 Open Access
Open Access
ARTICLE
Enhancing Disaster Response with IoFT: An Adaptive Communication Model for UAV-Based Surveillance
Computer Engineering Department, Sakarya University of Applied Sciences, Sakarya, Türkiye
* Corresponding Author: A. F. M. Suaib Akhter. Email:
Computer Modeling in Engineering & Sciences 2026, 146(2), 31 https://doi.org/10.32604/cmes.2026.077574
Received 12 December 2025; Accepted 22 January 2026; Issue published 26 February 2026
Abstract
The modern world remains vulnerable to natural disasters, including floods, earthquakes, wildfires, and others. These events remain unpredictable and inevitable, and recovering quickly and effectively requires significant effort and expense. Monitoring is becoming more efficient thanks to technologies such as Unmanned Aerial Vehicles (UAVs), which can access hard-to-reach areas and provide real-time data. However, in disaster-affected areas, these monitoring systems may encounter many obstacles when communicating with servers or transmitting monitored data. This paper proposes an adaptive communication model to overcome the challenges faced in disaster-affected areas. A base station is responsible for collecting data (such as images and videos) captured by UAVs performing surveillance within its communication range. This station is typically a tower providing fixed cellular network service. However, in the absence of such a tower, a selected UAV may serve as the station, depending on the situation. If surveillance needs to be performed outside the coverage area, it can continue to communicate via nearby UAVs through cooperative communication. UAVs with internet support, known as the Internet of Flying Things (IoFT), will also be utilized to enhance communication capacity and efficiency. The proposed communication model is validated through experiments, showing superior data transmission performance and higher throughput. Analysis indicates it outperforms traditional systems, even in rural areas, with or without internet access.Keywords
From the beginning of the world until now, natural disasters have caused severe destruction, including property damage and loss of life. All types of disasters (geophysical, hydrological, meteorological, and climatological) remain nearly impossible to stop, as they are unpredictable and inevitable [1,2]. Each year, disasters impact millions of people and animals, with financial losses reaching hundreds of billions of dollars globally [3]. According to the report by the Centre for Research on the Epidemiology of Disasters (CRED) in 2024, a total of 387 natural disaster occurrences were reported globally, resulting in a loss of over 30,000 human lives and financial damages exceeding $223 billion [4]. However, with improvements in current technology, it is now possible to reduce their impact through early prediction, forecasting, quick actions after their occurrence, monitoring, and rescue efforts. Among these, the first thing needed after a disaster is an efficient surveillance system for monitoring affected areas, detecting survivors, and assessing damage to ensure faster and more effective recovery [5].
Surveillance in a disaster-affected area is one of the most challenging tasks as in most cases it is impossible to reach or explore most of the affected areas. Previously and even now helicopters are used for surveillance and rescue though it is an expensive way and has many shortcomings. Reversely, UAVs, an impressive achievement of modern technology, are now widely used in various fields, such as forest firefighting, internet coverage, high-altitude communication, border monitoring, and power-line inspection [6]. As it is possible to equip UAVs with high-resolution cameras, they can capture live footage from any location and help find important information from inaccessible areas. Their capability to cover vast areas quickly and capture high-quality images and videos makes them very efficient tools for surveillance, even in places where it is difficult for humans to reach or where expensive tools like helicopters are required [6].
In disaster-affected areas, there are many obstacles that UAVs are required to face, and the most difficult problem is solving network availability issues [7]. This is because cellular networks and internet services are sometimes damaged by disasters. In such cases, UAVs have to fly long distances to transfer the captured information, which increases energy consumption and causes delays in delivering information [8]. As a result, recovery activities become slower. Moreover, if UAVs fly along random paths, some UAVs may cover the same area, while other areas are missed in surveillance. However, there may be some critical points that require continuous surveillance. In that case, dedicated UAVs are required for this purpose, with an energy-efficient operational facility.
For this purpose, this paper divides all possible operational situations into six distinct scenarios. Each scenario provides an optimized solution designed for a specific condition. For example, when a Base Station (BS) is available and the surrounding area requires continuous surveillance, UAVs operate under the BS coverage to ensure real-time communication (Scenario 1). For a similar situation where no fixed BS is available, a temporary BS (TempBS) using an internet-supported UAV is introduced to maintain network continuity and data transfer (Scenario 2). There could also be a situation (Scenario 3) where UAVs are required to perform surveillance in areas without any BS or TempBS coverage. In this case, a relay communication model is proposed, where a nearby UAV connected to a BS receives data from out-of-range UAVs and relays it to the BS. However, if the UAVs have internet connectivity, they will choose the faster channel and transmit data over it. Scenario 4 is prepared when critical points within a BS range require continuous monitoring, in which dedicated UAVs perform focused surveillance and directly send data to the BS/TempBS or server. In contrast, Scenario 5 addresses critical point surveillance outside BS coverage, where UAVs either use internet connectivity or receive relay support from nearby UAVs. Finally, if none of these facilities are available, Scenario 6 is designed for special-purpose UAVs that operate independently in isolated or communication-limited areas and later transfer stored data when network access becomes available, which represents a typical last-resort situation. Collectively, these six scenarios ensure the system’s adaptability under diverse disaster conditions, guaranteeing efficient communication, energy optimization, and continuous surveillance. In contrast to existing UAV-enabled dynamic multi-target tracking and sensing frameworks, which typically optimize trajectories for spatial target proximity, this research focuses on establishing a robust communication backbone. Our adaptive framework is distinguished by its ability to maintain high-throughput connectivity through six operational scenarios tailored for infrastructure-compromised disaster zones.
The key contributions of this paper are as follows.
• We propose a UAV-based surveillance system for monitoring areas affected by natural disasters, where a BS is responsible for data collection and transfer. This BS is not only equipped with internet access and UAV charging capabilities but also features advanced features to effectively manage and maintain the transmission area.
• While the BS facility is unavailable, an alternative scenario is presented using a TempBS, where a UAV with internet connectivity can act as a BS and provide similar services. It controls data transmission, optimizes UAV movement, and ensures continuous surveillance without interruption.
• To continue high-speed data transfer for the UAVs that perform surveillance outside the area of the BS/TempBS, a relay data transfer mechanism is introduced that enhances the system’s ability to expand the surveillance area, ensuring uninterrupted data flow across larger and more complex environments.
• The proposed model improves surveillance coverage by enabling UAVs to operate both within a coordinated network and independently, which is crucial for effective monitoring in remote or disaster-affected areas. In the event of unavailability of BS/TempBS or relay services, IOFT will be used to capture and transmit data immediately to ensure continuous surveillance.
These contributions highlight the practicality and adaptability of our UAV-based surveillance system in handling emergency situations and delivering reliable data in challenging environments. The rest of the paper is organized as follows: Section 2 presents the Literature Review and Motivations for the work; Section 3 provides detailed descriptions of the system, including its components, protocols, and scenarios; Section 4 offers some experimental analysis, covering both the communication protocols and the system’s energy efficiency; and finally, Section 5 concludes the paper.
2 Literature Review and Motivations
UAVs offer several advantages for disaster monitoring, and researchers focus on improving communication efficiency, reducing production costs, etc. While most solutions are effective, the situation changes during disasters due to the unavailability of the internet or inadequate network infrastructure. Additionally, multiple handovers in ad hoc networks can significantly reduce system throughput. In this section, we highlight recent and significant research on UAVs, particularly in the development of improved communication protocols.
The importance of UAV-based surveillance is clear to everyone. The key advantage of UAVs is their ability to access areas that are either unreachable for humans or prohibitively expensive to access. As a result, after disasters, the use of UAVs makes many difficult tasks easier. Several studies have focused on this topic. For example, in disaster recovery, UAVs are used to assess damage and support rescue efforts efficiently.
For example, in [9], the researchers developed an autonomous UAV surveillance system that uses computer vision and machine learning to secure critical locations. The system combines daylight and thermal cameras for detecting and classifying flying intruders, using the YOLO convolutional neural network for highly accurate detection with minimal false alarms. Similarly, ref. [10] proposed a UAV network for video surveillance in regions without cellular infrastructure, optimizing grid topology to eliminate blind spots and maintain video quality. Furthermore, ref. [11] addressed the challenges of using UAVs for traffic monitoring, particularly in detecting objects in cluttered aerial images. Additionally, ref. [12] proposed a hybrid surveillance system using UAVs and blimps to overcome limitations of both platforms. In [13], deep learning models were applied for violence detection and individual recognition in UAV-captured video footage. While researchers have developed autonomous surveillance for tracking specific intruders [9] or road traffic [11], these models often assume a stable underlying network. Our proposed model differs by shifting the focus toward multi-layered communication resilience—utilizing sectorized movement to minimize channel contention and maximize data backhauling efficiency in the absence of pre-existing infrastructure.
Moreover, in [14], the authors reviewed various UAV surveillance applications and optimization strategies, highlighting the use of artificial intelligence and advanced navigation algorithms to improve UAV performance in areas like environmental monitoring and infrastructure inspection. Another comprehensive survey, ref. [15], explored the potential of UAV swarms in adversarial scenarios, emphasizing the development of the Integrated Low Detection Probability (ILDP) method to minimize detection risks and improve real-time surveillance capabilities. These survey papers underline the expanding role of UAVs in diverse surveillance tasks, showcasing how advances in AI and swarm deployment strategies are pushing the boundaries of UAV technology for improved efficiency and effectiveness.
2.2 UAVs in Natural Disaster Recovery
UAVs have become essential tools in handling disasters and helping with recovery. They’re being used in many ways, from locating people and supplies to assessing damage and delivering aid. For example, ref. [16] developed a low-cost system where UAVs process images in real time to assess damage after disasters. Similarly, ref. [17] looked at how UAVs can be used to deliver emergency goods in areas where infrastructure is damaged. Their model helps multiple UAVs work together to ensure aid gets delivered efficiently. In [18], UAVs were used to test new techniques for controlling damage during disasters, providing quick information for faster responses.
UAVs are also invaluable for monitoring floods. In [19], researchers explored how UAVs are used to map and monitor flooded areas, giving real-time data that’s crucial for recovery. Another study [20] focused on how UAVs were deployed during the 2024 Noto Peninsula earthquake in Japan, where they played a key role in providing critical information to guide rescue operations.
UAVs play an equally crucial role in humanitarian aid operations. An example is provided by [21], who studied the utilization of UAVs in delivering assistance and overseeing disaster-affected regions, demonstrating the advancements in UAV technology. Additionally, ref. [22] explored the enhancements in disaster response brought about by AI-driven UAVs, which are capable of making intelligent choices and handling intricate duties. Narendran et al. demonstrated how UAVs can rapidly scan fire-affected areas in firefighting, enabling firefighters to grasp the situation more quickly [23].
Using artificial intelligence alongside UAVs can enhance the efficiency of disaster response. In [24], researchers highlighted how this pairing improves response times and coordination in disaster situations. Researchers in [25] suggested a smart city system that employs UAVs to uphold communication and evaluate damage in instances where conventional systems are ineffective. Another research conducted by [26] presented a UAV intended for emergency response during natural disasters, offering live data to support rescue operations. A thorough examination was carried out by Daud et al. regarding the applications of UAVs in disaster response. The research demonstrated that UAVs are more frequently aiding in duties such as surveillance, charting, and transporting goods to remote locations [27]. All of these research studies show that UAVs are increasingly necessary in disaster response, providing speedy and effective support in aiding recovery efforts.
2.3 Communication Protocols for UAVs
In unplanned scenarios, UAVs are manually controlled and move randomly. As a result, they miss important areas, leaving some places unexplored while others are captured multiple times by different UAVs. Without coordination, this leads to inefficiency. Another major issue is communication. UAVs, often referred to as the Internet of Flying Things (IoFT) when equipped with internet connectivity, can communicate directly via the internet [28]. However, in disaster recovery situations, internet access is often unavailable, making it necessary to use communication protocols like IEEE 802.11 to transfer the captured data to a location that has internet access.
To ensure efficient communication between UAVs, several methods are available. For example, Jin et al. developed a cluster-based video surveillance system designed for heterogeneous communication environments in smart cities targeted to enhance efficiency [29]. Wu et al. also proposed a multi-UAV clustering strategy to reduce insecure communication ranges and address security concerns in UAV networks by dynamically adjusting communication ranges [30]. An intelligent cluster-based communication system is proposed by Mehmood et al., targeted to enhance real-time data sharing and coordination among UAVs during emergency response operations [31]. Khayat et al. focus on weighted clustering schemes using latency-oriented trust for better reliability [32]. Likewise, Su et al. proposed a non-stationary cluster-based channel model for low-altitude UAV-to-vehicle communications [33]. Both of the models consider latency, trust, and dynamic conditions to improve communication efficiency.
Relay protocols are also proposed for UAVs to enhance the communication efficiency. For example, Wu et al. [34] introduced a cooperative cluster model that helps UAVs extend network coverage and integrate with terrestrial networks. Goel & Gupta proposed a multi-cluster cooperative approach to maintain connectivity in disaster-hit areas, ensuring stable communication even in harsh conditions [35].
Task-oriented and routing protocols focus on optimizing UAV missions. Lu et al. [36] presented a method that combines task assignment with trajectory planning targeted to achieve optimal resource distribution and enhancing mission performance in resource-constrained environments. Swain et al. [37] developed a reinforcement learning-based routing scheme that dynamically adjusts UAV paths for better adaptability. Wang et al. [38] developed a trajectory optimization model to improve energy efficiency, particularly in maritime UAV networks. In [39], Wei et al. propose a covert UAV communication scheme where a Cognitive Jammer (CJ) masks transmissions through spectrum sensing, eliminating the need for security-risky information synchronization links. Simulation results demonstrate that by optimizing trajectories and power levels, this method achieves a higher Minimum Average Covert Rate (MACR) with lower power consumption than traditional jamming methods, even under Warden location uncertainty.
These studies show different approaches to UAV communication, each addressing specific challenges. However, in extreme situations like natural disasters or remote locations, ensuring a stable and long-range network is still difficult. This paper proposes a structured communication protocol to solve these issues.
In disaster scenarios where network infrastructure is often compromised, the system must be adaptive to handle multiple situations. There is a pressing need for a comprehensive, autonomous surveillance system. This paper addresses such scenarios by proposing a UAV-based surveillance system tailored for disaster response.
Table 1 compares our work with existing research, highlighting that our approach provides an adaptive solution for continuous surveillance support under challenging conditions following disasters. Our approach prepared a comprehensive solution to handle possible scenarios for UAV-based surveillance systems. We also look at a real-world example: the earthquake in Maras, Türkiye, on February 6, 2022. During this disaster, both government and non-governmental groups sent UAVs to support surveillance and recovery efforts. Fig. 1 shows a conceptual view of UAV operations during the Maras earthquake. It illustrates how several UAVs were moving randomly, without following a proper communication protocol. However, observations from the response revealed that UAVs faced significant challenges due to the lack of a reliable communication system. As a result, UAVs had to travel long distances to transmit data, which consumed considerable energy and reduced system efficiency. This situation emphasizes the urgent need for an optimized communication system that minimizes energy usage while ensuring real-time data transmission.
