 Open Access
Open Access
ARTICLE
Information Diffusion Models and Fuzzing Algorithms for a Privacy-Aware Data Transmission Scheduling in 6G Heterogeneous ad hoc Networks
IT Department, Universidad Politécnica de Madrid, Alan Turing Street, Madrid, 28031, Spain
* Corresponding Author: Borja Bordel Sánchez. Email:
(This article belongs to the Special Issue: Cutting-Edge Security and Privacy Solutions for Next-Generation Intelligent Mobile Internet Technologies and Applications)
Computer Modeling in Engineering & Sciences 2026, 146(2), 43 https://doi.org/10.32604/cmes.2025.072603
Received 30 August 2025; Accepted 29 December 2025; Issue published 26 February 2026
Abstract
In this paper, we propose a new privacy-aware transmission scheduling algorithm for 6G ad hoc networks. This system enables end nodes to select the optimum time and scheme to transmit private data safely. In 6G dynamic heterogeneous infrastructures, unstable links and non-uniform hardware capabilities create critical issues regarding security and privacy. Traditional protocols are often too computationally heavy to allow 6G services to achieve their expected Quality-of-Service (QoS). As the transport network is built of ad hoc nodes, there is no guarantee about their trustworthiness or behavior, and transversal functionalities are delegated to the extreme nodes. However, while security can be guaranteed in extreme-to-extreme solutions, privacy cannot, as all intermediate nodes still have to handle the data packets they are transporting. Besides, traditional schemes for private anonymous ad hoc communications are vulnerable against modern intelligent attacks based on learning models. The proposed scheme fulfills this gap. Findings show the probability of a successful intelligent attack reduces by up to 65% compared to ad hoc networks with no privacy protection strategy when used the proposed technology. While congestion probability can remain below 0.001%, as required in 6G services.Keywords
6G mobile technologies are envisioned to enable a large new collection of innovative services with an enhanced extreme Quality-of-Service (QoS). These range from remote control of critical infrastructure (supported by extreme Ultra-Reliable Low Latency Communications or eURLLC with congestion probabilities below 0.001%) to immersive experiences based on enhanced Mobile Broadband Communications (eMBBC). But, among all these emerging services, those that require an overlay infrastructure are the most challenging.
Paradigms such as Industry 5.0 and Vehicular Ad-hoc Networks (VANET) rely on complex, heterogeneous infrastructures supported by underlying 6G links. In these new paradigms, dynamic adaptation and massive customization are key elements. Thus, 6G-powered mobile nodes, with an extremely varying catalog of hardware capabilities, are wirelessly interconnected in an ephemeral manner; and the architecture of the infrastructure can evolve and dynamically change according to the needs and the required customization. However, this approach introduces new open problems. On the one hand, a changing network topology must be managed with specific protocols and algorithms (such as choreographed self-configuration schemes) which may introduce additional overheads and redundancies. So, the extreme QoS expected from 6G deployments and communications might not be achieved at the final application level. On the other hand, transversal issues such as privacy, security, or reliability are very hard to guaranty when trustworthy paths at transport level cannot be analyzed and preserved in the long term. For some of these issues, extreme-to-extreme solutions are a valid response. For example, security schemes for abnormal data filtering can be implemented through Artificial Intelligence models in extreme nodes, and additional authentication planes can be included in base stations [1]. But this approach is not valid for privacy preservation.
In fact, in 6G heterogeneous ad hoc networks, intermediate nodes are not trustworthy, but all of them must handle the data packets for which they provide routing functionalities. This exposure allows attackers to capture private information in a transparent way. Malicious nodes can enter ad hoc networks long enough to deploy intelligent attacks, where learning algorithms extract patterns from even small packets. Some authors have proposed privacy preserving solutions for 6G ad hoc networks, such as anonymous message authentication and key exchange mechanisms [2], Blockchain-enabled data sharing [3], Blockchain-enabled trust computation [4], semantic-aware communications [5], or traffic densers against black hole attacks [6]. But they are computationally costly, with processing times between 200 and 500 ms [7] and almost 30% of CPU overload [8], and they greatly penalize the final Quality-of-Service at the overlay-network level. Actually, 6G eURLLC standards cannot be met when those existing privacy-preserving solutions are implemented. Therefore, new privacy-preserving technologies for 6G heterogeneous ad hoc networks are required; so, the expected 6G QoS is still feasible while modern intelligent attackers are mitigated.
Specifically, as current approaches require large processing and computational delays, the following research gaps are still uncovered:
• Privacy-preserving communication scheduling algorithms for 6G ad hoc networks, compatible with extreme QoS
• Protection schemes against illegitimate data capture and learning adapted to dynamic 6G ad hoc networks with ultra-reliable low-latency and lightweight computational cost
To fulfill these gaps, in this paper, we propose a privacy-aware data transmission scheduling algorithm which allows 6G ad hoc nodes to find the optimum balance between Quality-of-Service and privacy protection. So, 6G requirements are compatible with protection against intelligent attacks and illegitimate data capture. The algorithm is executed at the network level, so extreme nodes can calculate the optimum time slot and transmission frame for private data. The proposed algorithm uses fuzzing algorithms to generate false data packets, whose purpose is to confuse potential intelligent attackers operating within the ad hoc network. To analyze the level of learning and/or confusion of intelligent attackers, a probabilistic dynamical system is used. In this system, information diffusion models and network statistics are employed to estimate the amount of private information captured. Although this approach has no impact on network latency, false data packets can penalize effective network bandwidth. To avoid congestion situation, the teletraffic theory is employed to propose a combined model where queue models and network statistics are used to understand the behavior, lifecycle, and performance of ad hoc nodes when false data are injected. So, the final probabilistic model represents the balance between privacy and performance. Particle Swarm Optimization techniques can be used to find the optimum balance and transmission schedule.
The remainder of the manuscript is organized as follows. Section 2 introduces the state of the art in privacy-preserving solutions for 6G-enabled ad hoc networks. Section 3 presents the proposed contribution, the scheduling algorithm and the teletraffic model and the probabilistic information diffusion model. Section 4 describes the experimental methodology and experiments. Section 5 discusses the experimental results and Section 6 concludes the paper.
In general terms, privacy-preserving technologies in 6G networks can be classified into two big groups: intelligent mechanisms [9] and Blockchain-enabled solutions [10]. Next subsections discuss the limitations and research opportunities related to both alternatives. Section 2.1 analyzes Blockchain-enabled solutions, while Section 2.2 describes the previous intelligent and computational approaches.
2.1 Blockchain-Enabled Solutions for Privacy Preservation in 6G
Intelligent mechanisms include a federated learning scheme to preserve differential privacy [11] or semantic analyzers to remove sensible messages [11]. Blockchain-enabled solutions deploy overlay authentication layers [1], store transparent and immutable records of nodes’ reputation [12], and apply information theory techniques [13], information packet comparisons [4] or network virtual representations (digital twin) [14] to identify those nodes that are potentially collecting private data, in order to remove them from the infrastructure [15]. However, all these proposals require a long-term stable network configuration, so permanent and unique identifiers can be distributed, the intelligent algorithms can converge, and/or the virtual or reputational representations are stable enough to run the decision-making algorithms. But, in ad hoc networks, connections are ephemeral or, even, opportunistic. Also, the general network architecture is constantly evolving, preventing any analyzing algorithm or framework from converging or staying stable long-term. Then, different approaches are needed to preserve privacy.
In fact, some authors have investigated how Blockchain-enabled techniques could be adapted to ad hoc networks [16]. Certificateless authentications [17] or new protocols such as Cooperative Sensing Smart Contract [18] are described. Most of these schemes are designed to be lightweight (low computational latency), so the response time may be below the evolution rhythm in the ad hoc infrastructure. Delays of around 100 ms have been reported [18], but these values are above the expected performance in 6G ad hoc networks. Some other authors describe alternative network architectures, in which Blockchain networks act as orchestrators [19]. But this scheme is only valid for some specific applications and for very homogeneous networks [20], while future infrastructures are expected to be very heterogeneous.
Table 1 summarizes the relevant state of the art.
The technology proposed in this paper is not tailored for any specific application and can be used in any type of ad hoc network. Its main focus (thanks to numerical models and optimization algorithms) is to find the optimum balance between privacy-preservation and network performance so that 6G extreme QoS is met.
2.2 Intelligent and Computational Mechanisms for Privacy Preservation in 6G
Intelligent techniques for ad hoc networks may be found as well. Most of them focused on intrusion detection. From deep learning algorithms to detect illegitimate data capturers [21], to predictive techniques for the detection of abnormal private data handlers [22] and federated strategies to detect misbehaviors [23]. However, although the authors claim these techniques are fitted to match the requirements of ad hoc networks, convergence times in the range of thousands of seconds are still reported [23]. For many ad hoc network application scenarios (such as vehicular networks), this is not acceptable [24].
