 Open Access
Open Access
ARTICLE
Trust and QoS-Driven Query Service Provisioning Using Optimization
1 Department of Computer Science and Engineering, SRM Institute of Engineering and Technology, Ramapuram, Chennai, India
2 Department of Information Technology, Coimbatore Institute of Technology, Coimbatore, India
* Corresponding Author: K. Narmatha. Email:
Intelligent Automation & Soft Computing 2023, 36(2), 1827-1844. https://doi.org/10.32604/iasc.2023.028473
Received 11 February 2022; Accepted 24 June 2022; Issue published 05 January 2023
Abstract
The growing advancements with the Internet of Things (IoT) devices handle an enormous amount of data collected from various applications like healthcare, vehicle-based communication, and smart city. This research analyses cloud-based privacy preservation over the smart city based on query computation. However, there is a lack of resources to handle the incoming data and maintain them with higher privacy and security. Therefore, a solution based idea needs to be proposed to preserve the IoT data to set an innovative city environment. A querying service model is proposed to handle the incoming data collected from various environments as the data is not so trusted and highly sensitive towards vulnerability. If handling privacy, other inter-connected metrics like efficiency are also essential, which must be considered to fulfil the privacy requirements. Therefore, this work provides a query-based service model and clusters the query to measure the relevance of frequently generated queries. Here, a Bag of Query (BoQ) model is designed to collect the query from various sources. Validation is done with a descriptive service provisioning model to cluster the query and extract the query’s summary to get the final results. The processed data is preserved over the cloud storage system and optimized using an improved Grey Wolf Optimizer (GWO). It is used to attain global and local solutions regarding privacy preservation. The iterative data is evaluated without any over-fitting issues and computational complexity due to the tremendous data handling process. Based on this analysis, metrics like privacy, efficiency, computational complexity, the error rate is analyzed. The simulation is done with a MATLAB 2020a environment. The proposed model gives a better trade-off in contrast to existing approaches.Keywords
Internet of Things (IoT) is a platform that links the physical world and cyber world. This IoT technique makes the user gather information through sensors from the physical world to run queries regarding the collected data [1] and analyze the system’s performance. Various convenient methods are suggested, such as DeepDirect to bind the direction of learning [2] to monitor the data and examine it in shared circumstances. The IoT architecture called Multi-access Edge Computing (MEC) [3] emerges to comprise the edge servers. Contrary, MEC techniques perform complex computation and pose huge storage sources from the physical world than the conventional IoT techniques. This work proposed to address the problem of query processing in the recent IoT techniques. One of the essential tasks in the traditional IoT techniques is query processing, such as Wireless Sensor Networks (WSNs). The method has various current tasks [4].
There are two essential procedures: distributed strategy and centralized strategy in query processing for WSNs. Queries are processed with the help of cooperative sensor nodes in the distribution strategy. In contrast, all the sensed data are sent to cloud, responsible for query processing in the centralized system. Moreover, in the new IoT techniques, query processing is more complicated, and the mentioned query processing strategies are not helpful because of the below two difficulties. They are (i) voluminous sensed data [5]. Based on Cisco’s report [6], 31 billion connected IoT devices will be there at the end of 2020, and there are 75 billion devices will be available at the end of 2025. IoT devices provides huge amount of sensed data and process the query which leads to complex calculation and data transferring complexity. Data transmission is gradual, and the calculation workload will burden the cloud or sinks. Hence, the centralized strategy is not suited in wireless sensor networks. (ii) Complex Queries–The existing system made an attempt in query processing in the shared fashion in wireless sensor networks like range query, curve query, and top-k query [7]. Moreover, the queries are more complicated than those used in the conventional wireless sensor networks in the latest IoT techniques. The data is preprocessed through the sequence of services, including speech recognition, image processing, integration of data, and a node can deploy the AI model to answer the query in the new IoT technique and process the services in the data processing. For instance, if a user selects a vehicle’s license number that moves faster, the vehicles’ speed data can sort to attain the fast vehicle and recognize the vehicles’ image data to achieve the license number. The outcomes of mentioned two stages have to join to reach the outcome [8]. Moreover, the services mentioned earlier in data processing cannot be able to carry out at every sensor node since the sensor nodes have restricted calculation in wireless sensor networks, energy, and storage resources. It makes wireless sensor networks unable to process complicated queries in a shared fashion. Henceforth, the distribution strategy is not suited in wireless sensor networks.
