This journal publishes original research papers of reasonable permanent intellectual value, in the areas of computer modeling in engineering & Sciences, including, but not limited to computational mechanics, computational materials, computational mathematics, computational physics, computational chemistry, and computational biology, pertinent to solids, fluids, gases, biomaterials, and other continua spanning from various spatial length scales (quantum, nano, micro, meso, and macro), and various time scales (picoseconds to hours) are of interest. Papers which deal with multi-physics problems, as well as those which deal with the interfaces of mechanics, chemistry, and biology, are particularly encouraged. Novel computational approaches and state-of-the-art computation algorithms, such as soft computing, artificial intelligence-based machine learning methods, and computational statistical methods are welcome.
Science Citation Index (Web of Science): 2024 Impact Factor 2.5; Current Contents: Engineering, Computing & Technology; Scopus Citescore (Impact per Publication 2024): 4.4; SNIP (Source Normalized Impact per Paper 2024): 0.693; RG Journal Impact (average over last three years); Engineering Index (Compendex); Applied Mechanics Reviews; Cambridge Scientific Abstracts: Aerospace and High Technology, Materials Sciences & Engineering, and Computer & Information Systems Abstracts Database; CompuMath Citation Index; INSPEC Databases; Mathematical Reviews; MathSci Net; Mechanics; Science Alert; Science Navigator; Zentralblatt fur Mathematik; Portico, etc...
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080595 - 27 April 2026
(This article belongs to the Special Issue: Advanced Image Segmentation and Object Detection: Innovations, Challenges, and Applications)
Abstract Knowledge distillation bridges the performance gap between camera-based and LiDAR-based 3D detectors by leveraging the precise geometric information from LiDAR. However, cross-modal knowledge transfer remains challenging due to the inherent modality heterogeneity between LiDAR and camera data, which often leads to instability during training. In this work, we find that these instabilities are closely related to distribution mismatch in the cross-modal feature space and noisy teacher signals. To address this issue, we propose a novel distribution-aware cross-modal distillation framework, named DA-T3D. Specifically, we first explicitly model the LiDAR teacher’s Bird’s-Eye-View (BEV) feature distribution and use… More >
 Open Access
Open Access
EDITORIAL
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.083154 - 27 April 2026
(This article belongs to the Special Issue: Scientific Computing and Its Application to Engineering Problems)
Abstract This article has no abstract. More >
 Open Access
Open Access
EDITORIAL
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.082568 - 27 April 2026
(This article belongs to the Special Issue: Next-Generation Intelligent Networks and Systems: Advances in IoT, Edge Computing, and Secure Cyber-Physical Applications)
Abstract This article has no abstract. More >
 Open Access
Open Access
REVIEW
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079830 - 27 April 2026
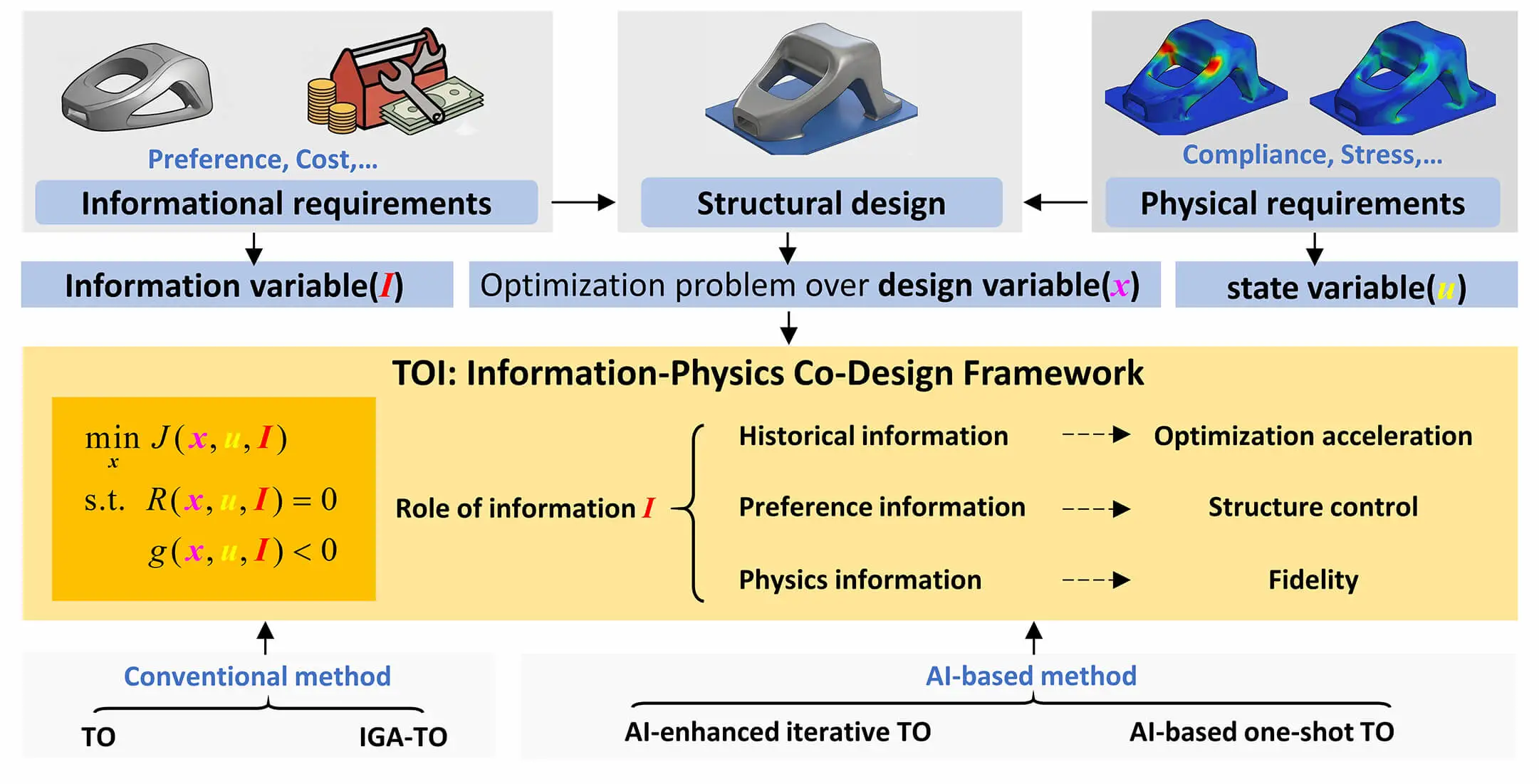
(This article belongs to the Special Issue: Topology Optimization: Theory, Methods, and Engineering Applications)
Abstract Topology optimization (TO) has become a core computational paradigm for structural design by defining optimality through physics-based objectives and constraints. However, practical engineering design often involves incomplete and imperfect physical modeling due to multi-physics coupling, manufacturing uncertainty, and computational constraints, leaving critical design factors insufficiently captured in purely physics-driven formulations. In parallel, data-driven and generative methods have enabled rapid topology generation and intent-aware design exploration, yet often weaken explicit optimality guarantees. This review argues that these seemingly divergent developments can be organized under a unified information–physics perspective. We term this emerging field Topology Optimization Informatics… More >
Graphic Abstract
 Open Access
Open Access
REVIEW
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.076279 - 27 April 2026
(This article belongs to the Special Issue: Advanced Computational Methods in Multiphysics Phenomena)
Abstract The Element-Free Galerkin (EFG) method was originally developed for linear solid mechanics problems, using Moving Least Squares (MLS) approximations to construct shape functions for the numerical approximation of the displacement field and its variations within the weak form of the equilibrium equations. Over the past decades, it has evolved into a versatile meshfree framework applicable to a broad spectrum of engineering and scientific problems. This review provides a comprehensive account of the main advances in EFG, tracing its development from the original formulation and early challenges to the strategies devised to overcome them. Subsequent improvements More >
 Open Access
Open Access
REVIEW
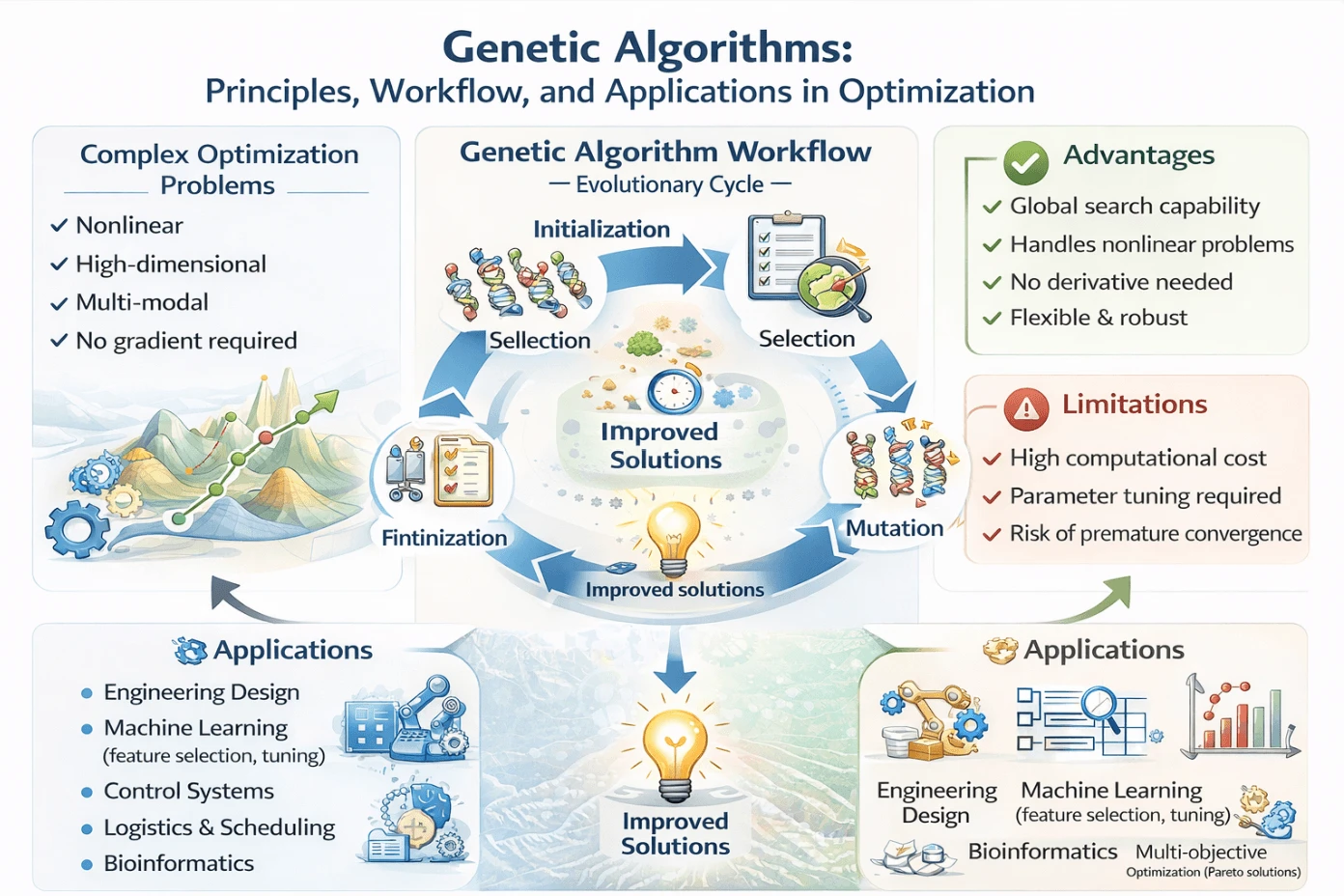
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079859 - 27 April 2026