Lightweight intelligent schemes for privacy preservation in ad hoc networks have been investigated in the last years. Some intelligent schemes have proven to be successful in optimizing QoS in communications [25], but privacy considerations are usually not integrated into these models. Some centralized security threat detection models are compatible with differential privacy by design [26], however, no particular instrument against illegitimate learning is integrated. On some occasions, anonymization and privacy are implemented; but they are commonly tailored for some particular applications or hardware capabilities (e.g., cameras) [27].
On the other hand, in the context of 6G Internet-of-Things (IoT), industrial IoT, or edge computing, authentication schemes are commonly proposed for privacy preservation [28]. Specifically, low-latency authentication algorithms [29] are studied, including strategies defined in other contexts such as certificateless authentication [30], two-factor [31], or three-factor authentication [32]. However, despite reported efforts, computational delays above 500 ms are still required [7]. And this delay is far above the expected latency in 6G networks (100 microseconds [33]). Some other authors propose traffic filters and classifiers to “sanitize” data and ensure that private information is not handled [34]. Although preliminary evaluations with offline datasets show good precision, their performance in real-time data exchange processes (especially in terms of computational delays) is still unknown.
Finally, some authors propose alternatives taking advantage of the mobility of the nodes. Algorithms to calculate privacy-preserving trajectories for data dissemination [35] have been reported, as well as technologies to group the transport nodes that are allowed to handle private data [36]. These schemes do not require a long-term network structure, and computational delays are acceptable. However, they assume that ad hoc nodes can freely choose the path for their data packets, which is not true for most scenarios (especially in opportunistic networks).
In this paper we propose a privacy-aware data transmission scheduler, where extreme nodes can calculate the optimum communication scheme to preserve their private data against intelligent attackers. We use probabilistic models, which can be employed by extreme nodes with no global knowledge about the ad hoc network. Besides, since we use probabilistic models, the network architecture may change dynamically without impact. Data packets and transmission protocols are not extended, and no additional overhead is introduced, so eURLLC is preserved by fulfilling the existing research gaps in the state of the art.
3 A Privacy-Aware Data Transmission Scheduling Algorithm
This section introduces the proposed framework to find the optimum data transmission schedule in terms of network performance (Quality-of-Service) and privacy preservation. A Particle Swarm Optimization strategy analyzes all possible schedules, their impact on network congestion and latency using teletraffic theory, and the potential learning achieved by intelligent attackers through probabilistic and information diffusion models. Section 3.1 introduces the general data transmission framework, the network and traffic models, and the fuzzing algorithm employed to propagate false information among the nodes. Section 3.2 introduces the probabilistic models used to describe information propagation in ad hoc networks and the potential learning of intelligent attackers. Finally, Section 3.3 combines both visions and proposes the global data transmission scheduling scheme. Fig. 1 shows a general description of the proposed technology.
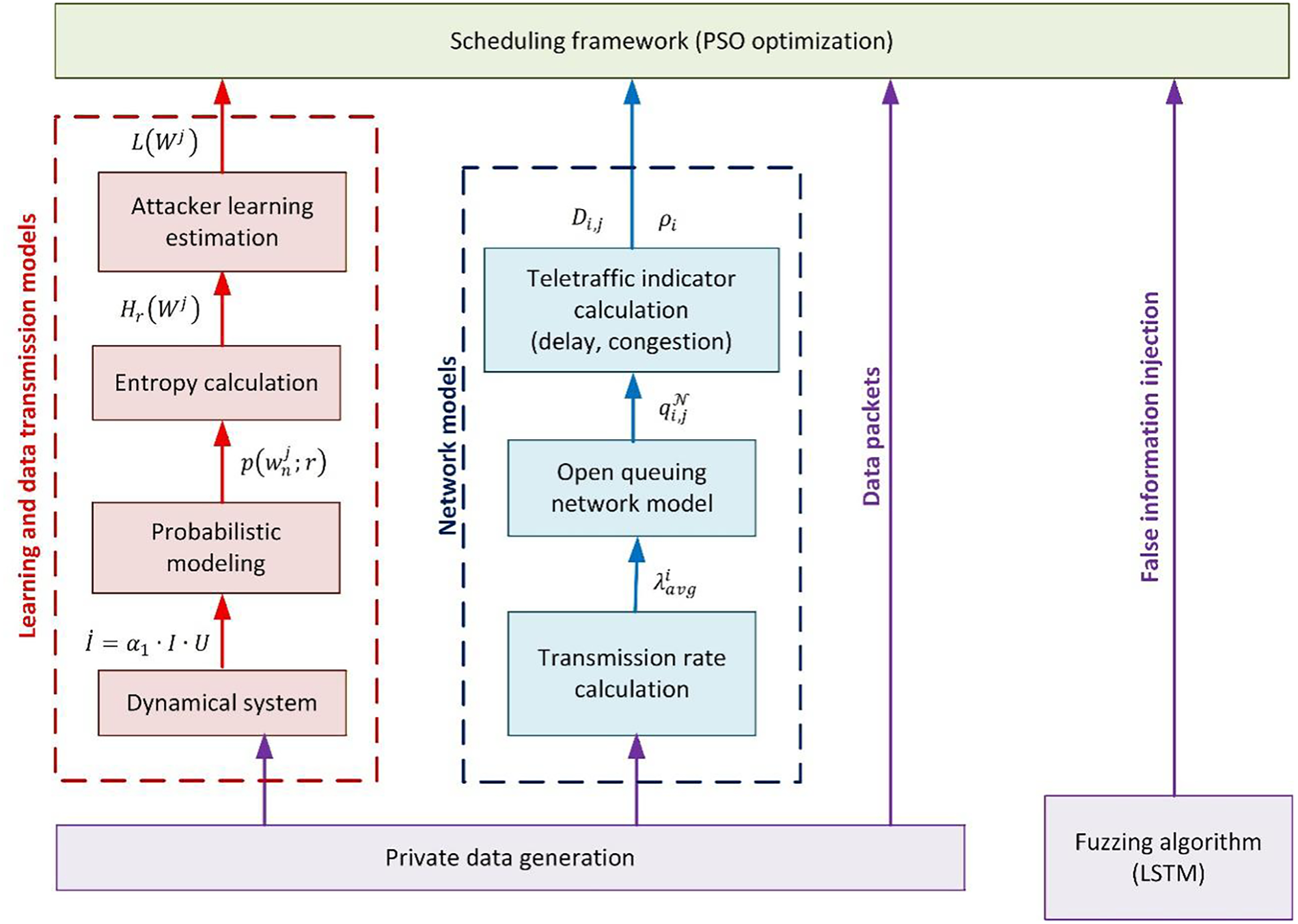
Figure 1: General overview of the proposed technology
3.1 Network Models and Fuzzing Algorithms
An ad hoc network can be described as a graph
Graph
Each node
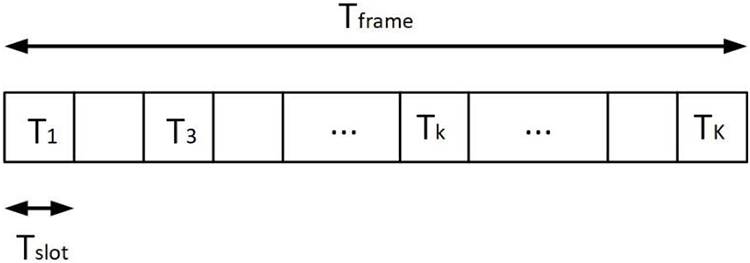
Figure 2: Structure of any time frame
Then, the instant transmission rate
With these parameters, any graph
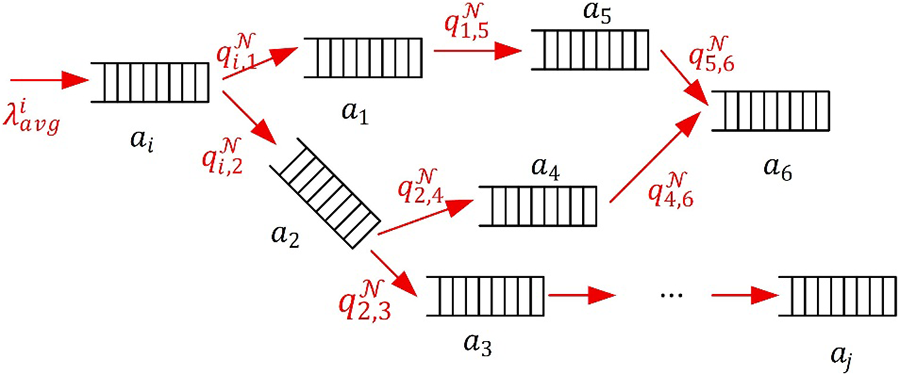
Figure 3: Ad hoc network as an open queuing network
Probabilities
Under these conditions, the punctual network congestion
Two restrictions on any potential data transmission scheme can be extracted now:
• Delay
• The punctual network congestion
To meet those restrictions, the number of dummy time slots
Although many different strategies to create false information have been reported (recently, for example, algorithms based on generative Artificial Intelligence are very common [38]), ad hoc networks require a solution computationally lightweight enough to be executed by nodes. We propose a fuzzing algorithm based on Long Short-Term Memory (LSTM), which still needs a training phase but does not require complex models to generate large populations of different data. Although simpler strategies could be used, current learning models are powerful enough to ignore entries with low entropy (information). So, injected fuzzed packets must replicate the information level of real data as precisely as possible.
