 Open Access
Open Access
ARTICLE
Yun Liu1, Jinghua Zhao1, Liang Ma1, Zijie Huang2,3,*, Lizhi Cai2,3, Jianxin Ge2,3
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.084179
Abstract Automated library migration reduces refactoring costs but challenges traditional evolutionary algorithms, which often suffer from premature convergence and poor recall in sparse, complex API mapping spaces. To address this, we propose QIMIG, a multi-objective optimization framework integrating quantum-inspired encoding with quality-aware and greedy heuristic filtering. QIMIG utilizes a probabilistic Q-bit representation to maintain population diversity and avoid local optima. Simultaneously, its heuristic components leverage historical usage context to filter semantic noise and guide the search toward valid mappings. Evaluated on 9 real-world migration rules derived from 57,447 open-source projects, QIMIG statistically significantly outperforms state-of-the-art baselines More >
 Open Access
Open Access
ARTICLE
Ying Cao1, Penghui Zhao1, Xinyu Qiao1, Ningfan Zhan1, Xiaomei Zou2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.084057
Abstract Multimodal Sentiment Analysis (MSA) integrates diverse modalities to identify emotional states, yet performance often suffers in scenarios with missing data. In this situation, despite the promising results of recent methods, the failure of part methods to fully exploit the latent valid information contained in incomplete modalities may degrade predictive performance. Besides, to address the oversight of varying contributions across modalities to sentiment understanding, the score-based weighting schemes in the exhibited methods remain overly sensitive to data fluctuations, leading to unstable and unreliable predictions. To this end, we propose a novel method, Data Mining and Uncertainty-Aware… More >
 Open Access
Open Access
ARTICLE
Amir Ijaz*, Hashem Haghbayan, Abdul Malik, Ethiopia Nigussie, Juha Plosila
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.083797
Abstract The exponential growth of the Internet of Things (IoT) has led to an urgent need for highly energy-efficient communication strategies, especially for battery-powered or self-sustaining devices. In this work, we present a comprehensive framework for minimizing communication energy in IoT nodes operating in swarm robotic systems. We examine and integrate multiple low-power wireless technologies (BLE, LoRaWAN, MQTT, CoAP) with advanced Medium Access Control (MAC) protocols. We additionally propose adaptive scenarios leveraging both ambient energy harvesting and passive backscatter transmission. Our solution employs adaptive scheduling and dynamic transmission power management. Specifically, a Deep Q-Learning (DQL) agent More >
 Open Access
Open Access
ARTICLE
Linyu Dong1, Tao Li2, Hao Li2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.083042
Abstract While Transformer-based detectors excel in global modeling, their efficacy in unmanned aerial vehicle (UAV)-based tiny object detection is limited by information loss during aggressive downsampling and the lack of high-frequency structural cues. To bridge this gap, we propose HiFreq-DETR, a dedicated framework that optimizes the synergy between spatial fidelity and semantic discriminability. The core innovation lies in its hierarchical information preservation strategy, which employs a ResNeSt14d backbone coupled with an
 Open Access
Open Access
ARTICLE
Xiaorong Feng1,2, Ying Gao1,*, Leyu Shi2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082481
Abstract Open source software has become a fundamental component of modern software ecosystems, supporting a wide range of critical applications in operating systems, cloud services, embedded systems, and security-sensitive infrastructures. However, the rapid growth of open source projects also brings increasingly serious security challenges. Many widely used C/C++ components still contain hidden vulnerabilities, and attackers are no longer limited to exploiting traditional memory-related bugs such as buffer overflows or use-after-free errors. In recent years, non-memory logic flaws, including improper authentication, incorrect state transitions, flawed boundary checks, and insecure API usage, have become more prevalent and more… More >
 Open Access
Open Access
ARTICLE
Shaohuang Bian1,#, Qinxiu Gao1,#, Shan Su1, Weifeng Wang1, Feng Huang2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081818
Abstract Tomato, as a globally important crop, its freshness directly affects postharvest quality, market value, and consumer acceptance. Traditional tomato freshness evaluation mainly relies on manual inspection and experience-based judgment, which is time-consuming, labor-intensive, and inefficient. Meanwhile, plasma technology has shown promising potential in agricultural preservation due to its safety and effectiveness, making the evaluation of tomato freshness after plasma treatment particularly important. In recent years, with the rapid development of deep learning technology, non-destructive detection methods based on image analysis have become important tools for agricultural product quality assessment. This study proposes an improved YOLOv8n-based… More >
 Open Access
Open Access
ARTICLE
Israt Jahan1, Afsana Begum1, Bibhas Roy Chowdhury Piyas1,*, Fahmid Al Farid2,3,*, Fatama Jannat Tisha1, Shahrin Islam1, Abu Saleh Musa Miah4, Hezerul Abdul Karim3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081631
Abstract Transforming underlying cardiovascular risk into actionable clinical decisions remains a major challenge in contemporary healthcare. Despite advances in cardiology, early-stage cardiovascular disease often remains undetected, which hinders timely intervention and leads to preventable deaths. To overcome this problem, this study presents an explainable machine learning framework for the early diagnosis of cardiovascular disease (CVD). Initially, this study examined several data-balancing strategies, for example, SMOTE (Synthetic Minority Over-sampling Technique), SMOTETomek (Synthetic Minority Over-sampling Technique + Tomek Links), Tomek Links, ADASYN (Adaptive Synthetic Sampling), and SMOTE-ENN (Synthetic Minority Over-sampling Technique-Edited Nearest Neighbors) within the data-preprocessing pipeline. We… More >
 Open Access
Open Access
REVIEW
AKM Bahalul Haque1,*, Al Amin Islam Ridoy2, Mohammad Rayhan3, Ivan Porres1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079525
Abstract Agentic AI is gaining new insights and advancements in the field of Artificial Intelligence, fostering significant potential to enable rapid transformation across various domains. This rapid advancement and the potential to revolutionize various domains advocate the need for a deeper understanding and firm grasp of the technology. Moreover, an investigation into state-of-the-art research directions in agentic AI needs to be conducted to comprehensively assess the potential scope for improvement and application. Therefore, to address these objectives, a comprehensive review can provide researchers and practitioners with valuable insights into the current state and future research scopes… More >
 Open Access
Open Access
ARTICLE
Akmalbek Abdusalomov1, Kudratjon Zohirov2, Azizbek Khojamurotov3, Furkat Safarov3,4, Alpamis Kutlimuratov5, Jasur Sevinov6,7, Zavqiddin Temirov8, Abror Buriboev5,9,10, Heung Seok Jeon11,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079237
Abstract Medical texts are often complex and difficult to understand for non-specialists, creating barriers to effective communication in the clinical and rehabilitation fields. Although recent advances in natural language processing (NLP) have enabled automated text simplification, existing approaches often struggle to maintain medical accuracy and frequently result in factual inconsistencies or distortions. To address these issues, we propose the Neuro-Semantic Clinical Filter (NSCF), a novel NLP-based framework designed for clinically accurate simplification of medical texts. The proposed method integrates a Medical Concept Graph Encoder (MCGE) to incorporate structured domain knowledge, a Neuro-Symbolic Transformer (NSTR) for supervised… More >
 Open Access
Open Access
ARTICLE
Spandana Saggurthi1, Anand Nayyar2, Sk Hasane Ahammad1, Sumendra Yogarayan3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080058
(This article belongs to the Special Issue: Nature-Inspired Optimization & Applications in Computer Science: From Particle Swarms to Hybrid Metaheuristics)
Abstract This work presents a multi-objective optimization framework for systematic design-space exploration of a 28 GHz single-stage cascode LNA (Low noise amplifier) in 22 nm FDSOI technology using NSGA-II and MOPSO algorithms. The objectives of the paper include simultaneous minimization of noise figure (NF) and power consumption while maximizing gain under matching and stability constraints. Using device parameters and circuit models that were developed for a 22 nm FDSOI process technology, an optimization framework was created in Python, with the passive components
 Open Access
Open Access
ARTICLE
Jianfeng Liu1, Yongjiao Yang1, Kangyi Yang1, Changhua Hu1, Zijia Xu1, Qingguo Shi2, Yi Su2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082804
(This article belongs to the Special Issue: Generative Artificial Intelligence and Large Language Models: Methods, Architectures, and Applications)
Abstract Power enterprise inspection and supervision require greater intelligence, efficiency, and standardization; however, existing approaches are limited by inefficient knowledge retrieval, inaccurate issue identification, and insufficient support for standardized reporting and rectification tracking. This study proposes a lightweight, domain-adaptive large language model (LLM) framework based on Low-Rank Adaptation (LoRA), integrating Retrieval-Augmented Generation (RAG) and structured prompt engineering to enable evidence-grounded inspection tasks. The framework achieves parameter-efficient adaptation through low-rank decomposition and constructs a domain-specific multimodal knowledge base, enhancing output traceability, consistency, and task generalization. A key contribution is the introduction of a Sensitive Information Control Gate, More >
 Open Access
Open Access
ARTICLE
Liangyu Lin, Li Feng*, Lin Huang
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.083047
Abstract The modern sports streaming market is severely fragmented, forcing fans into costly, siloed platforms. While blockchain-based decentralized architectures offer a unified, interoperable sport streaming ecosystem, securely delivering commercial video over untrusted infrastructure remains a profound cryptographic challenge. Existing schemes fail to simultaneously support highly granular on-demand highlights and large scale dynamic live subscriptions. To resolve this, we propose a novel decentralized authorization architecture that systematically integrates existing cryptographic primitives into a decoupled three-layer protocol. By securely bridging on-chain state transitions with off-chain cryptographic enforcement, our architecture directly maps commercial payment workflows onto the underlying key More >
 Open Access
Open Access
ARTICLE
Abolfazl Saghafi1,*, Soodeh Moallemian2, Miray Budak2, Rutvik Deshpande2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082996
Abstract Missing data remain a persistent challenge in statistical analysis and machine learning because many predictive methods require complete observations. Generative Adversarial Imputation Networks (GAIN) offer a flexible deep-learning approach for missing value imputation, but their practical use is limited by convergence instability, sensitivity to hyperparameter selection, and dependence on outdated software implementations. To address these limitations, we propose Enhanced Generative Adversarial Imputation Networks (EGAIN), a modernized extension of GAIN implemented in TensorFlow 2.x. EGAIN incorporates convolution-based generator and discriminator networks, a channel-stacked representation of the data and mask, and checkpoint-based training diagnostics to improve stability More >
 Open Access
Open Access
ARTICLE
Jiangyong Yu, Chuanping Hu*, Runnan Wang
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082810