Abstract This paper provides a thorough examination of Genetic Algorithms (GAs), a category of evolutionary computation methods derived from the concepts of natural selection and genetics. The main concept and operational principle of GAs are elucidated, highlighting the evolution of populations of candidate solutions across multiple generations to get optimal or near-optimal solutions for complicated problems. The paper delineates the sequential phases of a conventional GA, encompassing problem formulation, solution encoding, initialization of population, fitness evaluation, selection, crossover, mutation, and termination criteria, so offering a coherent framework for comprehending the algorithm’s functionality. Moreover, numerous prominent genetic… More >
Graphic Abstract
 Open Access
Open Access
REVIEW
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079037 - 27 April 2026
Abstract Snake Optimizer (SO) is a popular optimization algorithm developed by Hashim and Hussien, based on the competitive and selective mating nature of snakes. By emulating such natural methods, SO presents an intelligent method to solve complicated optimization problems, making it a valuable tool in various scientific and technological applications. This paper provides an extensive review of the SO, its inception, the development of different variants, and applications. This paper identifies several SO variants, such as improved SO variants using different strategies, hybridized SO variants with other metaheuristics, Binary SO variants to solve discrete optimization problems,… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079258 - 27 April 2026
Abstract Cracks can severely degrade the integrity and service performance of plate structures. Although most existing studies focus on identifying straight crack patterns using dynamic response data, curved crack paths have received far less attention, despite being more realistic in practice and having a stronger influence on structural behaviour. This study presents a computational and experimental framework for analyzing and identifying curved crack paths in cantilever plate structures based on dynamic response characteristics. Curved crack paths are modelled using second-order polynomial equations. Finite Element Analysis (FEA) is employed to evaluate the effects of polynomial coefficients and… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079375 - 27 April 2026
Abstract In structural optimization, data-driven surrogate models are often explored as alternatives to finite element analysis to reduce computational cost. However, conventional neural networks usually fail to capture key structural characteristics and are limited to predicting global responses (e.g., top displacement), but usually fail to achieve accurate internal force predictions with conventional training data volumes. As a result, most existing studies involving surrogate models did not concern internal force constraints. To address this issue, this study proposes a structural optimization framework based on a pre-trained Physics-Informed Neural Network (PINN) surrogate model. By embedding static equilibrium equation… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079578 - 27 April 2026
(This article belongs to the Special Issue: Topology Optimization: Theory, Methods, and Engineering Applications)
Abstract Topology optimization is widely used in lightweight structural design to determine optimal material distributions. However, density-based results are represented in an implicit pixel-wise form with blurred boundaries and jagged contours, which limits their direct use in engineering design and manufacturing. This study proposes a two-stage post-processing framework to reconstruct topology optimization results into explicit parametric geometries while preserving structural performance. The framework first extracts and processes contour points from the optimized density field and reconstructs the geometry using Non-Uniform Rational B-Splines (NURBS). A subsequent shape optimization step based on the fixed-grid finite element method (FG-FEM) More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080458 - 27 April 2026
(This article belongs to the Special Issue: Topology Optimization: Theory, Methods, and Engineering Applications)
Abstract In high-heat-flux environments, traditional cooling channels often fail to satisfy concurrent requirements for high heat transfer efficiency, temperature uniformity, and minimal pumping power. This study proposes an engineering-oriented topology optimization method for fluid-solid conjugate heat transfer to address the conflict between thermal performance and flow resistance under non-uniform heat sources. We introduce a pseudo-three-dimensional conjugate heat transfer model governed by Darcy’s law. This formulation retains three-dimensional effects, such as sidewall conduction and non-uniform surface heat flux. Moreover, the governing equations are reduced to two dimensions, thereby significantly enhancing computational efficiency. To resolve the discrepancy between More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079021 - 27 April 2026
(This article belongs to the Special Issue: Advances in Fracture Mechanics, Damage Mechanics, and Fatigue Modeling)
Abstract Cohesive zone models (CZMs) are widely used to simulate interfacial fracture, where the post-peak softening branch of the traction–separation law (TSL) can strongly influence both the predicted response and the numerical behavior, particularly when the fracture process zone is not small relative to the structure. In Abaqus, however, cohesive elements are natively restricted to bilinear and linear–exponential TSLs, and implementing other softening behaviors typically requires user subroutines, which requires advanced knowledge and limits rapid model development and testing. This work exploits Abaqus’s tabular damage-evolution capability in a different way by constructing the damage variable analytically… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079630 - 27 April 2026