Considering Edge Assisted IoT Data Monitoring System (EDMS) to process complicated queries in the new IoT technique (See Fig. 1). This EDMS can deploy to observe the security, traffic, environment change, and so on. However, EDMS can deploy to monitor the industrial parameters in the big factory. Fig. 1 represents the overview of EDMS [9]. The sensed data are gathered from various sources and are deposited in the shared fashion where the edge servers are linked with the remote cloud. It is used to translate the query into a sequence of services in data processing like information integration, image processing, top-k query processing, etc. These services are cached at the edge server in the data processing. It creates a plan for the query and allocates the work to a few edge servers if the query comes nearer to the cloud. The voluminous sensed data and complex queries should be processed in the shared fashion; since the edge servers require more storage resources and more calculation. In EDMS, the distributed query processing can better utilize resources and minimize the transmission and cost of computation [10]. Query processing is still tricky in heterogeneous system with various servers with multiple calculations and abilities in communication. Further, every query is interconnected in the data processing services, and the result of one service may be the input of other benefits. Henceforth, the unnecessary response latency is raised due to an improper query plan. This work investigates how to create a plan for query to boost the response delay of query in the EDMS. It is the first study examining query processing as per our knowledge. The benefaction of this work is described below.
■ To model a query service mechanism for the IoT-based data monitoring system and to establish privacy of the network model;
■ To analyze the trust and query service using a meta-heuristic optimization approach. Here, Gray Wolf Optimization (GWO) approach is adopted for managing the query service;
■ To simulate the performance of the anticipated model over MATLAB 2020a simulation environment and compare the performance with various existing approaches.

Figure 1: IoT data edge monitoring system
The work is structured as: Section 2 gives a comprehensive analysis of various existing approaches and discusses the pros and cons of the prevailing models. Section 3 gives the detailed analysis of the anticipated model in query processing, Quality of Service (QoS)-aware heuristic model and privacy to the network model. In Section 4, the numerical outcomes of the work are provided with graphical representation and work summary in Section 5.
The IoT technique has distinguished the state of data processing and collection. The gathered data has the Spatio-temporal context to perform an essential part in processing any analytics outcome and aligns the decision-making with two aspects [11]. The difficulties found that need to serve in the domain with data management effectively and the number of devices. A group of attempts disclose the chances for the distributed data management or distributed nodes’ management available in IoT. The identification of nodes is focused efficiently based on the request depending on the static criterion that explains the nodes or the data themselves [12]. The difficulty is obtaining a glance at the characteristics of nodes and the available data’s statistics. Moreover, edge nodes and IoT have revealed the various hardware and software features (for example, middleware). The researcher suggests a Distributed Data Service (DDS) that supports collecting and processing data [13]. This primary goal is to enable various and different IoT middleware systems to allocate the data services in common to cover the interoperability problems.
The execution of queries in parallel enhances the processing speed. It can efficiently distribute the application. Moreover, the data is partitioned to realize the parallel execution in the provided network environment. l. This setting is the typical scenario if considering the nodes or edge infrastructure. Multiple attempts are carried out to provide the separation algorithms of data over the top of batches or streams. The authors choose a sliding window technique [14]. Streams are divided on the fly by considering the query semantics. It proposes a multi-route optimizer and uses inter-stream and intra-stream correlation to generate the partitions efficiently. The authors present the separations of streams into a group of sub-streams on the operators of queries implemented in parallel. The group of properties are used to characterize the suggested partitioning functions that are structural properties (for example. Fast lookup, compactness), balance properties (for example, Processing, memory and communication), and adaptation properties (for example, Low migration, fast calculation).
The process of deploying the calculation and storage resources nearer to the mobile device or user by the MEC [15] helps to release the pressure on the workload of the cloud. Sensed data sent from the devices to the servers to analyze further. The authors in [16,17] examine the offloading issue and one mobile device and one MEC server. Some studies [18,19] discuss the offloading task issue in a MEC system with mobile devices and one MEC server. Few studies are concerned about the placement of service and the request routing issues. The authors aim to examine how to move or place the edge services to minimize latency response in in-service placement [20]. The request routing issue examines the user’s sending process and requests to suitable edge servers to enhance performance. Moreover, no works are mentioned about processing queries at edge servers.