Abstract With the proliferation of Internet of Things (IoT) devices, accurate device fingerprinting of highly encrypted traffic has emerged as a critical challenge for ensuring network security. Existing deep learning models are either difficult to deploy in real-time due to excessive computational complexity (e.g., Transformers) or are limited in performance because their structure does not match the inherent hierarchy of traffic data (e.g., flattened state space models). Furthermore, a general lack of transparency in their decision-making processes restricts their trustworthiness in security-critical scenarios. To address these challenges, this paper proposes a Hierarchical Mamba with Gated Attribution More >
 Open Access
Open Access
ARTICLE
Qiuguo Guan, Zhiyu Ren*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082704
Abstract To address trust-score drift and unsafe online adaptation under cross-domain attack-contaminated streams in Industrial Internet of Things (IIoT) edge environments, this paper proposes a risk-aware lightweight test-time adaptation (TTA) framework, named RaL-TTA, for dynamic trust evaluation of edge nodes. RaL-TTA constructs a low-dimensional robust feature space and a source-domain normal-entropy reference baseline, and performs selective online maintenance in the target domain through Kolmogorov–Smirnov (KS) drift detection, SafeBrake risk gating, Adaptive Batch Normalization (AdaBN) anchor protection, and budgeted sample-level safeguards. Low-risk batches are adapted by updating only lightweight Batch Normalization (BN) parameters, whereas high-risk batches freeze… More >
 Open Access
Open Access
ARTICLE
Sami Ullah1,2, Najmul Hassan2, Naeem Bhatti2, Asad Saleem1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082467
(This article belongs to the Special Issue: Development and Application of Deep Learning and Image Processing)
Abstract Underwater imaging facilitates the exploration of the underwater environment. However, irregular optical absorption and light scattering in water, ranging from clear to highly turbid conditions, often result in low visibility, color distortion, and blurriness in underwater images (UWIs). Conventional UWI enhancement methods are limited by inefficient physical modeling, while deep learning-based approaches are constrained by the scarcity of paired training datasets. In this work, we propose a hybrid learning framework for UWI enhancement that leverages the usefulness of both conventional and deep learning-based techniques. At first, we preprocess the UWIs using a revised underwater physical… More >
 Open Access
Open Access
ARTICLE
Sajad Homayoun*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082332
Abstract Intrusion detection systems depend on detailed security telemetry, yet such telemetry is often too sensitive to share or reuse outside controlled environments. Differential Privacy (DP) offers formal protection by injecting randomness, but its practical impact on detection utility is not well understood, especially under class imbalance and for rare attacks. This paper presents a controlled empirical study of feature-level DP applied to security telemetry for intrusion detection. Using a fixed model and a fixed train–test split, we vary only the privacy budget and quantify how performance changes across standard metrics, including macro-averaged scores and per-class More >
 Open Access
Open Access
ARTICLE
Xinshan Huang1, Zirui Pei1, Chaohong Tan2, Zuqiang Meng1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081626
(This article belongs to the Special Issue: Deep Learning for Emotion Recognition)
Abstract Multimodal Sentiment Analysis (MSA) plays an important role in understanding social media content; however, existing methods often struggle with the heterogeneity and complex interactions between images and text. These challenges include inter-modal information asymmetry, insufficient feature fusion, and noise interference, which collectively limit robustness and accuracy. To address these issues, we propose a multimodal sentiment classification model termed Multi-Branch Cross-Modal Cross-Attention Gating (MB-CMCAG). The model first incorporates a Transformer-based image caption generation module to convert raw images into semantically rich auxiliary textual descriptions, which complement the original text and form paired textual inputs with enhanced… More >
 Open Access
Open Access
ARTICLE
Sumaira Shafiq1, Naveed Ejaz2, Munam Ali Shah3,*, Rashid Kamal2, Adnan Sohail1, Sheraz Aslam4,5,6
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081534
(This article belongs to the Special Issue: Generative Artificial Intelligence and Large Language Models: Methods, Architectures, and Applications)
Abstract Lecture videos are widely used in modern education, yet answering questions from them remains challenging. Relevant information is often distributed across time and expressed through multiple modalities, including speech, slides, and visual content. Existing VideoQA approaches, including recent retrieval-augmented generation (RAG) methods, typically rely on static text representations or global video features. Consequently, they may retrieve evidence that is semantically relevant but temporally misaligned, leading to inaccurate or weakly grounded responses. In addition, dependence on external knowledge sources can introduce hallucinations and reduce reliability in educational settings. To address these limitations, we propose a temporally More >
 Open Access
Open Access
ARTICLE
Sheyun Zhang, Ruichun Gu*, Chaofeng Li, Zhijian Dong, Hefei Wang
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081065
Abstract Federated learning (FL) enables collaborative model training without sharing raw data. However, in real-world applications, clients often exhibit statistical heterogeneity, missing classes, and long-tailed distributions, which can substantially degrade the generalization performance of conventional parameter aggregation and some personalization approaches. Moreover, distillation or alignment-based methods may suffer from unstable supervision and difficult optimization under highly heterogeneous settings. To this end, this paper proposes a novel method called FKD-RTM (Heterogeneous Federated Knowledge Distillation Based on Residual-Enhanced Tree-to-MLP Knowledge Transfer). The key idea is to decouple local teaching from globally aggregatable student learning: we introduce a Gradient… More >
 Open Access
Open Access
ARTICLE
Jiali Chen1,2,3, Jiheng Zhang1,2,3, Xiaojie Chen1,2,3, Chong Zeng1,2,3, Honghui Yi1,2,3, Heming Jia4,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080569
(This article belongs to the Special Issue: Advances in Nature-Inspired and Metaheuristic Optimization Algorithms: Theory, Applications, and Emerging Trends)
Abstract Traditional heuristic algorithms often fall into local optima and converge slowly when test case prioritization is addressed in regression testing, making them inadequate for complex real-world scenarios. The Aquila optimizer, a novel metaheuristic algorithm, demonstrates strong global exploration capability but still faces limitations, including insufficient exploitation capability and slow convergence. To overcome these challenges, a multi-strategy improved chaotic Cauchy inverse cumulative distribution Aquila optimizer for test case prioritization is proposed. First, a logistic–sine–cosine composite chaotic mapping is introduced during the initialization phase of the Aquila optimizer to increase population diversity. Second, the mutated random walk… More >
 Open Access
Open Access
ARTICLE
Mohammad Muzayyin Amrulloh1,2, Tohari Ahmad1,*, Royyana Muslim Ijtihadie1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079951
Abstract The rapid development of digital technology has facilitated data exchange and communication, while simultaneously increasing security threats such as data theft and manipulation. As personal data is highly confidential, effective protection mechanisms are required in the digital era. Audio steganography hides secret messages (payload) within audio signals; however, many existing approaches rely on a single stego-audio output, which can lead to information leakage during storage or transmission if the file is intercepted. This vulnerability allows an attacker to more easily reconstruct the steganographic scheme from a single output. To address this limitation, this study proposes… More >
 Open Access
Open Access
ARTICLE
Ramakrishna Gandi1,*, Geetha A.1, Ramasubbareddy B.2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.077569
Abstract In the fields of affective computing, human-computer interaction, and psychological evaluation, the capacity to recognize emotions is crucial. Unimodal systems in the form of visual systems or of the physiological type are usually not designed to capture the complexity that exists in emotional states. The paper proposes NeuroVision: Multimodal Emotion Recognition System, combining facial video frames information and electroencephalogram (EEG) based information to enhance the accuracy and stability of the system. The system applies ResNet50 on the spatial information of facial expressions, Vision Transformer (ViT) on the temporal movements in the video, and an EEG-MLP… More >
 Open Access
Open Access
ARTICLE
Yunkeun Song1, Samuel Woo2, Suji Lee3, Yousik Lee3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.083267
(This article belongs to the Special Issue: Intelligent Transportation System (ITS) Safety and Security)
Abstract Software-Defined Vehicles (SDVs) increase cybersecurity complexity through the combination of external connectivity, software-intensive functions, and distributed development across vehicle manufacturers and suppliers. Although United Nations (UN) Regulation No. 155 and ISO/SAE 21434 require Threat Analysis and Risk Assessment (TARA) throughout the vehicle lifecycle, conventional TARA methodologies remain largely system-focused and often provide limited procedural guidance for coordinating supplier-derived TARA results at the vehicle level. This paper proposes an orchestration model for TARA across vehicle manufacturers and suppliers that structures TARA activities into the concept phase and the product development phases. The model defines interactions between… More >
 Open Access
Open Access
ARTICLE
Chengyu Hou1,2, Wenzao Li2, Hanyun Li3, Kui Liu1, Zhuoning Zhao1, Hongping Shu1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081575
Abstract The rapid growth of Internet of Things (IoT) and 5G technologies has led to a sharp increase in computing demands from wireless devices, making efficient task offloading a critical challenge. Key issues include reducing application latency, lowering the energy consumption of terminal devices, and improving overall system performance, all of which directly affect user experience. Traditional genetic algorithms (GA), inspired by biological evolution, have been widely used in task offloading, but they often suffer from slow convergence and a tendency to fall into local optima in complex scenarios, limiting their effectiveness. To address these drawbacks,… More >
 Open Access
Open Access
ARTICLE
Naeem Ullah1,*, Javed Ali Khan2, Michelina Ruocco3, Antonio Della Cioppa4, Ivanoe De Falco5, Giovanna Sannino5
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081477
Abstract Fruit diseases significantly impact agricultural productivity, yet automated detection systems often fail to provide interpretable predictions and are sensitive to background variations in images, particularly in orange fruit disease datasets. Current deep learning approaches are prone to background bias, which reduces explainability and generalization. To address this, we propose a deep learning framework that explicitly reduces background noise and bias in orange fruit disease image classification while providing interpretable, pixel-level predictions. The framework integrates existing architectural components, including grouped convolutions with channel shuffling, Leaky ReLU and clipped ReLU activations, and attention-based feature extraction, within a… More >
 Open Access
Open Access
ARTICLE
Weiguang Wang1,2, Jincai Li1, Mengqi Liu1, Mengke Liu1, Yuan Zhang1, Jingyan Wu1,*, Yang Liu3,*, Junbin Lou4, Yixin He5
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080341
(This article belongs to the Special Issue: Aerial Innovation Spectrum: All-Domain Research in UAV Communication, Navigation, and Autonomy)
Abstract To improve the accuracy of small object feature detection in complex backgrounds for Unmanned Aerial Vehicle (UAV) aerial photography and reduce computational complexity, we propose the lightweight UAV aerial photography small object detection method based on multi-scale feature fusion and contextual information. Firstly, by introducing the grouped content-aware reassembly (GCA) operator and designing lightweight pinwheel context convolution (LPConv), we extend the feature fusion path to the P2 layer, constructing a lightweight multi-scale feature fusion network (SG-PANet). Through the decoupling of fine-grained small object features and background interference features by the GCA operator, combined with the… More >