Abstract The design of foundations for high-voltage electrical network lattice towers depends on reliable prediction of resistance to uplift and lateral forces. Because foundation works contribute substantially to the total project cost, a clear understanding of ultimate pullout capacity and the associated failure mechanism is required to support safe and economical design. This paper presents a three-dimensional finite element investigation using PLAXIS 3D to quantify the influence of soil type (pure sand and sand with 8% fines), footing dimensions ((3.5 × 7), (5 × 10), (7.5 × 15)), relative compaction RC are 92% and 100%, and… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079597 - 27 April 2026
Abstract This paper investigates the vibro-acoustic coupling behavior of high-speed ball bearings and the mechanisms driving vibration and radiated noise. Ball bearings consist of an inner ring, outer ring, cage, and rolling elements, whose complex interactions—impact, friction, and geometric non-uniformities—are difficult to capture experimentally. To address this challenge, a coupled numerical approach is developed by integrating the explicit nonlinear solver LS-DYNA with the acoustic module in LMS Virtual.Lab. Simultaneously, fixed boundary constraints and no-slip contact conditions are applied in the modal analysis to identify excitation sources of structural vibrations. First, a three-sphere collision simulation is employed More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080453 - 27 April 2026
Abstract Structural optimization is essential for finding optimal designs in practical engineering tasks. Metaheuristic algorithms have been widely applied in structural optimization problems in recent years, especially when dealing with discrete design variables, the nonlinearity of the objective function and constraints. Unlike gradient-based algorithms, which rely on the slope variation of a function, metaheuristic algorithms do not require derivative calculations and thus avoid being trapped in local optimum. However, metaheuristic algorithms often require numerous function evaluations, involving costly structural analyses, thus increasing computational load considerably. This paper investigates a method to reduce computational load, specifically by… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.076245 - 27 April 2026
(This article belongs to the Special Issue: Swarm and Metaheuristic Optimization for Applied Engineering Application)
Abstract This article examines wafer lots scheduling in the diffusion area in semiconductor manufacturing. The diffusion area comprises multiple tool groups. Each of them contains non-identical semiconductor tools. All tools can process multiple wafer lots simultaneously, and wafer lots processed together in a tool are called a wafer batch. Besides, each wafer lot has specific queue time limits (QTLs) between consecutive processing operations, making the scheduling problem more complicated. To solve it, a discrete backtracking search optimization algorithm (DBSA) is designed for optimizing both wafer lot assignments and wafer batch processing sequences. Once the processing sequence of wafer… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078976 - 27 April 2026
(This article belongs to the Special Issue: Modeling and Applications of Bubble and Droplet in Engineering and Sciences)
Abstract Bubble dynamics near complex boundaries is critical for engineering applications like underwater explosions and cavitation control. This study investigates the collapsing behavior of near-wall bubbles adjacent to three boundary conditions (planar, elliptical convex, and elliptical concave surfaces) using a compressible multi-component flow model. The finite volume method combined with fifth-order Weighted Essentially Non-Oscillation (WENO) reconstruction and the Harten-Lax-van Leer Contact (HLLC) Riemann solver is employed for spatial discretization, while the third-order Total Variation Diminishing (TVD) Runge-Kutta scheme handles temporal discretization. Results show that elliptical convex and concave surfaces exhibit opposite regulatory effects: the convex surface More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078891 - 27 April 2026
(This article belongs to the Special Issue: Modeling, Control and Application of Smart Materials)
Abstract Piezoelectric smart materials have been widely used in applications such as soft robotic actuation, vibration control and sensing of aerospace structures. In such contexts, the smart structures are typically subjected to significant large deformations and strong electromechanical coupling effects, which pose considerable challenges for conventional analytical approaches and classical finite element models in accurately predicting their nonlinear dynamic responses and capturing multiphysics coupling behaviors. To address these challenges in modeling and analysis, this work develops a flexible–electrical coupled computational framework with a unified mesh description based on the absolute nodal coordinate formulation (ANCF). This coupling… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080607 - 27 April 2026
(This article belongs to the Special Issue: Numerical Modeling in Technical Diagnostics and Predictive Maintenance)