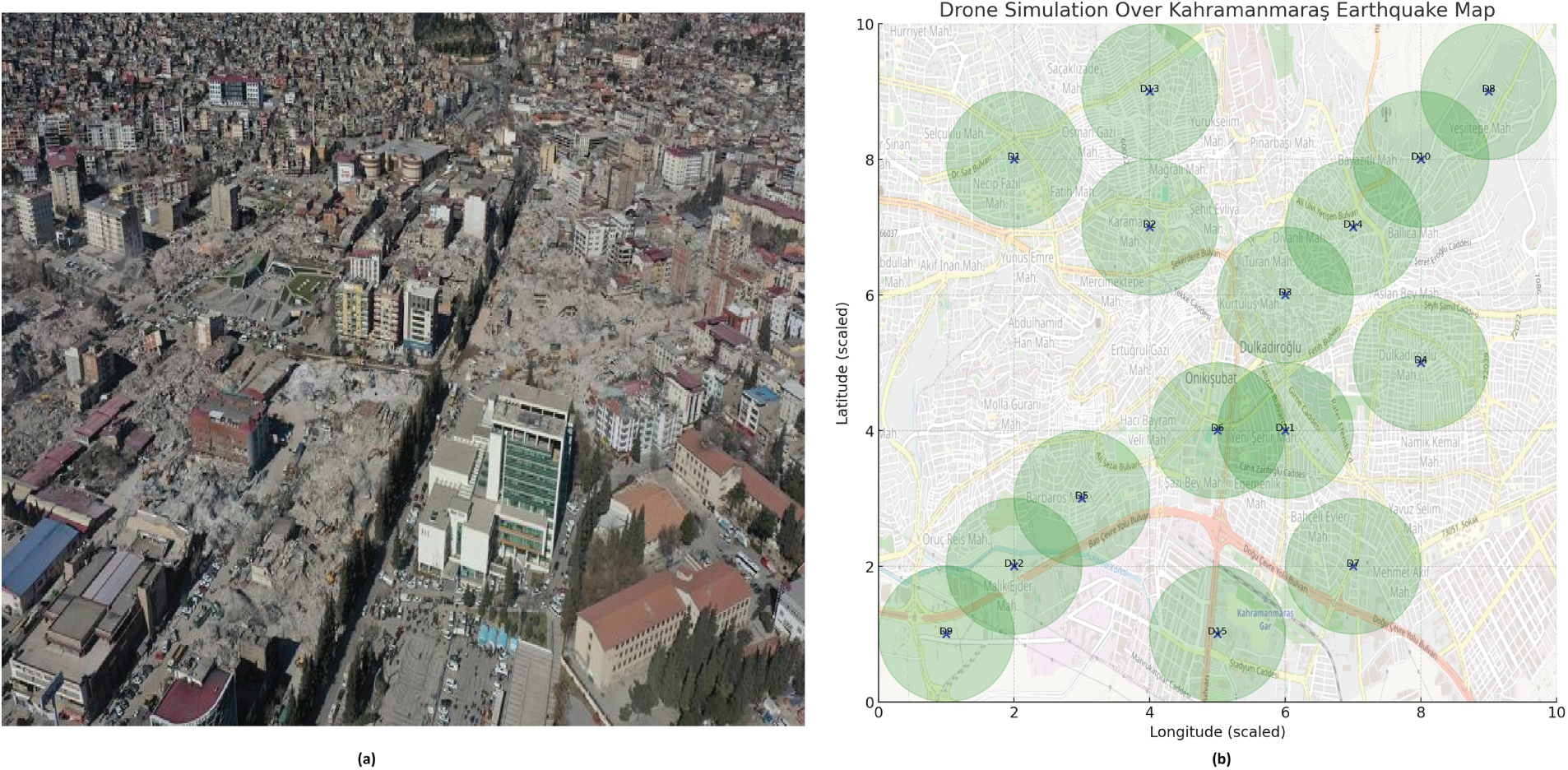
Figure 1: (a) Real view and (b) Conceptual view of UAV operations during the Kahramanmaraş earthquake, illustrating random movement and lack of coordinated communication [41].
To address the potential issues encountered during surveillance, this paper proposes a system that offers multiple communication supports, which UAVs can adapt to ensure continuous data transfer. These options include communication via BS/TempBS, relay support, or internet connectivity. Additionally, a peer-to-peer system is implemented, where UAVs follow predetermined pathways, ensuring that no other UAVs interfere and enabling uninterrupted data transfer during flight without continuous handshaking common in ad hoc networks. The well-planned network setup also reduces power consumption and which increases the operational time. The system is designed to be compatible with various additional features, such as hanging, wireless charging, and UAVs capable of image processing, further enhancing scalability.
Natural disasters are beyond our control, but to lessen their impact, this paper introduces a sustainable surveillance system. Proposed system is designed to monitor disaster-affected areas, especially those that are hard for humans to reach quickly, and to deliver real-time information to support recovery efforts. It utilizes the latest UAVs equipped with advanced technologies and employs efficient data-handling and sharing protocols. It can also be adapted to any UAV with at least a camera.
This section provides a comprehensive explanation of the system’s design. It begins with a description of the components and physical modules used, followed by an overview of two communication protocols. Then, various scenarios that may arise during disaster recovery are discussed, with explanations of how the proposed system addresses each. An illustration of these scenarios is provided in Fig. 2.
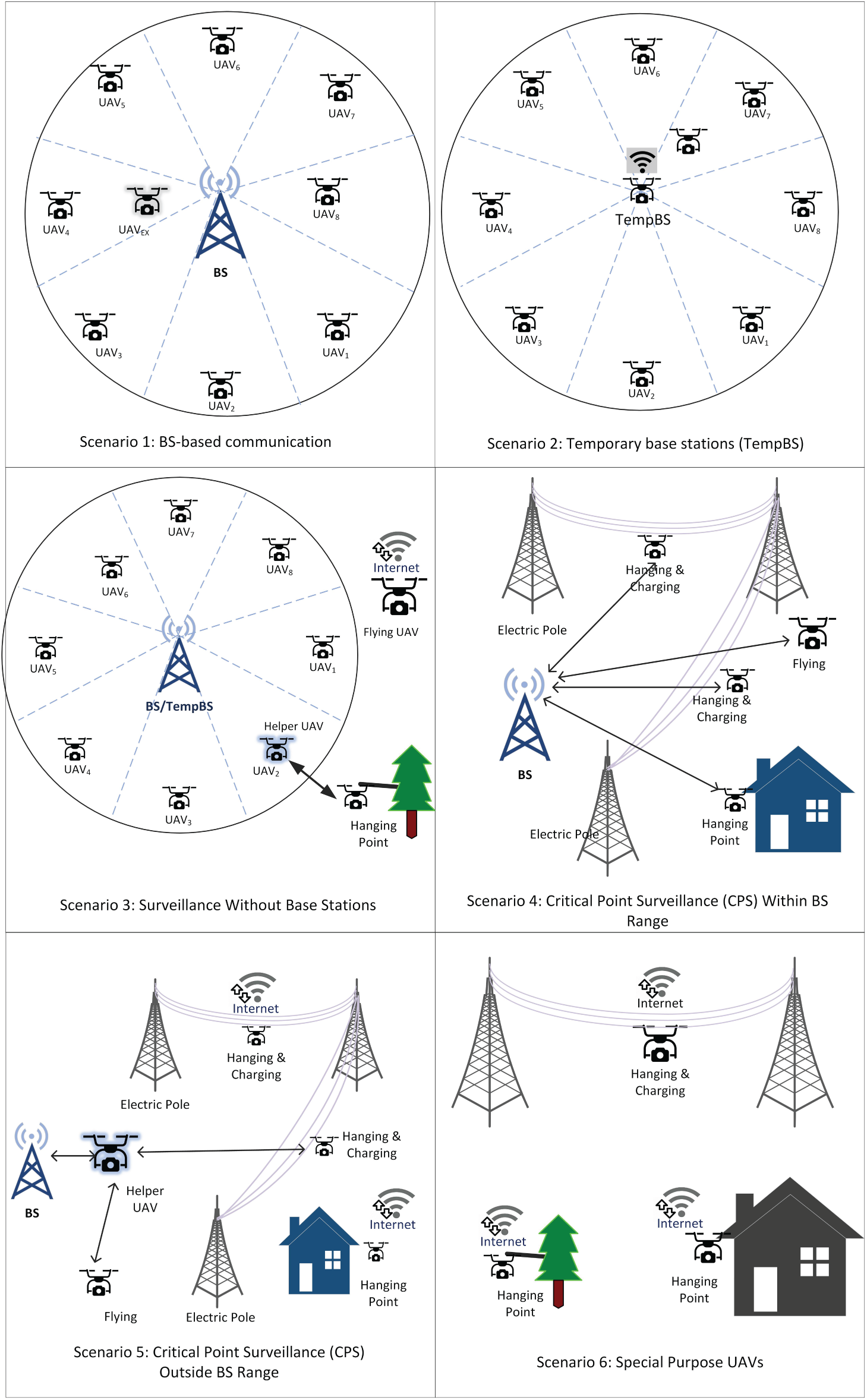
Figure 2: Overall view of disaster recovery scenarios and the UAV system’s operations (Details in Section 3.3 and Algorithm 1).
The proposed UAV-based disaster surveillance system comprises several essential components. This section provides a detailed description of the physical devices used in the system. Before diving into the communication protocols, the focus is on explaining these key physical components and their roles in ensuring effective disaster response.
To conduct effective surveillance operations, UAVs must possess specialized capabilities tailored to different geographical conditions. Since UAV configurations vary based on industrial, professional, entertainment, and other applications, the proposed model aims to integrate all possible UAV types.
For the sake of the proposed system, it has been assumed that the UAVs that participated have the following capabilities.
• High-resolution camera for capturing clear, detailed images and videos, crucial for accurately assessing disaster-affected areas and identifying objects or people in need of assistance.
• Powerful battery backup to ensure continuous operation, allowing UAVs to capture images and videos over extended periods without frequent recharging interruptions.
• On-Board Unit (OBU) to enable the UAV to join and participate in a peer-to-peer network, facilitating seamless communication with nearby BS/TempBS or UAVs for quick data sharing.
• Preferably equipped with internet connectivity to extend the surveillance range and transmission speed, ensuring real-time data transfer even in isolated areas.
The BS considered in the proposed system could either be a base station from a cellular service provider or one selected from UAVs with internet access. Although any UAV equipped with an On-Board Unit (OBU) and internet connectivity could serve as a BS, in such cases, the system’s longevity would be reduced compared to using dedicated BS models. The BS must be able to communicate with UAVs to collect data from them, as well as have a high-speed internet connection to transmit the collected data to the analysis server. Additionally, the BS must have sufficient processing power, memory, and storage capacity to handle data from 8 UAVs simultaneously and forward it to the processing center.
3.1.3 Temporary Base Stations (TempBS)
In situations where a BS is unavailable, a UAV with a relatively higher battery capacity and data processing capabilities will be selected as a TempBS. The TempBS performs similar tasks to the BS but lacks certain facilities, such as collecting data from surrounding UAVs and transmitting it to the server for further analysis via the internet. Since the TempBS stays in a fixed location, the UAVs should have perching or hanging capabilities, along with energy-saving features, to extend their operational time. However, charging facilities or backup batteries will also be helpful to provide continuous support.
To enable rapid information collection, two communication protocols are proposed. The first is a base station (BS)-based communication system, where all UAVs involved in the surveillance task operate with the BS at the center. These UAVs will continuously transfer data to and from the BS while performing their tasks.
The second protocol is designed for UAVs located outside the BS coverage area. In such cases, a volunteer UAV can act as a relay, forwarding data from the out-of-coverage UAVs to the BS. The details of these communication protocols are described in this section.
3.2.1 BS-Based Communication Protocol
In this system, a BS is considered the center of communication. Based on the coverage area of the BS, the maximum transmission area will be identified, and the total area will be divided into eight blocks (illustrated in Fig. 3). Each UAV is assigned to a single block and follows a static path that allows its camera to cover the entire block.
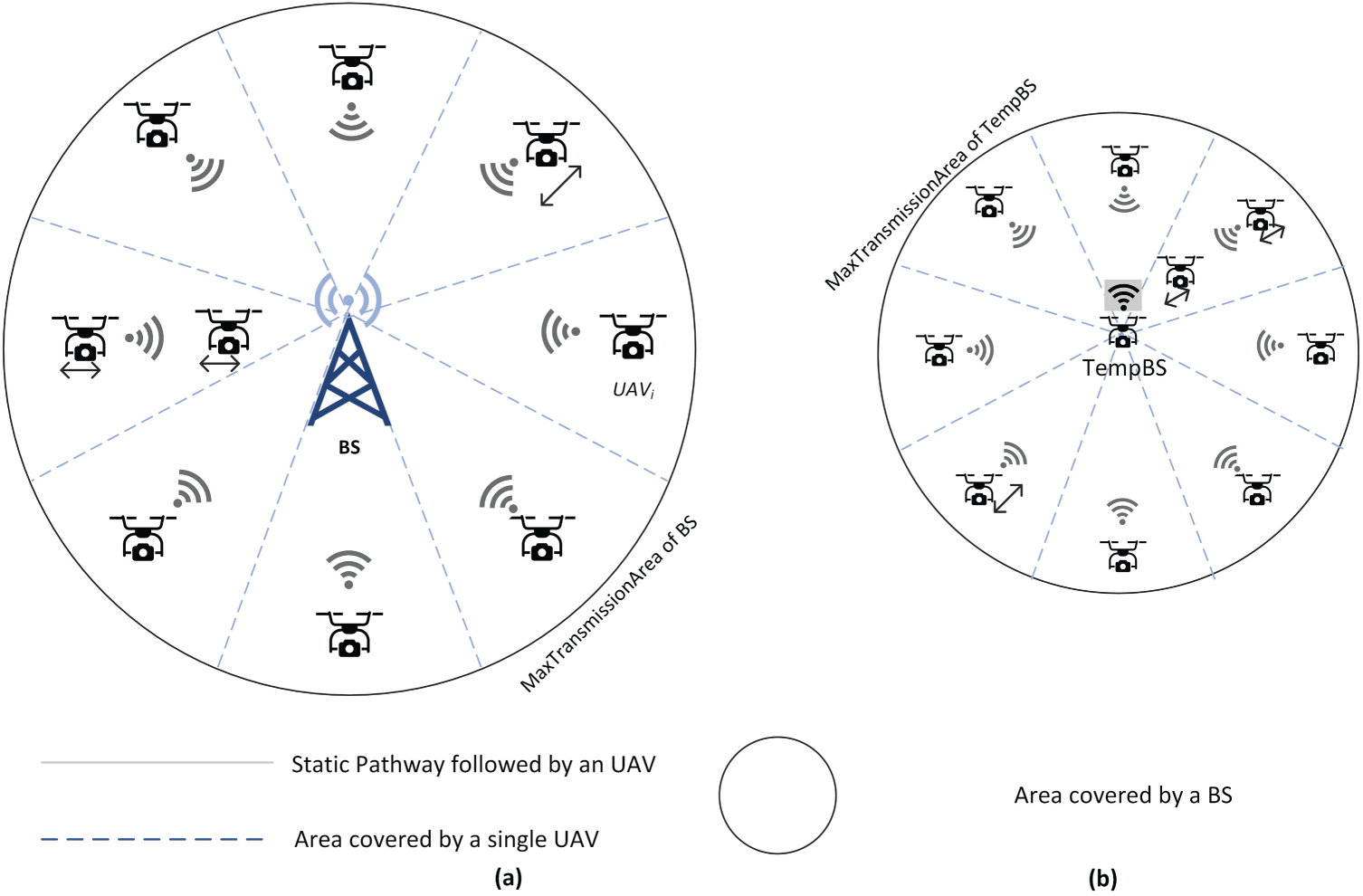
Figure 3: Spatial sectorization and scheduled trajectory mapping for the BS/TempBS-based system.