 Open Access
Open Access
ARTICLE
Pan Li1,2, Zhi Li3, Yingyou Wen2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.083087
Abstract The rapid advancement of edge intelligence in Industrial Internet of Things (IIoT) is transforming human–computer interaction from conventional “command execution” to complex “human–AI deep collaboration”. Within such safety-critical industrial environments, establishing robust mutual understanding and trust mechanisms
becomes a significant prerequisite for decision reliability and efficiency. However, existing industrial interaction systems predominantly focus on task progression and explicit command responses, lacking fine-grained, dynamic tracking of operators’ trust states, cognitive evolution, and behavioral dynamics. Moreover, current LLM-based user simulation in evaluation often exhibit an “over-cooperation” bias, failing to capture the cognitive conflicts and trust crises characteristic… More >
 Open Access
Open Access
ARTICLE
HyeSun Chang, Sangjun Lee*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082718
Abstract Accurate identification of heart murmurs from auscultation recordings is essential for early cardiovascular screening and diagnosis. While deep learning offers strong potential for automated heart murmur classification, existing models often exhibit overconfident, incorrect predictions and limited generalization due to dataset bias and class imbalance. To address these challenges, this study proposes a two-stage confidence-regulated learning framework that jointly optimizes feature representation and decision reliability. Rather than focusing solely on improving classification performance, this work emphasizes enhancing prediction reliability through confidence-aware decision-making. The proposed framework integrates supervised contrastive learning (SCL) to strengthen the discriminative structure of… More >
 Open Access
Open Access
ARTICLE
Jian Su1,2,*, Jiaqi Wang2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082531
Abstract Despite significant advances in object detection technology, vulnerable pedestrian detection in intelligent transportation systems remains highly challenging under complex weather conditions. Environmental factors such as fog, rain, and snow often lead to occlusion, motion blur, and low-contrast images, making small-scale or weak-featured vulnerable pedestrians difficult to accurately identify. Therefore, improving the detection accuracy and robustness of vulnerable pedestrians in complex weather scenarios has become an urgent research problem. To address this issue, this paper proposes an improved YOLOv8-based vulnerable pedestrian complex weather detection algorithm, termed VPCW-YOLO. The proposed method enhances detection performance through multiple structural… More >
 Open Access
Open Access
ARTICLE
Geunhwi Park1, Juneyoung Park2,*, Chunjoo Yoon3, Jaehong Park3
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081652
Abstract Urban flooding caused by extreme rainfall events disrupts transportation systems, yet generating realistic flood-traffic scenarios for disaster preparedness remains a labor-intensive manual process. This study proposes a Knowledge Graph (KG)-driven pipeline that automatically generates domain-specific training data for fine-tuning small language models (sLLMs) to synthesize urban flood-traffic scenarios. A domain KG comprising 58 entities and 285 relationships was constructed for Jinju City, South Korea, integrating empirical flood data from 112 local documents with quantitative rainfall-traffic impact values from 14 international studies. Nine domain constraint rules, including a novel spatial consistency rule, ensure the physical plausibility… More >
 Open Access
Open Access
ARTICLE
Meihuizi Jia1,*, Hongyan Ran1, Shanshan Li2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080333
Abstract Large language models (LLMs) have demonstrated considerable ability in solving various tasks via Chain-of-Thought (CoT) prompting, which has precipitated extensive research into their application for complex mathematical reasoning problems. However, current research on mathematical reasoning with CoT predominantly focuses on textual mathematical tasks, such as math word problems, while paying limited attention to multimodal geometric scenarios. To bridge this gap, we propose KG-HoT, a model that harnesses the generative and comprehension capabilities of Multimodal large language models (MLLMs) to enhance complex geometric problem-solving in multimodal systems. Our knowledge-grounded approach enables MLLMs to generate hybrid chains-of-thought More >
 Open Access
Open Access
ARTICLE
Rifat Sarker Aoyon1, Fahmid Al Farid2,3, Ismail Hossain4, Mahe Zabin5, Sarina Mansor2,*, Jia Uddin6,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079831
Abstract This research introduces an innovative lightweight image segmentation framework where models of hybrid architectures work together to predict the output and also have self-adapting ability, along with maintaining data privacy. In this framework, data is distributed and trained in a decentralized way using different deep learning architectures. That is how the advantages of all these models will be integrated into the system. Each trained model makes its own prediction, and the final output is determined through cooperation among these models. Here, the confidence-level and pixel-wise voting majority algorithms will be utilized for the co-operation-based output… More >
 Open Access
Open Access
ARTICLE
Isam Bahaa Aldallal1, Saadaldeen Rashid Ahmed2,3, Abdullahi Abdu Ibrahim1, Oguz Bayat4, Abu Saleh Musa Miah5, Fahmid Al Farid6,7,*, Md. Hezerul Abdul Karim6,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078742
(This article belongs to the Special Issue: Intelligent IoT for Smart Cities and Sustainable Energy Systems)
Abstract Urban parking problems worsen traffic jams, gas use, and pollution. Old parking systems often lack up-to-date space information, which annoys drivers and wastes their time. This research presents a smart IoT-enabled real-time space monitoring and booking system applicable to both urban parking management and Smart Manufacturing logistics environments, including loading bay coordination and Automated Guided Vehicle (AGV) docking station management. The system employs ultrasonic and IR sensors, managed by an Arduino UNO, to identify vehicles and track space availability. A servo-motor regulates entry. Slot data is presented on a Liquid Crystal Display screen and accessible More >
 Open Access
Open Access
ARTICLE
Karlo Borovčak1, Marina Bagić Babac1,*, Vedran Mornar2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078330
Abstract This study examines the potential of open-source foundation models for structured data analytics, with particular emphasis on SQL generation and business-oriented interpretation in single-agent and multi-agent large language model (LLM) systems. The proposed framework addresses a practical problem in analytics-intensive environments, where natural-language requests must be translated into executable, semantically appropriate SQL queries and subsequently interpreted in a form useful for business decision-making. The system is evaluated in two complementary settings: a custom SQL test suite designed around realistic marketing and e-commerce analytics tasks, and the public Spider benchmark, which supports comparison with prior text-to-SQL… More >
 Open Access
Open Access
ARTICLE
Miao Ye1, Ziheng Wang1, Qiuxiang Jiang1, Xingsi Xue2, Wenxi Liu3, Yu Ning1, Cheng Zhu1,4,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078282
Abstract In recent years, anomaly detection in Wireless Sensor Networks (WSNs) has been widely studied using Graph Neural Networks and Transformer-based methods. However, in multi-node and multi-modal data scenarios, these approaches still face challenges such as insufficient extraction of spatiotemporal correlation features, limited modeling capabilities when relying solely on either time-domain or frequency-domain information, and high computational overhead. To address these issues, this work aims to develop an anomaly detection model that balances detection performance with computational efficiency, enabling effective identification of complex anomaly patterns. Specifically, we propose a time–frequency feature extraction method with topological information… More >
 Open Access
Open Access
ARTICLE
Changzhu Shi, Hongmei Liu*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.074281
Abstract To address the critical challenges of small object detection in UAV imagery, this paper proposes DSGF-Net (Dense-SE Gated-Fusion Network), an enhanced architecture built upon YOLOv10. It integrates a Dense SE Network (DSENet) backbone, an Adaptive Gated Fusion (AGF) module, and a Channel-Spatial Attention (CSA) mechanism. Extensive experiments on VisDrone2019-DET and CODrone demonstrate that DSGF-Net achieves substantial mAP@0.5 improvements of 5.12% and 2.36% over the YOLOv10n baseline. More >
 Open Access
Open Access
ARTICLE
Yan Ge1, Zhenzhou Zhang2, Chien-Ming Chen3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.077790
Abstract Periodic pattern mining plays an important role in revealing recurring behavioral regularities from temporal sequence data. Most existing approaches, however, are developed for single-sequence settings and rarely account for quantitative information or sequence-level constraints when patterns recur across multiple sequences. This limits their usefulness in practical scenarios, where a pattern is expected to be not only periodic but also quantitatively significant in a sufficiently large portion of sequences. In this work, we formulate the problem of mining High-Quantitative Periodic Frequent Patterns (HQPFPS) from multi-sequence databases and propose an efficient algorithm, termed MHQPFPS. The proposed method… More >
 Open Access
Open Access
REVIEW
Leonidas Theodorakopoulos, Alexandra Theodoropoulou*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082270
Abstract Auditable autonomy is becoming a practical requirement for deploying large language model (LLM) agents in operational workflows where recommendations can trigger consequential actions. Many autonomy claims remain hard to evaluate because studies emphasize task completion or fluent explanations while underreporting tool privileges, verification conditions, rollback feasibility, and trace completeness. This review develops a decision-making–centered framework that treats autonomy as an auditable engineering property. It introduces a three-plane big data foundation: an evidence plane with provenance and freshness constraints; a decision-trace plane that records retrieval identifiers, tool invocations, intermediate checks, and policy evaluations; and an outcomes More >
 Open Access
Open Access
ARTICLE
Vipin Kumar (विपिन कुमार)1,*, Pushpendra Kumar2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081791
(This article belongs to the Special Issue: Alliance between First Principles Calculation and Machine Learning: Materials Discovery, Properties, and Applications)
Abstract In this paper, we report the effects of point defects and doping on the physical properties of the two-dimensional OsI2 monolayer. A point defect was created by removing a single Os/I atom from the perfect crystal lattice of the OsI2 monolayer. For doping, we use an isovalent Ru element from the transition-metal family. Point defects and doping alter the band structure by creating new localized electronic states within the gap. Moreover, the electronic bands show a shift due to point defects. However, changes in the bandgap due to point defects and doping are not remarkable. This… More >
 Open Access
Open Access
ARTICLE
Rana Lateef1, Asmaa Abdul Jabbar2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080975
(This article belongs to the Special Issue: Advances in Object Detection and Recognition)