The Directed Acyclic Graph (DAG) represents relationships among services. The author utilizes a directed edge in this paper to present the dependence among two services or two tasks. Every directed edge
The author [24] investigated the QoS parameters used for selection and service composition by evaluating some QoS parameters over the application layer: response time, execution time, reliability, cost, price, throughput, latency, and reputation. Moreover, the author does not discuss methods or techniques utilized to resolve the selection issues. The author performed the systematic analysis of SSA over the IoT environment which is classified as hybrid, decentralized and centralized classes. The author concentrates on some techniques to resolve the selection issue and QoS parameters used to evaluate the disadvantages and advantages of every algorithm. The author predicts the most influencing and challenging issues in the selection process over IoT environment.
The author [25] proposed a classification process to fulfil the IoT requirements and facilitates optimization over the various IoT layers. The proposed architecture composed of three layers like application, network and sensor layers. The conventional QoS attributes are merged with various IoT architectural characteristics, i.e., network cost, coverage, energy consumption, information accuracy and network deployment. The conventional QoS classification is not suitable to the complexity and heterogeneity of the IoT architecture. The sensor layer specifies the physical IoT infra-structure comprising of various edge nodes link like RFID tags, data centres, mobile devices, sensor networks and other heterogeneous devices. The layers perform sensing process as independent services and facilitates IoT environment to offer sensing and actuating abilities modelled as services with edge-node services via the cloud computing system. The QoS related layers include the sensor selection with essential infra-structure based on application/user requirements and sensing abilities. Therefore, this layers attempts to handle the scheduling and resource allocation process. For instance, the QoS in sensor layers include system lifetime, energy consumption and resource optimization. The SSA optimization is essential for QoS optimization for various sensor services. An optimal SSA is essential for sensor layer as multiple devices are suitable with some variation in quality that fulfils the application and user requirements. The service availability with these layers describes the failure or success of service request [25,26].
Data Monitoring System in IoT is depicted in Fig. 1. This system evolves the three main elements. They are (i) a network comprised of servers
The sensed data are gathered at the edge servers in a shared fashion. The gathered sensed data are the collected raw data from various sources like microphones, sensors, cameras, etc. Some preprocessing steps are carried out by the data like data integration, data sorting, speech recognition, image processing, and so on to validate query processing [27–30]. Moreover, if processing the queries in the cloud, complete sensed data needs to gather that will consume time, involves complex processing queries that will consume resources. A data query is considered the sequence of data processing tasks in this scenario due to the services in data processing located at edge servers. Then, processing the queries in a shared manner minimizes the query response latency and mitigate the cloud’s workload. [31,32]
