 Open Access
Open Access
ARTICLE
Arvind Prasad1,*, Ibrahim Aljubayri2, Mohammad Zubair Khan3,*, Abdulfattah Noorwali4
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.082021
(This article belongs to the Special Issue: Emerging Technologies in Information Security: Modeling, Algorithms, and Applications)
Abstract Intrusion detection in large-scale IoT deployments becomes particularly challenging during ongoing attack scenarios, where malicious traffic may temporarily dominate benign traffic. In such conditions, streaming network data exhibits severe class imbalance in favor of attack traffic, while device behavior remains heterogeneous, non-identically distributed (non-IID), and temporally evolving. Within federated learning environments, this imbalance can destabilize early aggregation rounds, dominant attack gradients bias the global model, distort decision boundaries, and degrade reliable discrimination of residual benign behavior. Since the server has no access to raw data, these effects can persist across communication rounds if not addressed… More >
 Open Access
Open Access
ARTICLE
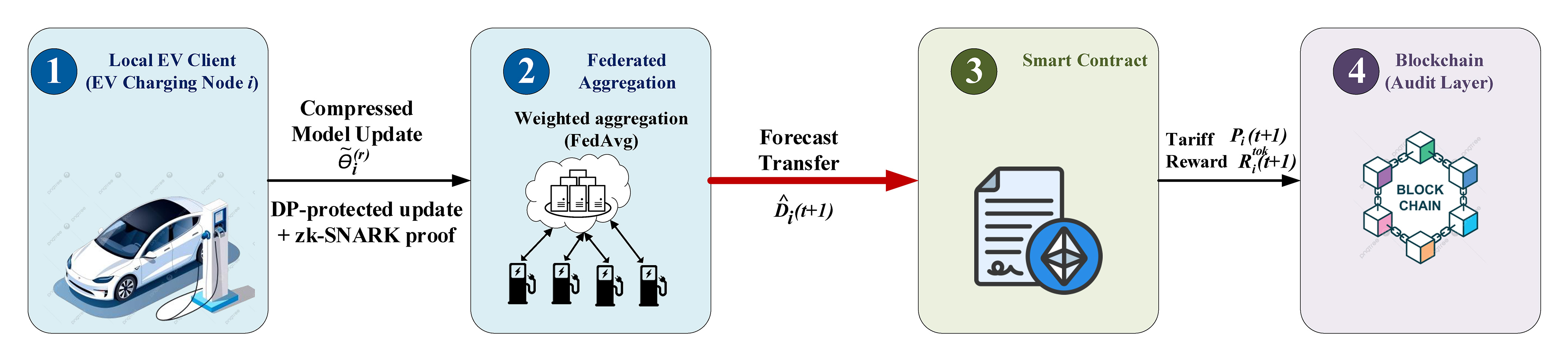
Lilia Tightiz1, L. Minh Dang2,3, Hyosik Yang1,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.081849
Abstract We present QFedFormer, a federated transformer for dynamic electric vehicle (EV)-charging price prediction that combines quantization-aware training, SHAP-guided explainability, and blockchain-based incentives. The framework trains across distributed charging stations without centralizing user data, and programmable contracts set tariffs from forecasted demand and user-declared flexibility, while token rewards are derived from SHAP-based utility scores and anchored on-chain via Merkle proofs. On a real-world dataset, QFedFormer attains an energy-demand RMSE of
Graphic Abstract
 Open Access
Open Access
ARTICLE
Zhou Fang#, Jiaqi Zhong#, Jun Luo*, Yuanzun Sun
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.081333
(This article belongs to the Special Issue: Advances in Computational Fracture Mechanics: Theories, Techniques, and Applications)