Abstract The challenges of underwater object detection are derived from complex environmental conditions, including light scattering, absorption, and turbidity. The deep learning approaches have enhanced the detection of objects in these low-visual conditions. This work presents a multi-stage object-detection framework for the underwater environment that performs well on the Semantic Segmentation of Underwater Imagery (SUIM) benchmark. To begin with, there is the adaptive Multi-Scale Retinex with Color Restoration (MSRCR) algorithm, which improves image quality by correcting color distortions and increasing contrast. Second, an augmented YOLOv8 model (with a ResNet-50 backbone and the Convolutional Block Attention Module More >
 Open Access
Open Access
ARTICLE
Huaixuan Yan, Yan Gong*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080178
Abstract To correctly diagnose faults in farm machinery, we need to know a lot about the field and have experience with maintenance. However, most of this important information is stored in old, unstructured documents like technical manuals and expert logs. These documents don’t have a standard way to be represented digitally, which makes it very hard to build automated diagnosis systems. There are three main technical problems with getting structured knowledge out of this kind of text: noise from optical character recognition (OCR) during digitization, the extreme lack of labeled samples in specialized fields (low-resource constraints),… More >
 Open Access
Open Access
ARTICLE
Mohammed Shukur Alfaras1,2,*, Oguz Karan3, Sefer Kurnaz1, Ayca Kurnaz Turkben4
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079577
Abstract Despite deep learning’s high precision in emotion identification, centralized training is associated with privacy and scalability concerns. The privacy-preserving federated learning model, Federated Hybrid-Optimized Emotion Recognition (Fed-HOER), introduced in this paper is an auto-tuning hyperparameters optimizer based on a hybrid Dung Beetle Optimizer-Fick’s Law Algorithm (DBO-FLA) optimizer. The global and local searches are optimized at two levels, and validation loss is minimized by 22%–24% without sharing raw data. The experiments on Extended Cohn–Kanade (CK+), Japanese Female Facial Expressions (JAFFE), and Karolinska Directed Emotional Faces (KDEF) exhibit a high generalization rate with a mean accuracy of More >
 Open Access
Open Access
REVIEW
Kamlesh Paswan1, Rajnish Singh2, Vivekanand Singh3, Brihaspati Singh4, Ankur Saxena5, Chandrmani Yadav6,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080581
(This article belongs to the Special Issue: Mechanical Behavior of Materials with Advanced Modeling and Characterization)
Abstract Electrical Discharge Machining (EDM) is governed by highly coupled, nonlinear electro-thermal-mechanical phenomena involving plasma-mediated energy transfer, rapid heat conduction, phase transformation, and resolidification over micro to nanosecond time scales. From a computational materials science perspective, EDM serves as a prototypical problem of extreme, localised energy–matter interaction, where predictive modelling requires rigorous treatment of multiphysics coupling and scale bridging. This review presents a critical synthesis of theoretical and numerical frameworks for modelling advanced EDM configurations, including vibration-assisted and turning-based EDM, powder- and nano-additive-assisted EDM, and alternative dielectric environments. The review consolidates continuum-based formulations that describe the… More >
 Open Access
Open Access
ARTICLE
Danilo Greco*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082708
Abstract The Enhanced Graph Neural Network Autoencoder (Enhanced GNN-AE), recently proposed for unsupervised cybersecurity monitoring in battery energy storage systems (BESSs), builds a multiscale
 Open Access
Open Access
ARTICLE
Yu Zhang1,2,#, Shihan Tan1,#, Guangyao Lian2, Congying Dun3, Qiwei Hu1,*, Chiming Guo1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081931
Abstract Gearboxes are critical components in the transmission systems of various mechanical equipment. Subjected to complex and harsh operating conditions for a long time, they suffer from a high failure rate and potentially severe consequences. Traditional fault diagnosis methods are limited by problems such as noise interference, and can hardly meet the requirements in terms of diagnostic accuracy, generalization ability, and reliability. To tackle the deficiencies of traditional gearbox fault diagnosis methods, including insufficient utilization of features, poor generalization under small-sample conditions, and weak model interpretability, this paper proposes a fault diagnosis method based on multi-dimensional… More >
 Open Access
Open Access
ARTICLE
Sun-Kyoung Kang1, Yeonwoo Lee2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081553
Abstract Black ice formation on road surfaces presents a serious hazard due to its low visibility and high slipperiness, underscoring the critical need for timely and accurate detection in intelligent transportation systems. In this paper, we propose AdaMsDCNet, an adaptive multi-scale dilated convolution network designed for real-time black-ice semantic segmentation on resource-constrained edge platforms, applying a Convolutional Neural Network (CNN) with an adaptive Multi-Scale Dilated Convolution (MsDC) feature fusion encoder-decoder architecture. The key concept of AdaMsDCNet is to employ an encoder-decoder architecture with parallel multi-scale dilated convolutional paths that adjust dilation rates at different encoder depths… More >
 Open Access
Open Access
ARTICLE
Chao Zhang1, Weidong Zhong1, Xu An Wang1, Weiwei Jiang2,*, Ziteng Wang2, Miao Tian1, Jianhong Ling1, Hangjiang Du1, Yunhui Duan1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081399
Abstract The integrity risks posed by data outsourcing in cloud storage have driven the development of remote data integrity auditing (RDIA) technologies. However, traditional schemes rely on trusted third-party auditors (TPAs), leading to potential collusion and single-point failure vulnerabilities. The integration of blockchain alleviates these issues through decentralization and transparency, yet existing blockchain-based certificateless auditing schemes still suffer from security flaws in the tag generation phase. Addressing the tag forgery vulnerability in Miao et al.’s scheme, which stems from the absence of random parameters in the hash function input, this paper proposes a lightweight enhancement mechanism: More >
 Open Access
Open Access
REVIEW
Shafidah Shafian1,*, Azlan Ismail2,3
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080623
Abstract Organic solar cells (OSCs) have progressed rapidly in recent years, driven by advances in donor polymers, non-fullerene acceptors, and increasingly complex binary and multicomponent blend architectures. Despite these achievements, device performance remains governed by strongly coupled molecular, morphological, and processing variables, making materials optimization inherently multidimensional and difficult to navigate using conventional trial-and-error approaches. The growing availability of experimental data and computational descriptors has therefore encouraged the integration of machine learning (ML) techniques into OSC research as a complementary strategy for accelerating materials discovery and device optimization. Among the available ML strategies, ensemble learning has… More >
 Open Access
Open Access
REVIEW
Hamza Ahmed1, Hassan Jamil Syed2,*, Aqsa Aslam1, Sehar Zehra1, Ummay Faseeha1, Nurzati Iwani Othman2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080115
(This article belongs to the Special Issue: Integrating Computing Technology of Cloud-Fog-Edge Environments and its Application)
Abstract Edge computing is an emerging model for latency-sensitive and distributed applications. However, the observability of edge computing systems in heterogeneous environments remains a challenge, as most existing approaches are limited to only the system, service, application, and network layers. This paper surveys state-of-the-art solutions for edge observability and monitoring. The paper further introduces a thematic taxonomy that groups the state-of-the-art edge observability and monitoring literature based on monitoring intent, telemetry indicators, observability scope, architectural layers, deployment environments, and observability toolchains. Finally, we compare representative solutions in terms of latency, system overhead, bandwidth consumption, and detection More >
 Open Access
Open Access
ARTICLE
Hsuan-Chih Ku1, Jyun-Kai Yang1, Pang-Wei Tsai1, Shih-Hsiung Lee2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079318
Abstract With the rapid proliferation of the Industrial Internet of Things (IIoT), Building Automation Systems (BAS) and Industrial Control Systems (ICS) are increasingly exposed to sophisticated cyber threats. Conventional Intrusion Detection Systems (IDS) often encounter significant limitations when addressing emerging or hybrid attack patterns, primarily due to delayed signature updates and high false-positive rates. Meanwhile, existing anomaly detection approaches frequently lack sufficient awareness of the physical domain, making them ineffective in identifying falsification attacks that comply with communication protocol specifications while violating underlying physical laws. To address these challenges, this study proposes a hybrid threat detection… More >
 Open Access
Open Access
ARTICLE
Junzhe Zhao1,2, Wencan Zhu1,3, Qiang Wang1, Hui Chen2, Yan Liu2, Kaihong Zheng3, Zhibo Zhang2,3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078880
Abstract Vacancy defects in graphene are inevitably introduced during the fabrication of graphene-reinforced metal matrix composites through mechanical processing, chemical reactions, or in-service environmental exposure. Despite their prevalence, the precise atomic-scale impact of these vacancies on dislocation motion, strengthening mechanisms, and failure behavior remains incompletely understood. To address this gap, we employ molecular dynamics simulations to construct aluminum-graphene interface models featuring systematically varied vacancy defect concentrations, enabling a detailed investigation of dislocation–interface interactions and the underlying reinforcement and failure mechanisms under shear deformation. Compared to pristine graphene, interfaces containing vacancy defects exhibit significantly enhanced out-of-plane buckling… More >
 Open Access
Open Access
ARTICLE
Poluru Eswaraiah1, Uddagiri Sirisha2,*, Shaik Abdul Nabi3, Revathi Durgam4, Pallavi Malavath5, Gilakara Muni Nagamani6
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078511
Abstract The growing volume of digital text complicates the extraction of relevant information from unstructured data. Transformer models such as BERT, ALBERT, and RoBERTa are powerful, but they may face challenges in hyperparameter optimization and adaptation to new domains. To address this issue, a hybrid ensemble BERT model is suggested, optimized using the Walrus Optimization Algorithm (WaOA). The framework applies PCA to reduce dimensionality, ontology normalization, and K-means clustering to improve semantic comprehension. Experimental results on the SQuAD 2.0 and MS MARCO datasets show that the proposed model outperforms the baseline models. WaOA (Weighted Average of More >
 Open Access
Open Access
ARTICLE
Xiaolei Ding, Wenjian Liu*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2025.072458
Abstract Backdoor attacks pose a critical threat to the reliability and trustworthiness of machine learning models, as they allow adversaries to manipulate model behavior through the injection of malicious patterns during training. Existing defenses, such as data filtering, fine-tuning, and model pruning, often lack provable guarantees or require retraining from scratch, resulting in significant computational costs. In this work, we propose GTMU (Game-Theoretic Machine Unlearning), a novel backdoor removal framework that formulates the unlearning process as a repeated game between the defender and a virtual attacker. The defender aims to strategically remove poisoned contributions while preserving benign… More >
 Open Access
Open Access
ARTICLE
Anh Thi Diem Nguyen1,2, Tham Vo1, Vinh Truong Hoang3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082845
(This article belongs to the Special Issue: Big Data Technologies and Applications for a Data-Driven World)