LSTM has the ability of removing, keeping, and/or updating some specific parts of a given data input, but preserving at long-term the desired pieces of information using the memory unit. Fig. 4 shows the proposed fuzzing algorithm.
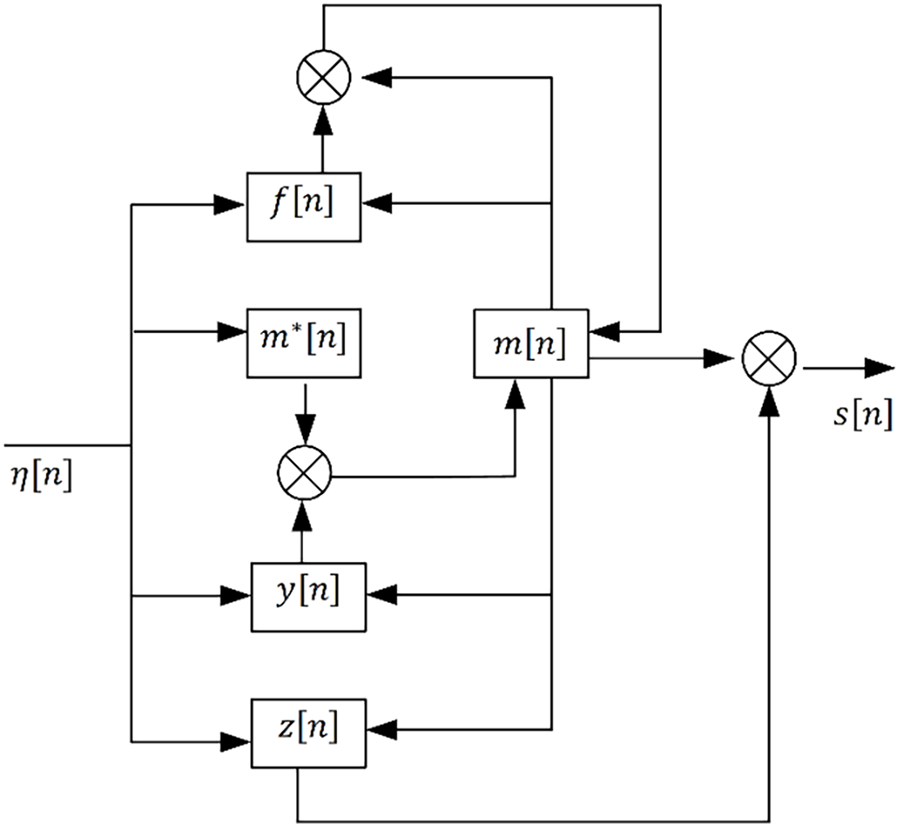
Figure 4: Block diagram for the LTSM-based fuzzing algorithm
The fuzzing algorithm includes tree basic blocks: the input block described by function
In this work, hyperparameters are calculated using a backpropagation through time (BPTT) technique, and a dataset including private data units and examples of fuzzed data units where the sensible information has been removed and/or randomized. BPTT is selected as its complexity and scalability is linear, ensuring the training delays do not grow uncontrollably when large ad hoc networks with dynamic heterogenous behaviors are modeled. Besides, BPTT can be trained with relatively small datasets (some thousands of entries) and get high precision models.
The final question is to determine which information units
3.2 Probabilistic Models for Data Transmission and Learning Level in Intelligent Attacks
While an elevated number of dummy time slots
For an intelligent attacker running illegitimate data capture at node
First, entropy
Second, probability
Probability
Probability
This dynamical system can be numerically solved, using, for example, Runge-Kutta methods, and variable
Finally, the parameters
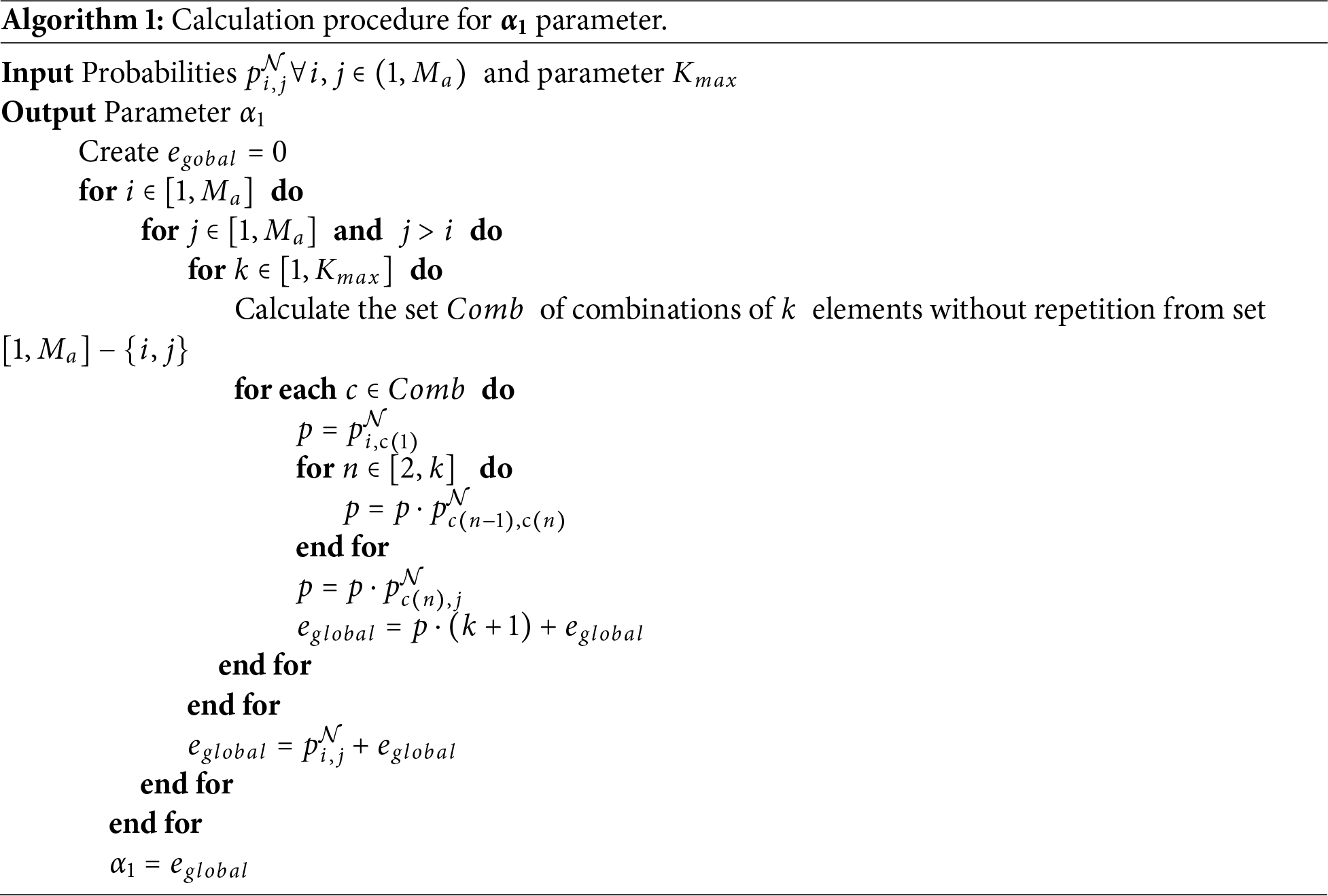
Parameter
Finally, parameter
Then, one additional restriction for any data transmission schedule can be extracted, ensuring privacy preservation: learning level
Any candidate to be the optimum privacy-aware data transmission schedule must minimize an objective function
But scheduling must be also efficient in computational terms, so a maximum of
The final purpose is to find the state
In this PSO algorithm,
Finally, the states
4 Experimental Methodology and Validation
In order to evaluate the performance and utility of the proposed scheduling algorithm, an experimental validation is carried out. The experiments are based on simulation scenarios and tools, representing different configurations to exhaustively analyze the behavior of the proposed technology.
All simulations were designed and executed using MATLAB R2022a software, with standard precision. Contrary to other suites, MATLAB allows deep control of calculation precision and computational cost, so the specific configurations of small ad hoc nodes can be replicated with fidelity, and scalability experiments can be carried out with a reduced experimental error. Anyway, if ad hoc nodes with very reduced numerical precision are employed, results could be sightly different.
Each simulation was repeated twelve times to ensure that exogenous numerical effects do not impact the final results. In order to minimize errors, the consolidated results are calculated as the average value of all individual simulations. The random parameters required to run the simulations were randomly selected by the default MATLAB libraries, in order to remove any possible bias introduced by human intervention. Any possible exogenous effect should be mitigated by repeating simulations ten times.
