Submission Deadline: 31 December 2026 View: 557 Submit to Special Issue
Dr. Mahmoud Eid Farfoura
Email: m.farfoura@zuj.edu.jo
Affiliation: Cybersecurity Department, Al-Zaytoonah University of Jordan, Amman, Jordan
Research Interests: machine learning, malware detection, cybersecurity, information security, digital watermarking, information hiding, multimedia security, video processing, data protection, feature engineering, lightweight deep learning models

Prof. Mohammad Alia
Email: dr.m.alia@zuj.edu.jo
Affiliation: Cybersecurity Department, Al-Zaytoonah University of Jordan, Amman, Jordan
Research Interests: information security, cryptography, network security, cryptocurrency, system analysis and design

Prof. Adnan Hanif
Email: adnan_hnaif@zuj.edu.jo
Affiliation: Cybersecurity Department, Al-Zaytoonah University of Jordan, Amman, Jordan
Research Interests: network security, computer networks and communications, information security, parallel computing

Dr. Ibrahim Mashal
Email: i.mashal@zuj.edu.jo
Affiliation: Cybersecurity Department, Al-Zaytoonah University of Jordan, Amman, Jordan
Research Interests: internet of things, wireless sensor networks, artificial intelligence, recommender systems, smart homes, multi-criteria decision making methods, technology adoption and acceptance, malware detection

Dr. Ahmad Alkhatib
Email: ahmad.alkhatib@zuj.edu.jo
Affiliation: Cybersecurity Department, Al-Zaytoonah University of Jordan, Amman, Jordan
Research Interests: wireless sensor networks, WSN applications, computer networks and communications, road traffic management systems, localization, forest fire detection systems, natural disaster detection systems, internet of things, ad hoc networks, intelligent transportation systems, optical fiber, cloud computing, satellite communication, robotics, machine learning, malware detection

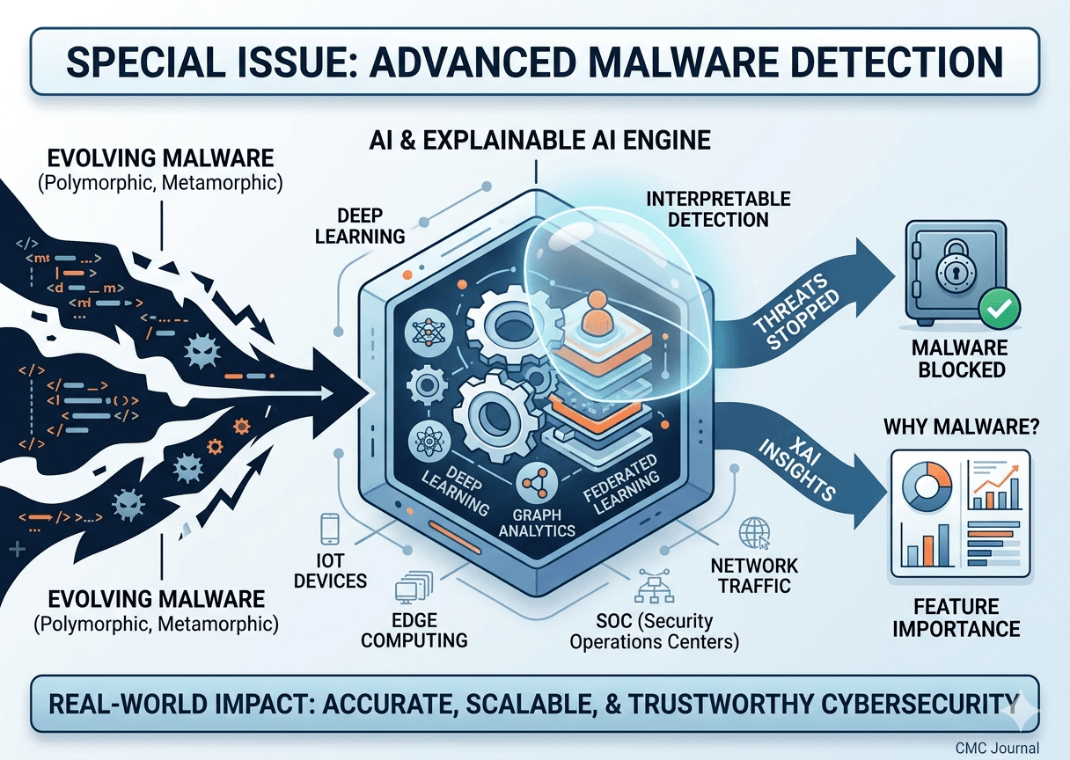
Malware is rapidly evolving—using polymorphism, metamorphism, and AI-driven behaviors—to evade traditional signature- and rule-based defenses. This Special Issue addresses that gap by focusing on next-generation malware detection methods that combine accuracy, robustness, scalability, and interpretability. It prioritizes practical, deployable research using techniques such as machine learning, deep learning, graph analytics, and explainable AI. Emphasis is placed on industrial relevance and real-world challenges including production-scale deployment, SOC performance, integration with existing cybersecurity systems, and operation on resource-constrained platforms (IoT/edge). The goal is to advance state-of-the-art methods while improving the reliability and trustworthiness of cyber-physical systems.
Theme:
Advanced and Interpretable Malware Detection in Modern Cyber Environments
Key Topics of Interest:
· AI-driven malware detection methods
· Deep learning for static and dynamic analysis
· Graph-based and geometric deep learning approaches
· Malware detection for IoT and edge devices
· Defenses against adversarial attacks and robust detection techniques
· Explainable and interpretable detection models
· Federated learning for privacy-preserving detection
· Behavioral and anomaly-based detection
· Detection in encrypted traffic
· Benchmark datasets and evaluation frameworks
· Real-world system deployment and SOC applications
· Scalable, real-time detection architectures
· Integration with existing cybersecurity infrastructures
· Industry datasets and operational benchmarking
· Cryptographic methods for secure malware analysis
This concise summary captures the Special Issue's focus on innovative, practical, and interpretable malware detection research with strong attention to deployment and industrial impact.


 Submit a Paper
Submit a Paper Propose a Special lssue
Propose a Special lssue