Abstract The t′ phase of yttria-stabilized zirconia (t′-YSZ) is the most extensively used top coat material in thermal barrier coatings (TBCs). Its relatively high fracture toughness is among the most important factors that enable t′-YSZ to stand out from other candidate ceramics. Unveiling the toughening mechanisms of t′-YSZ is conducive to the development of next-generation top-coat materials. In this paper, a coupled phase field model is proposed to study crack growth and domain evolution in polycrystalline t′-YSZ. Two distinct polycrystal microstructures are considered to investigate the impact of the initial domain structure on the toughening behavior. In Polycrystal I,… More >
 Open Access
Open Access
ARTICLE
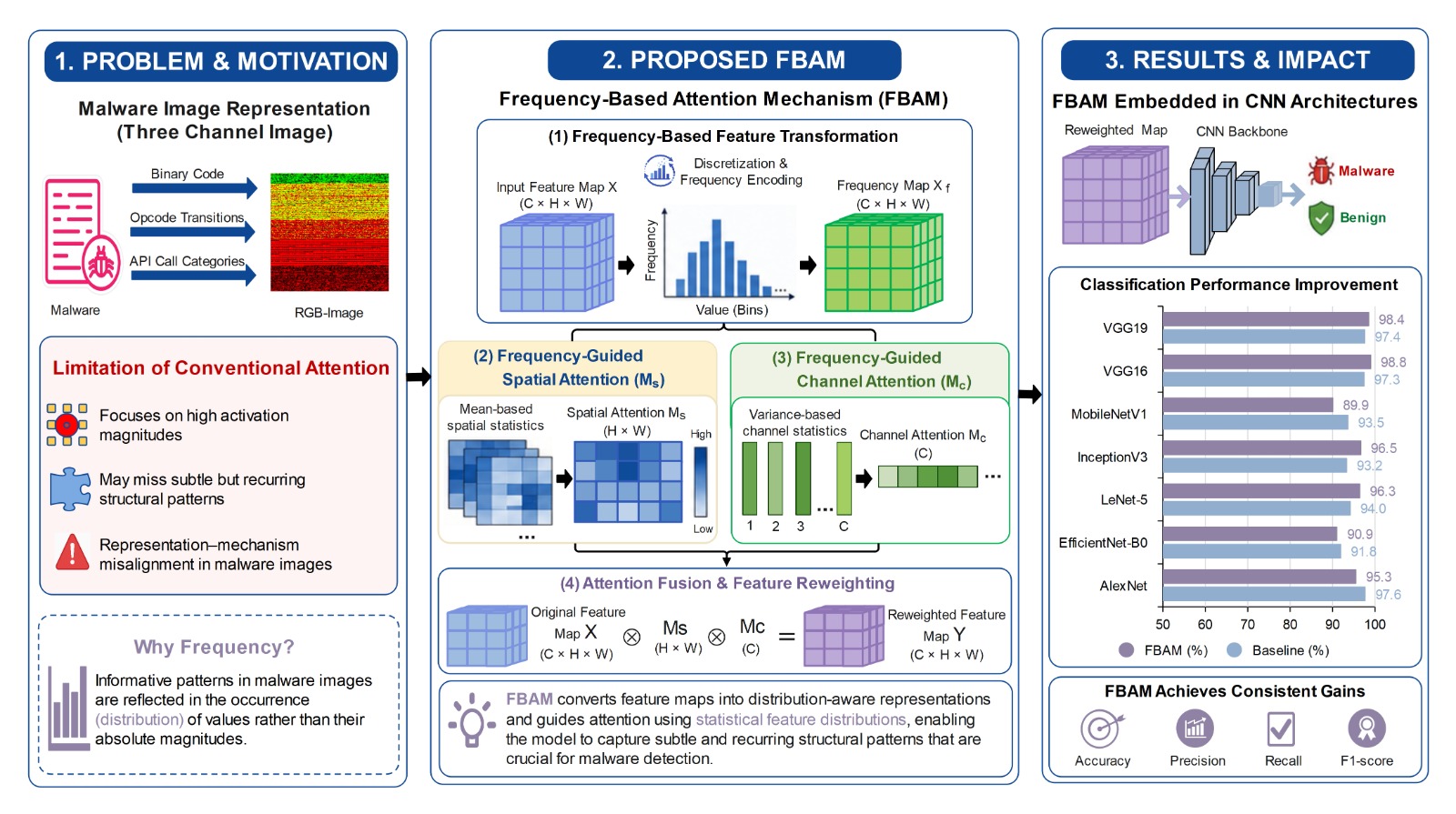
Anis Elgarduh1, Anazida Zainal1, Fuad A. Ghaleb2, Sultan Noman Qasem3,*, Abdullah M. Albarrak3, Faisal Saeed2
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080862
(This article belongs to the Special Issue: Emerging Technologies in Information Security: Modeling, Algorithms, and Applications)
Abstract The rapid growth and increasing sophistication of malware pose significant challenges to traditional detection methods. Convolutional neural network (CNN)-based malware image classification methods have emerged as a promising approach by transforming binary files into visual representations and enabling automated feature extraction. To enhance discriminative learning, recent studies have incorporated attention mechanisms originally developed for natural image and natural language processing tasks. However, these mechanisms embed inductive biases that assume spatial coherence and visually salient semantics, assumptions that do not necessarily hold in malware image representations, where informative patterns may be subtle, structurally encoded, and globally… More >
Graphic Abstract
 Open Access
Open Access
ARTICLE
Manal Ghannam1, Bilgen Kaymakamzade1,2, Muhammad Farman1,3,4, Kottakkaran Sooppy Nisar5,*, Mohammed Altaf Ahmed6
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.081075
(This article belongs to the Special Issue: Mathematical Aspects of Computational Biology and Bioinformatics-III)
Abstract In Vitro Fertilization (IVF) has been a major medical advancement in the field of fertility treatment.