If necessary, depending on the availability of UAVs and the importance of an area, a block can be covered by two UAVs. In such cases, while one UAV moves forward, the other can cover the backside of the block. Fig. 3 illustrates the overall concept of BS-supported block-based surveillance, where 3a represents a typical BS with a larger coverage area, and 3b shows a scenario with a TempBS. Fig. 4 presents a visual representation of the BS/TempBS-based system and the UAVs, along with their coverage areas.
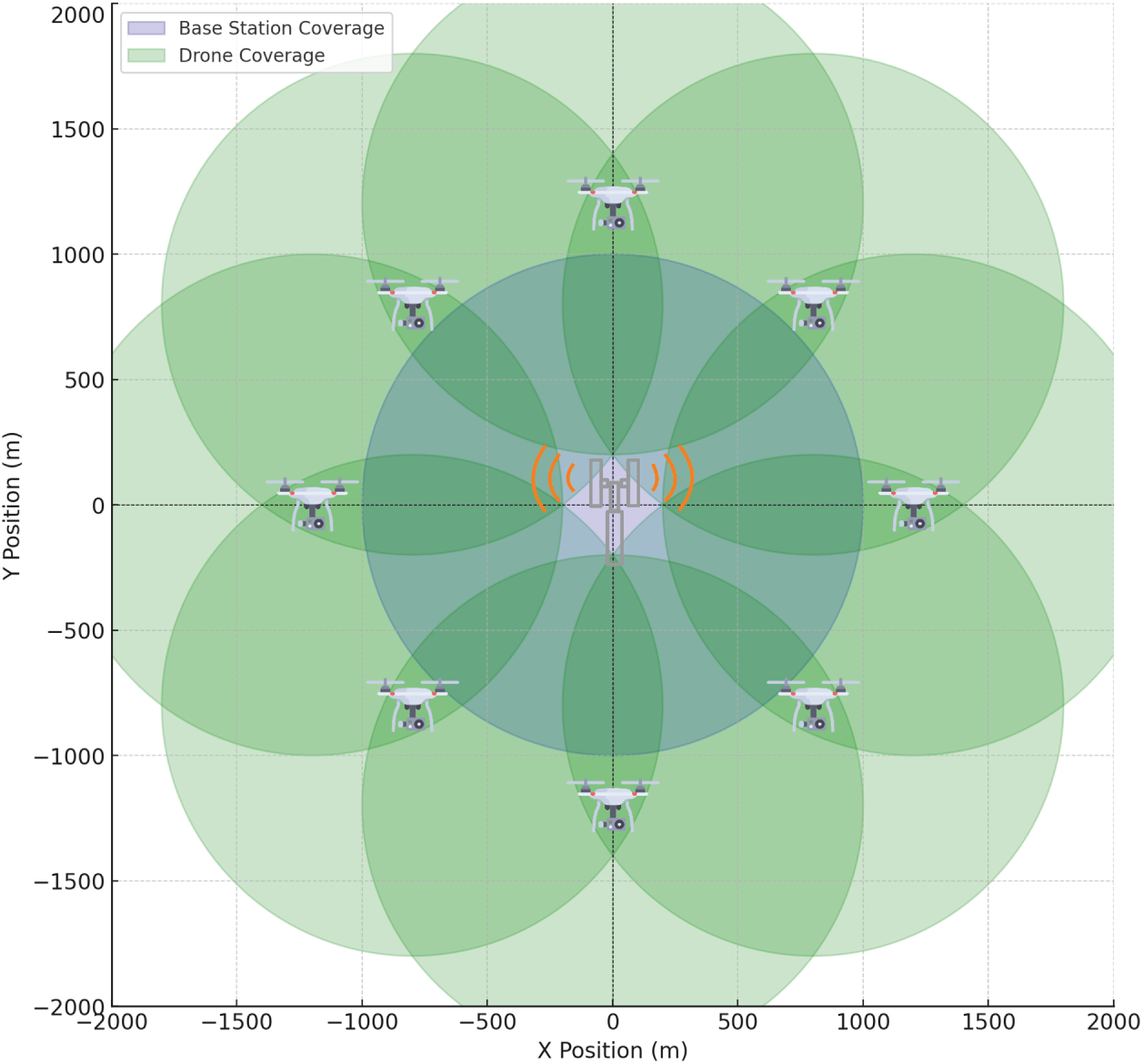
Figure 4: A visual representation of the BS/TempBS-based system and UAVs with their coverage area.
When one or more UAVs are assigned to a specific block, they move from the BS to the MaxTransmissionArea and then return to the BS or the TempBS. During their movement, UAVs continuously capture video of the disaster-affected area and transmit it to the BS via their OBUs. Initially, typical data packets are exchanged to establish a connection between the UAV and the BS/TempBS. After establishing the connection, data transmission continues until the UAV’s battery reaches a minimum level.
Each block requires a backup UAV. For instance, if there are eight blocks, eight additional UAVs must be on standby to provide backup surveillance service when one UAV is resting and recharging.
Since the members of a particular block are fixed, specific packets are created or modified from IEEE 802.11 RTS/CTS [42] to enable faster and more efficient registration and communication. The packet structures are described in Fig. 5. Whenever a new UAV starts operating, it sends an RTS (Ready to Send) signal to the BS. The BS responds by sending a special packet, RFBI (Request for Block Information), to support the block-based system. After receiving the RFBI, the UAV sends a BI packet that includes the assigned block information. Upon receiving BI, the BS sends a CTS (Clear to Send) message, and the UAV starts transmitting data. If a UAV leaves a block for recharging or other purposes, it sends a block leave request to the BS so the BS can remove it from the active list. The simplified message transmission is shown in Fig. 6a.
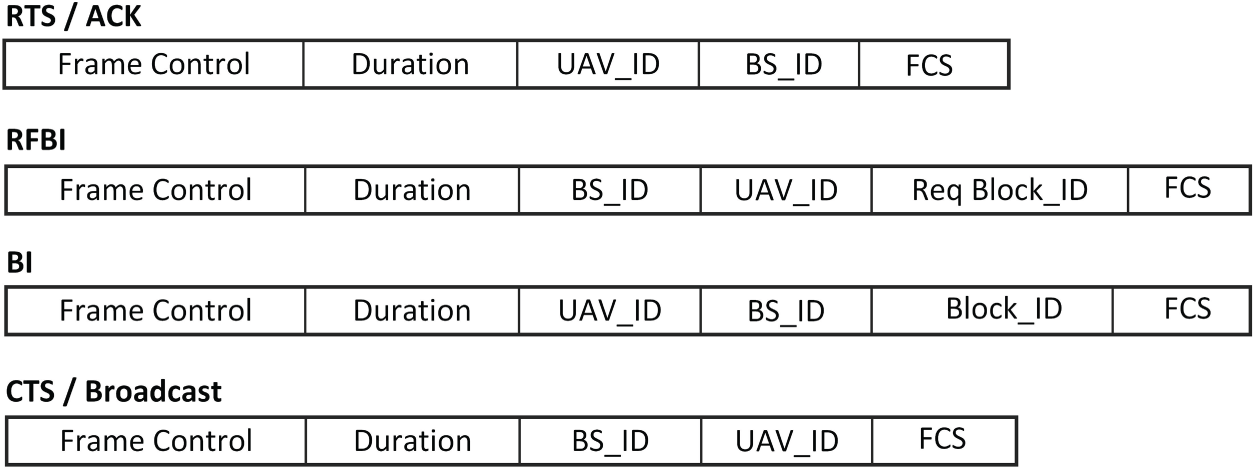
Figure 5: Modified packet structure for BS-based communication system.
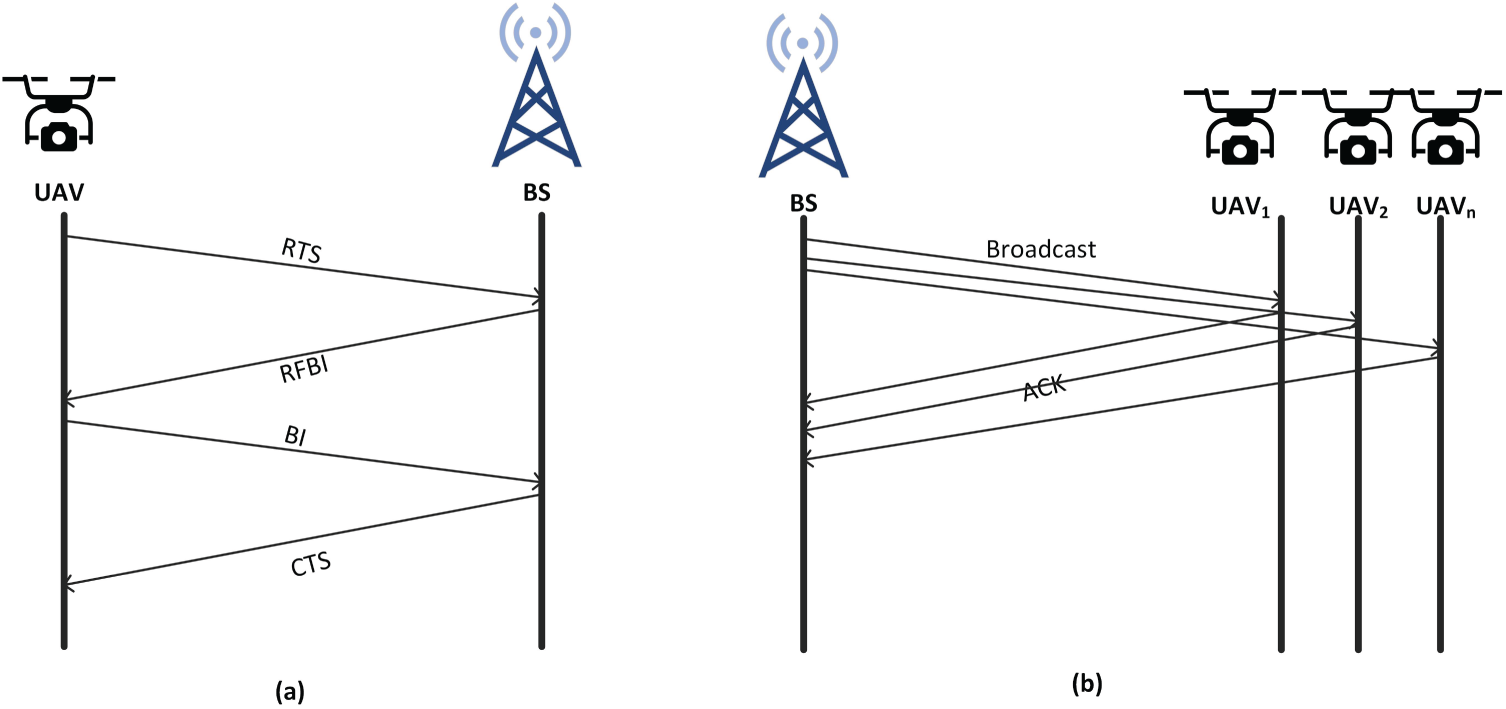
Figure 6: Message transmission system in BS-based communication.
The BS can broadcast messages to all UAVs within its coverage area in the event of an energy-related issue. In such cases, the BS does not use the typical RTS/CTS method but performs a direct broadcast to all UAVs and waits for ACK (Acknowledgment) messages from them. The broadcasting process is illustrated in Fig. 6b.
All BSs are connected to a central server via the internet, enabling continuous transmission of data received from their member UAVs for further investigation and decision-making. This transmission continues until any UAV reaches its minimum charge level. The server must arrange a backup UAV for each UAV so that when one returns for recharging, another can immediately take its place to maintain continuous surveillance.
3.2.2 Relay Communication Protocol
If UAVs need to surveil a particular area or a fixed point and are out of range of any BS and lack an internet connection, the proposed relay communication protocol can be utilized to ensure faster, more reliable, high-throughput, and low-latency connectivity. To provide this service in the proposed model, we have modified some packet structures from the IEEE 802.11p standards [43].
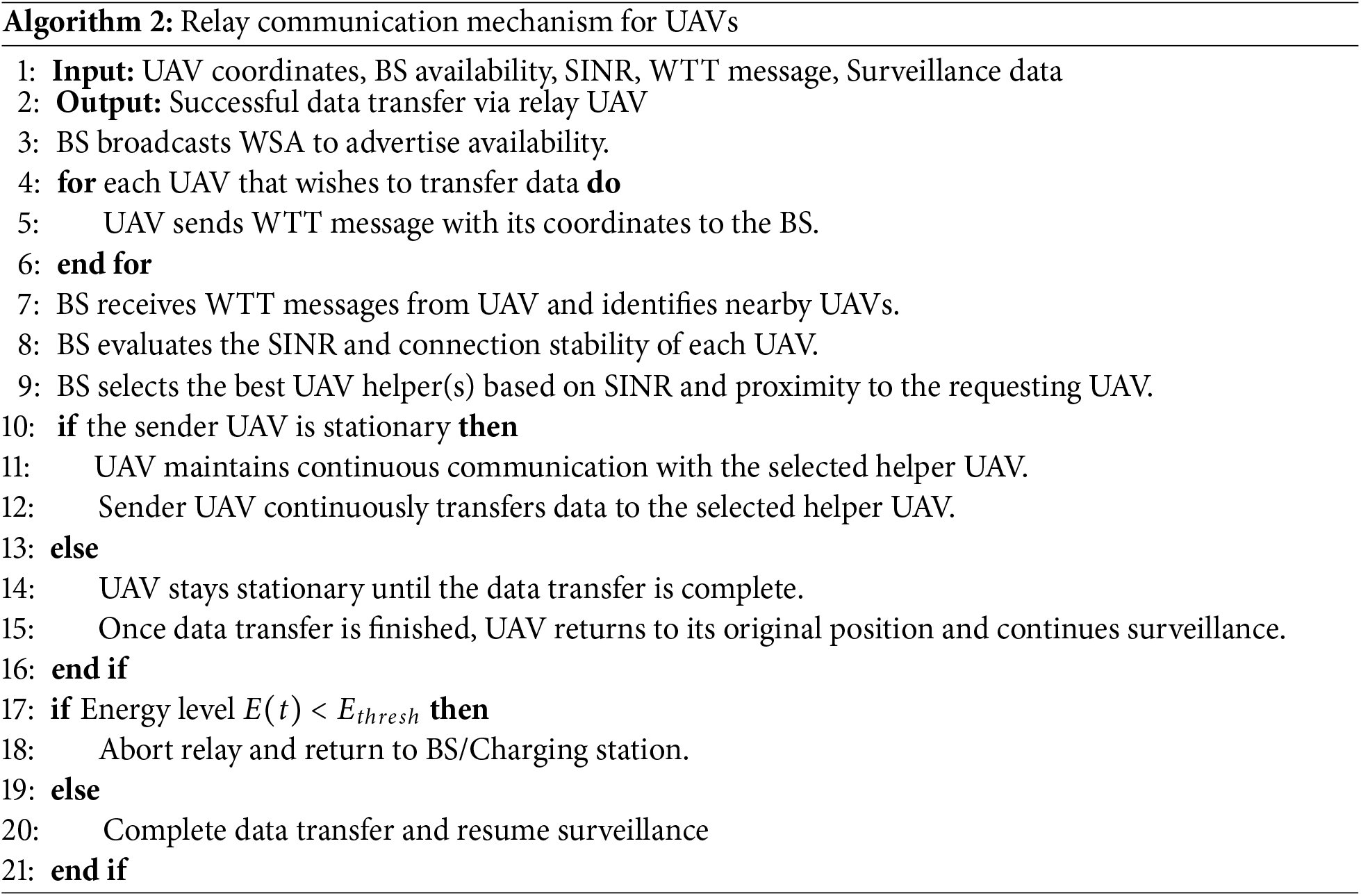
The communication process begins when the BS broadcasts a Wireless Access in Vehicular Environments (WAVE) Service Advertisement (WSA) to advertise its availability. UAVs that wish to transfer their data send a Want to Transmit (WTT) message, sharing their coordinates with the BS. The BS then selects one or more UAVs that are nearest to the coordinates of the requester, considering their Signal-to-Interference-plus-Noise Ratio (SINR) and the stability of the connection. Since the BS knows the coordinates of both the UAVs under its coverage and the requester, it can easily select the best helper UAV. The BS sends the information by using ACK message. This approach simplifies and optimizes the relay handshaking process, making it more efficient and less time-consuming. Fig. 7 illustrates the scenarios with BS/TempBS and UAVs, along with their communication areas.