Abstract The reliable detection of cracks in engineering materials remains a fundamental challenge in nondestructive testing, especially in applications that require automated inspection, reduced instrumentation costs, and robustness under noisy operational conditions. Traditional nondestructive evaluation techniques often rely on complex sensing setups or expert-dependent interpretation, which can limit scalability and real-time applicability. In this context, this study addresses the scientific problem of achieving reliable and automated crack detection using simplified sensing architectures combined with intelligent data-driven analysis. This work proposes an intelligent signal classification framework for crack detection in polymeric materials based on machine learning and… More >
 Open Access
Open Access
ARTICLE
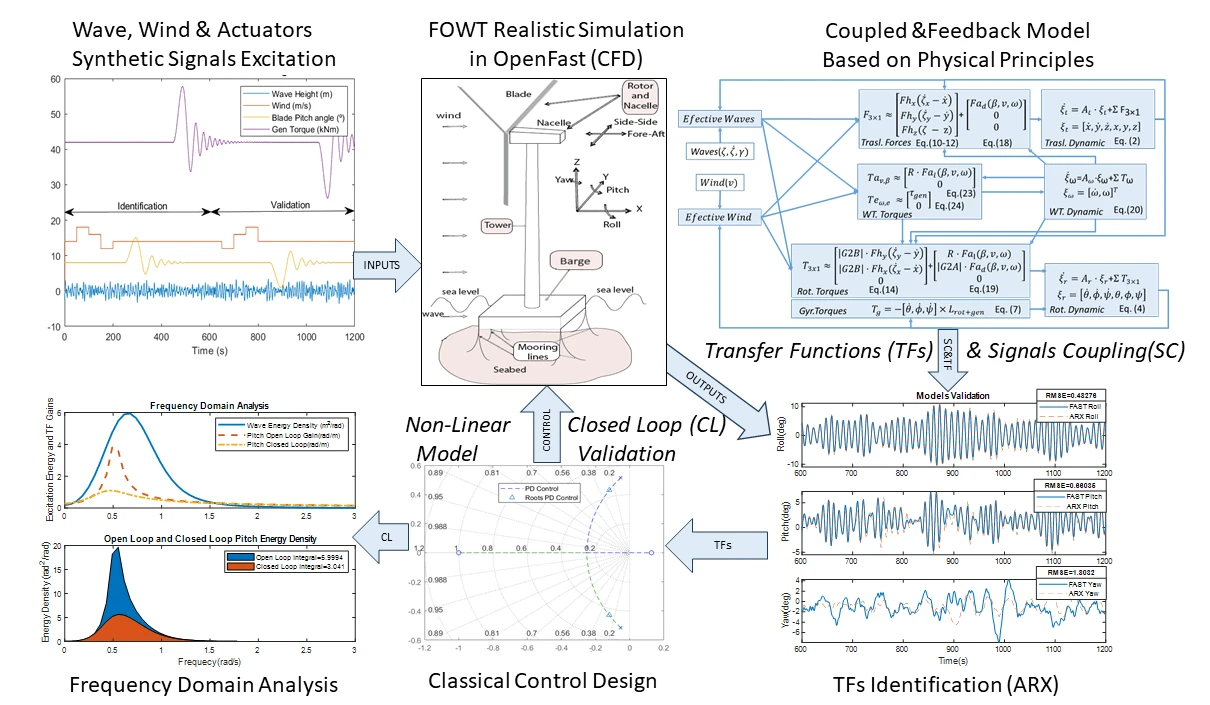
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.077663 - 27 April 2026
Abstract Wind turbines are highly efficient energy converters that exploit locally available renewable resources across many regions. In modern floating offshore wind turbines (FOWTs), strong aerodynamic and hydrodynamic loads give rise to nonlinear and tightly coupled dynamics, which typically require dedicated—and computationally demanding—simulation tools for analysis and control design. This work introduces a simplified, control-oriented mathematical model of a FOWT, derived directly from fundamental force and torque balances and explicitly incorporating the gyroscopic effect, which is often neglected in onshore wind turbines due to its comparatively lower significance. Model parameters are identified for the NREL 5-MW… More >
Graphic Abstract
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079927 - 27 April 2026
Abstract This paper introduces a novel dual-layer optimization fault diagnosis framework for inter-turn short-circuit (ITSC) faults in permanent magnet synchronous motors (PMSMs). The synergistic of a SABO-optimized VMD for enhanced feature extraction and an MFO-optimized SVM for intelligent classification is proposed. Firstly, mathematical and simulation models of ITSC faults in PMSMs are established to obtain fault phase currents and motor electromagnetic torques as characteristic fault signals. Then, the SABO algorithm is used to optimize the VMD parameters, followed by VMD decomposition of the characteristic fault signals to obtain Intrinsic Mode Functions (IMFs), and the time-domain parameters More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.076888 - 27 April 2026
Abstract The engine serves as the primary component that generates power and drives vehicle movement. Given its critical role, accurately diagnosing engine faults is essential for ensuring vehicle safety and reliability. Recent advances in machine learning (ML) have enabled the development of artificial intelligence (AI)-based diagnostic models with strong predictive performance. However, the lack of transparency in these models constrains user confidence in their diagnostic outcomes. While explainable AI (XAI) methods such as local interpretable model-agnostic explanations (LIME) and Shapley additive explanations (SHAP) have been introduced to improve interpretability, their reliance on visual outputs requires manual… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.076217 - 27 April 2026
Abstract Accurate electricity load forecasting is crucial for optimizing power distribution networks, especially in rapidly growing cities like Tabriz (annual consumption growth of 7.2%). This study presents a hybrid AI framework integrating the Temporal Fusion Transformer (TFT) and XGBoost for residual error correction. The model is trained and evaluated using actual consumption data from Tabriz’s distribution network (2021–2023). Compared to a baseline TFT model, the proposed framework demonstrates a 11.2% reduction in RMSE (from 0.1249 to 0.1109) and a 10.7% decrease in MAE (from 0.0998 to 0.0891). Attention mechanism analysis reveals temperature (importance coefficient = 0.32), More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079763 - 27 April 2026
Abstract The integration of wind-based DG introduces significant variability and uncertainty into the operation of distribution networks, which complicates the planning and decision-making process. This paper presents a dual-objective stochastic optimization framework for the optimal allocation of wind DG, considering dynamic network reconfiguration across multiple loading conditions. Probabilistic modeling of wind speed is integrated using the Weibull distribution and the associated wind power uncertainty is discretized through a scenario-based point estimation method. Variability in load is accounted for by considering multiple loading levels, and the integrated uncertainty space is constructed as the Cartesian product of wind… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.073647 - 27 April 2026
Abstract In recent years, the proliferation of social networks has been remarkable, providing a rich source for data mining endeavors. However, a significant challenge lies in safeguarding the privacy of individuals while sharing these databases publicly. Current approaches, such as K-anonymity, L-diversity, and T-closeness, are commonly employed for data anonymization in social networks. However, these techniques entail considerable information loss due to random alterations in the graph-based datasets. To address these limitations, this paper introduces a new anonymization technique called KMFC-GWO, which combines K-Member Fuzzy Clustering with Grey Wolf Optimizer. This integrated method is designed to… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.077726 - 27 April 2026
(This article belongs to the Special Issue: Computational Modeling, Simulation, and Algorithmic Methods for Dynamical Systems)
