro KP, Lee JM, Kim DS. Generative adversarial networks based on edge computing with blockchain architecture for security system. In: Proceedings of the 2020 International Conference on Artificial Intelligence in Information and Communication (ICAIIC); 2020 Feb 19–21; Fukuoka, Japan. p. 39–42. doi:10.1109/icaiic48513.2020.9065231. [Google Scholar] [CrossRef]
12. AL-Shaaby AA, AlKharobi T. Cryptography and steganography: new approach. Trans Netw Commun. 2017;5(6):25–38. doi:10.14738/tnc.56.3914. [Google Scholar] [CrossRef]
13. Khari M, Garg AK, Gandomi AH, Gupta R, Patan R, Balusamy B. Securing data in Internet of Things (IoT) using cryptography and steganography techniques. IEEE Trans Syst Man Cybern, Syst. 2020;50(1):73–80. doi:10.1109/tsmc.2019.2903785. [Google Scholar] [CrossRef]
14. Wang Z, Feng G, Qian Z, Zhang X. JPEG steganography with content similarity evaluation. IEEE Trans Cybern. 2023;53(8):5082–93. doi:10.1109/tcyb.2022.3155732. [Google Scholar] [PubMed] [CrossRef]
15. Gurunath R, Alahmadi AH, Samanta D, Khan MZ, Alahmadi A. A novel approach for linguistic steganography evaluation based on artificial neural networks. IEEE Access. 2021;9:120869–79. doi:10.1109/access.2021.3108183. [Google Scholar] [CrossRef]
16. Aftabi SZ, Ahmadi A, Farzi S. Fraud detection in financial statements using data mining and GAN models. Expert Syst Appl. 2023;227(2019):120144. doi:10.1016/j.eswa.2023.120144. [Google Scholar] [CrossRef]
17. Castelblanco A, Rivera E, Solano J, Tengana L, López C, Ochoa M. Dynamic face authentication systems: deep learning verification for camera close-up and head rotation paradigms. Comput Secur. 2022;115(8):102629. doi:10.1016/j.cose.2022.102629. [Google Scholar] [CrossRef]
18. Awotunde JB, Ogundokun RO, Misra S, Adeniyi EA, Sharma MM. Blockchain-based framework for secure transaction in mobile banking platform. In: Hybrid intelligent systems. Cham, Switzerland: Springer International Publishing; 2021. p. 525–34. doi:10.1007/978-3-030-73050-5_53. [Google Scholar] [CrossRef]
19. Luo X, Zhang P, Zhang M, Li H, Cheng Q. A novel covert communication method based on Bitcoin transaction. IEEE Trans Ind Inf. 2022;18(4):2830–9. doi:10.1109/tii.2021.3100480. [Google Scholar] [CrossRef]
20. Jahnavi S, Nandini C. Multifold secured bank application authentication service using random visual cryptography and multimodal steganography with blockchain technology. In: Proceedings of 3rd International Conference on Recent Trends in Machine Learning, IoT, Smart Cities and Applications; 2022 Mar 28–29; Hyderabad, India. Singapore: Springer Nature; 2023. p. 119–35. doi:10.1007/978-981-19-6088-8_12. [Google Scholar] [CrossRef]
21. Saxena N, Varshney D. Smart home security solutions using facial authentication and speaker recognition through artificial neural networks. Int J Cogn Comput Eng. 2021;2(12):154–64. doi:10.1016/j.ijcce.2021.10.001. [Google Scholar] [CrossRef]
22. Xu Y, Xu X, Jiao J, Li K, Xu C, He S. Multi-view face synthesis via progressive face flow. IEEE Trans Image Process. 2021;30:6024–35. doi:10.1109/tip.2021.3090658. [Google Scholar] [PubMed] [CrossRef]