Abstract Keeping customers engaged remains a major challenge in appointment-based services, where user behavior continuously shifts due to seasonal, market, and social factors. These dynamic changes often cause concept drift, rendering traditional deep clustering models unreliable because they assume stable data distributions. Most existing approaches handle representation learning, parameter optimization, and model updating as separate components, limiting their adaptability in real-world streaming environments. This study proposes Hybrid-RL, a novel adaptive clustering framework that unifies incremental deep representation learning, multi-head reinforcement learning for joint hyperparameter optimization (number of clusters, latent dimension, and clustering method), incremental model updating,… More >
 Open Access
Open Access
ARTICLE
Muhammad Jawad1, Muhammad Mudassir Ahmad Alwi2,*, Akbar Niaz2, Monaf Hodhod3, Noor ul Amin4, Fiaz Hussain5,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079905
Abstract Lead sulfide (PbS) is a narrow bandgap IV–VI semiconductor with important applications in infrared optoelectronics and thermoelectric energy conversion. Surface engineering and controlled doping provide effective strategies for tuning its electronic and optical properties. In this work, the structural, electronic, optical, and thermoelectric properties of bulk PbS, pristine PbS (110) surfaces, and Ga- and Ag-doped PbS (110) surfaces are systematically investigated using density functional theory within the full-potential linearized augmented plane wave framework. The calculated lattice constant of bulk PbS is 5.88 Å, which agrees well with experimental data. Electronic structure calculations show that bulk… More >
 Open Access
Open Access
ARTICLE
Xiaoyong Zhao1, Jiamin Wu2,*, Lei Wang2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.077179
Abstract With the continuous improvement of the performance of large language models, how to further enhance their ability in complex tasks has become a key issue. The task of abnormal text detection poses a challenge to the model in identifying non-standard semantics due to its semantic complexity and high-risk features. However, existing fine-tuning methods rely heavily on static data selection strategies, making it difficult to adapt to the dynamic evolution of model capabilities, resulting in low training efficiency. This article proposes ADS (Adaptive Dataset Selection), an adaptive framework for selecting data in anomaly text detection. ADS… More >
 Open Access
Open Access
ARTICLE
Xiaorong Feng1,2, Ying Gao1,*, Pengyi Du2, Leyu Shi1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.075938
Abstract In recent years, large language models (LLMs) have seen growing application in code understanding and security analysis. However, their performance relies heavily on prompt context quality and engineering design, with unstable vulnerability detection and high false positive rates remaining key bottlenecks to reliable adoption. This paper systematically reviews advances in prompt engineering and context optimization across four core areas and proposes LARA (LLM-Augmented Reachability Analysis), a neural-symbolic framework leveraging code property graphs (CPGs), which uses a static analysis engine to extract source-to-sink data flow paths, integrates systematic prompt engineering to create context-aware prompts, and invokes… More >
 Open Access
Open Access
ARTICLE
Kanyang Jiang1, Yingkai Kang2, Ming Li2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.083294
(This article belongs to the Special Issue: AI-Driven Optimization for Secure and Sustainable Edge IoT Services)
Abstract The Internet of Vehicular Agents (IoVA) interconnects distributed AI agents across vehicular networks to deliver real-time intelligent services for vehicular users. Due to the limited computing capacity of vehicles, AI agents are deployed on nearby RoadSide Units (RSUs) to perform computation-intensive inference. As vehicles traverse RSU coverage boundaries, AI agents must migrate to target RSUs to maintain service continuity. However, the communication and computing resources at each RSU are shared among multiple co-served vehicles, creating coupled allocation decisions that jointly determine system latency and energy consumption. To address this challenge, we propose a low-latency and… More >
 Open Access
Open Access
ARTICLE
Yu Shi1, Yunfeng Dong1,*, Lu Tian2,3
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080577
Abstract Failure prognosis provides critical decision-making support for Integrated System Health Management (ISHM), ensuring the operational safety of satellites in orbit. Temporal Convolutional Networks (TCNs), known for their capability in processing time-series data, have become an important approach for failure prognosis. The gradual performance degradation of satellites, combined with multi-physics coupling effects, gives rise to multi-scale features. However, existing TCN based failure prognosis methods remain limited in their ability to simultaneously capture both local and global features, posing challenges when processing such multi-scale features. To address this issue, a Cascaded Temporal Convolution and Transformer Network (CTCTN)… More >
 Open Access
Open Access
REVIEW
Langyue Zhao1,2, Yubin Yuan3,*, Yiquan Wu2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080232
Abstract This paper presents a systematic survey of machine vision-based surface defect detection technologies, focusing on five core challenges in the field: interference from complex backgrounds, small object detection, class imbalance, dynamic scene modeling, and cross-scenario generalization. It reviews key technical approaches corresponding to these challenges over the past five years. Furthermore, a dataset characterization analysis framework is established around these challenges, summarizing and comparing the characteristics of over 40 publicly available datasets across more than ten scenarios, including PCB, photovoltaic, metal, and pavement surfaces. Quantitative selection metrics (such as the small target coefficient and texture More >
 Open Access
Open Access
ARTICLE
Ambreen Memon1, Aaron Bere1, Muhammad Nadeem Ali2, Byung-Seo Kim2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078988
Abstract The modern internet infrastructure has enabled numerous applications by providing a seamless connectivity experience across each mode of connectivity. Infrastructure-based connectivity and device-to-device (D2D) are well-known connectivity modes for internet-based applications. The selection of the underlying communication medium significantly affects energy consumption during data transfer. This study proposes an Energy-Efficient Data Dissemination Approach (EEDDA) that integrates encounter prediction with a multi-criteria decision-making (MCDM) framework to reduce infrastructure-based energy consumption in IoT mobility environments. Unlike traditional optimization approaches that focus on single-objective routing or static network models, the proposed framework dynamically selects between Device-to-Device (D2D) and More >
 Open Access
Open Access
ARTICLE
Aihua Wu, Chenlu Huang*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078692
Abstract Three-dimensional (3D) point cloud semantic segmentation is a core task in indoor scene understanding, providing detailed semantic information about spatial structures and object categories in indoor environments. Although methods based on deep learning have made steady progress in recent years, accurately segmenting complex indoor scenes remains challenging due to the unordered nature of point clouds and variations across large scales. Most existing networks have limited capability for multi-scale feature aggregation and struggle to balance local geometric details with global semantic context. These issues are further exacerbated by hierarchical downsampling, which often leads to the loss… More >
 Open Access
Open Access
ARTICLE
Anping Wan1,2,3, Yingchang Gao1,3, Weikang Liu1, Rui Yin1, Khalil Al-Bukhaiti1,3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081719
Abstract Vertical roller mills are essential for energy-intensive grinding in cement, minerals, and metallurgy industries, consuming up to 50% of plant electricity and frequently experiencing operational instabilities (including excessive vibration and main motor current fluctuations) that drive unplanned downtime, increased wear, and reduced throughput. Despite their importance, real-time autonomous optimization remains challenging due to the nonlinear interactions among grinding pressure, feed rate, separator speed, and aerodynamic factors, which limit traditional control strategies under varying loads. This paper presents a real-time operational optimization system for large-scale vertical roller mills using big industrial data and artificial intelligence (AI).… More >
 Open Access
Open Access
ARTICLE
Haotian Cao1,2, Qingsheng Zhu1,2,3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081695
Abstract Point Cloud Registration (PCR) is a basic task in computer vision, mobile robotics, and autonomous driving. PCR primarily faces challenges, including insufficient registration performance in low-overlap scenarios and high computational resource consumption in large-scale point cloud scenarios. Most recent PCR methods are transformer-based. Methods like transformers have quadratic computational complexity , leading to rapid increases in computational cost with large-scale point cloud data. To address these problems, an iterative PCR method named
 Open Access
Open Access
ARTICLE
Yao-Bo Long1, Yu-Ke Ouyang2, Bo Zhuang2, Ao-Qi Liu3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081203
Abstract This study addresses the real-time visual tracking task in edge environments by proposing a robust visual servoing control system based on a higher-order sliding mode observer, enabling a quadrotor UAV to autonomously track a moving soccer ball during outdoor sports broadcasts while relying solely on a monocular camera and an inertial measurement unit, thereby eliminating any dependency on external positioning or velocity sensors such as GPS. The system adopts a hierarchical control architecture in which the observer plays a central role: operating on resource-constrained edge devices, it leverages only visual information to estimate unknown external… More >
 Open Access
Open Access
ARTICLE
Pangwei Wang1,*, Jie Wang1, Zipeng Wang1, Hangrui Dong2, Li Wang1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080815
(This article belongs to the Special Issue: Intelligent Transportation System (ITS) Safety and Security)
Abstract Traffic holographic perception refers to the real-time, high-fidelity, and multi-dimensional sensing of traffic states through the fusion of heterogeneous sensors, including cameras, radars, and connected vehicle data. The multi-source perception data obtained thereby can provide a complete digital representation of the road network for the Intelligent Transportation System (ITS). However, sensors are vulnerable to environmental interference, which can result in data loss at specific points or along arterial highways for certain periods, potentially undermining system safety and decision-making reliability. To address these challenges, a deep learning method based on Graph Convolutional Networks (GCN) and Gated… More >
 Open Access
Open Access
ARTICLE
Bin Fang1, Qi Yu1, Han Wu2, Xingxing Hou2, Jingyu Zhang2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080210
(This article belongs to the Special Issue: AI-Driven Optimization for Secure and Sustainable Edge IoT Services)
Abstract The integration of Internet of Things (IoT) with blockchain technology introduces significant challenges in handling massive and frequent transaction data generated by distributed IoT devices. The Unspent Transaction Output (UTXO) model, widely adopted in blockchain systems like Bitcoin, faces critical scalability issues when applied to IoT environments. This is because the datasets it processes expand rapidly, which consumes a large amount of memory and increases the disk access latency of resource-constrained IoT nodes. Existing optimization approaches exhibit limitations in dynamic adaptability and protocol compatibility. To address these challenges, we propose an improved blockchain-empowered storage service More >
 Open Access
Open Access
ARTICLE
Ying Tang1, Chuanyi Ma2, Feng Guo1,*, Wenhao Sun1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079851