Abstract Many linear-in-parameters models arising in identification and control can be expressed as single-layer artificial neural networks (ANNs) with linear activation, enabling online learning via first-order optimization. In practice, however, standard gradient descent often exhibits slow convergence, large intermediate weights, and stagnation when the regressor data are ill-conditioned or computations are performed under finite precision. This paper proposes Gradient Descent with Time-Decaying Regularization (GD-TDR), a training algorithm that augments the quadratic loss with a regularization term whose weight decays exponentially in time. The proposed schedule enforces uniform strong convexity during early iterations, effectively mitigating neural-paralysis-like behavior associated More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.076957 - 27 April 2026
Abstract Air pollution poses a serious public health threat in developing countries such as Pakistan, where rapid urbanization and industrialization have intensified atmospheric contamination. Although mobile sensing deployed on public transportation expands spatial coverage beyond fixed monitoring stations, accurate high-resolution pollution mapping remains constrained by sparse observations, computational burden, neglected pollutant interactions, and limited interpretability. To address these challenges, this study proposes a unified physics-informed deep learning framework for fine-grained air pollution map reconstruction and joint multi-pollutant estimation. The framework integrates mobile and stationary monitoring data with atmospheric dispersion principles to enhance physical consistency under limited… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078601 - 27 April 2026
(This article belongs to the Special Issue: Recent Advances in Geospatial Artificial Intelligence (GeoAI) Models, Approaches, and Applications)
Abstract Traffic light detection and fault identification using images from road traffic cameras are important for intelligent traffic management and urban safety monitoring. However, images collected in real traffic environments show clear differences in camera view, lighting conditions, weather, and background complexity. As a result, traffic lights vary greatly in scale, spatial location, and appearance, which reduces detection accuracy in complex scenes. To deal with this problem, this paper presents a multi-scene traffic light detection and fault identification framework based on dual-attention image fusion. Large-scale road camera data from the Chengdu Traffic Management Bureau are used,… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079203 - 27 April 2026
(This article belongs to the Special Issue: Innovative Computational Models for Smart Cities)
Abstract Real-time data processing is essential in the evolving landscape of IoT applications, ensuring efficiency, reliability, and adaptability. However, conventional clustering algorithms often face difficulties in managing high-frequency, continuous IoT data streams due to limited adaptability and high computational overhead. To address these challenges, this study proposes a resilient adaptation of the BIRCH (Balanced Iterative Reducing and Clustering using Hierarchies) algorithm, tailored specifically for streaming IoT data. The enhanced approach dynamically recalculates clusters and determines the optimal number of clusters using the KneeLocator method. Unlike the original batch-oriented BIRCH, the modified version processes data incrementally, enabling More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079827 - 27 April 2026
(This article belongs to the Special Issue: Innovative Computational Models for Smart Cities)
Abstract The rapid growth of Internet of Things (IoT) technologies has transformed modern urban environments into complex smart cities, generating vast amounts of high-dimensional, heterogeneous data. Effectively analyzing this data is crucial for optimizing urban infrastructure, enhancing quality of life, and supporting sustainable development. However, smart city data presents significant challenges, including non-linear dependencies, noisy signals, and high dimensionality. To address these challenges, this study proposes the Dynamic Leader Sibha Algorithm (DLSA), a novel metaheuristic optimization technique inspired by the structured counting dynamics of the Sibha. The DLSA was applied to the Smart Cities Index dataset,… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079058 - 27 April 2026
(This article belongs to the Special Issue: Environment Modeling for Applications of Mobile Robots)
Abstract Autonomous robot teams operating in dynamic, uncertain environments require reliable mechanisms to build decentralized context models without centralized coordination. Traditional consensus methods often fail under uncertainty caused by inconsistent sensing, communication delays, or heterogeneous perception models. This paper introduces the Decentralized Belief Consensus (DBC) algorithm, a novel approach that integrates probabilistic reasoning with entropy-based certainty measures to enable adaptive and robust consensus formation in heterogeneous multi-robot systems. Each robot quantifies the uncertainty of its local observations using Shannon entropy, derives a certainty score, and fuses beliefs with neighbors through certainty-weighted averaging. This allows the team… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079324 - 27 April 2026
(This article belongs to the Special Issue: Digital Twins and Virtual Engineering Systems for Sustainable and Intelligent Decision Making: Advanced Computational Modeling, Data Integration, and AI-Driven Simulation)