Suppose that data sources D types are available in the monitored region like the surveillance cameras gives image data, temperature sensors provide temperature data, speed detectors gives speed data, etc. The sensed data created in the monitored region denotes
The remote cloud and the edge servers interface using a backbone network. The communication among the cloud and edge servers are more decelerated (without loss of generality). For every link
The remote cloud and edge servers give various data processing services like data integration, speech recognition, and image processing for processing the sensed data. Suppose F denotes the universal set of services. For every
The computing resources are required that are noticed by
and the connectivity among
where
This phase is composed of communication direction initiated from the user to Cluster Head (CH) via the sensing server (SS). It includes two messages: message from the user to SS and SS to CH. The first protocol message is designed on the user side and delivered to the SS. The query is encrypted with global public key
The essential factor while determining the actual protocol messages is any sort of key (asymmetric or symmetric) to the query responder (sensing device), i.e., the initiator is unauthenticated. The query responder has a public and global public key. Thus, initiator uses the public key to set some secure channel for response with the encryption of random key K with the public key over the sensing platform (query Q). Thus, the message protocol known as
It possesses the decryption and query delivery of the actual recipient and the user response. Here, the
The output m is parsed as the original query Q and response key

Figure 2: Flow diagram of proposed model
The SS cannot acquire information from content analysis; however, it needs statistical analysis. In the query privacy phase, the sensing server needs to learn the external colluders where the user generates a query to the connected nodes k to the query response. When k is larger sufficiently, query privacy is fulfilled with the mapping and
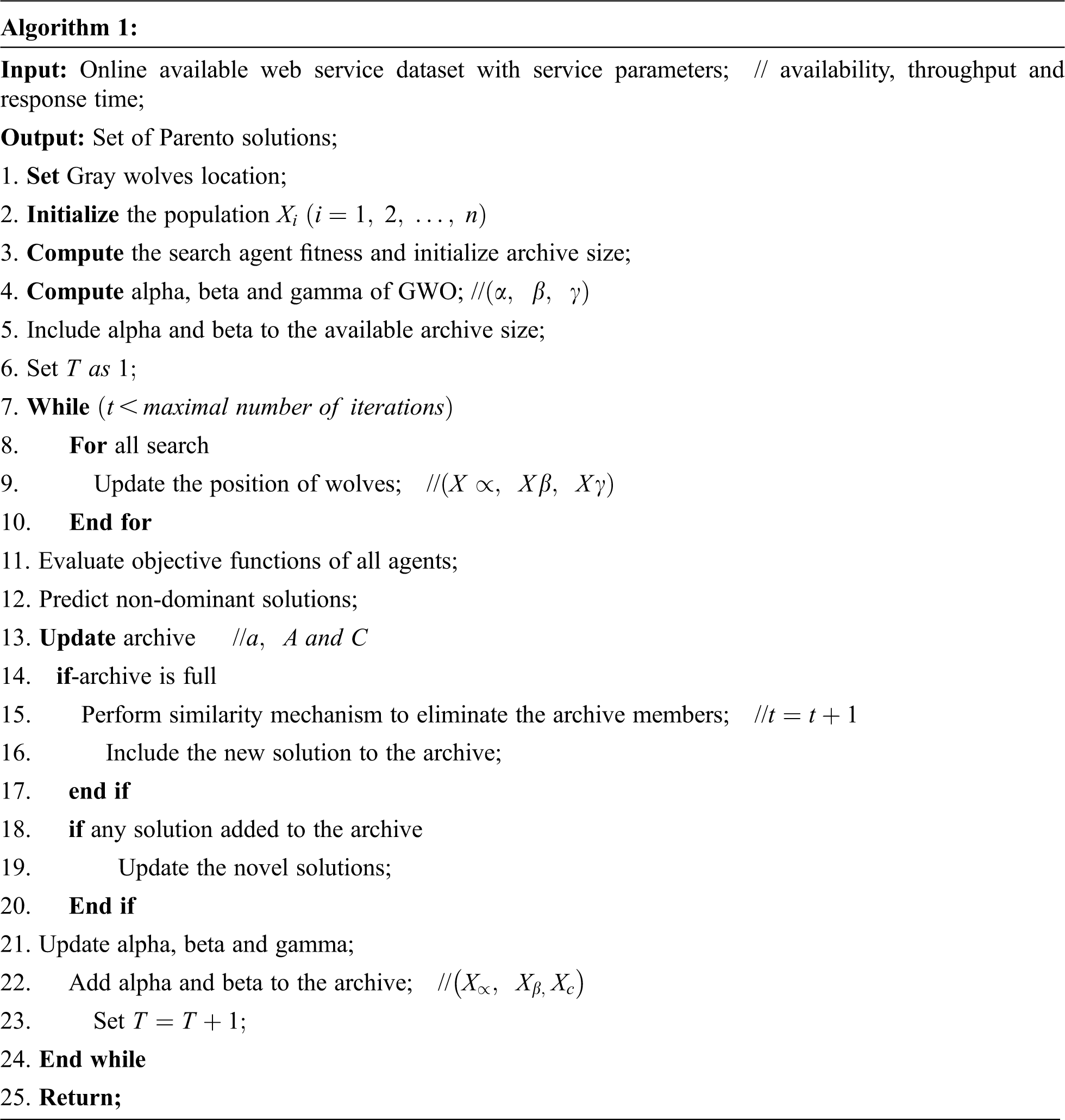
Here, Grey-wolf Optimizer is applicable for the IoT environment to establish privacy, QoS-aware trust service using two diverse mechanisms. They are storage analysis with Parento solution and Parento archive. The former provides a novel solution to control one or more IoT files, and the dominative or redundant incoming data is eliminated. Therefore, a new solution is offered to the archive. When the generated new solution and k-archive members are not dominated, the new solution is added to the archive. Similarly, when the archive is complete, the similarity among the dominative schemes is computed with the Euclidean distance with the prediction of two or more methods with only similarity and eliminating one amongst them. The similarity of the new solution is lesser to enhance the diversity of the final approximation. While the latter mechanism provides a unique solution in all iterations; therefore, it is essential to use the Parento archive to store the Parento solution. When the number of Parento solutions exceeds the number of services, it specifies the archive size, and the archive is clipped based on the crowding distance. Thus, it leads to an NP-hard problem.
The QoS-aware trust establishment in IoT is quantified based on the individual grey wolf and the prey in the multi-objective grey wolf, where the location corresponds to the service coordination scheme. The leader wolf role is to control the direction of grey wolves motion. Thus, it increases service coordination by fulfilling the service requirements and provides optimal solutions finally.