It has helped millions of individuals and couples overcome infertility by providing a workable option. It involves
removing eggs from the ovaries of a female, fertilizing those eggs with male sperm in a monitored lab condition. In
this work, we developed a new model to show the success of In Vitro Fertilization rates in women through a fractional-
order compartmental modeling framework by using real data. The developed model is analyzed statistically, and the
biological feasibility of the model. The Lipschitz… More >
 Open Access
Open Access
ARTICLE
Qingxiang Meng1,2,*, Zijie He1,2, Yajun Cao1,2, Weijiang Chu3
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.083227
(This article belongs to the Special Issue: Advanced Computational Methods in Multiphysics Phenomena)
Abstract Constitutive modeling for geomaterials remains challenging because of limited data availability, strong nonlinearity, pressure sensitivity, and the non-smooth characteristics of commonly used yield surfaces. This study presents a deep-learning-based constitutive method for geomaterials that incorporates a neural stress-integration procedure based on the cutting plane algorithm (CPA). Two compact fully connected networks are trained to learn the yield function and its stress gradient from an augmented stress-state dataset. The trained networks are then incorporated into a cutting plane return-mapping procedure, in which only first-order information is required for the plastic stress return. This avoids explicit analytical More >
 Open Access
Open Access
ARTICLE
Aravapalli Rama Satish1, Sai Babu Veesam2,*, Shonak Bansal3,*, Krishna Prakash4, Mohammad Rashed Iqbal Faruque5,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080403
Abstract Real-time video streams now flood everything from security cameras to social media, yet current summarization systems still stumble when audio, visual, and semantic cues unfold with tangled cause–and–effect patterns. Most cross-modal transformers treat correlations as if time were a flat canvas, ignoring how an early sound might trigger a later visual event in the process. They also lack mechanisms to predict tracking uncertainty, adapt to narrative shifts, or evolve their own evaluation criteria, leaving summaries brittle and often incoherent in process. To address these gaps, we propose a Cross-Modal Context Fusion framework built from five… More >
 Open Access
Open Access
ARTICLE
Miguel A. Millán1,*, Rubén Galindo2, Fausto Molina-Gómez1
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080219
(This article belongs to the Special Issue: Soft Computing Applications of Civil Engineering including AI-based Optimization and Prediction)
Abstract Low-density volcanic rocks have specific geomechanical properties that require complex laboratory tests and characterization that are not usually available in common geotechnical studies. A pyroclastic rock behaves at sufficiently “low” stress levels as if it were a conventional rock under the action of an external load, but when subjected to higher stresses, the bonds between its particles can break, leading to a sudden decrease in its volume and the reorganization of its particles, thus forming a more compact structure than the initial one. This process is known as “mechanical collapse” and involves a drastic change… More >
 Open Access
Open Access
ARTICLE
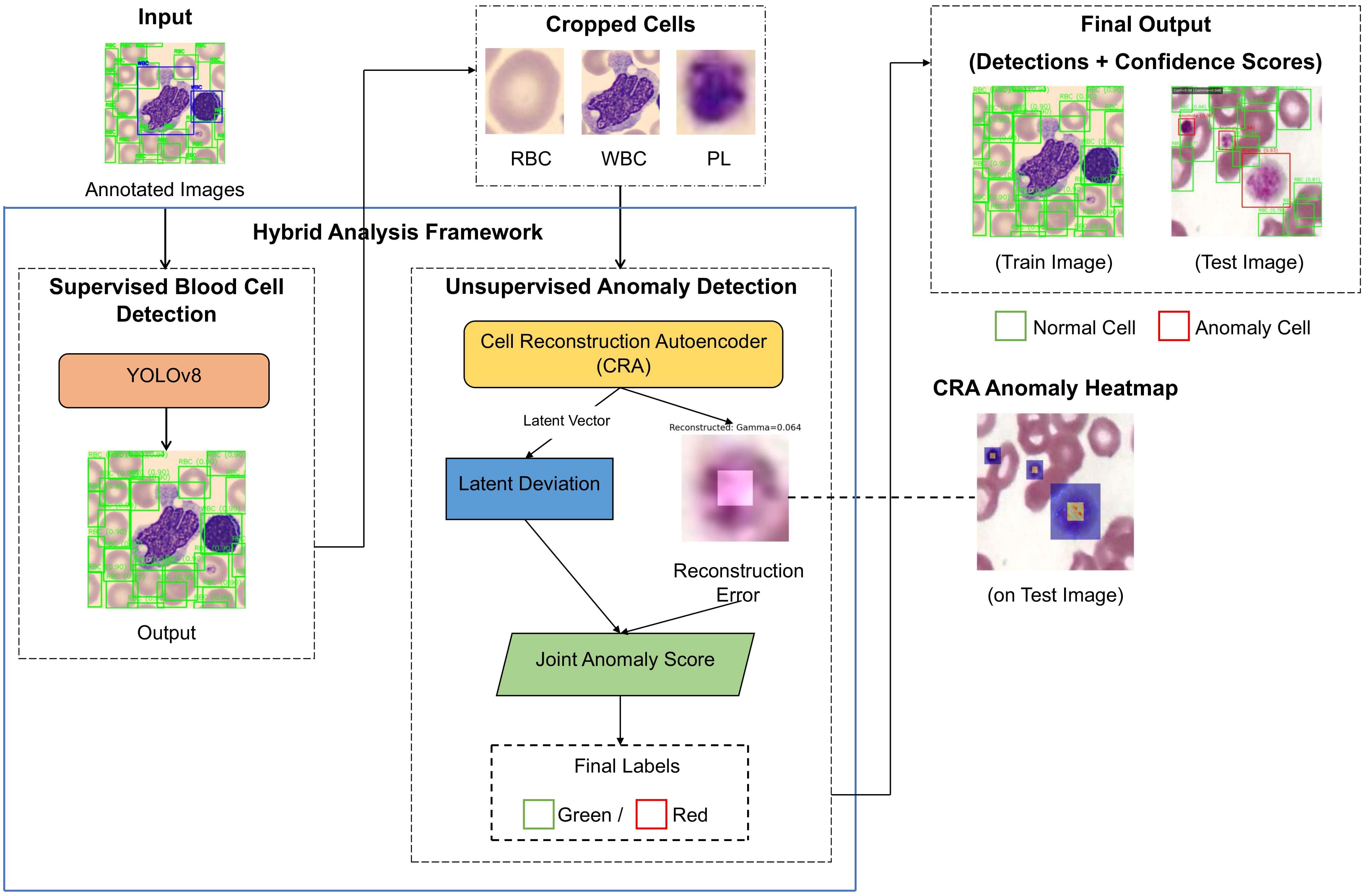
Issac Neha Margret, Rajakumar Krishnan*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.079104
Abstract Background: Examining peripheral blood smears is a vital diagnostic tool in hematology. Although deep learning-based automated systems have improved the accuracy of blood cell detection, most current methods depend on fully supervised learning and need extensive annotations to identify unusual cell shapes. Clinical practice often lacks these complete annotations, limiting the ability to generalize to rare or unseen abnormalities. To address this issue of incomplete annotated data, this paper introduces a hybrid framework that recognizes anomalies for reliable and clear analysis of peripheral blood smears. Methods: The proposed framework combines supervised blood cell detection with… More >