Abstract Road Abandoned Objects (RAOs) pose significant threats to traffic safety, particularly due to their small size, irregular shapes, and unpredictable distribution in complex road environments. The primary objective of this study is to develop an accurate and real-time detection framework for RAOs while maintaining low computational cost for practical deployment. To achieve this, we propose RAO-YOLO, a lightweight vision-based detection framework built upon an enhanced YOLO architecture. Specifically, a Mixed Aggregation Network (MANet) is introduced to improve multi-scale feature representation, and a Lightweight Shared Detail-Enhanced Detection (LSDD) head is designed to enhance localization accuracy for More >
 Open Access
Open Access
REVIEW
Xinjie Yao1, Junjie Zhu2, Tao Hong3,4, Dengyu Zhao5, Weikai Liu6, Guangsheng Xie7,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.075316
(This article belongs to the Special Issue: Attention Mechanism-based Complex System Pattern Intelligent Recognition and Accurate Prediction)
Abstract The attention mechanism, as a key technology for enhancing the performance of deep learning, is gaining increasingly widespread attention in medical image analysis due to its ability to focus on critical features and suppress redundant information. In recent years, the continuous evolution of attention methods has significantly improved their accuracy and robustness in key medical tasks such as lesion detection, tissue segmentation, and multimodal fusion, providing crucial support for building reliable clinical decision support systems. This paper systematically reviews the advances in attention-based methods for medical image analysis, comparing their performance with mainstream models like… More >
 Open Access
Open Access
ARTICLE
Ahmad Almufarreh1, Rogaia Hassan Osman Hassan2,3, Ashfaq Ahmad4, Muhammad Arshad2,5,*, Choo Wou Onn6
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082264
Abstract The explosive increase in connectivity has multiplied the volume and speed of network traffic, putting the world at greater risk from sophisticated and emerging cyber-attacks. Smart learning environments, which rely on cloud-based learning management systems, virtual classrooms, and interconnected educational devices, generate large volumes of dynamic network traffic that must be continuously monitored to protect sensitive academic data and ensure uninterrupted learning services. In this study, three supervised machine learning classifiers, namely Random Forest, Logistic Regression, and k-Nearest Neighbours (kNN), are designed and evaluated for anomaly detection using the UNSW-NB15 benchmark. Models are trained and… More >
 Open Access
Open Access
ARTICLE
Xiong Luo*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081416
Abstract Large multimodal models (LMMs) can produce fluent radiology reports, yet two clinically important error modes remain common: unsupported assertions and missed findings. Optimizing both under open supervision remains difficult because many pipelines still rely on overlapping parser families during training and evaluation. This paper introduces Truth-Anchored Dual-Extractor Counterfactual-Constrained Training (TA-DECT), which combines an ontology-derived atomic finding interface with four coupled objectives: structured prediction, dual-extractor minimax consistency on generated reports, deterministic counterfactual selectivity under evidence removal, and label-anchored completeness. In matched-path internal comparisons across chest radiographs (CheXpert, MIMIC-CXR, MIMIC-CXR-JPG) and chest computed tomography (CT; CT-RATE), TA-DECT More >
 Open Access
Open Access
ARTICLE
Zheng Xu1,2, Zihao Pan1, Ning Yang1, Daoxing Guo1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080559
(This article belongs to the Special Issue: Aerial Innovation Spectrum: All-Domain Research in UAV Communication, Navigation, and Autonomy)
Abstract Unmanned Aerial Vehicle (UAV) communications in complex electromagnetic environments face challenges such as strong interference, high dynamic Doppler shifts, and limited onboard computing power. In these scenarios, traditional blind beamforming algorithms suffer from slow convergence and difficulty in handling Gaussian-like signals (e.g., Orthogonal Frequency Division Multiplexing (OFDM)). To address these issues, this paper proposes a Lightweight Robust Transfer learning-based Blind Beam Forming method (LRT-BF). This method constructs a self-supervised optimization framework centered on a pre-trained signal classifier and innovatively introduces a joint loss function combining classification confidence guidance with output power minimization, achieving fully blind… More >
 Open Access
Open Access
ARTICLE
Asma Sattar1, Maryam Bukhari2, M. Saud Khan3, Anam Mustaqeem4, Mi Young Lee5, Seungmin Rho5,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078413
Abstract Video surveillance systems play an important role in maintaining security in smart city environments. In this context, person identification (Re-ID) systems based on deep learning are currently drawing substantial academic interest. However, these systems remain vulnerable to adversarial attacks. In existing methods, several attacks against Re-ID systems have been designed; nevertheless, they operate in the spatial domain. Existing attacks often suffer from perturbation visibility and low imperceptibility, making them easily detectable by human observers or automated detection systems. From this line of research, this study proposed a novel and potent alternative by designing frequency domain… More >
 Open Access
Open Access
ARTICLE
Shuaiyu Zhu1, Sergey Ablameyko1,2, Ji Li3,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082486
(This article belongs to the Special Issue: Advances in Image Generation: Theories, Architectures, and Applications)
Abstract Satellite remote sensing images pose significant challenges for object detection due to their high resolution, complex scenes, and large variations in target scales. To address the insufficient detection accuracy of the YOLOv11n model in remote sensing imagery, this paper proposes two improvement strategies. Method 1: (a) a Large Separable Kernel Attention (LSKA) mechanism is introduced into the backbone network to enhance feature extraction for small objects; (b) a Gold-YOLO structure is incorporated into the neck network to achieve multi-scale feature fusion, thereby improving the detection performance of objects at different scales. Method 2: (a) the More >
 Open Access
Open Access
ARTICLE
Zhichao Pei, Ou Ye*, Panyu Yang, Kaiwen He
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081490
Abstract To address the issue of insufficient transferability of existing adversarial example generation methods for vision-language pre-training (VLP) models, this paper proposes an adversarial example transfer method for VLP models based on negative sample feature perturbation. First, a novel cross-modal collaborative perturbation strategy is constructed. By introducing negative samples into the cross-modal perturbation mechanism, the strategy explores more perturbation directions, breaks the original modal alignment constraints and avoids the local focus of adversarial perturbations. Then, to reduce the computational cost, a dynamic threshold attack strategy is built to measure the modal similarity of the generated adversarial… More >
 Open Access
Open Access
ARTICLE
Peeyush Kumar Kamlesh1,*, Himanshi Sharma2, Shrikant Verma1, Ajay Singh Verma3,4, Reena Saxena5, Dinesh C. Sharma6
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081382
Abstract In the present work, Ba3PX3 (X = F, Cl, Br, I) all-inorganic and lead-free halide compositions have been studied as possible replacements for hybrid perovskites using first-principles calculations. All the considered materials were found to exhibit direct band gaps at the Γ-point, decreasing from 2.37 eV (Ba3PF3) to 1.48 eV (Ba3PI3). The optical calculations reveal strong absorption in the visible and near-UV regions, with the static dielectric constants ranging from 2.75 to 4.35 in the halide series. All the compounds are mechanically stable and have tuneable ductility and stiffness properties. Lattice stability is confirmed by thermodynamic analysis More >
 Open Access
Open Access
ARTICLE
Hongbin Wang1,2, Liusong Li1,2, Di Jiang1,2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079330
Abstract Multimodal sentiment analysis aims to fuse emotional information from data across different modalities to predict human emotional states. Although existing multimodal sentiment analysis methods have made significant progress, the heterogeneity between modalities still leads to an imbalance in feature space distribution, thereby hindering the effective learning and fusion of multimodal representations. In addition, the presence of emotion-irrelevant information in auxiliary modalities is another major factor contributing to differences in feature space distributions. To address this issue, we propose a Hierarchical Contrastive Representation Learning framework with Multimodal Feature Decoupling (HCRL-MFD). To reduce emotion-irrelevant information and optimize… More >
 Open Access
Open Access
ARTICLE
Yejin Kwon1, Jeongcheol Lee1, Youngbom Park2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080249
Abstract The web-based High-Performance Computing (HPC) platform provides a simulation environment that enables users to perform computational science and engineering tasks through web services, thereby eliminating the need for complex terminal-based environments. Notwithstanding the aforementioned advantages, extant platforms frequently necessitate a considerable degree of user expertise, whilst the intricacy of simulation configuration and execution engenders limitations in terms of accessibility and usability. Furthermore, while Retrieval-Augmented Generation (RAG)-based systems are effective for information retrieval, they are insufficient for accurately constructing and invoking executable service tools. In order to address these limitations, this study proposes a user agent… More >
 Open Access
Open Access
ARTICLE
Kemeng Zhu1, Dingju Zhu1,2,*, Shihua Mao1, Jinchen Wu3, Depeng Kong4, Kaileung Yung5, Andrew W. H. Ip6
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082431
Abstract Unmanned aerial vehicles (UAVs) have become an increasingly important platform for agricultural remote sensing, yet the accurate recognition of pests and diseases is frequently compromised by drastic scale variability and complex environmental backgrounds. To address these challenges, this study introduces a novel attention-driven approach centered on a Multi-Scale Grouped Channel–Spatial Dual Attention (MS-GCDA) mechanism. The MS-GCDA module achieves robust feature calibration by decoupling and jointly modeling multi-scale spatial contexts and grouped channel dependencies, which significantly enhances the model’s sensitivity to fine-grained disease symptoms while suppressing background clutter. This core mechanism is integrated into Augmented EfficientNet… More >
 Open Access
Open Access
ARTICLE
Vinh Truong Hoang*, Nghia Dinh, Luu Quang Phuong, Kiet Tran-Trung, Ha Duong Thi Hong, Bay Nguyen Van, Hau Nguyen Trung, Thien Ho Huong
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078743
(This article belongs to the Special Issue: Attention Mechanism-based Complex System Pattern Intelligent Recognition and Accurate Prediction)
Abstract Visual speech recognition is a central problem in computer vision, encompassing both lip reading (visual speech recognition) and sign language recognition. Although substantial progress has been achieved independently on each task, their complementary characteristics have rarely been explored jointly. In this work we propose UniModal-LSR (Unified Multimodal Lip and Sign Recognition), a novel deep learning framework that jointly addresses lip reading and sign language recognition within a single multimodal architecture. By exploiting shared properties of visual communication channels, namely temporal dynamics, spatial articulation structure, and contextual dependencies, the proposed model enables bidirectional transfer of knowledge… More >
 Open Access
Open Access
ARTICLE
Li Chen1, Fan Zhang2,*, Guangwei Xie3, Yanzhao Gao1, Xiaofeng Qi1, Mingqian Sun2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.078314
Abstract Remote sensing object detection aims to identify and localize specific targets in satellite or aerial imagery. Spiking Neural Networks (SNNs), benefiting from their implicit feedback-based and event-driven brain-inspired dynamics, offer a promising solution to alleviate the high energy consumption of conventional ANN-based detection models. However, existing SNN-based approaches for remote sensing object detection—particularly for small, arbitrarily rotated objects—are still in their infancy and suffer from a substantial performance gap compared with ANN counterparts. In this work, we draw inspiration from the hierarchical sparse perception mechanisms of biological vision and integrate dynamic receptive field modulation into… More >