4 Numerical Results and Discussion
This section describes the performance evaluation of the suggested algorithm using extensive simulations. The execution of the proposed algorithms on various situations has been carried out in a MATLAB simulation environment. The multiple edge servers differ from 5 to 30. Let C denote the average capability of edge server computation. The C value is assumed with the domain of [10, 40 GHz]. The edge server capability calculation is assigned in a random way based on average value C. Further, the analysis on the cloud capability

Figure 3: Node creation

Figure 4: Cluster formation

Figure 5: Node connectivity

Figure 6: Distance measure from source to CH = 5.0921

Figure 7: Distance measure from source to CH = 52.352
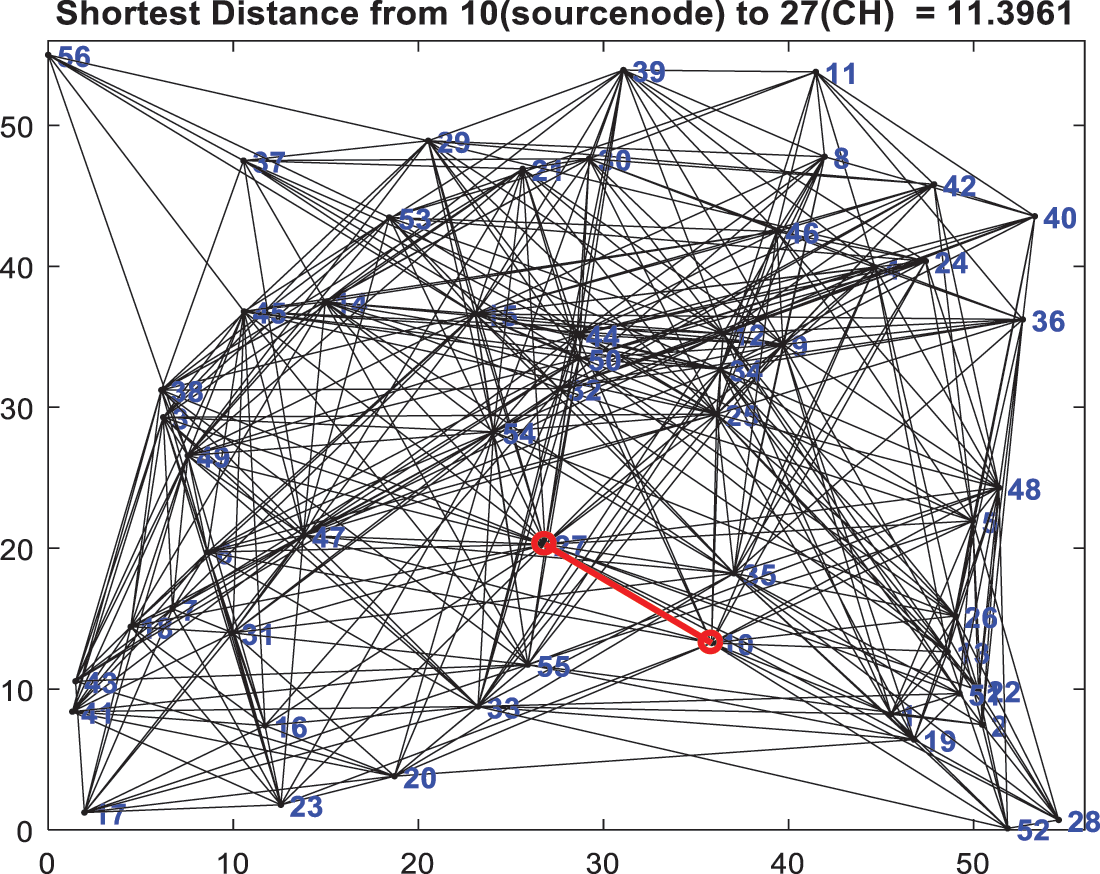
Figure 8: Distance measure from source to CH = 11.3961
This work creates the various criteria in the set of simulations and differ the multiple servers (5 to 30) with average capacity of 20 GHz; the average rate of data of every communication is 50 F. The execution of the suggested algorithm on these kinds of circumstances computes the lower/upper bound of the latency in query processing. The latency occurred with the proposed algorithm is 50.3% reduced and better other approaches. There is calculation of resources if there are huge edge servers over the network environment. Henceforth, the performance of the anticipated algorithm is nearer to the lower bound (30 edge servers). Moreover, the proposed algorithm’s latency is 2.20 times higher than the lower bound (five servers). However, the upper bound of latency has no remarkable change if the size of





Figure 9: Response time comparison

Figure 10: Availability measure

Figure 11: Throughput comparison

Figure 12: Trust establishment
Tab. 1 depicts the comparison of the response time. The comparison is done for successive iterations like 0.5, 1, 1.5, 2, 2.5, 3, 3.5, 4 and 4.5 respectively. The response time of BoQ-IQWO during 4.5 iteration is 2.6 s which is 1.0, 6.4, and 1.8 s lesser than MODA, PSO and MOGWO. The availability of BoQ-IGWO is 7.5 which is 0.5, 3 and 1.8 higher than other approaches. The throughput of the anticipated model is 6 which is 2.4, 2.5, and 1.7 higher than other approaches. The trust of the anticipated model is 6.2 which is 2.4, 2.3 and 0.4 higher than other approaches.