Graphic Abstract
 Open Access
Open Access
ARTICLE
Yuyan Ning1,2, Haiyun Huang1, Legend Zhang3, Wei Wei4, Hao Quan5, Bo Yang1,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.083345
(This article belongs to the Special Issue: Emerging Artificial Intelligence Technologies and Applications-II)
Abstract Hybrid CNN-Transformer models are widely used in medical image segmentation because they combine CNN-based local feature extraction with Transformer-based global context modeling. Despite their popularity, these models face several challenges, including computational complexity, noise blurring, and information loss. This paper proposes an enhanced convolutional attention network (ECANet) for liver segmentation. ECANet uses a U-shaped architecture with efficient channel-attention-based skip connections. Both the encoder and decoder are constructed using enhanced convolutional Transformer (ECT) blocks, where group convolution is integrated into the convolutional attention module for efficient Token embedding and channel disentanglement, and a Token-wise multi-layer perceptron More >
 Open Access
Open Access
ARTICLE
Maram Fahaad Almufareh1,*, Samabia Tehsin2,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.081129
(This article belongs to the Special Issue: Mathematical Aspects of Computational Biology and Bioinformatics-III)
Abstract This article presents a Hierarchical Pathway-Masked Attention Autoencoder (H-PAAE), a biologically inspired representation-learning framework that enables explainable AI-guided cancer diagnosis. The model directly integrates the curated MSigDB Hallmark pathways, introducing pathway-constrained information flow and mechanistic interpretability through multi-level attention mechanisms. Based on TCGA RNA-seq data from 33 tumor types, H-PAAE compresses approximately 20,000 genes into a 128-dimensional latent space while preserving biologically meaningful structure. When used with XGBoost classification, H-PAAE delivers 92.37% test accuracy and 99.38% macro-AUROC with robust cross-validation results (92.5
 Open Access
Open Access
ARTICLE
Kottakkaran Sooppy Nisar1,*, Muhammad Farman2,3,4, Ali Hasan3, Mohammed Altaf Ahmed5, Mohammad Tabish6
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080973
(This article belongs to the Special Issue: Recent Developments on Computational Biology-II)
Abstract A global health concern, neurodegenerative disorders like Parkinson’s and Alzheimer’s impact both mental and physical functioning. The complex interplay among immunological response, protein accumulation, and brain health necessitates sophisticated mathematical modeling. This study introduces a fractional-order mathematical model using the Mittag-Leffler derivative to describe the dynamics of neurodegeneration, incorporating key biological factors such as functioning and infected neurons, extracellular alpha-synuclein, microglia, and T-cells. A fundamental assumption of the model is that neuronal deterioration is influenced by memory effects, where past states impact current disease progression, making fractional-order calculus more suitable than traditional integer-order models. The… More >
 Open Access
Open Access
ARTICLE
Wafa Alagal1,*, Zanyar A. Ameen2,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.083259
Abstract Diabetes remains a major global health challenge and requires diagnostic systems capable of handling uncertainty and sometimes conflicting clinical evidence. In this study, a Disc T-Spherical Fuzzy (DT-SF) TOPSIS framework is proposed for diabetes risk assessment, where the radius parameter is used to encode the confidence associated with each diagnostic attribute. The methodology also integrates the Analytic Hierarchy Process (AHP) to determine the relative importance of several key risk factors, including blood glucose, body mass index, family history, lifestyle factors, and clinical symptoms. One important feature of the proposed approach is the ternary classification scheme,… More >