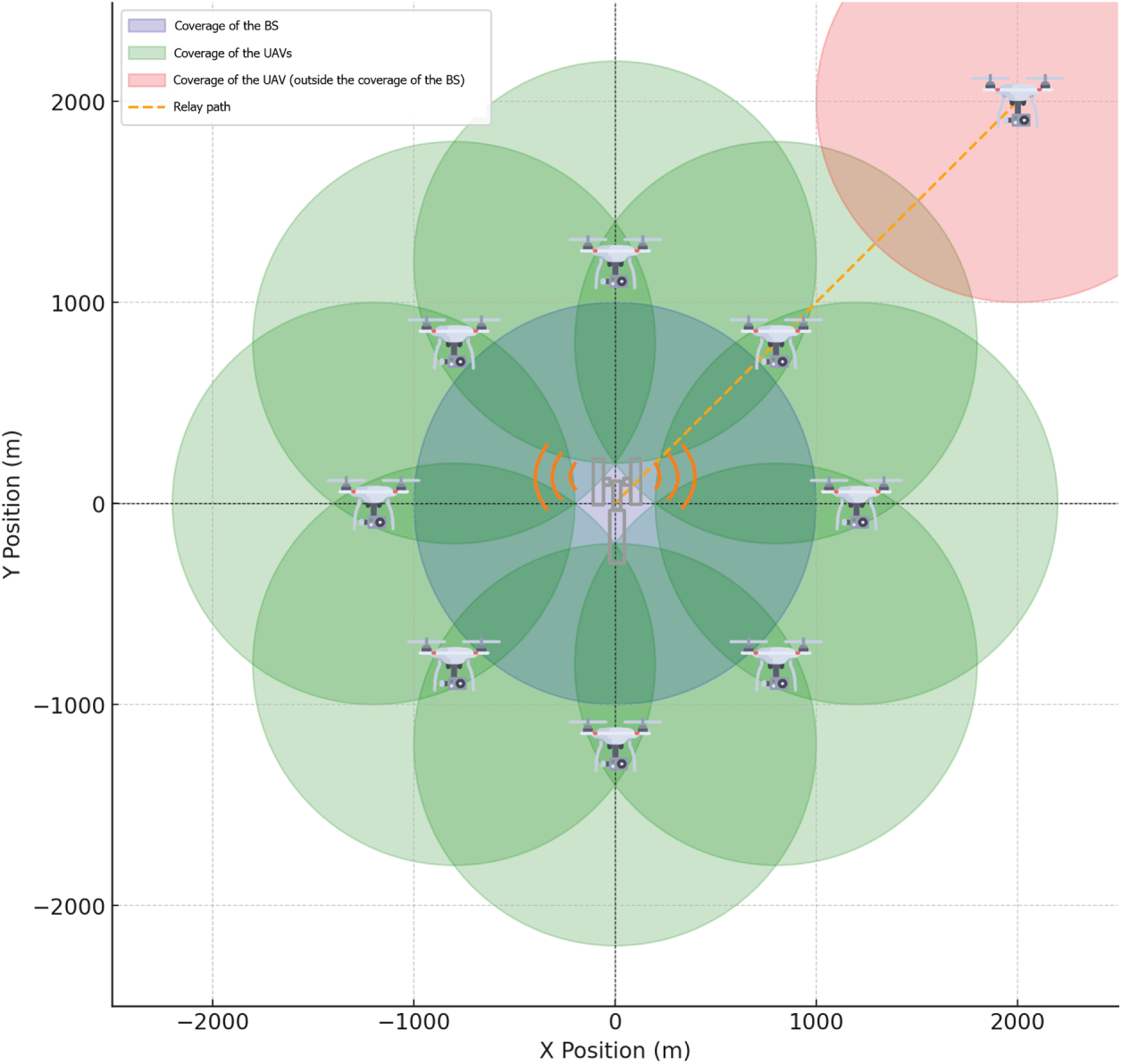
Figure 7: A relay system to transfer data from a UAV outside the coverage of BS.
The surveillance data transfer can happen in two ways:
1. If the sender UAV is stationary, it can maintain continuous communication with the helper UAV and transfer data uninterruptedly.
2. If the sender is in motion, it will remain in a fixed position until the data transfer is complete to maintain a stable connection with the helper UAV.
Once the data transfer finishes, the sender UAV returns to its previous position and resumes its surveillance duties. The complete process is summarized in Algorithm 2 and the handshake between the UAVs with the BS is illustrated in Fig. 8.
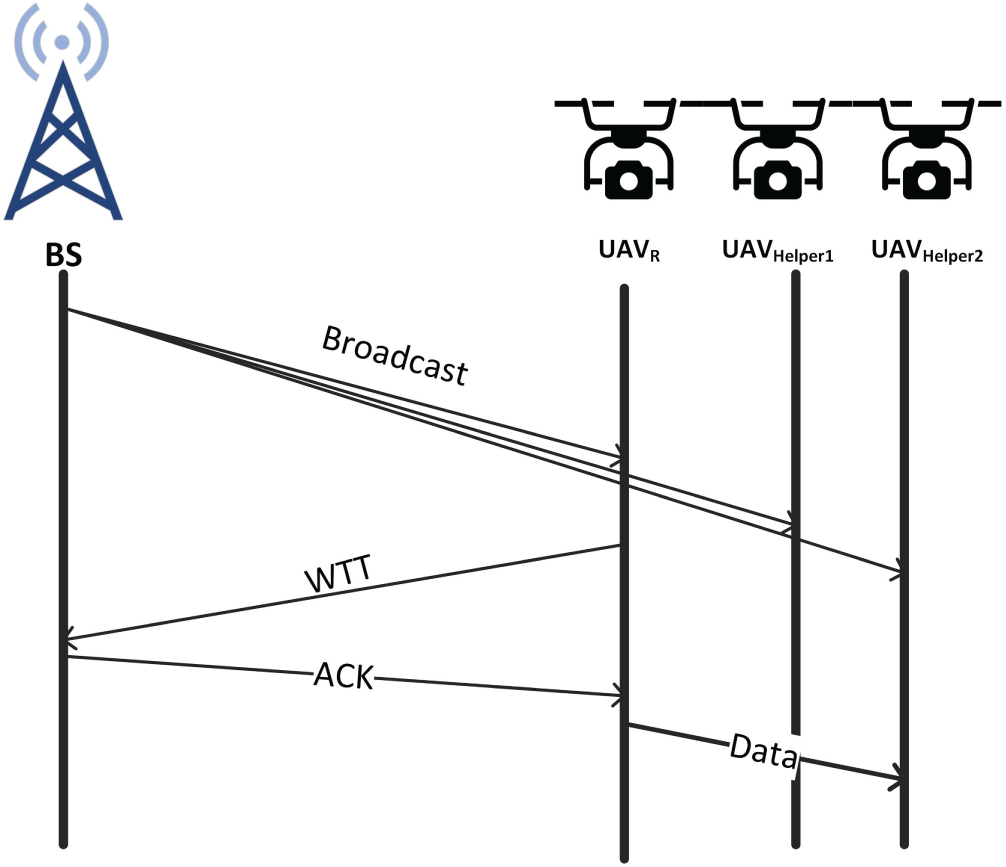
Figure 8: Handshake between the BS and UAVs for relay communication.
The trade-off between communication downtime and surveillance effectiveness is managed through a coordinated backup system. While a UAV in Scenario 3 or 5 may temporarily cease movement to ensure a stable relay link, the system’s overall effectiveness is maintained by a 1:1 backup ratio, where standby UAVs are deployed to fill coverage gaps.
We quantify this trade-off using the Surveillance Continuity Metric (
where
Disasters present numerous challenges, often making it difficult for a system to adhere to a strict plan. To ensure the sustainability of the proposed system model, it will be described through the lens of various potential scenarios. Six distinct scenarios are considered, each of which may arise during surveillance operations in disaster-affected areas. Real-world experiences have been gathered from recovery units involved in actual disaster recovery efforts, one from the 2022 Kahramanmaraş earthquake in Türkiye and another from the 2024 flood in Bangladesh. This section explains how the proposed method adapts to these scenarios, addressing both moving surveillance and stationary point surveillance. Algorithm 1 presented in this section explains all the scenarios.
3.3.1 Scenario 1: A BS-Based Communication Protocol
In situations where continuous surveillance is required over a large area with a radius of X km, the system can adapt by dividing the larger area into smaller, manageable zones, each with a similar radius. This division ensures that surveillance remains consistent and efficient, even in larger regions. The value of X depends on the capacity of the base station (BS). If the range of the BS is X/2, then the area covered by each BS will be half the total area of X km, and the entire surveillance area will need to be divided accordingly to maintain continuous coverage. A visual representation of this scenario is available in Fig. 4.
This is the scenario that can be considered the main scenario, because with this, the most efficient management and data communication can be ensured. Details of the communication model of this scenario are explained in this Section 3.2.1. The scenario ensures complete surveillance around its coverage area with real-time communication facilities. Moreover, as the UAVs are able to communicate just by using OBU, UAVs with minimum capabilities are able to participate in this scenario.
However, if UAVs with internet connectivity are available, they provide an additional advantage by transmitting data directly to the central data center, reducing the data load on the BS and speeding up the overall data flow for real-time analysis.
3.3.2 Scenario 2: Temporary Base Stations (TempBS)
In large-scale natural disasters, cellular phone towers may not be available or accessible for use as base stations. In such cases, certain UAVs can be designated as temporary BS to maintain the BS-based surveillance protocol.
For a UAV to serve as a TempBS, it must have the capability to receive data from member UAVs and possess internet connectivity to transfer this data to the central server for analysis. If the TempBS also has perching capability and a stable surface to perch on, its efficiency will be enhanced. Furthermore, if it can perch on an electric line with an AC current flow, or have any other wired or wireless charging facility, it can harvest energy from the line using the charging module, ensuring continuous operation. This ability allows the TempBS to remain functional as a BS for extended periods, maximizing its operational efficiency.
Once a UAV is set up as a temporary BS, the coverage area is divided into eight sections, with eight UAVs assigned to perform surveillance. These UAVs will operate in a configuration similar to that described in Scenario 1, following the communication protocol outlined in Section 3.2.1.
3.3.3 Scenario 3: Surveillance without BS/TempBS
There may be situations where UAVs are required to monitor an area where no BS or TempBS are available, or where only specific, targeted areas need to be monitored rather than a full circular coverage. In such cases, two solutions can be applied.
UAVs with Internet Connectivity: If UAVs equipped with internet connectivity are available, there is no need for a BS-based formation. These UAVs can independently collect surveillance data and transfer it directly to the central server without relying on a base station.
UAVs without Internet Connectivity: For UAVs without internet connectivity, a relay communication protocol will be used to ensure efficient data transmission, as explained in Section 3.2.2. These UAVs will broadcast a request to locate the nearest UAV within a nearby transmission range. The nearest UAV can then collect the surveillance data from the out-of-range UAV and relay it to the BS. This approach allows the proposed system to extend its surveillance coverage, even in areas without direct BS access (as detailed in Section 3.3.2).
Fig 8 illustrates the relay scenario of the proposed model. The technical details of the relay model are discussed in the implementation section.
3.3.4 Scenario 4: Critical Point Surveillance (CPS) within BS Range
For critical point surveillance within the range of a base station (BS), UAVs without internet connectivity can still be used effectively. These UAVs can perform continuous surveillance at critical points, and if possible, they can use their perching capabilities to conserve energy. Among these, UAVs with perching and energy harvesting capability are the ideal choice, as they can both perch and charge, enabling extended surveillance without the need for frequent returns for recharging.
The primary advantage of this model is that it requires no additional movement for data transfer. However, if the UAVs are equipped with internet connectivity, they can directly transfer data to the central server rather than routing it through the BS. This reduces the load on the BS and maximizes data transfer efficiency. If the UAV’s battery level reaches a minimum threshold, it will return to the nearest BS or any available charging point to recharge before resuming its CPS duties. This system ensures that critical points are consistently monitored while maintaining operational efficiency for the UAVs.
3.3.5 Scenario 5: CPS outside BS Range
When performing Critical Point Surveillance (CPS) outside the range of a base station (BS), there are two possible conditions depending on the UAV’s connectivity and the availability of nearby UAVs.
UAVs with Internet Connectivity: If the UAVs are equipped with internet connectivity, they can maintain a direct connection to the central server for continuous data transfer. UAV with internet connectivity are suitable for this scenario, as they are capable of connecting directly to the server, enabling real-time data transmission without relying on the BS.
UAVs without Internet Connectivity: For UAVs without internet connectivity, if they are outside the BS coverage area, they can search for other UAVs within the BS range that can assist them. These UAVs can request data transfer assistance using the relay communication protocol described in Section 3.2.2. The nearest UAV inside the BS range will collect the data from the out-of-range UAV and relay it to the BS for further processing.
Both methods are suitable for real-time data communication, ensuring continuous surveillance in the absence of direct BS connectivity. However, if a UAV performing CPS cannot find a nearby UAV to assist or does not have internet connectivity, it must return to the nearest BS or charging point when its battery reaches a minimum threshold.
3.3.6 Scenario 6: Special Purpose UAVs
In this scenario, UAVs operate independently without internet connectivity, onboard unit (OBU) capabilities, or access to a base station (BS) or helper UAVs. These UAVs conduct surveillance on their own, making it essential for them to utilize perching and charging capabilities (if available) to maximize operational efficiency and prolong flight time.