Consider the situation with ten edge servers in the group of simulations that differs the multiple services in every acyclic graph from 4 to 14. The system parameters values are identical to the mentioned set of simulations. The specific number of services is created randomly, depending on the suggested algorithm. The proposed algorithm acquires the latency is 43.4% smaller than the upper bound, 3.05 times greater than the lower bound is considered. The ratio between the developed and optimal latency is smaller than the approximation ratio in the proposed algorithm. The upper bound maximizes the maximum number of services since the capability calculation of the cloud is stronger. The acquired latency maximizes from 174 to 372 s if the amount of services differs from 4 to 14 in the proposed algorithm. Further, the lower bound has no remarkable change if
The capability calculation of every edge server identifies the latency in analysis and also influences the latency of query processing. The ten edge servers should be deployed as
The rate of data transmission greatly influences the latency of query processing. The data transmission rate depends on the 5G network in the group of simulations. Assume, an average data transmission rate differs from 200–1000 Mbps, the latency to transmit 1GB data differs from 1 to 5 s. Various situations are generated and execute the suggested algorithm that depends on the average data transmission rates. The latency and upper bound are maximized remarkably if the data rate gets lower. Moreover, the lower bound maximizes gradually if the data rate is minimized since the services are considered to be carried out entirely in a distributed way. Further, the acquired latency is 35.7% lesser than the upper bound in the proposed algorithm if the data rate grows from 200 to 1000 Mbps, and the latency gets increased almost five times in the proposed algorithm. As a result, the latency of every communication link significantly influences the latency during data processing.
The proposed system describes that the distributed query processing issue is investigated in the distributed system. The problem in query processing is defined that targets to derive the query processing plan with less latency of query response. The minimal issue in query processing is NP-Hard. Primarily, exceptional cases with fewer query processing issues are investigated and confirmed. The optimal solution for the minor problem in query processing in polynomial time is obtained for these two cases. Hence, an approximation algorithm is proposed to resolve the minor issue in query processing and gives the analysis that this algorithm creates a suitable approximation ratio. The simulation outcomes are illustrated to determine the algorithm’s performance, and the simulation outcomes implicit that this algorithm is efficient. This study concentrates on reducing latency, and our future research is to examine the energy-efficiency algorithms in a distributed management system.
Funding Statement: The authors received no specific funding for this study.
Conflicts of Interest: The authors declare that they have no conflicts of interest to report regarding the present study.