Abstract Ensuring operational safety for autonomous vehicles is a critical challenge in modern engineering, particularly due to the intricate interactions among diverse traffic participants. Traditional approaches often treat planning and prediction as unidirectional processes, failing to capture the dynamic, game-theoretic nature of real-world traffic. In the context of Digital Twins, there is an urgent need for high-fidelity virtual representations that can model the continuous, bidirectional evolution of the ego vehicle and surrounding agents to support robust decision-making under uncertainty. To address these limitations, a novel framework named Planning by Simulation with mutual influence prediction is proposed,… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079954 - 27 April 2026
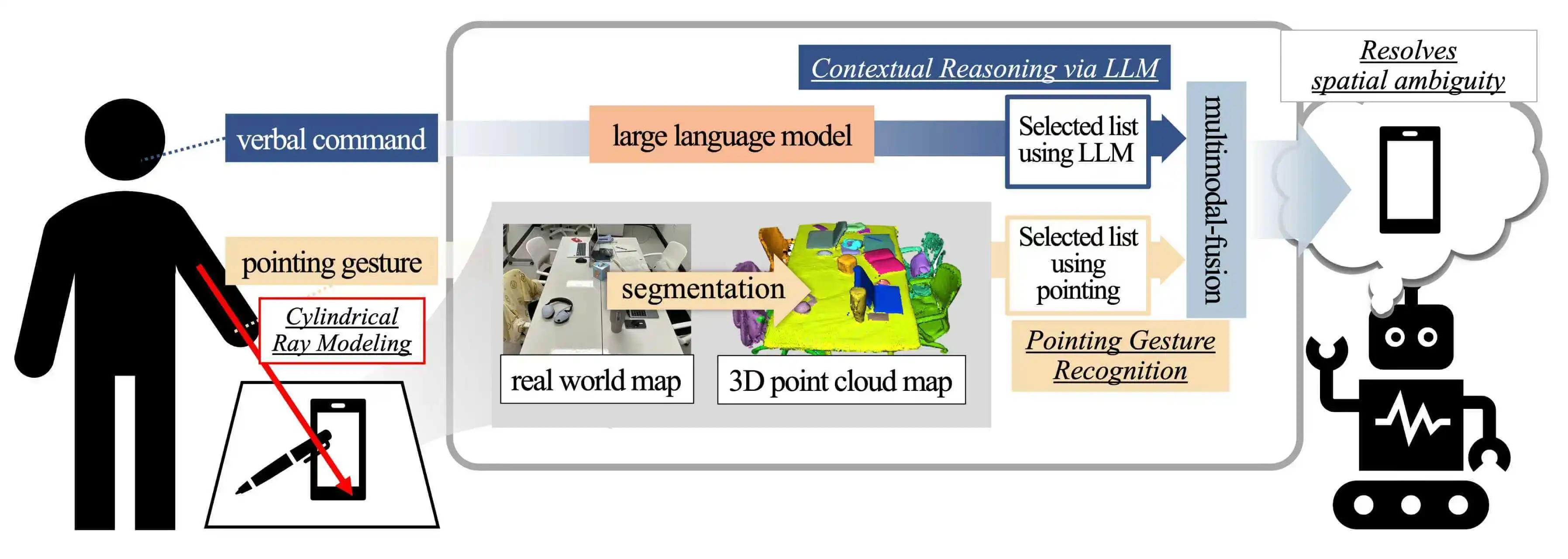
Abstract In everyday life, people effectively convey their intentions through pointing gestures without explicitly naming objects. In particular, pointing gestures used in conjunction with linguistic expressions such as “this” and “that” play a crucial role in intuitively indicating objects or locations in space. Although research on the recognition of such nonverbal gestures has been actively pursued within the field of human-computer interaction (HCI), accurately interpreting a user’s intent remains challenging in situations where the pointing gesture is ambiguous. This paper proposes an integrated system that combines a large language model (LLM), capable of understanding complex human… More >
Graphic Abstract
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.079697 - 27 April 2026
Abstract Knowledge distillation has shown impressive results in different fields, including detection, recognition, and generation. These models are excellent at tasks such as speech recognition, but they need to be shrunk down using adaptive knowledge distillation (AKD). The use of AKD can improve human-computer interactions and streamline data collection in the field of Speech Emotion Recognition (SER). This study presents a high-level approach that employs a novel adaptive knowledge distillation (AKD) with spatio-temporal transformers to acquire advanced semantic features from the input signal. This method uses an instance-by-instance correlation between the teacher and a student to determine the More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080624 - 27 April 2026
(This article belongs to the Special Issue: Data-Driven and Physics-Informed Machine Learning for Digital Twin, Surrogate Modeling, and Model Discovery, with An Emphasis on Industrial Applications)
Abstract Automated reading of analog gauges in industrial environments is essential for predictive maintenance and safety monitoring. However, conventional computer vision approaches encounter two fundamental bottlenecks: polar unwrapping techniques induce severe nonlinear scaling distortions under oblique viewing angles and axis-aligned bounding boxes (AABBs) are geometrically inefficient for encapsulating high-aspect-ratio rotating needles. To overcome these limitations, this paper proposes a novel end-to-end framework that innovatively redefines gauge reading as a structural pose estimation task. We model each gauge as a topological five-keypoint skeleton (
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.081316 - 27 April 2026
Abstract Gastrointestinal polyps are well-known precursors to colorectal cancer (CRC), making their accurate detection and segmentation during colonoscopy essential for early diagnosis and cancer prevention. Deep learning–based segmentation models trained on publicly available datasets such as Kvasir-SEG have demonstrated promising performance; however, two key challenges remain: limited robustness across diverse polyp morphologies and endoscopic imaging conditions, and the lack of interpretable decision-making mechanisms that support clinical trust and validation. Many existing centralized segmentation approaches are primarily optimized using overlap-based metrics such as the Dice coefficient and intersection over union (IoU), without adequately analyzing challenging cases such… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078862 - 27 April 2026
(This article belongs to the Special Issue: Advances in Deep Learning and Computer Vision for Intelligent Systems: Methods, Applications, and Future Directions)
Abstract Urban intersections contain severe blind zones where buildings and roadside obstacles block line-of-sight sensing, limiting the ability of autonomous vehicles to anticipate hidden hazards. This paper presents an urban-intersection-oriented non-line-of-sight (NLOS) perception framework that exploits specular reflections from building surfaces using 77 GHz frequency-modulated continuous-wave (FMCW) automotive radar. All evaluations are conducted in a MATLAB-based simulation environment that models intersection geometry, building-induced occlusions, and specular reflection-assisted propagation, and generates 77-GHz FMCW radar echoes under controllable interference; real-world validation with measured radar data and richer multipath/material modeling is planned as future work. To improve robustness under… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080335 - 27 April 2026
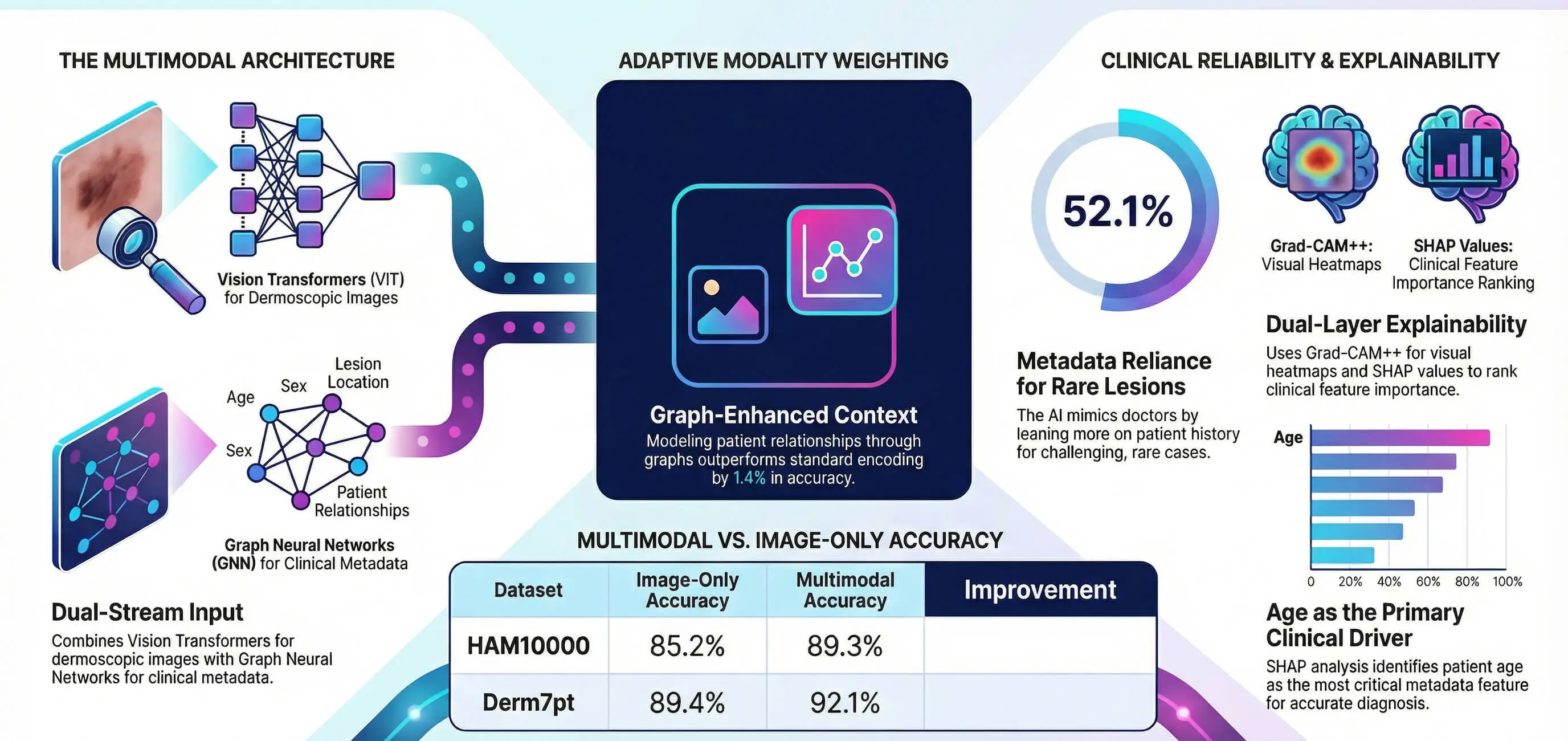
(This article belongs to the Special Issue: Advances in Deep Learning and Computer Vision for Intelligent Systems: Methods, Applications, and Future Directions)