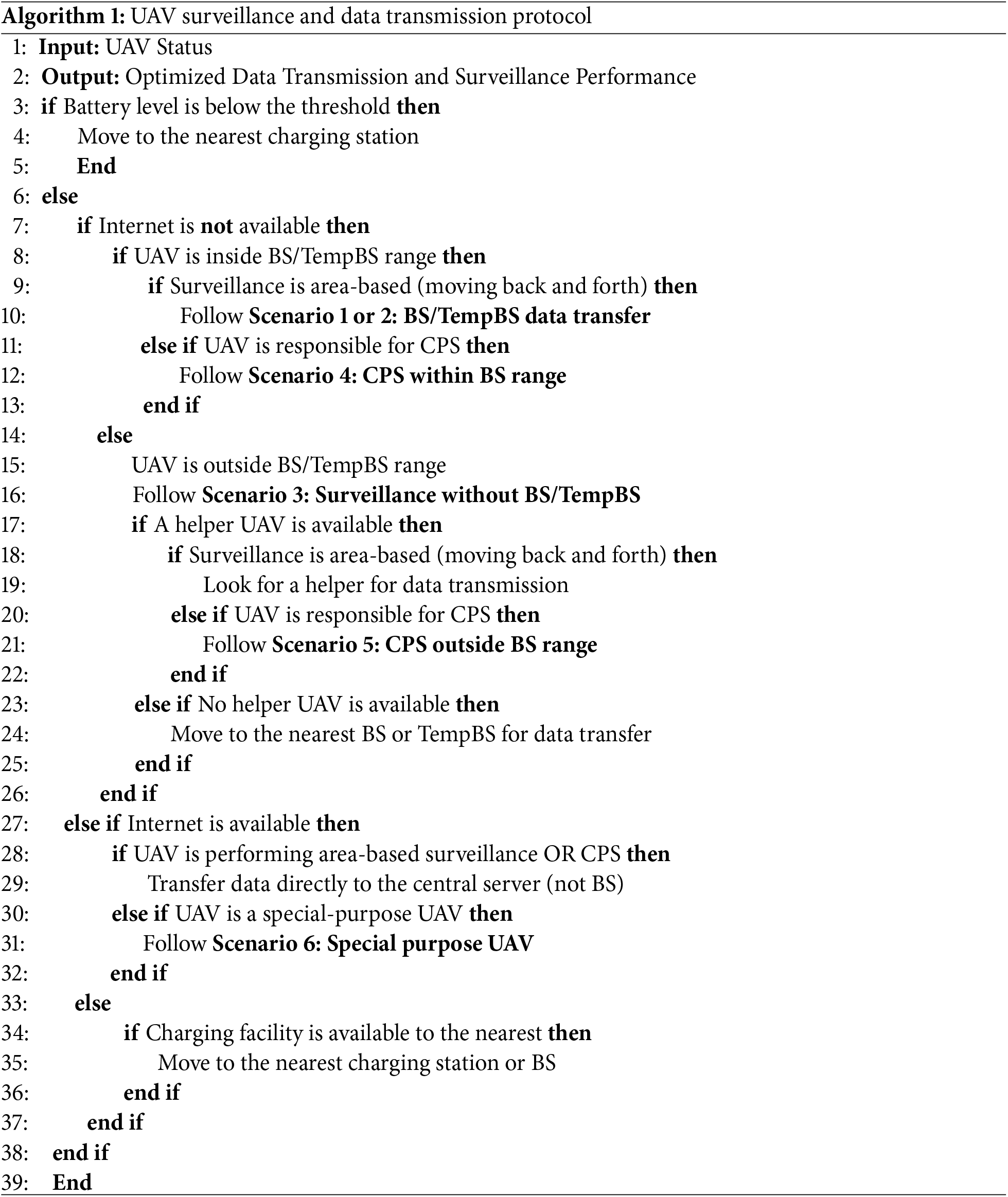
Given their limited connectivity and reliance on local energy resources, these UAVs will periodically need to travel to a location with internet access, such as a BS or temporary BS, in order to transfer the collected surveillance data for further analysis. To integrate all the discussed scenarios into a cohesive framework, a unified algorithm can be implemented for better understanding and management of operations in various contexts. Algorithm 1 outlines the steps for managing all the scenarios efficiently.
The proposed communication protocol ensures continuous and efficient surveillance by adapting to various operational scenarios based on UAV capabilities and network availability. By dynamically adjusting between BS-based communication, relay protocols, and temporary base stations, the system ensures optimal performance even in challenging environments. Additionally, the intelligent management of UAV resources, such as battery levels and energy conservation, guarantees prolonged operation and reliable data transmission, making it suitable for a wide range of surveillance applications.
4.1 UAV Selection and Specifications
The proposed model is designed to support a wide range of UAVs. As described in the system structure section, both basic UAVs equipped only with cameras and more advanced ones with features like internet connectivity, WiFi, perching, and charging capabilities can all participate in the system.
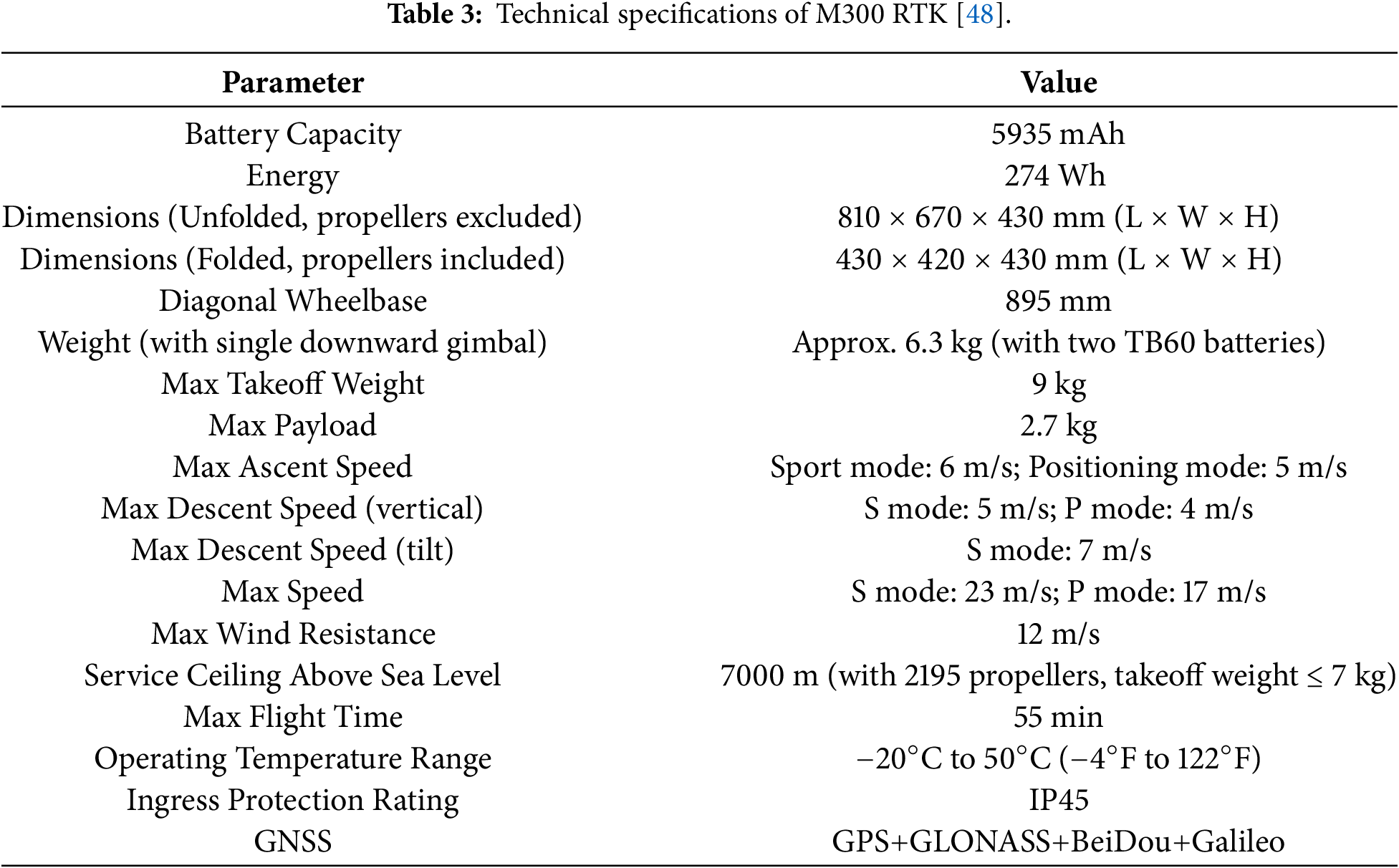
For our experimental analysis, we considered several popular UAV models currently available in the market. These include the DJI Phantom 4 Pro [44], Autel Robotics EVO II [45], Holy Stone HS720 [46], Parrot Anafi [47], and the DJI Matrice 300 RTK [48]. Among these, for our further experiments we have selected the DJI Matrice 300 RTK due to its specifications like maximum speed of 23 m/s, support of IEEE 802.11n (Wi-Fi 4) and IEEE 802.11ac (Wi-Fi 5). This enables fast data transfer of up to 1300 Mbps. Although the DJI Phantom 4 Pro and Autel Robotics EVO II support WiFi 5, they offer slightly lower data rates. In contrast, the Holy Stone HS720 and Parrot Anafi rely on the older IEEE 802.11n (WiFi 4) protocol, which limits their data transfer capabilities to 300 Mbps. Not only that, rather in terms of Maximum movement speed, battery capacity, energy ratings, flight time, etc., is considering the DJI Matrice 300 RTK performs better than others. These qualities make it perfect for the proposed surveillance system. Fig. 9 provides images of the UAVs, while Table 2 compares their specifications.

Figure 9: UAV Models.
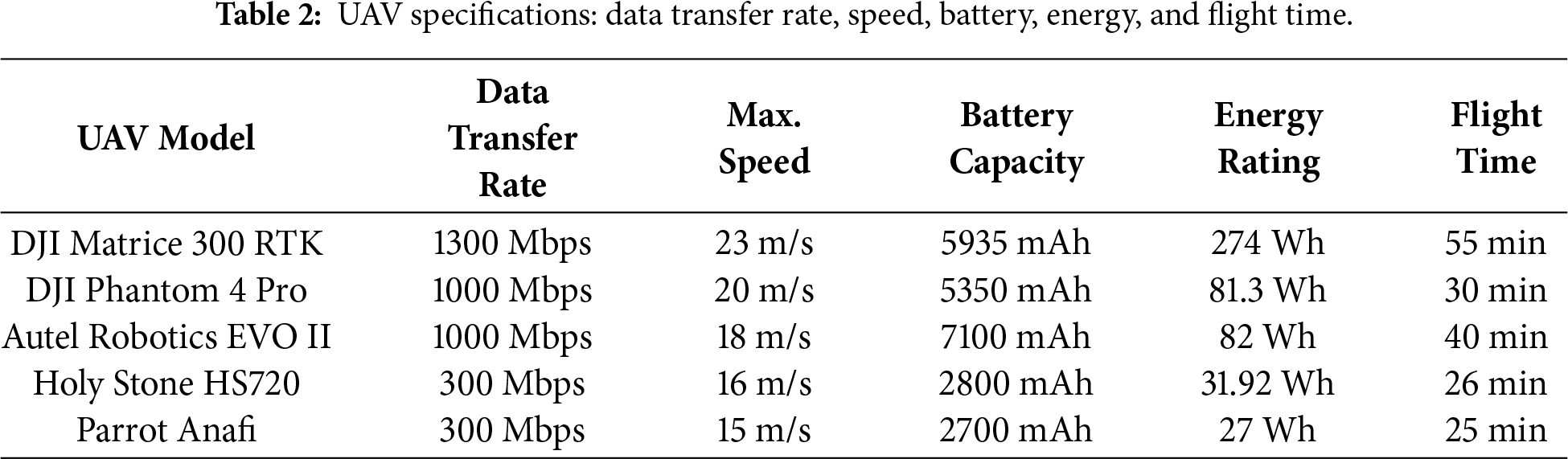
Table 3 summarizes the DJI Matrice 300 RTK (M300 RTK), an industrial-grade UAV with a 9 kg max takeoff weight and 2.7 kg payload capacity. It offers a 55-minute flight time (without payload) and supports various sensors for mapping, surveillance, and inspection. In Sport Mode (S Mode), it reaches speeds of 6 m/s ascent, 5 m/s descent, and 7 m/s tilt descent, while in Positioning Mode (P Mode), it focuses on stability with 5 m/s ascent and 4 m/s descent. The M300 RTK’s navigation system ensures precise positioning, with RTK-based accuracy of
In this evaluation, it is assumed that the UAV system maintains continuous operation over the mission period through a coordinated rotation with backup units. This assumption ensures that the steady-state throughput analysis remains independent of individual battery depletion cycles.
4.2 Performance of the Communication Systems
The performance of the proposed base station-supported communication model is largely influenced by its throughput compared to the traditional communication system. This section offers a detailed comparison between the proposed method and the traditional approach. Additionally, it explores the impact of different UAV models and their communication capabilities on overall throughput, highlighting how these factors contribute to the system’s efficiency.