As hardware platform, we employed a Linux architecture (Ubuntu 20.04 LTS) with the following hardware characteristics: Dell R540 Rack 2U, 96 GB RAM, two processors Intel Xeon Silver 4114 2.2G, HD 2 TB SATA 7.2K rpm.
Two different experiments were developed. In the first experiment, the congestion probability, QoS- compliance probability, and the probability of a successful intelligent attack are monitored in an ad hoc network implementing the proposed solution. Networks with different sizes (number of nodes,
All experiments simulated an ad hoc network in a smart lab. Different nodes with sensing capabilities had to route small data pieces towards a gateway, so later the information can be sent to a cloud infrastructure based on FIWARE components where it is stored. Nodes could include sensors for temperature, humidity, and carbon dioxide. To represent the heterogeneity of real ad hoc networks, nodes implemented totally or partially these sensing capabilities in a random basis. New information was produced every three minutes. As the proposed solution was local, the final results were calculated as the average from all individual nodes. To ensure some coherent information can be extracted from that data, they replicated real measures. Measures from the same dataset were used to train the fuzzing algorithm offline, and the final trained model was integrated into the simulation.
The real data for the training process and the simulated data generation were produced with real DTH-11 sensors (for humidity and temperature measurements) and CCS811 sensors for carbon dioxide measurements. Fuzzing algorithm was trained using Jupyter notebook technologies.
In all simulations, an intelligent attacker randomly placed within the ad hoc network developed an illegitimate data capture. This attack was based on a multi-layer perceptron [39], as this intelligent model has proved to carry out successful attacks learning from network data packets [40]. Although other intelligent models could be used as well [41], depending on the target application and focus.
To analyze the computational cost, internal functions and mechanisms from MATLAB were employed. On the other hand, congestion and latency at every network node were calculated numerically using teletraffic theory. The success probability of intelligent attackers was later estimated, by testing the trained model during simulations with new real data not employed before. To facilitate comparisons, percentages were used. For all simulations, congestion, excessive latency, or successful attacks were detected when the proposed thresholds, i.e.,
Finally, for all simulations in the experimental phase, the system was configured with the parameters indicated in Table 2.
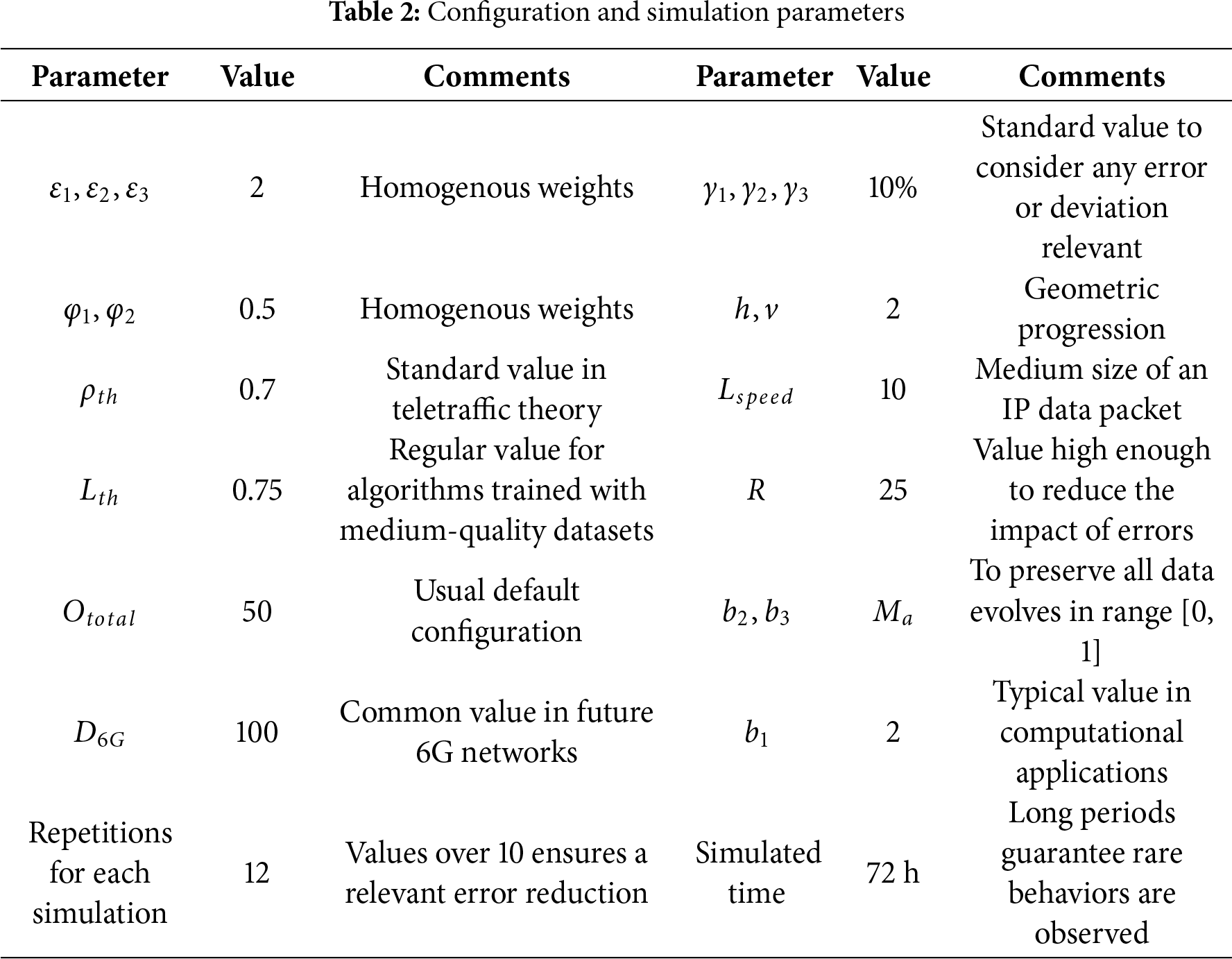
Fig. 5 shows the congestion probability, in terms of the number of network nodes
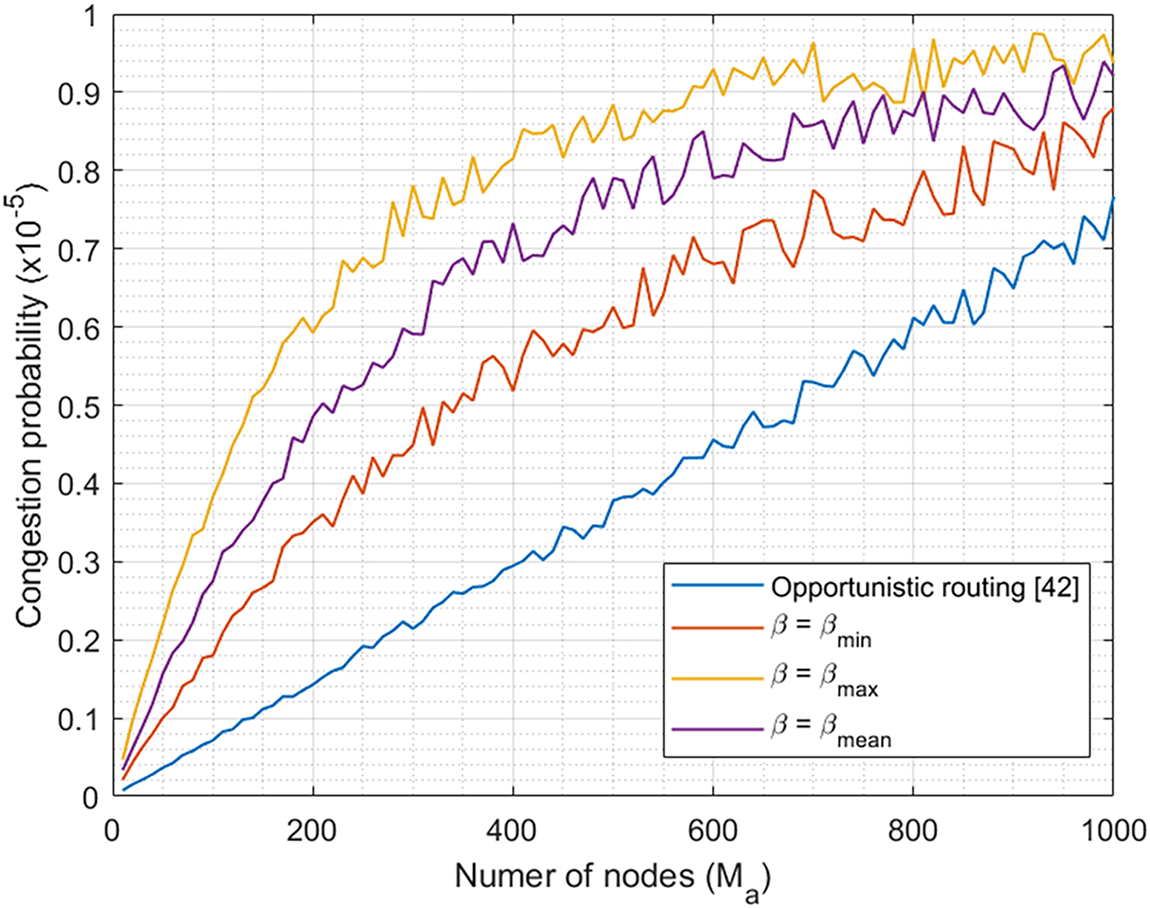
Figure 5: Congestion probability depending on
In ad hoc networks implementing the proposed scheduling solution, expected 6G QoS is also met, as congestion never exceeds 0.001%. But in this case, evolution is exponential and congestion probability higher.