 Open Access
Open Access
ARTICLE
Lin Fang1,2, Razi Abdul-Rahman1,*, Cheng-Fu Yang3,4,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080387
Abstract Parallel mechanisms are extensively employed in industrial logistics, food processing, and medical applications. Due to the strong nonlinearity and cross-axis coupling inherent in closed-chain kinematics, fault diagnostic performance is highly sensitive to signal perturbations and class imbalance under noisy measurement conditions. Furthermore, diagnostic models trained under single-fault scenarios often exhibit notable performance degradation when transferred to compound fault conditions as a result of distribution shift. In this study, a Delta 3D printer, as a representative parallel mechanism, is adopted as the experimental platform. An interpretable three-stage diagnostic framework is proposed, in which compound fault diagnosis… More >
 Open Access
Open Access
ARTICLE
Yunlong Teng1, Ying Liu2, Jianhong Liang1, Jinshang Luo3,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.082594
(This article belongs to the Special Issue: Machine Learning-Assisted Structural Integrity Assessment and Design Optimization under Uncertainty)
Abstract Over the past decades, surrogate model-aided reliability analysis approaches grounded in active learning have undergone extensive development. However, Gaussian process models like Kriging suffer from severe computational burdens when handling high-dimensional problems or large samples. Conversely, machine learning algorithms such as extreme learning machines exhibit high computational efficiency but lack variance output and stability, making them difficult to employ for adaptive active learning strategies. To address these limitations, this study proposes a population Monte Carlo method based on an adaptive closed neuron extreme learning machine. First, a closed neuron strategy uses a consistency metric to… More >
 Open Access
Open Access
ARTICLE
Mahmood Ashraf1,2, Nuha Zamzami3, Shtwai Alsubai4, Raed Alharthi5, Muhammad Umer6,*, Yunyoung Nam7, Yongwon Cho7,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.078738
(This article belongs to the Special Issue: Emerging Artificial Intelligence Technologies and Applications-II)
Abstract Hyperspectral image (HSI) denoising is a crucial preprocessing step that significantly enhances the performance of downstream applications, such as object detection and classification. Whereas deep neural networks have achieved remarkable performance in HSI denoising, many existing models rely mostly on vanilla convolutions, which often fail to capture fine-grained noise patterns and structural details in real-time HSIs. To address these limitations, we propose a novel Center-Difference Convolutional Network (CDCN) designed to effectively suppress various noise types while preserving the inherent structure of HSIs. By leveraging center-difference convolution (CDC), our model captures both gradient and intensity information… More >
 Open Access
Open Access
ARTICLE
Cristina Roxana Popa1, Maria Tănase2,*, Gheorghe Brănoiu3, Elena-Emilia Sirbu4,5, Cătălina Călin4
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.082244
(This article belongs to the Special Issue: Computational Modelling of Advanced Polymeric Materials and Structures)
Abstract Glass-fiber-reinforced polymer (GFRP) pipes are increasingly used in aggressive environments due to their high corrosion resistance and favorable mechanical properties. However, long-term exposure to saline environments and elevated temperatures can lead to degradation of their structural performance. This study investigates the influence of accelerated saltwater aging on the tensile behavior and structural characteristics of GFRP pipes and proposes machine-learning-based predictive models for the ultimate tensile strength (UTS). Experimental specimens were immersed in a 3.5% NaCl solution under controlled temperature and exposure time conditions. Tensile testing revealed that the unexposed samples exhibited a maximum UTS of… More >