4.2.1 Throughput Analysis: Proposed vs. Traditional System
The primary objective of the proposed method is to enhance communication efficiency by minimizing contention. To evaluate this, we compare the throughput of the proposed BS-surrounded system against a traditional contention-based MAC protocol. The normalized system throughput,
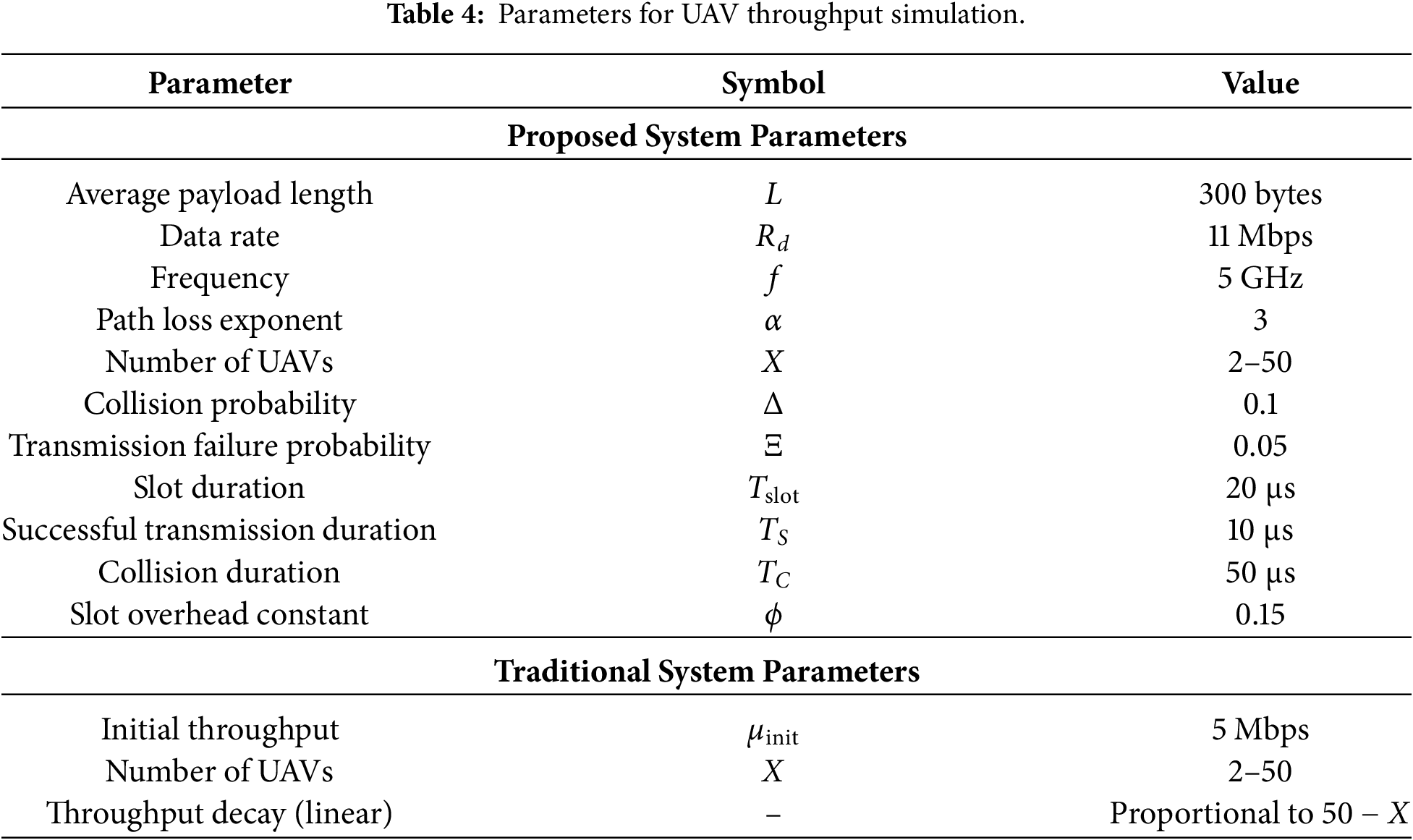
A. Traditional System Throughput
In a traditional ad-hoc network, all X nodes in the system contend for the same channel. The normalized throughput for the traditional system,
By defining
B. Proposed System Throughput
In contrast, the proposed BS-surrounded method enables higher efficiency by partitioning the network into clusters. For the
In our sectorized movement model, the probability of successful transmission
Since our system restricts
Finally, the total system throughput,
C. Comparison Analysis
Fig. 10 illustrates a comparison of the throughputs of the proposed system with the traditional system. In the traditional system, UAVs operate erratically, resulting in unstable connections and a significant packet loss rate caused by the UAVs’ unpredictable movements. Unpredictable motion leads to regular communication interruptions, making it difficult to maintain a reliable data transfer connection. In contrast, in the proposed system, UAVs follow a set pathway during their operational period, resulting in more consistent movement and reliable connections. Data transfer is not constant; it takes place only when the UAVs arrive in a specific transmission zone, where the signal strength is usually sufficient to reduce packet losses. This behavior is quantitatively reflected in the throughput performance. As shown in the simulation results, the traditional system suffers from a sharp decline in
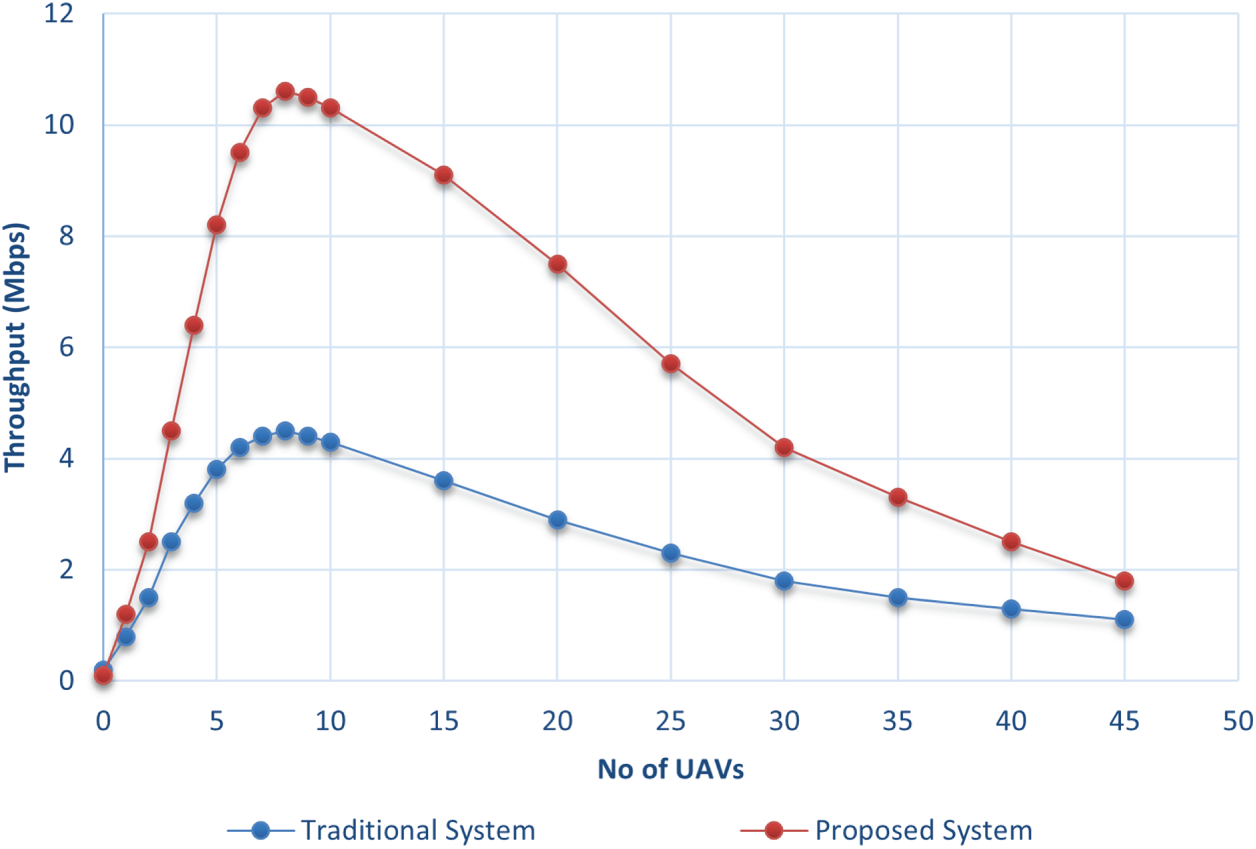
Figure 10: Throughput of the BS-based system vs. traditional communication protocol.
4.2.2 Throughput of Different UAVs
To compare the performance of the UAVs mentioned in Table 2, the experiment was performed under the same scenario. The results show that the DJI Matrice 300 RTK has the highest throughput among all the others. Even as the number of UAVs increases, their higher data transfer rates enable more efficient communication and reduced packet loss. The DJI Phantom 4 Pro and Autel Robotics EVO II produce good throughput, though slightly behind the Matrice 300 RTK. Meanwhile, the other UAVs show lower throughput values. These UAVs have comparatively lower data transfer rates, which likely results in less efficient data handling, particularly as the number of UAVs increases. The result is illustrated in Fig. 11.
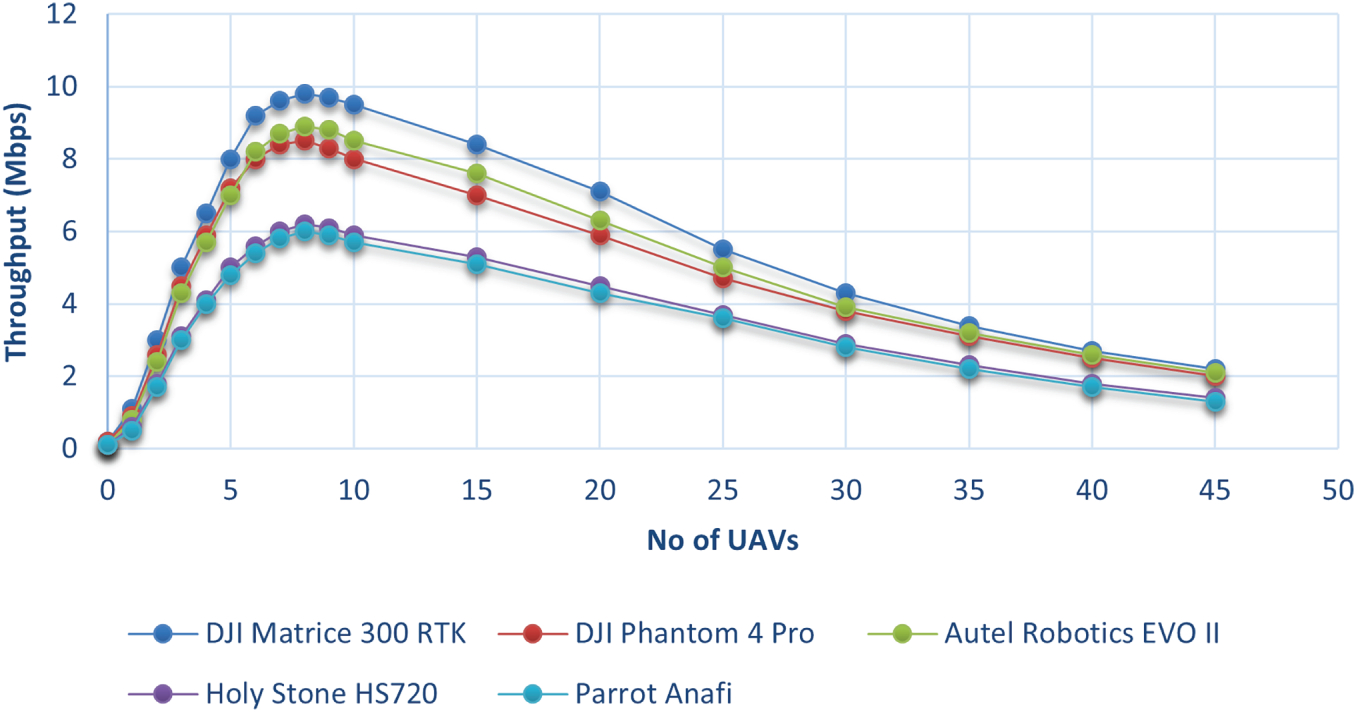
Figure 11: Throughput of different UAVs.
4.3 Energy Efficiency Analysis
A key objective of the proposed system is to maximize energy efficiency. To achieve this, all modules of the system are designed with energy conservation in mind. Moreover, the scenarios are carefully crafted to ensure that the UAVs are utilized in the most energy-efficient manner possible. In this section, we present a comparative analysis to demonstrate the level of energy efficiency that the proposed system can achieve.
4.3.1 Efficiency of the Communication Model
This paper proposes a BS-based communication model where UAVs follow a fixed path for surveillance, moving back and forth in a controlled manner. The energy efficiency of this proposed system is grounded in the physical relationship between power consumption and flight dynamics. For a UAV of mass
In contrast, UAVs that move randomly experience frequent and rapid changes in altitude, direction, and speed. These erratic movements force the motors to operate in high-torque regimes to overcome inertia, leading to significantly higher energy consumption. The mathematical model for remaining energy
where
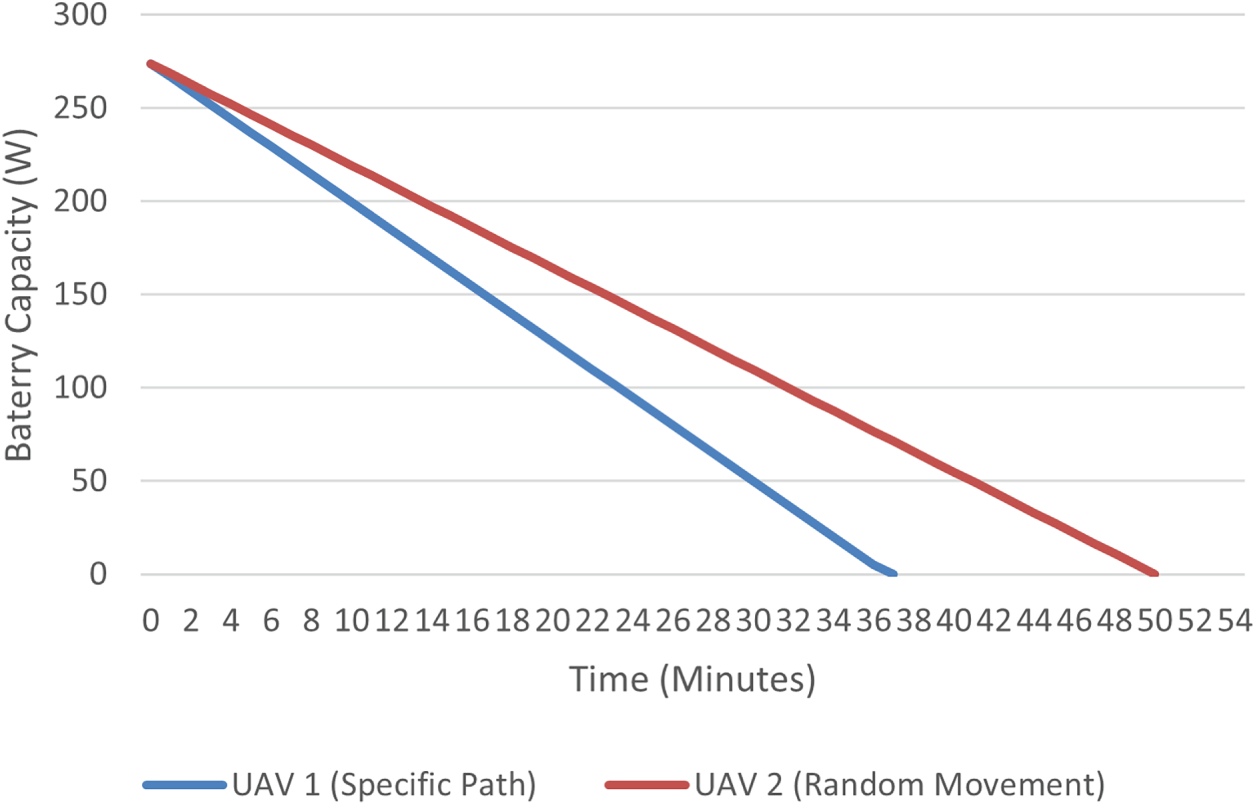
Figure 12: Energy consumption comparison of the DJI Matrice 300 RTK: Random movement (higher acceleration spikes) vs. Specific path movement (steady-state velocity).
Empirical tests conducted with a DJI Matrice 300 RTK confirmed this physical model. When following the specific, coordinated path, the battery reached its minimum threshold at the 50-min mark. Conversely, under random path movement, the battery was depleted in only 37 min due to the high inertial power penalties of erratic maneuvers. This data indicates that approximately 26% greater efficiency can be achieved with the proposed method, thereby directly extending the operational duration of the disaster response mission.
Furthermore, the relationship between data throughput and energy is managed by replacing active nodes with backup units once they reach the 15% energy threshold. This rotation strategy prevents the throughput degradation typically caused by low-power states or node failures, ensuring that the energy-efficient sectorized movement translates into long-term communication stability.
4.3.2 Energy Consumption Analysis
A comparison between four UAVs are presented in Fig. 13. UAV1 is flying while capturing video and transferring data, UAV2 is steady and capturing video, UAV3 is perching while capturing video and transferring data, and UAV4 is perching and charging while capturing video and transferring data. UAV4’s battery increases due to continuous charging. UAV1 and UAV2 run out of battery first.