 Open Access
Open Access
ARTICLE
Kang-Woo Lee, Dong-Hee Lee*, Dae-Il Kwon*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081667
(This article belongs to the Special Issue: AI-Enabled Prognostics and Health Management: Advanced Methodologies, Intelligent Systems, and Field Applications)
Abstract Early-life cycle-life prediction for lithium-ion batteries—estimating end-of-life from initial cycles—is valuable for rapid cell screening and battery health management. We investigate whether an explicit correlation-structure descriptor can complement physics-informed ΔQ-based indicators and generic early-cycle statistical features on the Severson 124-cell benchmark. We develop a lightweight hybrid framework that combines ΔQ-based health indicators, data-driven statistical features, and Laplacian Eigenmaps embeddings derived from a Pearson-correlation feature graph, with XGBoost used as the predictor. Across five feature configurations (ΔQ Only, ΔQ + Statistics, Hybrid Append, VIF + Laplacian, and Integrated Laplacian), we evaluate pointwise regression accuracy using RMSE and R2 together… More >
Graphic Abstract
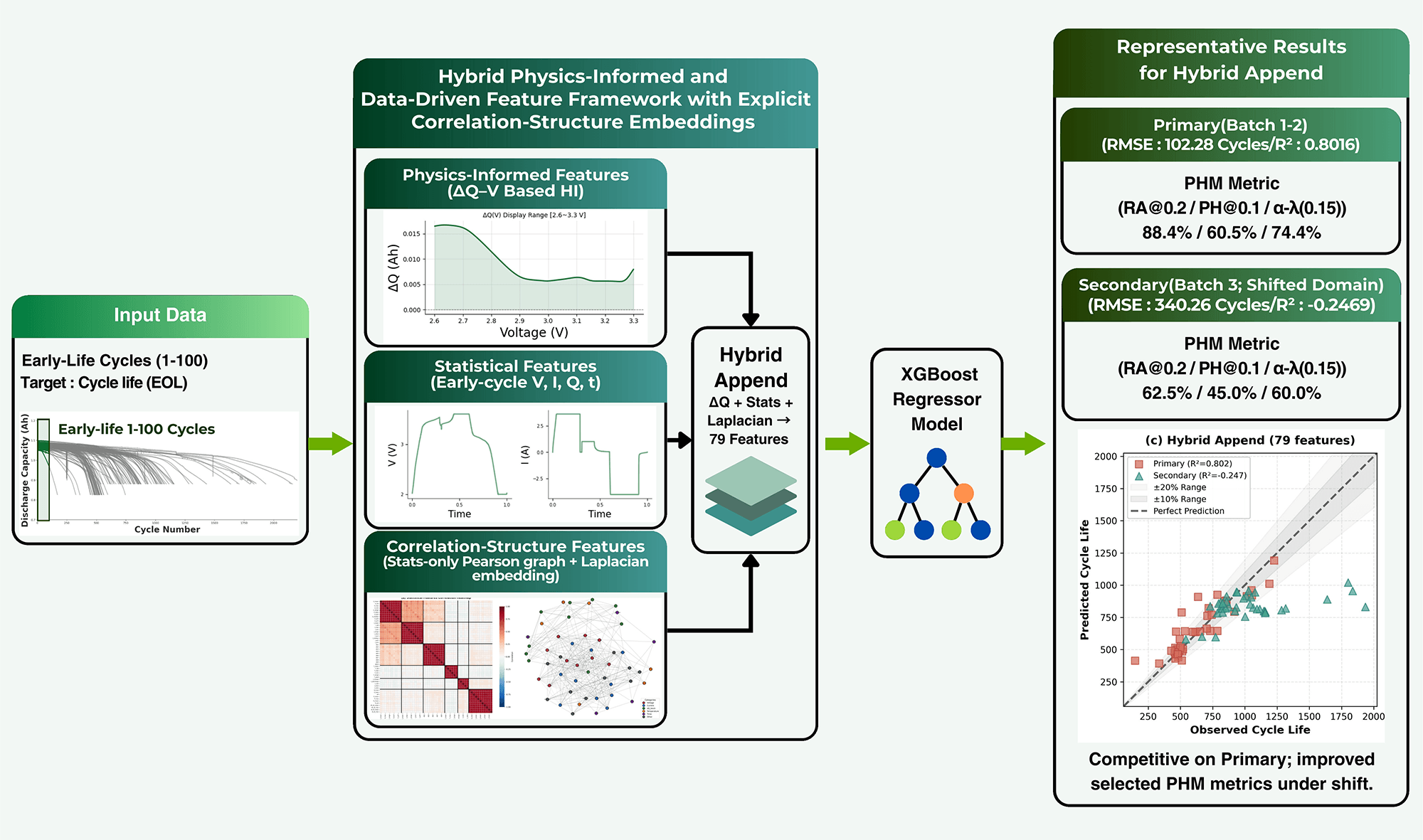
 Open Access
Open Access
ARTICLE
DongHwan Ku, Sun Park*, JongWon Kim
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079582
(This article belongs to the Special Issue: Advancing Edge-Cloud Systems with Software-Defined Networking and Intelligence-Driven Approaches)
Abstract In future smart cities, ensuring urban safety requires data-driven decision-making through real-time monitoring tailored to dynamic, complex environments. Such surveillance relies on diverse mobile sensor devices, including drones, robots, patrol vehicles, and portable sensors. However, scaling and validating these systems directly in the real world is constrained by high costs, safety risks, and limited reproducibility across operating conditions. A scalable Digital Twin (DT) model can overcome these constraints by reproducing real-world mobile surveillance in a virtual environment, enabling large-scale simulations of sensor deployment, communication scenarios, and high-density visual data processing. Nevertheless, digital twins still face… More >
 Open Access
Open Access
ARTICLE
Nikita Sakovich1, Dmitry Aksenov1, Ekaterina Pleshakova1,*, Sergey Gataullin1,2
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079522
Abstract We introduce the DARE-Q (Distribution-Aware Residual Entropy Quantization) method—a post-training quantization method for neural network weights designed to reduce bit-width with minimal degradation of model quality. Unlike traditional approaches that solely optimize the mean squared error of weight approximation, DARE-Q additionally considers the entropy of the quantization residual, allowing for control over the statistical properties of the resulting error. The method is based on channel-wise symmetric uniform quantization with scaling based on a combined loss function that includes L2 distortion and entropy regularization. The DARE-Q method is implemented as a compact DAREQuantLinear module which can… More >
 Open Access
Open Access
ARTICLE
Akmalbek Abdusalomov1, Kudratjon Zohirov2, Sojida Ochilova2, Jakhongir Oramov3, Zafar Ruziyev3, Malika Rustamova4, Gulrukh Sherboboyeva5, Komil Tashev6,7, Young Im Cho1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081292
(This article belongs to the Special Issue: Integrating Generative AI with UAVs for Autonomous Navigation and Decision Making)
Abstract Unmanned aerial vehicles (UAVs) are also increasingly becoming more often in the transportation infrastructure of smart cities, so that they can successfully achieve real-time observation of traffic, emergency coordination, and two-way communication relaying. However, the security and privacy risks arising in open, highly mobile intelligent transportation systems (ITS) enabled by UAVs are critical, as they pose threats of impersonation, replay, Sybil, and tracking attacks. Secondly, standard static authentication mechanisms are unable to support dynamic risk environments and excessive resource consumption on UAV platforms with limited capacity. To address these challenges, this study introduces a Generative-AI-assisted… More >
 Open Access
Open Access
ARTICLE
Xiangqin Chen*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079663
Abstract Simultaneous localization and mapping (SLAM) must remain reliable when sensing suites and operating conditions vary across platforms and deployments. Beyond correspondence degradation, a dominant deployment failure mode is misweighted constraints: under distribution shift, uncertainty estimates can become miscalibrated, allowing a small set of overconfident factors to dominate iterative optimization and destabilize inference. This article presents conformal-calibrated foundation-factor graph SLAM (
 Open Access
Open Access
ARTICLE
Lei Wang1, Hongji Luo2, Yong Heng2, Jingnan Tang2, Xiaochuan Ju2, Jianwei An1,*, Haitao Xu1, Xianwei Zhou1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.082418
(This article belongs to the Special Issue: Advanced Networking Technologies for Intelligent Transportation and Connected Vehicles)
Abstract In intelligent connected vehicles (ICVs) system, driving users connect to service providers (SPs) to obtain location-based services (LBS). Users transmit large volumes of encrypted sensitive information related to their itineraries to SPs to access value-added services. Attackers may launch chosen-ciphertext attacks (CCA) against SPs by exploiting the malleability of homomorphic encryption. This enables adversaries to infer or steal private key information, thereby threatening the long-term privacy of user data. Furthermore, existing key management technologies in ICVs system predominantly rely on passive defense strategies and suffer from limitations such as single protection mechanisms, delayed updates, and More >
 Open Access
Open Access
ARTICLE
Zhihao Zhang1,#, Zhuodong Liu1,#, Xiangyu Li2, Lei Zhang1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081922
(This article belongs to the Special Issue: Recent Advances in Malware Detection)
Abstract Financial fraud detection across institutions faces a fundamental tension between the need for diverse training data and regulatory prohibitions on sharing sensitive records. Existing federated learning approaches suffer from performance degradation under non-IID distributions and substantial utility losses when uniform differential privacy is applied to inherently sparse fraud signals. To this end, this paper proposes HiFraud, a hierarchical federated framework featuring three key components: fraud-aware dynamic clustering with complementarity regularization to group institutions by fraud pattern similarity while preserving rare-type representation; star-chain knowledge transfer augmented by not-true-class distillation to propagate novel fraud patterns rapidly within… More >
 Open Access
Open Access
ARTICLE
Zhe Wang1, Yu Yan2, Junqi Tong1, Yijun Lin1, Dechun Yin1,*, Xiaoliang Zhao1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081155
Abstract As software applications grow increasingly large and complex, traditional code vulnerability detection methods struggle with performance and efficiency. Although code visualization-based algorithms have demonstrated effectiveness in capturing sparse features and complex workflows in large-scale source code, their capacity to extract global semantic information and intricate long-range dependencies remains limited. Recent large language model (LLM)-based approaches have shown promising accuracy by leveraging rich contextual information, but their high computational cost often limits practical efficiency. To address these challenges, we propose VulSCP, a new framework that integrates sequential convolution with a parallel attention mechanism. Specifically, VulSCP first… More >
 Open Access
Open Access
ARTICLE
Junyi Wang1, Jianghai Geng1,*, Jiaqi Liu2, Haibin Zhu3
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080895
Abstract In intelligent manufacturing and remanufacturing systems, the thermal safety of the power distribution infrastructure is crucial for ensuring production continuity, equipment reliability, and operational resilience. Traditional temperature monitoring methods often have problems such as high deployment costs, strong environmental sensitivity, or limited physical interpretability in distributed workshop environments. To address these limitations, this study proposes a physically information-driven intelligent thermal color-changing fault identification framework. Based on thermochromic experiments, irreversible color-changing coatings are selected, which are combined with a visual-based computing pipeline for autonomous overheating detection. The framework proposes a thermal fault temperature identification algorithm based… More >
 Open Access
Open Access
REVIEW
Yuyin Ma1, Yufang Liu1, Yijun Lu2, Zhen Tian3, Fujiang Yuan4, Yanhong Peng4,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080309
(This article belongs to the Special Issue: Computational Materials Design and Intelligent Processing for Advanced Alloys and Manufacturing Systems)
Abstract Additive manufacturing (AM) has emerged as a transformative technology in modern manufacturing, offering unprecedented capabilities for producing complex geometries and customized components. However, the widespread adoption of AM is hindered by insufficient quality control, stemming from the multi-factor coupling characteristics of the manufacturing process. Machine learning (ML) presents a promising solution by enabling data-driven approaches to process optimization, quality prediction, and defect detection. This review examines the application landscape of ML techniques in AM through comprehensive analysis of recent literature. The study categorizes ML applications into four primary domains: real-time process monitoring and control, process… More >
 Open Access
Open Access
ARTICLE
Rubina Castro1,2, Bruno Silva1,3, Luiz Guerreiro Lopes1,4, Fábio Mendonça1,2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079979
(This article belongs to the Special Issue: Advances in Nature-Inspired and Metaheuristic Optimization Algorithms: Theory, Applications, and Emerging Trends)
Abstract Path planning for autonomous underwater vehicles requires reliable and computationally efficient methods, particularly in cluttered environments. This work presents a comparative evaluation of representative approaches, including metaheuristic optimization methods (continuous genetic algorithm, particle swarm optimization, gray wolf optimizer, and Jaya), a sampling-based method (probabilistic roadmap with genetic refinement), a reactive strategy (artificial potential fields), and a control-based approach (model predictive control with control barrier functions). The algorithms are assessed in a controlled two-dimensional simulated workspace with randomly generated obstacles and systematically increasing obstacle density. Each configuration is evaluated across multiple independent trials using metrics such… More >
 Open Access
Open Access
REVIEW
Shan Jiang1, Wenxin You2, Haoran Zhang3, Shichang Xuan3,*, Jiaxing Shen4
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079321
Abstract Large Language Models (LLMs) have been playing a transformative role in natural language understanding and generation, yet adapting LLMs to domain-specific and privacy-sensitive data remains challenging under centralized training. Federated Learning (FL) provides a promising alternative by enabling training LLMs collaboratively without sharing raw data. However, integrating FL and LLMs introduces new challenges, including model size, device heterogeneity, non-IID data, and alignment requirements. This survey offers a structured overview of the federated LLM ecosystem. We present a comprehensive taxonomy encompassing system architectures, advanced data strategies for addressing heterogeneity, and retrieval-augmented generation in federated contexts. Additionally, More >
 Open Access
Open Access
ARTICLE
Mohammed Saad Javeed1, MD AL Rafi2, Arifa Akter Eva3, Muhammad Firoz Mridha3, Qiangfu Zhao4,*, Jungpil Shin4,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.076825
(This article belongs to the Special Issue: Advances in Machine Learning and Artificial Intelligence for Intrusion Detection Systems)