In fact, the proposed solution increases the data input streams, as they do not only include private data but also false fuzzed information. Due to this increase, the congestion probability also goes up with the number of nodes. An exponential evolution is also coherent, as traffic follows a Poisson distribution and
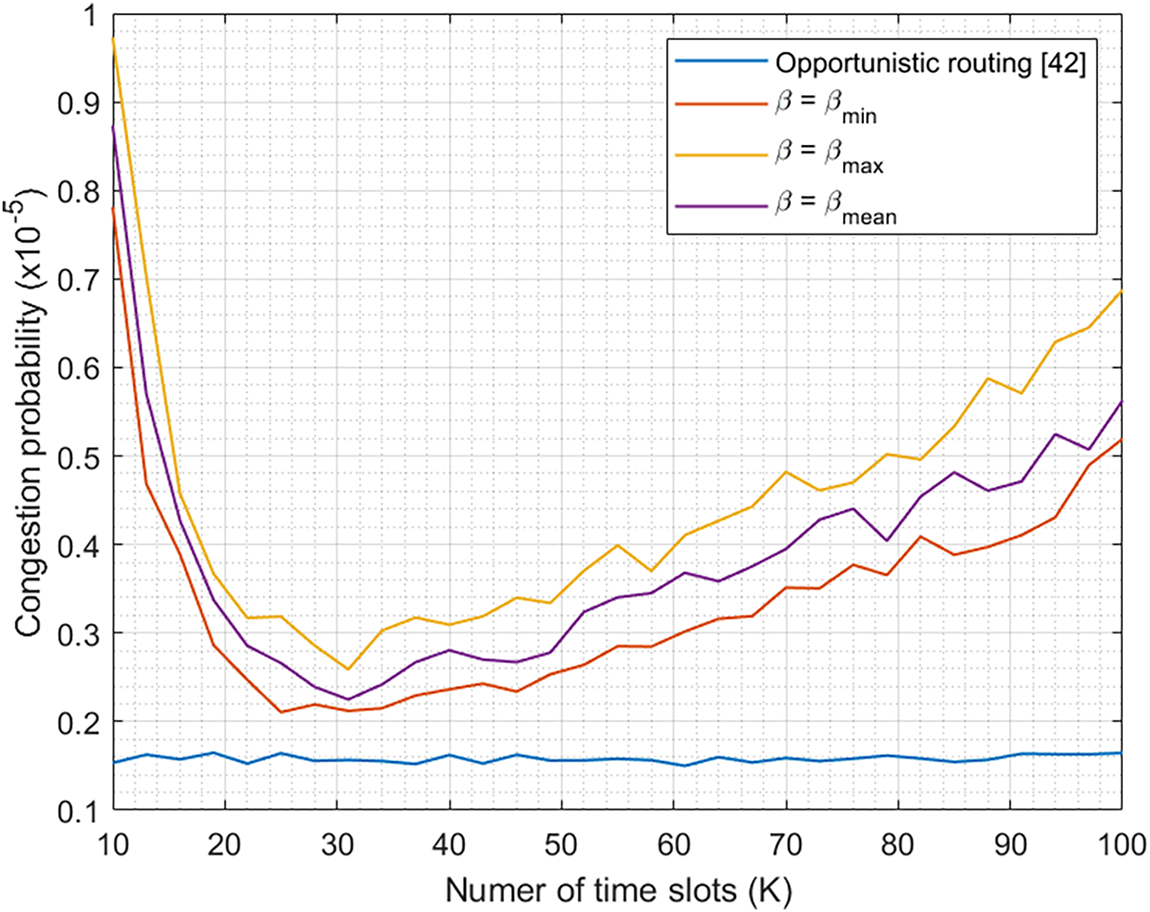
Figure 6: Congestion probability depending on
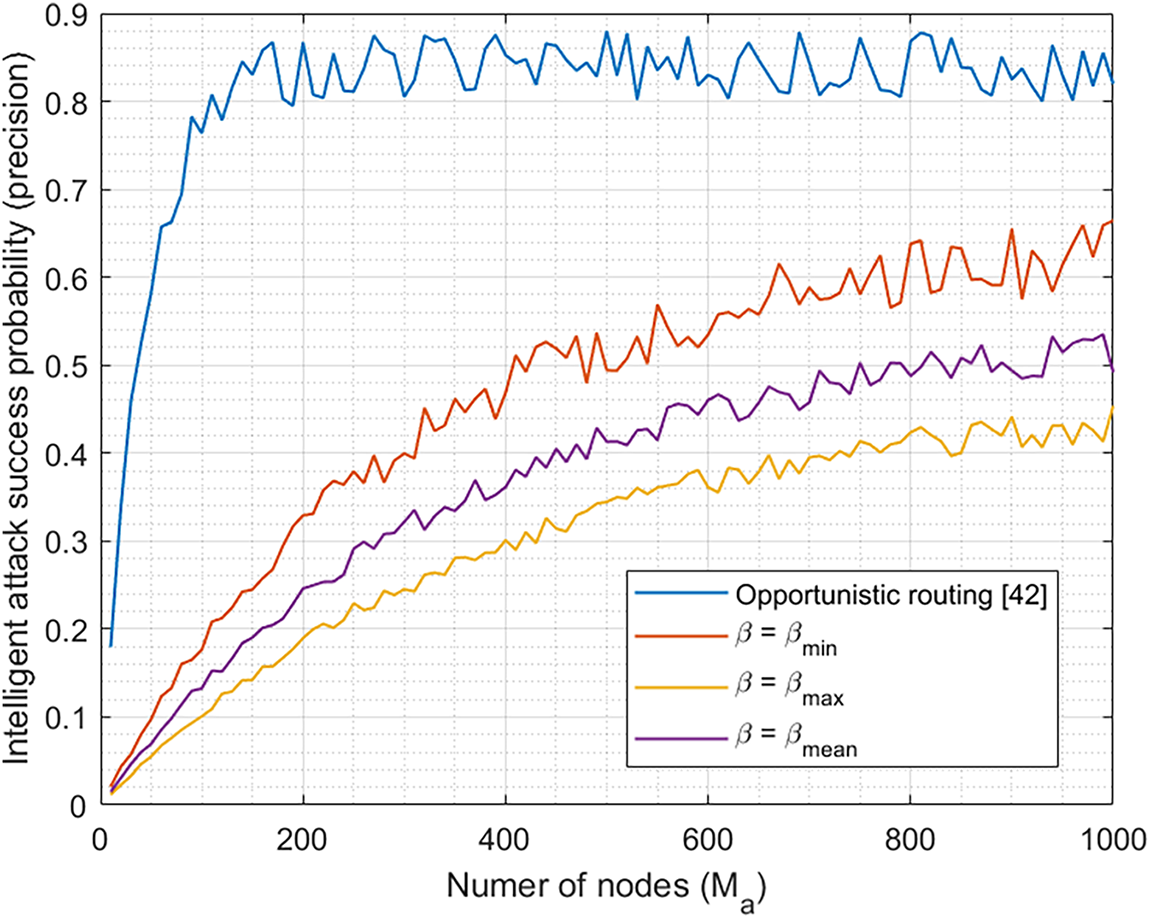
Figure 7: Probability of successful intelligent attack depending on
For ad hoc networks larger than
Fig. 6 shows the congestion probability, calculated during the first experiment, for different values of
As in Fig. 5, the differences between different
So, in conclusion, the proposed solution is acceptable in terms of network performance and fully compatible with 6G standards.