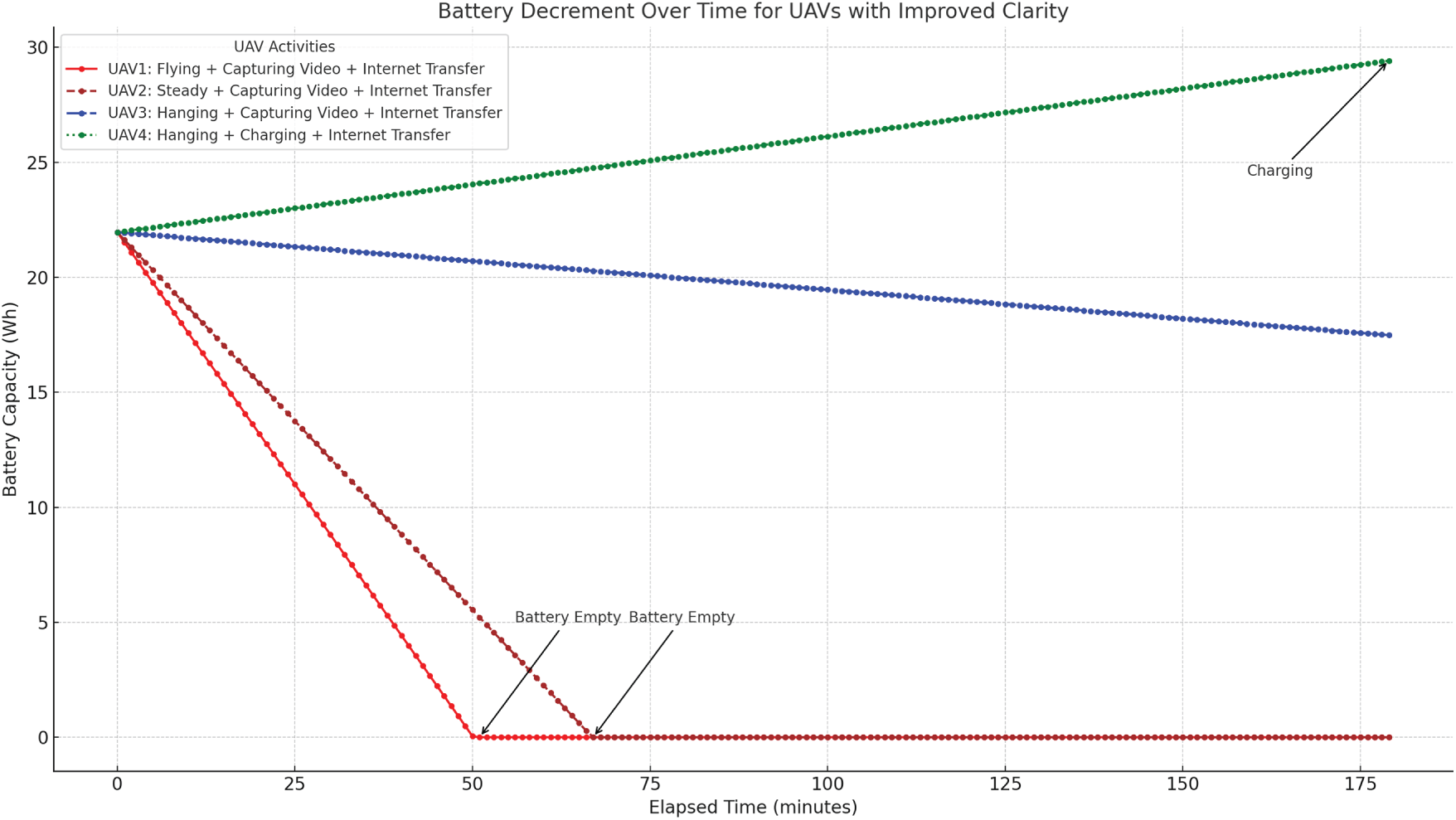
Figure 13: Battery decrement over time for UAVs with different activities.
Flying UAVs deplete battery fastest, while perching and charging ensures sustained operation. The energy consumption data demonstrates significant efficiency improvements due to perching and charging (illustrated in Fig. 14). While flying consumes 1500 W, perching reduces power consumption to only 10 W, achieving a 99.3% reduction in energy usage. Additionally, when perching is combined with charging, the energy balance becomes negative (e.g., −200 W for perching and charging), enabling continuous operation without battery depletion. Even with additional tasks like video capture and data transfer, the perching and charging mechanism sustains unlimited monitoring, making it far more efficient than hovering or flying, which are limited to 75 and 55 min, respectively. These results highlight that perching extends operational time dramatically, while perching with charging enables uninterrupted surveillance, overcoming energy constraints in UAV-based disaster monitoring.
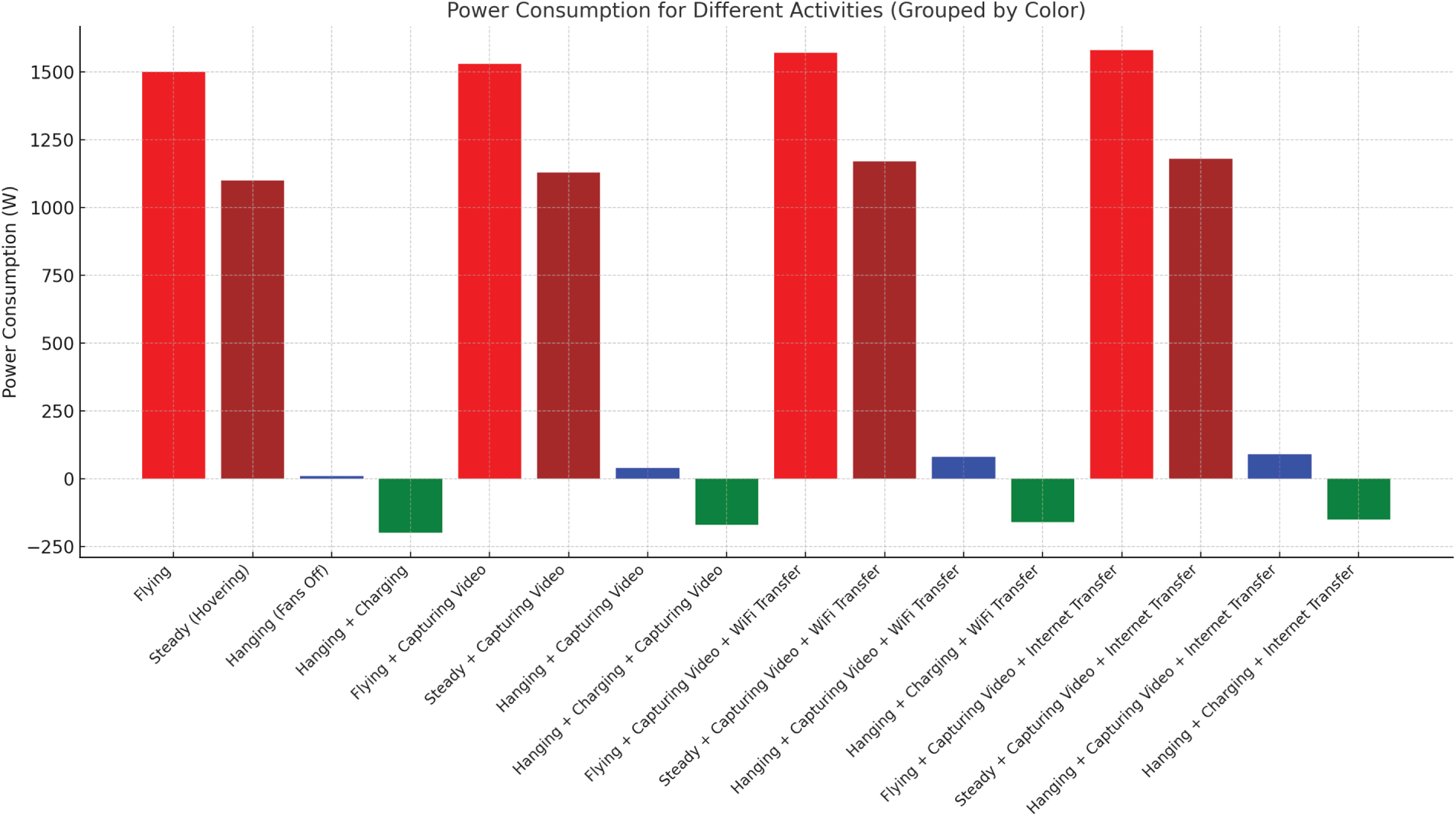
Figure 14: Energy consumption of Matrice 300RTK in different situations.
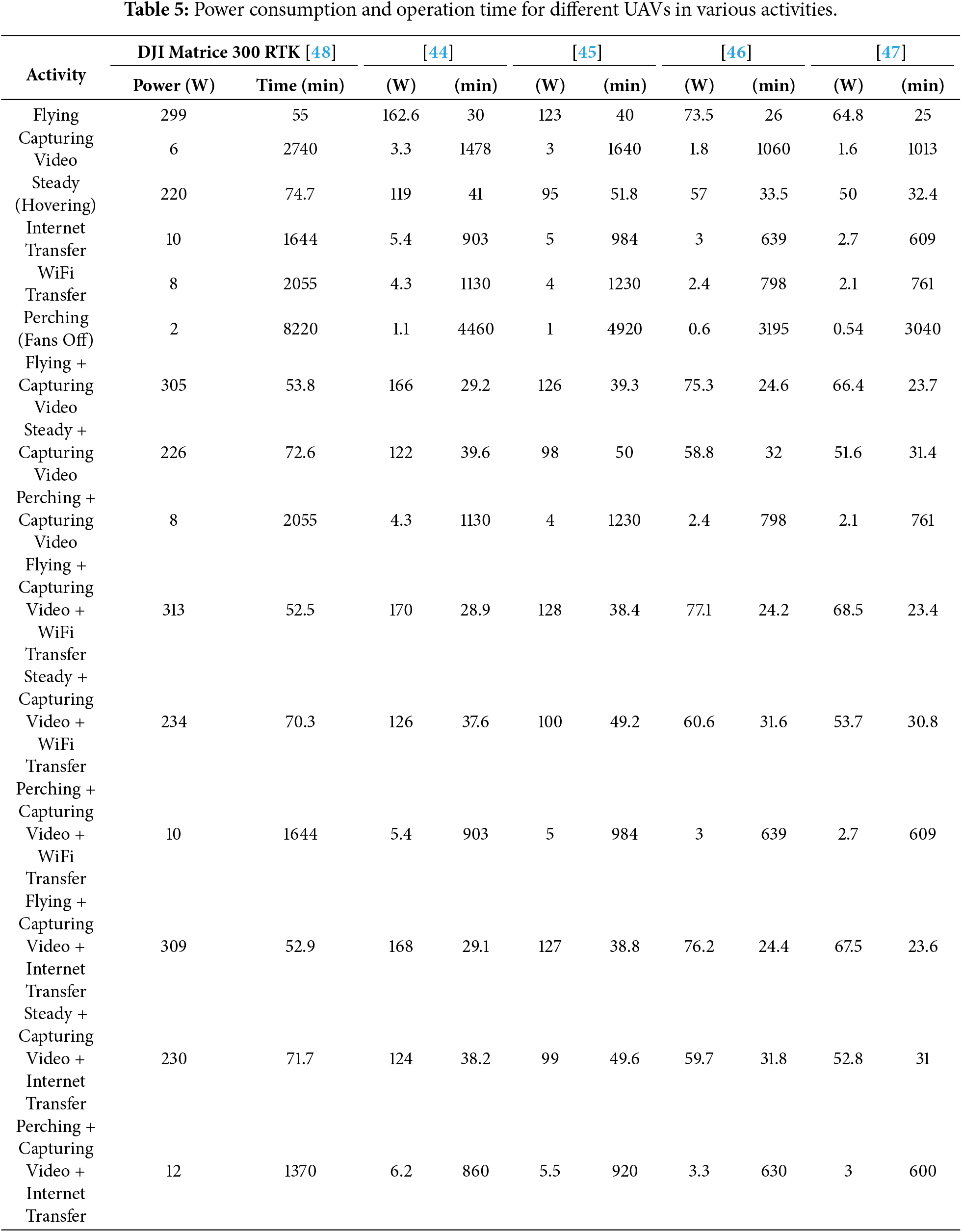
To compare the energy efficiency across various UAV models, Table 5 presents different power consumption scenarios for five distinct UAV models. The analysis demonstrates that the DJI Matrice 300 RTK outperforms the other UAVs by a significant margin.
This paper aims to provide an improved solution for UAV-based surveillance systems during natural disasters. It is designed to accommodate UAVs with both low and high capabilities, allowing them to effectively cope with various severe situations while ensuring efficient data transfer. Based on real-world disaster recovery experiences, six distinct scenarios are presented, each ensuring continuous surveillance and data transfer while minimizing resource usage and reducing energy consumption. UAVs, whether equipped with an On-Board Unit (OBU) and internet connectivity, can participate in the system. UAVs with higher capabilities, such as those serving as a TempBS (Temporary Base Station), can perform more complex tasks.
The system also proposes two scenarios to enhance the scalability of surveillance and data transfer: one utilizing relay communication and the other leveraging IoFT (Internet of Flying Things). To optimize UAV throughput, the system divides the area into eight zones and assigns UAVs to cover specific regions by moving back and forth rather than flying randomly. Furthermore, the system eliminates the need for continuous handshaking, unlike ad hoc networks. Experiments show that this approach reduces energy consumption by 26%. Throughput analysis indicates that the proposed method outperforms the traditional system. Additionally, the system incorporates UAVs with perching and wireless charging capabilities, extending surveillance operations by 99.3% for perching, and allowing continuous operation as long as charging is available.
In the future, the system will be tested with various communication protocols to identify the most effective one. It will also be evaluated with more advanced UAVs, equipped with capabilities such as automated human/object detection, thermal imaging, and heat sensing. Additionally, efforts will be made to reduce the processing time for captured video and image data, aiming to further enhance disaster recovery responses.
Acknowledgement: Not applicable.
Funding Statement: The author received no specific funding for this study.
Availability of Data and Materials: The author confirms that the data supporting the findings of this study are available within the article.
Ethics Approval: Not applicable.
Conflicts of Interest: The author declares no conflicts of interest.