23. Wang Z, Feng G, Shen L, Zhang X. Cover selection for steganography using image similarity. IEEE Trans Dependable Secure Comput. 2022;6505:1–13. doi:10.1109/tdsc.2022.3181039. [Google Scholar] [CrossRef]
24. Candes DDE, Demanet L, Ying L. Fast discrete curvelet transforms. Scalable Comput: Pract Exp. 2006;5(3):861–99. doi:10.1137/05064182X. [Google Scholar] [CrossRef]
25. Yang CH, Weng CY, Wang SJ, Sun HM. Adaptive data hiding in edge areas of images with spatial LSB domain systems. IEEE Trans Inform Forensic Secur. 2008;3(3):488–97. doi:10.1109/tifs.2008.926097. [Google Scholar] [CrossRef]
26. Chen F, Wang J, Li J, Xu Y, Zhang C, Xiang T. TrustBuilder: a non-repudiation scheme for IoT cloud applications. Comput Secur. 2022;116(4):102664. doi:10.1016/j.cose.2022.102664. [Google Scholar] [CrossRef]
27. Mangala N, Naveen DR, Reddy BE, Buyya R, Venugopal KR, Iyengar SS, et al. Secure pharmaceutical supply chain using blockchain in IoT cloud systems. Internet Things. 2024;26(19):101215. doi:10.1016/j.iot.2024.101215. [Google Scholar] [CrossRef]
28. Dashkevich N, Counsell S, Destefanis G. Blockchain application for central banks: a systematic mapping study. IEEE Access. 2020;8:139918–52. doi:10.1109/access.2020.3012295. [Google Scholar] [CrossRef]
29. Pandey A, Bhatt DL, Bhowmik T. Limitations and applicability of gans in banking domain. Santiago de Compostela, Spain: aDGN@ECAI; 2020. p. 1–6. [Google Scholar]
30. Tang ZR, Chen QQ, Sun ZH, Xiong P, Zhang BH, Jiang L, et al. Few-sample generation of amount in figures for financial multi-bill scene based on GAN. IEEE Trans Comput Soc Syst. 2023;10(3):1326–34. doi:10.1109/tcss.2021.3136602. [Google Scholar] [CrossRef]
31. Yu S, Han H, Shan S, Chen X. CMOS-GAN: semi-supervised generative adversarial model for cross-modality face image synthesis. IEEE Trans Image Process. 2023;32:144–58. doi:10.1109/tip.2022.3226413. [Google Scholar] [PubMed] [CrossRef]
32. Lee J, Lee M. FIDGAN: a generative adversarial network with an inception distance. In: Proceedings of the 2023 International Conference on Artificial Intelligence in Information and Communication (ICAIIC); 2023 Feb 20–23; Bali, Indonesia. p. 397–400. doi:10.1109/icaiic57133.2023.10066964. [Google Scholar] [CrossRef]
33. Liu M, Deng J, Yang M, Cheng X, Xie T, Deng P, et al. Express construction for GANs from latent representation to data distribution. Appl Sci. 2022;12(8):3910. doi:10.3390/app12083910. [Google Scholar] [CrossRef]
34. Liu J, Wang C, Su H, Du B, Tao D. Multistage GAN for fabric defect detection. IEEE Trans Image Process. 2020;29:3388–400. doi:10.1109/tip.2019.2959741. [Google Scholar] [PubMed] [CrossRef]
35. Cao Y, Zhou Z, Chakraborty C, Wang M, Wu QMJ, Sun X, et al. Generative steganography based on long readable text generation. IEEE Trans Comput Soc Syst. 2024;11(4):1–11. doi:10.1109/TCSS.2022.3174013. [Google Scholar] [CrossRef]
36. Tan J, Liao X, Liu J, Cao Y, Jiang H. Channel attention image steganography with generative adversarial networks. IEEE Trans Netw Sci Eng. 2022;9(2):888–903. doi:10.1109/tnse.2021.3139671. [Google Scholar] [CrossRef]