Fig. 7 shows the probability of a successful intelligent attack, depending on the number of nodes
This reduction is more extreme for small networks, where data diffusion is faster and straightforward. For larger networks, when data may get lost, queued, or delayed, the discrepancies between reality and the proposed information diffusion model increases, and the probability does the same. In this case, implementations of
To conclude the first experiment, Fig. 8 shows the probability of a successful intelligent attack, depending on the number of time slots K in each time frame. Again, as can be seen, traditional opportunistic routing strategies are independent of this parameter, while the proposed scheduling algorithm shows behavior as a “saddle”. The differences between the implementations of β function are equivalent to those explained before (Fig. 5). Reduction in success probability, in this case, achieves “only” 50% under the best circumstances. Again, the “saddle” form is typical of PSO algorithms were the number of particles changes, as the global optimization error evolves similarly and that causes an increase in the success probability. Tradeoff between privacy protection and network performance is equivalent to the previous discussion. If we take
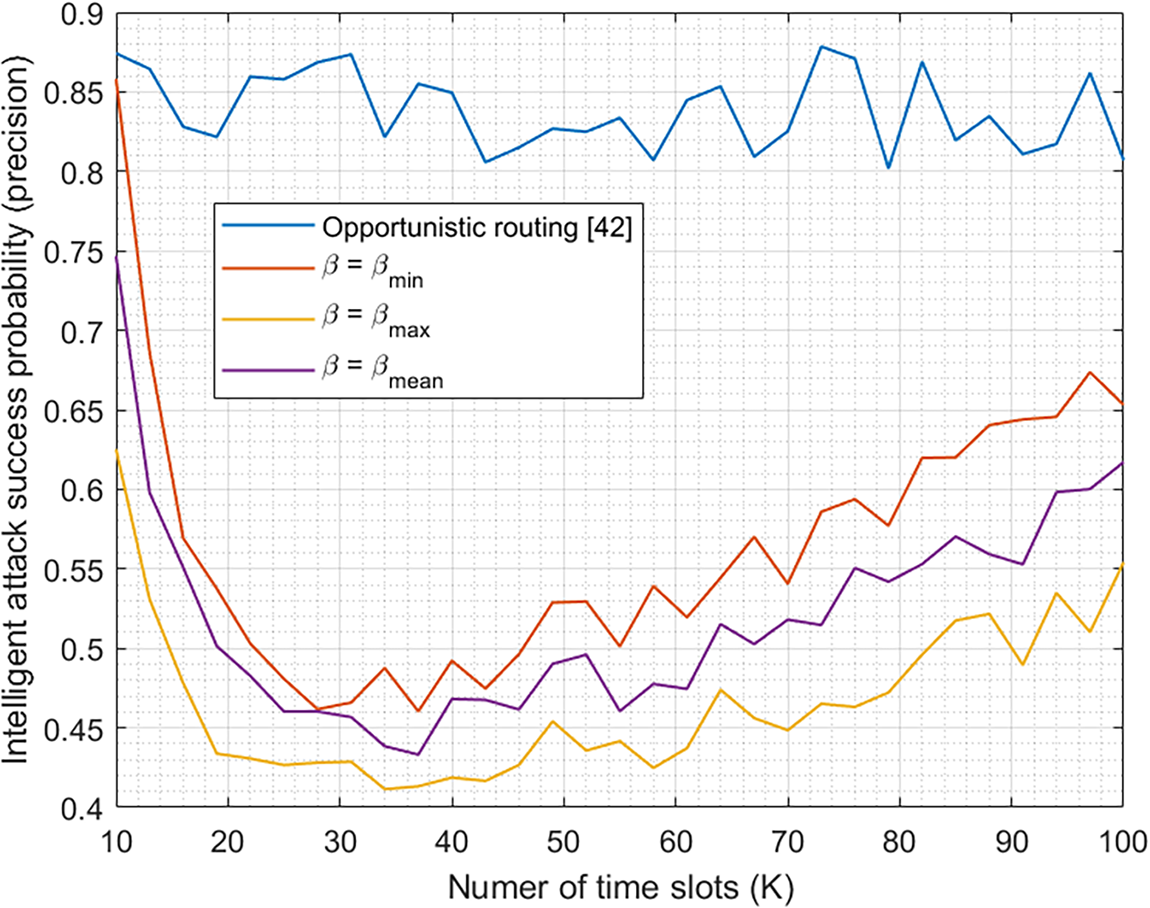
Figure 8: Probability of successful intelligent attack depending on
In conclusion, the proposed algorithm provides successful privacy-aware scheduling for data transmission in 6G-enabled ad hoc networks.
Finally, Fig. 9 shows the results of the second experiment. As can be seen, for the optimum values of
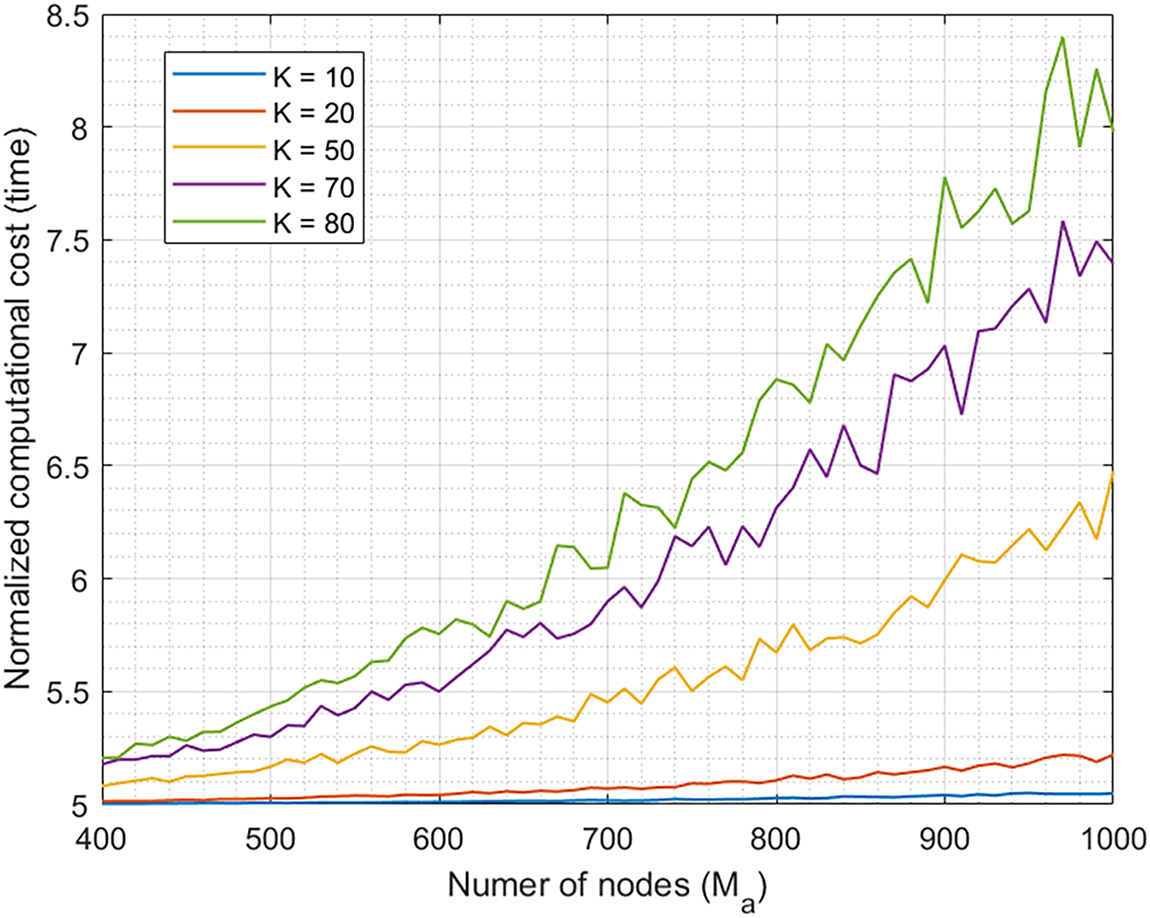
Figure 9: Normalized computational cost, showing a polynomial scalability
This increase in computational cost is inevitable, as new functions are included. But even in the worst scenario, the increase is below one magnitude order.
Regarding the changes with
In conclusion, the proposed algorithm matches the best computational behavior currently reported in the state of the art, and any increase does not achieve one additional magnitude order. So, the proposed solution is admissible, in computational terms, to be deployed in ad hoc networks.
In this paper, we propose a scheduling algorithm, so that extreme nodes can choose the optimum time and scheme to transmit private data and keep them safe, making compatible network performance and 6G extreme QoS. The scheduler uses a probabilistic function in which teletraffic theory and information diffusion models are combined to find the optimum balance between privacy and Quality-of-Service. Real private data are optimally mixed with false information generated by fuzzing algorithms, so the learning level in intelligent attackers is reduced but network performance is preserved. A probabilistic dynamical system is employed to represent and control the potential learning of intelligent attackers. While queue models and networks statistics are used to understand the behavior, lifecycle, and performance of ad hoc nodes.
An experimental validation based on simulation scenarios is provided. Results show that the probability of a successful intelligent attack reduces to 65% compared to ad hoc networks with no privacy protection strategy. Besides, an increase in the congestion probability is observed, caused by the additional fuzzed information injected by the proposed solution. But, in any case, the performance achieved is compatible with the expected 6G Quality-of-Service.
In practical scenarios, the proposed solution could enable critical real-time applications that handle private and sensitive data, such as Industry 5.0 services in essential infrastructures (e.g., power plants) or remote healthcare support in emergency situations. Future work should investigate its behavior in real environments, particularly in resource-constrained elements such as unattended fungible nodes. The use of real 6G testbeds will also be considered in future work.
Acknowledgement: None.
Funding Statement: This work has received funding from the European Commission by the Ruralities project (grant agreement no. 101060876).