 Open Access
Open Access
ARTICLE
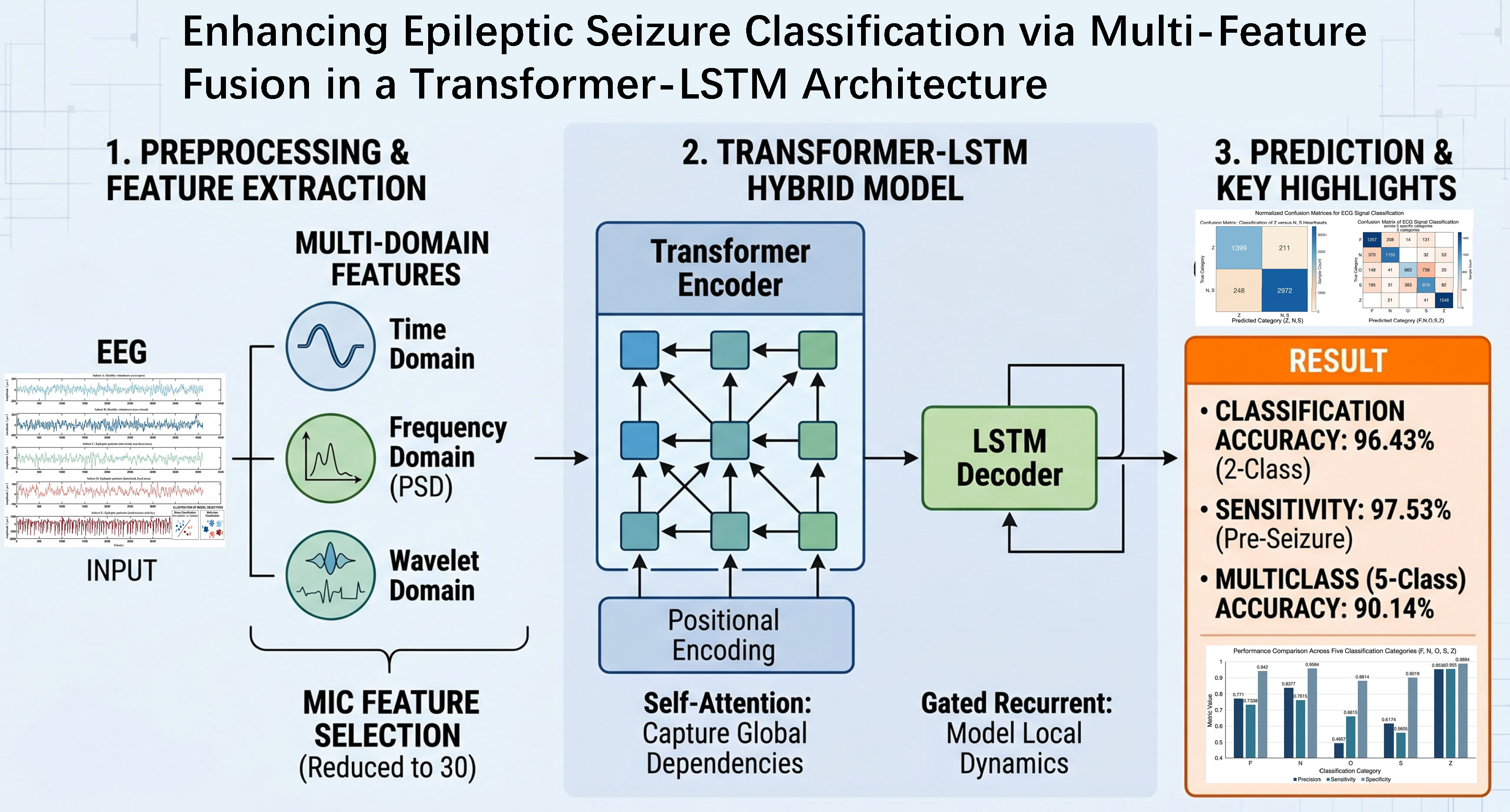
Gaoteng Yuan1,*, Ping Qiu2, Qika Lin3, Jianchu Lin1, Xiang Li1, Dongping Gao4
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.081152
Abstract Epilepsy is a chronic neurological disorder characterized by recurrent seizures, posing significant challenges to patients’ quality of life. Accurate classification of seizure states is crucial for effective intervention. This paper presents a deep learning-based approach for epileptic seizure classification by integrating multi-feature analysis of electroencephalogram (EEG) signals. The proposed method begins with signal preprocessing, including denoising, segmentation, and label construction. Subsequently, a comprehensive set of temporal, spectral, and wavelet-based features—such as signal mean, power, heart rate, and wavelet coefficients—is extracted. Feature selection is then performed using the Maximal Information Coefficient (MIC) to identify the most… More >
Graphic Abstract
 Open Access
Open Access
ARTICLE
Ahmed Muthanna Nori1,*, Ali Kadhim Abdulabbas1, Safwan Nadweh2, Abdullrahman A. Al-Shammaa3,*, Hassan M. Hussein Farh3
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080276
Abstract Voltage instability and reactive power fluctuations represent major challenges for DFIG-based wind turbines under load variations and grid disturbances. This paper proposes an integrated fault ride-through enhancement scheme based on a STATCOM supported by a Battery Energy Storage System (BESS) and a braking chopper (BC). The STATCOM regulates the DFIG terminal voltage through dynamic reactive power compensation using a coordinated outer voltage loop and inner synchronous dq-axis current control. The BESS supports the STATCOM DC side and enables fast bidirectional power exchange, while the BC suppresses overvoltage in the DFIG back-to-back converter DC-link during fault… More >
 Open Access
Open Access
ARTICLE
Botambu Collins, Jin-Taek Seong*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.082245
Abstract Classical image denoising methods remain relevant in practical scenarios where training data or noise models are unavailable, yet their performance is highly sensitive to parameter selection. Non-Local Means (NLM) is a representative example whose effectiveness depends critically on smoothing strength, patch size, and search window configuration. This paper formulates NLM parameter selection as a black-box optimization problem under unknown noise conditions and employs adaptive metaheuristic optimization strategies for this task. We propose an adaptive optimization framework that integrates rank-based perturbation, opposition-based learning, Lévy-flight exploration, and noise-aware parameter constraints to improve robustness and convergence. The proposed More >
 Open Access
Open Access
ARTICLE
Pasquale De Luca1,2,*, Livia Marcellino1
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.082664
(This article belongs to the Special Issue: Advances in Mathematical Modeling: Numerical Approaches and Simulation for Computational Biology)
Abstract Osteosarcoma is the most common primary malignant bone tumor in pediatric populations. This work presents an extended Physics-Informed Neural Network framework that incorporates interferon-gamma (IFN-
 Open Access
Open Access
ARTICLE
Cesar Guevara*, Victoria Lopez
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.081473
(This article belongs to the Special Issue: Machine Learning and Data Fusion for Autonomous Control and Surveillance Systems)