Abstract Hybrid and multi-cloud infrastructures make IP address management (IPAM) difficult, especially when IP and Domain Name System (DNS) records must stay consistent across on-premises networks and cloud platforms. Traditional IPAM tools often lack deep automation and cross-platform visibility, which leads to DNS drift, IP conflicts, and configuration errors. This paper proposes a unified, Application Programming Interface (API)-driven IPAM framework that integrates Infoblox Network Identity Operating System (NIOS) with Amazon Web Services (AWS) Route53 and Azure DNS using Infrastructure-as-Code and CI/CD pipelines. We generate an IPAM event log from Infoblox API simulations and fuse it with More >
 Open Access
Open Access
ARTICLE
Jiayi Tang1, Liang Cao2,*, Guanghui Xu1, Manqi Dong2, Ming Li3
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081488
(This article belongs to the Special Issue: M5S: Multiphysics Modelling of Multiscale and Multifunctional Materials and Structures)
Abstract The accelerated design of next-generation semiconductor interconnects faces a critical “applicability gap”. Purely data-driven models effectively navigate vast chemical spaces, but they often yield candidates that are theoretically performant yet violate practical manufacturing constraints. To bridge this disconnect, this study proposes a neuro-symbolic decision support framework that systematically integrates inductive graph learning with deductive engineering logic for Safe-by-Design material screening. The framework operates through a hierarchical dual-stream architecture. First, an inductive Graph Neural Network (GNN) engine transforms 3D crystal structures into topological graph representations to predict thermodynamic stability and metallicity with high discriminative power (AUC… More >
 Open Access
Open Access
ARTICLE
Peiying Zhang1,2, Yihong Yu1,2, Lizhuang Tan3,4,*, Shuqing He5, Jian Wang6, Ameer El-Sayed7
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.081224
(This article belongs to the Special Issue: Advanced Edge Computing and Artificial Intelligence in Smart Environment)
Abstract As a core information infrastructure in the 6G era, the Space-Air-Ground Integrated Network (SAGIN) integrates space-based, air-based, and ground-based network resources to achieve seamless communication across all domains. However, its characteristics such as heterogeneous node coupling and dynamic topology changes make it prone to cascading failures, severely threatening critical business continuity in Internet of Things (IoT) applications spanning smart cities, healthcare, transportation, and industrial automation. This paper conducts systematic research addressing challenges including modeling difficulties in SAGIN cascading failure propagation, insufficient coordination of defense strategies, and poor resource adaptability. First, a multi-factor coupled dynamic model… More >
 Open Access
Open Access
REVIEW
Hitesh Mohapatra*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080961
(This article belongs to the Special Issue: AI-Driven Optimization for Secure and Sustainable Edge IoT Services)
Abstract This review systematically analyzes Reinforcement Learning approaches for self-healing in energy-constrained secure edge IoT networks across 82 studies from 2020 to 2026. Unlike existing surveys that focus on general RL applications, the proposed review focuses on a three-level taxonomy that uniquely addresses edge IoT deployment realities through formulation-scope-hardware mapping. The work develops a novel three-level taxonomy classifying recovery scope (node, link, service, network), RL formulations (tabular, deep, multi-agent, model-based), and constraint integration (energy, latency, security, hybrid), revealing service migration dominance at 30% coverage and node recovery achieving 38% maximum energy savings. Normalized performance baselines establish More >
 Open Access
Open Access
ARTICLE
Xionglve Li1, Changsheng Hou2,*, Yuzhou Huang3, Zhenyu Qiu1, Gang Hu1, Bingnan Hou1, Wei Dong1, Zhiping Cai1
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080452
Abstract The Internet inter-domain paths, i.e., the AS paths, are important for network management, traffic engineering, and security. Due to business confidentiality, security, and privacy, the AS path information is non-public. Due to limited measurement resources, obtaining AS path information by measurement-based approaches is not scalable. Therefore, path inference approaches are proposed to broaden the availability of path information. These approaches assume that AS paths remain stable over a certain period of time, yet conflicting research findings question this assumption. Furthermore, the duration of the “certain period of time” is not clearly defined. Thus, we aim… More >
 Open Access
Open Access
ARTICLE
Xuan-Thuc Nguyen1, Le-Minh Nguyen1, Ngoc-Quynh Nguyen1, Nhu-Nghia Bui2, Dinh-Quy Vu3,*, Thai-Viet Dang2,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080008
(This article belongs to the Special Issue: Aerial Innovation Spectrum: All-Domain Research in UAV Communication, Navigation, and Autonomy)
Abstract The development of unmanned automated vehicles (UAVs) has become a key focus in aerial robotics, fueling the need for navigation systems capable of performing complex and delicate tasks with speed and precision. However, the end-to-end path tracking process often encounters challenges in learning efficiency, generalization, and varying environmental conditions. In this paper, we propose the novel IRL-TP framework for learning-based UAVs’ trajectory planning that employs a deep inverse reinforcement learning (IRL) approach. Firstly, the RL-based path planner must develop a reward function that effectively captures flight safety, collision avoidance, trajectory smoothness, and navigation efficiency within… More >
 Open Access
Open Access
REVIEW
Manjodh Kaur1, Princy Randhawa2,*, Jitendra Jaiswal2, Deepak Dubal3, Ravindra N. Bulakhe4,5, Deepanraj Balakrishnan6, Nithesh Naik7,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079503
Abstract This review emphasizes the growing role of artificial intelligence (AI) in transforming the materials discovery process into a data-driven and autonomous approach. It systematically traces the evolution of scientific paradigms in materials science and examines how machine learning, generative models, and AI agents are revolutionizing the design, screening, and optimization of materials. A key contribution is a detailed, step-by-step machine learning framework that guides researchers through data collection, preprocessing, feature engineering, model development, and validation, utilizing publicly available materials databases and computational tools. Additionally, the review discusses the latest advances in generative AI and autonomous More >
 Open Access
Open Access
ARTICLE
Zhen Yan1, Jiani Huang1, Yanlin Gu1, Qingqing Xu1, Yuyu Guo1, Kun Lin2, Juan Hou1,*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079204
(This article belongs to the Special Issue: Mechanical Behavior of Materials with Advanced Modeling and Characterization)
Abstract This study addresses the challenge of balancing “high deposition efficiency with large layer thickness” and “component mechanical integrity” in Laser Powder Bed Fusion (LPBF) additive manufacturing. Using 304L stainless steel as an example, a hybrid modeling strategy combining physical mechanism models and residual machine learning was proposed, achieving accurate prediction of densification at H = 60, 90, and 120 μm (test set R2 = 0.833, MAE = 0.104). Within the Doehlert matrix experimental design framework, the coupled effects of laser power, scanning speed, and scanning spacing on densification behavior, microstructure evolution, and mechanical response at different… More >
 Open Access
Open Access
ARTICLE
Chellaiah Ayyanar, Sumit Pramanik*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.079080
(This article belongs to the Special Issue: Mechanical Behavior of Materials with Advanced Modeling and Characterization)
Abstract The potential of nontoxic elastomers like polydimethylsiloxane (PDMS) and bioceramic hydroxyapatite (HA) crystals has been demonstrated in numerous advanced applications. However, their crosslinking behavior in a composite system has not yet been modeled through simulation. Therefore, we employed a simulation-based approach to construct initial unit cell models of PDMS and HA, and for the first time, created PDMS-HA molecular structures using Materials Studio (MS) software. Molecular dynamics (MD) methods were applied to gain deeper insight into the structural framework and physical properties of PDMS, HA, and PDMS-HA composite. Equilibrium state via Forcite, physical, chemical, and thermal… More >
 Open Access
Open Access
ARTICLE
Chanyoung Kim, Jion Kim, Byeong-Seok Shin*
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080992
Abstract Diffusion-based methods have substantially improved the performance of full-body Text-to-Motion (T2M) generation from natural language descriptions. Despite this progress, accurately capturing the fine-grained semantics of composite prompts remains challenging. Approaches that rely solely on a single global text condition often fail to retain part-specific semantic cues, leading to deviations in the motions of certain body parts from the intended descriptions. Recent methods have attempted to address this by incorporating both global and local conditions, yet these are typically combined using fixed ratios or applied in separate stages, which restricts their adaptability to evolving semantic requirements… More >
Graphic Abstract
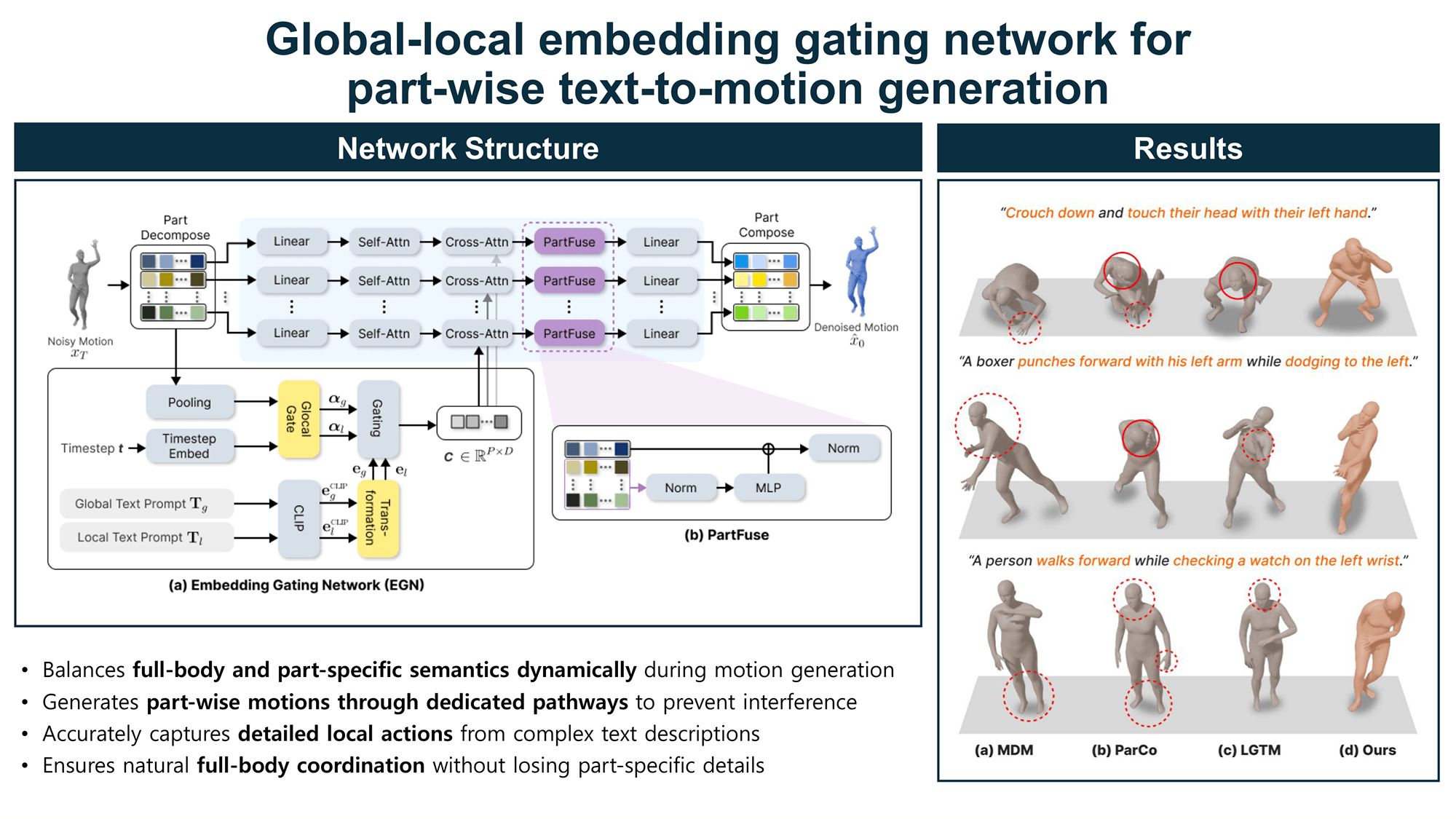
 Open Access
Open Access
ARTICLE
Ammar Odeh*, Osama Alhaj Hassan, Anas Abu Taleb
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080940
Abstract The rapid growth of sophisticated malware and the increasing diversity of computing environments have exposed critical limitations in traditional centralized malware detection systems, particularly in data privacy, scalability, and adaptability. This study proposes a privacy-preserving, collaborative malware-detection framework that leverages federated learning to improve detection accuracy while keeping sensitive data local to participating devices. The objective is to address emerging malware threats by combining behavioral and memory-based analysis within a decentralized learning paradigm. The proposed framework employs federated learning to train a global malware detection model without transferring raw data. Each client locally extracts discriminative… More >
 Open Access
Open Access
ARTICLE
Zhaoxu Zhou, Yanjiang Liu, Zibin Dai*, Junwei Li
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080072
Abstract Stream ciphers are simple to implement and fast at encrypting and decrypting data, making them very important in information security. Boolean functions are a core part of stream ciphers. However, their mainstream hardware implementations face two main problems, including wasted area resources and excessive critical path delay. These issues limit the energy efficiency and integration level of stream cipher chips. To address these problems, this paper proposes an energy-efficient design method for a 64-bit Boolean function reconfigurable operation unit (BFROU), aiming to improve the computational efficiency of Boolean functions in stream ciphers. To optimize the… More >
 Open Access
Open Access
ARTICLE
Bhanu Talwar1,*, Puneet Thapar1, Tahani Alsubait2, Mai Alduailij3, Ateeq Ur Rehman4,*, Salil Bharany5
CMC-Computers, Materials & Continua, DOI:10.32604/cmc.2026.080977
(This article belongs to the Special Issue: Advanced Localization and Multi-Sensor Fusion in WSN, IoT & VANET)
Abstract Wireless Sensor Networks (WSNs) play a vital role in smart city Internet of Things (IoT) applications, including environmental monitoring, intelligent transportation, and infrastructure management. However, limited battery capacity, uneven energy consumption, and inefficient clustering and routing mechanisms significantly reduce network lifetime, reliability, and scalability, especially in large-scale IoT deployments. Traditional routing protocols often rely on single-objective optimization or static clustering strategies, which fail to maintain long-term energy balance and stable communication performance. To address these challenges, this paper proposes iPAFAR, a Pareto-based multi-objective clustering and routing framework designed for IoT-enabled WSNs. The proposed model formulates… More >