Author Contributions: The authors confirm contribution to the paper as follows: study conception and design: Borja Bordel Sánchez; data collection: Ramón Alcarria, Borja Bordel Sánchez; analysis and interpretation of results: Ramón Alcarria, Tomás Robles; draft manuscript preparation: Borja Bordel Sánchez, Tomás Robles. All authors reviewed the results and approved the final version of the manuscript.
Availability of Data and Materials: The authors confirm that the data supporting the findings of this study are available within the article.
Ethics Approval: Not applicable.
Conflicts of Interest: The authors declare no conflicts of interest to report regarding the present study.
References
1. Xu H, Zhou Z, Zhang L, Sun Y, Chih-Lin I. BE-RAN: blockchain-enabled open RAN for 6G with DID and privacy-preserving communication. In: Proceedings of the 2024 IEEE Globecom Workshops (GC Wkshps); 2024 Dec 8–12; Cape Town, South Africa. p. 1015–21. doi:10.1109/gcwkshp64532.2024.11100619. [Google Scholar] [CrossRef]
2. Vijayakumar P, Azees M, Kozlov SA, Rodrigues JJPC. An anonymous batch authentication and key exchange protocols for 6G enabled VANETs. IEEE Trans Intell Transport Syst. 2022;23(2):1630–8. doi:10.1109/tits.2021.3099488. [Google Scholar] [CrossRef]
3. Wang Z, Xu Y, Liu J, Li Z, Li Z, Jia H, et al. An efficient data sharing scheme for privacy protection based on blockchain and edge intelligence in 6G-VANET. Wirel Commun Mob Comput. 2022;2022(1):5031112. doi:10.1155/2022/5031112. [Google Scholar] [CrossRef]
4. Singh Rawat G, Singh K, Shariq M, Das AK, Ashraf Chaudhry S, Lorenz P. BTC2PA: a blockchain-assisted trust computation with conditional privacy-preserving authentication for connected vehicles. IEEE Trans Intell Transport Syst. 2025;26(1):1134–48. doi:10.1109/tits.2024.3488184. [Google Scholar] [CrossRef]
5. Guo S, Zhang A, Wang Y, Feng C, Quek TQS. Semantic-enabled 6G communication: a task-oriented and privacy-preserving perspective. IEEE Netw. 2025;1:3547760. doi:10.1109/mnet.2025.3547760. [Google Scholar] [CrossRef]
6. Soni G, Chandravanshi K. A novel privacy-preserving and denser traffic management system in 6G-VANET routing against black hole attack. In: Sustainable communication networks and application. Singapore: Springer Nature; 2022. p. 649–63. doi:10.1007/978-981-16-6605-6_49. [Google Scholar] [CrossRef]
7. Liao L, Zhao J, Hu H, Sun X. Secure and efficient message authentication scheme for 6G-enabled VANETs. Electronics. 2022;11(15):2385. doi:10.3390/electronics11152385. [Google Scholar] [CrossRef]
8. Xu T, Wang N, Pang Q, Zhao X. Security and privacy of 6G wireless communication using fog computing and multi-access edge computing. Scalable Comput Pract Exp. 2024;25(2):770–81. doi:10.12694/scpe.v25i2.2629. [Google Scholar] [CrossRef]
9. Xu Q, Su Z, Li R. Security and privacy in artificial intelligence-enabled 6G. IEEE Netw. 2022;36(5):188–96. doi:10.1109/mnet.117.2100730. [Google Scholar] [CrossRef]
10. Nguyen T, Tran N, Loven L, Partala J, Kechadi MT, Pirttikangas S. Privacy-aware blockchain innovation for 6G: challenges and opportunities. In: Proceedings of the 2020 2nd 6G Wireless Summit (6G SUMMIT); 2020 Mar 17–20; Levi, Finland. p. 1–5. doi:10.1109/6gsummit49458.2020.9083832. [Google Scholar] [CrossRef]
11. Wang X, Lyu J, Peter JD, Kim BG. Privacy-preserving AI framework for 6G-enabled consumer electronics. IEEE Trans Consumer Electron. 2024;70(1):3940–50. doi:10.1109/tce.2024.3371928. [Google Scholar] [CrossRef]
12. Velliangiri S, Manoharan R, Ramachandran S, Rajasekar V. Blockchain based privacy preserving framework for emerging 6G wireless communications. IEEE Trans Ind Inf. 2022;18(7):4868–74. doi:10.1109/tii.2021.3107556. [Google Scholar] [CrossRef]
13. Bordel B, Alcarria R, Robles T. A blockchain ledger for securing isolated ambient intelligence deployments using reputation and information theory metrics. Wirel Netw. 2024;30(6):5887–903. doi:10.1007/s11276-023-03375-9. [Google Scholar] [CrossRef]
14. Guan Y, Lu R, Zheng Y, Zhang S, Shao J, Wei G. Toward privacy-preserving cybertwin-based spatiotemporal keyword query for ITS in 6G era. IEEE Internet Things J. 2021;8(22):16243–55. doi:10.1109/jiot.2021.3096674. [Google Scholar] [CrossRef]
15. Sánchez BB, Alcarria R, Robles T. A probabilistic trust model and control algorithm to protect 6G networks against malicious data injection attacks in edge computing environments. Comput Model Eng Sci. 2024;141(1):631–54. doi:10.32604/cmes.2024.050349. [Google Scholar] [CrossRef]
16. Zainuddin AA, Omar NF, Zakaria NN, Mbourou Camara NA. Privacy-preserving techniques for IoT data in 6G networks with blockchain integration: a review. Int J Perceptive Cogn Comput. 2023;9(2):80–92. doi:10.31436/ijpcc.v9i2.405. [Google Scholar] [CrossRef]
17. Ilyas I, Din IU, Alourani A, Ashraf MU. Lightweight consortium blockchain-enabled secured Vehicular ad Hoc Network using certificateless conditional privacy-preserving authentication mechanism. PLoS One. 2024;19(10):e0310267. doi:10.1371/journal.pone.0310267. [Google Scholar] [PubMed] [CrossRef]
18. Vuppula R, Pradhan HS. Blockchain-oriented location privacy preserving for cooperative spectrum sensing in 6G wireless networks. IET Blockchain. 2023;3(2):74–97. doi:10.1049/blc2.12025. [Google Scholar] [CrossRef]
19. Alharthi A, Ni Q, Jiang R. A privacy-preservation framework based on biometrics blockchain (BBC) to prevent attacks in VANET. IEEE Access. 2021;9:87299–309. doi:10.1109/access.2021.3086225. [Google Scholar] [CrossRef]
20. Zhang J, Jiang Y, Cui J, He D, Bolodurina I, Zhong H. DBCPA: dual blockchain-assisted conditional privacy-preserving authentication framework and protocol for vehicular ad hoc networks. IEEE Trans Mob Comput. 2024;23(2):1127–41. doi:10.1109/TMC.2022.3230853. [Google Scholar] [CrossRef]