References
1. X. Zeng, G. Xu, X. Zheng, Y. Xiang and W. Zhou, “E-AUA: An efficient anonymous user authentication protocol for mobile IoT,” IEEE Internet Things Journal, vol. 6, no. 2, pp. 1506–1519, 2019. [Google Scholar]
2. R. Paulet, M. G. Kaosar, X. Yi and E. Bertino, “Privacy-preserving and content-protecting location-based queries,” IEEE Transactions on Knowledge and Data Engineering, vol. 26, no. 5, pp. 1200–1210, 2013. [Google Scholar]
3. T. Ma, J. Jia, Y. Xue, Y. Tian, A. Al-Dhelaan et al., “Protection of location privacy for moving kNN queries in social networks,” Applied Soft Computing, vol. 66, pp. 525–532, 2018. [Google Scholar]
4. M. Elkhorn, S. Shahrestani and H. Cheung, “A review of mobile location privacy in the internet of things,” in Proc. 10th Int. Conf. on ICT and Knowledge Engineering, Bangkok, Thailand, pp. 266–272, 2012. [Google Scholar]
5. J. Zhou, Z. Cao, X. Dong and A. V. Vasilakos, “Security and privacy for cloud-based IoT: Challenges,” IEEE Communications Magazine, vol. 55, no. 1, pp. 26–33, 2017. [Google Scholar]
6. X. Pan, J. Xu and X. Meng, “Protecting location privacy against location-dependent attacks in mobile services,” IEEE Transactions on Knowledge and Data Engineering, vol. 24, no. 8, pp. 1506–1519, 2011. [Google Scholar]
7. C. Zhou, T. Wang, W. Jiang and H. Tian, “Practical k nearest neighbor query scheme with two-party guarantees in road networks, ” in Proc. 17th IEEE Int. Conf. Trust, Security and Privacy in Computing and Communications, 12th IEEE Int. Conf. on Big Data Science and Engineering (TrustCom/BigDataSE), New York, USA, pp. 1316–1321, 2018. [Google Scholar]
8. T. Wang, M. Z. A. Bhuiyan, G. Wang, L. Qi, J. Wu et al., “Preserving balance between privacy and data integrity in edge-assisted internet of things,” IEEE Internet Things Journal, vol. 7, no. 4, pp. 2679–2689, 2020. [Google Scholar]
9. T. Tao, M. Z. A. Bhuiyan, M. A. Rahman, T. Wang, J. Wu et al., “TrustData: Trustworthy and secured data collection for event detection in the industrial cyber-physical system,” IEEE Transactions on Industrial Informatics, vol. 16, no. 5, pp. 3311–3321, 2019. [Google Scholar]
10. T. Wang, H. Luo, X. Zheng and M. Xie, “Crowdsourcing mechanism for trust evaluation in CPCS based on intelligent mobile edge computing,” ACM Transactions on Intelligent Systems and Technology (TIST), vol. 10, no. 6, pp. 1–19, 2019. [Google Scholar]
11. T. Wang, D. Zhao, S. Cai, W. Jia and A. Liu, “Bidirectional prediction based underwater data collection protocol for end-edge-cloud orchestrated system,” IEEE Transactions on Industrial Informatics, vol. 16, no. 7, pp. 4791–4799, 2019. [Google Scholar]
12. Q. A. Arain, I. Memon, Z. Deng, M. H. Memon, F. A. Manga et al., “Location monitoring approach: Multiple mix-zones with location privacy protection based on traffic flow over road networks,” Multimedia Tools and Applications, vol. 77, no. 5, pp. 5563–5607, 2018. [Google Scholar]
13. W. Eltarjaman, R. Dewri and R. Thurimella, “Private retrieval of POI details in top-K queries,” IEEE Transactions on Mobile Computing, vol. 16, no. 9, pp. 2611–2624, 2016. [Google Scholar]
14. X. Meng, H. Zhu and G. Kollios, “Top-k query processing on encrypted databases with strong security guarantees,” in Proc. IEEE 34th Int. Conf. on Data Engineering (ICDE), Paris, France, pp. 353–364, 2018. [Google Scholar]
15. K. A. Hafeez, L. Zhao, J. W. Mark, X. Shen and Z. Niu, “Distributed multichannel and mobility-aware cluster-based MAC protocol for vehicular ad hoc networks,” IEEE Transactions on Vehicular Technology, vol. 62, no. 8, pp. 3886–3902, 2013. [Google Scholar]
16. T. Wang, J. Zeng, Y. Lai, Y. Cai, H. Tian et al., “Data collection from WSNs to the cloud-based on mobile fog elements,” Future Generation Computer Systems, vol. 105, pp. 864–872, 2020. [Google Scholar]
17. Y. K. Wu, H. Huang, Q. Wu, A. Liu and T. Wang, “A risk defence method based on microscopic state prediction with partial information observations in social networks,” Journal of Parallel and Distributed Computing, vol. 131, pp. 189–199, 2019. [Google Scholar]