Abstract The use of automated skin lesion classification is still a disadvantage, since there is a great visual similarity between benign and malignant lesions. The majority of deep learning methods utilize dermoscopic images only, without taking into account clinical metadata employed by dermatologists on a regular basis. The following paper proposes a vision-graph multimodal framework that links Image encoding to graph neural networks based on metadata representation through the fusion of learnable attention. The framework focuses on three limitations, which are underutilization of clinical context, absence of interpretability, and suboptimal incorporation of modalities. Gradient-weighted Class Activation… More >
Graphic Abstract
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.077324 - 27 April 2026
(This article belongs to the Special Issue: Recent Advances in Signal Processing and Computer Vision)
Abstract Early detection of Mild Cognitive Impairment (MCI) with FDG-PET is essential for timely Alzheimer’s disease intervention. However, PET image quality is limited by low spatial resolution, partial volume effects, and Poisson noise. Standard enhancement methods, such as Bilateral filtering or Contrast Limited Adaptive Histogram Equalization (CLAHE), can increase contrast but often introduce heavy noise or distort image texture, while deep learning methods may produce hallucinated structures. We propose a fully data-adaptive, non-learned 3D enhancement framework whose output is deterministic for a given input volume, that combines Laplacian-based local contrast modulation with a gradient-gated Difference-of-Gaussians (DoG)… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080241 - 27 April 2026
(This article belongs to the Special Issue: Artificial Intelligence Models in Healthcare: Challenges, Methods, and Applications)
Abstract Magnetic Resonance Imaging is one of the most commonly used neuro-oncology imaging modalities, which is a non-invasive mode of imaging and helps in detecting brain abnormalities in an effective way. Earlier researchers have demonstrated that brain tumor segmentation and classification can be effectively performed using deep learning techniques. Existing studies are primarily aimed at increasing prediction accuracy and provide insignificant consideration to model interpretability, limiting their practical application in clinical practice. To address this limitation, this research presents a two-stage explainable deep learning model, which combines transformer-based segmentation with an ensemble classification model that is… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078892 - 27 April 2026
(This article belongs to the Special Issue: Artificial Intelligence Models in Healthcare: Challenges, Methods, and Applications)
Abstract Lung cancer (LC) is among the dangerous cancers spreading progressively, and a timely LC diagnosis becomes a dire need of the time. Various imaging-based studies have been conducted for accurate LC examination through computed tomography (CT), X-ray, and histopathology. Worldwide, the proportion of LC-affected patients in hospitals is growing, thereby increasing imaging data for fast processing and early examination. To facilitate histopathological imaging-based automated and timely decision making for accurate LC prediction, a Context Aware Fusion Network (CAFNet) for holistic feature learning and spatially localized feature learning is proposed in this study for the efficient… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080279 - 27 April 2026
(This article belongs to the Special Issue: Advanced Computational Intelligence Techniques, Uncertain Knowledge Processing and Multi-Attribute Group Decision-Making Methods Applied in Modeling of Medical Diagnosis and Prognosis)
Abstract Lung cancer accounts for the highest number of cancer deaths globally, underscoring the urgent need for early and precise detection to enhance patient outcomes. While deep learning has made remarkable strides in analyzing medical images, current approaches face a fundamental challenge. They cannot adequately capture detailed local patterns and broader contextual relationships within lung Computed tomography (CT) scans. To address this limitation, we introduce AMVT-NMN (adaptive multi-scale vision transformer with neuromorphic memory networks), which combines three complementary mechanisms. The dynamic adaptive kernel networks component intelligently adjusts receptive field sizes based on input characteristics, enabling flexible… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078510 - 27 April 2026
(This article belongs to the Special Issue: Exploring the Impact of Artificial Intelligence on Healthcare: Insights into Data Management, Integration, and Ethical Considerations)
Abstract Cardiovascular diseases (CVD) remain the leading cause of global mortality, making early and accurate diagnosis essential for improving patient outcomes. However, most existing deep learning approaches address cardiac image segmentation or disease classification independently, limiting their effectiveness in complex clinical decision-making scenarios. In this study, we propose an explainable spatio-temporal deep learning framework that integrates segmentation-guided representation learning with efficient temporal modeling for automated CVD detection. The proposed architecture incorporates the Segment Anything Model for Medical Imaging in 2D (SAM-Med2D) to achieve accurate cardiac structure segmentation, followed by Mamba-based temporal feature extraction and Transformer-driven spatial… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.077118 - 27 April 2026