21. Mustafa Hilal A, Alzahrani JS, Abunadi I, Nemri N, Al-Wesabi FN, Motwakel A, et al. Intelligent deep learning model for privacy preserving IIoT on 6G environment. Comput Mater Continua. 2022;72(1):333–48. doi:10.32604/cmc.2022.024794. [Google Scholar] [CrossRef]
22. Li H, Li S, Min G. Lightweight privacy-preserving predictive maintenance in 6G enabled IIoT. J Ind Inf Integr. 2024;39(3):100548. doi:10.1016/j.jii.2023.100548. [Google Scholar] [CrossRef]
23. Jai Vinita L, Vetriselvi V. Federated learning-based misbehaviour detection on an emergency message dissemination scenario for the 6G-enabled internet of vehicles. Ad Hoc Netw. 2023;144(3):103153. doi:10.1016/j.adhoc.2023.103153. [Google Scholar] [CrossRef]
24. Bordel B, Alcarria R, Chung J, Kettimuthu R. Efficient and choreographed quality-of- service management in dense 6G verticals with high-speed mobility requirements. Integr Comput Aided Eng. 2024;31(2):173–95. doi:10.3233/ica-230722. [Google Scholar] [CrossRef]
25. Inzillo V, Garompolo D, Giglio C. Enhancing smart city connectivity: a multi-metric CNN-LSTM beamforming based approach to optimize dynamic source routing in 6G networks for MANETs and VANETs. Smart Cities. 2024;7(5):3022–54. doi:10.3390/smartcities7050118. [Google Scholar] [CrossRef]
26. Al-Rubaye RHK, Türkben AK. Using artificial intelligence to evaluating detection of cybersecurity threats in ad hoc networks. Babylon J Netw. 2024;2024:45–56. doi:10.58496/bjn/2024/006. [Google Scholar] [CrossRef]
27. Li L, Zhu F, Eicher-Miller HA, Thomas JG, Huang Y, Sazonov E. Extra-lightweight AI-based privacy preserving framework for egocentric wearable cameras. In: Proceedings of the 2025 IEEE/CVF Conference on Computer Vision and Pattern Recognition Workshops (CVPRW); 2025 Jun 11–12; Nashville, TN, USA. p. 401–10. doi:10.1109/cvprw67362.2025.00044. [Google Scholar] [CrossRef]
28. Su H, Dong S, Zhang T. A hybrid blockchain-based privacy-preserving authentication scheme for vehicular ad hoc networks. IEEE Trans Veh Technol. 2024;73(11):17059–72. doi:10.1109/tvt.2024.3424786. [Google Scholar] [CrossRef]
29. Cheng G, Huang J, Wang Y, Zhao J, Kong L, Deng S, et al. Conditional privacy-preserving multi-Doma in authentication and pseudonym management for 6G-enabled IoV. IEEE Trans Inf Forensics Secur. 2024;19(5):10206–20. doi:10.1109/tifs.2023.3314211. [Google Scholar] [CrossRef]
30. Zhu F, Yi X, Abuadbba A, Khalil I, Huang X, Xu F. A security-enhanced certificateless conditional privacy-preserving authentication scheme for vehicular ad hoc networks. IEEE Trans Intell Transport Syst. 2023;24(10):10456–66. doi:10.1109/tits.2023.3275077. [Google Scholar] [CrossRef]
31. Al Sibahee MA, Nyangaresi VO, Abduljabbar ZA, Luo C, Zhang J, Ma J. Two-factor privacy-preserving protocol for efficient authentication in Internet of vehicles networks. IEEE Internet Things J. 2024;11(8):14253–66. doi:10.1109/JIOT.2023.3340259. [Google Scholar] [CrossRef]
32. Xu T, Xu C, Xu Z. An efficient three-factor privacy-preserving authentication and key agreement protocol for vehicular ad-hoc network. China Commun. 2021;18(12):315–31. doi:10.23919/jcc.2021.12.020. [Google Scholar] [CrossRef]
33. Banafaa M, Shayea I, Din J, Hadri Azmi M, Alashbi A, Ibrahim Daradkeh Y, et al. 6G mobile communication technology: requirements, targets, applications, challenges, advantages, and opportunities. Alex Eng J. 2023;64:245–74. doi:10.1016/j.aej.2022.08.017. [Google Scholar] [CrossRef]
34. Lin JC, Srivastava G, Zhang Y, Djenouri Y, Aloqaily M. Privacy-preserving multiobjective sanitization model in 6G IoT environments. IEEE Internet Things J. 2021;8(7):5340–9. doi:10.1109/jiot.2020.3032896. [Google Scholar] [CrossRef]
35. Xia Y, Wu L, Zheng X, Yu T, Jin J. Data dissemination with trajectory privacy protection for 6G-oriented vehicular networks. IEEE Internet Things J. 2022;9(21):21469–80. doi:10.1109/JIOT.2022.3183406. [Google Scholar] [CrossRef]
36. Tamilvizhi T, Surendran R, Andres Tavera Romero C, Sadish Sendil M. Privacy preserving reliable data transmission in cluster based vehicular adhoc networks. Intell Autom Soft Comput. 2022;34(2):1265–79. doi:10.32604/iasc.2022.026331. [Google Scholar] [CrossRef]
37. Karyakarte M, Agarkar A, Kulkarni L, Patil M, Chavhan G, Sule B. Dynamic opportunistic routing protocol for ad-hoc Internet of Vehicles (IoV). Computing. 2024;106(6):1707–28. doi:10.1007/s00607-023-01248-9. [Google Scholar] [CrossRef]
38. Goyal M, Mahmoud QH. A systematic review of synthetic data generation techniques using generative AI. Electronics. 2024;13(17):3509. doi:10.3390/electronics13173509. [Google Scholar] [CrossRef]
39. Kruse R, Mostaghim S, Borgelt C, Braune C, Steinbrecher M. Multi-layer perceptrons. In: Computational intelligence. Berlin/Heidelberg, Germany: Springer; 2022. p. 53–124. doi:10.1007/978-3-030-42227-1_5. [Google Scholar] [CrossRef]
40. Ahmed S, Khan ZA, Mohsin SM, Latif S, Aslam S, Mujlid H, et al. Effective and efficient DDoS attack detection using deep learning algorithm, multi-layer perceptron. Future Internet. 2023;15(2):76. doi:10.3390/fi15020076. [Google Scholar] [CrossRef]
41. Khalaf BA, Mostafa SA, Mustapha A, Abed Mohammed M, Abduallah WM. Comprehensive review of artificial intelligence and statistical approaches in distributed denial of service attack and defense methods. IEEE Access. 2019;7:51691–713. doi:10.1109/access.2019.2908998. [Google Scholar] [CrossRef]
42. Yamamoto R, Yamazaki T, Ohzahata S. VORTEX: network-driven opportunistic routing for ad hoc networks. Sensors. 2023;23(6):2893. doi:10.3390/s23062893. [Google Scholar] [PubMed] [CrossRef]
Cite This Article
 Copyright © 2026 The Author(s). Published by Tech Science Press.
Copyright © 2026 The Author(s). Published by Tech Science Press.This work is licensed under a Creative Commons Attribution 4.0 International License , which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue View Full Text
View Full Text Download PDF
Download PDF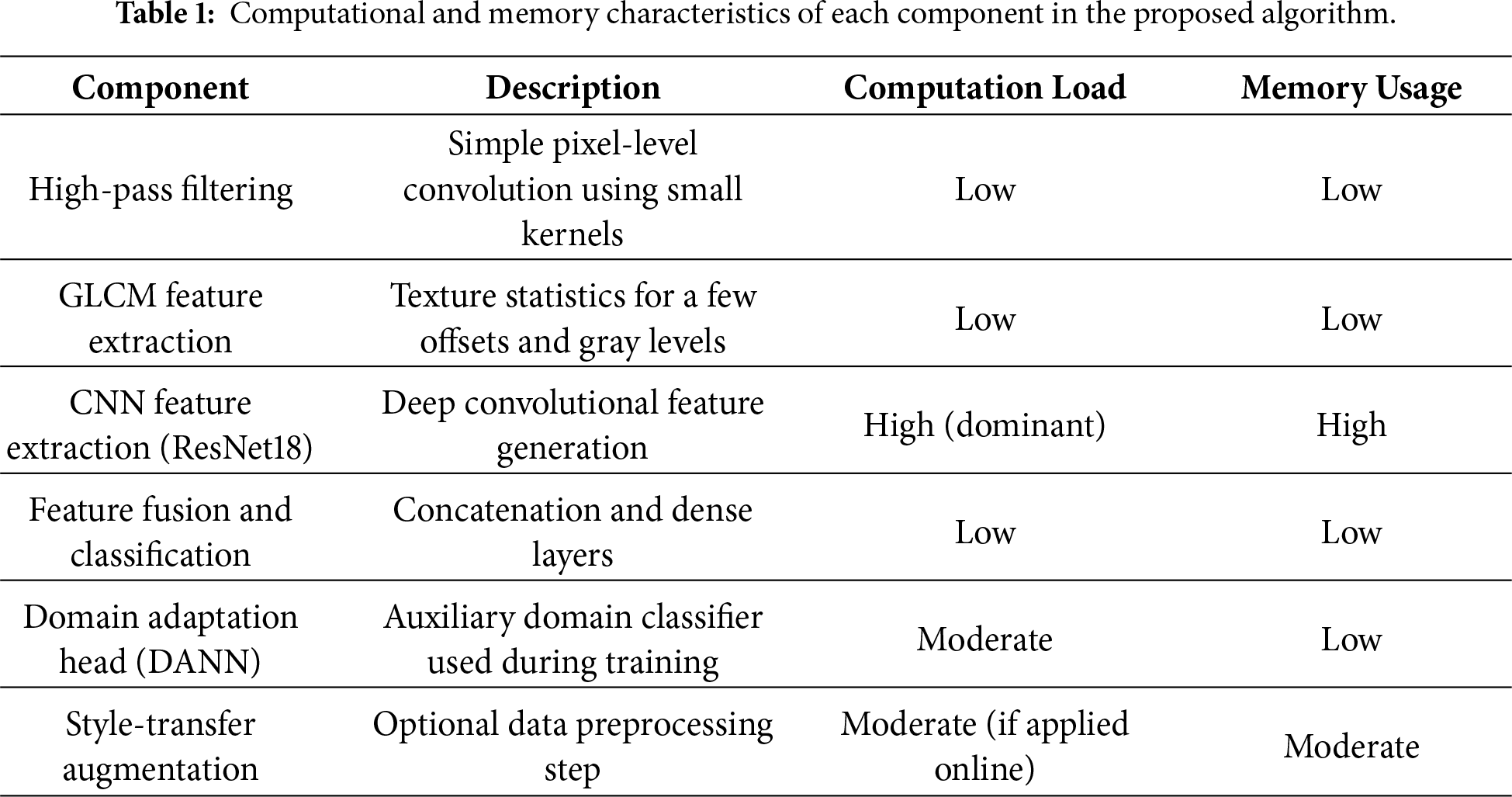
 Downloads
Downloads
 Citation Tools
Citation Tools