18. B. Zhou, J. Li, X. Wang, Y. Gu, L. Xu et al., “Online internet traffic monitoring system using spark streaming,” Big Data Mining and Analytics, vol. 1, no. 1, pp. 47–56, 2018. [Google Scholar]
19. C. Wang, C. Wang, Z. Wang, X. Ye, J. X. Yu et al., “DeepDirect: Learning directions of social ties with edge-based network embedding,” IEEE Transactions on Knowledge and Data Engineering, vol. 31, no. 12, pp. 2277–2291, 2018. [Google Scholar]
20. Y. Xiao, Y. Jia, C. Liu, X. Cheng, J. Yu et al., “Edge computing security: State of the art and challenges,” Proceedings of the IEEE, vol. 107, no. 8, pp. 1608–1631, 2019. [Google Scholar]
21. S. Cheng, Z. Cai and J. Li, “Curve query processing in wireless sensor networks,” IEEE Transactions on Vehicular Technology, vol. 64, no. 11, pp. 5198–5209, 2014. [Google Scholar]
22. T. Shi, S. Cheng, Z. Cai and J. Li, “Adaptive connected dominating set discovering algorithm in energy-harvest sensor networks,” in 35th IEEE INFOCOM, San Francisco, CA, USA, pp. 1–9, 2016. [Google Scholar]
23. X. Chen, L. Jiao, W. Li and X. Fu, “Efficient multi-user computation offloading for mobile-edge cloud computing,” IEEE/ACM Transactions on Networking, vol. 24, no. 5, pp. 2795–2808, 2015. [Google Scholar]
24. X. Cao, F. Wang, J. Xu, R. Zhang and S. Cui, “Joint computation and communication cooperation for mobile edge computing,” in 16th Int. Symp. on Modeling and Optimization in Mobile, Ad Hoc, and Wireless Networks, Shanghai, China, pp. 1–6, 2018. [Google Scholar]
25. K. Poularakis, J. Llorca, A. M. Tulino, I. Taylor and L. Tassiulas, “Joint service placement and request routing in multi-cell mobile edge computing networks,” in IEEE Int. Conf. on Computer Communications, Paris, France, pp. 10–18, 2019. [Google Scholar]
26. W. Sun, G. Z. Dai, X. R. Zhang and X. Z. He, “TBE-net: A three-branch embedding network with part-aware ability and feature complementary learning for vehicle re-identification,” IEEE Transactions on Intelligent Transportation Systems, pp. 1–13, 2021. https://doi.org/10.1109/TITS.2021.3130403. [Google Scholar]
27. W. Sun, L. Dai, X. R. Zhang, P. S. Chang and X. Z. He, “RSOD: Real-time small object detection algorithm in UAV-based traffic monitoring,” Applied Intelligence, pp. 1–16, 2021. https://doi.org/10.1007/s10489-021-02893-3. [Google Scholar]
28. P. Muneeshwari and M. Kishanthini,“A New Framework for Anomaly Detection in NSLKDD Dataset using Hybrid Neuro-Weighted Genetic Algorithm,” Journal of Computational Science and Intelligent Technologies, vol. 1, no. 1, pp. 29–36, 2020. https://doi.org/10.53409/mnaa.jcsit1105. [Google Scholar]
29. R. Mugesh, “A Survey on Security Risks in Internet of Things (IoT) Environment,” Journal of Computational Science and Intelligent Technologies, vol. 1, no. 2, pp. 1–8, 2020. https://doi.org/10.53409/mnaa.jcsit20201201 [Google Scholar]
30. H. Q. Alatawi, S. F. Aluneizi, A. S. Makki, M. M. Alshamrani and N. M. Albalawi, “An Effectiveness of AI Approaches in Human Disease Diagnosis for Increasing Efficiency of Medical Systems- Review,” Journal of Computational Science and Intelligent Technologies, vol. 2, no. 3, pp. 1–8, 2021. https://doi.org/10.53409/mnaa/jcsit/2301.S. [Google Scholar]
31. S. P. Sasirekha, A. Priya, T. Anitha and P. Sherubh, “Data Processing and Management in IoT and Wireless Sensor Network,” Journal of Physics: Conference Series, vol. 1712, no. 1, pp. 012002, 2020. https://doi.org/10.1088/1742-6596/1712/1/012002. [Google Scholar]
32. R. Khilar, K. Mariyappan, M. S. Christo, J. Amutharaj, T. Anitha et al., “Artificial Intelligence-Based Security Protocols to Resist Attacks in Internet of Things,” Wireless Communications and Mobile Computing, vol. 2022, no. 1440538, pp. 1–10, 2022. https://doi.org/10.1155/2022/1440538. [Google Scholar]
Cite This Article
 Copyright © 2023 The Author(s). Published by Tech Science Press.
Copyright © 2023 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF Downloads
Downloads
 Citation Tools
Citation Tools