(This article belongs to the Special Issue: Computer Modeling for Future Communications and Networks)
Abstract Some critical applications of emergency, Active Safe Driving (ASD), eV2X, and LEO communications require ultra-low delay and highly reliable transmission according to beyond 5G-Advanced (5G-A), 6G, and LEO specifications. Related studies proposed various scheduling algorithms in terms of single and multiple QoS requirements. However, these approaches tend to prioritize traditional QoS requirements while neglecting crucial considerations such as bearer costs and associated benefits. Moreover, most scheduling neglects the carrying cost according to the radio resource state and the bringing reward from different types of flows. Thus, this paper proposes a novel cost-based flow scheduling (eSCFS)… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078467 - 27 April 2026
(This article belongs to the Special Issue: Computer Modeling for Future Communications and Networks)
Abstract The rapid proliferation of Internet of Things (IoT) devices has increased the importance of network intrusion detection systems (NIDS) for protecting modern networks. However, many machine learning and deep learning based NIDS rely on large volumes of labeled attack data, which is often impractical to obtain for newly emerging or rare attacks. This paper presents a benchmark-style systematic evaluation of meta-learning-based Few-Shot Learning (FSL) classifiers for detecting previously unseen intrusions with limited labeled data. We investigate three representative FSL models, namely Prototypical Networks, Relation Networks, and MetaOptNet, and further examine two decision-level ensemble strategies based… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.077316 - 27 April 2026
(This article belongs to the Special Issue: Machine learning and Blockchain for AIoT: Robustness, Privacy, Trust and Security)
Abstract The growing frequency of malicious attacks on Internet of Things (IoT) devices has rendered conventional approaches with static label-dependent risk assessment models obsolete, especially when coping with unknown and continuously evolving threats. To mitigate these challenges, a novel dynamic trust evaluation framework approach is proposed in this work. The proposed framework utilized unsupervised learning and zero-knowledge proofs to assess device risks in complex environments adaptively, with an accuracy rate of 98.96% for normal clustering and 95.39% for anomalies. K-means clustering algorithm is leveraged to distinguish risk patterns with an additional Decision Tree classification algorithm to More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.077799 - 27 April 2026
(This article belongs to the Special Issue: Advanced Security and Privacy for Future Mobile Internet and Convergence Applications: A Computer Modeling Approach)
Abstract Due to its partly open-source architecture, which allows for application analysis and repackaging, along with its large market share, the Android operating system is a main target for malware. In recent years, researchers have widely adopted neural network-based methods for detecting Android malware, achieving impressive results but without interpretability. Interpretability is crucial for showing how models behave and identifying biases in their predictions, which helps in validating and improving them. Additionally, in urgent malware analysis situations, interpretability lets analysts quickly assess harmful behaviors and aids in future malware development and investigation. Therefore, interpretability is vital… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.078247 - 27 April 2026
(This article belongs to the Special Issue: Advanced Security and Privacy for Future Mobile Internet and Convergence Applications: A Computer Modeling Approach)
Abstract In next-generation non-terrestrial network environments, the increasing risk of detection by unauthorized observers has motivated extensive research on covert communication approaches that minimize the probability of detection. In particular, jamming-assisted cooperative covert communication has attracted significant attention as an effective approach to simultaneously ensure communication performance and security, leading to growing interest in cooperative architectures among heterogeneous platforms. This study investigates covert communication in Low Earth Orbit (LEO) satellite–unmanned aerial vehicle (UAV) cooperative networks, where the LEO satellite serves a legitimate user, while the UAV acts as a cooperative jammer to enhance covertness. A network… More >
 Open Access
Open Access
ARTICLE
CMES-Computer Modeling in Engineering & Sciences, Vol.147, No.1, 2026, DOI:10.32604/cmes.2026.080287 - 27 April 2026
(This article belongs to the Special Issue: Emerging Technologies in Information Security: Modeling, Algorithms, and Applications)
Abstract The real-time systems perform key functionalities in various fields to automate the communication and response in critical events. The Internet of Things (IoT), integrated with numerous physical objects, gathers environmental data, processes it at the edge, and provides intelligent decisions while routing health records to processing units. However, the dynamic and resource-constrained nature of IoT-based healthcare environments introduces significant challenges related to latency, transmission costs, and the reliable interaction of devices amid uncertain activities. In this work, we propose a framework for a consistent and trustworthy system that uses a weighted trust aggregation model to More >