Abstract This study presents a mobile expert system for on-device detection and short-horizon forecasting of aggression using affordable edge hardware. The proposed framework combines lightweight on-body and ambient signals, compact sequential predictors, and an interpretable fuzzy decision layer that converts calibrated probabilities into actionable and auditable alerts. In a subject-held-out pilot study with 10 independent participants, the system achieved a macro-averaged F1 score of 98.3% and an area under the receiver operating characteristic curve of 0.998 on the held-out test split. These results should be interpreted as pilot-scale held-out estimates rather than as definitive evidence of… More >
 Open Access
Open Access
ARTICLE
Jaewan Lee1, Seonghwan Park2, Junghwan Kook1,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080930
(This article belongs to the Special Issue: Machine Learning, Data-Driven and Novel Approaches in Computational Mechanics)
Abstract In bearing fault diagnosis for Prognostics and Health Management (PHM), the overall performance of data-driven models is strongly influenced by the coupled effects of preprocessing, model configuration, and decision fusion. However, these components are often optimized independently, resulting in fragmented workflows that limit global optimality, reproducibility, and computational efficiency of the model. This study presents a computationally unified three-stage sequential optimization framework that systematically coordinates the preprocessing selection, model hyperparameter optimization, and decision-level fusion within a consistent surrogate-based optimization architecture. In the first stage, candidate preprocessing schemes reflecting physical fault mechanisms—outer race, inner race, rolling… More >
 Open Access
Open Access
ARTICLE
Hong Min1,*, Yousef Ibrahim Daradkeh2, Jung Taek Seo3,*, Mohd Anjum4, Sana Shahab5
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080871
(This article belongs to the Special Issue: Emerging Technologies in Information Security: Modeling, Algorithms, and Applications)
Abstract This study presents a computational modeling framework for efficient and secure computation offloading in Internet of Things (IoT)-enabled smart contract systems. The integration of IoT, edge computing, and blockchain introduces significant challenges, including limited device capacity, high verification cost, and scalability constraints. Existing blockchain verification approaches depend on computationally intensive cryptographic operations that are inefficient for resource-constrained IoT devices, resulting in increased latency, energy consumption, and transaction costs. To address these issues, this study proposes the Zero-Knowledge Fuzzy Logic Offloading and Rollup (Z-FLOR) framework, an adaptive and energy-efficient model designed to enable secure and verifiable… More >
 Open Access
Open Access
ARTICLE
Riad Mollik Babu1, Md. Shafiul Alam2,*, Md. Hasibur Rahman3, Mohammad Ali2, Md. Alamgir Hossain4, Md. Arifuzzaman5
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.082366
Abstract The increasing penetration of solar photovoltaic (PV) systems into power grids poses challenges due to their inherent intermittency and variability, which can compromise grid stability and reliability. Hybridizing solar PV with wind energy and a battery energy storage system (BESS) offers a promising solution by leveraging resource complementarity and providing fast frequency response. This study presents a techno-economic and environmental assessment of a hybrid renewable energy system. Wind turbines and a BESS are integrated with the existing 7.5 MW Sirajganj Solar PV Power Plant in Bangladesh. The proposed hybrid configuration is evaluated using real-world operational… More >
 Open Access
Open Access
ARTICLE
Jinha Kim1, Hwankuk Kim2,*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.082504
(This article belongs to the Special Issue: Advanced Security and Privacy for Future Mobile Internet and Convergence Applications: A Computer Modeling Approach)