References
1. Alotaibi J, Oubbati OS, Atiquzzaman M, Alromithy F, Altimania MR. Optimizing disaster response with UAV-mounted RIS and HAP-enabled edge computing in 6G networks. J Netw Comput Appl. 2025;241(4):104213. doi:10.1016/j.jnca.2025.104213. [Google Scholar] [CrossRef]
2. Hidalgo J, Baez AA. Natural disasters. Crit Care Clin. 2019;35(4):591–607. doi:10.1016/j.ccc.2019.05.001. [Google Scholar] [PubMed] [CrossRef]
3. Disaster Risk Reduction UNO. Types and impacts of natural disasters. 2024 [cited 2025 Feb 11]. Available from: https://www.undrr.org/. [Google Scholar]
4. Research on the Epidemiology of Disasters (CRED) C. Annual disaster statistical review: the numbers and trends. 2024 [cited 2025 Dec 11]. Available from: https://www.cred.be/publications. [Google Scholar]
5. Khan A, Gupta S, Gupta SK. Emerging UAV technology for disaster detection, mitigation, response, and preparedness. J Field Robot. 2022;39(6):905–55. doi:10.1002/rob.22075. [Google Scholar] [CrossRef]
6. Ahmad T, Morel A, Cheng N, Palaniappan K, Calyam P, Sun K, et al. Future UAV/drone systems for intelligent active surveillance and monitoring. ACM Comput Surv. 2025;58(2):1–37. doi:10.1145/3760389. [Google Scholar] [CrossRef]
7. Abdellatif AA, Elmancy A, Mohamed A, Massoud A, Lebda W, Naji KK. PDSR: efficient UAV deployment for swift and accurate post-disaster search and rescue. IEEE Int Things Mag. 2025;8(3):149–56. doi:10.1109/iotm.001.2400139. [Google Scholar] [CrossRef]
8. Chandran I, Vipin K. Multi-UAV networks for disaster monitoring: challenges and opportunities from a network perspective. Drone Syst Appl. 2024;12(5):1–28. doi:10.1139/dsa-2023-0079. [Google Scholar] [CrossRef]
9. Unlu E, Zenou E, Riviere N, Dupouy PE. An autonomous drone surveillance and tracking architecture. Electronic Imaging. 2019;31(15):1–7. doi:10.2352/issn.2470-1173.2019.15.avm-035. [Google Scholar] [CrossRef]
10. Kumar N, Ghosh M, Singhal C. UAV network for surveillance of inaccessible regions with zero blind spots. In: IEEE INFOCOM 2020-IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS). Piscataway, NJ, USA: IEEE; 2020. p. 1213–8. [Google Scholar]
11. Gupta H, Verma OP. Monitoring and surveillance of urban road traffic using low altitude drone images: a deep learning approach. Multimed Tools Appl. 2022;81(14):19683–703. doi:10.1007/s11042-021-11146-x. [Google Scholar] [CrossRef]
12. Adorni E, Rozhok A, Revetria R, Ivanov M. Literature review on drones used in the surveillance field. In: Proceedings of the International MultiConference of Engineers and Computer Scientists 2021 (IMECS 2021); 2021 Oct 20–22; Hong Kong, China; 2021. p. 20–2. [Google Scholar]
13. Srivastava A, Badal T, Saxena P, Vidyarthi A, Singh R. UAV surveillance for violence detection and individual identification. Autom Softw Eng. 2022;29(1):28. doi:10.1007/s10515-022-00323-3. [Google Scholar] [CrossRef]
14. Fang Z, Savkin AV. Strategies for optimized UAV surveillance in various tasks and scenarios: a review. Drones. 2024;8(5):193. doi:10.3390/drones8050193. [Google Scholar] [CrossRef]
15. Fan J, Lei L, Cai S, Shen G, Cao P, Zhang L. Area surveillance with low detection probability using UAV swarms. IEEE Trans Veh Technol. 2024;73(2):1736–52. doi:10.1109/tvt.2023.3318641. [Google Scholar] [CrossRef]
16. Auccahuasi W, Herrera L, Rojas K, Urbano K, Romero L, Lovera D, et al. Low-cost system for on-board image processing in real time, applied to disaster mitigation. In: AIP Conference Proceedings. Melville, NY, USA: AIP Publishing LLC; 2023. Vol. 2725. [Google Scholar]
17. Chen L, Song D, Zhang S. Research on multi UAVS task allocation method for post disaster emergency goods distribution. In: Journal of Physics: Conference Series. Vol. 2607. Bristol, UK: IOP Publishing; 2023. [Google Scholar]
18. Maiti M, Kayal P. Exploring innovative techniques for damage control during natural disasters. J Saf Sci Resil. 2024;5(2):147–55. doi:10.1016/j.jnlssr.2024.02.004. [Google Scholar] [CrossRef]
19. Iqbal U, Riaz MZB, Zhao J, Barthelemy J, Perez P. Drones for flood monitoring, mapping and detection: a bibliometric review. Drones. 2023;7(1):32. doi:10.3390/drones7010032. [Google Scholar] [CrossRef]
20. Ishiwatari M. Leveraging drones for effective disaster management: a comprehensive analysis of the 2024 Noto Peninsula earthquake case in Japan. Prog Disast Sci. 2024;23(1):100348. doi:10.1016/j.pdisas.2024.100348. [Google Scholar] [CrossRef]
21. Emad Alfaris R, Vafakhah Z, Jalayer M. Application of drones in humanitarian relief: a review of state of art and recent advances and recommendations. Transp Res Rec. 2024;2678(7):689–705. doi:10.1177/03611981231209033. [Google Scholar] [CrossRef]
22. Krichen M, Abdalzaher MS. Advances in AI and drone-based natural disaster management: a survey. In: 2023 20th ACS/IEEE International Conference on Computer Systems and Applications (AICCSA). Piscataway, NJ, USA: IEEE; 2023. p. 1–6. [Google Scholar]
23. Narendran R, Vinesh T, Cheong SH, Yee HX. Aerial drones for fire disaster response. In: Drones-various applications. London, UK: IntechOpen; 2023. p. 1–15. [Google Scholar]
24. Singh R, Manoharan G, Singh S. Strategic deployment of AI and drones enhancing disaster management in natural disasters. In: AI and IoT for proactive disaster management. Hershey, PA, USA: IGI Global; 2024. p. 172–203. [Google Scholar]
25. Alawad W, Halima NB, Aziz L. An unmanned aerial vehicle (UAV) system for disaster and crisis management in smart cities. Electronics. 2023;12(4):1051. doi:10.3390/electronics12041051. [Google Scholar] [CrossRef]
26. Sowmya V, Janani AS, Hussain SM, Aashica A, Arvindh S. Creating a resilient solution: innovating an emergency response drone for natural disasters. In: 2024 10th International Conference on Communication and Signal Processing (ICCSP). Piscataway, NJ, USA: IEEE; 2024. p. 344–8. [Google Scholar]
27. Daud SMSM, Yusof MYPM, Heo CC, Khoo LS, Singh MKC, Mahmood MS, et al. Applications of drone in disaster management: a scoping review. Sci Justice. 2022;62(1):30–42. doi:10.1016/j.scijus.2021.11.002. [Google Scholar] [PubMed] [CrossRef]
28. Muñoz M, Torres M, Gil J, Guzmán J. An Internet of Things platform for heterogeneous data integration: methodology and application examples. J Netw Comput Appl. 2025;240(7):104197. doi:10.1016/j.jnca.2025.104197. [Google Scholar] [CrossRef]
29. Jin Y, Qian Z, Yang W. UAV cluster-based video surveillance system optimization in heterogeneous communication of smart cities. IEEE Access. 2020;8:55654–64. doi:10.1109/access.2020.2981647. [Google Scholar] [CrossRef]
30. Wu J, Zou L, Zhao L, Al-Dubai A, Mackenzie L, Min G. A multi-UAV clustering strategy for reducing insecure communication range. Comput Netw. 2019;158(2):132–42. doi:10.1016/j.comnet.2019.04.028. [Google Scholar] [CrossRef]
31. Mehmood A, Iqbal Z, Shah AA, Maple C, Lloret J. An intelligent cluster-based communication system for multi-unmanned aerial vehicles for searching and rescuing. Electronics. 2023;12(3):607. doi:10.3390/electronics12030607. [Google Scholar] [CrossRef]
32. Khayat G, Mavromoustakis CX, Pitsillides A, Batalla JM, Markakis EK, Mastorakis G. On the weighted cluster S-UAV scheme using latency-oriented trust. IEEE Access. 2023;11:56310–23. doi:10.1109/access.2023.3282441. [Google Scholar] [CrossRef]
33. Su Z, Li C, Chen W. A non-stationary cluster-based channel model for low-altitude unmanned-aerial-vehicle-to-vehicle communications. Drones. 2023;7(10):640. doi:10.3390/drones7100640. [Google Scholar] [CrossRef]
34. Wu H, Tao X, Zhang N, Shen X. Cooperative UAV cluster-assisted terrestrial cellular networks for ubiquitous coverage. IEEE J Sel Areas Commun. 2018;36(9):2045–58. doi:10.1109/jsac.2018.2864418. [Google Scholar] [CrossRef]
35. Goel N, Gupta V. Drone-assisted-cooperation for multi-cluster disaster scenario in next generation wireless communication. Wirel Pers Commun. 2024;135(3):1679–99. doi:10.1007/s11277-024-11141-z. [Google Scholar] [CrossRef]
36. Lu Z, Wu G, Zhou F, Wu Q. Intelligently joint task assignment and trajectory planning for UAV cluster with limited communication. IEEE Trans Veh Technol. 2024;73(9):13122–37. doi:10.1109/tvt.2024.3390221. [Google Scholar] [CrossRef]
37. Swain S, Khilar PM, Senapati BR. A reinforcement learning-based cluster routing scheme with dynamic path planning for mutli-uav network. Veh Commun. 2023;41(3):100605. doi:10.1016/j.vehcom.2023.100605. [Google Scholar] [CrossRef]
38. Wang X, Jiao H, Gao Q, Wu Y, Jing T, Qian J. Trajectory optimization for maximization of energy efficiency with dynamic cluster and wireless power for UAV-assisted maritime communication. IET Commun. 2024;18(6):409–20. doi:10.1049/cmu2.12742. [Google Scholar] [CrossRef]
39. Wei J, Guo Y, Wang H, Gu J, Liu J, Ding G. Cognitive jamming-aided UAV multi-user covert communication. IEEE J Sel Areas Commun. 2025. doi:10.1109/jsac.2025.3639012. [Google Scholar] [CrossRef]
40. Zhao W, Zhang J, Li D. Clustering and beamwidth optimization for UAV-assisted wireless communication. Sensors. 2023;23(23):9614. doi:10.3390/s23239614. [Google Scholar] [PubMed] [CrossRef]
41. Haber T. Kahramanmaras’ta Enkaz Kaldirma Çalismalari 19 Mahallede Devam Edecek. 2025 [cited 2025 May 23]. Available from: https://www.trthaber.com/haber/turkiye/kahramanmarasta-enkaz-kaldirma-calismalari-19-mahallede-devam-edecek-757856.html. [Google Scholar]
42. IEEE 802.11 RTS/CTS. Wikipedia, the free encyclopedia. 2024 [cited 2025 Nov 27]. Available from: https://en.wikipedia.org/wiki/IEEE_802.11_RTS/CTS. [Google Scholar]
43. IEEE 802.11p. Wikipedia, the free Encyclopedia. 2024 [cited 2025 Nov 27]. Available from: https://en.wikipedia.org/wiki/IEEE_802.11p. [Google Scholar]
44. DJI. Phantom 4 Pro—specifications, FAQs, videos, tutorials. 2025 [cited 2025 Feb 3]. Available from: https://www.dji.com/global/support/product/phantom-4-pro. [Google Scholar]
45. Robotics A. Autel EVO II series. 2025 [cited 2025 Feb 3]. Available from: https://shop.autelrobotics.com/collections/autel-evo-ii-series. [Google Scholar]
46. Stone H. HS720 GPS starter drone for outdoor. 2025 [cited 2025 Feb 3]. Available from: https://www.holystone.com/en/Drones/Premium/HS720.html. [Google Scholar]
47. Parrot. ANAFI—the flying 4K HDR camera that you can take with you everywhere. 2025 [cited 2025 Feb 3]. Available from: https://www.parrot.com/en/drones/anafi. [Google Scholar]
48. DJI. Matrice 300 RTK—specifications, FAQs, videos, tutorials. 2025 [cited 2025 Feb 3]. Available from: https://www.dji.com/global/support/product/matrice-300. [Google Scholar]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF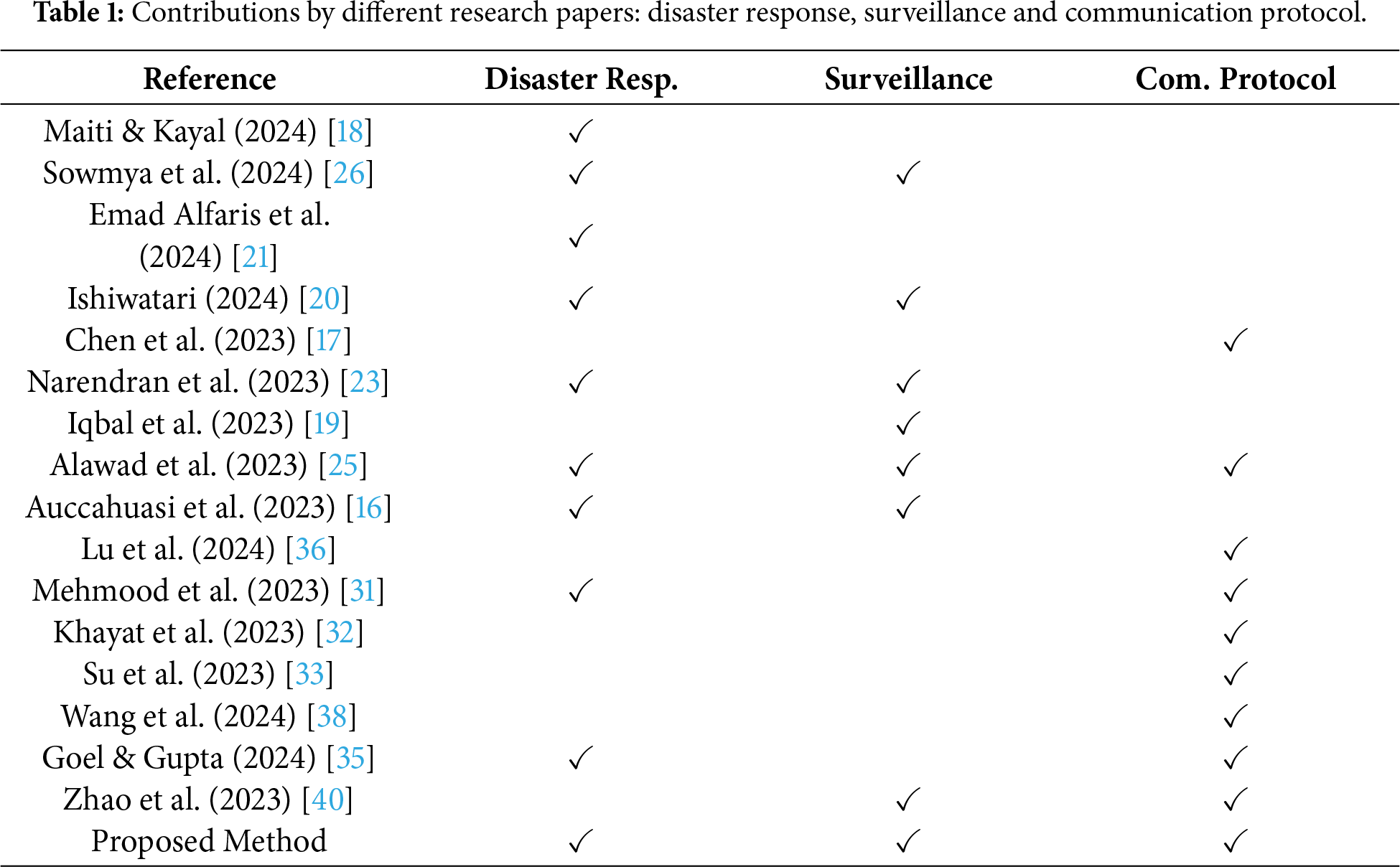
 Downloads
Downloads
 Citation Tools
Citation Tools