37. Zhou Z, Su Y, Li J, Yu K, Wu QMJ, Fu Z, et al. Secret-to-image reversible transformation for generative steganography. IEEE Trans Dependable Secure Comput. 2023;20(5):4118–34. doi:10.1109/tdsc.2022.3217661. [Google Scholar] [CrossRef]
38. Peng F, Chen G, Long M. A robust coverless steganography based on generative adversarial networks and gradient descent approximation. IEEE Trans Circuits Syst Video Technol. 2022;32(9):5817–29. doi:10.1109/tcsvt.2022.3161419. [Google Scholar] [CrossRef]
39. Guo L, Ni J, Shi YQ. Uniform embedding for efficient JPEG steganography. IEEE Trans Inform Forensic Secur. 2014;9(5):814–25. doi:10.1109/tifs.2014.2312817. [Google Scholar] [CrossRef]
40. Abdel Wahab OF, Khalaf AAM, Hussein AI, Hamed HFA. Hiding data using efficient combination of RSA cryptography, and compression steganography techniques. IEEE Access. 2021;9:31805–15. doi:10.1109/access.2021.3060317. [Google Scholar] [CrossRef]
41. Takaoğlu M, Özyavaş A, Ajlouni N, Alshahrani A, Alkasasbeh B. A novel and robust hybrid blockchain and steganography scheme. Appl Sci. 2021;11(22):10698. doi:10.3390/app112210698. [Google Scholar] [CrossRef]
42. Tahiri MA, Karmouni I, Mchichou I, Bencherqui A, El Maloufy A, Karmouni H, et al. Enhanced security framework for medical data embedding based on octonionic steganographic transforms and FPGA-accelerated integrity verification. Alex Eng J. 2025;125(12):480–95. doi:10.1016/j.aej.2025.04.029. [Google Scholar] [CrossRef]
43. El Maloufy A, Tahiri MA, Bencherqui A, Karmouni H, Sayyouri M. Secure and invisible dual watermarking for digital content based on optimized octonion moments and chaotic metaheuristics. Comput Mater Contin. 2025;85(3):5789–822. doi:10.32604/cmc.2025.068885. [Google Scholar] [CrossRef]
44. Yin X, Liu X. Multi-task convolutional neural network for pose-invariant face recognition. IEEE Trans Image Process. 2018;27(2):964–75. doi:10.1109/tip.2017.2765830. [Google Scholar] [PubMed] [CrossRef]
45. Li R, Song T, Mei B, Li H, Cheng X, Sun L. Blockchain for large-scale Internet of Things data storage and protection. IEEE Trans Serv Comput. 2019;12(5):762–71. doi:10.1109/tsc.2018.2853167. [Google Scholar] [CrossRef]
46. Liang W, Fan Y, Li KC, Zhang D, Gaudiot JL. Secure data storage and recovery in industrial blockchain network environments. IEEE Trans Ind Inf. 2020;16(10):6543–52. doi:10.1109/tii.2020.2966069. [Google Scholar] [CrossRef]
47. Tao F, Cheng Y, Xu LD, Zhang L, Li BH. CCIoT-CMfg: cloud computing and Internet of Things-based cloud manufacturing service system. IEEE Trans Ind Inf. 2014;10(2):1435–42. doi:10.1109/tii.2014.2306383. [Google Scholar] [CrossRef]
48. Indian face database, Kanpur, India: Department of CSE, IIT Kanpur; 2002. [Google Scholar]
49. Aliyev E. How can you validate the accuracy of a generative adversarial network. San Juan, PR, USA: Machine Learning Mastery; 2023 [cited 2025 Jan 1]. Available from: https://www.linkedin.com/advice/0/how-can-you-validate-accuracy-generative-adversarial. [Google Scholar]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF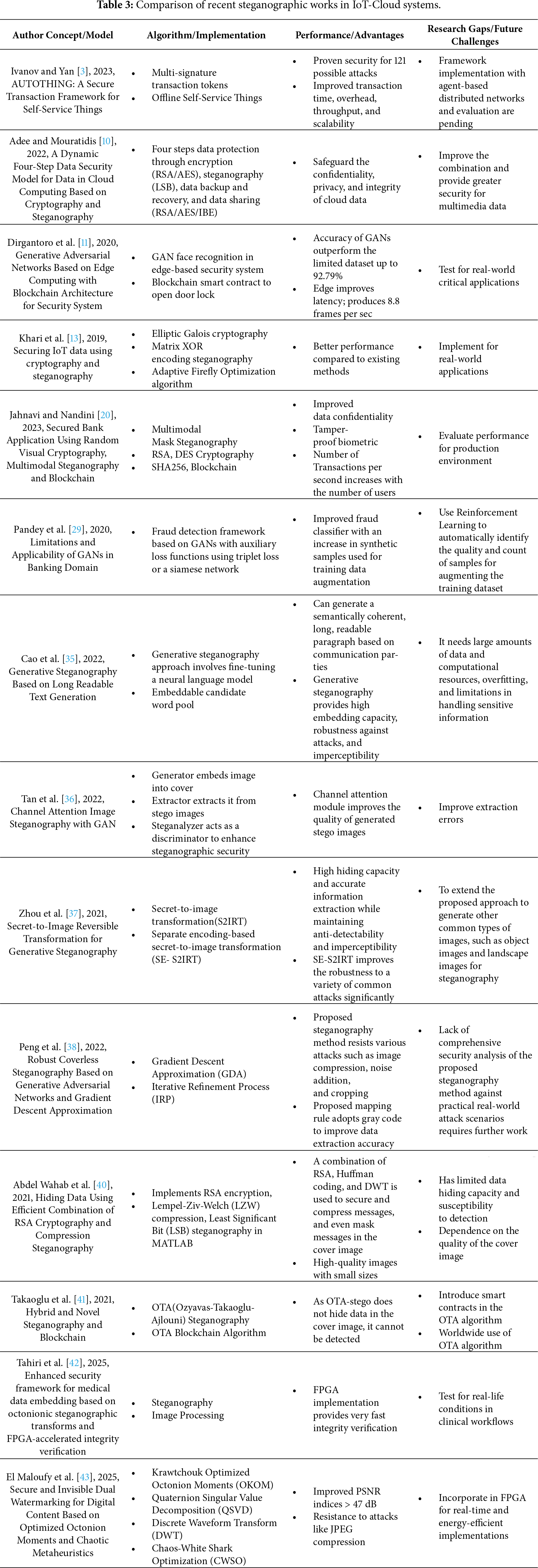
 Downloads
Downloads
 Citation Tools
Citation Tools