Abstract The advent of 5th Generation (5G) mobile networks has introduced Network Slicing as a core mechanism for supporting heterogeneous vertical services—such as enhanced Mobile Broadband (eMBB), Ultra-Reliable Low-Latency Communication (URLLC), and massive Machine-Type Communication (mMTC) over a shared physical infrastructure, thereby significantly expanding the attack surface at the User Plane Function (UPF). Securing this multi-slice environment requires intrusion detection systems that can simultaneously accommodate the statistical heterogeneity of per-slice traffic and the stringent Quality of Service (QoS) constraints of real-time slices, yet the practical cost of obtaining high-quality labeled traffic in operational 5G cores remains… More >
 Open Access
Open Access
ARTICLE
Samuel Martínez-Gutiérrez1,*, Carlos Gutiérrez1, Alejandro Merino1, Diego García-Álvarez2, Daniel Sarabia1
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.081247
(This article belongs to the Special Issue: Intelligent Control and Machine Learning for Renewable Energy Systems and Industries)
Abstract Accurate modelling of power production in wind power systems is essential for optimizing their real-time operation and meeting technical or economic objectives. However, the precise modelling of wind turbine power output remains challenging, particularly when relying on conventional parametric models, which often struggle to capture complex or non-linear behaviors. This paper compares three modelling approaches to estimate the power produced by a real wind turbine (a Senvion MM82/2050 located in France): one parametric, based on analytical expressions of the power coefficient CP(λ, β); another nonparametric, which uses Gaussian processes (GP) to probabilistically model the relationship between… More >
 Open Access
Open Access
ARTICLE
David Amilo1,*, Khadijeh Sadri1, Evren Hincal1,2, Chinedu Izuchukwu3, Mohamed Hafez4,5, Muhammad Farman1,6,7, Kottakkaran Sooppy Nisar8,9
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.077921
(This article belongs to the Special Issue: Innovative Applications of Fractional Modeling and AI for Real-World Problems)
Abstract Spinal disorders, such as disk hernia and spondylolisthesis, affect millions worldwide, leading to chronic pain and reduced quality of life due to disruptions in biomechanical alignment. Traditional diagnostic methods often overlook the viscoelastic memory effects in spinal tissues, necessitating advanced models that integrate machine learning with fractional calculus for improved accuracy and interpretability. The research introduces a new fractional-order machine learning system that analyzes vertebral column abnormalities through biomechanical motion analysis by using the University of California, Irvine (UCI) vertebral column dataset. The system selects the best machine learning model from Random Forest (RF), Gradient… More >
 Open Access
Open Access
ARTICLE
Shuaiqi Song, Lijie Grace Zhang, James D. Lee*
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.080567
Abstract The theory of thermomechanical-electromagnetic coupling was constructed. The finite element analysis of thermo-visco-elastic-plastic-electromagnetic continuum was formulated. Then the problem of wave propagation in this continuum was solved in two stages. In Stage I, a nearly static thermomechanical solution of a hollow cylinder, subject to twist and temperature gradient, was obtained. Then, in Stage II, the problem of wave propagation of scalar and vector potentials, due to deformation and temperature gradient, was solved. In the second approach, in Stage I, the static electric field and static magnetic field are obtained through static scalar and vector potentials, More >
 Open Access
Open Access
EDITORIAL
Wenbing Zhao1,*, Pan Wang2
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.084481
(This article belongs to the Special Issue: Computer Modeling for Future Communications and Networks)
Abstract This article has no abstract. More >
 Open Access
Open Access
EDITORIAL
Siamak Talatahari*, Amin Beheshti
CMES-Computer Modeling in Engineering & Sciences, DOI:10.32604/cmes.2026.084097
(This article belongs to the Special Issue: Applied Artificial Intelligence: Advanced Solutions for Engineering Real-World Challenges)
Abstract This article has no abstract. More >